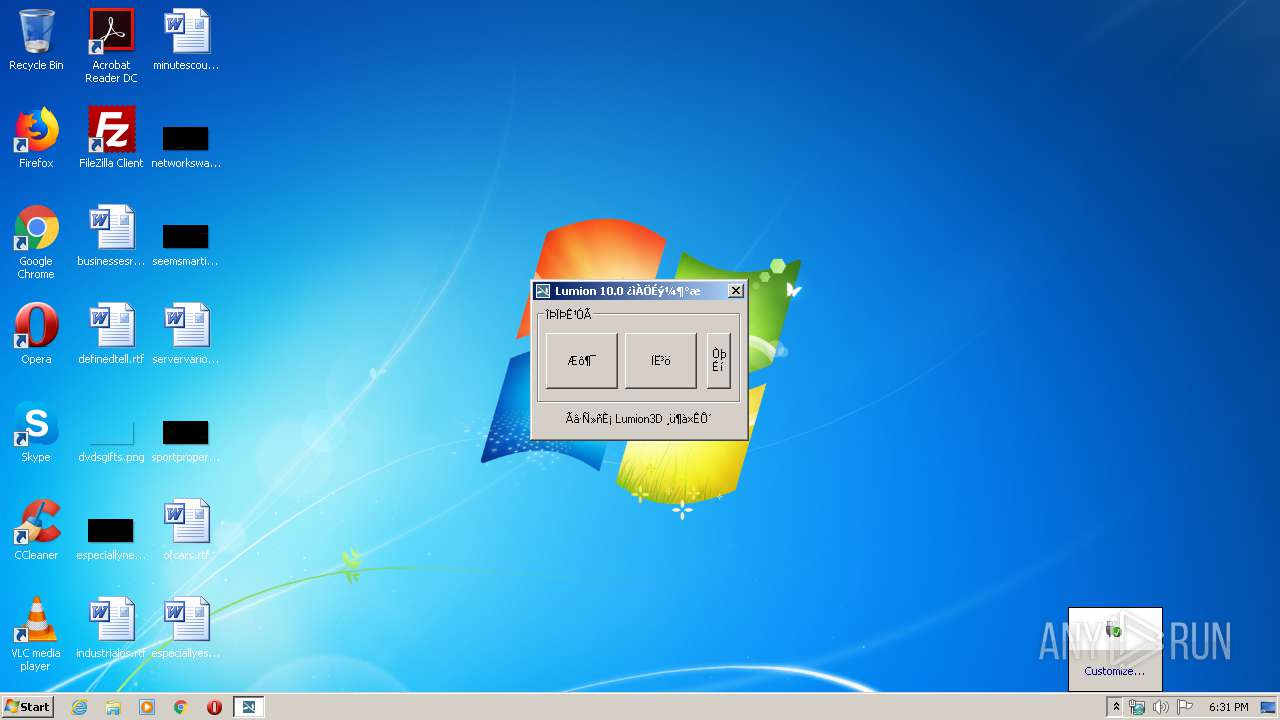
| File name: | Lumion10.exe |
| Full analysis: | https://app.any.run/tasks/38f23afb-b830-45f5-b635-823bf422e2de |
| Verdict: | No threats detected |
| Analysis date: | March 22, 2020, 18:30:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 606A70172FAE52F00A040A1D78D4B7AD |
| SHA1: | 2E963B3CABB85F0BB6015C17397E88ACED1F68A2 |
| SHA256: | 97E63AF43423B7487B75494C0BD59DC0606056D5B408DA8A6A88DBB5EDCEDA50 |
| SSDEEP: | 98304:IC1IzpW+KJnZwQecEWDpSdwROomdQ6VXu:I7bKJWQecEKSdjomdQ69u |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- Lumion10.exe (PID: 3696)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (16.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (12.7) |
| .exe | | | Win64 Executable (generic) (11.2) |
| .scr | | | Windows screen saver (5.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:01 08:44:12+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 569344 |
| InitializedDataSize: | 3473408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6c236 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
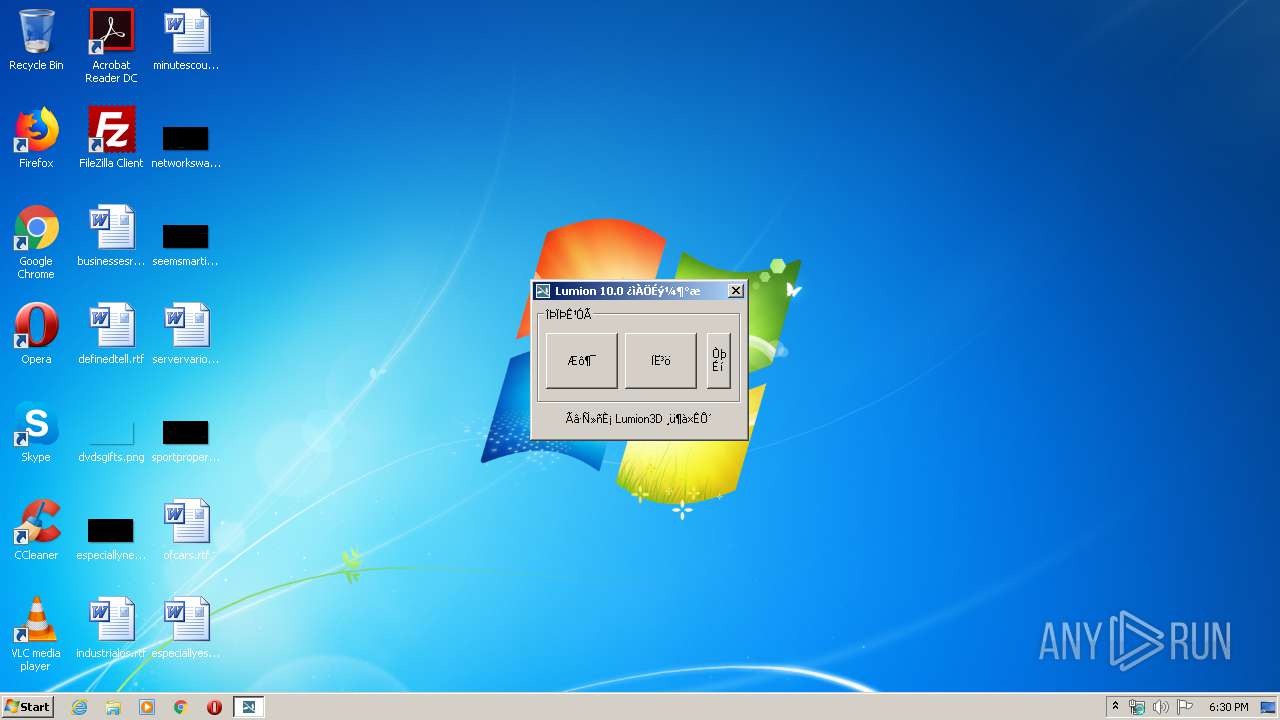
| FileDescription: | 易语言程序 |
| ProductName: | Lumion 10快乐升级版 |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | 我是一只鱼 |
| LegalCopyright: | Lumion 10快乐升级版本仅限学习使用,商业用途请使用正版。 |
| Comments: | 本程序使用易语言编写(http://www.eyuyan.com) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Dec-2019 07:44:12 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| FileDescription: | 易语言程序 |
| ProductName: | Lumion 10快乐升级版 |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | 我是一只鱼 |
| LegalCopyright: | Lumion 10快乐升级版本仅限学习使用,商业用途请使用正版。 |
| Comments: | 本程序使用易语言编写(http://www.eyuyan.com) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 01-Dec-2019 07:44:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008ABBA | 0x0008B000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56575 |
.rdata | 0x0008C000 | 0x003174EA | 0x00318000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.1652 |
.data | 0x003A4000 | 0x00042A6A | 0x00018000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.37662 |
.rsrc | 0x003E7000 | 0x0001FC4C | 0x00020000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.11467 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.2458 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.21366 | 1736 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 6.09976 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.40564 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 2.63367 | 19496 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 2.16238 | 74792 | Latin 1 / Western European | UNKNOWN | RT_ICON |
127 | 1.4183 | 12 | Latin 1 / Western European | Chinese - PRC | RT_MENU |
150 | 3.06278 | 152 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
Imports
ADVAPI32.dll |
AVIFIL32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVFW32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WINMM.dll |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3696 | "C:\Users\admin\AppData\Local\Temp\Lumion10.exe" | C:\Users\admin\AppData\Local\Temp\Lumion10.exe | explorer.exe | ||||||||||||
User: admin Company: 我是一只鱼 Integrity Level: MEDIUM Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
4
Read events
4
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
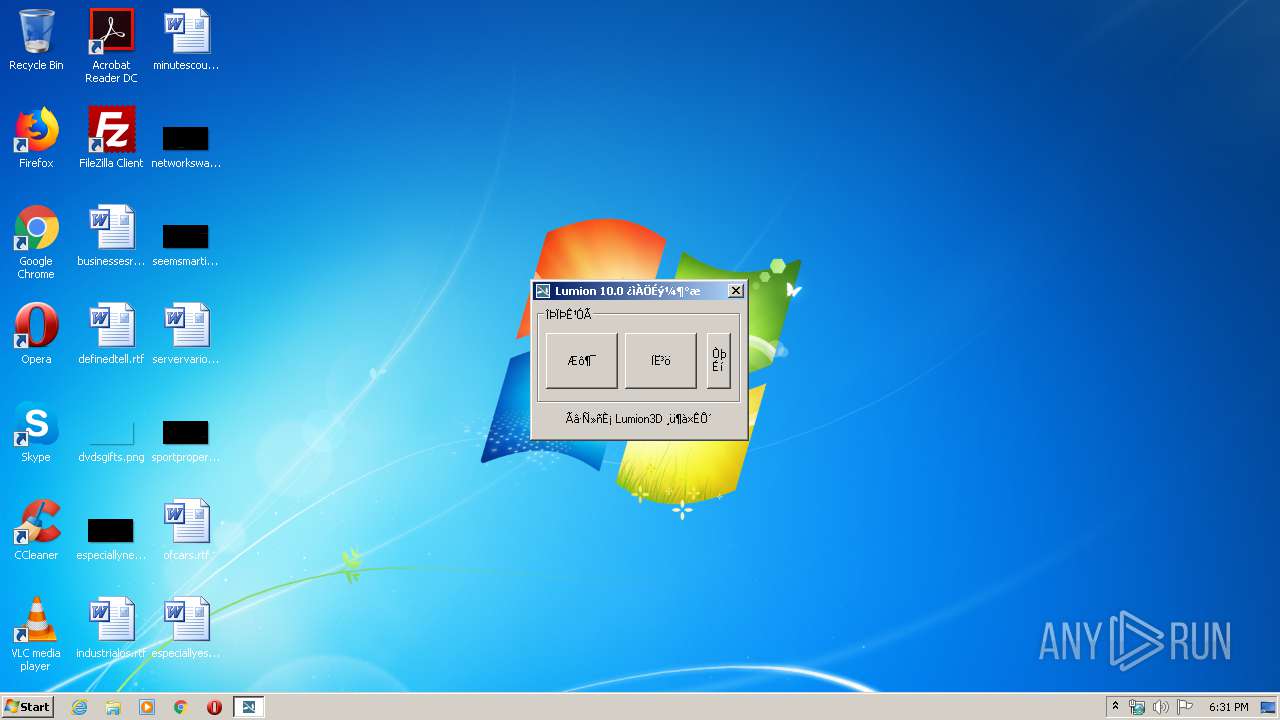
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3696 | Lumion10.exe | C:\Users\admin\AppData\Local\Temp\LumCore.dll | executable | |
MD5:— | SHA256:— | |||
| 3696 | Lumion10.exe | C:\Users\admin\AppData\Local\Temp\HighPoly.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report