analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
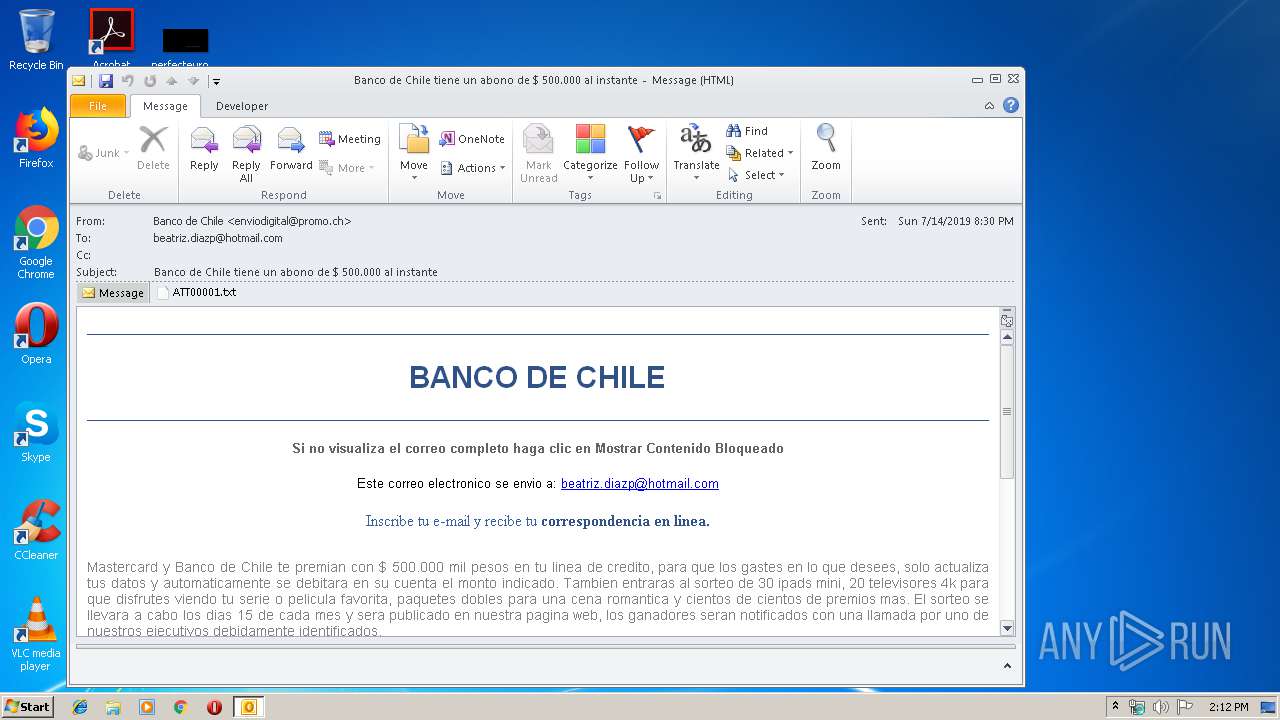
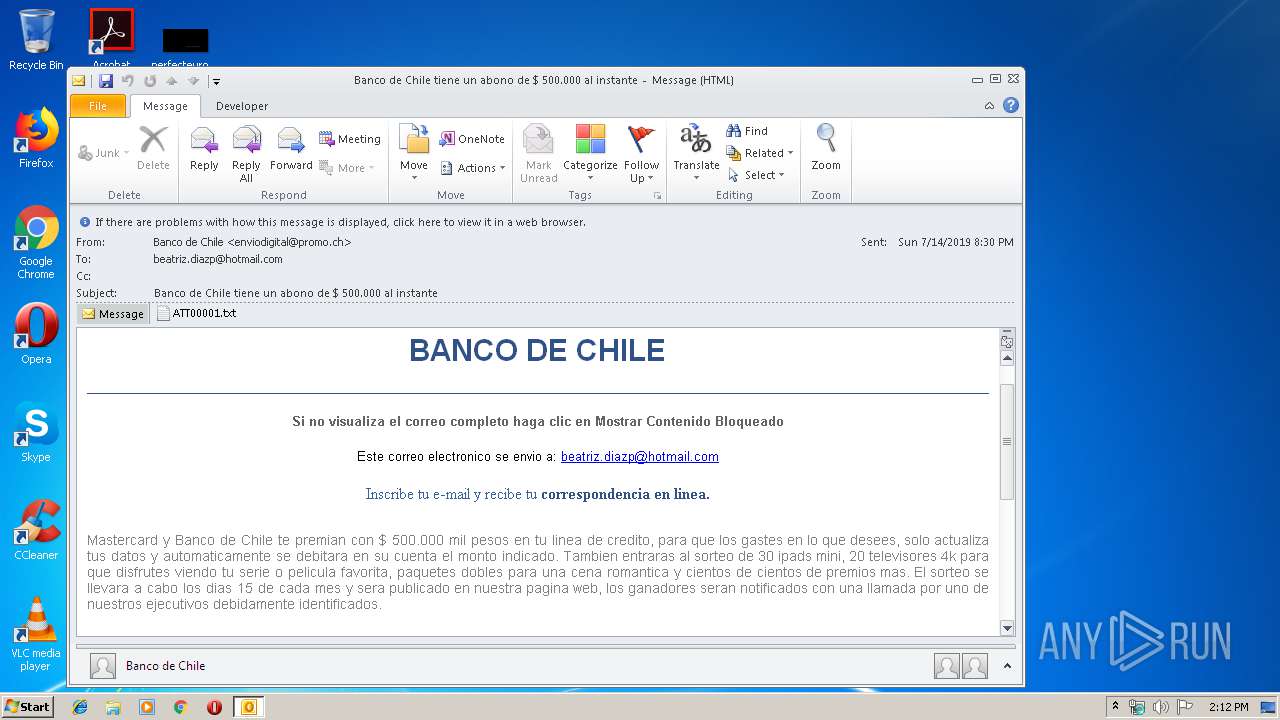
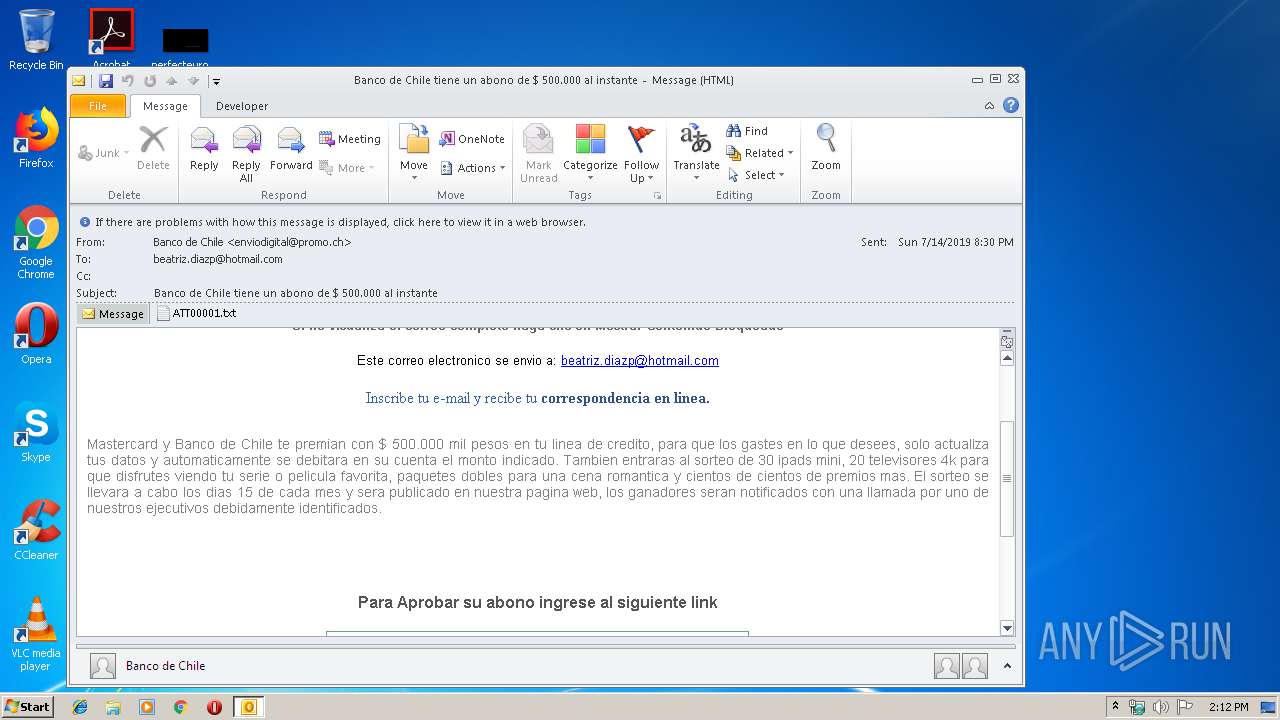
| File name: | Banco de Chile tiene un abono de $ 500.000 al instante.msg |
| Full analysis: | https://app.any.run/tasks/c74de45f-2208-4c20-a3c3-20f2678b4400 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 13:12:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 46C63DEC4B0B4F408D1042725A81EB1E |
| SHA1: | 3B4FB32DC6F7E31289087D2BF0F18C4C9A304771 |
| SHA256: | 97DFFC3771B0F9746FA23E0181626089BAC67EFA147EB8D333FBCFC749682C78 |
| SSDEEP: | 768:IMC2l9ZFqh/9lpDplrqU92B2UkGg6XzQPyjojdcEf6uHaioMSv8zyuq:JZo/DrFDUd0PyjojioZSkzy |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3500)
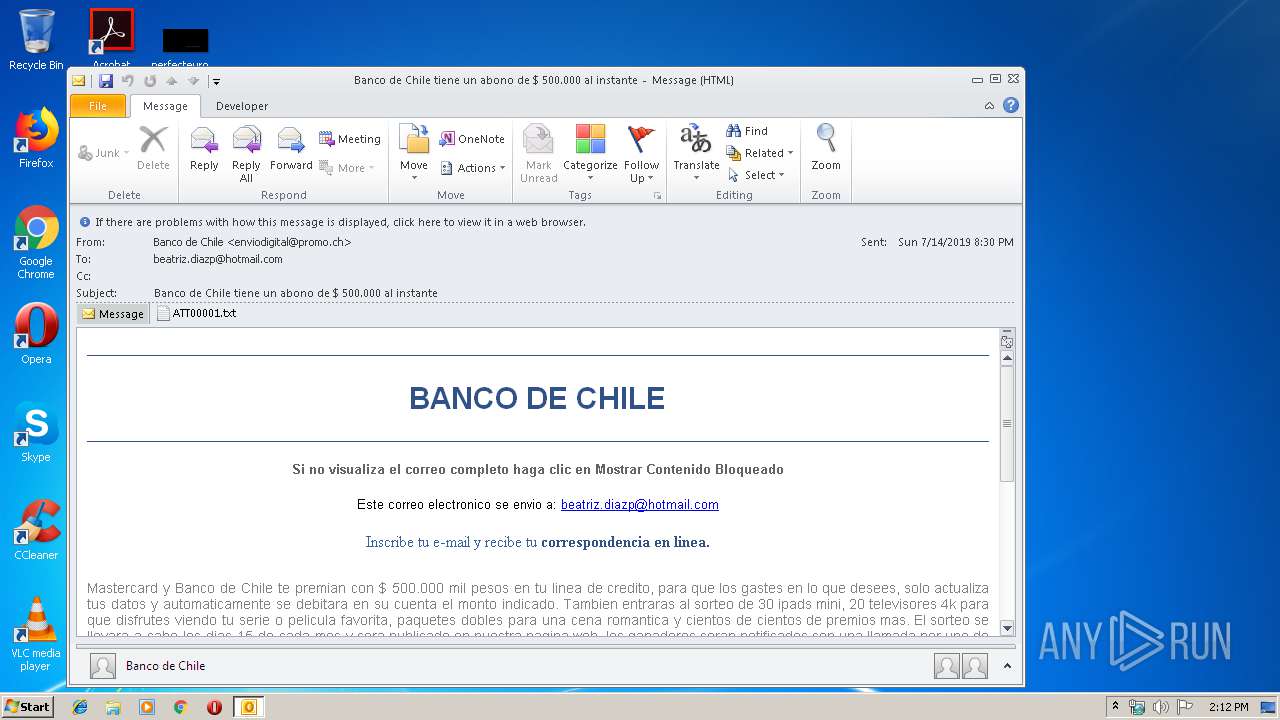
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3500)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3500)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3500)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3500)
Application launched itself
- iexplore.exe (PID: 3776)
Creates files in the user directory
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 3776)
Reads internet explorer settings
- iexplore.exe (PID: 2460)
Changes internet zones settings
- iexplore.exe (PID: 3776)
Reads Internet Cache Settings
- iexplore.exe (PID: 2460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3500 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Banco de Chile tiene un abono de $ 500.000 al instante.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 14.0.6025.1000 | ||||
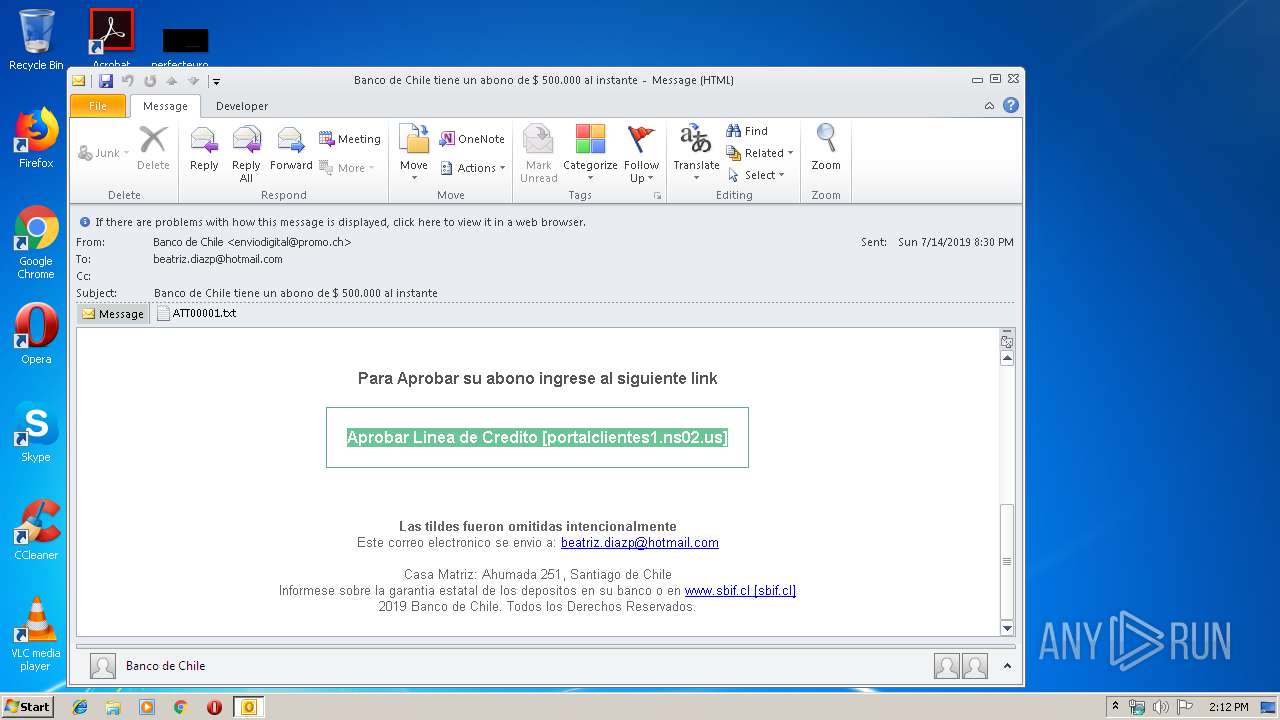
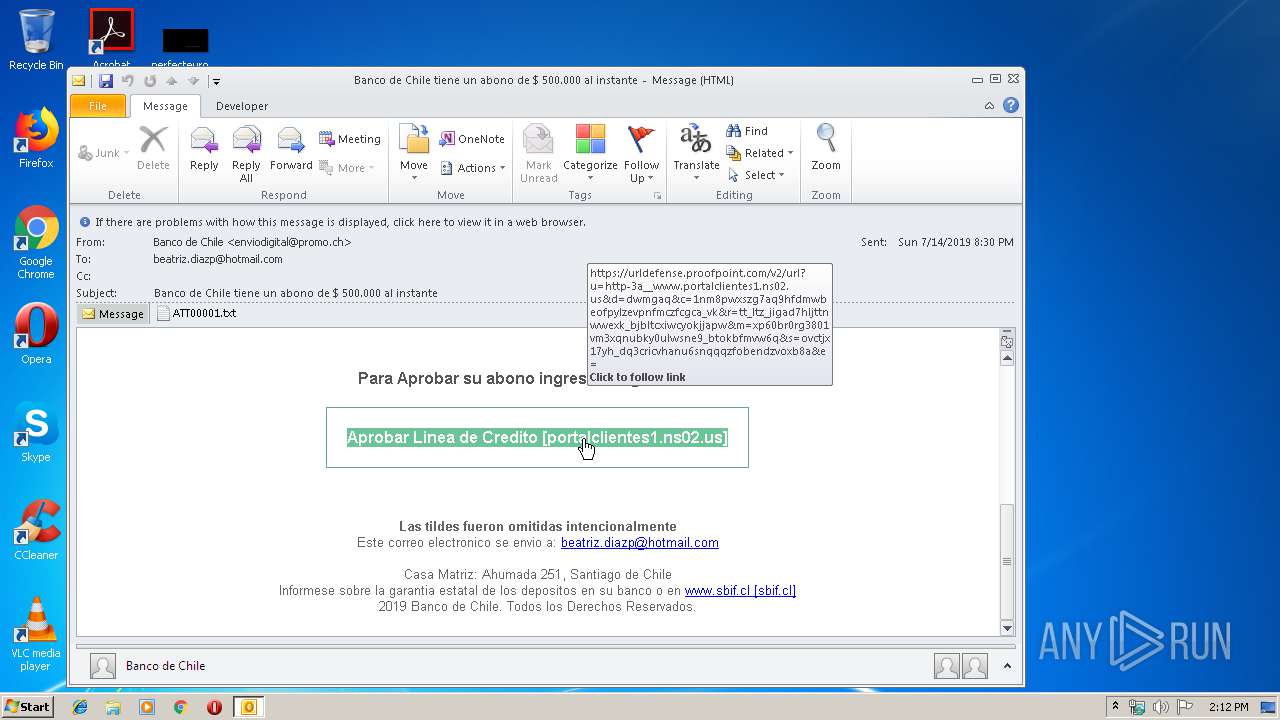
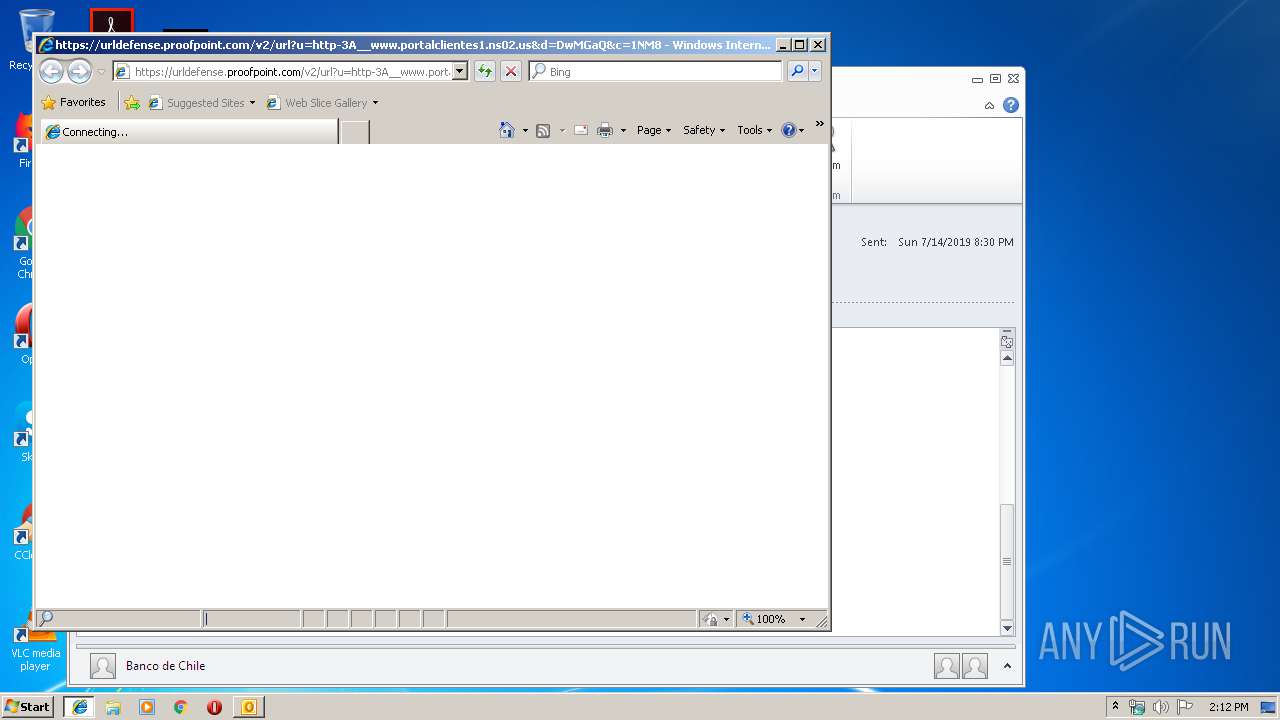
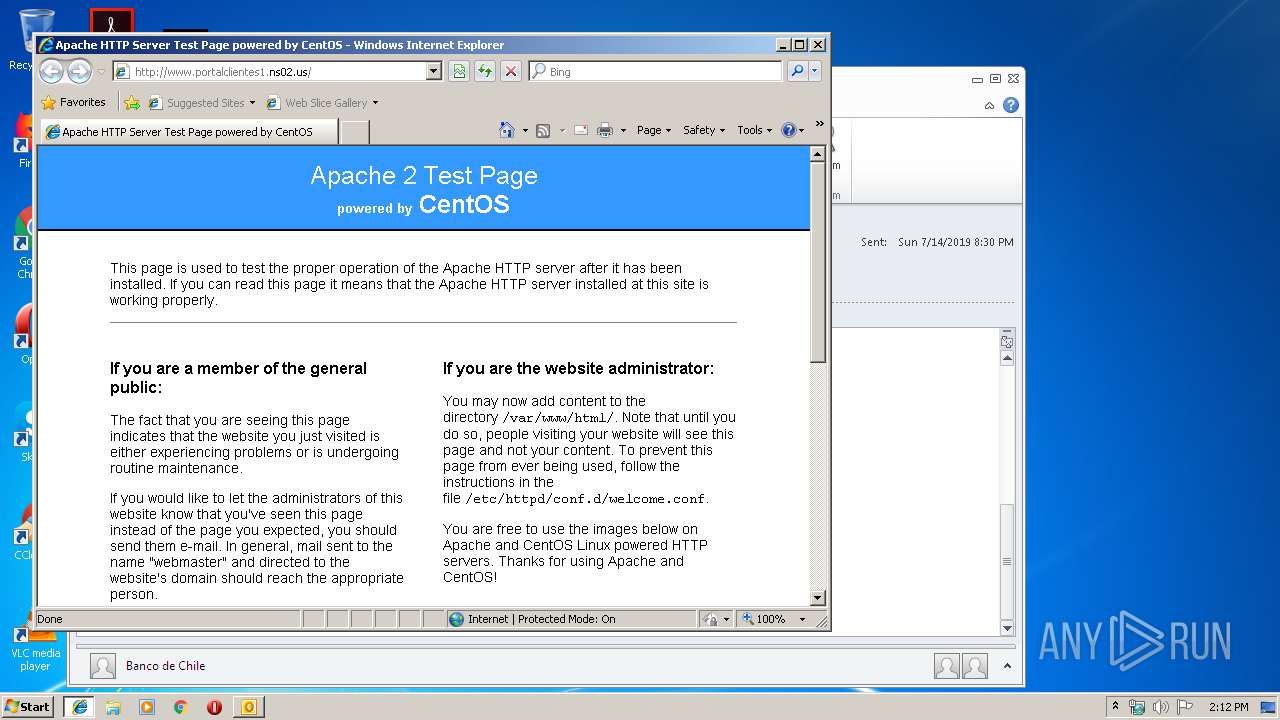
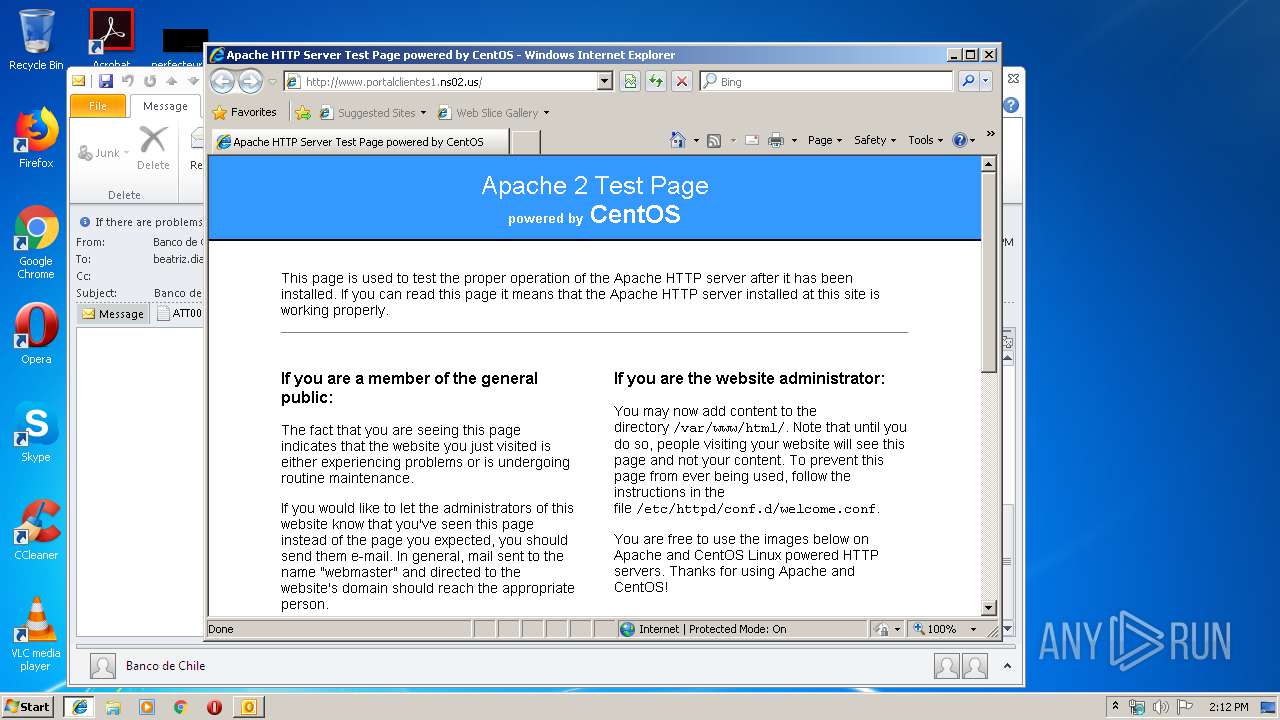
| 3776 | "C:\Program Files\Internet Explorer\iexplore.exe" https://urldefense.proofpoint.com/v2/url?u=http-3A__www.portalclientes1.ns02.us&d=DwMGaQ&c=1NM8PwXszG7AQ9HfdmWbEOfpyLzEVPnFMcZFCGca_Vk&r=tt_ltz_JigAD7HLJTTNWweXk_BJBlTcXiWcyOKjjaPw&m=xP60BR0rg3801vm3XqNubKy0ulWsNe9_bTokBfMVW6Q&s=ovCTJX17YH_DQ3cricVhaNu6sNQqQZFObeNDZvoxB8A&e= | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
| 2460 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3776 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
Total events
1 580
Read events
1 120
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
35
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3500 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE800.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3776 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3500 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:EAE890A1F64E64742C3CDF1099F96516 | SHA256:94D843E96B7C2D15AF76491220720A7F97E5316472EFE559BEF7837A9113DF41 | |||
| 3776 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3500 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:04D692DD4A2C448442E109902AC62D62 | SHA256:1CC56B180D11884EEC0A0F09CBC208C7E5AF6567E91DC4E43FBC7E39A98778E5 | |||
| 3500 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_425F8F903B7DDF468E61CDB12E310742.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 3500 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_E08576A38BFFC841B5ADF6EA9EDB764E.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 3500 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TCPrefs_2_F6DBAF331D22C94286B3165A9FE04763.dat | xml | |
MD5:F194B1FA12F9B6F46A47391FAE8BEEC2 | SHA256:FCD8D7E030BE6EA7588E5C6CB568E3F1BDFC263942074B693942A27DF9521A74 | |||
| 3776 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Feeds Cache\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3500 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_03CE07B77CDA8E4F9E1D7AE54B365655.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2460 | iexplore.exe | GET | — | 104.238.220.34:80 | http://www.portalclientes1.ns02.us/icons/poweredby.png | US | — | — | suspicious |
2460 | iexplore.exe | GET | 200 | 104.238.220.34:80 | http://www.portalclientes1.ns02.us/icons/apache_pb.gif | US | image | 2.27 Kb | suspicious |
3776 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2460 | iexplore.exe | GET | 403 | 104.238.220.34:80 | http://www.portalclientes1.ns02.us/ | US | html | 4.92 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3776 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3500 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2460 | iexplore.exe | 104.238.220.34:80 | www.portalclientes1.ns02.us | Versaweb, LLC | US | malicious |
2460 | iexplore.exe | 67.231.146.66:443 | urldefense.proofpoint.com | Proofpoint, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
urldefense.proofpoint.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.portalclientes1.ns02.us |
| suspicious |
Threats
3 ETPRO signatures available at the full report