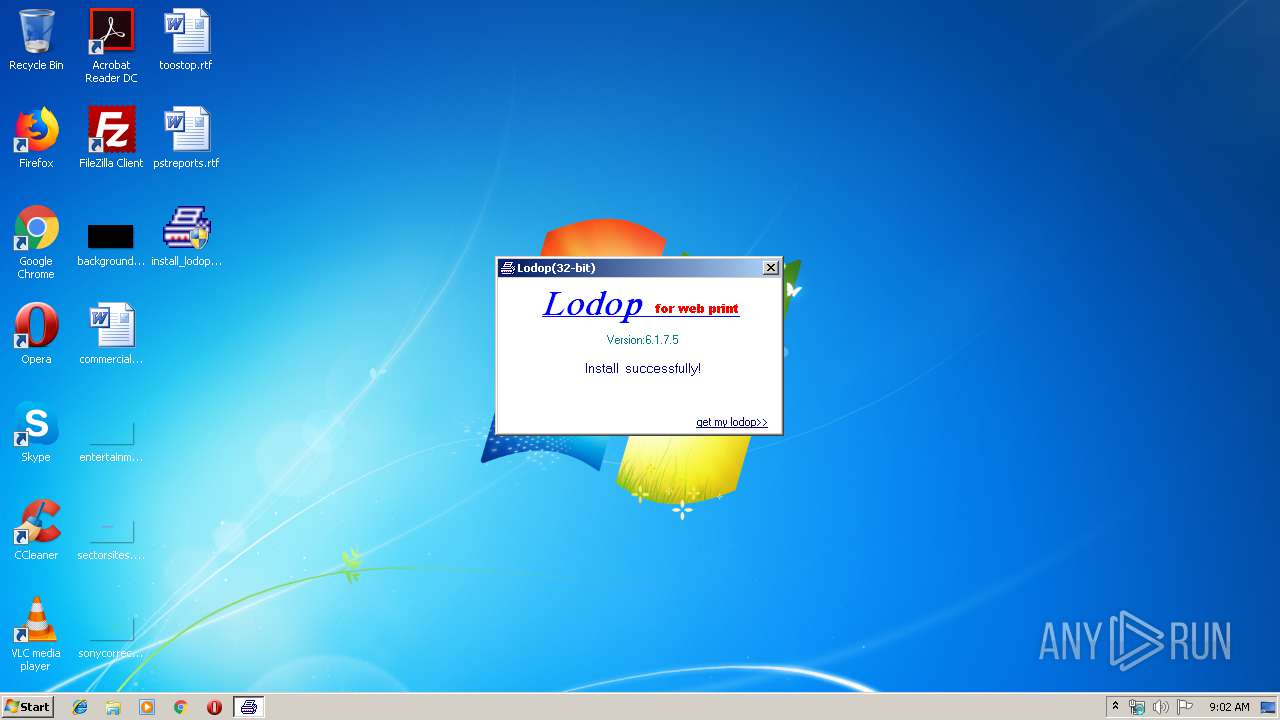
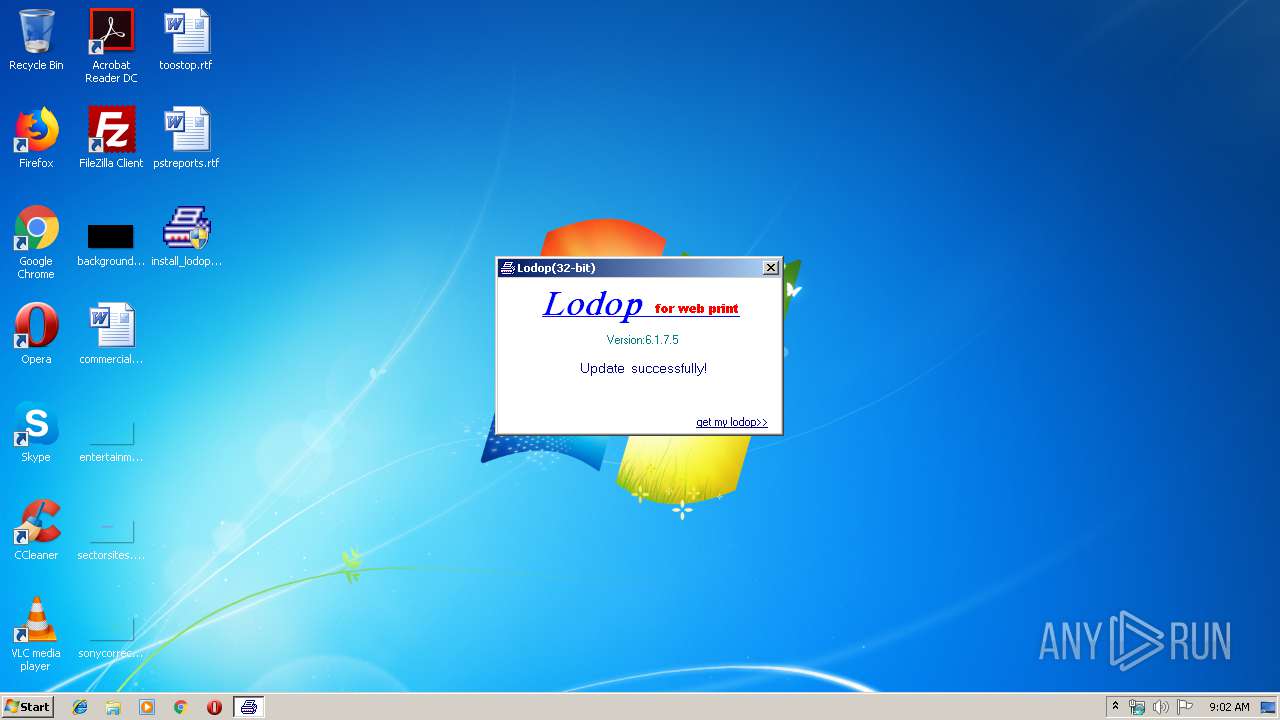
| File name: | install_lodop32.exe |
| Full analysis: | https://app.any.run/tasks/6e242940-0647-4165-8987-cca62ab7ad0c |
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2019, 09:01:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 8F5C20472803B32102DD3E5D17F6F504 |
| SHA1: | C3A32AC5494B4CA19C5558A8BE8E9FDF1E3E1CAC |
| SHA256: | 9788A86209D8463DE9DA92F71131A2416587371945EC911EFBF09C30731EA334 |
| SSDEEP: | 49152:tXi++t3L914D1Mv9soAEUuFD4PB17BqgLtwKj56xL2XlPO0yfrib4YIPy:c5EK7AEdFD4PBdBqowKjOLIPO0grwkPy |
MALICIOUS
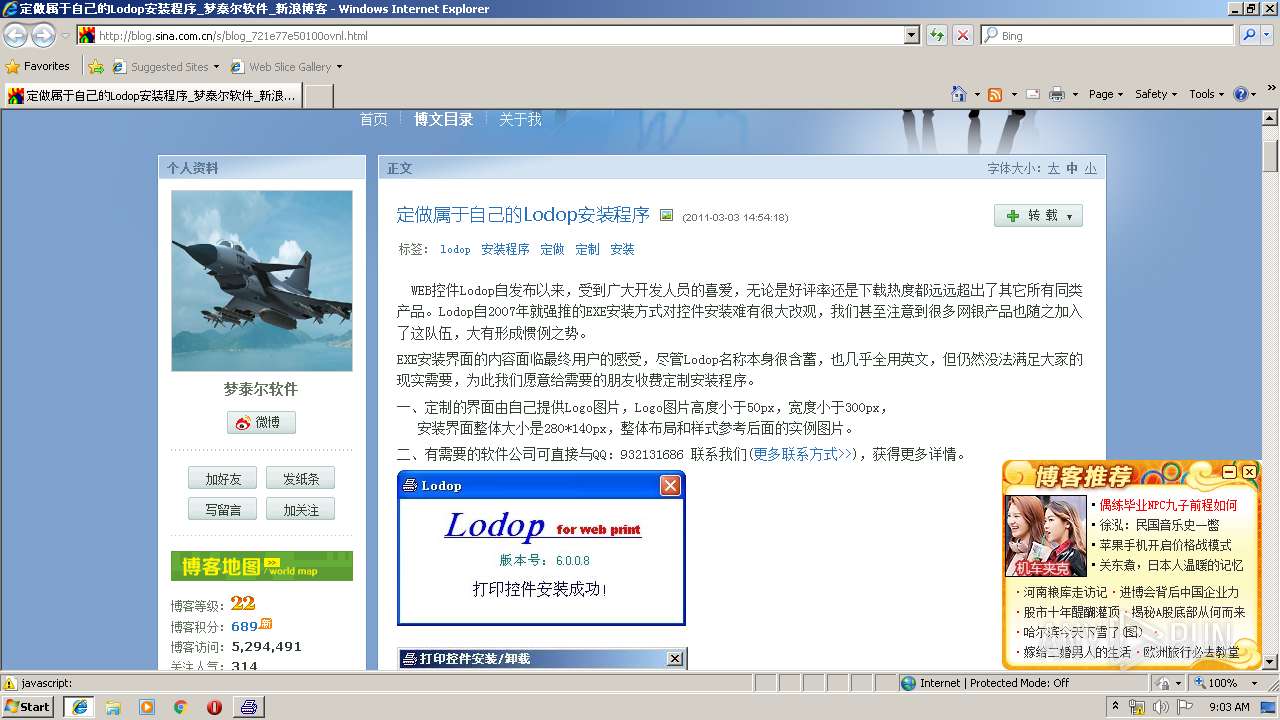
Loads dropped or rewritten executable
- install_lodop32.exe (PID: 3592)
- install_lodop32.exe (PID: 1404)
SUSPICIOUS
Creates files in the program directory
- install_lodop32.exe (PID: 3592)
- install_lodop32.exe (PID: 1404)
Executable content was dropped or overwritten
- install_lodop32.exe (PID: 3592)
- install_lodop32.exe (PID: 1404)
Creates files in the user directory
- install_lodop32.exe (PID: 3592)
- install_lodop32.exe (PID: 1404)
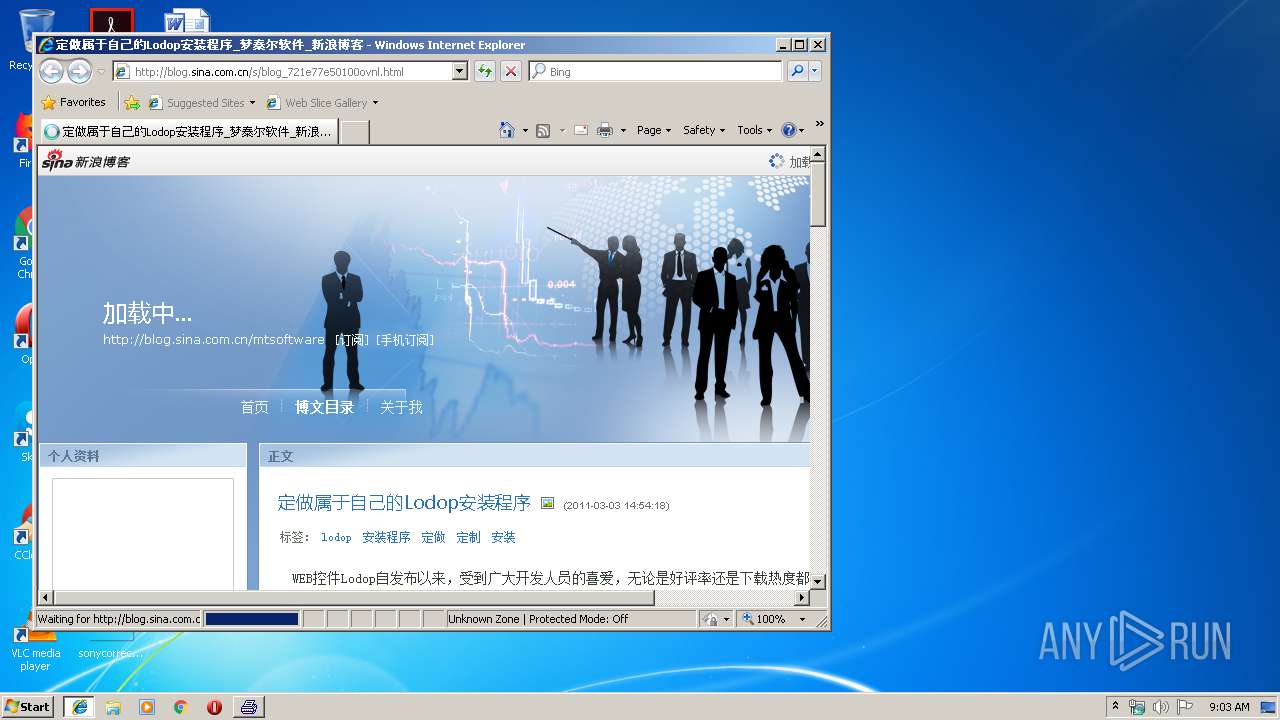
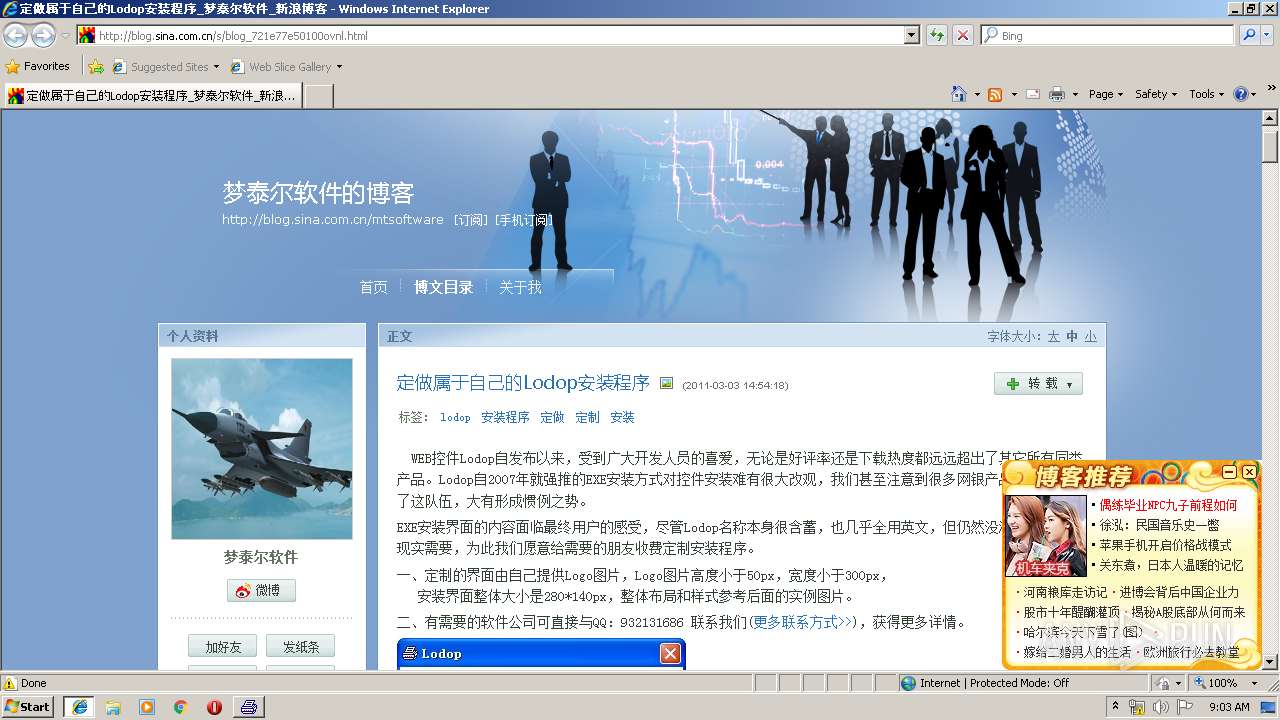
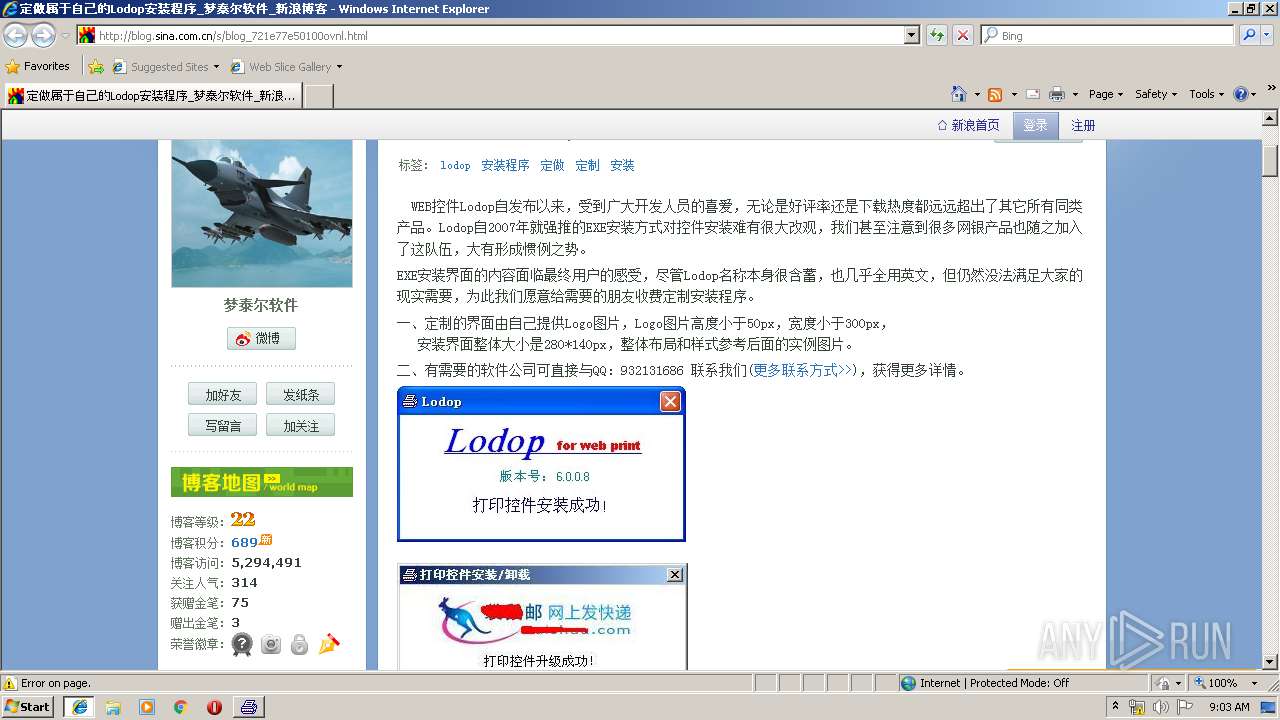
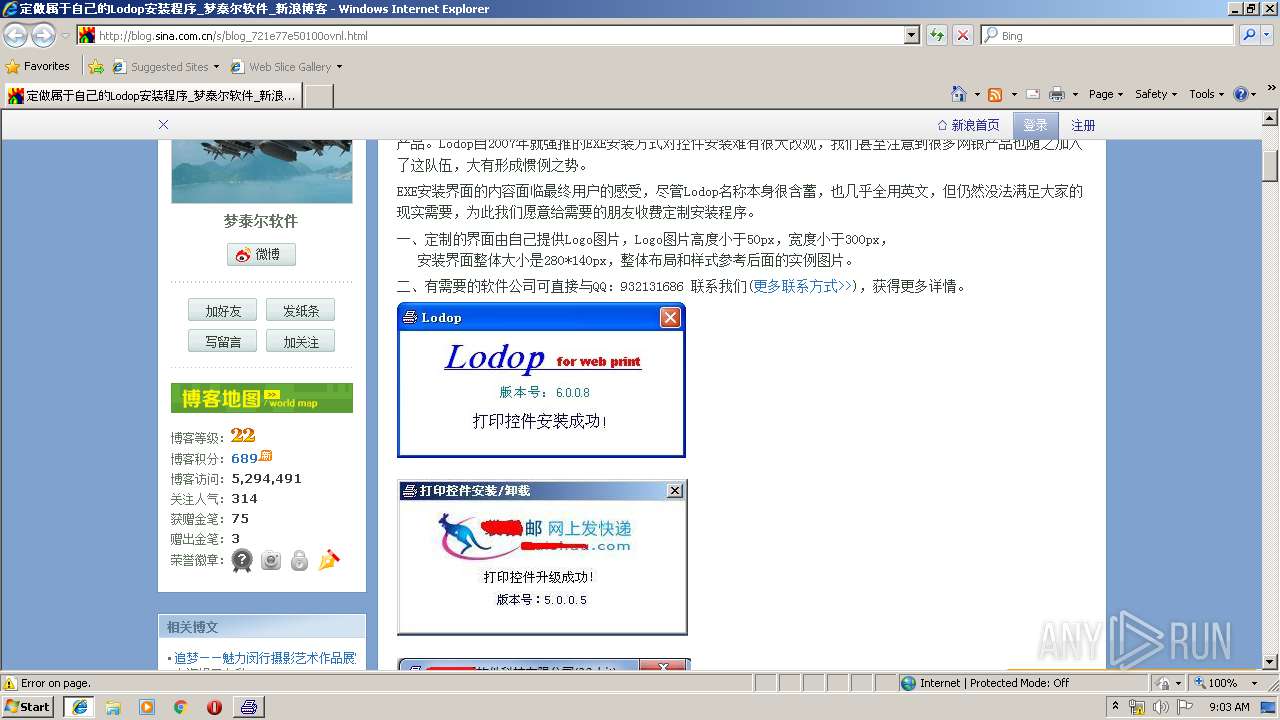
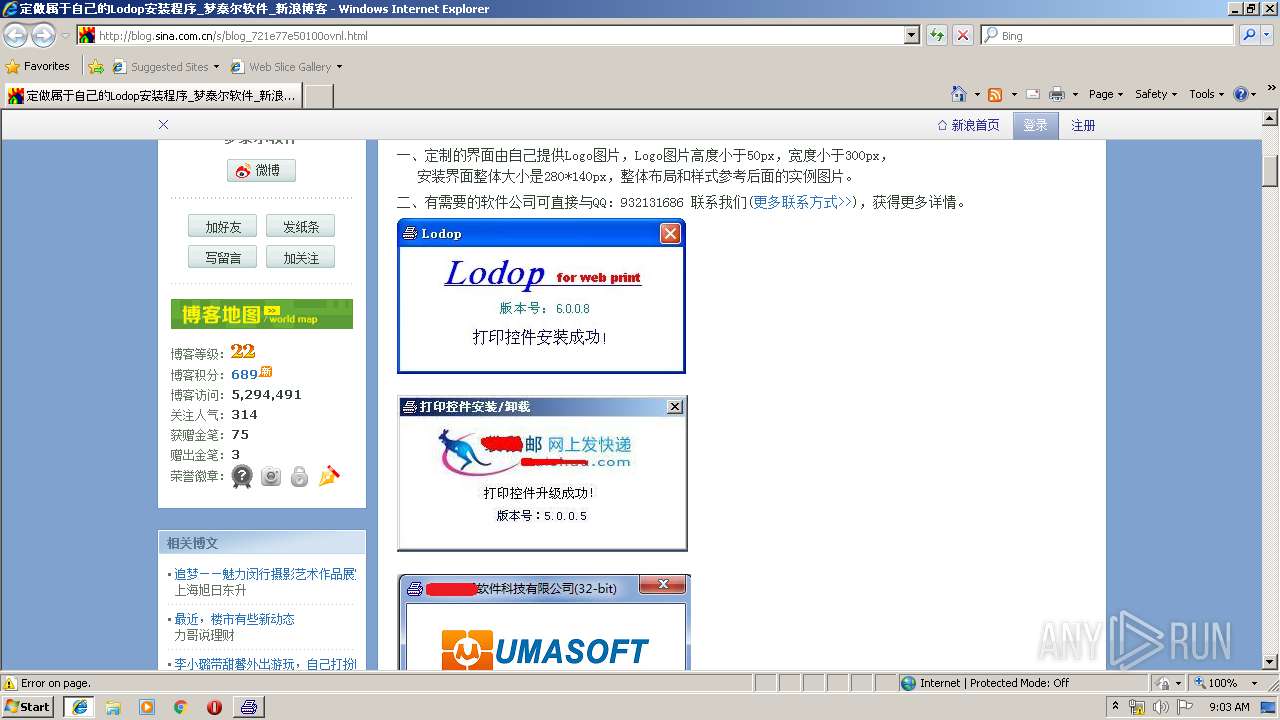
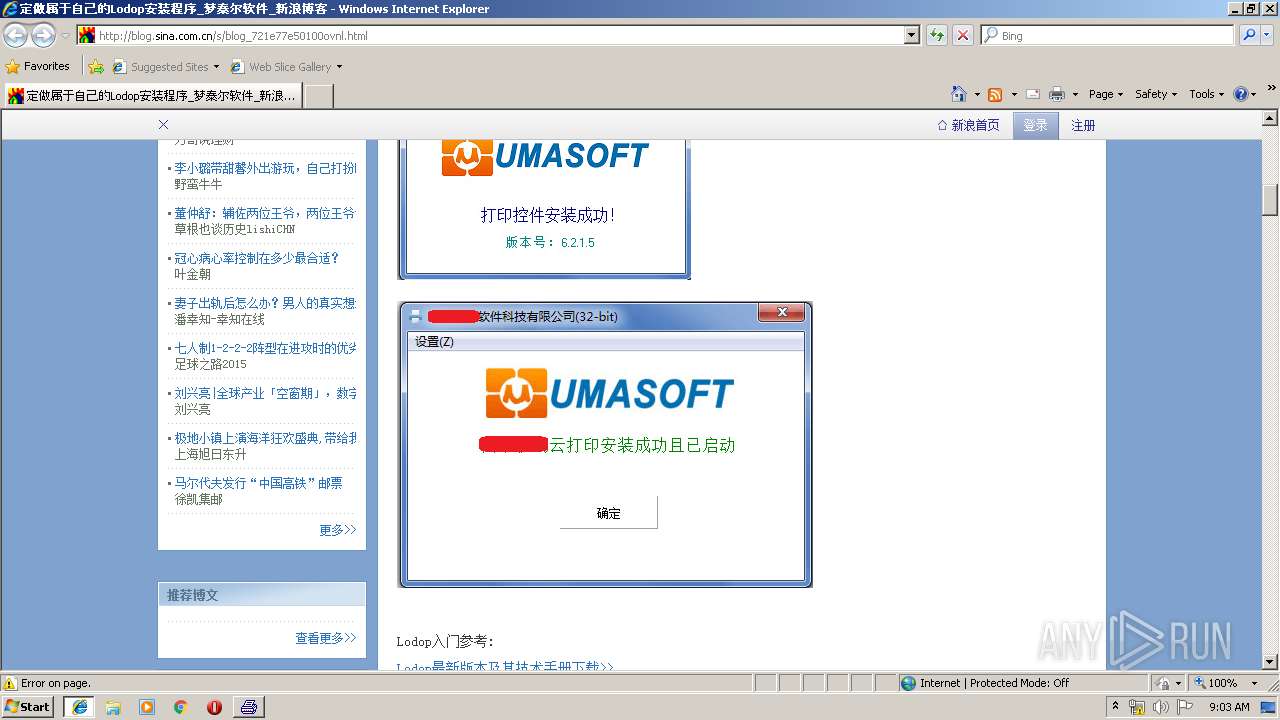
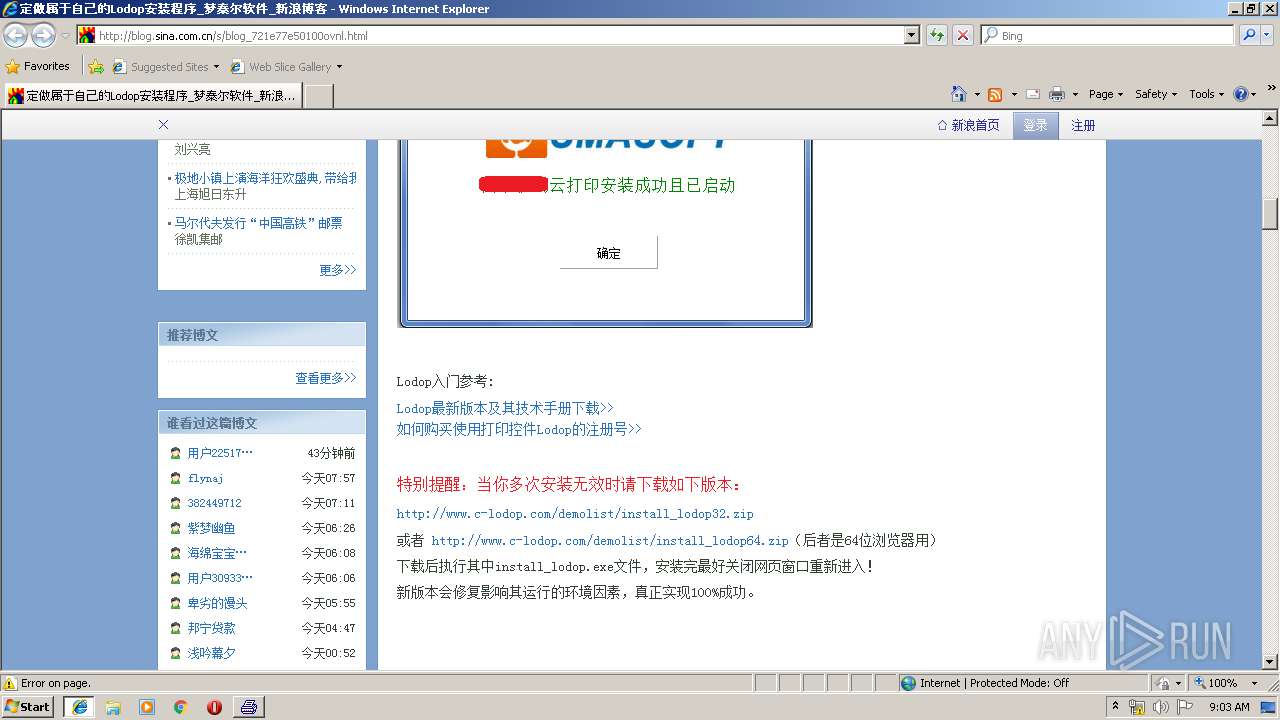
Starts Internet Explorer
- install_lodop32.exe (PID: 1404)
Check for Java to be installed
- iexplore.exe (PID: 3780)
INFO
Manual execution by user
- install_lodop32.exe (PID: 1404)
- install_lodop32.exe (PID: 3336)
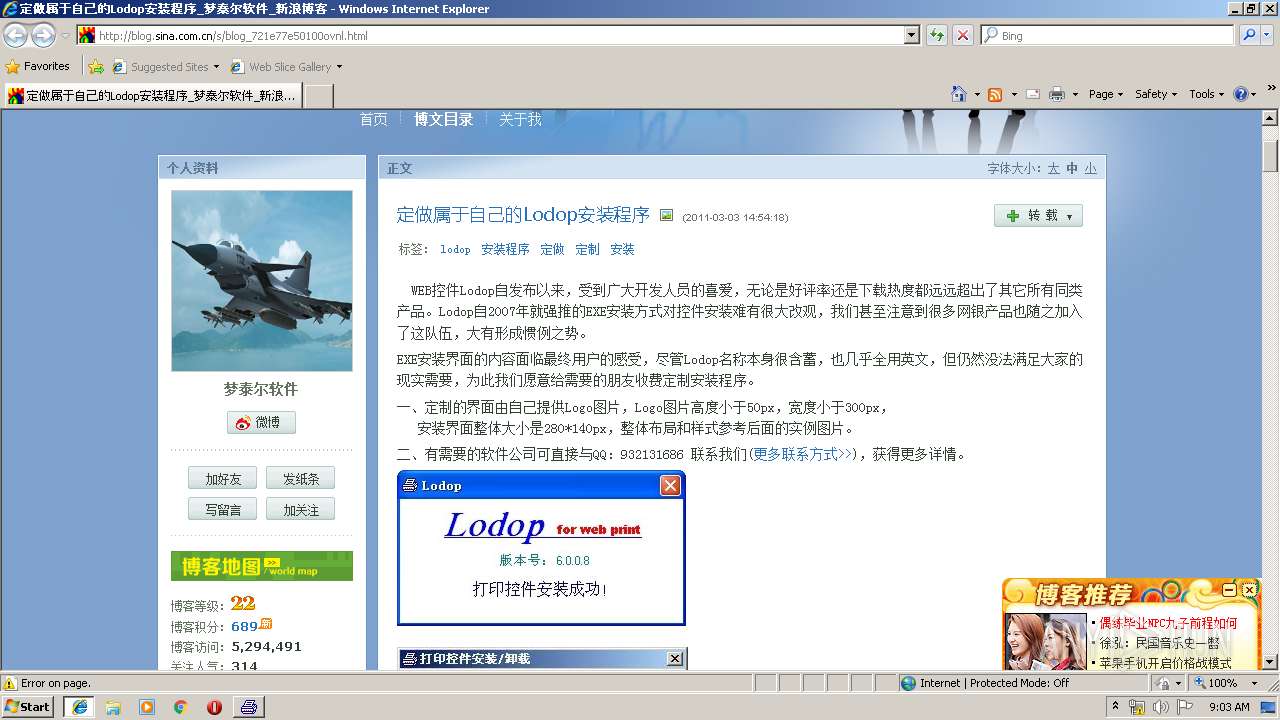
Changes internet zones settings
- iexplore.exe (PID: 3780)
Reads Internet Cache Settings
- iexplore.exe (PID: 2796)
Reads settings of System Certificates
- iexplore.exe (PID: 2796)
Creates files in the user directory
- iexplore.exe (PID: 2796)
- iexplore.exe (PID: 3780)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2796)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2796)
Changes settings of System certificates
- iexplore.exe (PID: 2796)
Reads internet explorer settings
- iexplore.exe (PID: 2796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:03:20 04:18:53+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 2387968 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 667648 |
| EntryPoint: | 0x2ea4e0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
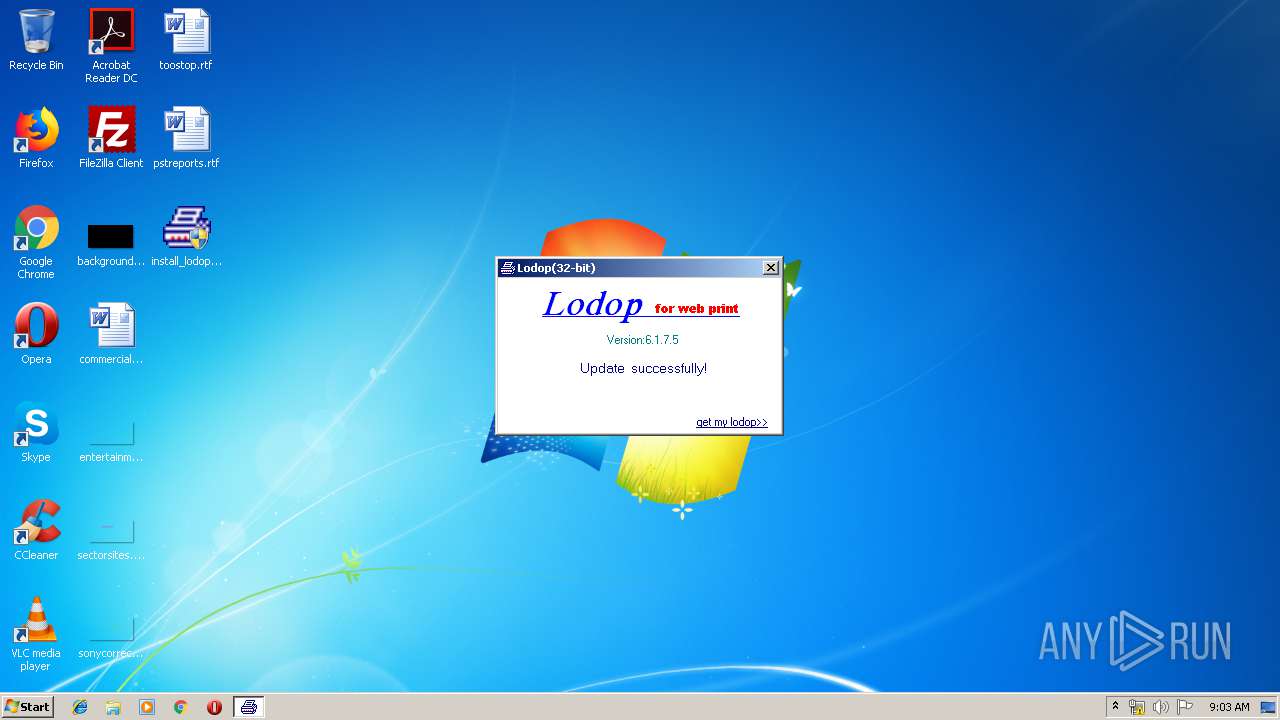
| FileVersionNumber: | 6.1.7.5 |
| ProductVersionNumber: | 6.1.7.5 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | MTSoftware(CN) |
| FileDescription: | Print Control Lodop(32-bit) Install |
| FileVersion: | 6.1.7.5 |
| InternalName: | Lodop(劳道谱) Install |
| LegalCopyright: | 梦泰尔软件工作室 MTSoftware(CN) |
| LegalTrademarks: | Lodop |
| OriginalFileName: | install_lodop32.exe |
| ProductName: | Lodop(劳道谱) Install |
| ProductVersion: | 6.1 |
| Comments: | 梦泰尔软件工作室 MTSoftware(CN) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Mar-2014 03:18:53 |
| Detected languages: |
|
| CompanyName: | MTSoftware(CN) |
| FileDescription: | Print Control Lodop(32-bit) Install |
| FileVersion: | 6.1.7.5 |
| InternalName: | Lodop(劳道谱) Install |
| LegalCopyright: | 梦泰尔软件工作室 MTSoftware(CN) |
| LegalTrademarks: | Lodop |
| OriginalFilename: | install_lodop32.exe |
| ProductName: | Lodop(劳道谱) Install |
| ProductVersion: | 6.1 |
| Comments: | 梦泰尔软件工作室 MTSoftware(CN) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-Mar-2014 03:18:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x000A3000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x000A4000 | 0x00247000 | 0x00246800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.80336 |
.rsrc | 0x002EB000 | 0x00002000 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.52907 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.70881 | 920 | UNKNOWN | Chinese - PRC | RT_VERSION |
2 | 6.98671 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3 | 6.94276 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 6.96447 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 7.12469 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 7.12907 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 7.00203 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4080 | 5.38811 | 64 | UNKNOWN | UNKNOWN | RT_STRING |
4081 | 7.43182 | 900 | UNKNOWN | UNKNOWN | RT_STRING |
4082 | 6.65398 | 172 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
msimg32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
48
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 976 | "C:\Users\admin\Desktop\install_lodop32.exe" -f “output.txt” | C:\Users\admin\Desktop\install_lodop32.exe | — | explorer.exe | |||||||||||
User: admin Company: MTSoftware(CN) Integrity Level: MEDIUM Description: Print Control Lodop(32-bit) Install Exit code: 3221226540 Version: 6.1.7.5 Modules
| |||||||||||||||
| 1404 | "C:\Users\admin\Desktop\install_lodop32.exe" | C:\Users\admin\Desktop\install_lodop32.exe | explorer.exe | ||||||||||||
User: admin Company: MTSoftware(CN) Integrity Level: HIGH Description: Print Control Lodop(32-bit) Install Exit code: 0 Version: 6.1.7.5 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3780 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3336 | "C:\Users\admin\Desktop\install_lodop32.exe" | C:\Users\admin\Desktop\install_lodop32.exe | — | explorer.exe | |||||||||||
User: admin Company: MTSoftware(CN) Integrity Level: MEDIUM Description: Print Control Lodop(32-bit) Install Exit code: 3221226540 Version: 6.1.7.5 Modules
| |||||||||||||||
| 3592 | "C:\Users\admin\Desktop\install_lodop32.exe" -f “output.txt” | C:\Users\admin\Desktop\install_lodop32.exe | explorer.exe | ||||||||||||
User: admin Company: MTSoftware(CN) Integrity Level: HIGH Description: Print Control Lodop(32-bit) Install Exit code: 0 Version: 6.1.7.5 Modules
| |||||||||||||||
| 3780 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | install_lodop32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
637
Read events
417
Write events
218
Delete events
2
Modification events
| (PID) Process: | (3592) install_lodop32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{0F9014E9-F31C-408E-9CBA-C484B39066ED}\6.0 |
| Operation: | write | Name: | |
Value: Lodop | |||
| (PID) Process: | (3592) install_lodop32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{0F9014E9-F31C-408E-9CBA-C484B39066ED}\6.0\FLAGS |
| Operation: | write | Name: | |
Value: 2 | |||
| (PID) Process: | (3592) install_lodop32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{0F9014E9-F31C-408E-9CBA-C484B39066ED}\6.0\0\win32 |
| Operation: | write | Name: | |
Value: C:\Program Files\MountTaiSoftware\Lodop\CAOSOFT_WEB_PRINT_lodop.ocx | |||
| (PID) Process: | (3592) install_lodop32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{0F9014E9-F31C-408E-9CBA-C484B39066ED}\6.0\HELPDIR |
| Operation: | write | Name: | |
Value: C:\Program Files\MountTaiSoftware\Lodop\ | |||
| (PID) Process: | (3592) install_lodop32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{409D8542-9C63-4719-8DF6-ABDA44494A4E} |
| Operation: | write | Name: | |
Value: ILodopX | |||
| (PID) Process: | (3592) install_lodop32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{409D8542-9C63-4719-8DF6-ABDA44494A4E}\ProxyStubClsid |
| Operation: | write | Name: | |
Value: {00020424-0000-0000-C000-000000000046} | |||
| (PID) Process: | (3592) install_lodop32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{409D8542-9C63-4719-8DF6-ABDA44494A4E}\ProxyStubClsid32 |
| Operation: | write | Name: | |
Value: {00020424-0000-0000-C000-000000000046} | |||
| (PID) Process: | (3592) install_lodop32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{409D8542-9C63-4719-8DF6-ABDA44494A4E}\TypeLib |
| Operation: | write | Name: | |
Value: {0F9014E9-F31C-408E-9CBA-C484B39066ED} | |||
| (PID) Process: | (3592) install_lodop32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{409D8542-9C63-4719-8DF6-ABDA44494A4E}\TypeLib |
| Operation: | write | Name: | Version |
Value: 6.0 | |||
| (PID) Process: | (3592) install_lodop32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{0DC96C68-587A-486E-93D8-7BA1EAF5B9CB} |
| Operation: | write | Name: | |
Value: ILodopXEvents | |||
Executable files
6
Suspicious files
5
Text files
178
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3780 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3780 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1404 | install_lodop32.exe | C:\Program Files\MountTaiSoftware\Lodop\NPCAOSOFT_WEB_PRINT_lodop.dll | executable | |
MD5:— | SHA256:— | |||
| 3592 | install_lodop32.exe | C:\Users\Administrator\NTUSER.DAT.LOG1 | log | |
MD5:— | SHA256:— | |||
| 3592 | install_lodop32.exe | C:\Users\Administrator\NTUSER.DAT | hiv | |
MD5:— | SHA256:— | |||
| 3592 | install_lodop32.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG1 | log | |
MD5:— | SHA256:— | |||
| 2796 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\PrivacIE\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3592 | install_lodop32.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3780 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 1404 | install_lodop32.exe | C:\Program Files\MountTaiSoftware\Lodop\CAOSOFT_WEB_PRINT_lodop.ocx | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
156
TCP/UDP connections
67
DNS requests
42
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2796 | iexplore.exe | GET | 200 | 47.246.43.223:80 | http://simg.sinajs.cn/blog7style/css/conf/blog/article.css | US | text | 42.5 Kb | whitelisted |
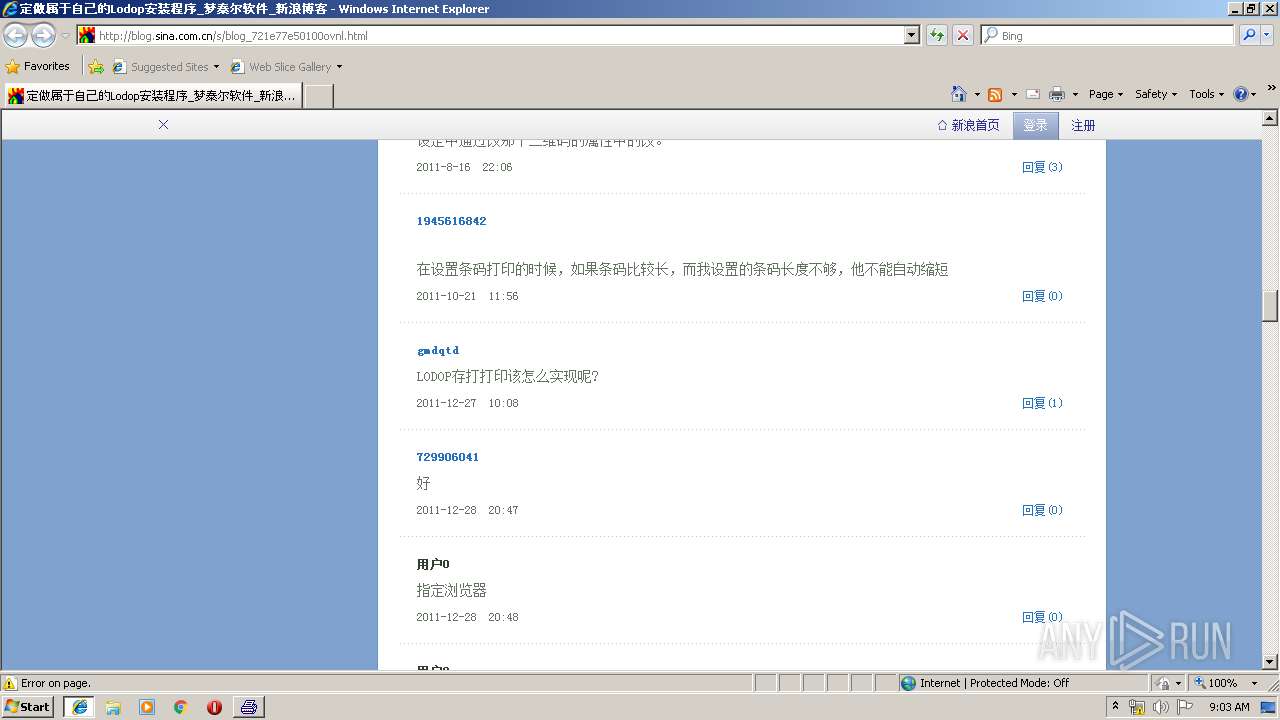
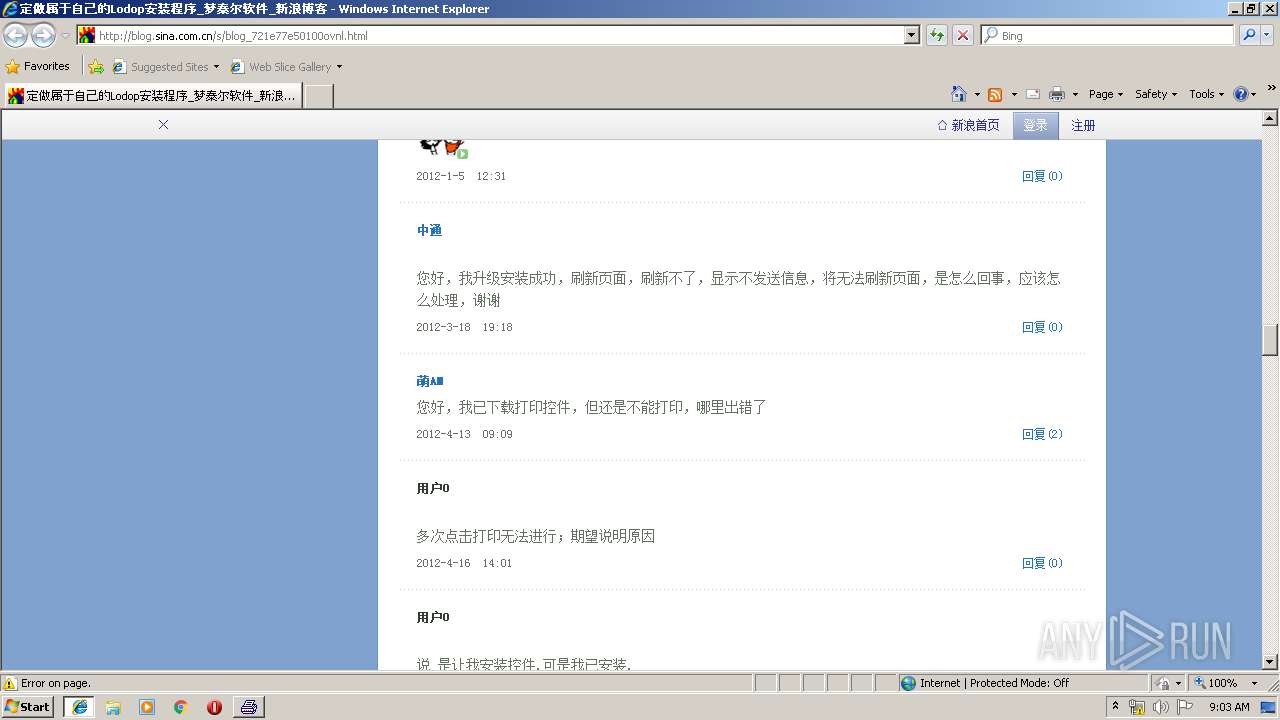
2796 | iexplore.exe | GET | 200 | 49.7.37.126:80 | http://blog.sina.com.cn/s/blog_721e77e50100ovnl.html | CN | html | 9.41 Kb | suspicious |
2796 | iexplore.exe | GET | 200 | 47.246.43.223:80 | http://simg.sinajs.cn/blog7style/css/module/common/blog.css | US | text | 12.1 Kb | whitelisted |
2796 | iexplore.exe | GET | 200 | 47.246.43.223:80 | http://simg.sinajs.cn/blog7style/images/common/loading.gif | US | image | 722 b | whitelisted |
2796 | iexplore.exe | GET | 200 | 47.246.43.223:80 | http://simg.sinajs.cn/blog7style/css/common/common.css | US | text | 63.2 Kb | whitelisted |
2796 | iexplore.exe | GET | 200 | 47.246.43.223:80 | http://simg.sinajs.cn/blog7newtpl/image/16/16_8/images/modelhead.png | US | image | 979 b | whitelisted |
2796 | iexplore.exe | GET | 200 | 47.246.43.223:80 | http://simg.sinajs.cn/blog7newtpl/css/16/16_8/t.css | US | text | 2.22 Kb | whitelisted |
2796 | iexplore.exe | GET | 200 | 47.246.43.223:80 | http://simg.sinajs.cn/blog7newtpl/image/16/16_8/images/sinablogb.jpg | US | image | 106 Kb | whitelisted |
2796 | iexplore.exe | GET | 200 | 47.246.43.223:80 | http://simg.sinajs.cn/blog7newtpl/image/16/16_8/images/sg_newsp.png | US | image | 4.46 Kb | whitelisted |
2796 | iexplore.exe | GET | 200 | 47.246.43.223:80 | http://simg.sinajs.cn/blog7style/images/common/topbar/topbar_logo.gif | US | image | 1.42 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3780 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2796 | iexplore.exe | 47.246.43.223:80 | simg.sinajs.cn | — | US | malicious |
2796 | iexplore.exe | 36.51.254.37:80 | i.sso.sina.com.cn | ISP | CN | unknown |
2796 | iexplore.exe | 2.18.233.49:80 | d1.sina.com.cn | Akamai International B.V. | — | whitelisted |
2796 | iexplore.exe | 49.7.37.126:80 | blog.sina.com.cn | — | CN | suspicious |
2796 | iexplore.exe | 49.7.36.113:80 | control.blog.sina.com.cn | — | CN | unknown |
2796 | iexplore.exe | 49.7.37.59:80 | hs.blog.sina.com.cn | — | CN | unknown |
2796 | iexplore.exe | 49.7.36.105:80 | blogtj.sinajs.cn | — | CN | unknown |
2796 | iexplore.exe | 49.7.37.94:80 | comet.blog.sina.com.cn | — | CN | suspicious |
2796 | iexplore.exe | 123.126.45.75:80 | comment5.news.sina.com.cn | China Unicom Beijing Province Network | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blog.sina.com.cn |
| suspicious |
www.bing.com |
| whitelisted |
simg.sinajs.cn |
| whitelisted |
d1.sina.com.cn |
| whitelisted |
sjs.sinajs.cn |
| whitelisted |
i.sso.sina.com.cn |
| whitelisted |
d5.sina.com.cn |
| whitelisted |
control.blog.sina.com.cn |
| unknown |
sax.sina.com.cn |
| whitelisted |
d2.sina.com.cn |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2796 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |