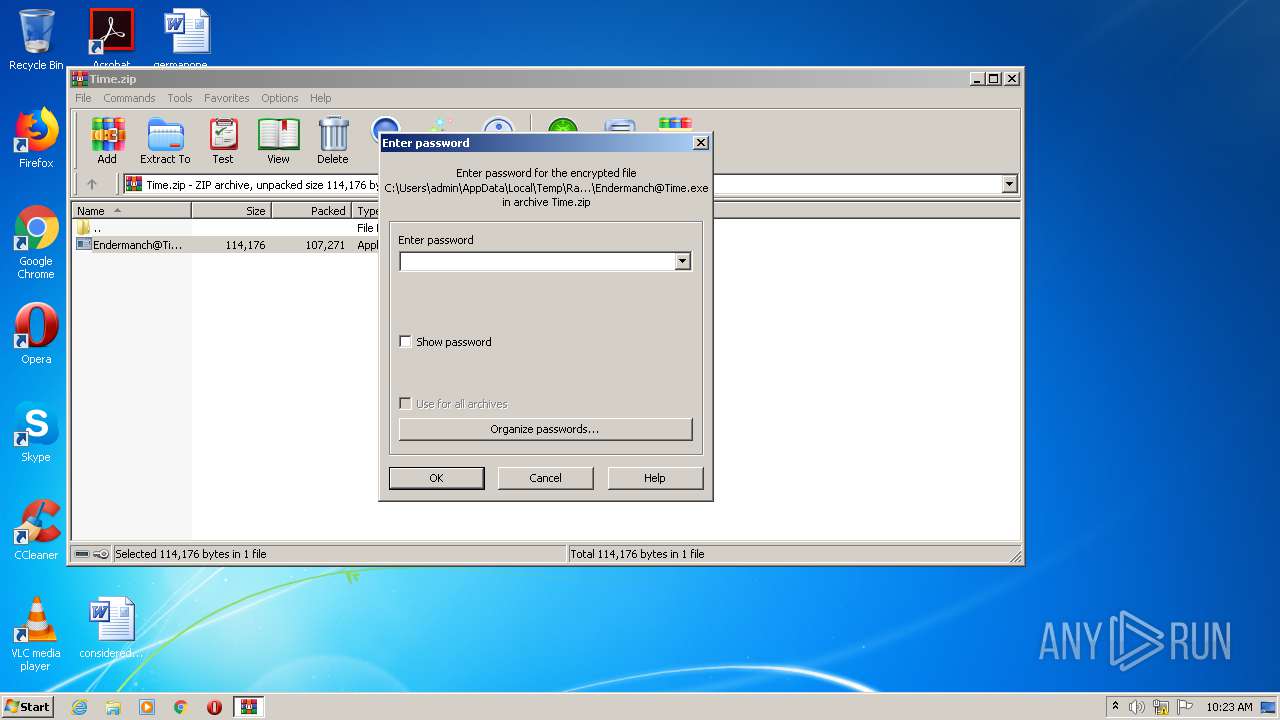
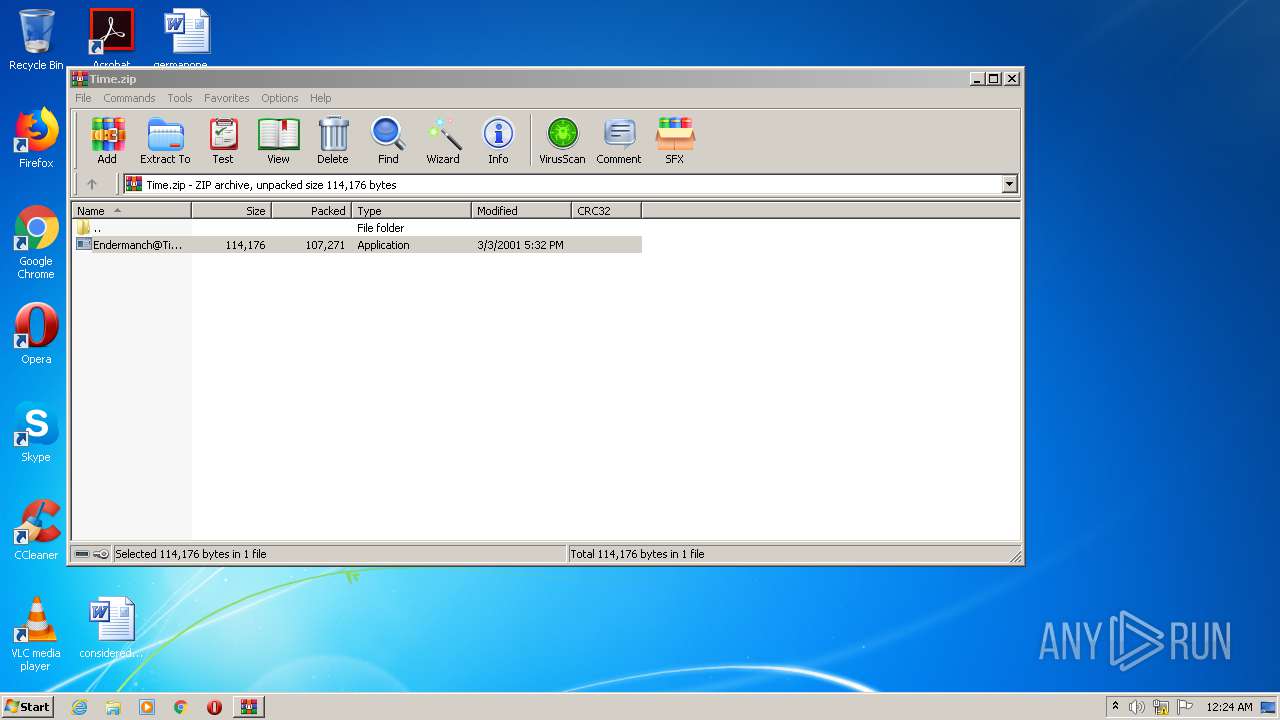
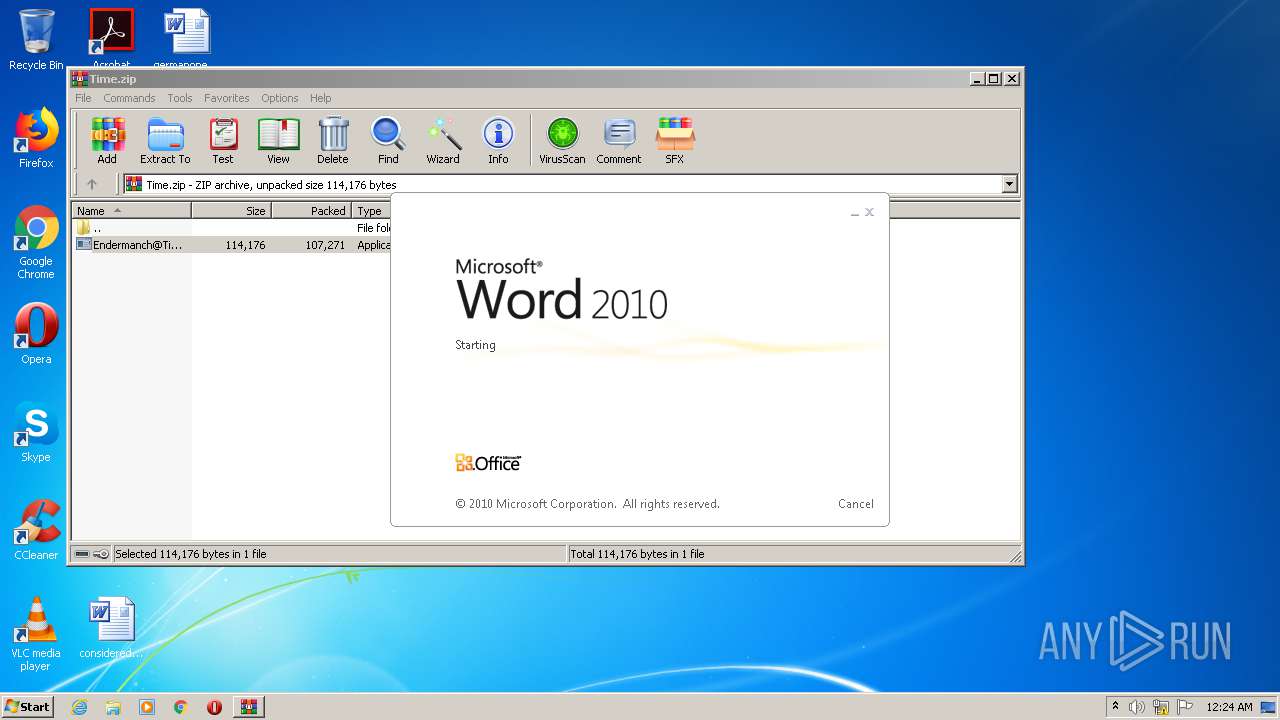
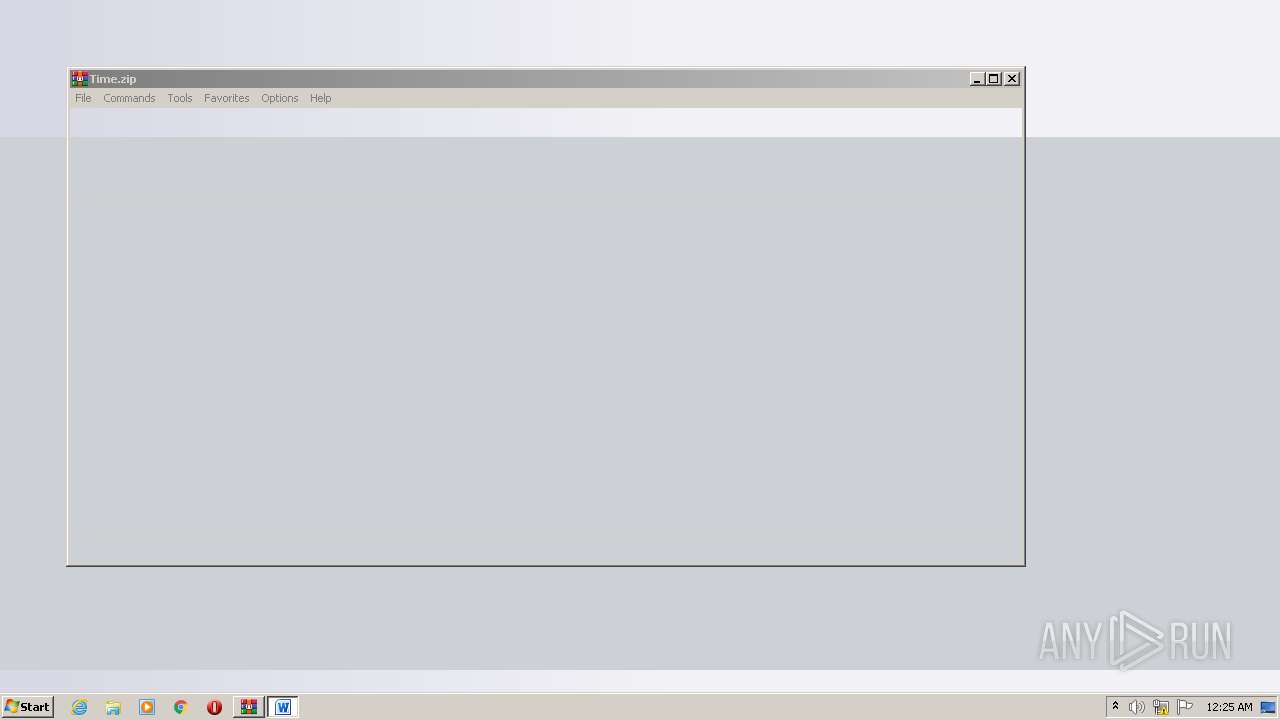
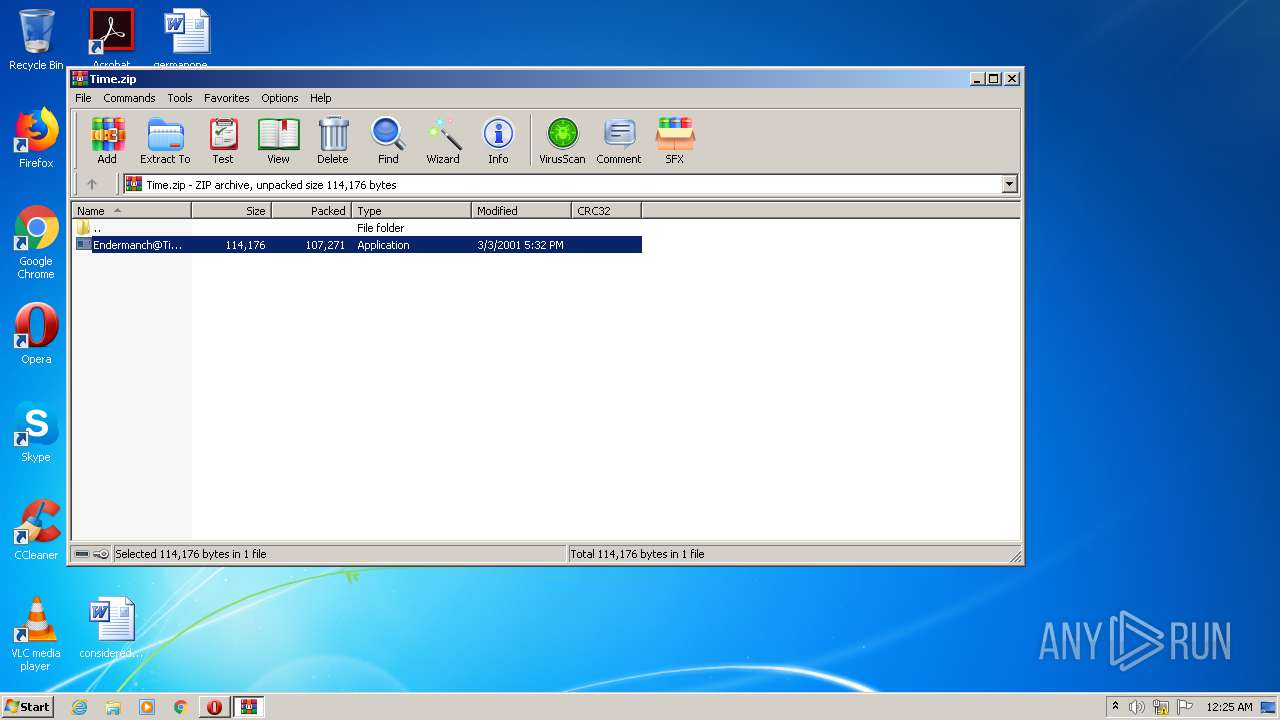
| File name: | Time.zip |
| Full analysis: | https://app.any.run/tasks/dc07097c-5cbb-4941-bf93-f65812ac0d08 |
| Verdict: | Malicious activity |
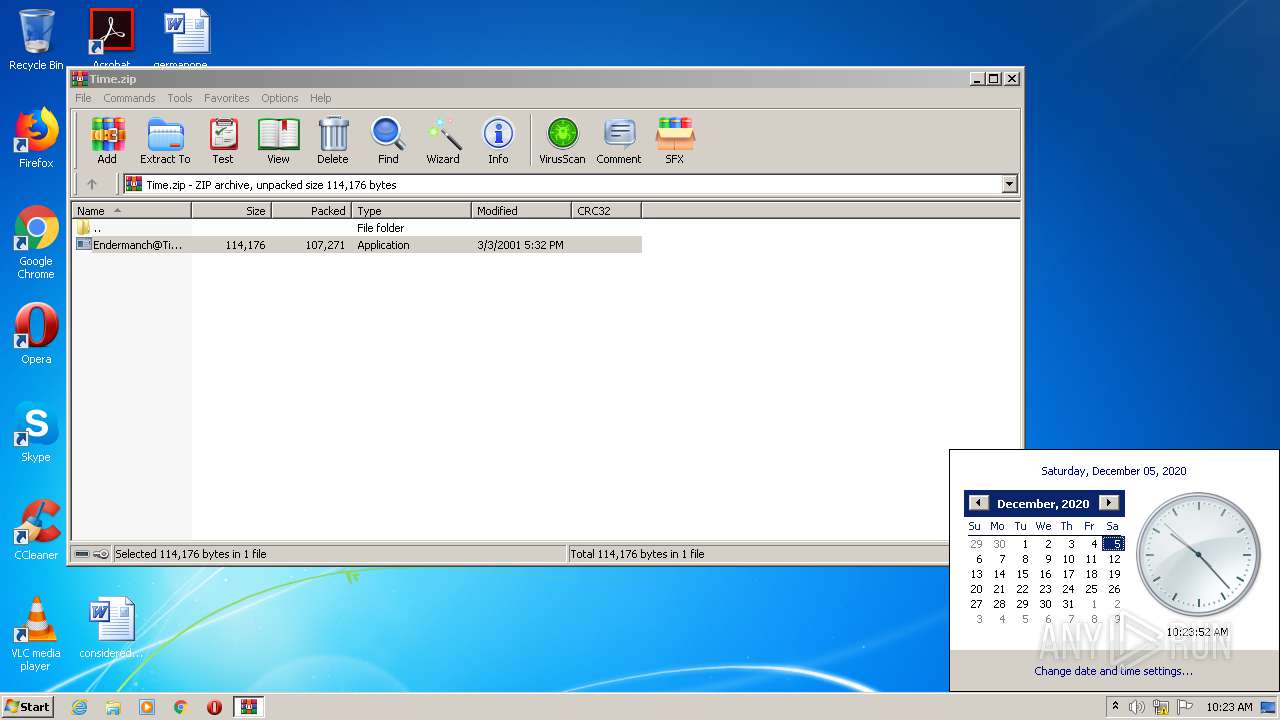
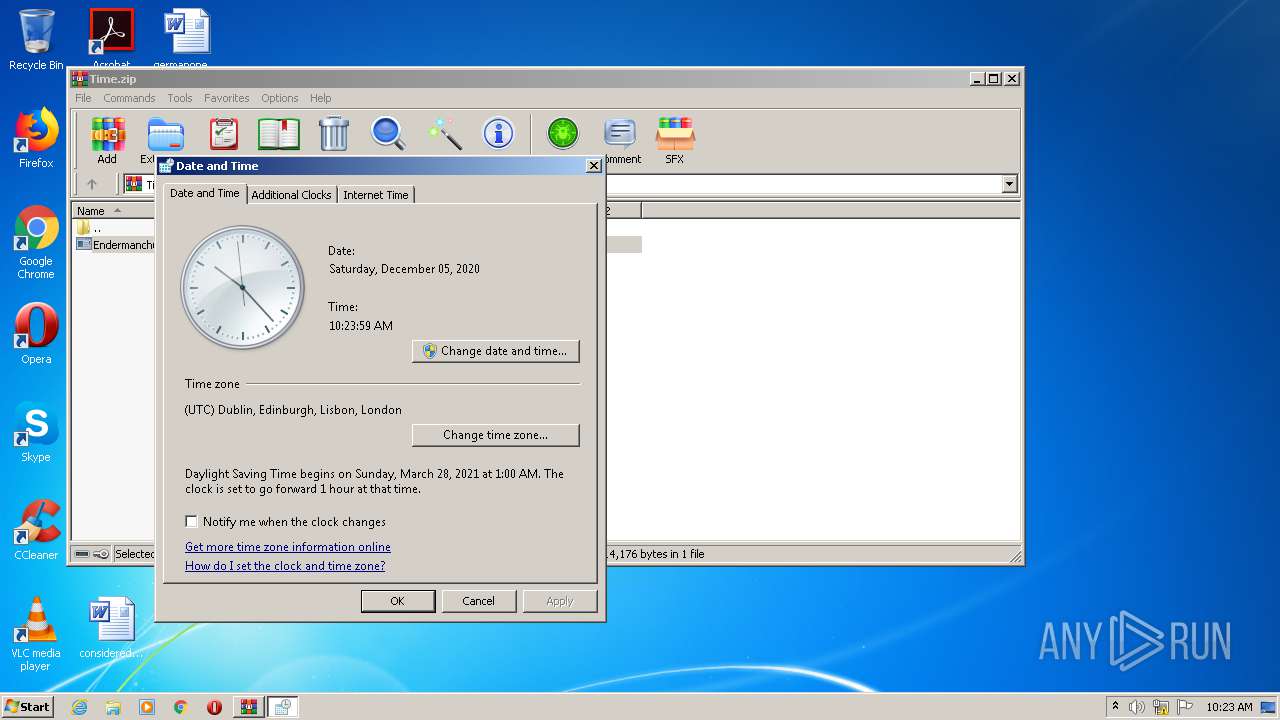
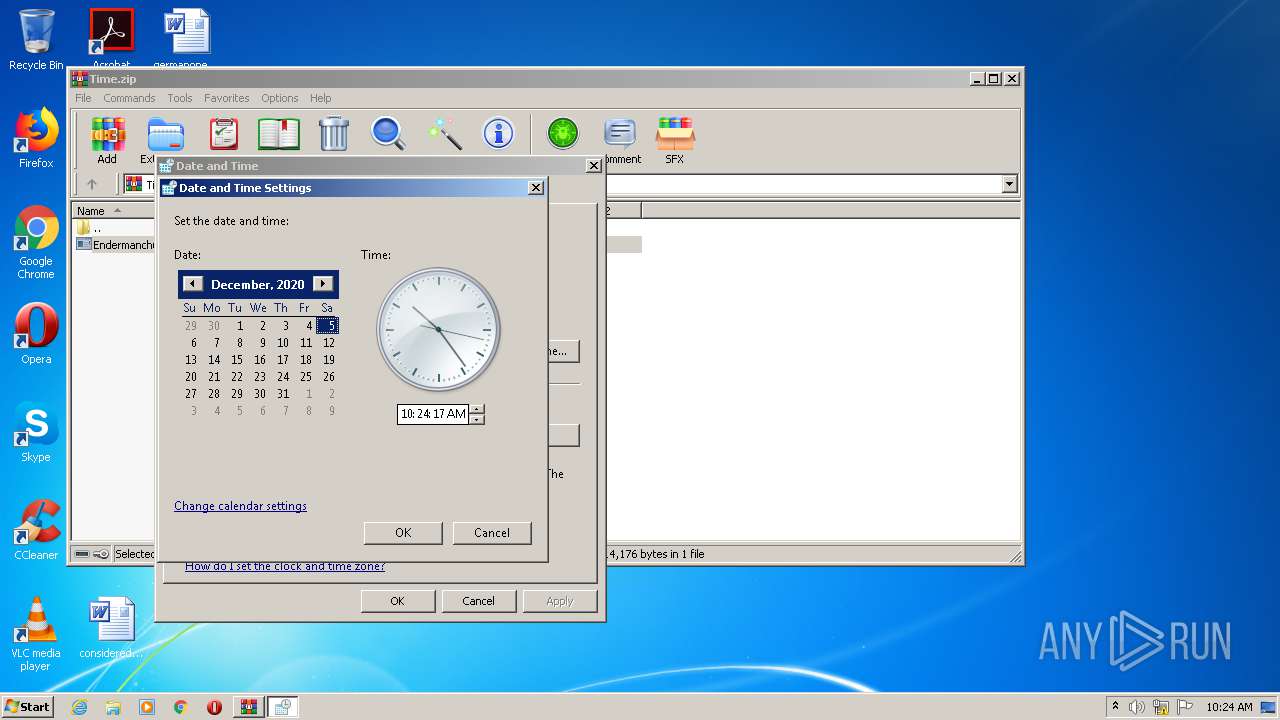
| Analysis date: | December 05, 2020, 10:23:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 9418544D8CF5E54F71381E0CBBF71F90 |
| SHA1: | 765B2B506571EEBB0C7057F8EAE4DF19A02DF227 |
| SHA256: | 97B8F7FE0101ACC64E962067791943FC8182ACA1A692B18B88247D984212C513 |
| SSDEEP: | 1536:QtTGxuUAKTHFoNq+ZyO1e4YuO0U0MUy98O+SSjwEHwm/ScmIJkf1GZKejR7p6TYT:wGp/THFolyL5IndSSUyZmIJkaEYZuMLP |
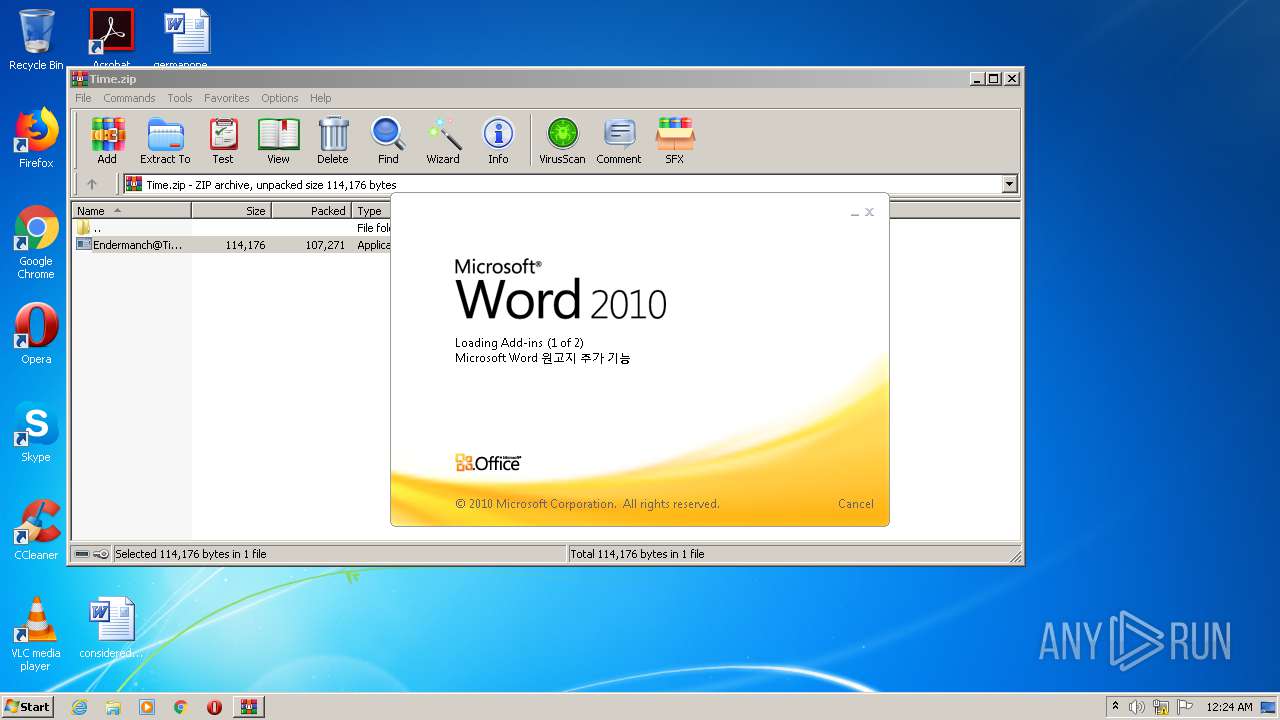
MALICIOUS
Application was dropped or rewritten from another process
- Endermanch@Time.exe (PID: 3800)
- Endermanch@Time.exe (PID: 2604)
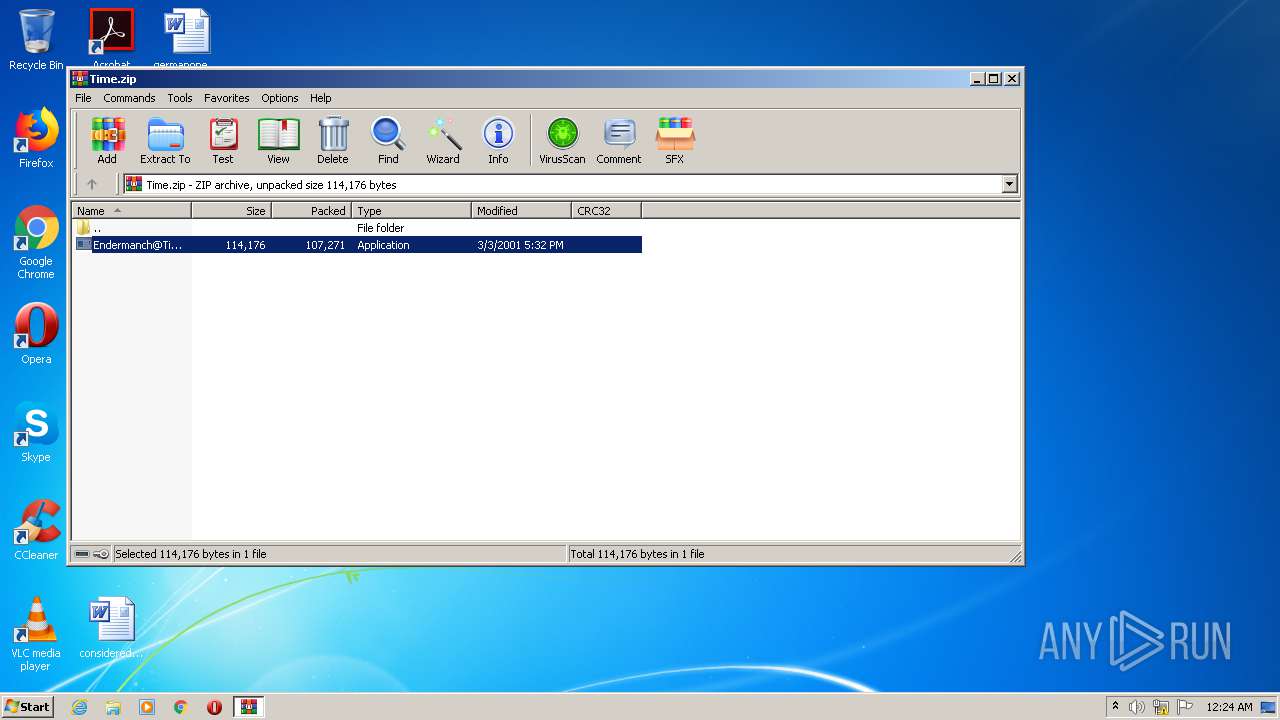
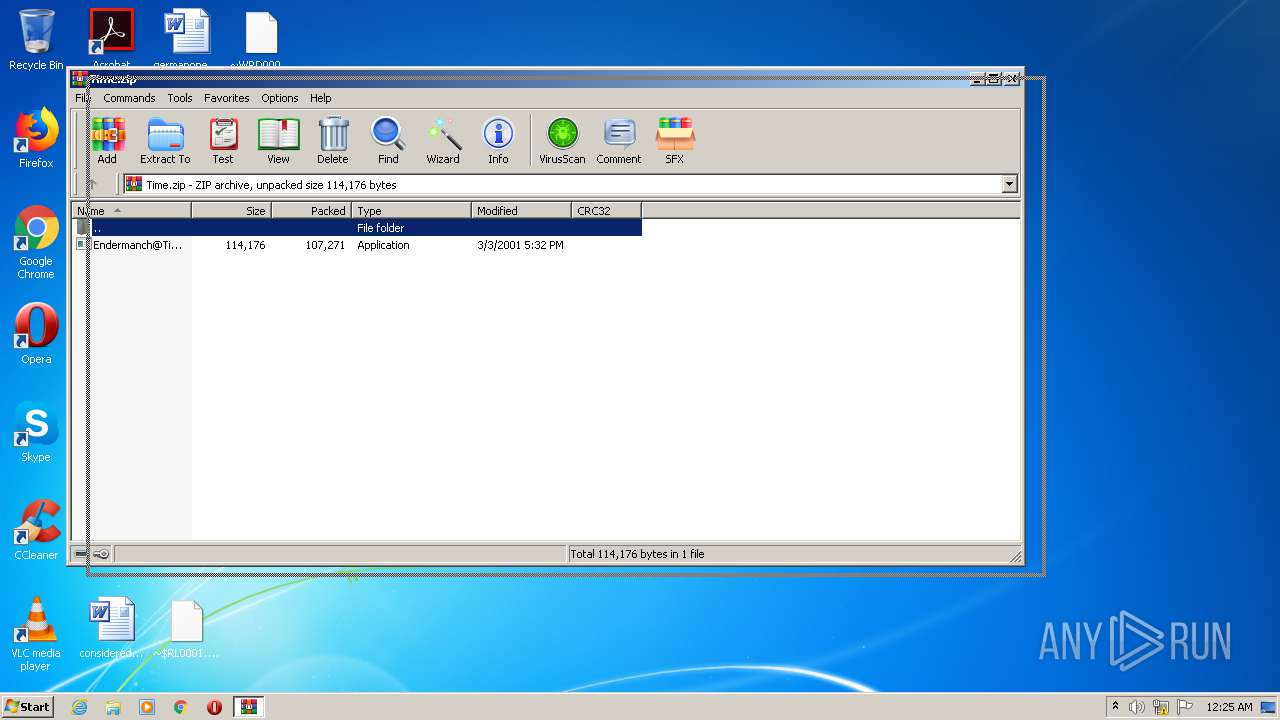
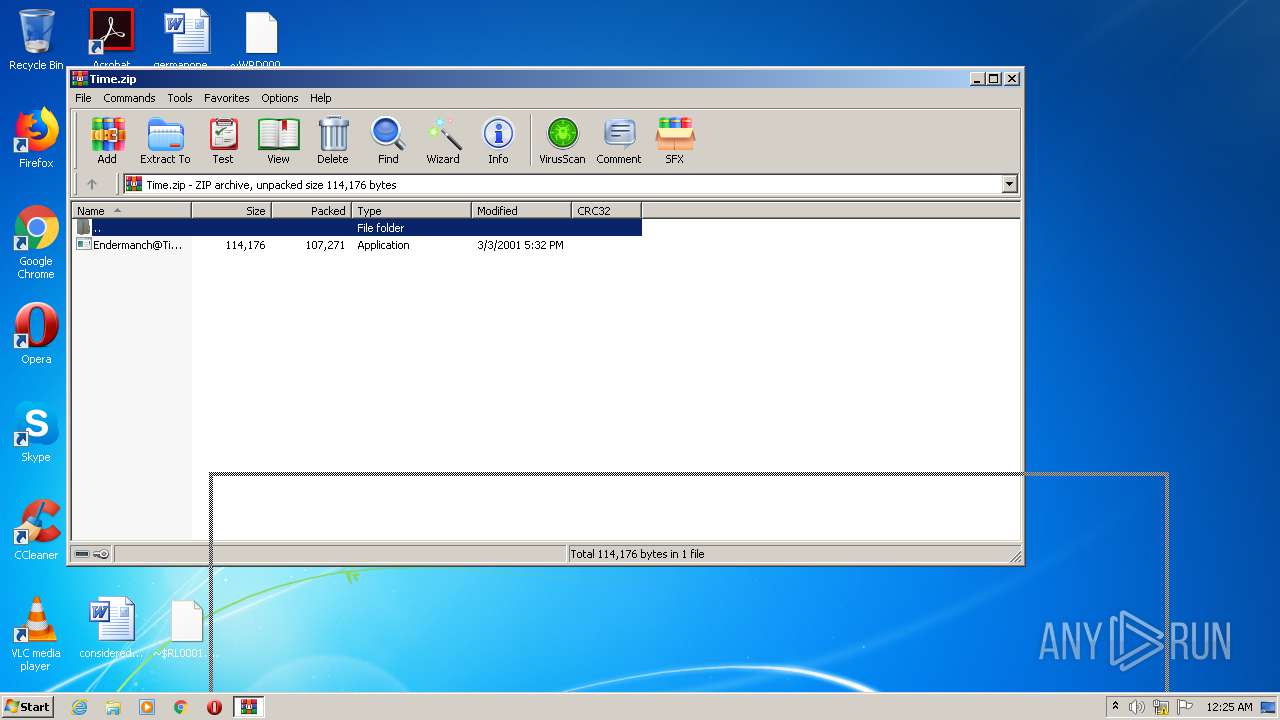
Drops executable file immediately after starts
- WinRAR.exe (PID: 948)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 948)
Drops a file with too old compile date
- WinRAR.exe (PID: 948)
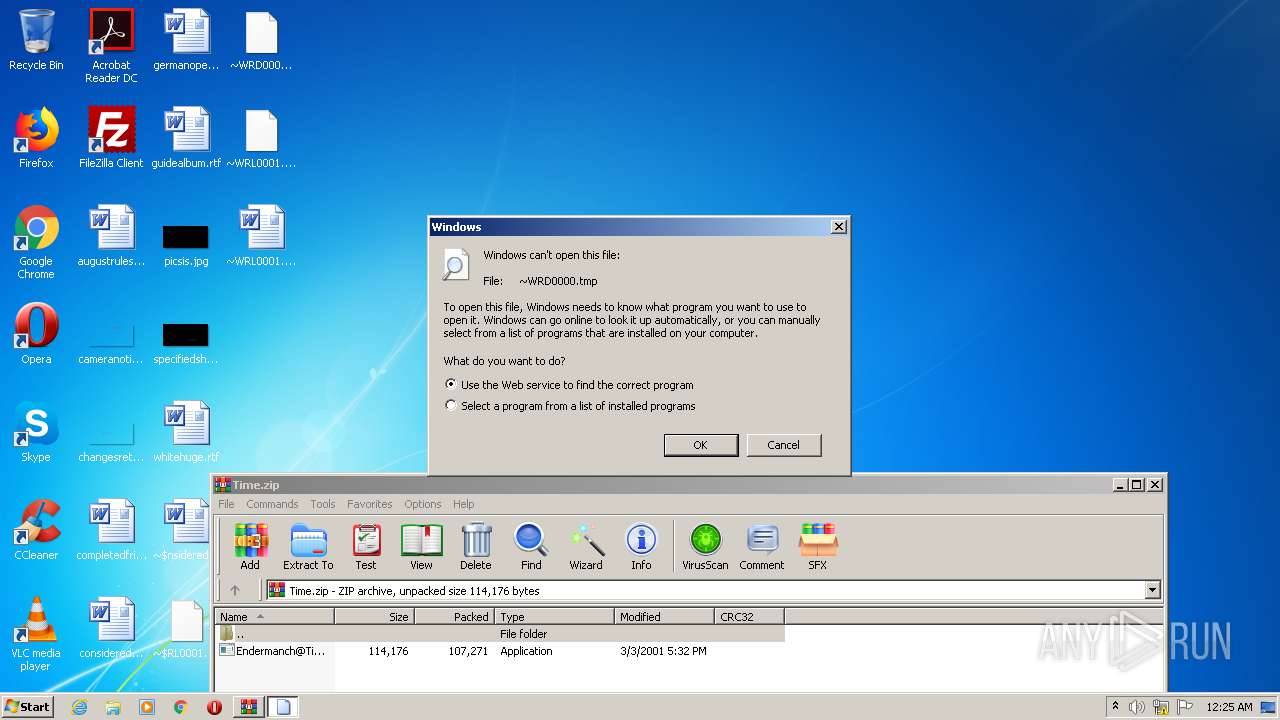
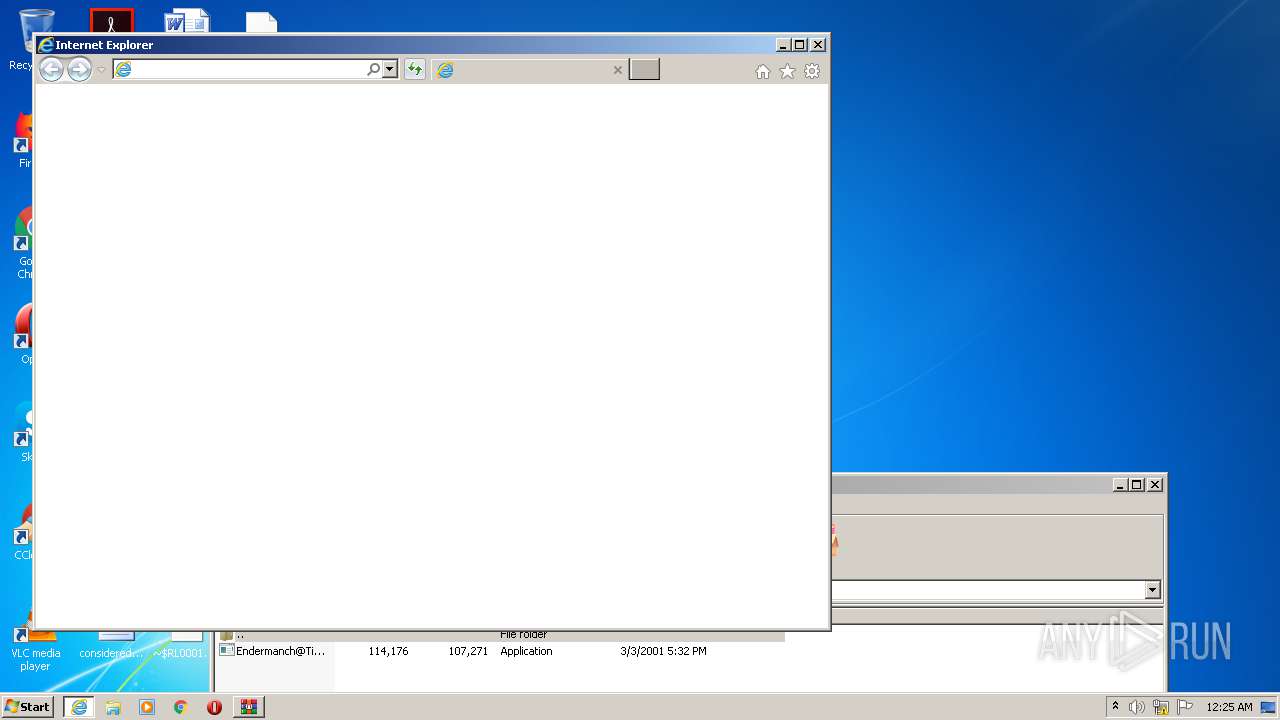
Starts Internet Explorer
- rundll32.exe (PID: 3824)
Executed via COM
- DllHost.exe (PID: 2684)
Uses RUNDLL32.EXE to load library
- control.exe (PID: 3800)
INFO
Application launched itself
- iexplore.exe (PID: 2788)
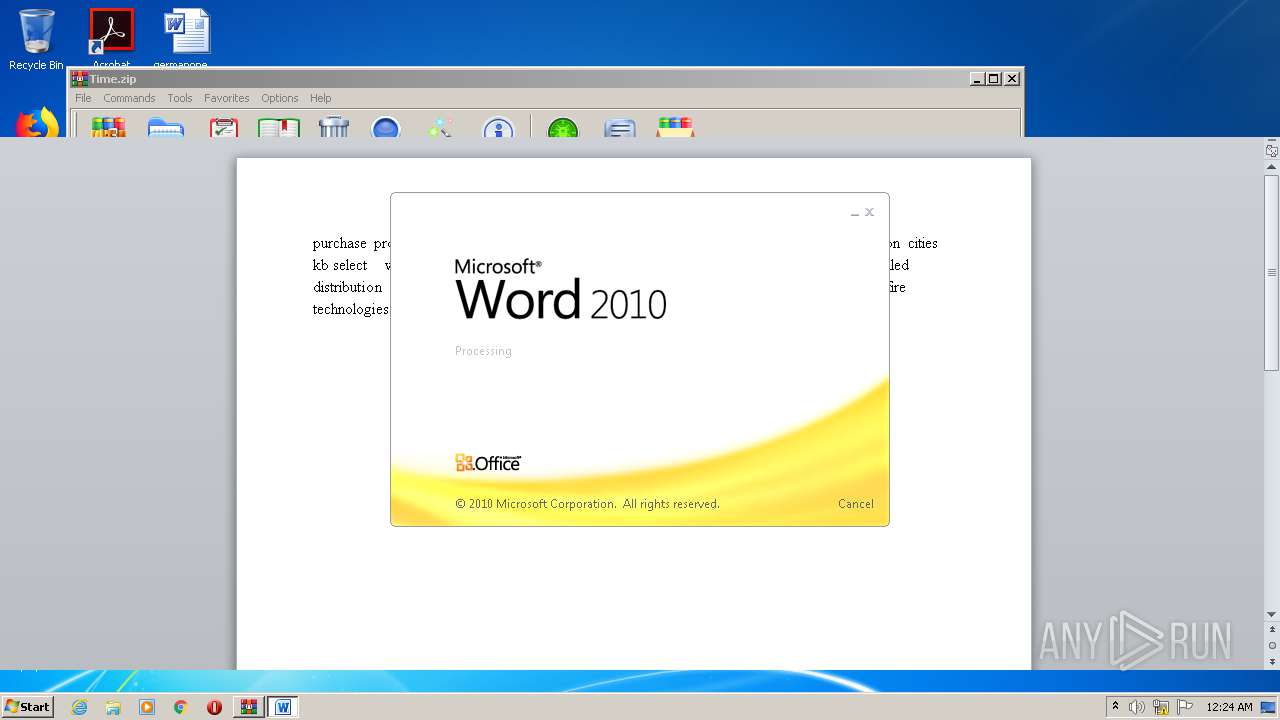
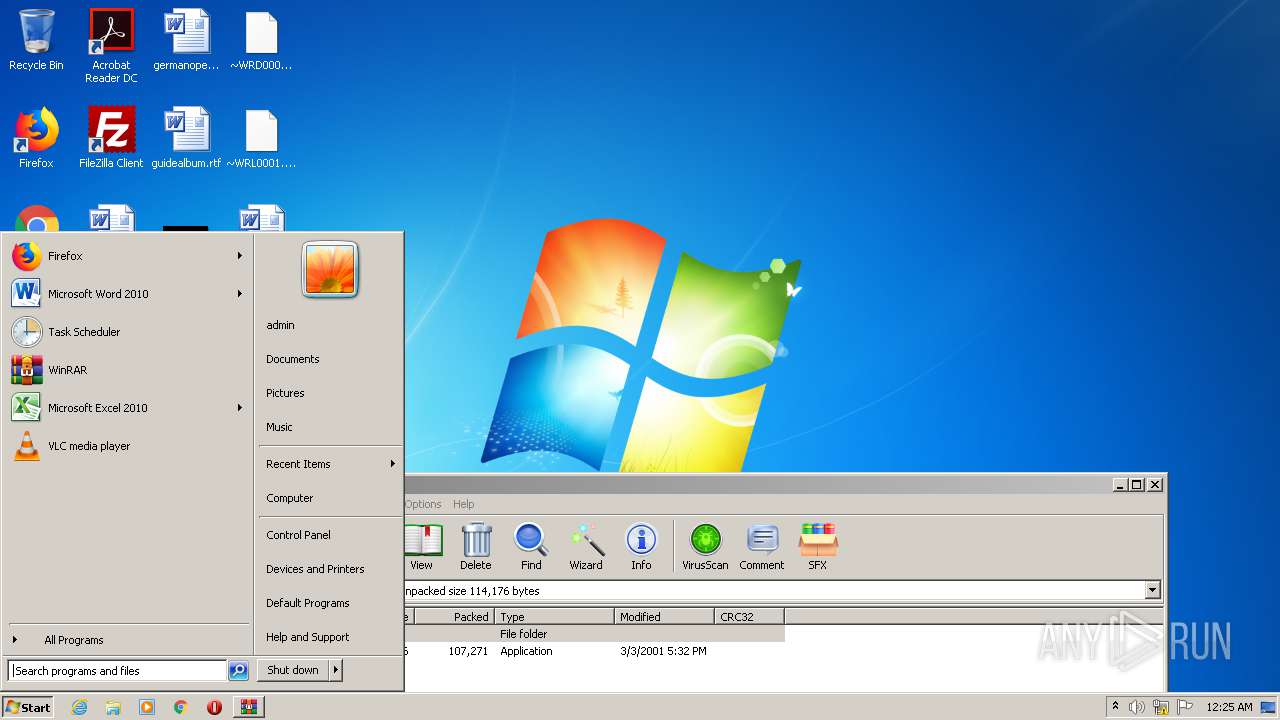
Manual execution by user
- control.exe (PID: 3800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
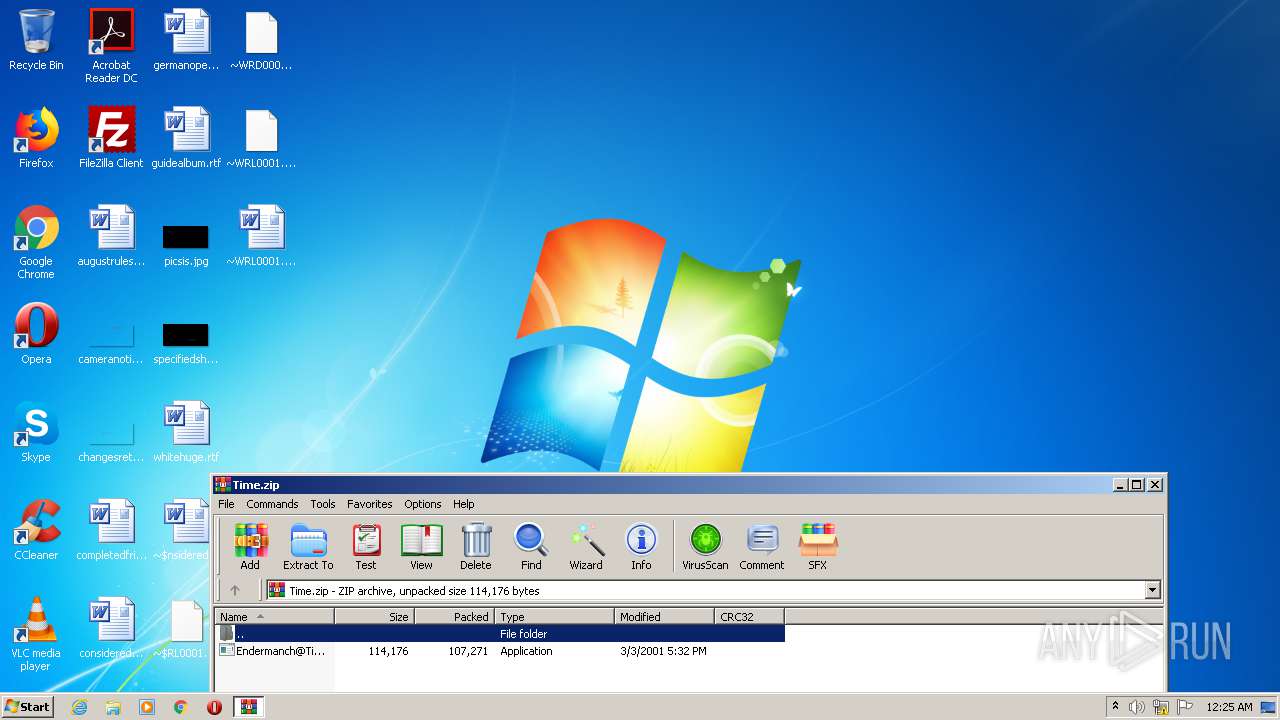
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2001:03:03 20:32:06 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 107271 |
| ZipUncompressedSize: | 114176 |
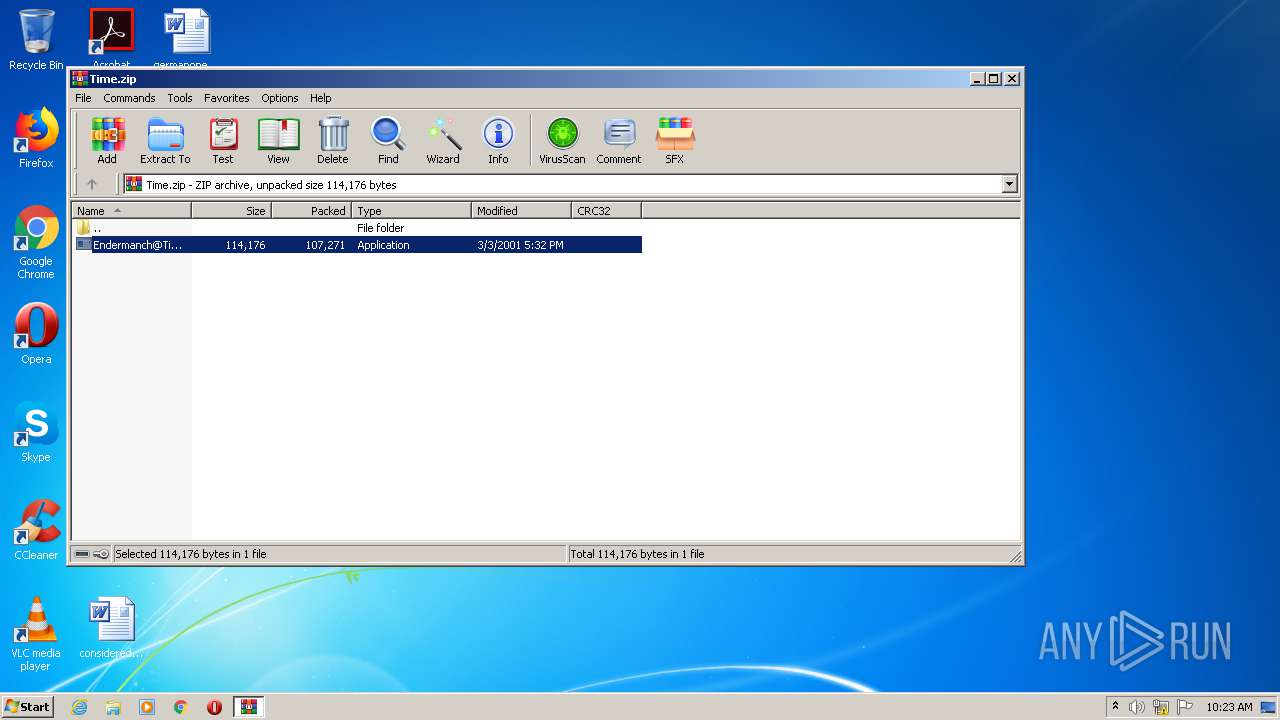
| ZipFileName: | Endermanch@Time.exe |
Total processes
54
Monitored processes
11
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
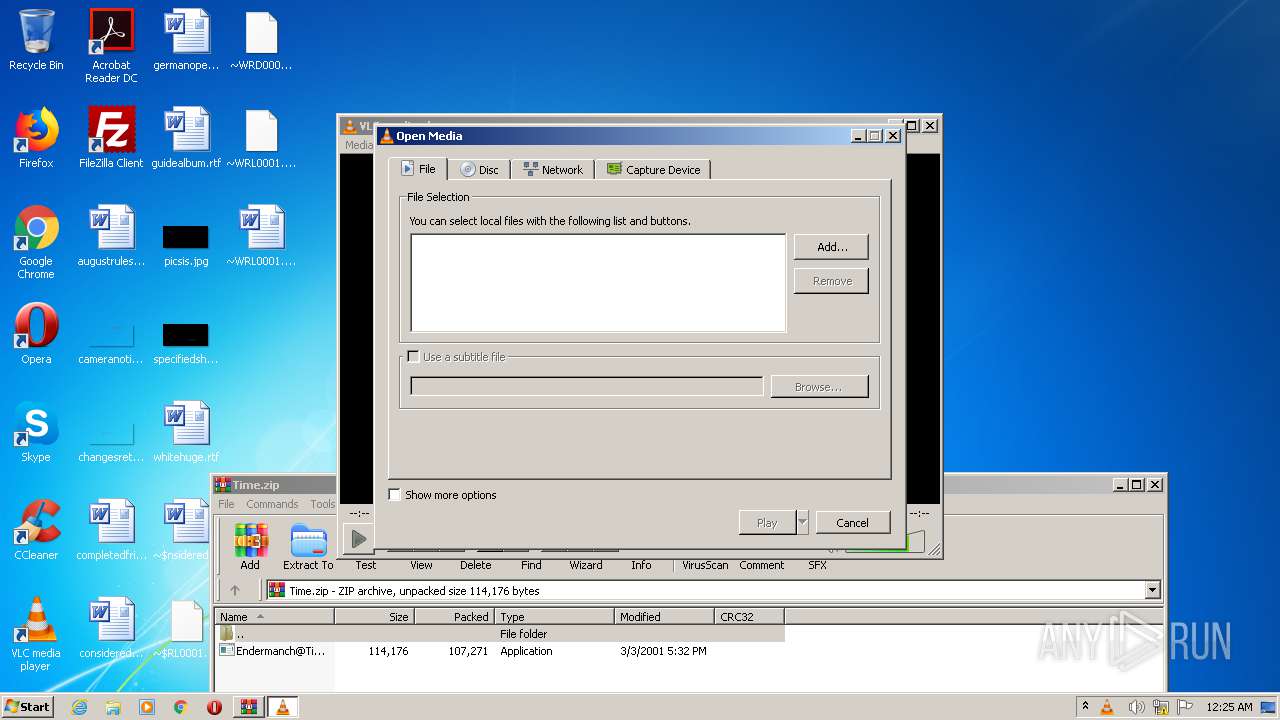
| 948 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Time.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1073807364 Version: 5.60.0 Modules
| |||||||||||||||
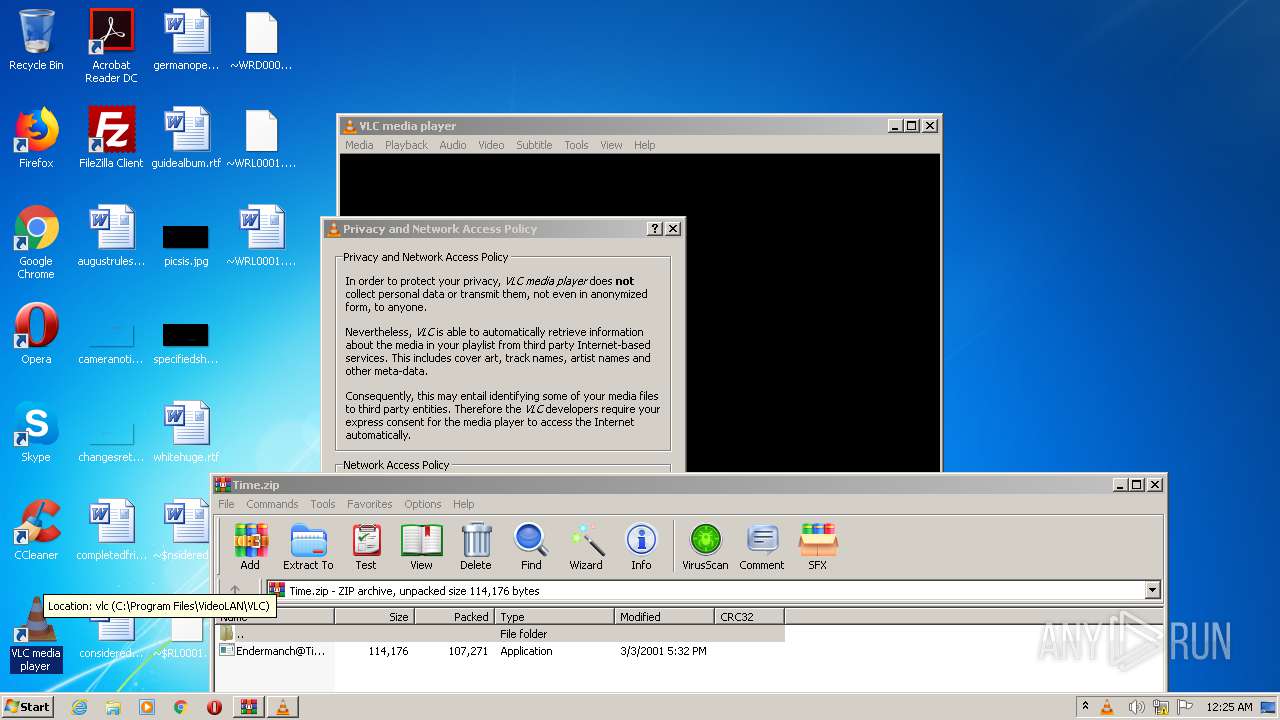
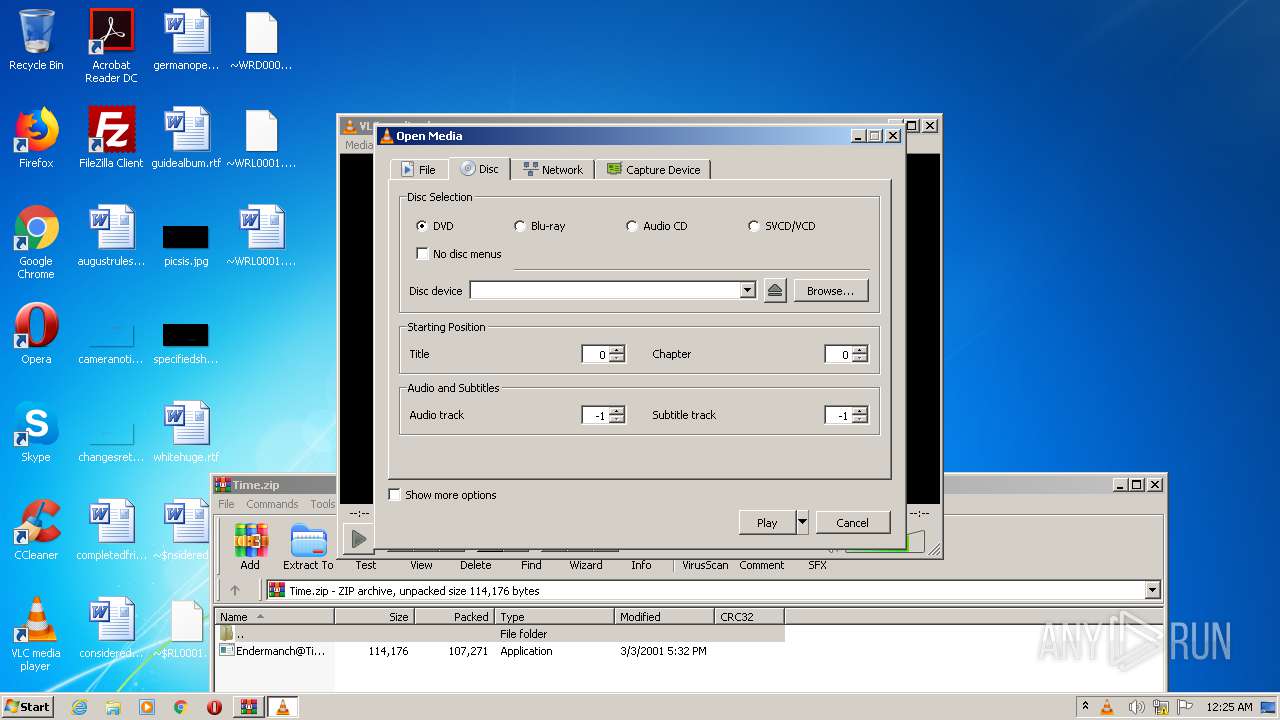
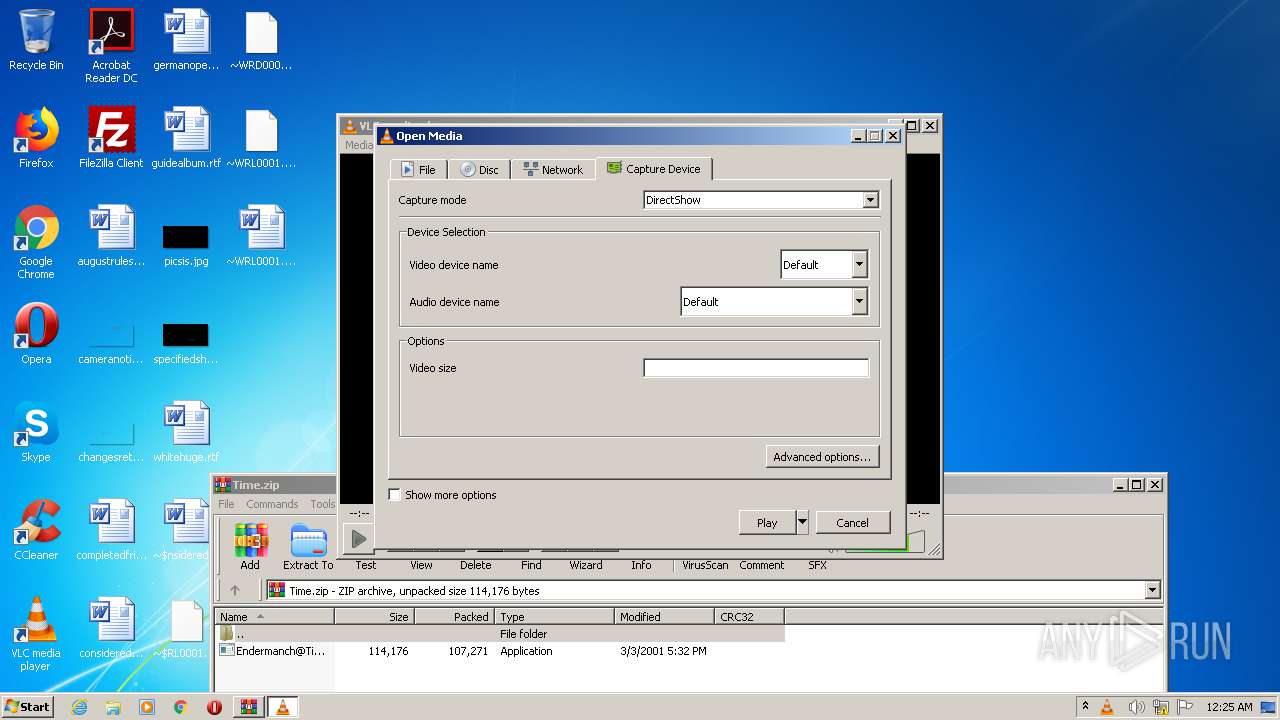
| 2084 | "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 2148 | "C:\Windows\system32\rundll32.exe" Shell32.dll,Control_RunDLL "C:\Windows\system32\timedate.cpl", | C:\Windows\system32\rundll32.exe | — | control.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
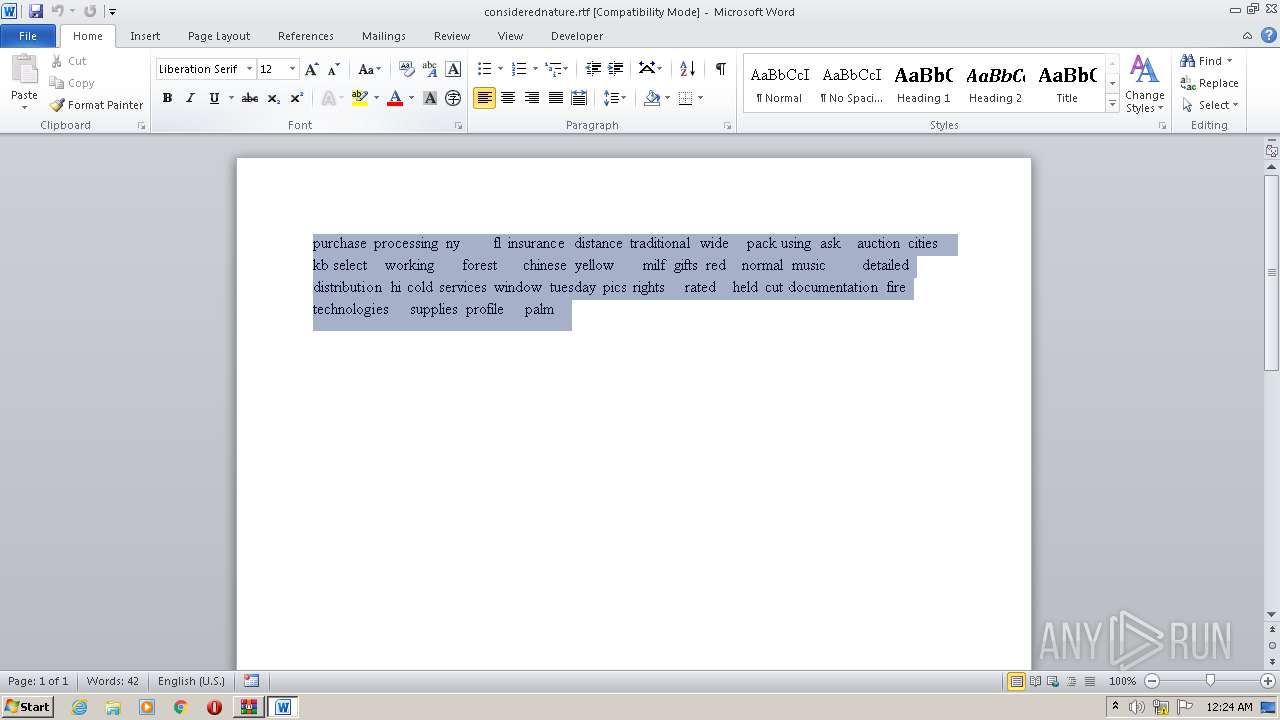
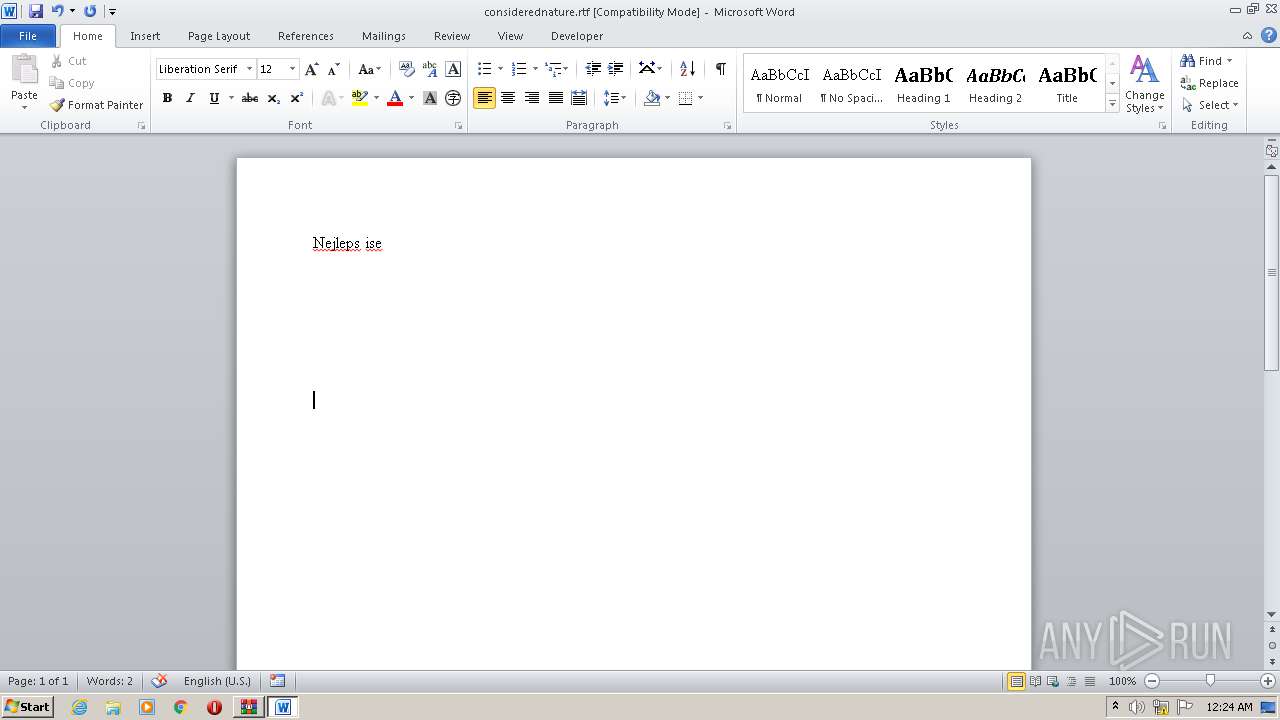
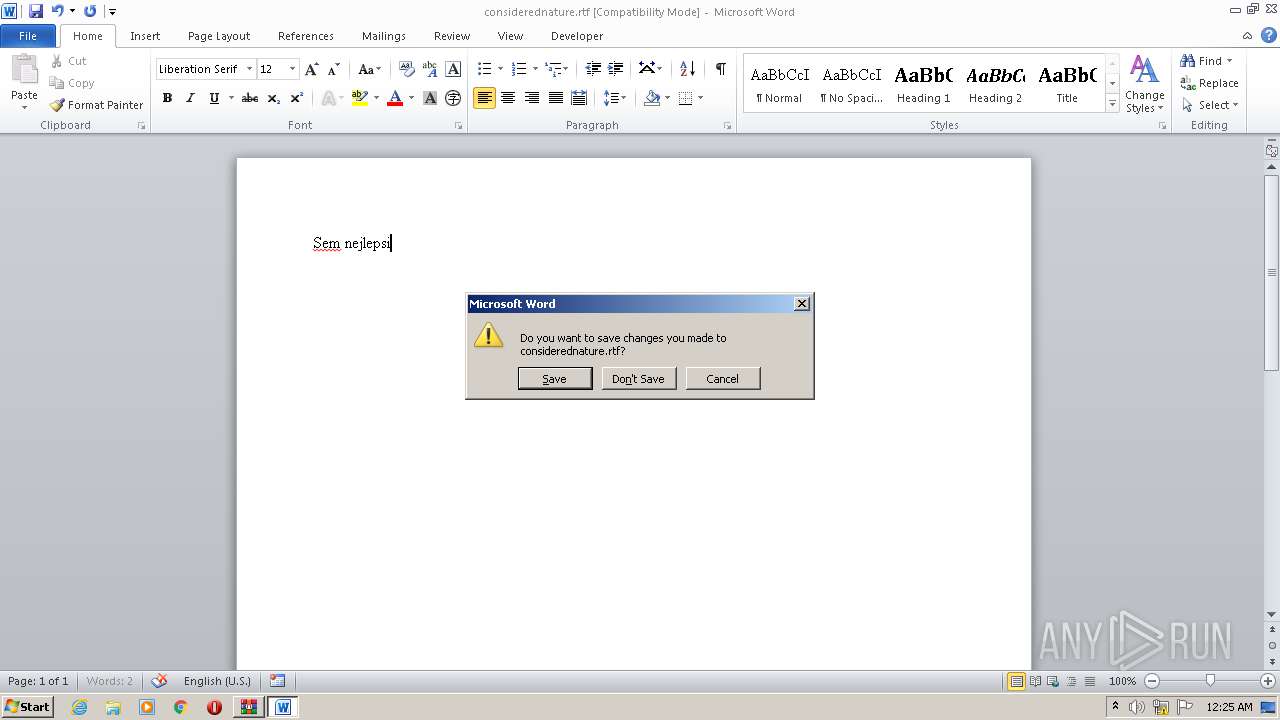
| 2496 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\considerednature.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2604 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb948.14989\Endermanch@Time.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb948.14989\Endermanch@Time.exe | — | WinRAR.exe | |||||||||||
User: admin Company: RJL Software, Inc. Integrity Level: MEDIUM Description: Randomly changes the time Exit code: 1073807364 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2684 | C:\Windows\system32\DllHost.exe /Processid:{9DF523B0-A6C0-4EA9-B5F1-F4565C3AC8B8} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 2760 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2788 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=tmp | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1073807364 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3800 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb948.19842\Endermanch@Time.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb948.19842\Endermanch@Time.exe | — | WinRAR.exe | |||||||||||
User: admin Company: RJL Software, Inc. Integrity Level: MEDIUM Description: Randomly changes the time Exit code: 1073807364 Version: 1.0.0.0 | |||||||||||||||
| 3800 | "C:\Windows\System32\control.exe" "C:\Windows\system32\timedate.cpl", | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
482
Read events
464
Write events
18
Delete events
0
Modification events
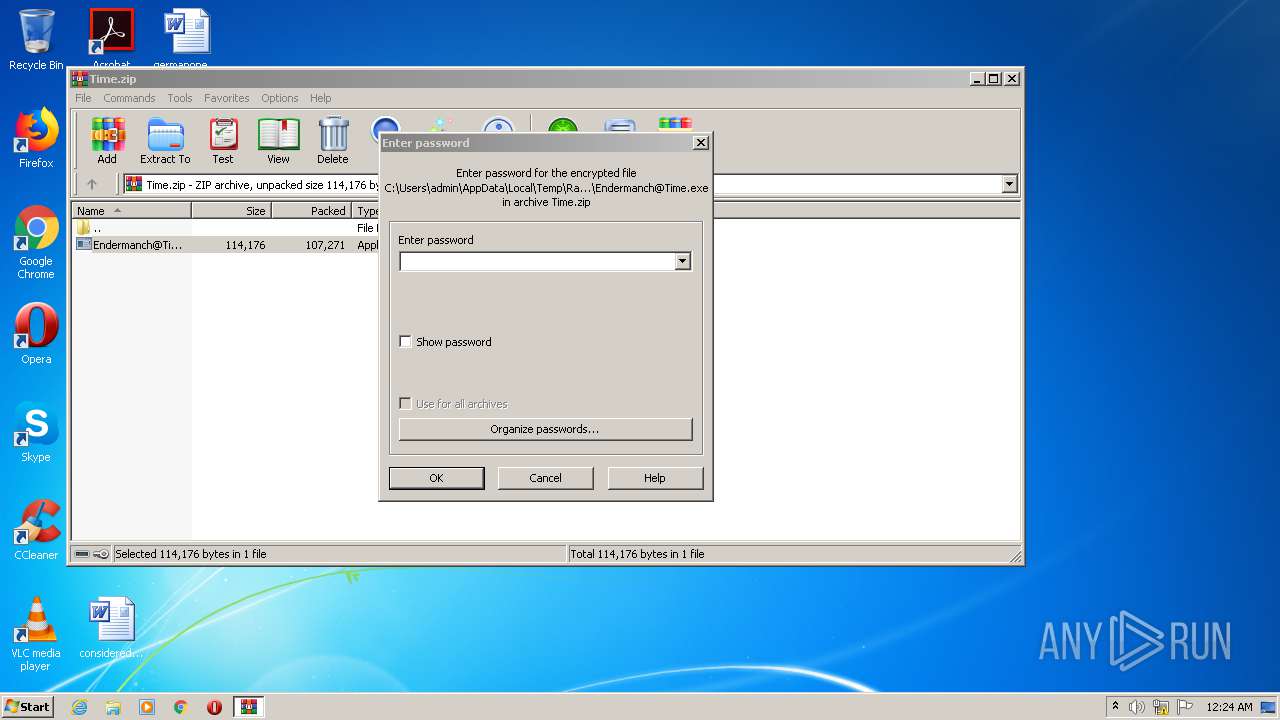
| (PID) Process: | (948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (948) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Time.zip | |||
| (PID) Process: | (948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
6
Text files
18
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD661.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\Desktop\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{A474E4E4-15F6-4A74-A906-BE38AD531FFB}.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{5939D9DC-5011-4382-A94E-A41CF9F8B41B}.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{564F50D7-5101-4AEC-BCB7-531E5F835634}.tmp | — | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab833B.tmp | — | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab833C.tmp | — | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar833D.tmp | — | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar833E.tmp | — | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1AAELD7A.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
10
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1044 | svchost.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/fd/ls/l?IG=3A6BA0369BF84EC0BB15D81927D02BA7&CID=2433DAD7968F6C3D13CCD540977A6D94&Type=Event.CPT&DATA={"pp":{"S":"A","FC":109,"BC":109,"SE":-1,"TC":-1,"H":156,"BP":375,"CT":3844,"IL":11},"ad":[-1,-1,776,528,1164,2663,0]}&P=SERP&DA=DUB02 | US | — | — | whitelisted |
1044 | svchost.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/rs/5s/kh/ic/eF3rIdIG4fsLyPy7mzgRnjCDKIA.png | US | image | 11.8 Kb | whitelisted |
1044 | svchost.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/rp/5rqGloMo94v3vwNVR5OsxDNd8d0.svg | US | image | 461 b | whitelisted |
1044 | svchost.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/sa/simg/favicon-2x.ico | US | image | 4.19 Kb | whitelisted |
1044 | svchost.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/search?form=MO0035&q=open+tmp+file | US | html | 211 Kb | whitelisted |
2760 | iexplore.exe | GET | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=tmp | US | — | — | whitelisted |
2788 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2760 | iexplore.exe | GET | 301 | 92.122.188.53:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=tmp | unknown | — | — | whitelisted |
1044 | svchost.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/rp/ZricD7XDh2XWjN68qgUU8lqqArQ.png | US | image | 609 b | whitelisted |
1044 | svchost.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/rp/Jl2vUSlEIqWjk-99MuYp4W74zvQ.svg | US | image | 1.49 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2760 | iexplore.exe | 23.43.214.226:80 | go.microsoft.com | Akamai International B.V. | US | malicious |
2788 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2760 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2788 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2760 | iexplore.exe | 92.122.188.53:80 | shell.windows.com | NTT America, Inc. | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | dshow interface error: no video capture device was detected
|