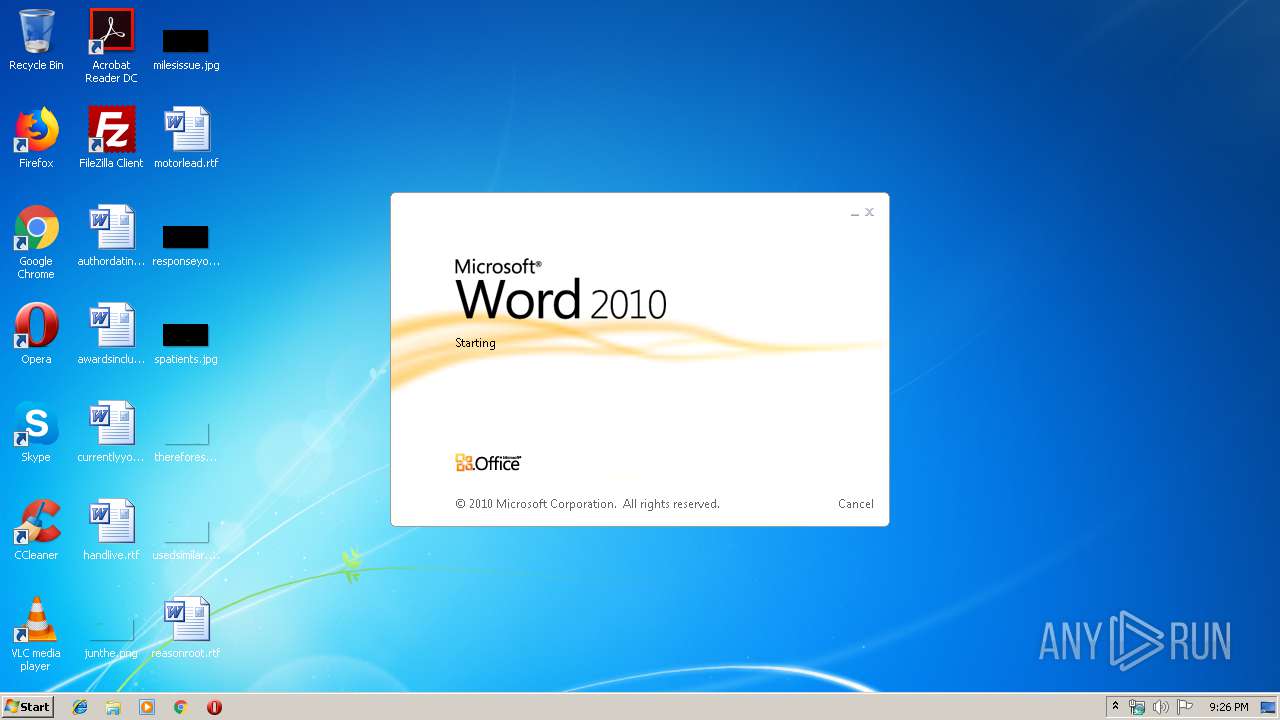
| File name: | AppStoreDisconnect.docx |
| Full analysis: | https://app.any.run/tasks/02112967-381d-45de-bfb4-dd939bc36a2f |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 20:25:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 29716E67C207E73DF82B2259C7FBA5A5 |
| SHA1: | E82020A00CEADFA5B419E7A76089F504BCBAEA2E |
| SHA256: | 97CD0BB9A7999EB2A3F6D0AABB693FD577B38B88826D3BF0ED98B16C708D44A2 |
| SSDEEP: | 192:CtXe9748abNxtpgoZ22NNAf7cwj4JhKqmdiY2KeXWf911M+OCBE5axblhUqdN:aOZ4LbNxt/ZtNNAfQJhKqR411Vt5UYN |
MALICIOUS
No malicious indicators.SUSPICIOUS
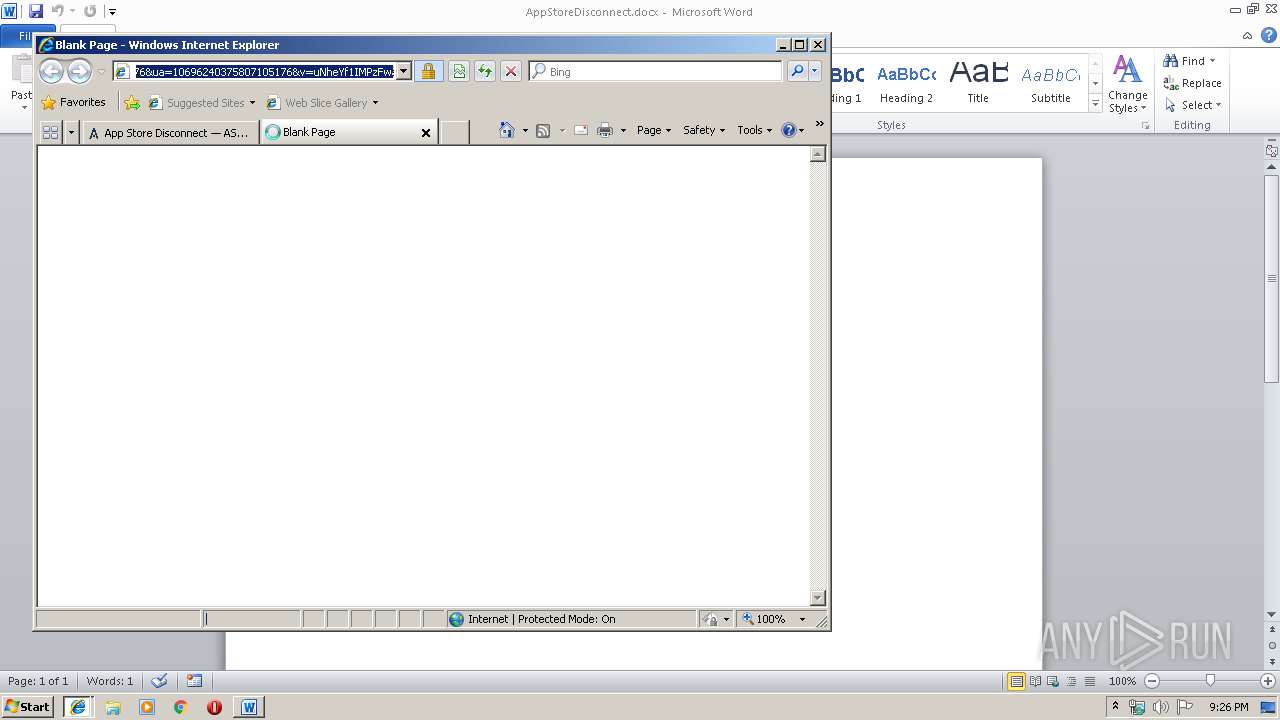
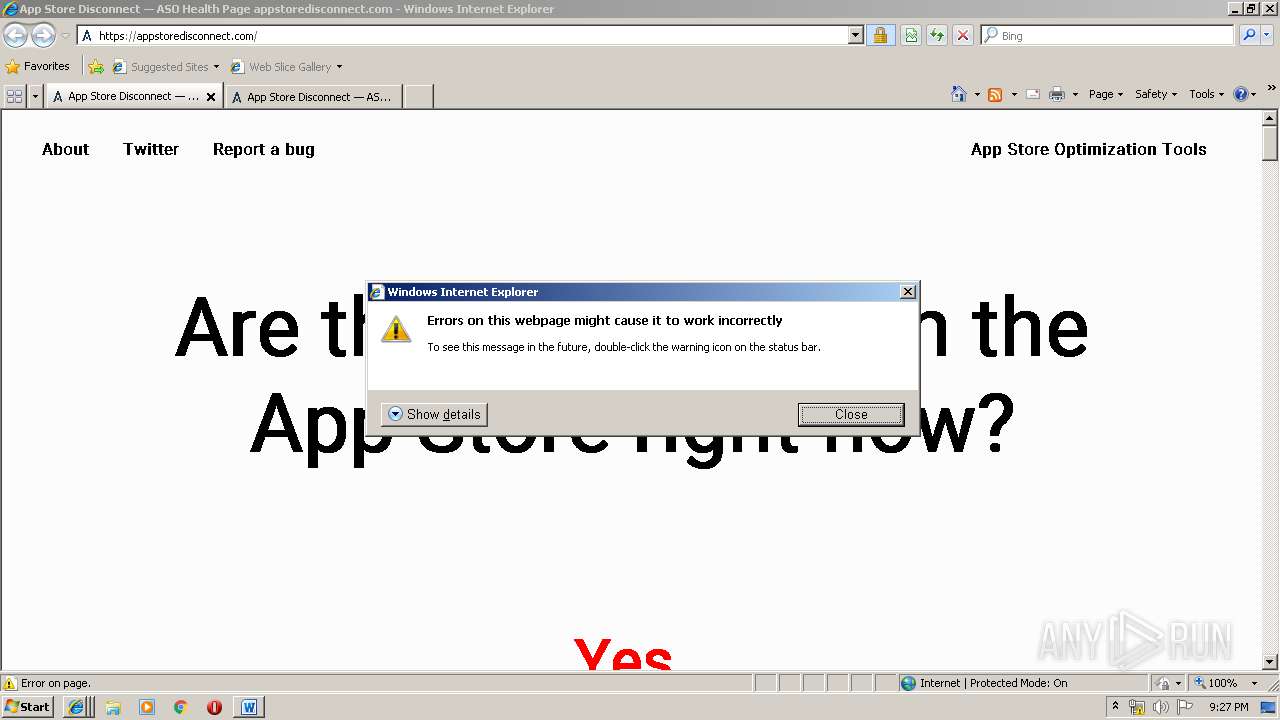
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1340)
- iexplore.exe (PID: 3544)
Reads internet explorer settings
- WINWORD.EXE (PID: 3088)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3088)
Changes internet zones settings
- iexplore.exe (PID: 3544)
Creates files in the user directory
- WINWORD.EXE (PID: 3088)
- iexplore.exe (PID: 3776)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1340)
- iexplore.exe (PID: 3468)
- iexplore.exe (PID: 2672)
- iexplore.exe (PID: 3544)
- iexplore.exe (PID: 3140)
Reads settings of System Certificates
- iexplore.exe (PID: 3544)
Reads Internet Cache Settings
- iexplore.exe (PID: 3776)
- iexplore.exe (PID: 3468)
- iexplore.exe (PID: 2672)
- iexplore.exe (PID: 3140)
Reads internet explorer settings
- iexplore.exe (PID: 3776)
- iexplore.exe (PID: 3468)
- iexplore.exe (PID: 2672)
- iexplore.exe (PID: 3140)
Application launched itself
- iexplore.exe (PID: 3544)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3544)
Changes settings of System certificates
- iexplore.exe (PID: 3544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x6cd2a4df |
| ZipCompressedSize: | 346 |
| ZipUncompressedSize: | 1312 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Toor, Omar |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | Toor, Omar |
| RevisionNumber: | 1 |
| CreateDate: | 2019:07:17 20:24:00Z |
| ModifyDate: | 2019:07:17 20:25:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | 11 |
| Characters: | 67 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 77 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
42
Monitored processes
7
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1340 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3544 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3088 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\AppStoreDisconnect.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3140 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3544 CREDAT:334081 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3468 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3544 CREDAT:6402 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3544 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3776 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3544 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 762
Read events
1 913
Write events
840
Delete events
9
Modification events
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | .,% |
Value: 2E2C2500100C0000010000000000000000000000 | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324417054 | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324417168 | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324417169 | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 100C0000160755DDDD3CD50100000000 | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %.% |
Value: 252E2500100C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | %.% |
Value: 252E2500100C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3088) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
5
Text files
215
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD08E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
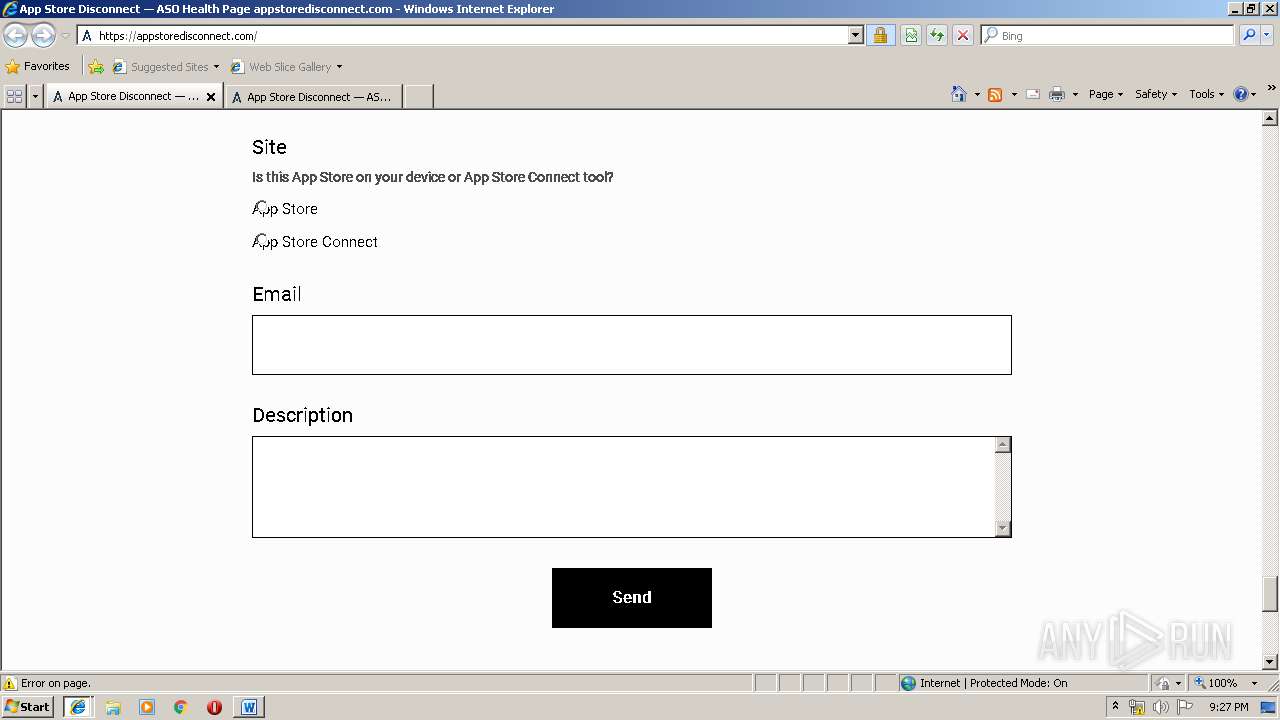
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@appstoredisconnect[1].txt | — | |
MD5:— | SHA256:— | |||
| 3544 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3544 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF102D10A975D48DAF.TMP | — | |
MD5:— | SHA256:— | |||
| 3776 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@appstoredisconnect[1].txt | — | |
MD5:— | SHA256:— | |||
| 3776 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U0DJAS3L\appstoredisconnect_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@appstoredisconnect[2].txt | text | |
MD5:— | SHA256:— | |||
| 3088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$pStoreDisconnect.docx | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
101
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
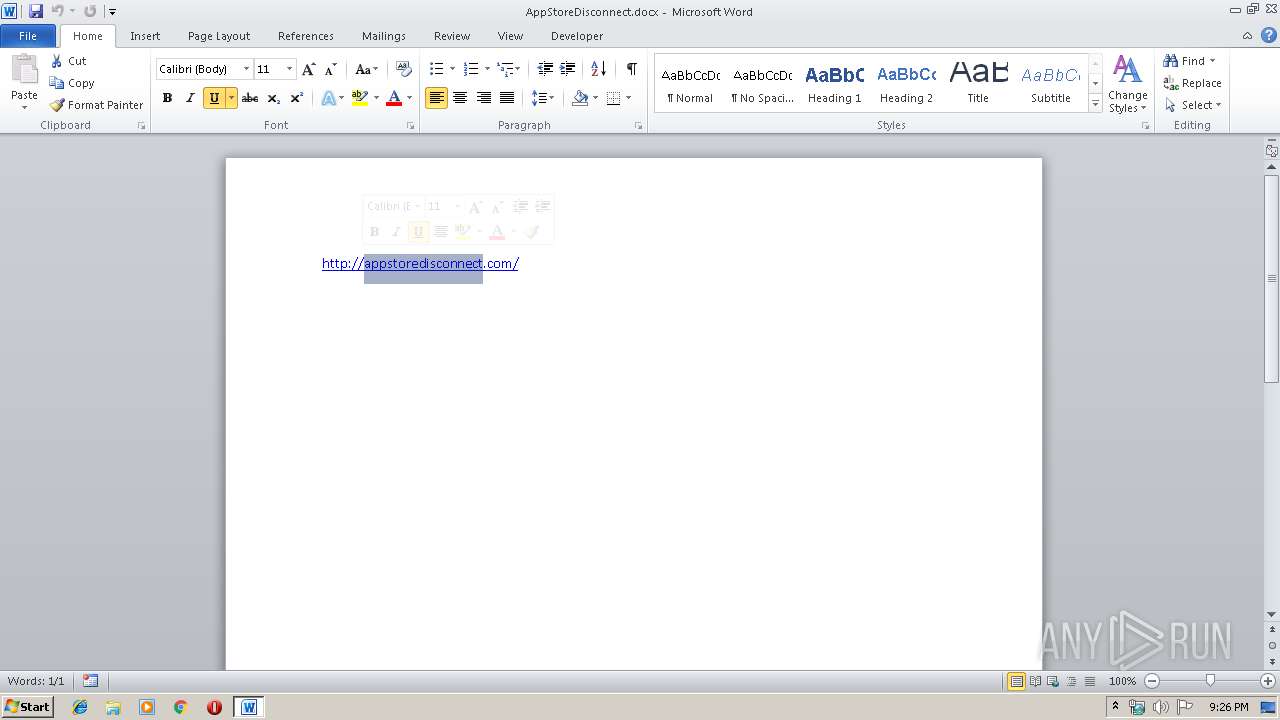
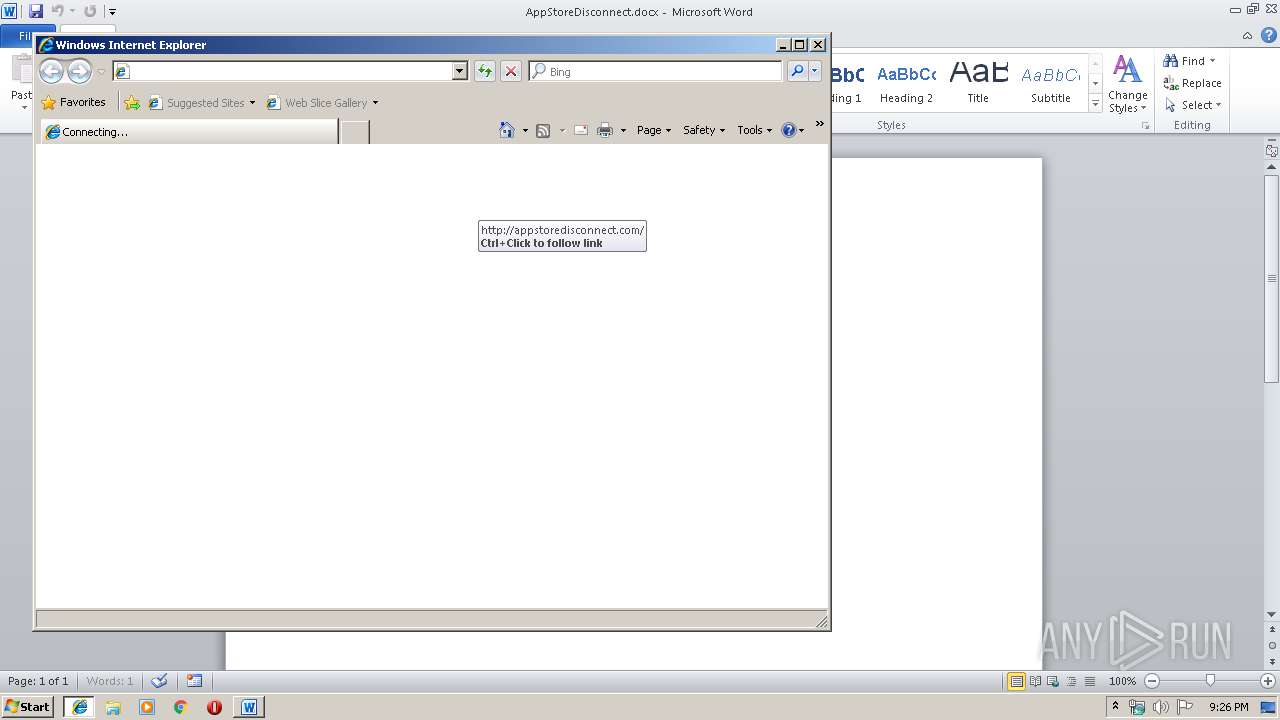
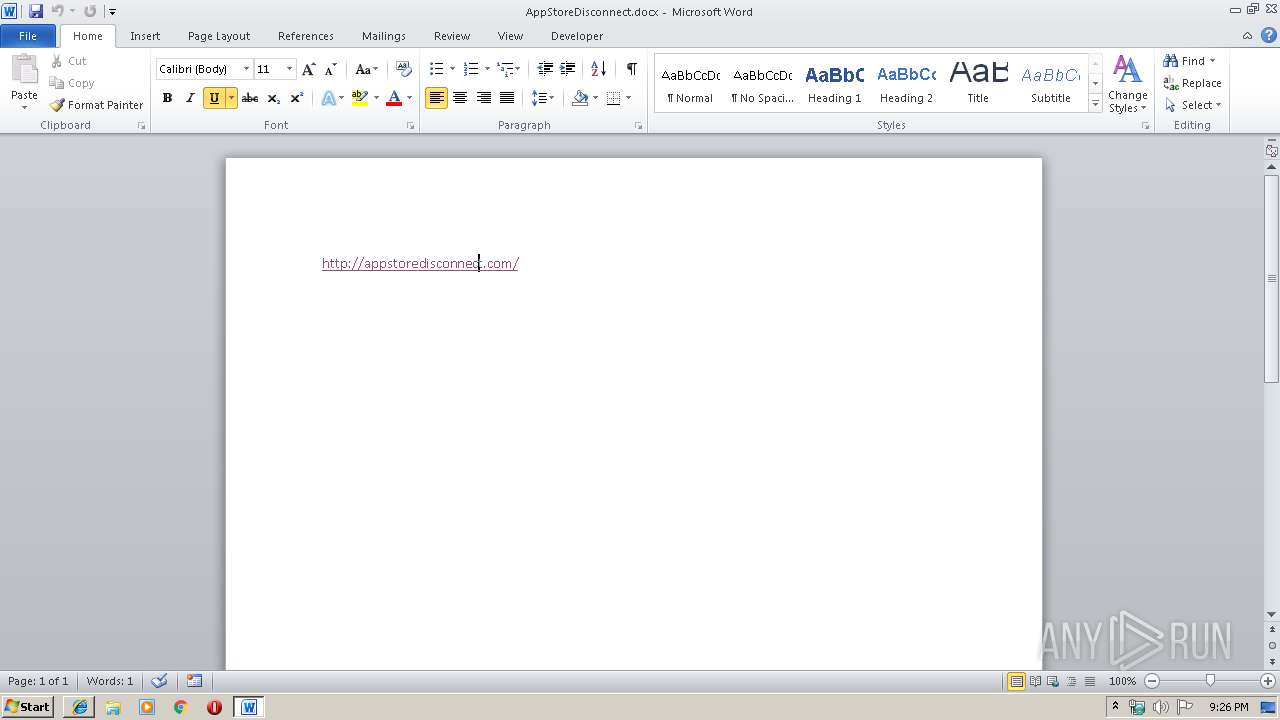
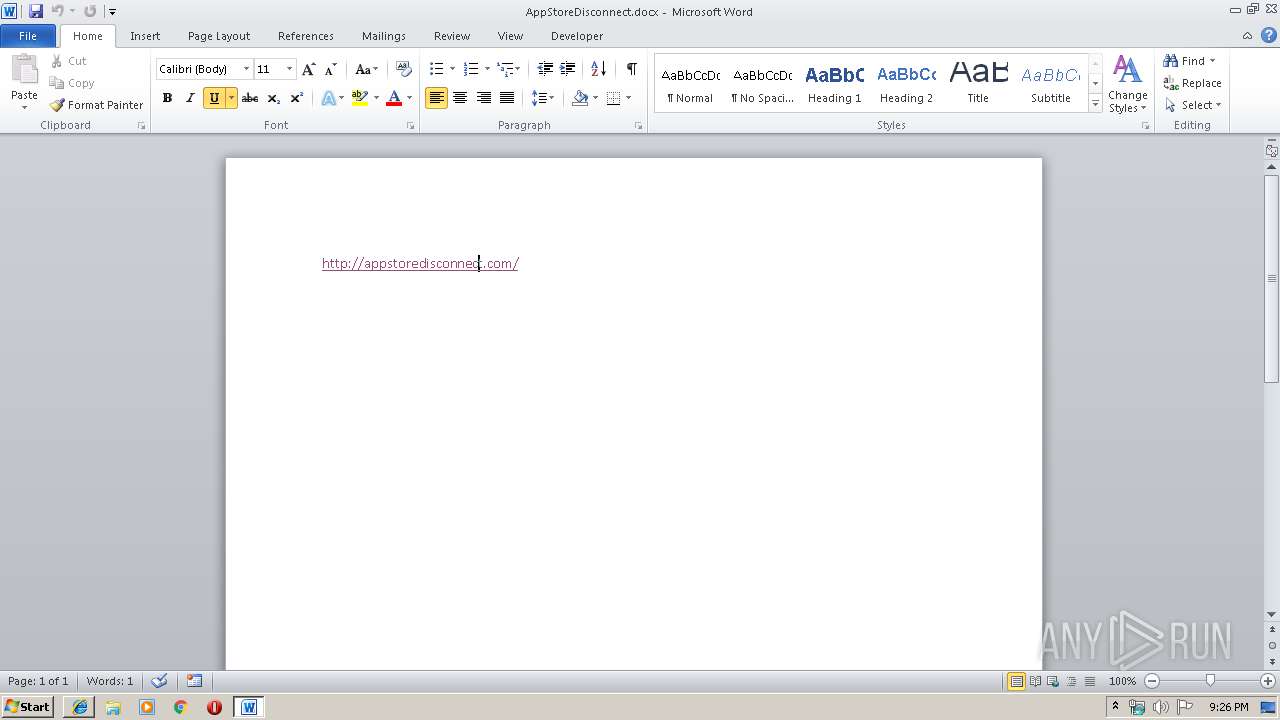
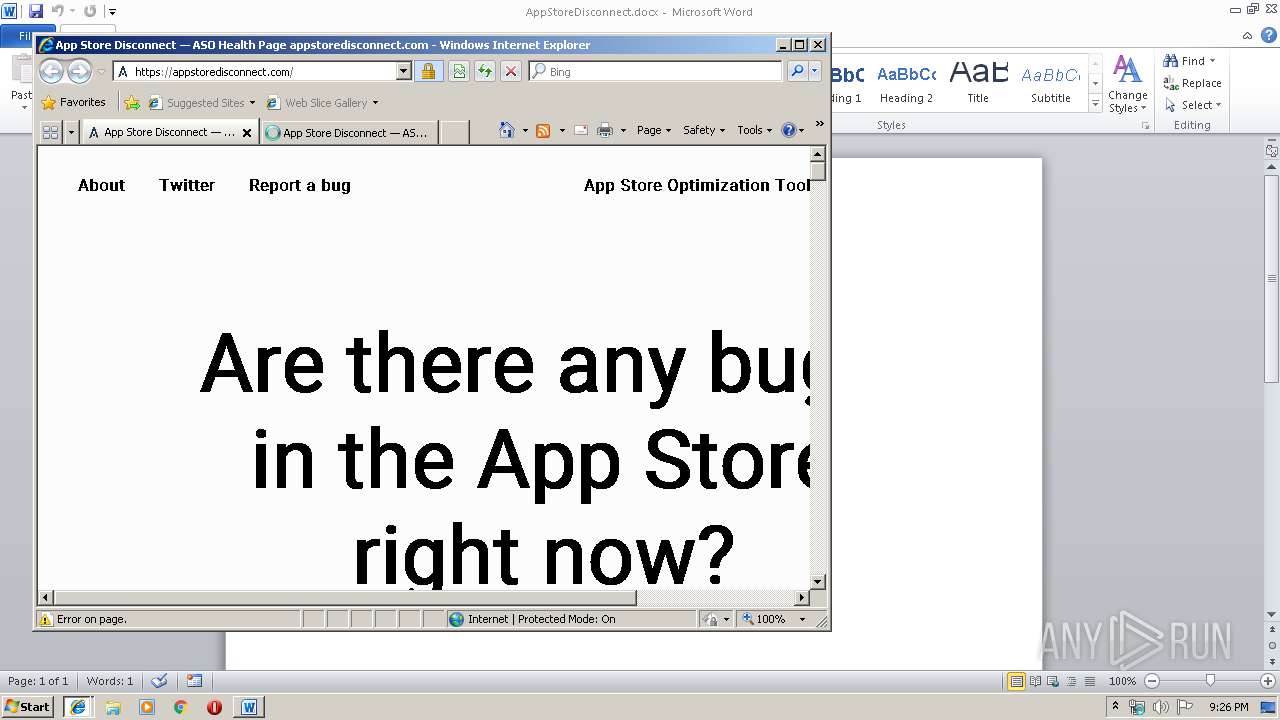
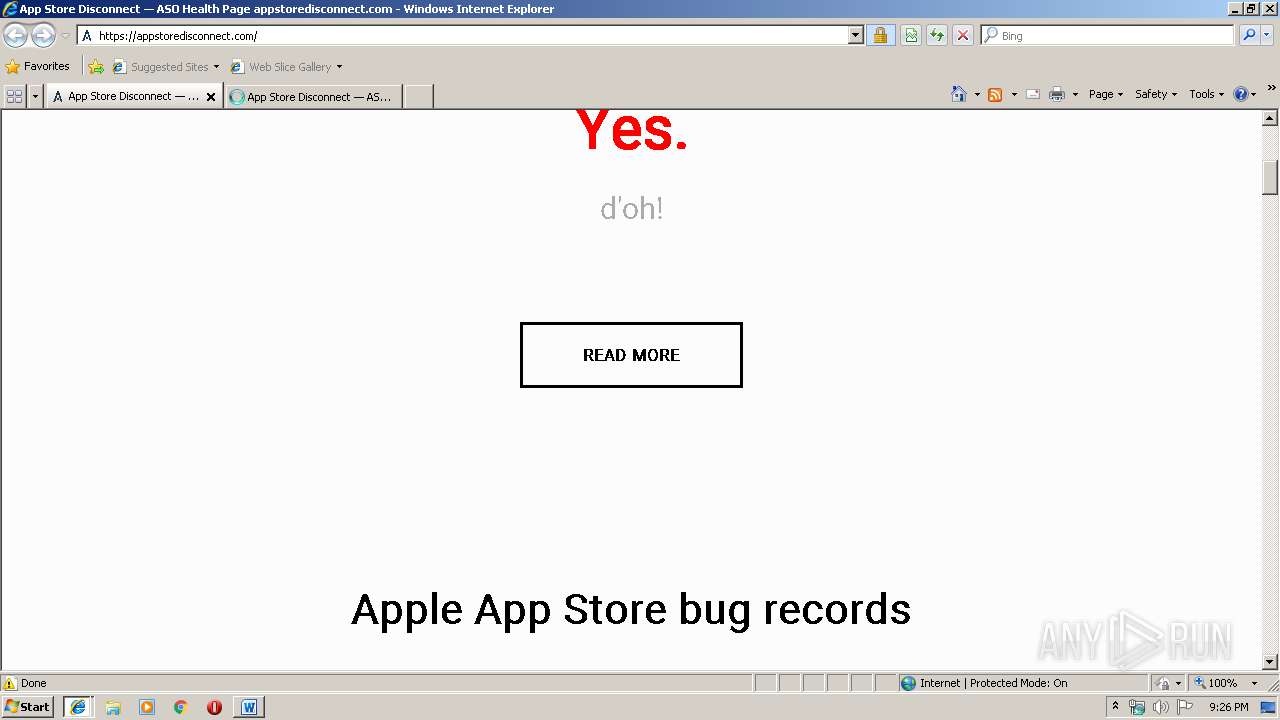
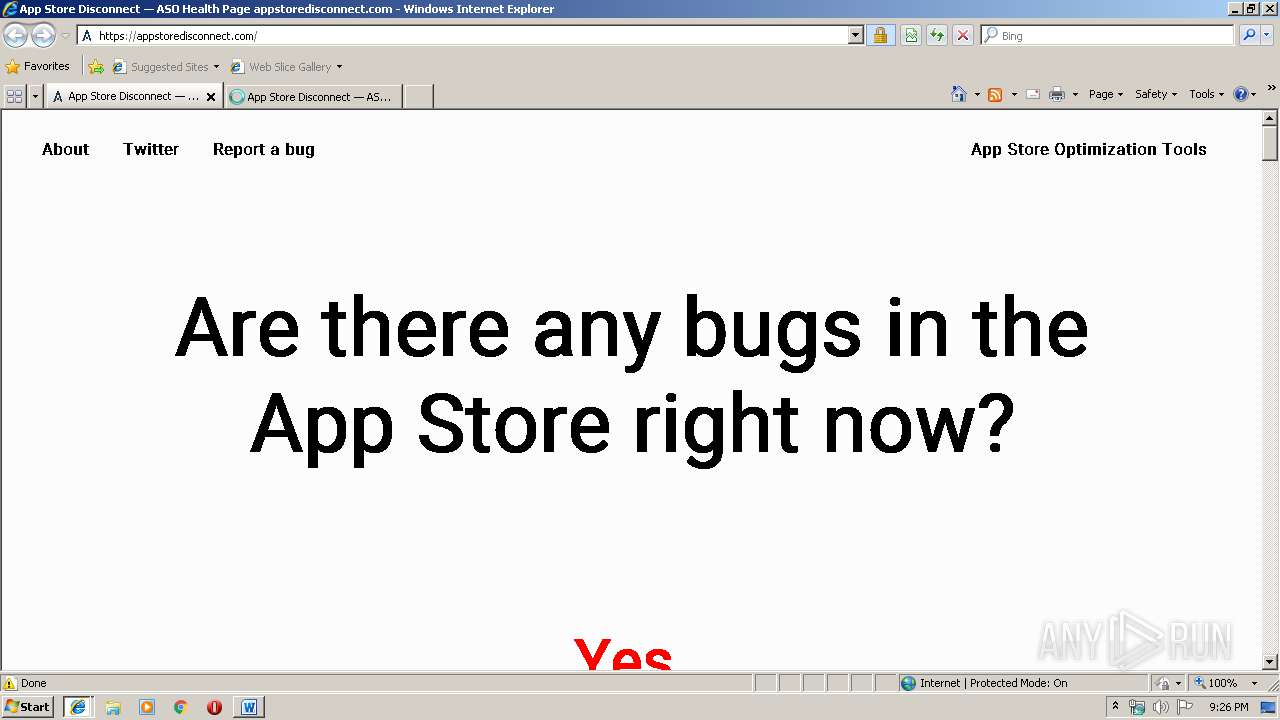
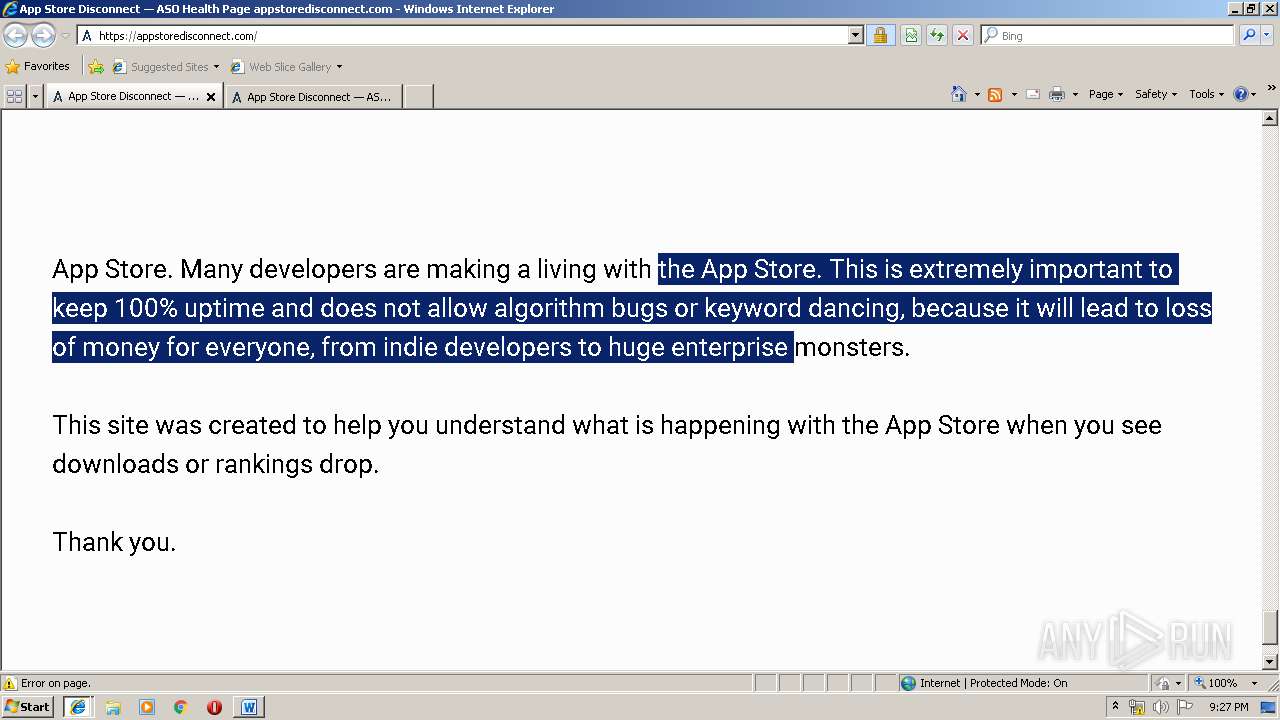
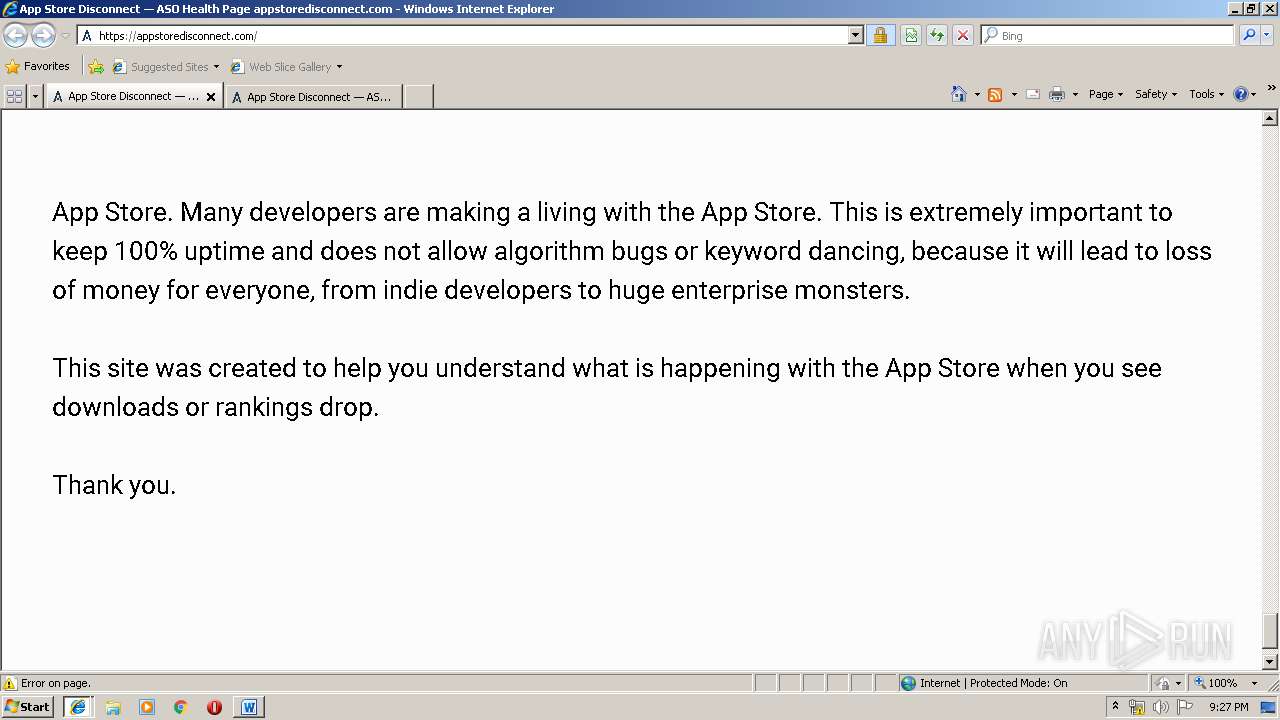
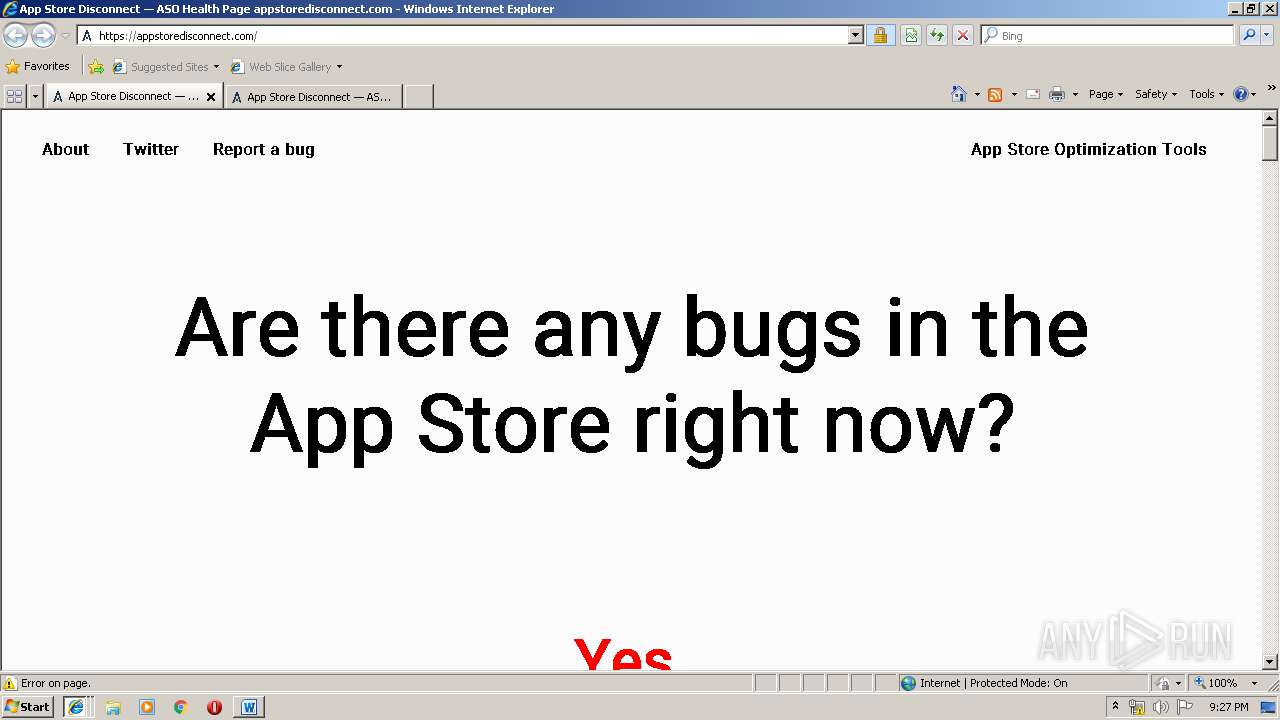
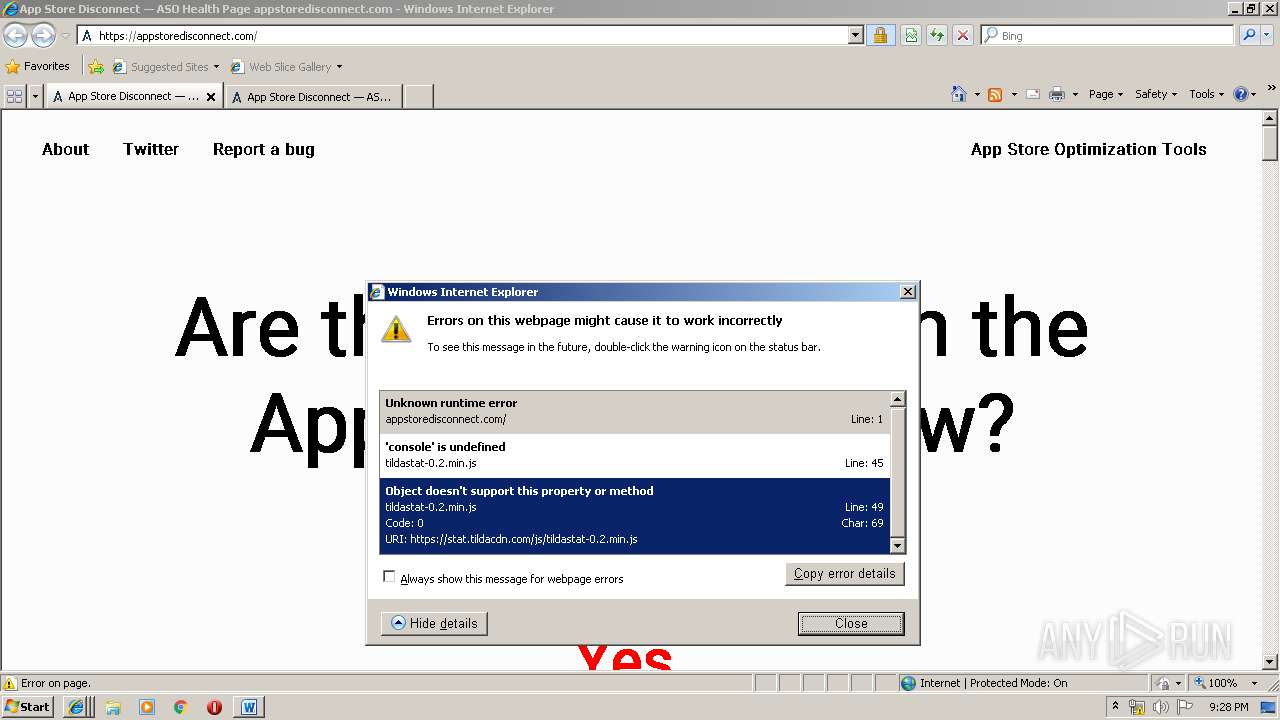
3088 | WINWORD.EXE | GET | 301 | 185.165.123.206:80 | http://appstoredisconnect.com/ | RU | html | 239 b | malicious |
3088 | WINWORD.EXE | GET | 301 | 185.165.123.206:80 | http://appstoredisconnect.com/ | RU | html | 239 b | malicious |
3544 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3544 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3544 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3776 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.3 Kb | whitelisted |
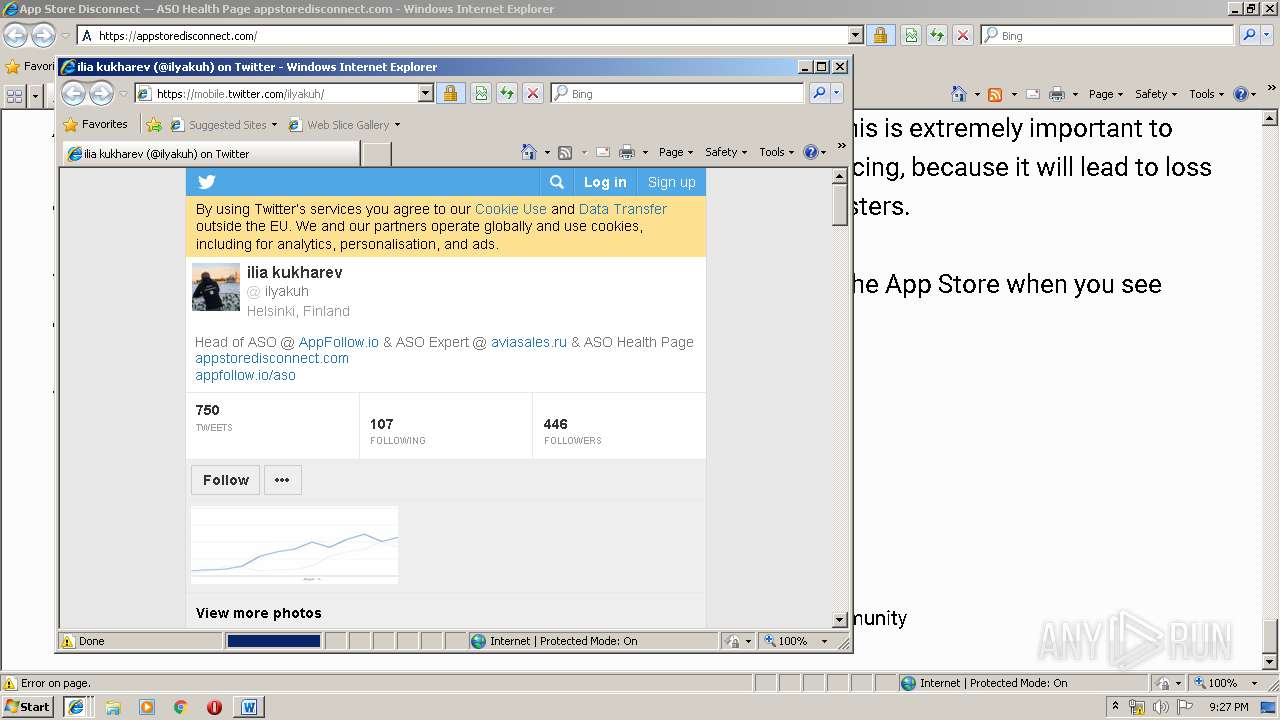
3776 | iexplore.exe | GET | 301 | 88.99.142.137:80 | http://appfollow.io/ | DE | html | 185 b | whitelisted |
3544 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
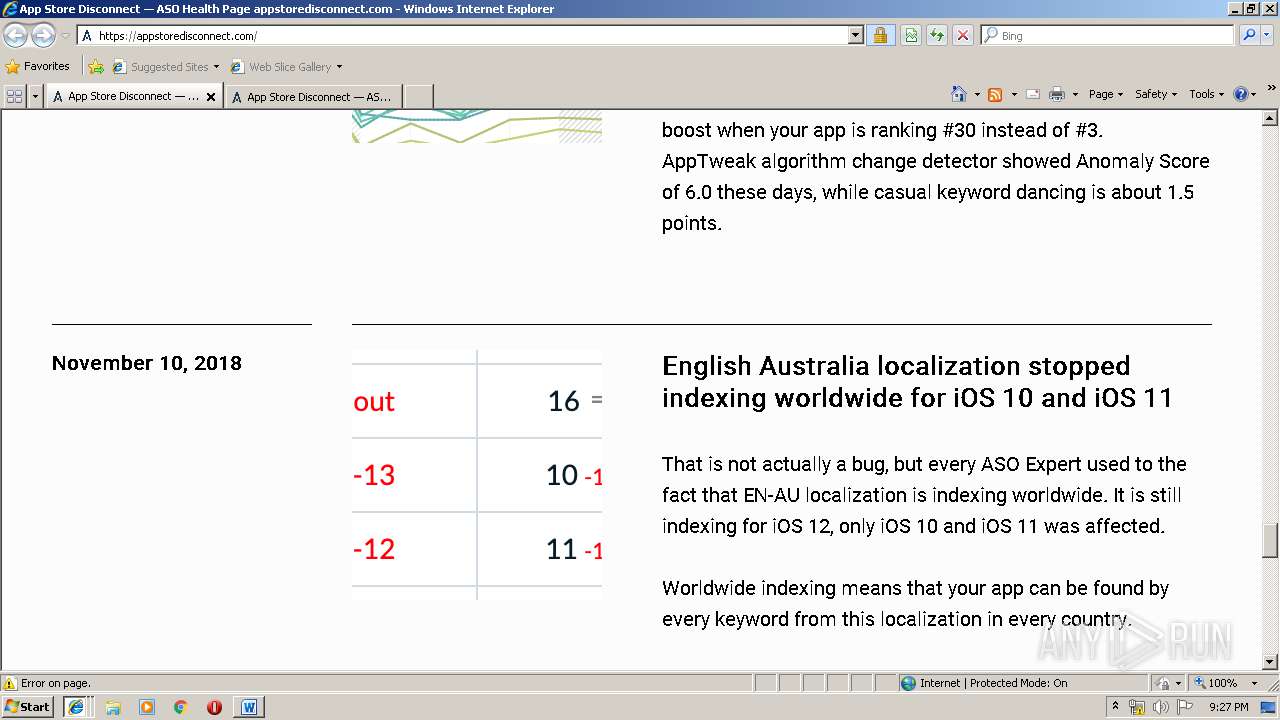
3088 | WINWORD.EXE | 185.165.123.206:80 | appstoredisconnect.com | Variti LLC | RU | malicious |
3088 | WINWORD.EXE | 185.165.123.206:443 | appstoredisconnect.com | Variti LLC | RU | malicious |
3544 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
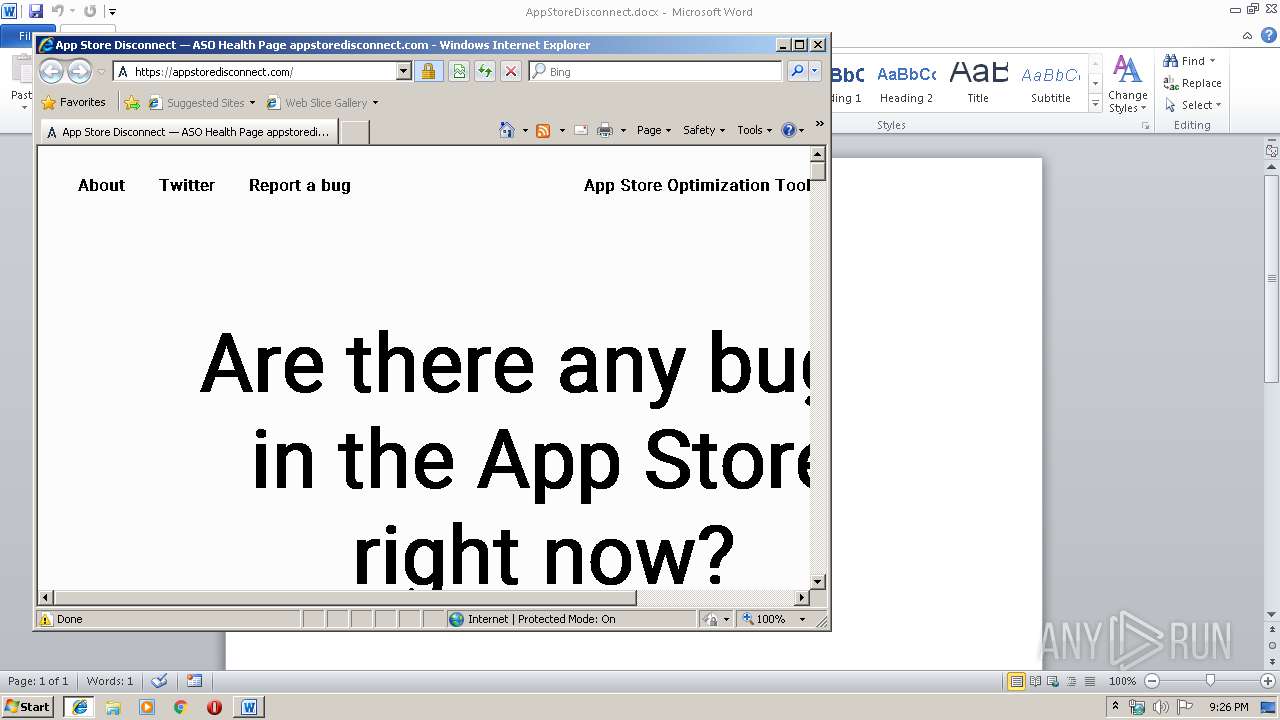
3776 | iexplore.exe | 185.165.123.206:443 | appstoredisconnect.com | Variti LLC | RU | malicious |
3776 | iexplore.exe | 178.248.234.191:443 | tilda.ws | HLL LLC | RU | malicious |
— | — | 5.254.23.239:443 | static.tildacdn.com | — | RO | unknown |
3776 | iexplore.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3776 | iexplore.exe | 172.217.16.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3776 | iexplore.exe | 77.244.208.197:443 | stat.tildacdn.com | OOO Network of data-centers Selectel | RU | unknown |
3544 | iexplore.exe | 5.254.23.239:443 | static.tildacdn.com | — | RO | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
appstoredisconnect.com |
| malicious |
www.bing.com |
| whitelisted |
static.tildacdn.com |
| shared |
tilda.ws |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
stat.tildacdn.com |
| shared |
ohio8.vchecks.me |
| unknown |