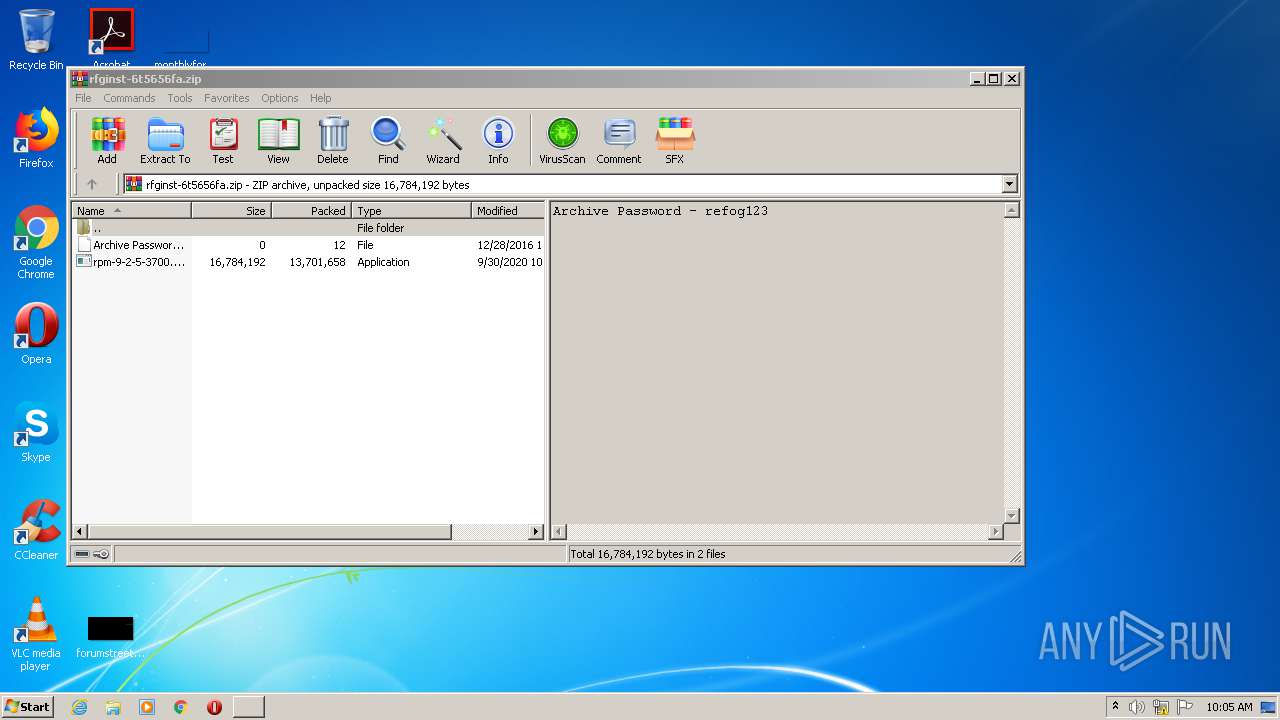
| File name: | rfginst-6t5656fa.zip |
| Full analysis: | https://app.any.run/tasks/eaa9042f-9600-4ad3-95ee-ab221f838f8a |
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2020, 10:05:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | DECA2E38B76DD80C7C31D6A93DB5D8D1 |
| SHA1: | B8E6E935C2C74AA4D1BC5C02E228C61E400455F1 |
| SHA256: | 97F46D2066B84392352EEF948BC1E71A6556241A8B0B2434042C0737DA4231A5 |
| SSDEEP: | 393216:1/iTLhwrg2XWiOeZz/1QJRdNztiZHhd0xDu4+iKgYd:CLhTxeJ/1QJtcZHhdiCXd |
MALICIOUS
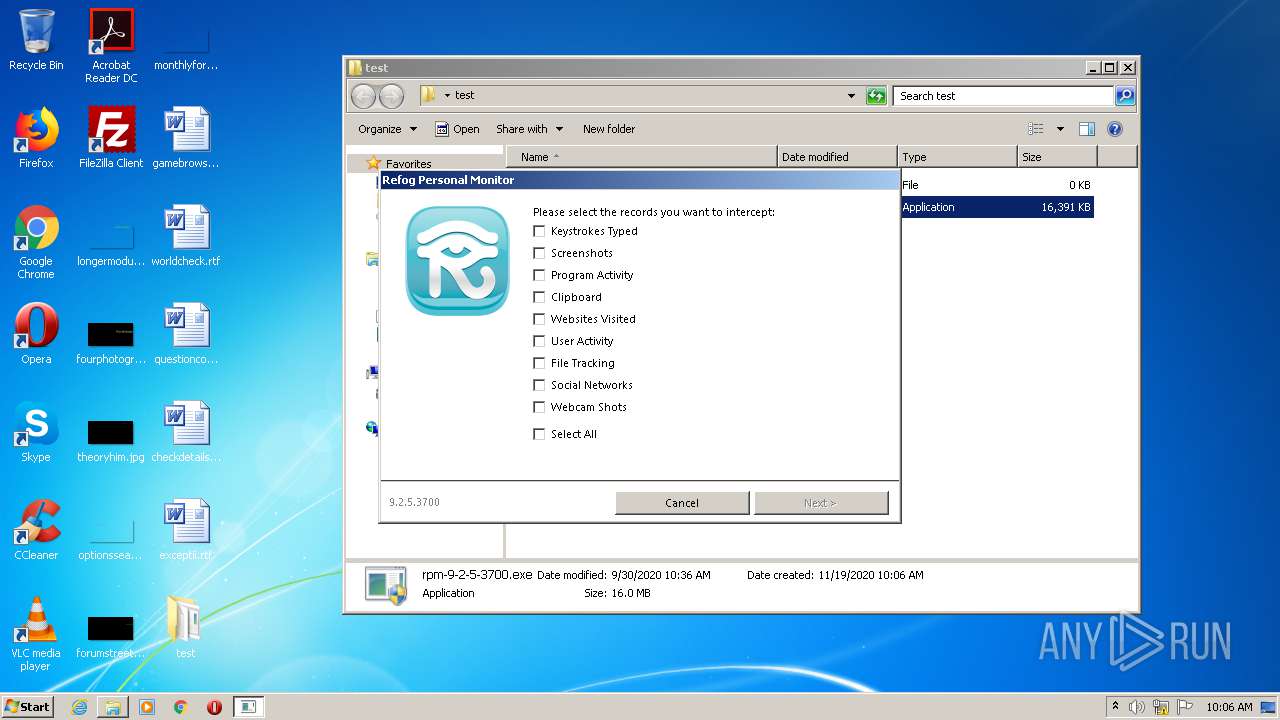
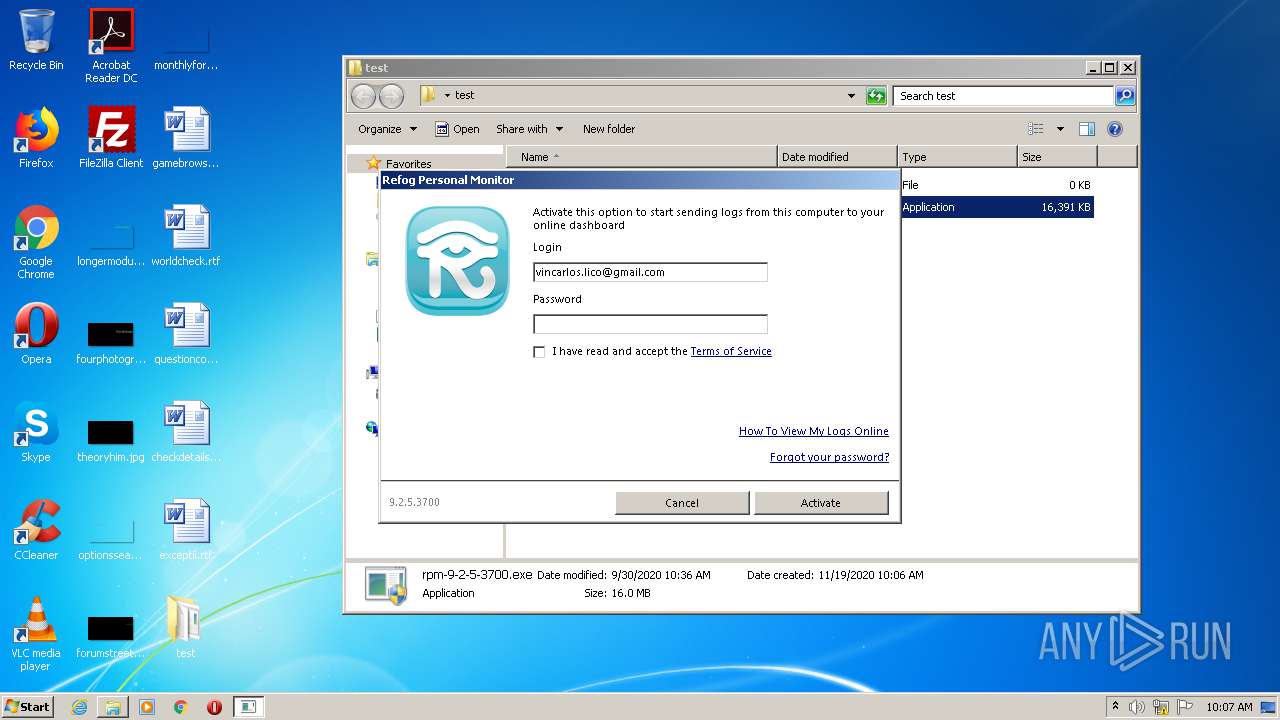
Application was dropped or rewritten from another process
- rpm-9-2-5-3700.exe (PID: 4088)
- rpm-9-2-5-3700.exe (PID: 1688)
- rpm-9-2-5-3700.exe (PID: 996)
- rpm-9-2-5-3700.exe (PID: 2780)
SUSPICIOUS
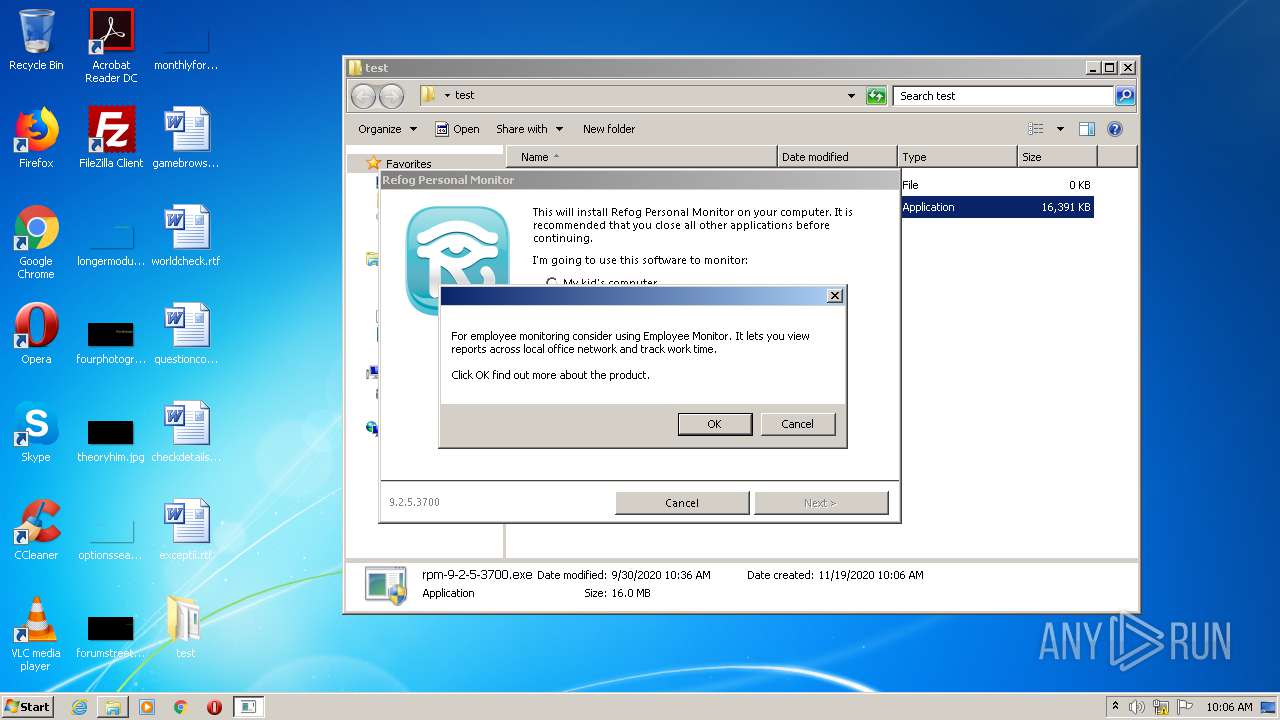
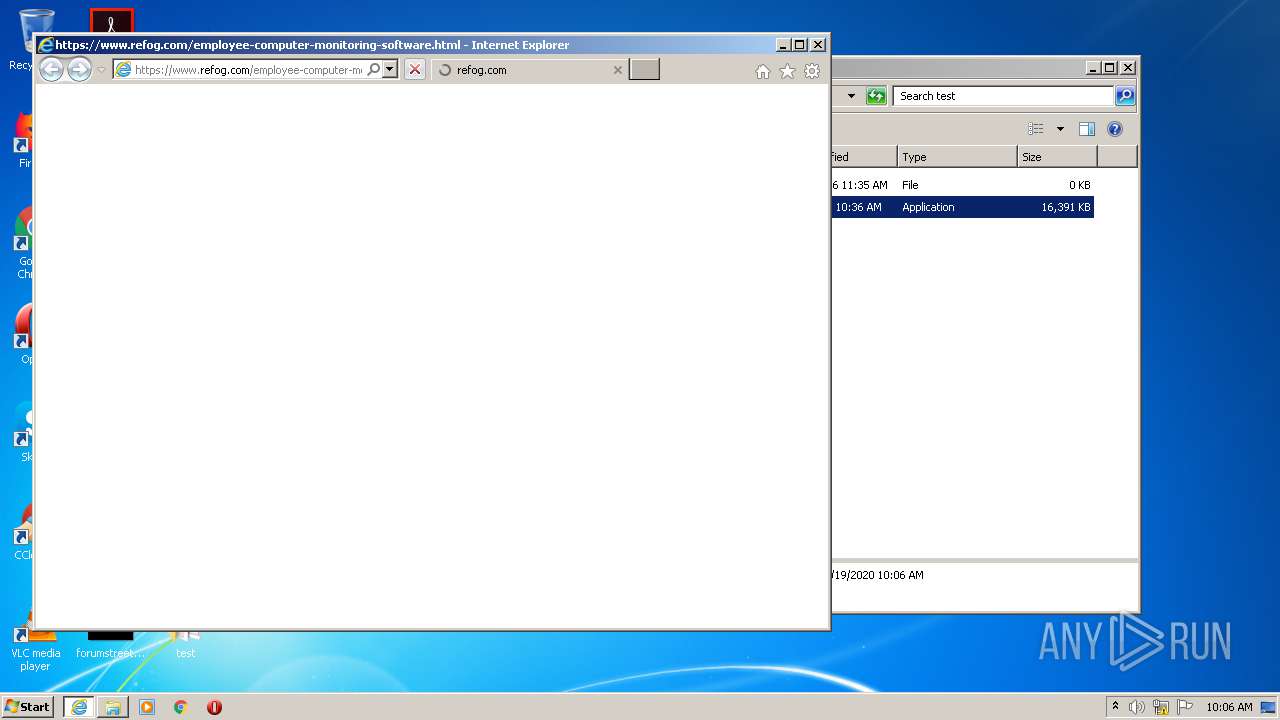
Starts Internet Explorer
- rpm-9-2-5-3700.exe (PID: 996)
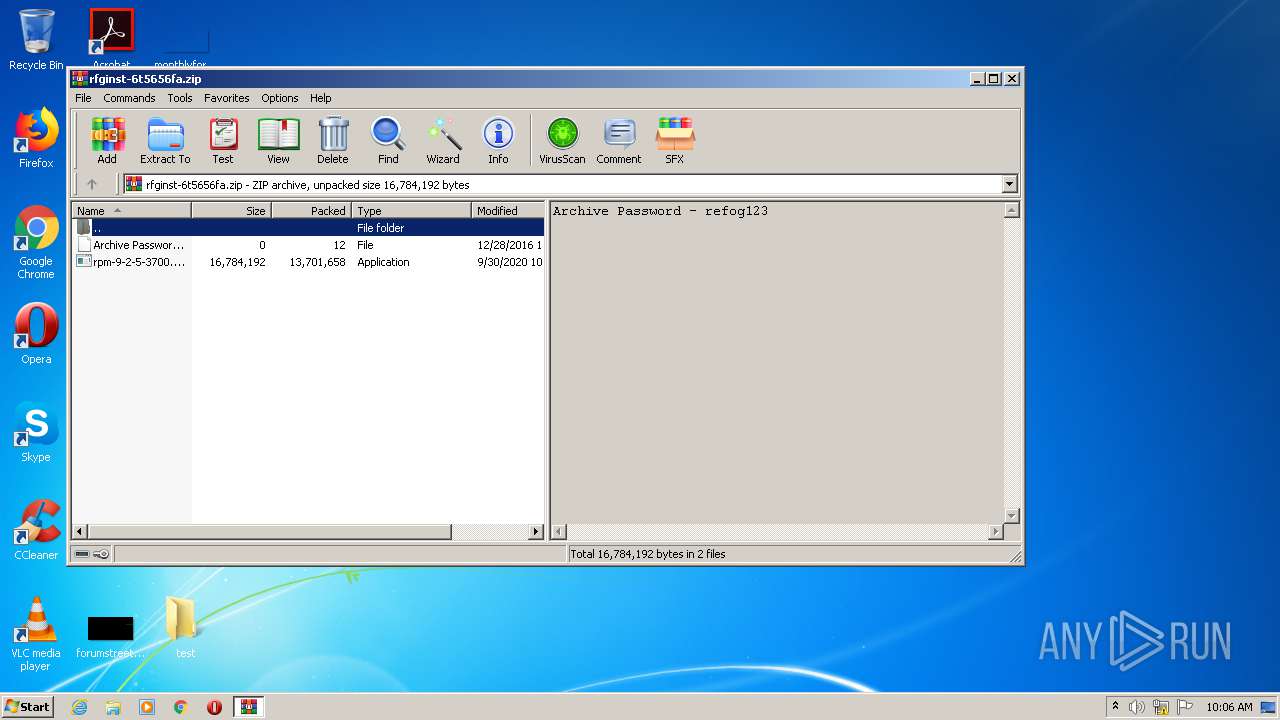
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2792)
INFO
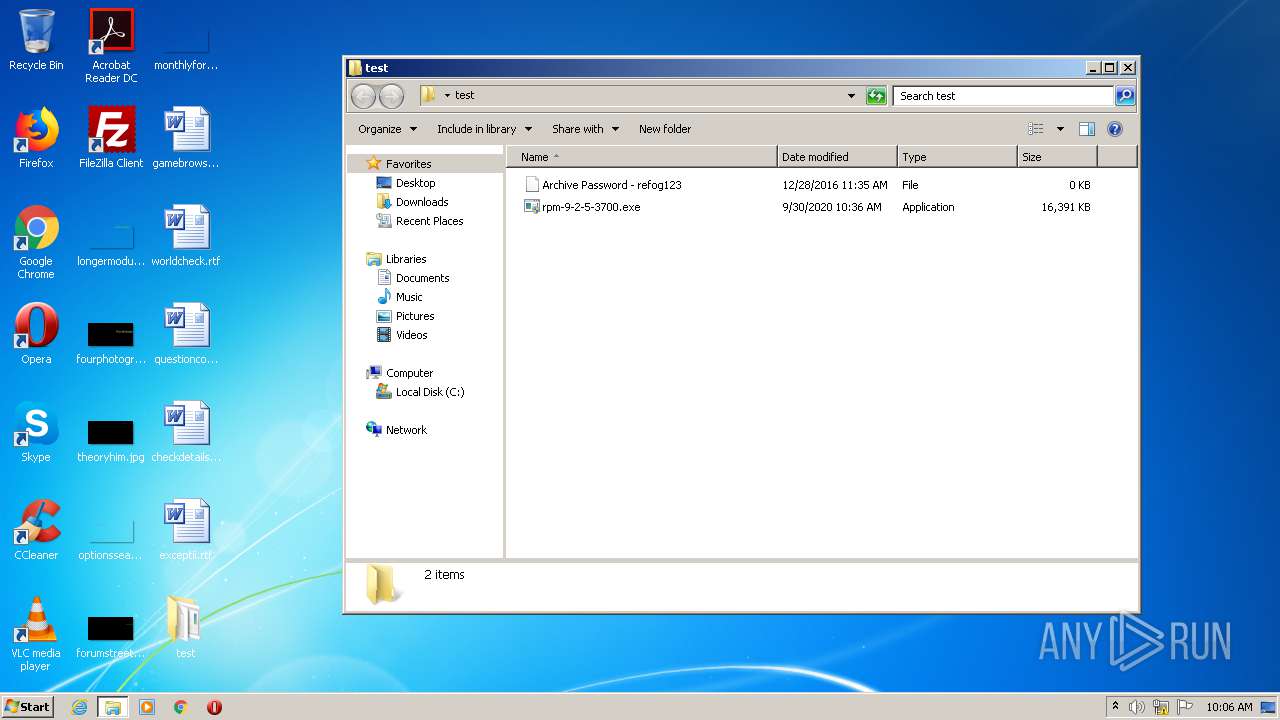
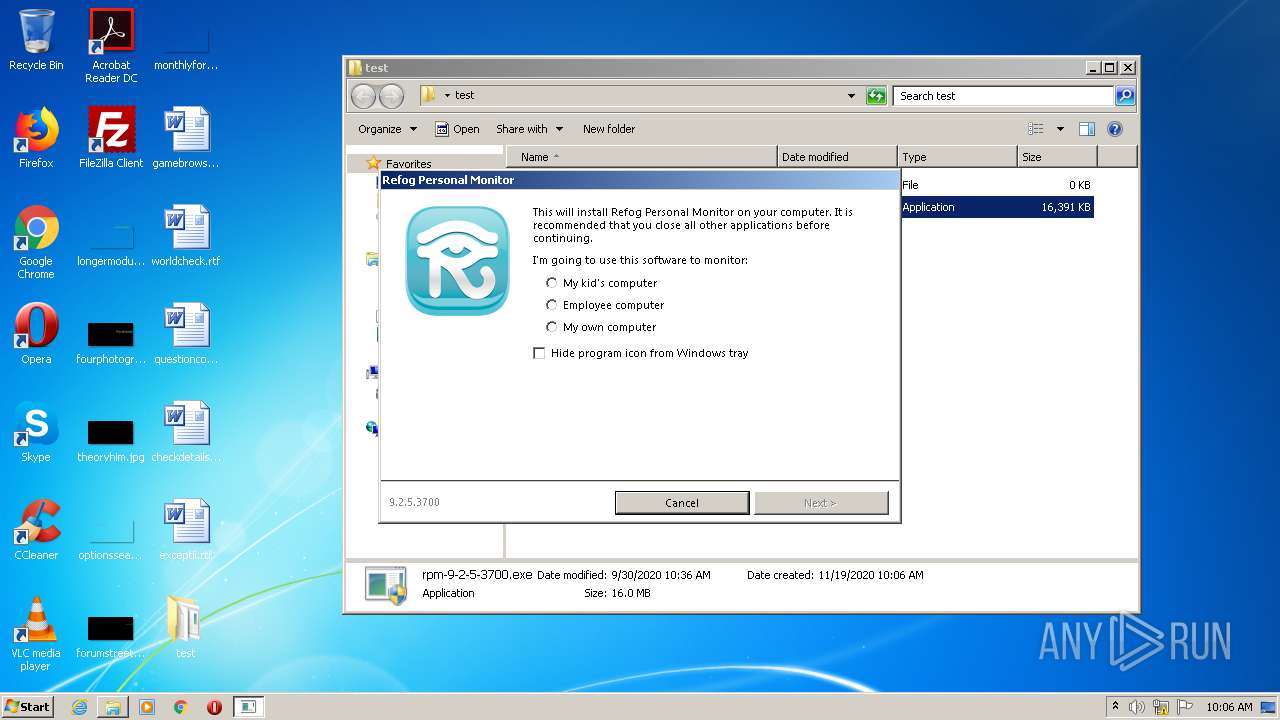
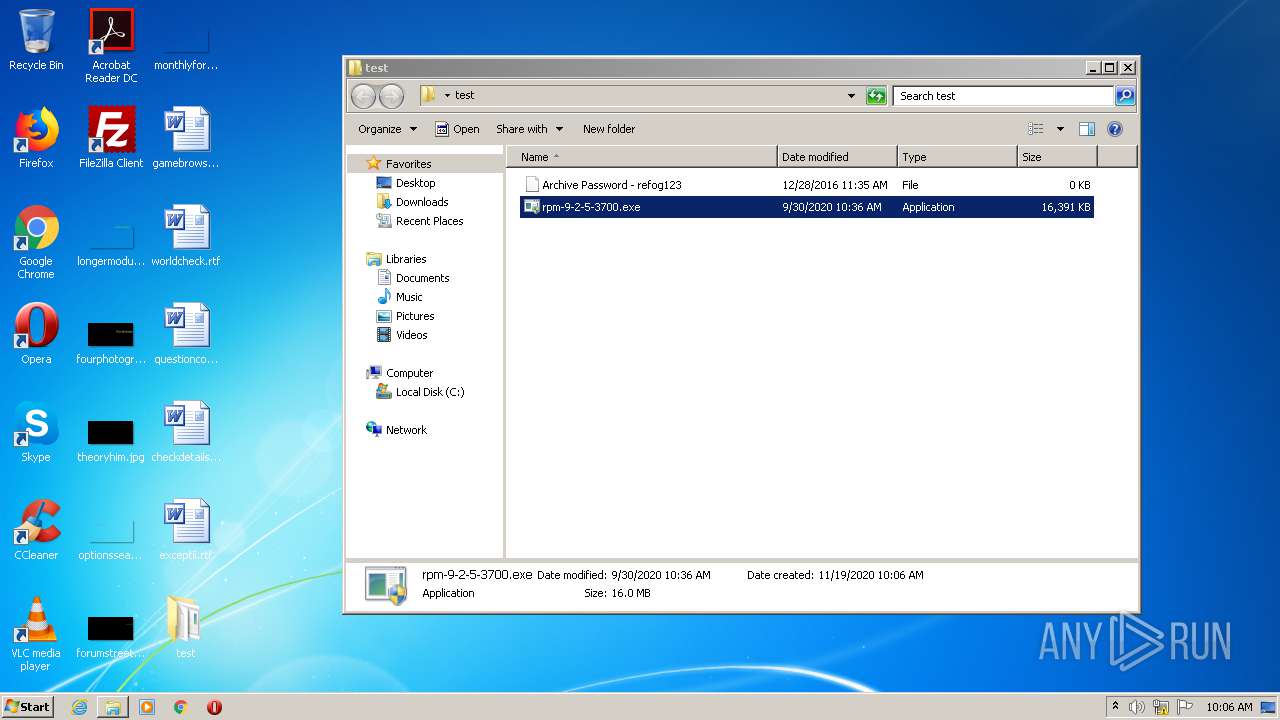
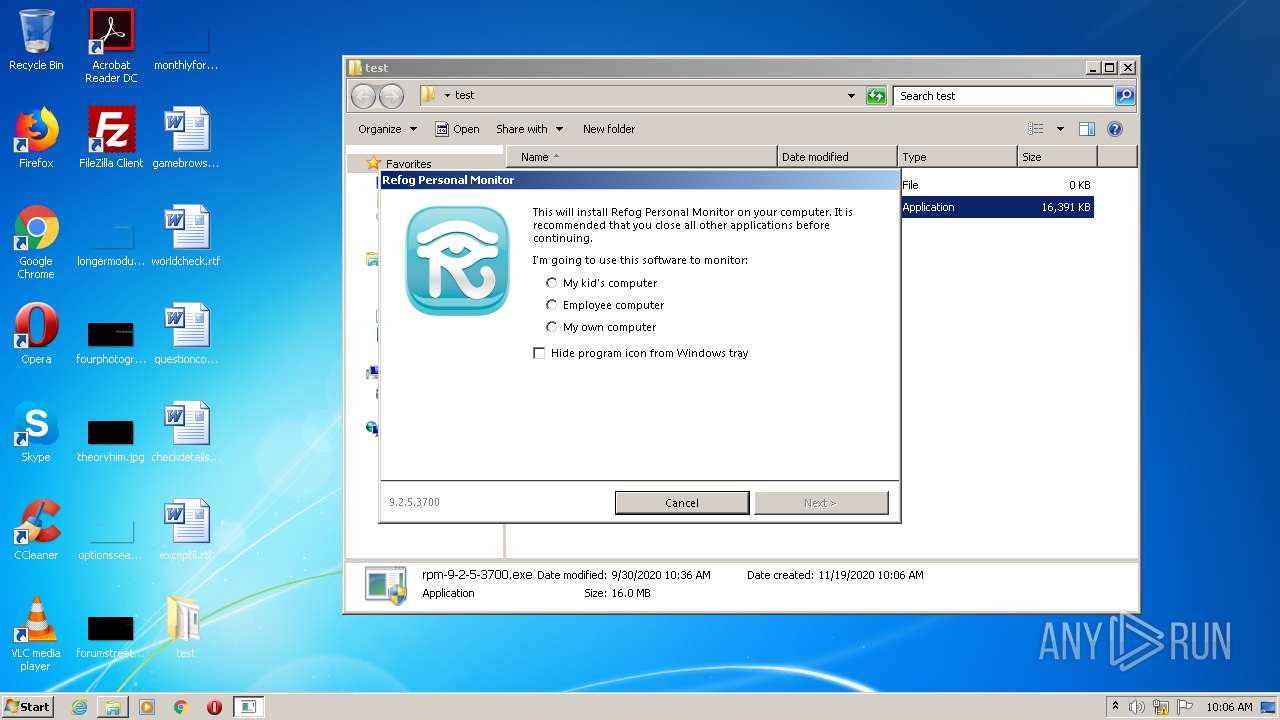
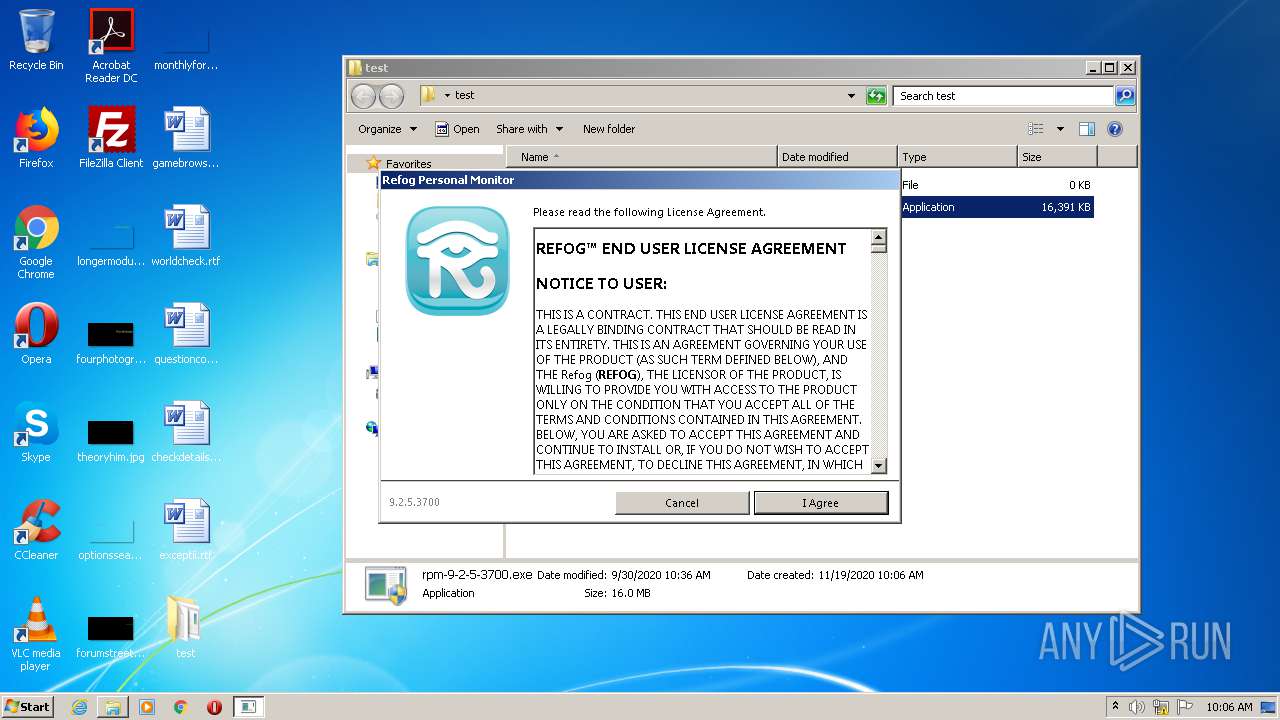
Manual execution by user
- rpm-9-2-5-3700.exe (PID: 4088)
- rpm-9-2-5-3700.exe (PID: 996)
- rpm-9-2-5-3700.exe (PID: 1688)
- rpm-9-2-5-3700.exe (PID: 2780)
Changes internet zones settings
- iexplore.exe (PID: 1692)
Application launched itself
- iexplore.exe (PID: 1692)
Reads Internet Cache Settings
- iexplore.exe (PID: 2160)
- iexplore.exe (PID: 1692)
Changes settings of System certificates
- iexplore.exe (PID: 2160)
Reads settings of System Certificates
- iexplore.exe (PID: 2160)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2160)
Reads internet explorer settings
- iexplore.exe (PID: 2160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | None |
| ZipModifyDate: | 2016:12:28 14:35:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 12 |
| ZipUncompressedSize: | 12 |
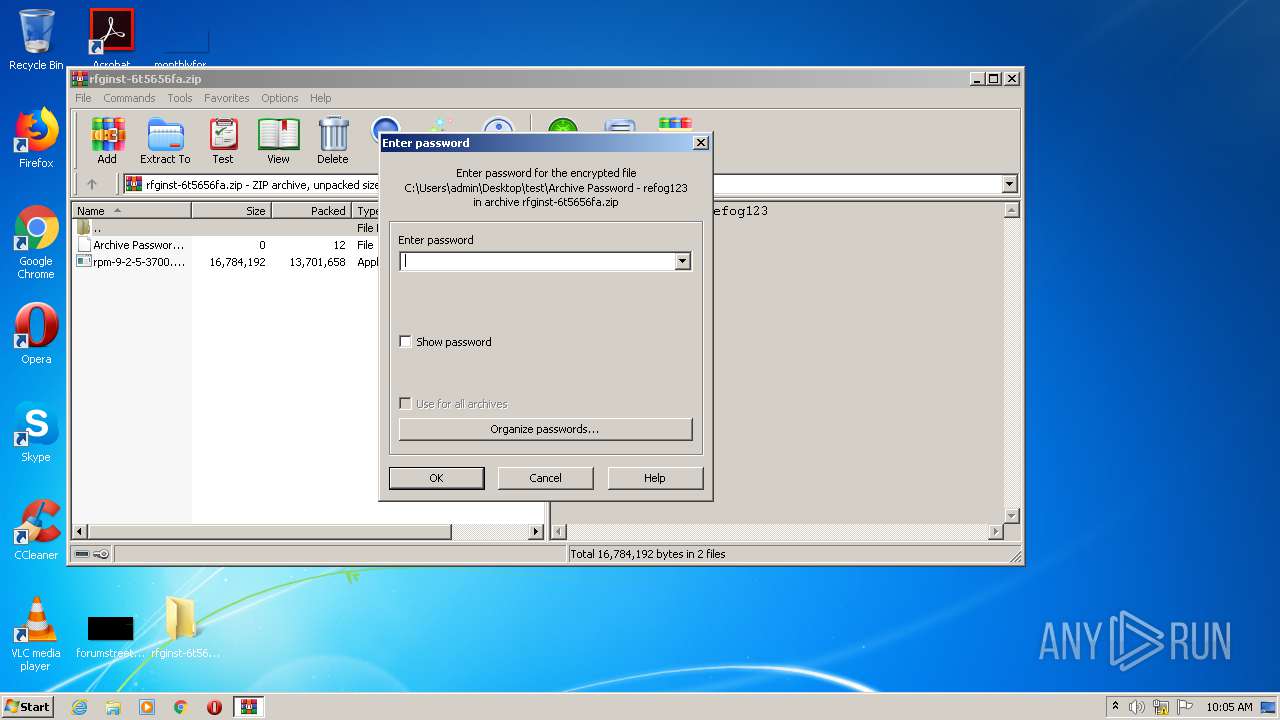
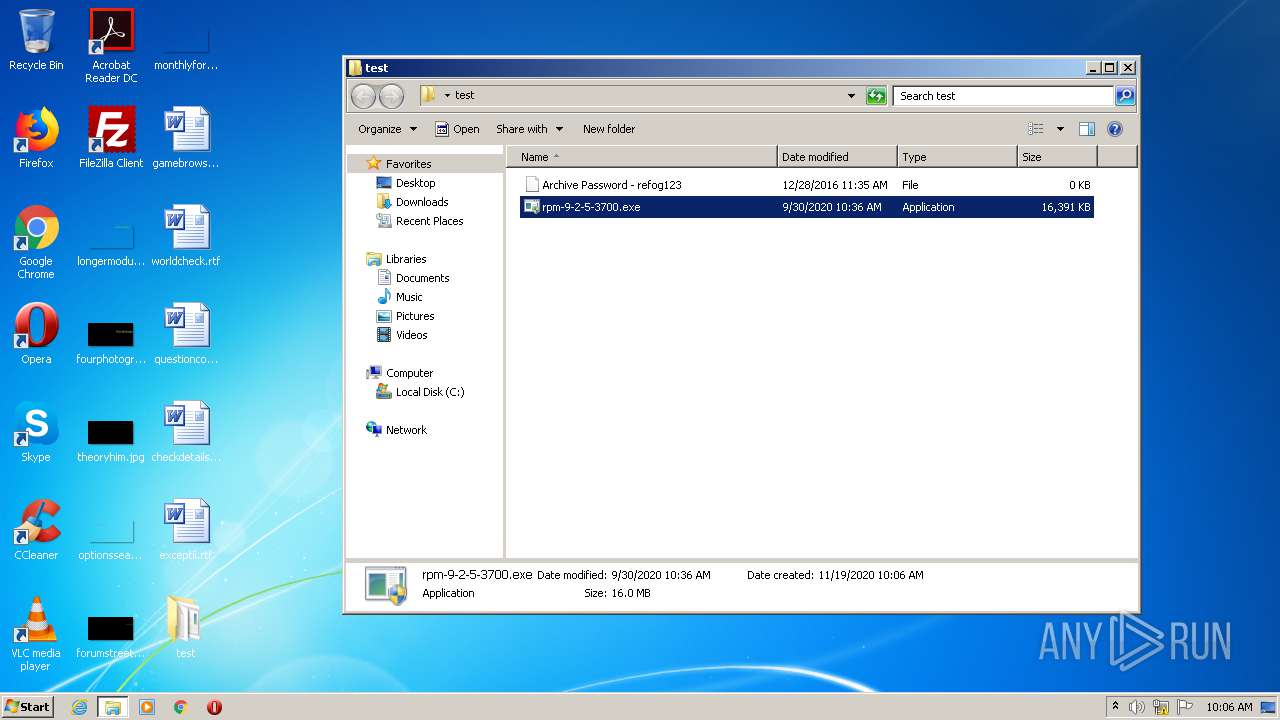
| ZipFileName: | Archive Password - refog123 |
Total processes
49
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 996 | "C:\Users\admin\Desktop\test\rpm-9-2-5-3700.exe" | C:\Users\admin\Desktop\test\rpm-9-2-5-3700.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 9.2.5.3700 Modules
| |||||||||||||||
| 1688 | "C:\Users\admin\Desktop\test\rpm-9-2-5-3700.exe" | C:\Users\admin\Desktop\test\rpm-9-2-5-3700.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 9.2.5.3700 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.refog.com/employee-computer-monitoring-software.html | C:\Program Files\Internet Explorer\iexplore.exe | rpm-9-2-5-3700.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1692 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\Desktop\test\rpm-9-2-5-3700.exe" | C:\Users\admin\Desktop\test\rpm-9-2-5-3700.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 9.2.5.3700 Modules
| |||||||||||||||
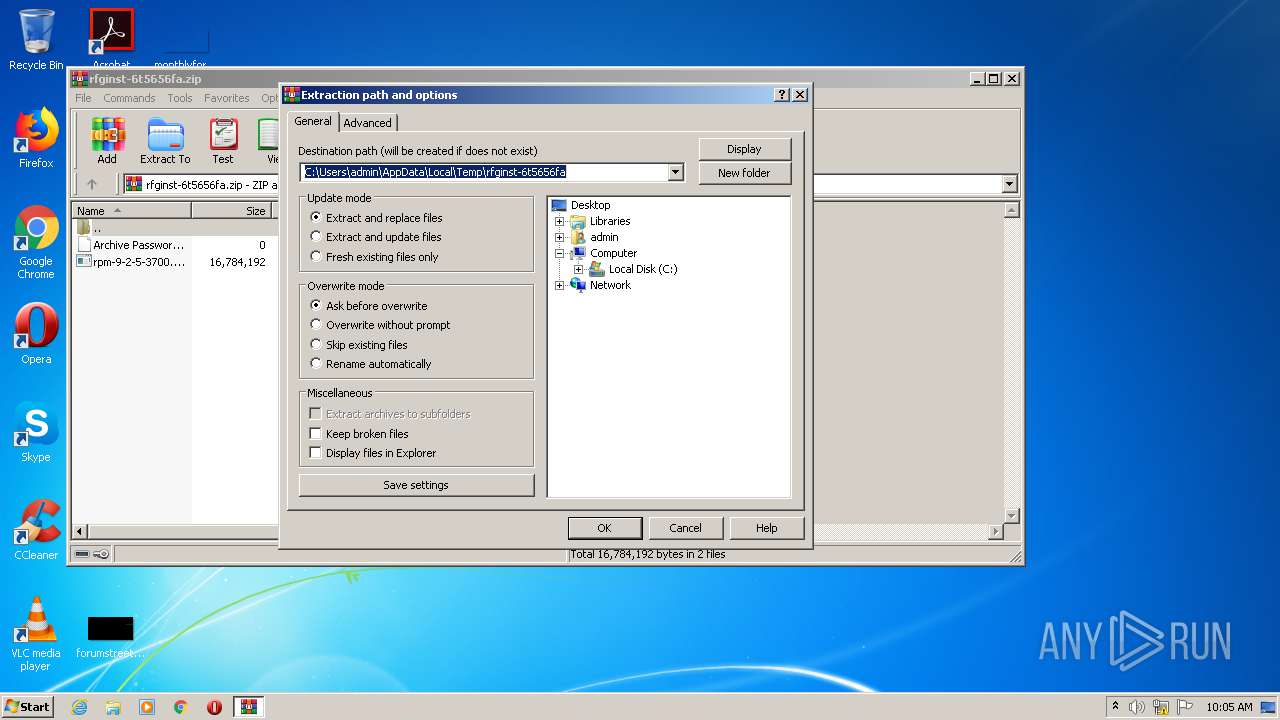
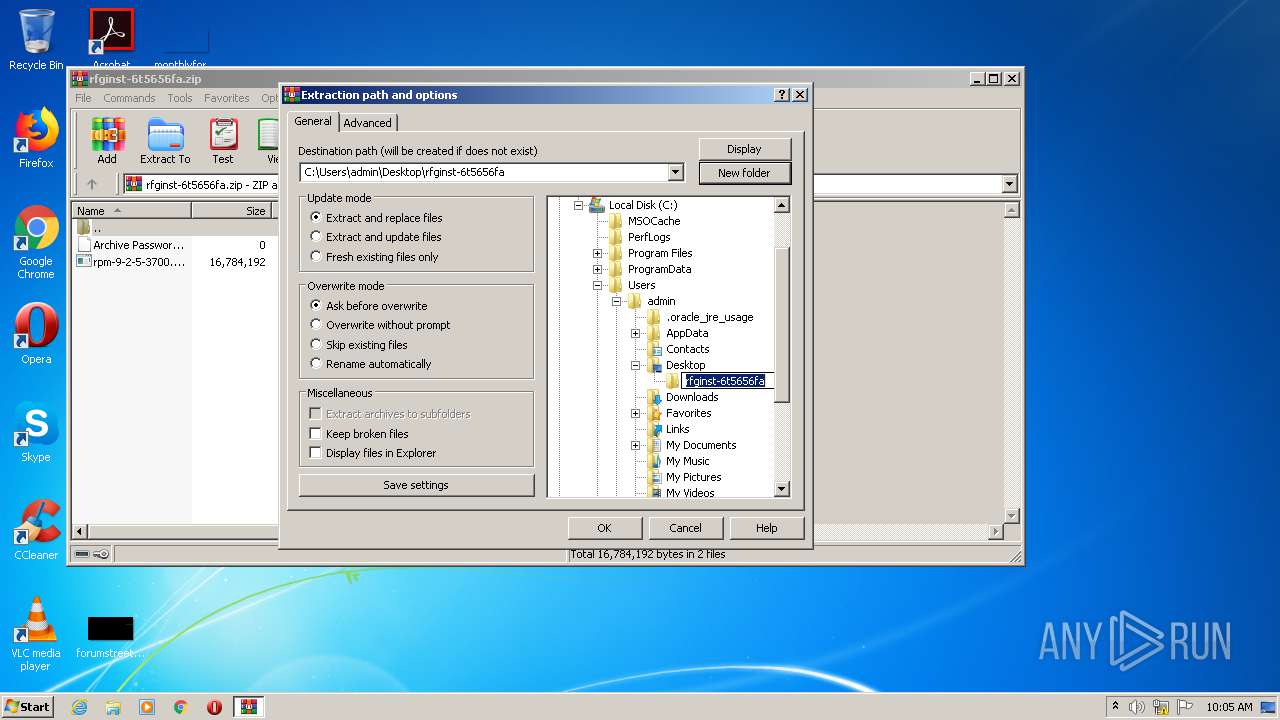
| 2792 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\rfginst-6t5656fa.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 4088 | "C:\Users\admin\Desktop\test\rpm-9-2-5-3700.exe" | C:\Users\admin\Desktop\test\rpm-9-2-5-3700.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 9.2.5.3700 Modules
| |||||||||||||||
Total events
1 110
Read events
1 004
Write events
105
Delete events
1
Modification events
| (PID) Process: | (2792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2792) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\rfginst-6t5656fa.zip | |||
| (PID) Process: | (2792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\test | |||
| (PID) Process: | (2792) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
1
Suspicious files
36
Text files
6
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2792 | WinRAR.exe | C:\Users\admin\Desktop\test | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab2232.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab2231.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar2234.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar2233.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab2245.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar2246.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab2256.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar2267.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab2E8D.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
31
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2160 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
2160 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
2160 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
2160 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
2160 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEHmYkrvsJDR4qtZ8x5mSSD8%3D | US | der | 471 b | whitelisted |
2160 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDQ45PuSdkrhAgAAAAAYdbq | US | der | 472 b | whitelisted |
2160 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCED%2B3i4nRcxO0AgAAAAB%2F1N4%3D | US | der | 471 b | whitelisted |
2160 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEG%2B%2F62CH3FZYCAAAAABh1oc%3D | US | der | 471 b | whitelisted |
2160 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCED%2B3i4nRcxO0AgAAAAB%2F1N4%3D | US | der | 471 b | whitelisted |
2160 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCED%2B3i4nRcxO0AgAAAAB%2F1N4%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2160 | iexplore.exe | 192.241.194.213:443 | www.refog.com | Digital Ocean, Inc. | US | unknown |
2160 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
2160 | iexplore.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2160 | iexplore.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1692 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2160 | iexplore.exe | 172.217.16.200:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2160 | iexplore.exe | 216.58.212.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2160 | iexplore.exe | 216.58.212.163:443 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2160 | iexplore.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2160 | iexplore.exe | 142.250.74.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.refog.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |