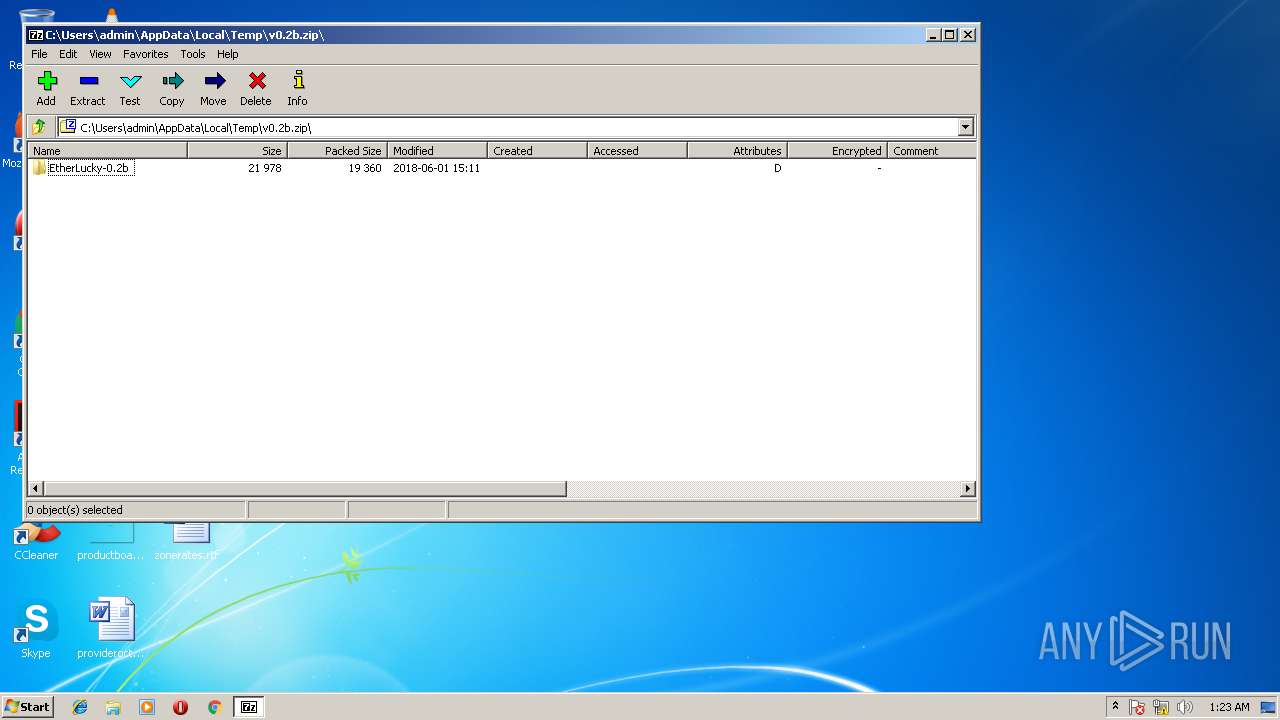
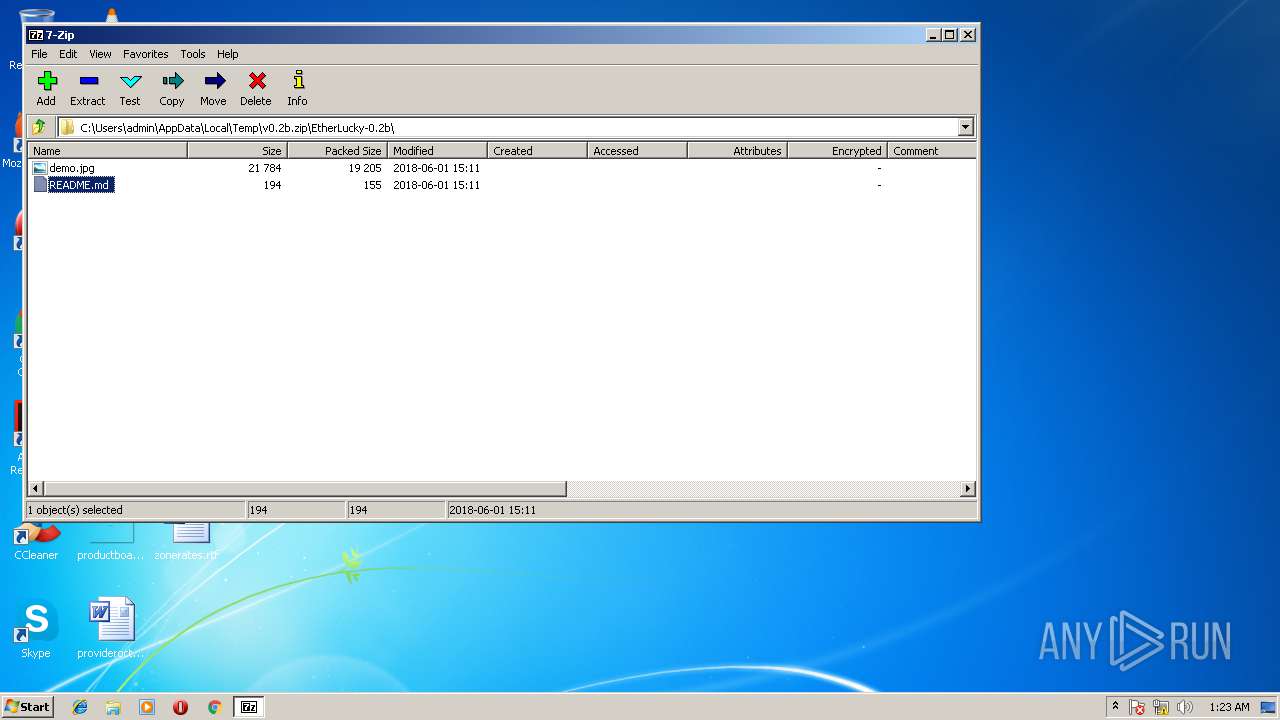
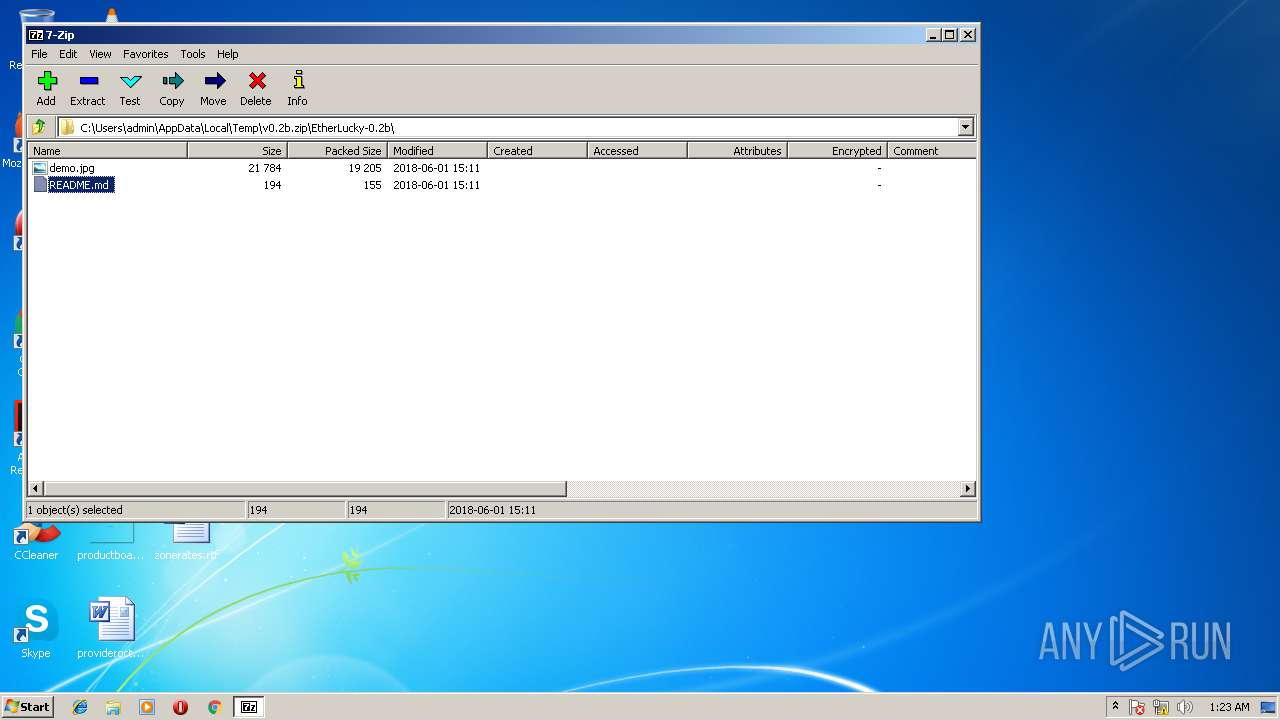
| download: | v0.2b.zip |
| Full analysis: | https://app.any.run/tasks/d1fa2534-6891-4691-b24a-bc7a76a84b99 |
| Verdict: | No threats detected |
| Analysis date: | June 16, 2018, 00:22:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | A348C96E7ED01D1B7E9FD0DB242A3C1A |
| SHA1: | D7A6F17BB358F6F51445EBB4662C957BDE7209FE |
| SHA256: | 97EDCA38CCA56A4487558515FD27411E01922FBE84E96E71FB24E1716690431E |
| SSDEEP: | 384:g086GJvn9UMy/ZKgyjHG2XVJpmH7P8okiXGcHSC161rA7KQ3uMgBE+zIx9uzu2qp:g086GhneBByjHG2FJU7P8okcH+cpDgBq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies the open verb of a shell class
- rundll32.exe (PID: 2492)
INFO
Dropped object may contain URL's
- 7zFM.exe (PID: 3220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:06:01 07:11:14 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | EtherLucky-0.2b/ |
Total processes
34
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
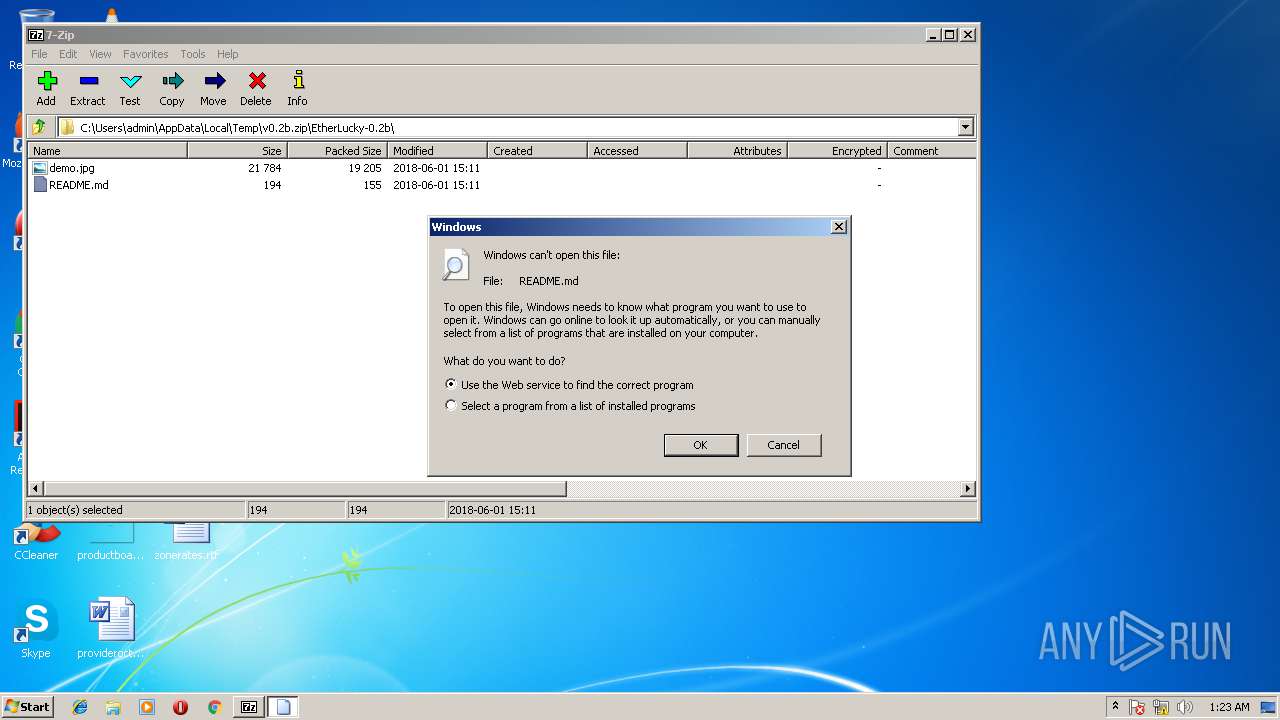
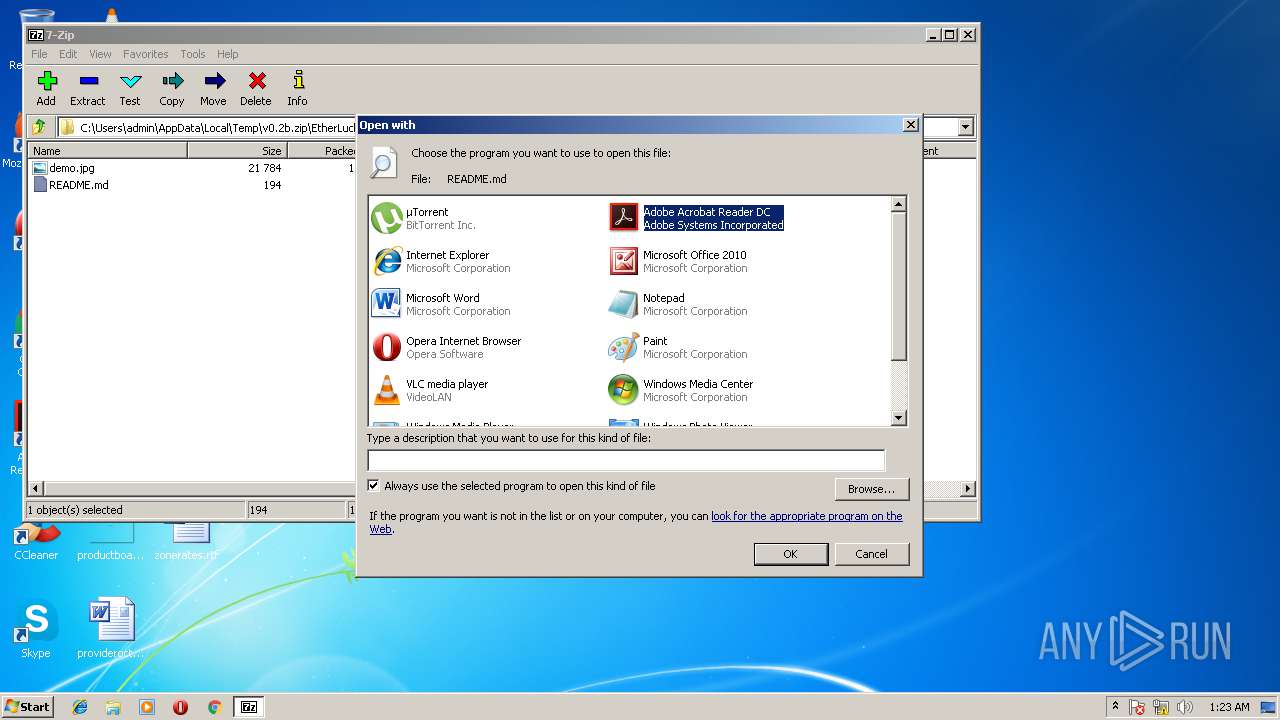
| 2492 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\7zO49C4E4B4\README.md | C:\Windows\system32\rundll32.exe | — | 7zFM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
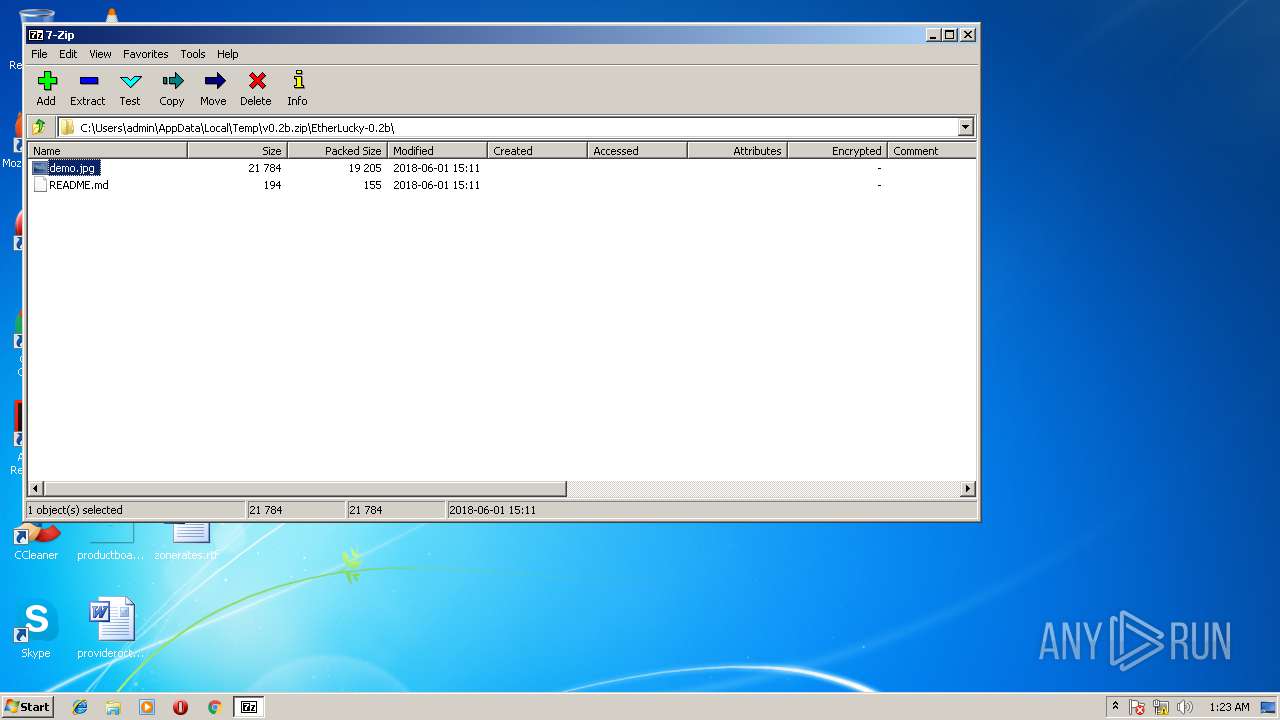
| 3220 | "C:\Program Files\7-Zip\7zFM.exe" "C:\Users\admin\AppData\Local\Temp\v0.2b.zip" | C:\Program Files\7-Zip\7zFM.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
| 3792 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
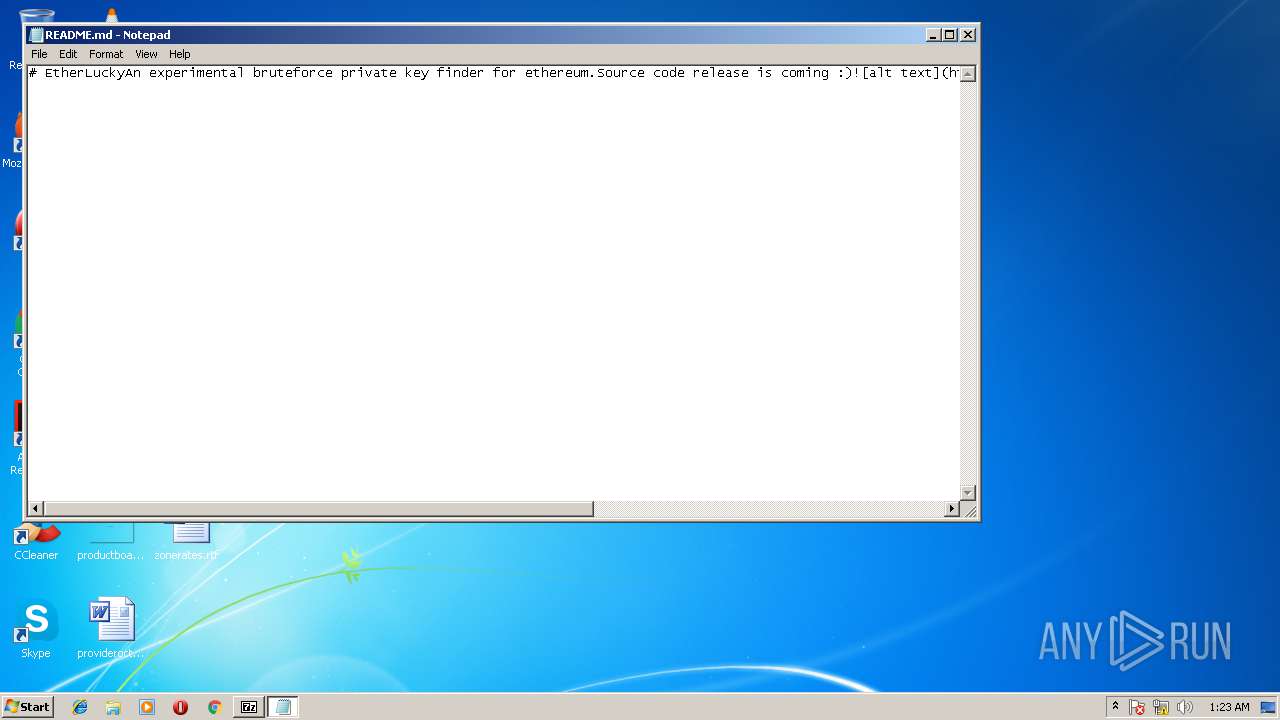
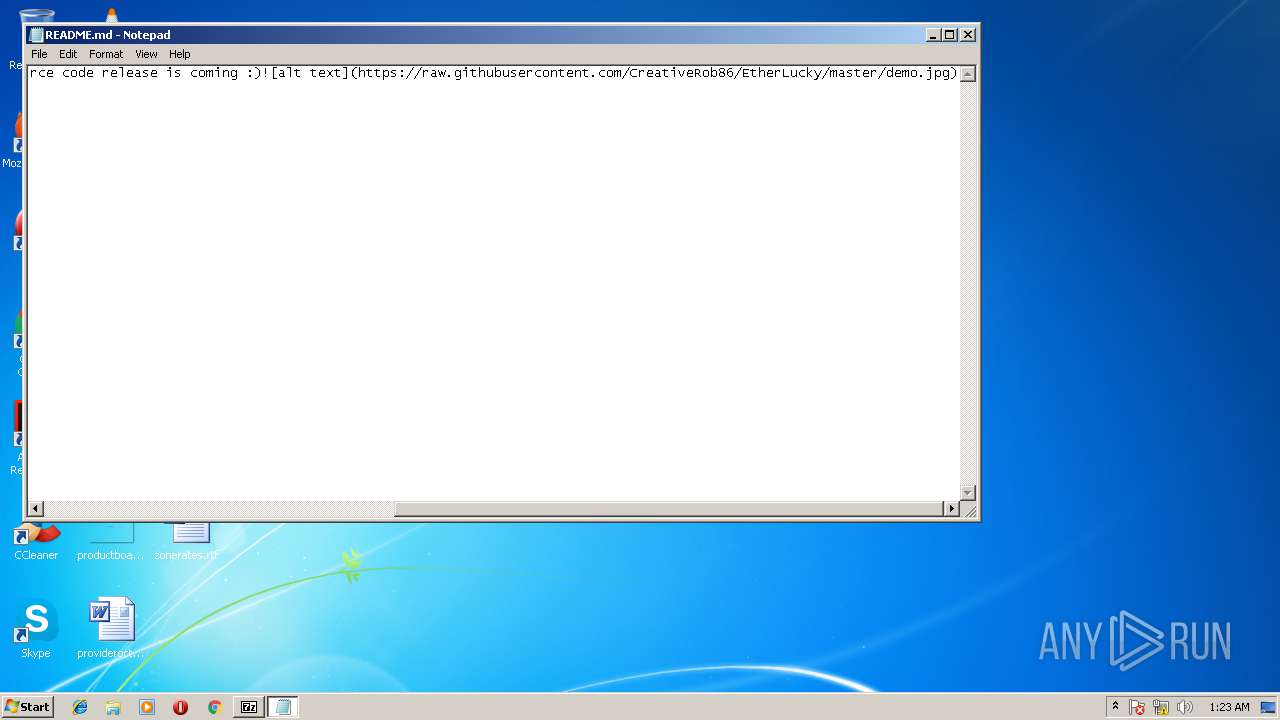
| 3984 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\7zO49C4E4B4\README.md | C:\Windows\system32\NOTEPAD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
881
Read events
806
Write events
75
Delete events
0
Modification events
| (PID) Process: | (3792) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (3220) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {00000122-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000002AB666440805D401 | |||
| (PID) Process: | (3220) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: 7zFM.exe | |||
| (PID) Process: | (3792) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (2492) rundll32.exe | Key: | HKEY_CLASSES_ROOT\md_auto_file |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (2492) rundll32.exe | Key: | HKEY_CLASSES_ROOT\.md |
| Operation: | write | Name: | |
Value: md_auto_file | |||
| (PID) Process: | (2492) rundll32.exe | Key: | HKEY_CLASSES_ROOT\md_auto_file\shell\edit\command |
| Operation: | write | Name: | |
Value: %SystemRoot%\system32\NOTEPAD.EXE %1 | |||
| (PID) Process: | (2492) rundll32.exe | Key: | HKEY_CLASSES_ROOT\md_auto_file\shell\open\command |
| Operation: | write | Name: | |
Value: %SystemRoot%\system32\NOTEPAD.EXE %1 | |||
| (PID) Process: | (2492) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.md\OpenWithList |
| Operation: | write | Name: | a |
Value: NOTEPAD.EXE | |||
| (PID) Process: | (2492) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.md\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
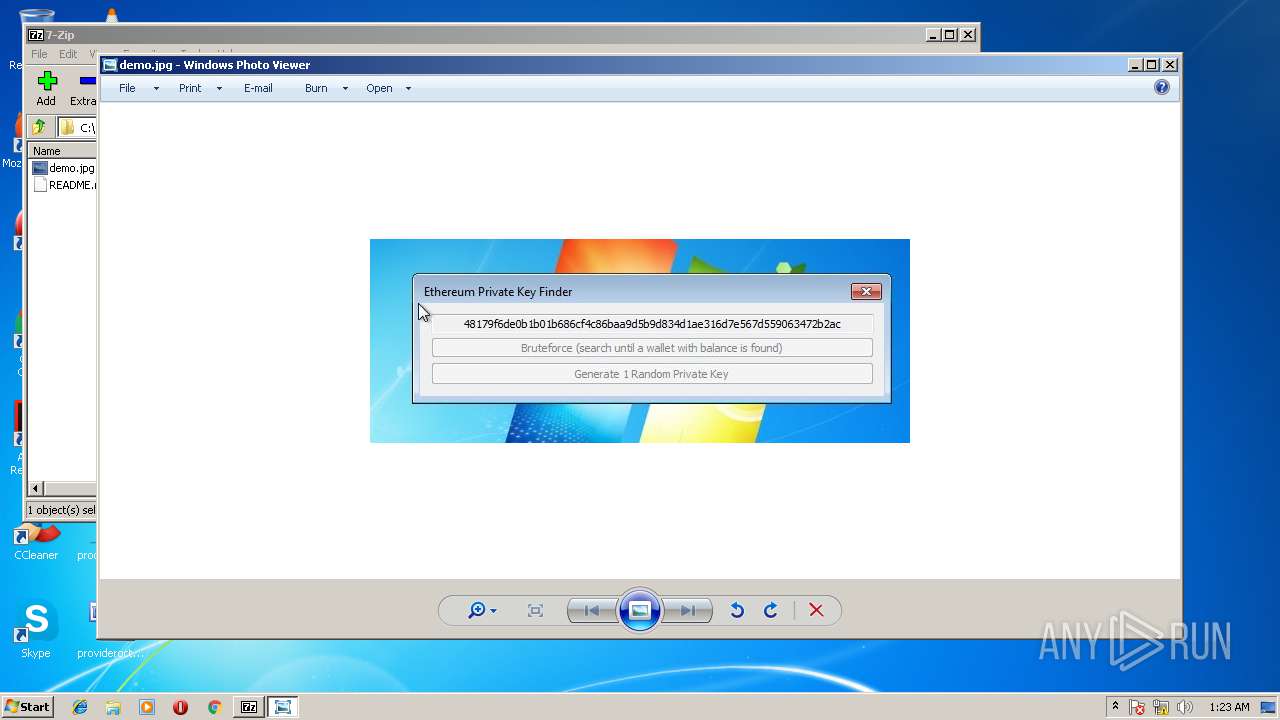
| 3220 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zO49C43644\demo.jpg | image | |
MD5:— | SHA256:— | |||
| 3220 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zO49C4E4B4\README.md | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report