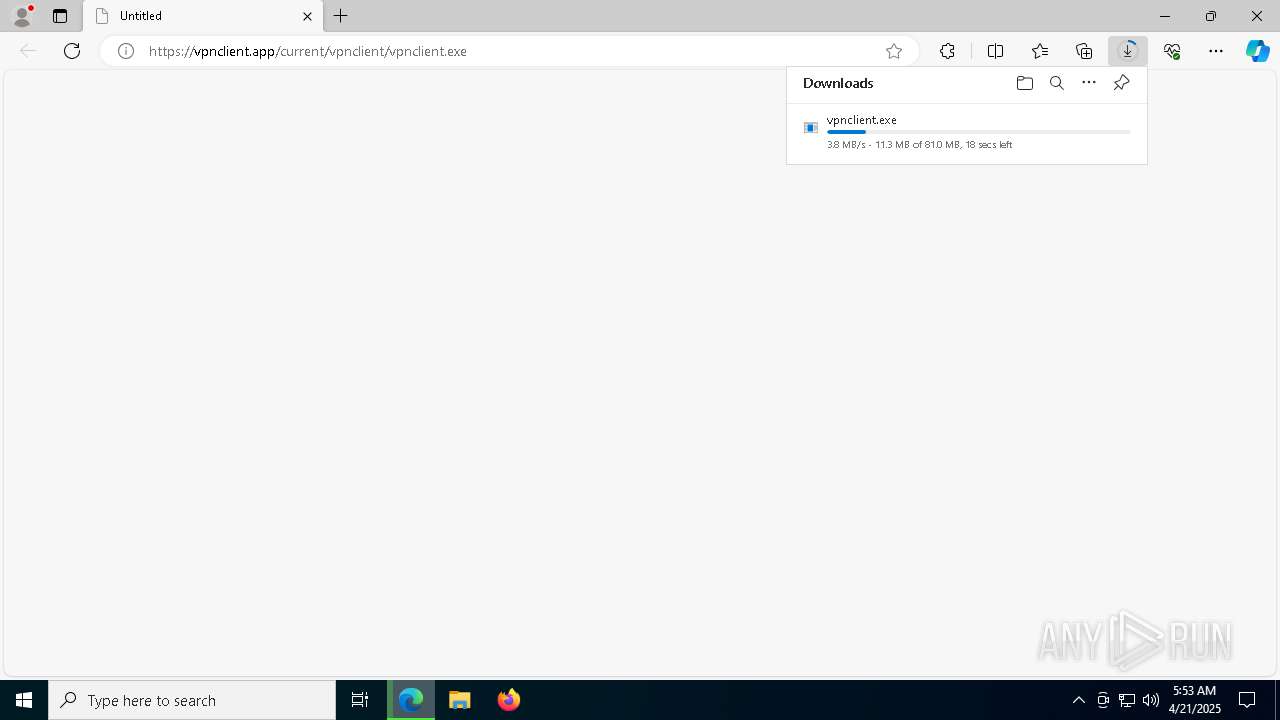
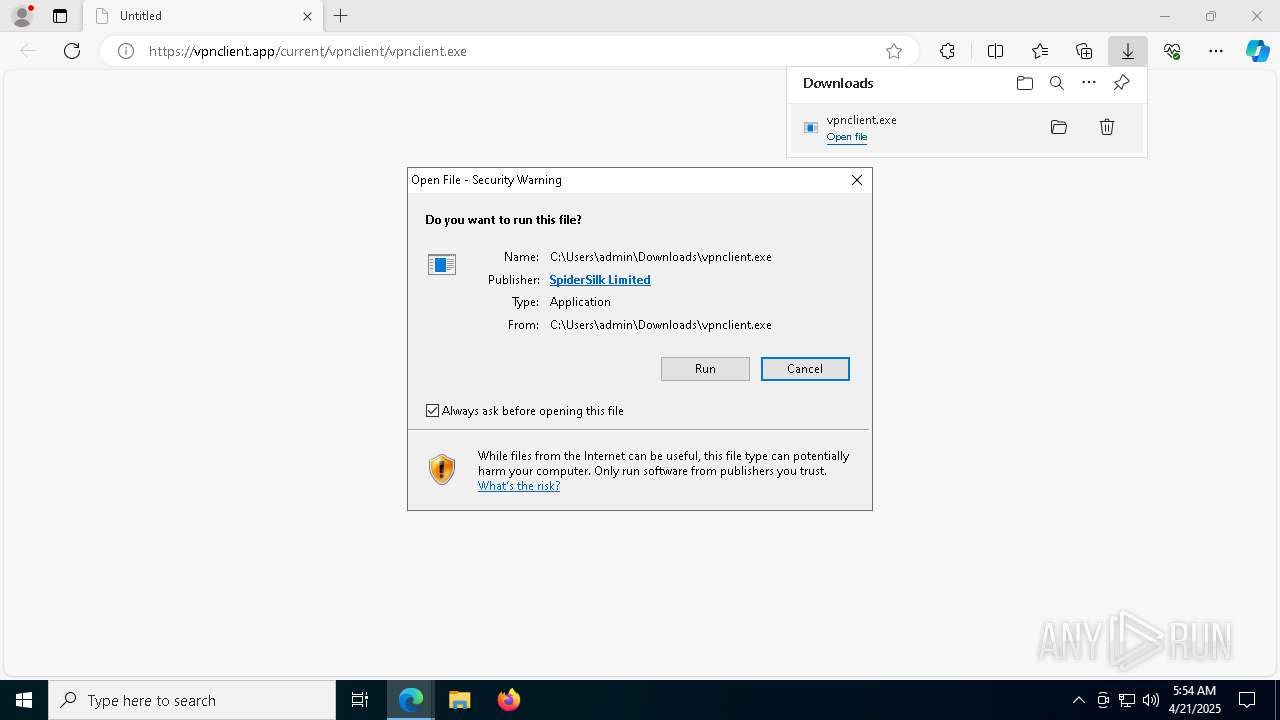
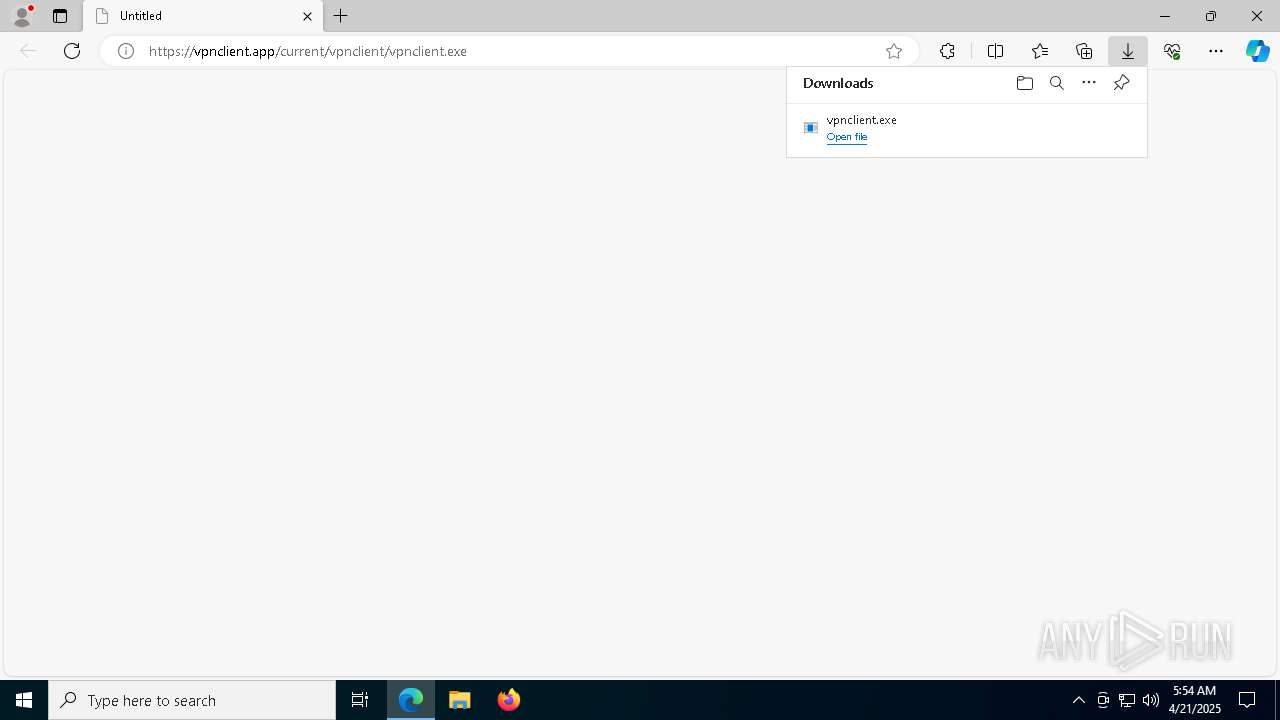
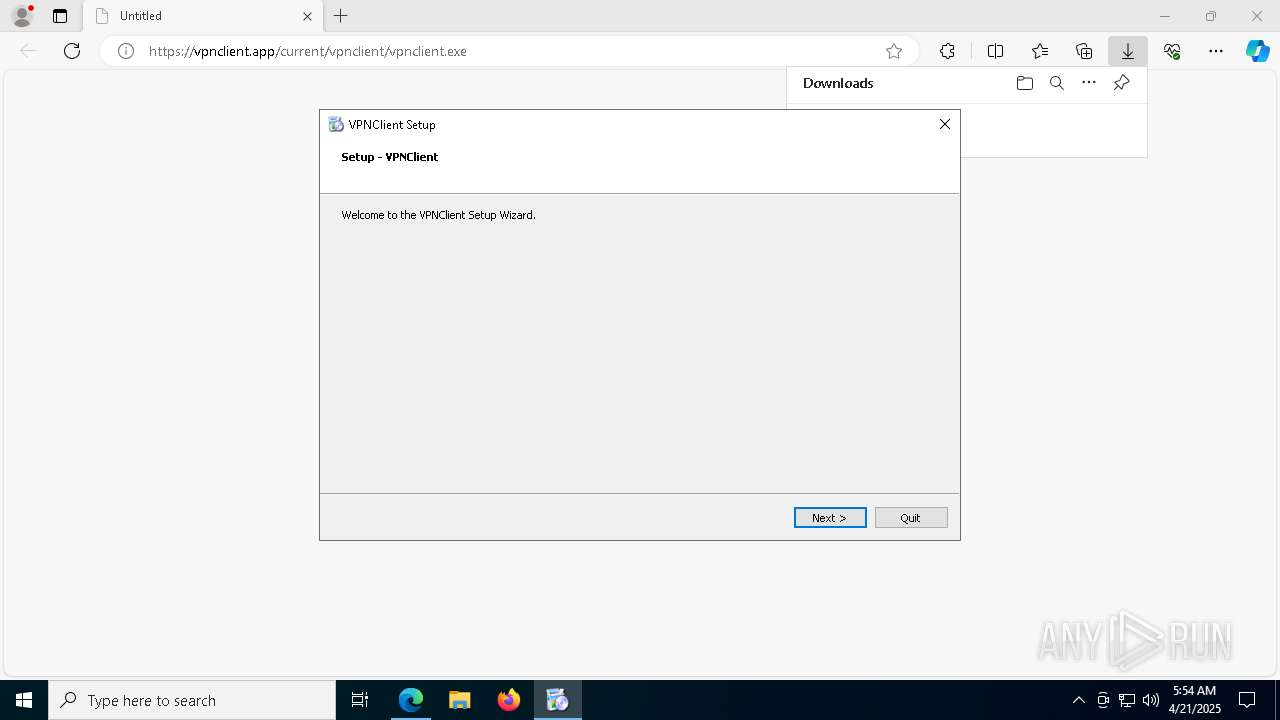
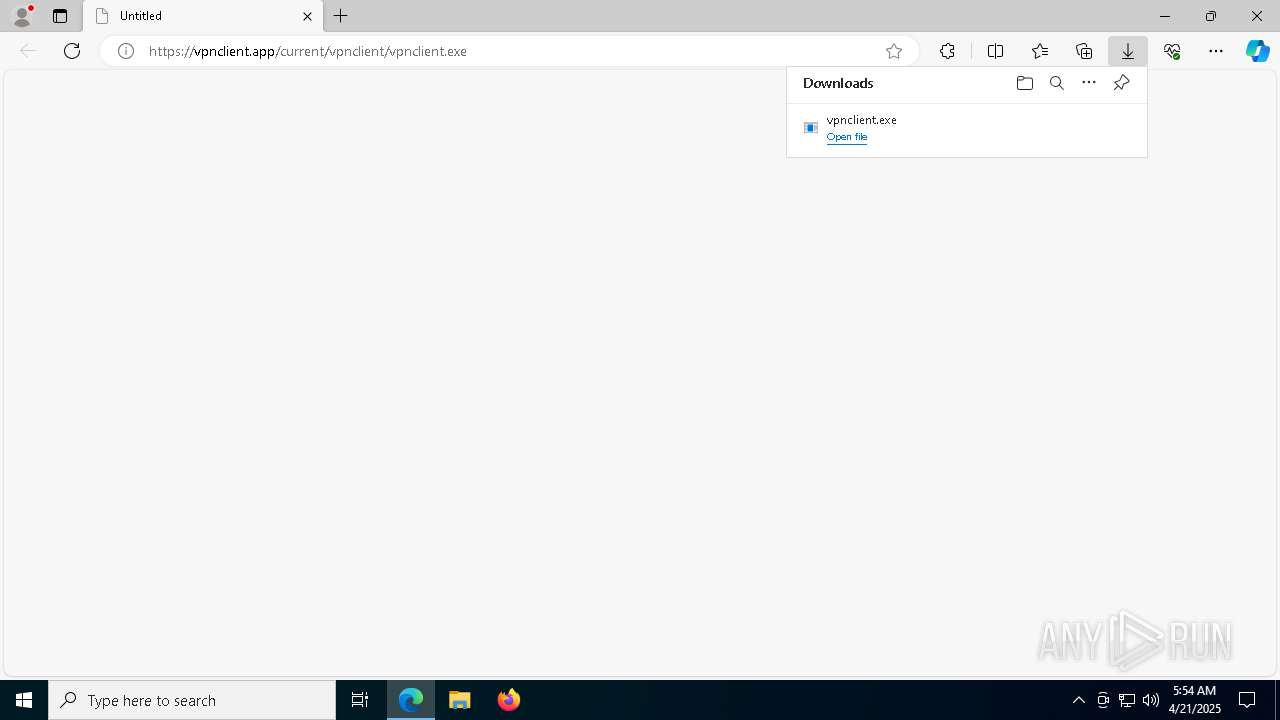
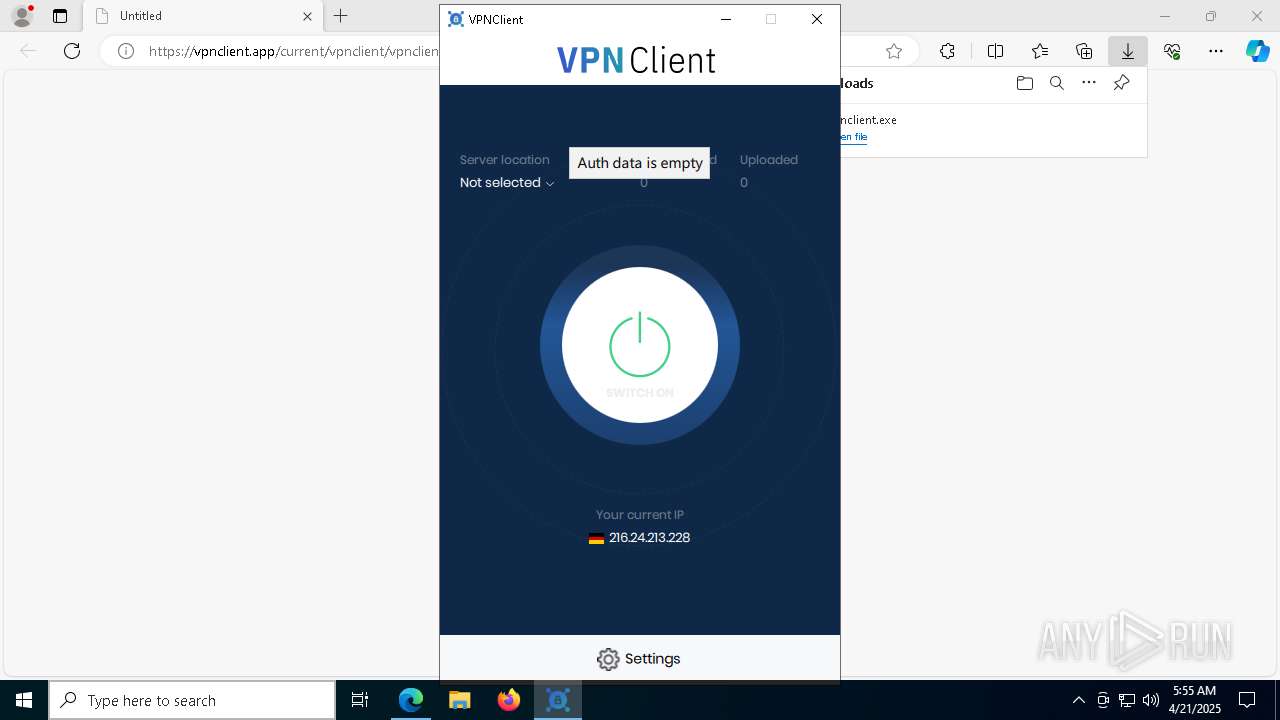
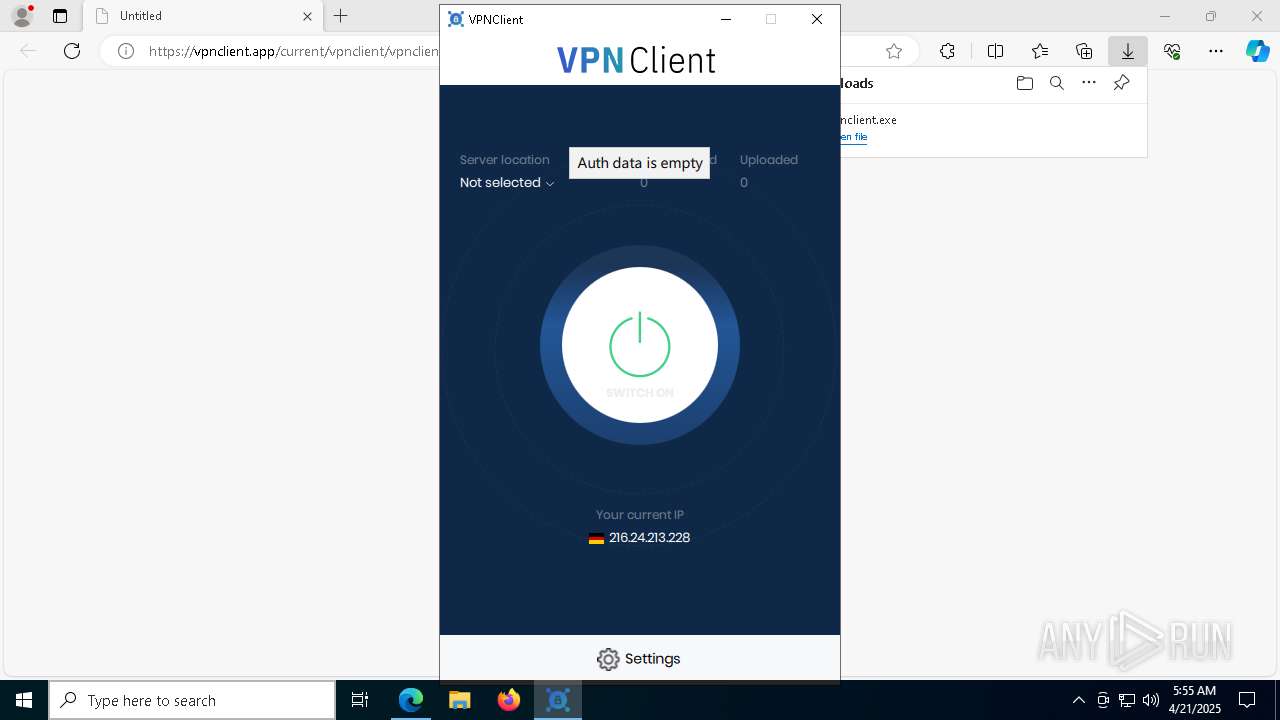
| URL: | https://vpnclient.app/current/vpnclient/vpnclient.exe |
| Full analysis: | https://app.any.run/tasks/d81d7672-2876-4419-aca9-40bc25d168be |
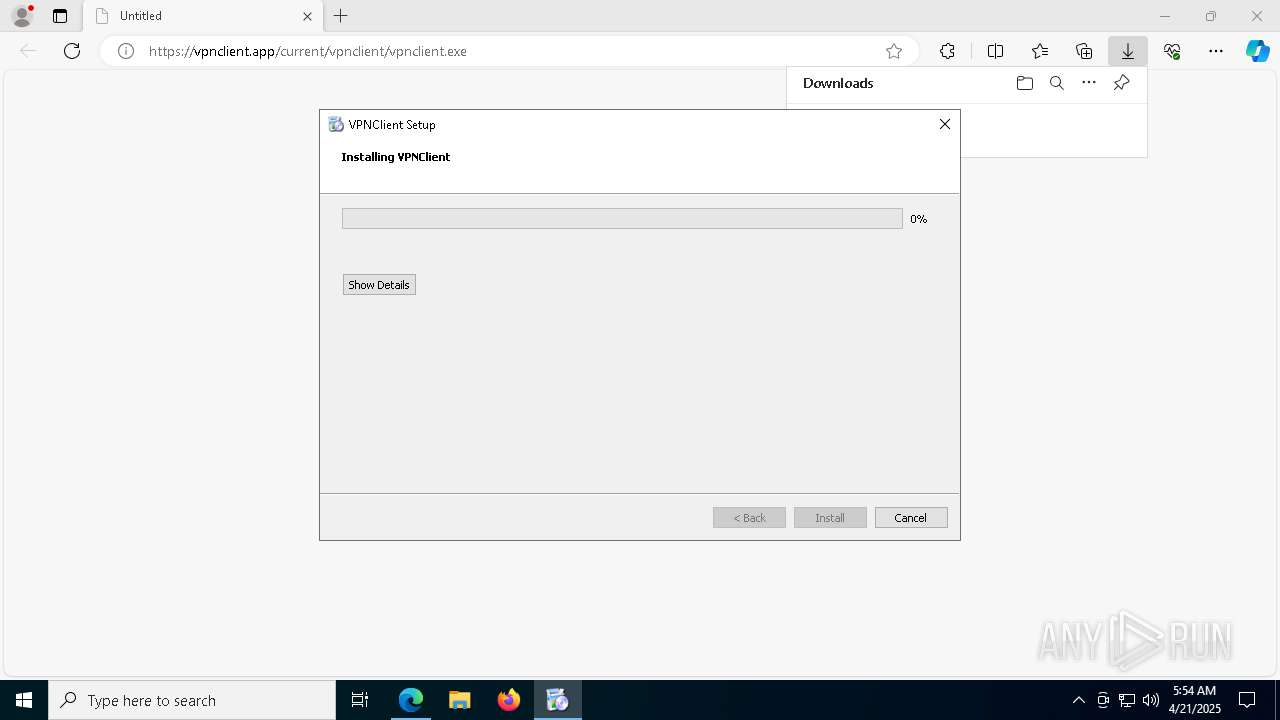
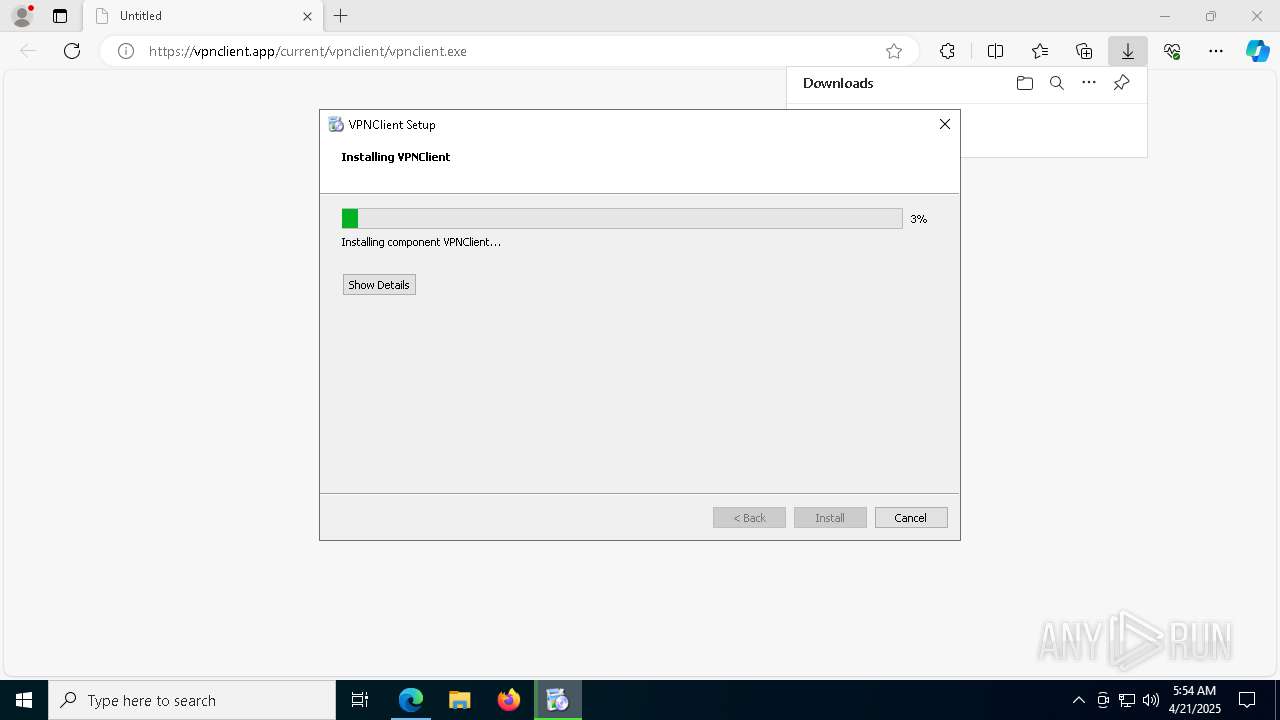
| Verdict: | Malicious activity |
| Analysis date: | April 21, 2025, 05:53:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | AF4E3ACAFBED561B314E59B025AAFE68 |
| SHA1: | 5EDFD7D23A4FCE4B817C357C3DD79ADCF415B66D |
| SHA256: | 97D404001CF69BAED58743EE1FA8C4113614E3ABFF190A15DF0D1D7264A28DF4 |
| SSDEEP: | 3:N8OfAIGJzWGJzJn:21IGMG/n |
MALICIOUS
Starts NET.EXE for service management
- vpnclient.exe (PID: 8616)
- net.exe (PID: 8244)
Deletes a file (SCRIPT)
- cscript.exe (PID: 720)
- cscript.exe (PID: 2108)
SUSPICIOUS
Application launched itself
- vpnclient.exe (PID: 9188)
Executable content was dropped or overwritten
- vpnclient.exe (PID: 8616)
- tapinstall.exe (PID: 7772)
- drvinst.exe (PID: 8100)
- drvinst.exe (PID: 728)
- cscript.exe (PID: 2108)
Process drops legitimate windows executable
- vpnclient.exe (PID: 8616)
There is functionality for taking screenshot (YARA)
- vpnclient.exe (PID: 9188)
Detected use of alternative data streams (AltDS)
- vpnclient.exe (PID: 9188)
- maintenancetool.exe (PID: 2552)
The process drops C-runtime libraries
- vpnclient.exe (PID: 8616)
Drops a system driver (possible attempt to evade defenses)
- vpnclient.exe (PID: 8616)
- drvinst.exe (PID: 8100)
- drvinst.exe (PID: 728)
- tapinstall.exe (PID: 7772)
Get information on the list of running processes
- vpnclient.exe (PID: 9188)
Reads security settings of Internet Explorer
- tapinstall.exe (PID: 7772)
- vpnclient.exe (PID: 9188)
Creates files in the driver directory
- drvinst.exe (PID: 8100)
- drvinst.exe (PID: 728)
Creates or modifies Windows services
- drvinst.exe (PID: 728)
Creates a new Windows service
- sc.exe (PID: 9028)
Creates a software uninstall entry
- vpnclient.exe (PID: 8616)
The process executes VB scripts
- vpnclient.exe (PID: 8616)
Executes as Windows Service
- vpn-service.exe (PID: 6940)
Starts CMD.EXE for commands execution
- vpn-service.exe (PID: 6940)
- vpnclient.exe (PID: 9188)
- VPNClient.exe (PID: 840)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 2108)
- cscript.exe (PID: 720)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 2108)
- cscript.exe (PID: 720)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 2108)
- cscript.exe (PID: 720)
Uses WMIC.EXE to obtain information about the network interface controller
- dns.exe (PID: 1532)
- VPNClient.exe (PID: 840)
Windows service management via SC.EXE
- sc.exe (PID: 516)
Restarts service on failure
- sc.exe (PID: 7848)
Uses DRIVERQUERY.EXE to obtain a list of installed device drivers
- cmd.exe (PID: 7992)
Uses ROUTE.EXE to obtain the routing table information
- VPNClient.exe (PID: 840)
Uses TASKKILL.EXE to kill process
- vpn-service.exe (PID: 6940)
Uses WMIC.EXE to obtain data on processes
- VPNClient.exe (PID: 840)
INFO
Checks supported languages
- identity_helper.exe (PID: 8500)
- vpnclient.exe (PID: 8616)
- vpnclient.exe (PID: 9188)
- tapinstall.exe (PID: 7772)
- app-conf.exe (PID: 5216)
- tapinstall.exe (PID: 8088)
- drvinst.exe (PID: 8100)
- drvinst.exe (PID: 728)
- tapinstall.exe (PID: 8724)
- tapinstall.exe (PID: 7864)
- tapinstall.exe (PID: 8748)
- tapinstall.exe (PID: 7432)
- app-conf.exe (PID: 2040)
- tapinstall.exe (PID: 5360)
- vpn-service.exe (PID: 6940)
- dns.exe (PID: 1532)
- killswitch.exe (PID: 7804)
- VPNClient.exe (PID: 840)
- maintenancetool.exe (PID: 2552)
- tapinstall.exe (PID: 8592)
Application launched itself
- msedge.exe (PID: 6480)
Create files in a temporary directory
- vpnclient.exe (PID: 9188)
- tapinstall.exe (PID: 7772)
- vpnclient.exe (PID: 8616)
- VPNClient.exe (PID: 840)
- maintenancetool.exe (PID: 2552)
Reads the computer name
- identity_helper.exe (PID: 8500)
- vpnclient.exe (PID: 9188)
- vpnclient.exe (PID: 8616)
- tapinstall.exe (PID: 7772)
- drvinst.exe (PID: 8100)
- drvinst.exe (PID: 728)
- vpn-service.exe (PID: 6940)
- killswitch.exe (PID: 7804)
- dns.exe (PID: 1532)
- VPNClient.exe (PID: 840)
- maintenancetool.exe (PID: 2552)
Reads Environment values
- identity_helper.exe (PID: 8500)
Process checks computer location settings
- vpnclient.exe (PID: 9188)
Creates files in the program directory
- vpnclient.exe (PID: 8616)
- vpn-service.exe (PID: 6940)
- dns.exe (PID: 1532)
The sample compiled with english language support
- vpnclient.exe (PID: 8616)
- tapinstall.exe (PID: 7772)
- drvinst.exe (PID: 8100)
- drvinst.exe (PID: 728)
- cscript.exe (PID: 2108)
Executable content was dropped or overwritten
- msedge.exe (PID: 6480)
Reads the software policy settings
- slui.exe (PID: 8344)
- drvinst.exe (PID: 8100)
- tapinstall.exe (PID: 7772)
Process checks whether UAC notifications are on
- vpnclient.exe (PID: 9188)
Reads the machine GUID from the registry
- tapinstall.exe (PID: 7772)
- drvinst.exe (PID: 8100)
- vpnclient.exe (PID: 8616)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2108)
- cscript.exe (PID: 720)
- WMIC.exe (PID: 7788)
- WMIC.exe (PID: 8240)
- WMIC.exe (PID: 6264)
Qt framework related mutex has been found
- VPNClient.exe (PID: 840)
Creates files or folders in the user directory
- VPNClient.exe (PID: 840)
Prints a route via ROUTE.EXE
- ROUTE.EXE (PID: 8840)
Checks proxy server information
- VPNClient.exe (PID: 840)
- maintenancetool.exe (PID: 2552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
236
Monitored processes
98
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | cmd /C "start Start.lnk" | C:\Windows\SysWOW64\cmd.exe | — | vpnclient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7120 --field-trial-handle=2300,i,16264097407976547157,10509603820472879014,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | sc description VPNClient-service "VPNClient Service" | C:\Windows\SysWOW64\sc.exe | — | vpnclient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | cscript //Nologo C:\Users\admin\AppData\Local\Temp\deferredrenamejxDnrR.vbs | C:\Windows\SysWOW64\cscript.exe | — | vpnclient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 728 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\WINDOWS\INF\oem1.inf" "oem1.inf:3beb73aff103cc24:tap0901.ndi:9.23.1.601:tap0901," "4d14a44ff" "00000000000001D8" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
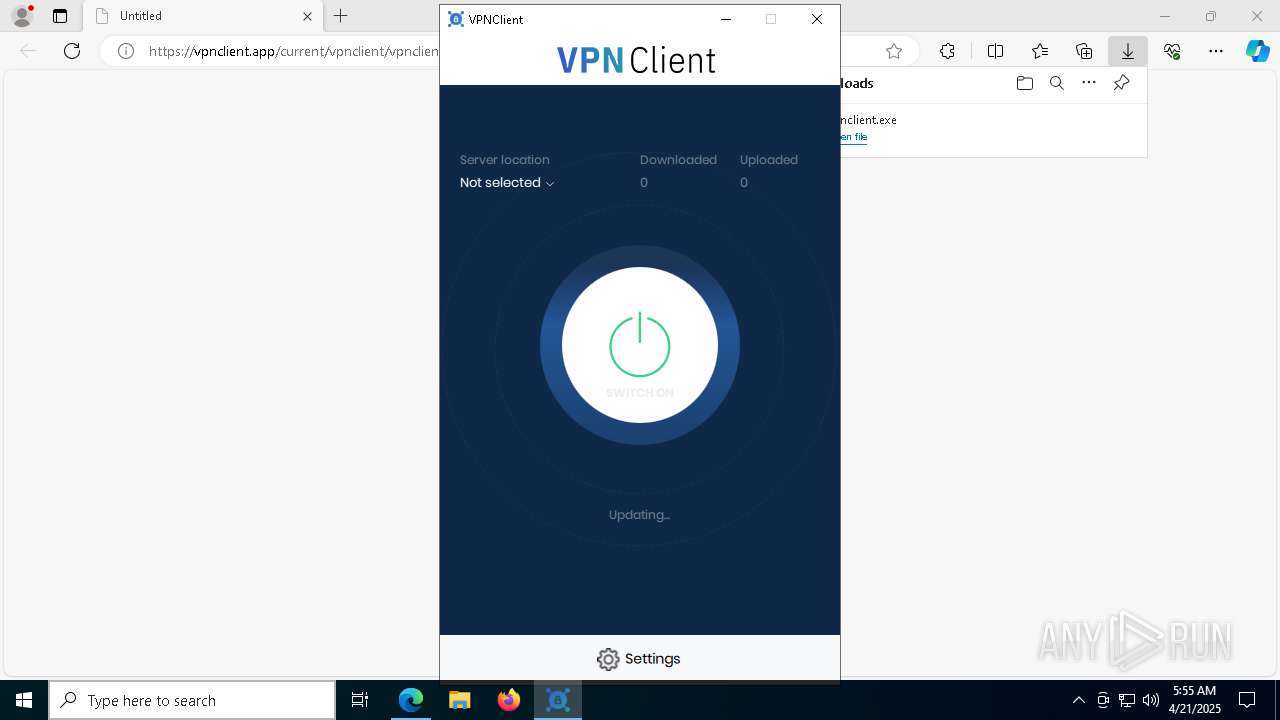
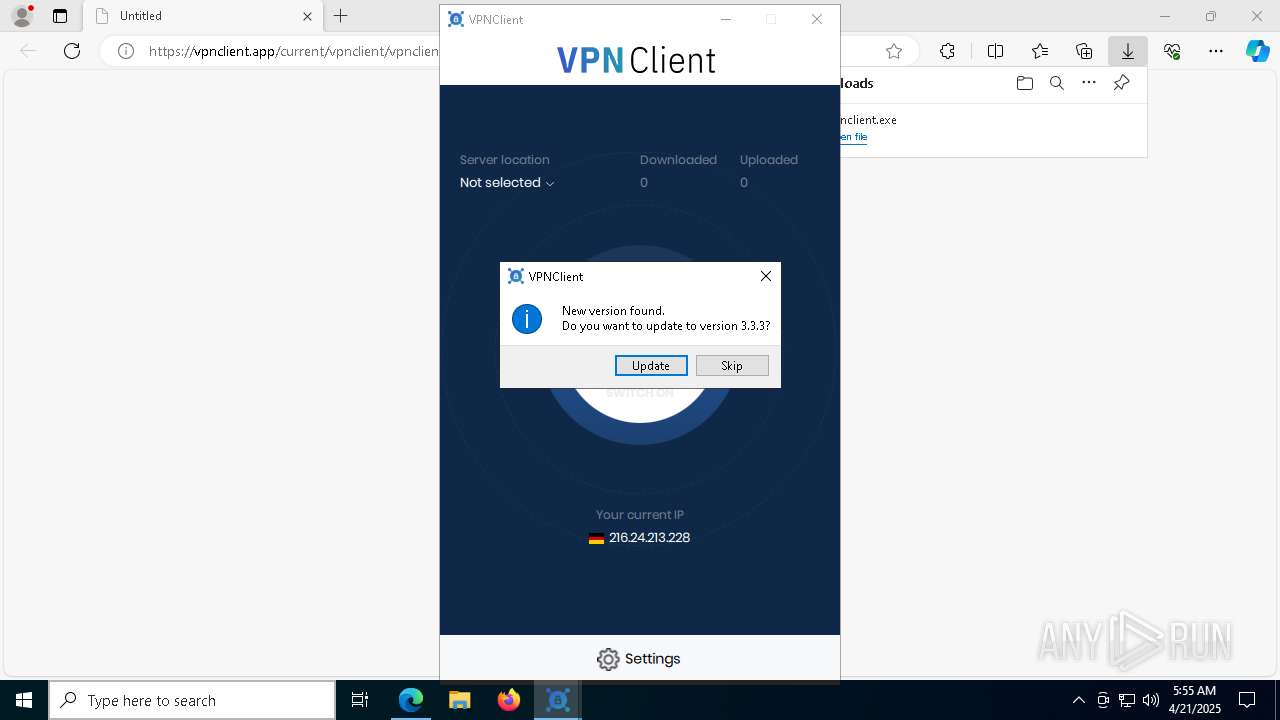
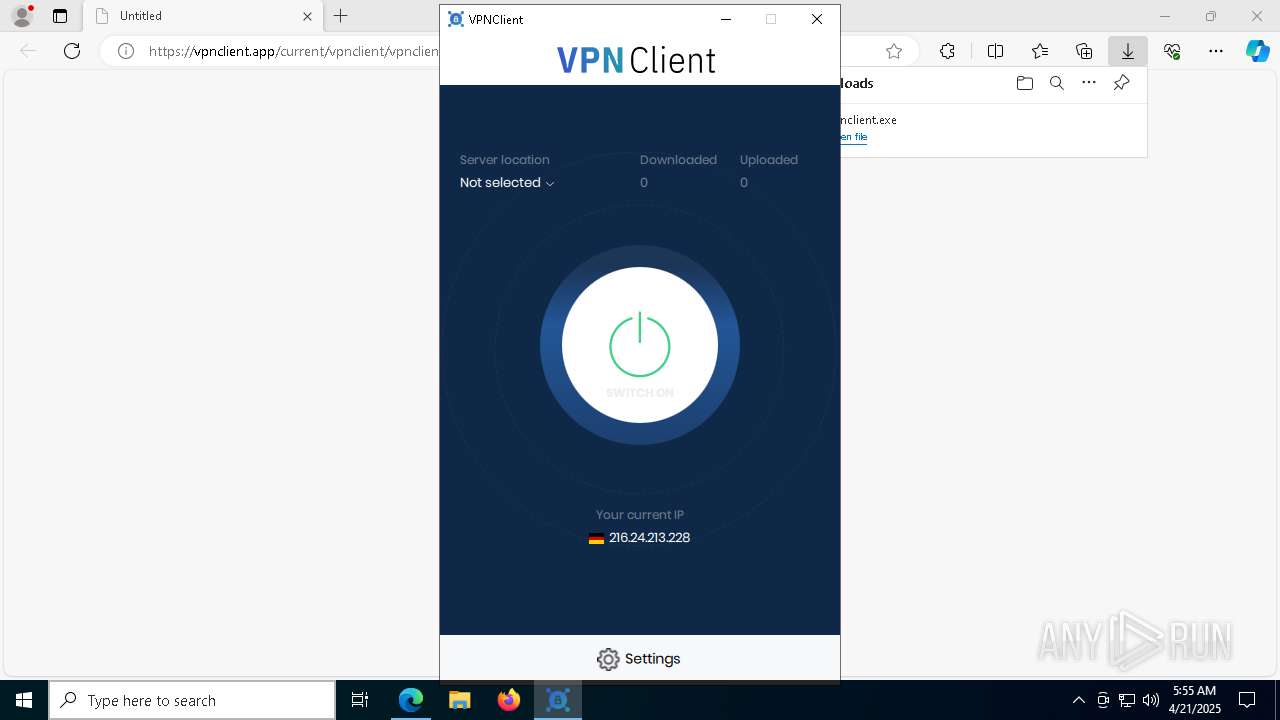
| 840 | "C:\Program Files (x86)\VPNClient\VPNClient.exe" | C:\Program Files (x86)\VPNClient\VPNClient.exe | cmd.exe | ||||||||||||
User: admin Company: VPNClient Integrity Level: MEDIUM Description: Desktop client for VPN Modules
| |||||||||||||||
| 896 | C:\WINDOWS\system32\cmd.exe /c "C:\Program Files (x86)\VPNClient\dns.exe" reset | C:\Windows\SysWOW64\cmd.exe | — | vpn-service.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | taskkill /f /im openvpn.exe | C:\Windows\SysWOW64\taskkill.exe | — | vpn-service.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\Program Files (x86)\VPNClient\dns.exe" reset | C:\Program Files (x86)\VPNClient\dns.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: VPNClient Integrity Level: SYSTEM Description: Desktop client for VPN Exit code: 0 Modules
| |||||||||||||||
Total events
23 700
Read events
23 618
Write events
75
Delete events
7
Modification events
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7135BA0A-9EB4-4324-A063-B1C59CDB5B4F} | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1ED318C6D9912F00 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2AA621C6D9912F00 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 000846C6D9912F00 | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
122
Suspicious files
323
Text files
583
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b3e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b3f0.TMP | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b400.TMP | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b40f.TMP | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b40f.TMP | — | |
MD5:— | SHA256:— | |||
| 6480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
61
DNS requests
55
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6480 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1760 | SIHClient.exe | GET | 200 | 23.217.49.217:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8512 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1745625001&P2=404&P3=2&P4=N8loaHhCWZ9dLTaUGfe5nqUUmaYZZy4ZvYNPOemqbwRjgmZeZByiwvx9R%2bJGBK4B3lHgeK4FB9GT%2beQNG1ZGmQ%3d%3d | unknown | — | — | whitelisted |
1760 | SIHClient.exe | GET | 200 | 23.217.49.217:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8512 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1745625001&P2=404&P3=2&P4=N8loaHhCWZ9dLTaUGfe5nqUUmaYZZy4ZvYNPOemqbwRjgmZeZByiwvx9R%2bJGBK4B3lHgeK4FB9GT%2beQNG1ZGmQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6480 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7352 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
vpnclient.app |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |