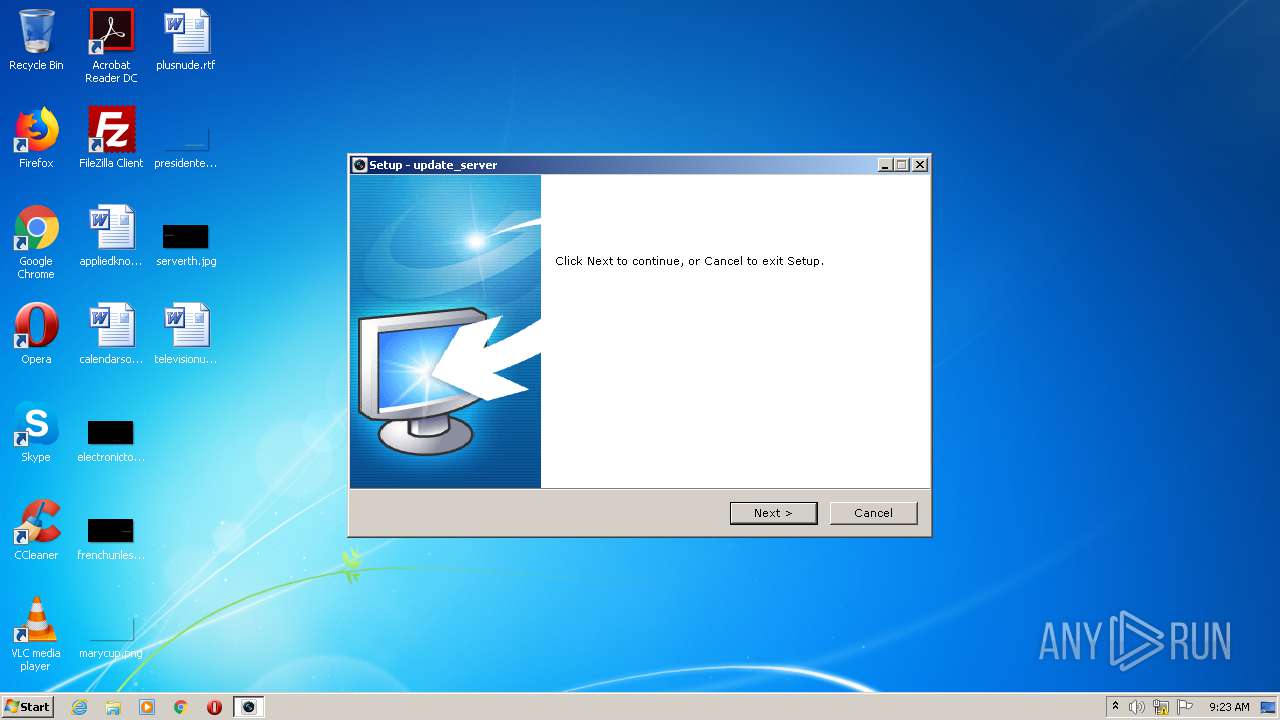
| download: | update_server.exe |
| Full analysis: | https://app.any.run/tasks/c42ec14c-e5d3-4ab5-9d65-74e4169530ea |
| Verdict: | Malicious activity |
| Analysis date: | December 09, 2020, 09:23:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 00BDF110E174A3A21AF41F0BC83D8885 |
| SHA1: | 7FE6D4E54184D2F96FC71AA161E3AA64F5D65BB7 |
| SHA256: | 980B3BF13ADA5F02AA6642E45489600966B5825A382FD0BA3DFAE9BE8AD9FD62 |
| SSDEEP: | 49152:+2Q2fcbD7vqpLO9jmzJUab9WcsXlxMOc+f5ry0LjygM9hzTXlloP0cpOLUgbh:nQqYD7K0jmzJnAxMOc+fJygjygMbzzlR |
MALICIOUS
Drops executable file immediately after starts
- update_server.tmp (PID: 2156)
- update_server.exe (PID: 1908)
Loads dropped or rewritten executable
- SPUpDateServer.exe (PID: 3720)
Application was dropped or rewritten from another process
- SPUpDateServer.exe (PID: 3720)
- startUp.exe (PID: 3072)
SUSPICIOUS
Executable content was dropped or overwritten
- update_server.exe (PID: 1908)
- update_server.tmp (PID: 2156)
Drops a file with too old compile date
- update_server.exe (PID: 1908)
- update_server.tmp (PID: 2156)
Drops a file that was compiled in debug mode
- update_server.tmp (PID: 2156)
Creates a directory in Program Files
- update_server.tmp (PID: 2156)
- SPUpDateServer.exe (PID: 3720)
Creates files in the program directory
- SPUpDateServer.exe (PID: 3720)
INFO
Loads dropped or rewritten executable
- update_server.tmp (PID: 2156)
Application was dropped or rewritten from another process
- update_server.tmp (PID: 2156)
Creates files in the program directory
- update_server.tmp (PID: 2156)
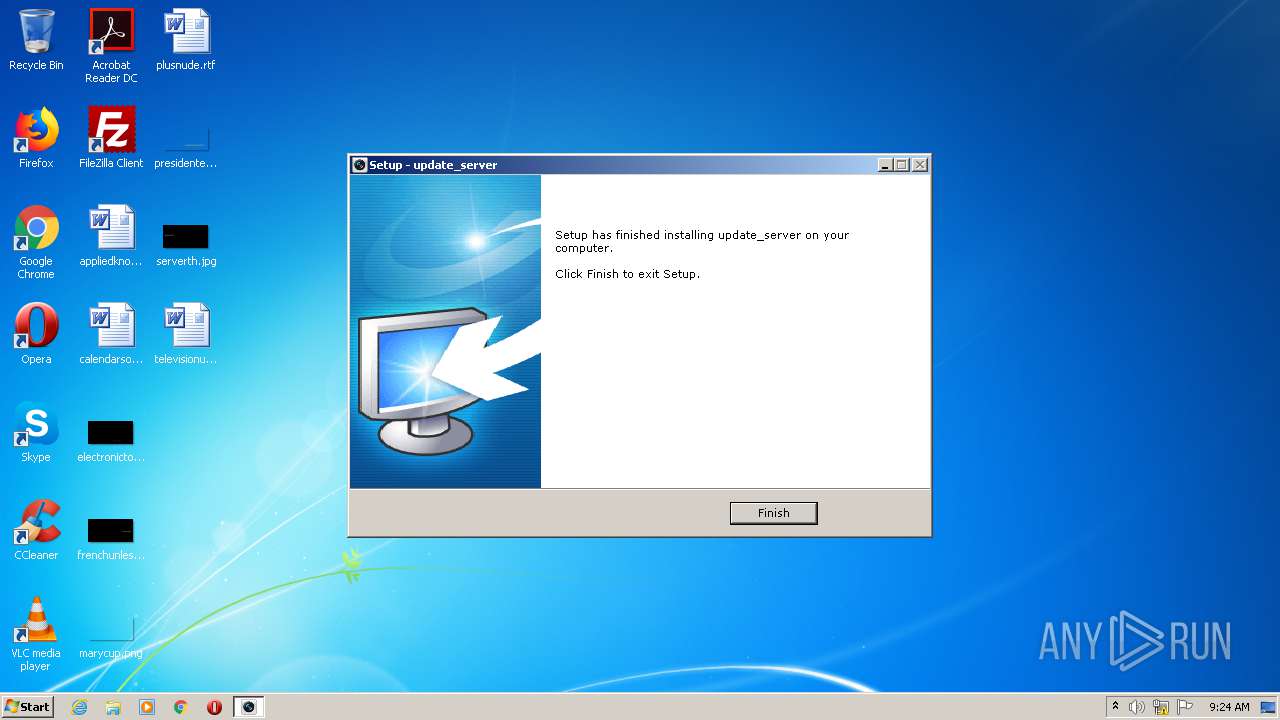
Creates a software uninstall entry
- update_server.tmp (PID: 2156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 14848 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b24 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.1.0 |
| ProductVersionNumber: | 2.3.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | update_server Setup |
| FileVersion: | 2.3.1.0 |
| LegalCopyright: | |
| ProductName: | update_server |
| ProductVersion: | 2.3.1.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | update_server Setup |
| FileVersion: | 2.3.1.0 |
| LegalCopyright: | - |
| ProductName: | update_server |
| ProductVersion: | 2.3.1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009244 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52973 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73422 |
BSS | 0x0000C000 | 0x00000E48 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x0000286C | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.77585 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04657 | 1387 | Latin 1 / Western European | English - United States | RT_MANIFEST |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | Latin 1 / Western European | UNKNOWN | RT_STRING |
11111 | 4.50366 | 44 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
MAINICON | 1.7815 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
41
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1908 | "C:\Users\admin\AppData\Local\Temp\update_server.exe" | C:\Users\admin\AppData\Local\Temp\update_server.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: update_server Setup Exit code: 0 Version: 2.3.1.0 Modules
| |||||||||||||||
| 2156 | "C:\Users\admin\AppData\Local\Temp\is-0FP1B.tmp\update_server.tmp" /SL5="$60138,2432407,53760,C:\Users\admin\AppData\Local\Temp\update_server.exe" | C:\Users\admin\AppData\Local\Temp\is-0FP1B.tmp\update_server.tmp | update_server.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.50.0.0 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Local\Temp\update_server.exe" | C:\Users\admin\AppData\Local\Temp\update_server.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: update_server Setup Exit code: 3221226540 Version: 2.3.1.0 Modules
| |||||||||||||||
| 3072 | "C:\Program Files\hik\update_server\startUp.exe" | C:\Program Files\hik\update_server\startUp.exe | update_server.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: startUp Application Exit code: 0 Version: 2, 3, 0, 0 Modules
| |||||||||||||||
| 3720 | "C:\Program Files\hik\update_server\SPUpDateServer.exe" | C:\Program Files\hik\update_server\SPUpDateServer.exe | startUp.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SPUpDate Application Exit code: 0 Version: 2, 3, 1, 0 Modules
| |||||||||||||||
Total events
400
Read events
380
Write events
20
Delete events
0
Modification events
| (PID) Process: | (2156) update_server.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | SPUpDateServerrun |
Value: C:\Program Files\hik\update_server\startUp.exe | |||
| (PID) Process: | (2156) update_server.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\shipin7\shipin7_update_server |
| Operation: | write | Name: | InstallPath |
Value: C:\Program Files\hik\update_server | |||
| (PID) Process: | (2156) update_server.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\shipin7\shipin7_update_server |
| Operation: | write | Name: | ClientType |
Value: PCUpdateServer | |||
| (PID) Process: | (2156) update_server.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\shipin7\shipin7_update_server |
| Operation: | write | Name: | ClientVision |
Value: 2.3.1.0 | |||
| (PID) Process: | (2156) update_server.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\shipin7\shipin7_update_server |
| Operation: | write | Name: | ClientKey |
Value: 10 | |||
| (PID) Process: | (2156) update_server.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A9A0CFDF-AD32-4FA0-8179-405A04F8E7DA}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.3.5 (a) | |||
| (PID) Process: | (2156) update_server.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A9A0CFDF-AD32-4FA0-8179-405A04F8E7DA}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\hik\update_server | |||
| (PID) Process: | (2156) update_server.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A9A0CFDF-AD32-4FA0-8179-405A04F8E7DA}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\hik\update_server\ | |||
| (PID) Process: | (2156) update_server.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A9A0CFDF-AD32-4FA0-8179-405A04F8E7DA}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: hik | |||
| (PID) Process: | (2156) update_server.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A9A0CFDF-AD32-4FA0-8179-405A04F8E7DA}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
26
Suspicious files
0
Text files
9
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2156 | update_server.tmp | C:\Program Files\hik\update_server\is-BSBIQ.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | update_server.tmp | C:\Program Files\hik\update_server\is-89REE.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | update_server.tmp | C:\Program Files\hik\update_server\is-4U52Q.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | update_server.tmp | C:\Program Files\hik\update_server\is-5A0S0.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | update_server.tmp | C:\Program Files\hik\update_server\is-G0DQ4.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | update_server.tmp | C:\Program Files\hik\update_server\is-O00I4.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | update_server.tmp | C:\Program Files\hik\update_server\is-3L0GC.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | update_server.tmp | C:\Program Files\hik\update_server\is-SVJ6R.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | update_server.tmp | C:\Program Files\hik\update_server\is-T3NJC.tmp | — | |
MD5:— | SHA256:— | |||
| 2156 | update_server.tmp | C:\Program Files\hik\update_server\is-C8NVA.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
4
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3720 | SPUpDateServer.exe | POST | 200 | 183.136.184.226:80 | http://log.ys7.com:80/statistics.do?systemName=studio_client_upgrade&cts=10&sl_ver=&sys_ver=6.1&sys_build=4026539441&b1=7601&hc=6c3675c54628e3d02bb253e27d3bc636&clt_ver=2.3.1.0 | CN | text | 4 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3720 | SPUpDateServer.exe | 183.136.184.252:443 | api.ys7.com | No.288,Fu-chun Road | CN | unknown |
3720 | SPUpDateServer.exe | 183.136.184.226:80 | log.ys7.com | No.288,Fu-chun Road | CN | unknown |
3720 | SPUpDateServer.exe | 183.136.184.218:443 | api.ys7.com | No.288,Fu-chun Road | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ys7.com |
| unknown |
log.ys7.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3720 | SPUpDateServer.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
3720 | SPUpDateServer.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
Process | Message |
|---|---|
startUp.exe | *****¿ªÆôÉý¼¶¼ì²â½ø³ÌC:\Program Files\hik\update_server\SPUpDateServer.exe
|
SPUpDateServer.exe | SPUPDATE_Init
|
SPUpDateServer.exe | GetVisionNodeInfo success ,path:SOFTWARE\shipin7\shipin7_update_server,Vision:2.3.1.0
|
SPUpDateServer.exe | SPUPDATE_GetVersion
|
SPUpDateServer.exe | SetUnhandledExceptionFilter succ |
SPUpDateServer.exe | SPUPDATE_Start start
|
SPUpDateServer.exe | SPIpcServe start success
|
SPUpDateServer.exe | SPUPDATE_Start end
|
SPUpDateServer.exe | ReadPhysicalDriveInNTWithZeroRights ret:1 |
SPUpDateServer.exe | check updateserver update
|