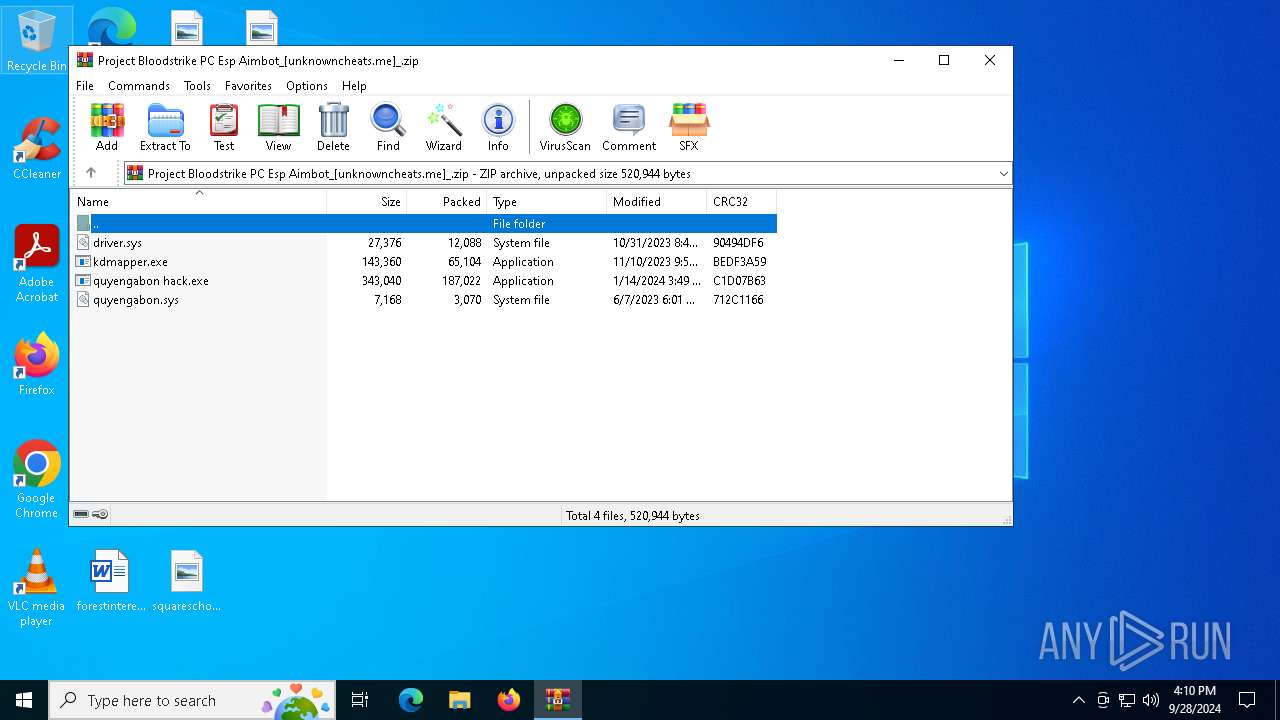
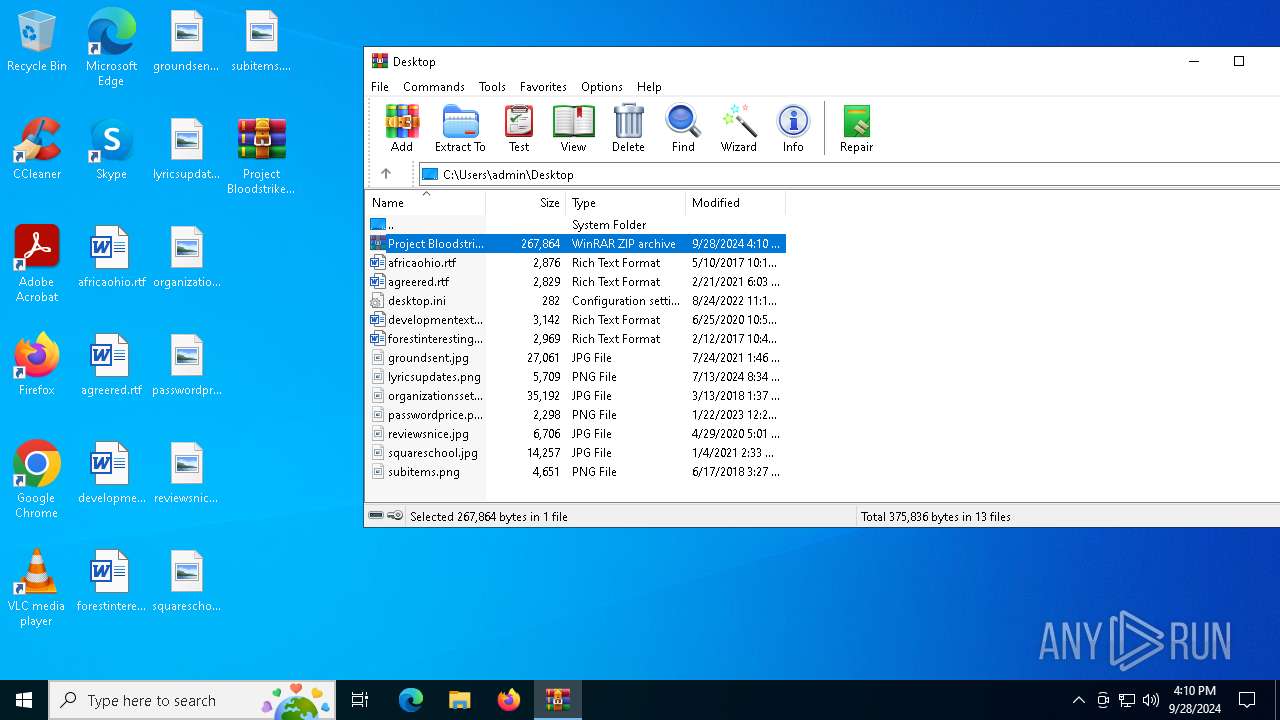
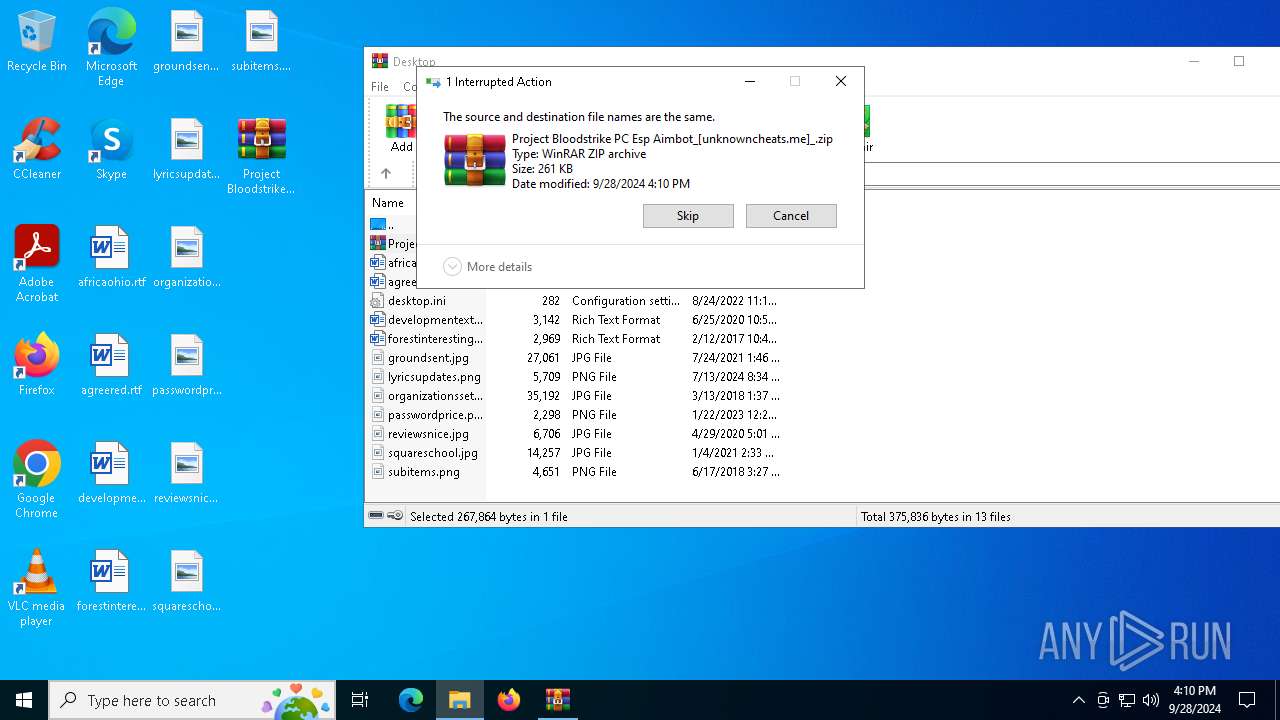
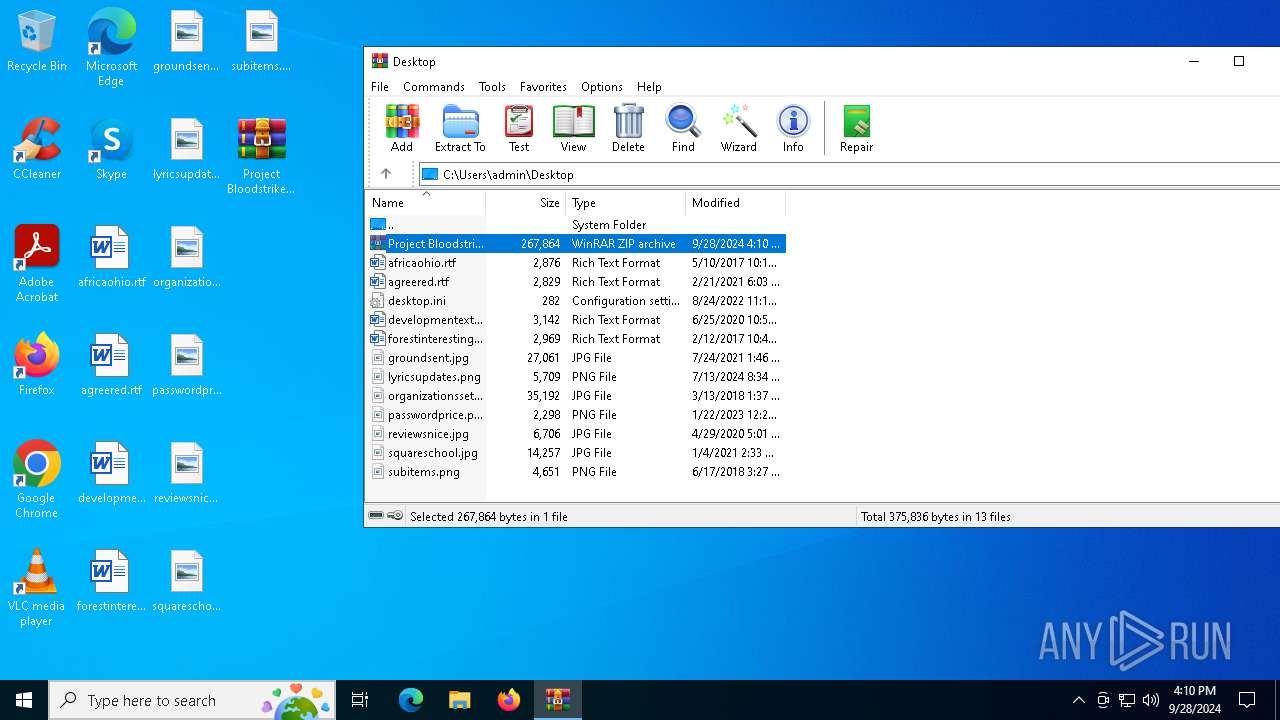
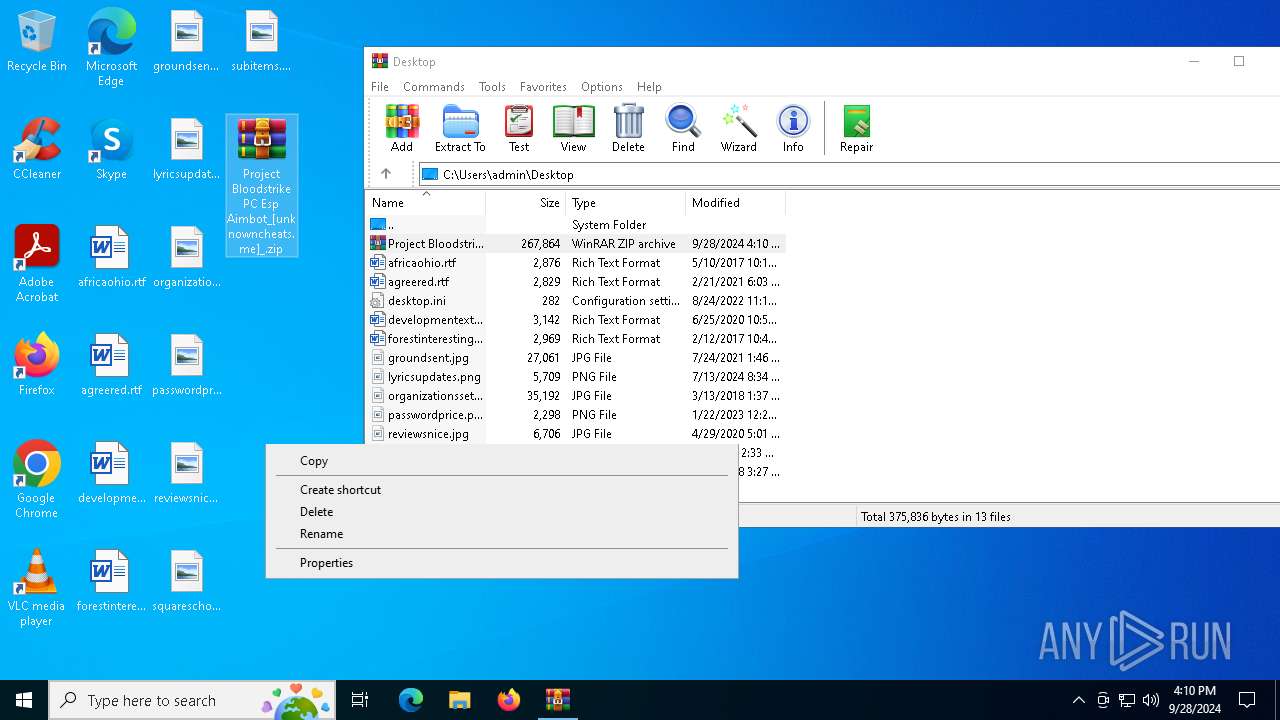
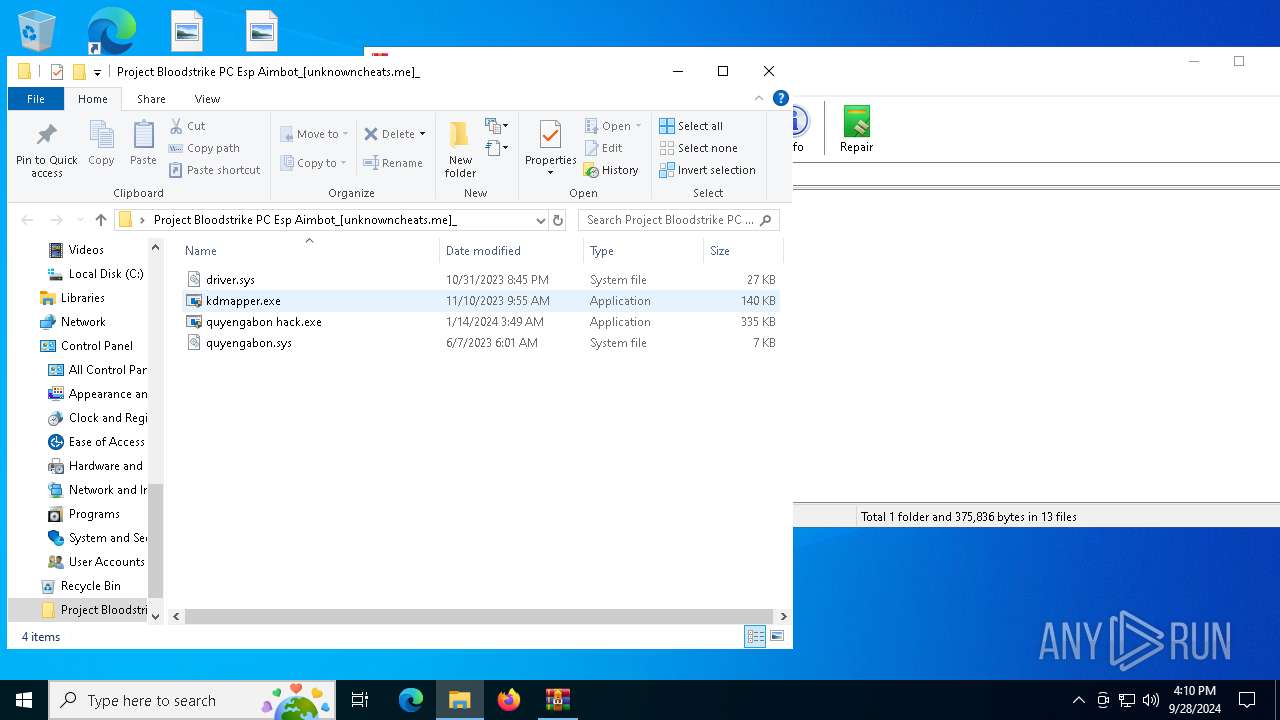
| File name: | Project Bloodstrike PC Esp Aimbot_[unknowncheats.me]_.zip |
| Full analysis: | https://app.any.run/tasks/440930e6-7258-4570-b242-48ac96b54f63 |
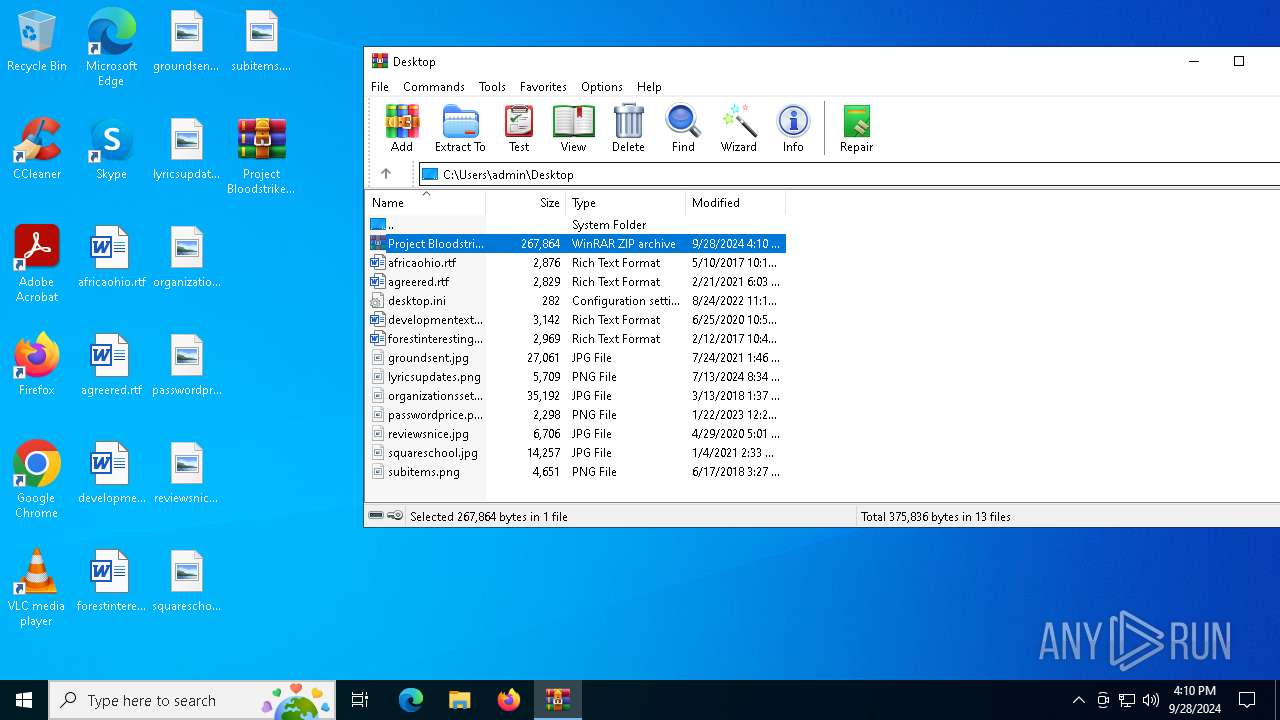
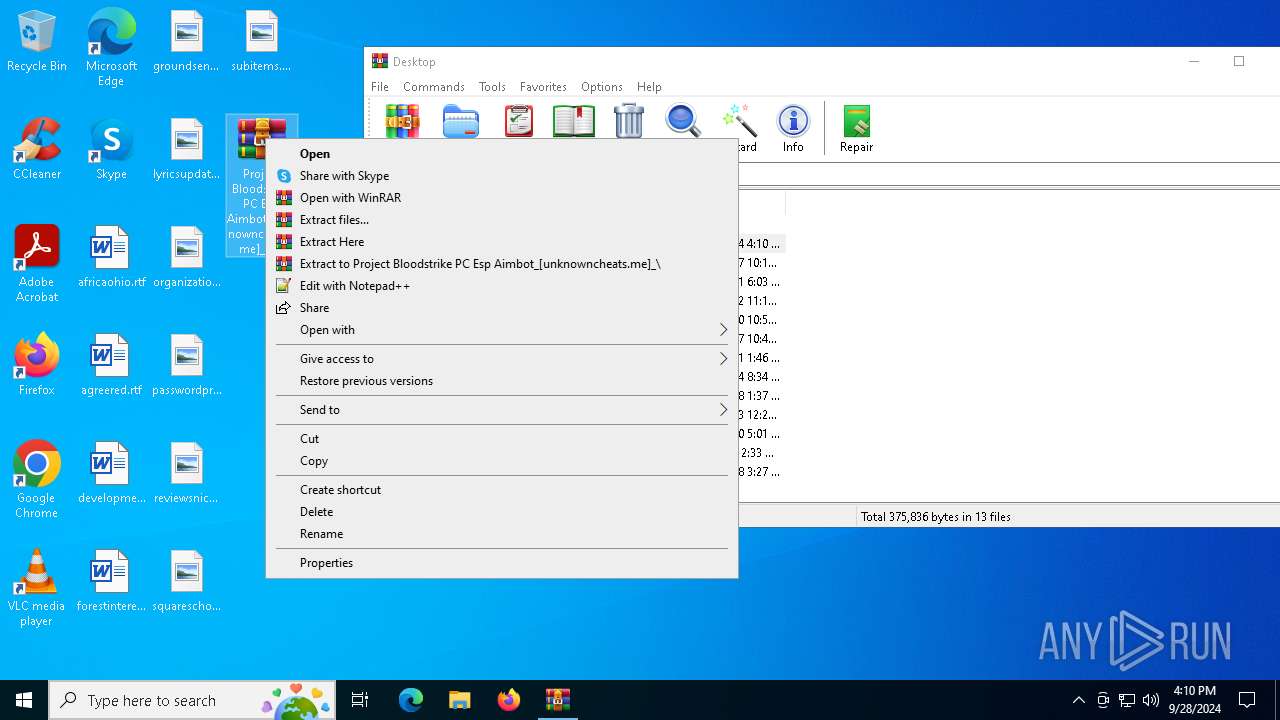
| Verdict: | Malicious activity |
| Analysis date: | September 28, 2024, 16:10:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 37CBAFF5D4142B86EBA75B2A175027C3 |
| SHA1: | 65458106D69E215A5B83E2EBF2D128773258FCBA |
| SHA256: | 978365F28CB253B7F7730846F64143204DD6FFD95FA98100BF69F391C596D6C8 |
| SSDEEP: | 12288:xX0tz7JDv5e+RxA9MZPFtQgXhWbHRY7GmK2zk:xX0F7JDBe+RxA9MhFtQgRWbH+im3o |
MALICIOUS
No malicious indicators.SUSPICIOUS
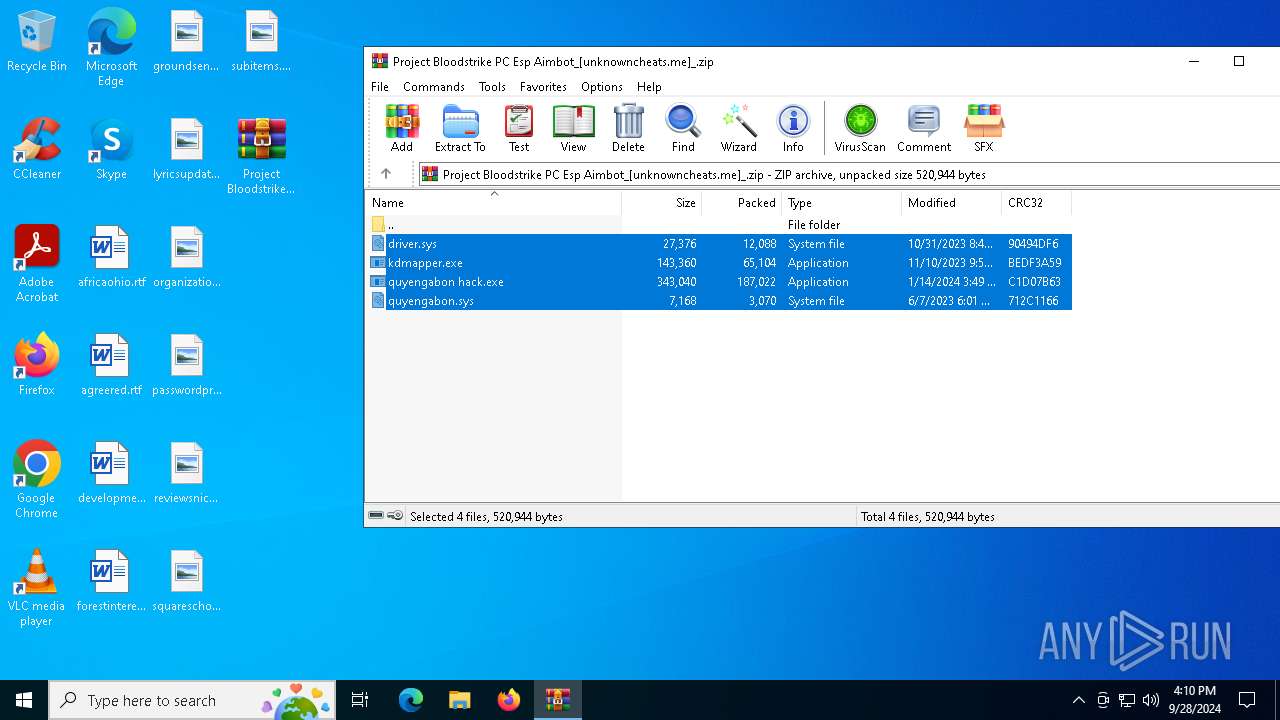
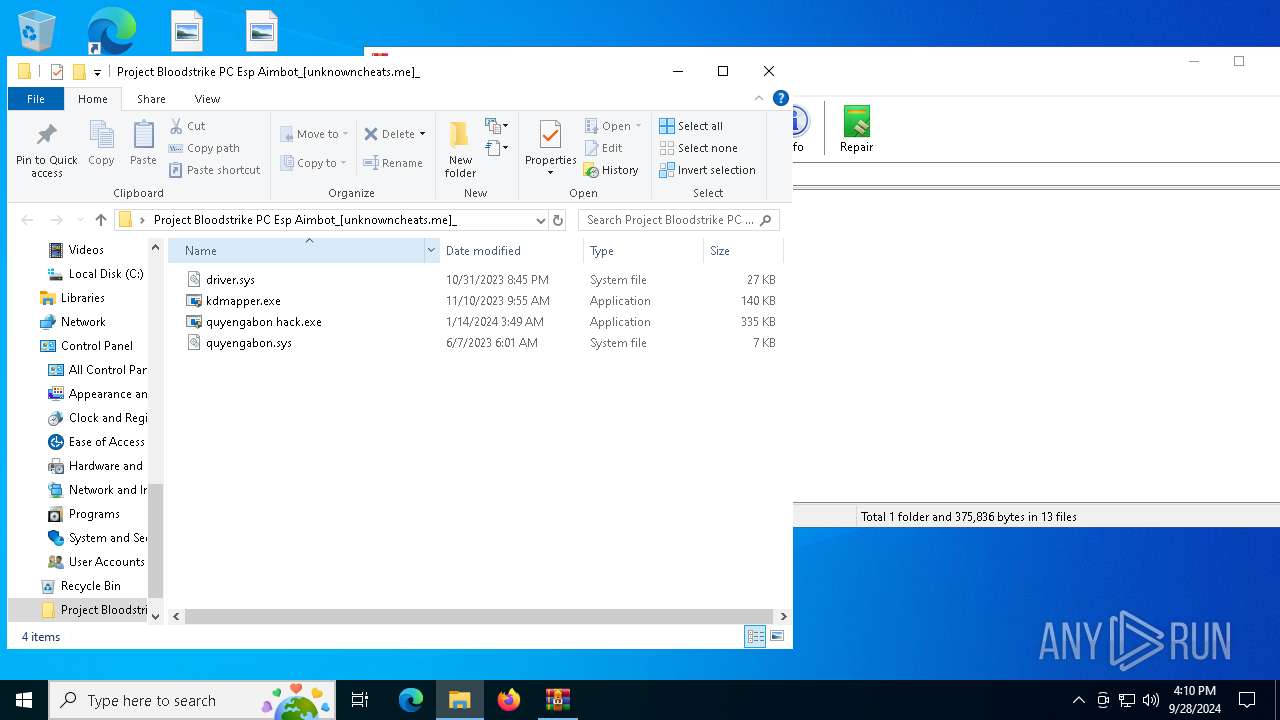
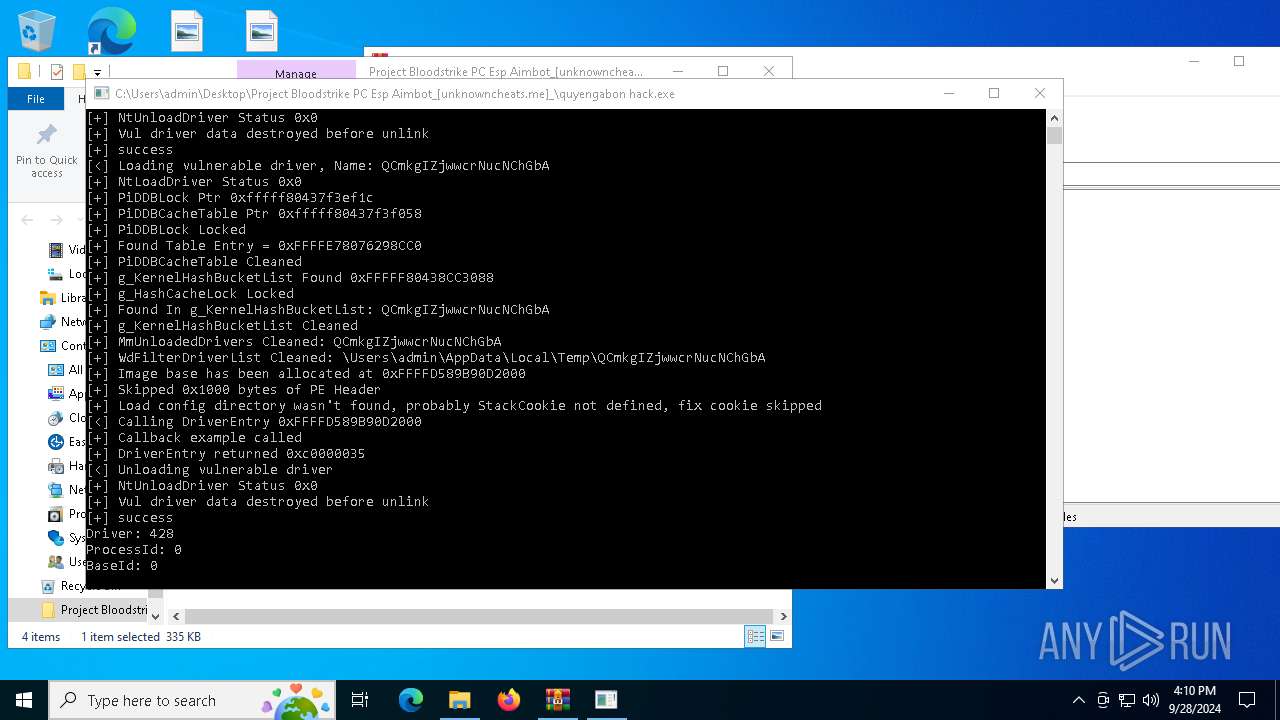
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 4172)
Executable content was dropped or overwritten
- kdmapper.exe (PID: 5700)
- kdmapper.exe (PID: 4368)
- kdmapper.exe (PID: 5208)
- kdmapper.exe (PID: 5244)
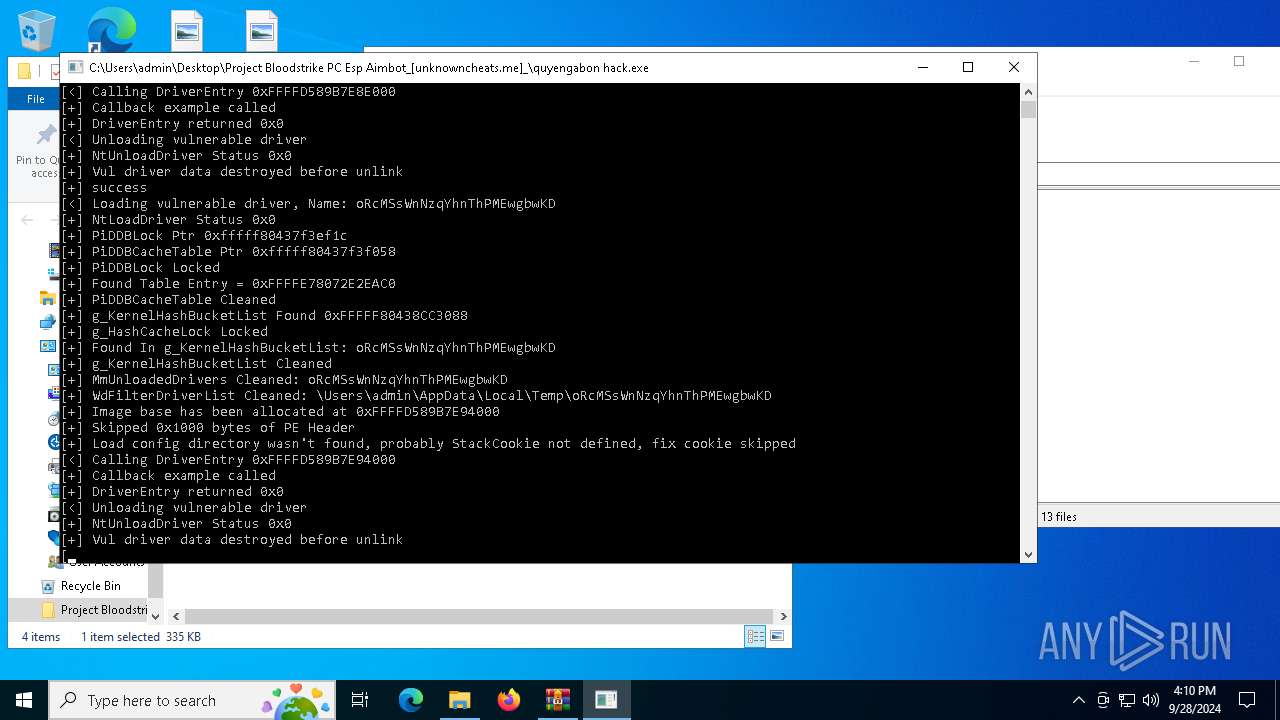
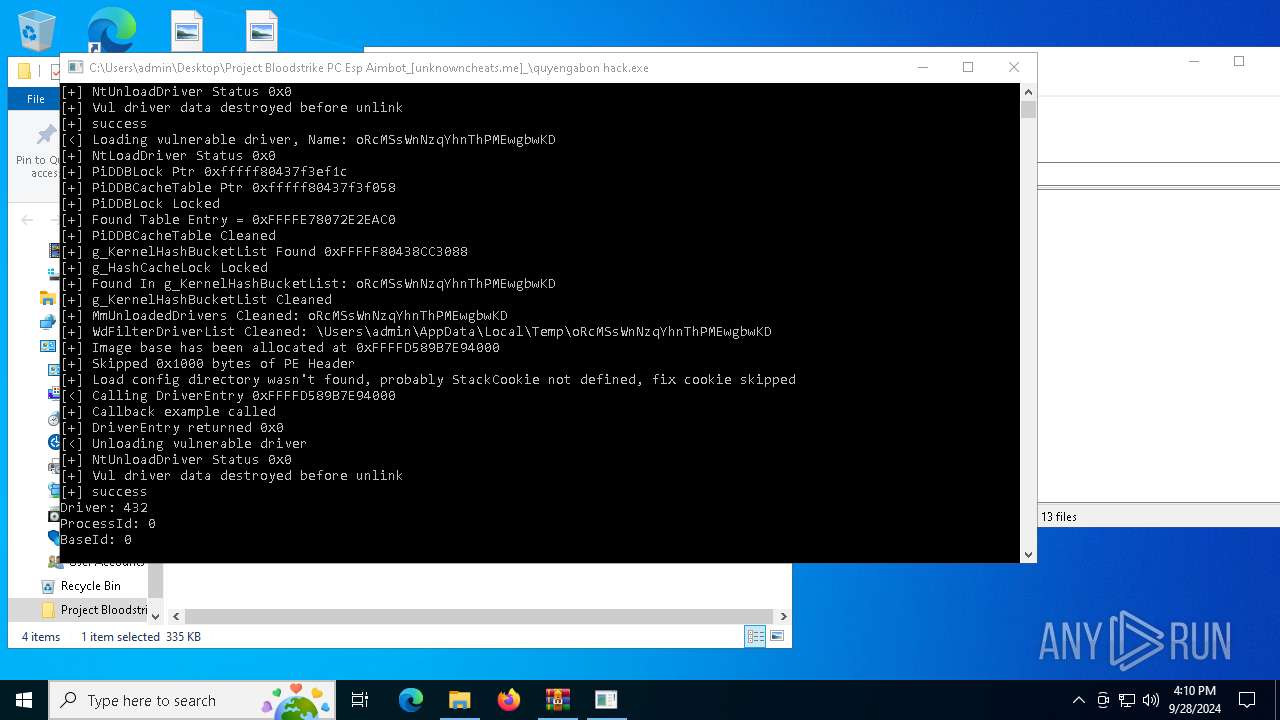
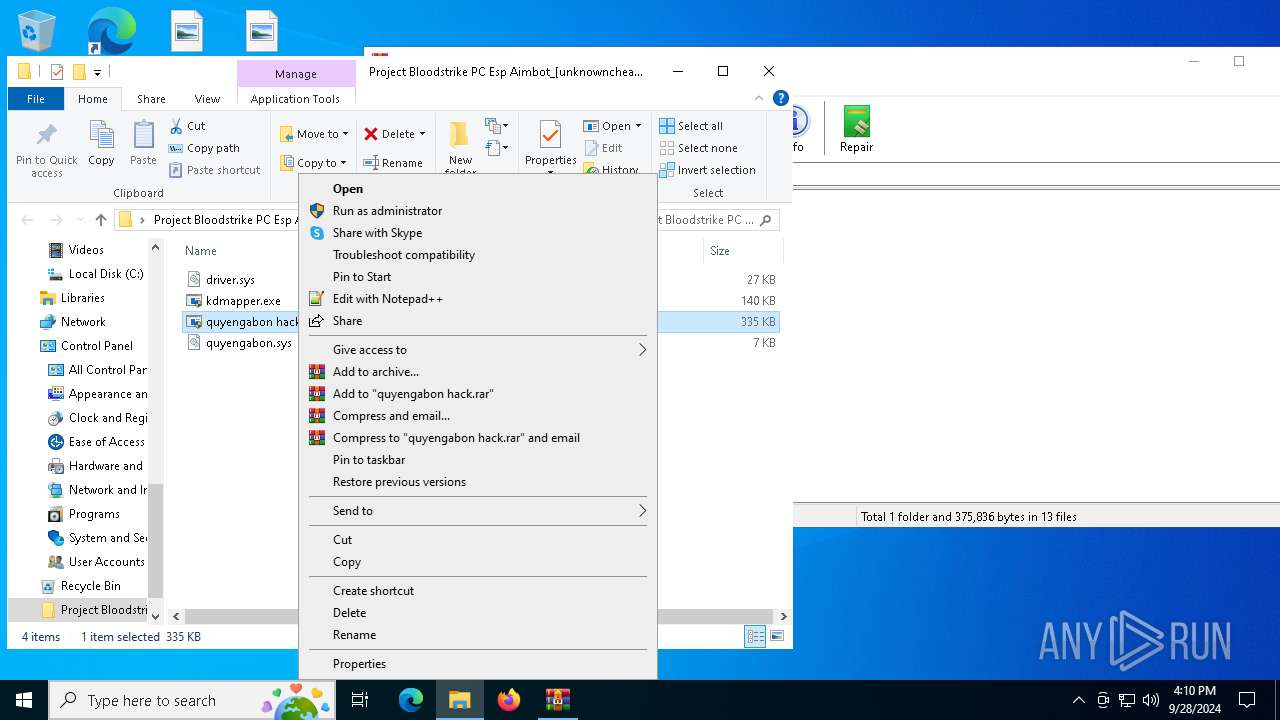
Starts CMD.EXE for commands execution
- quyengabon hack.exe (PID: 1488)
- quyengabon hack.exe (PID: 6476)
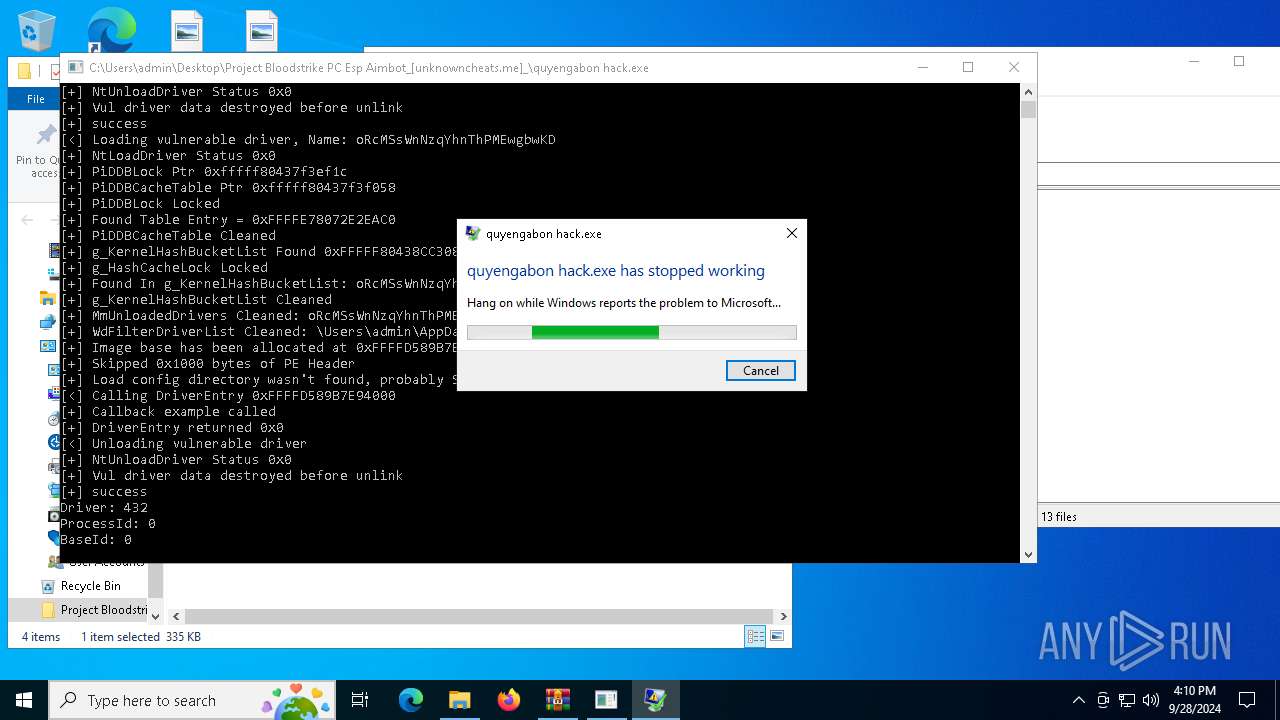
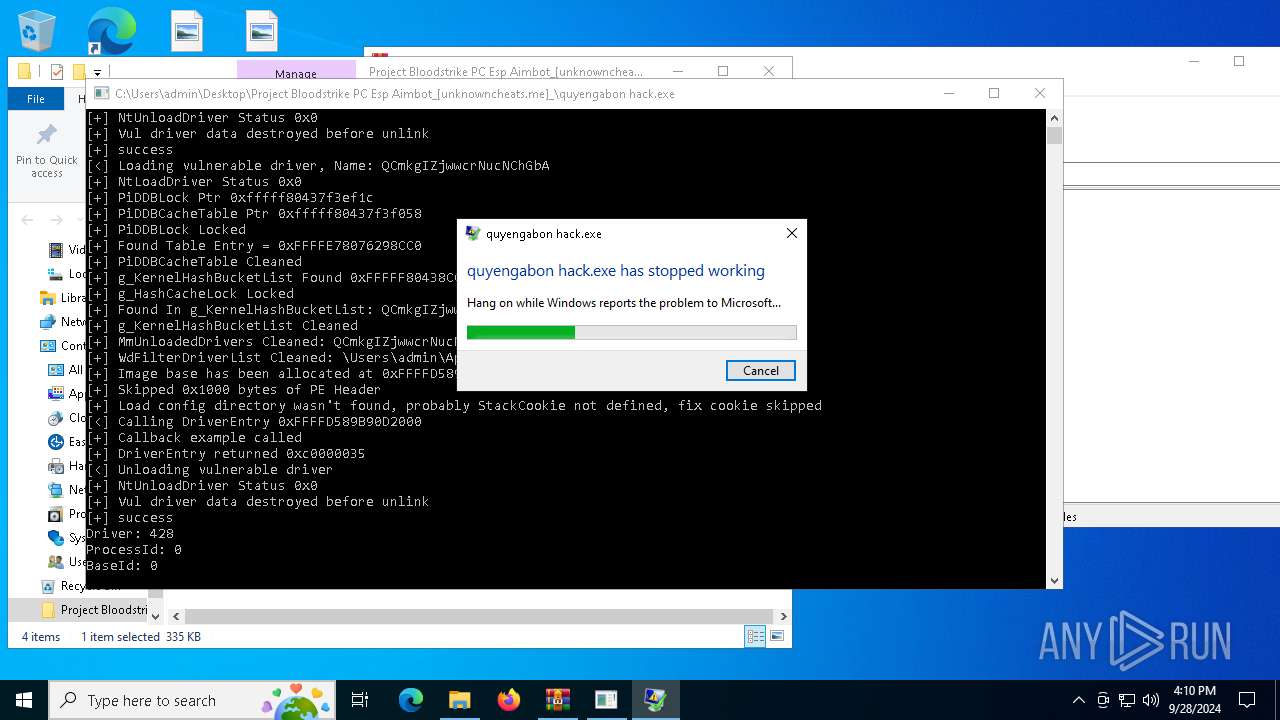
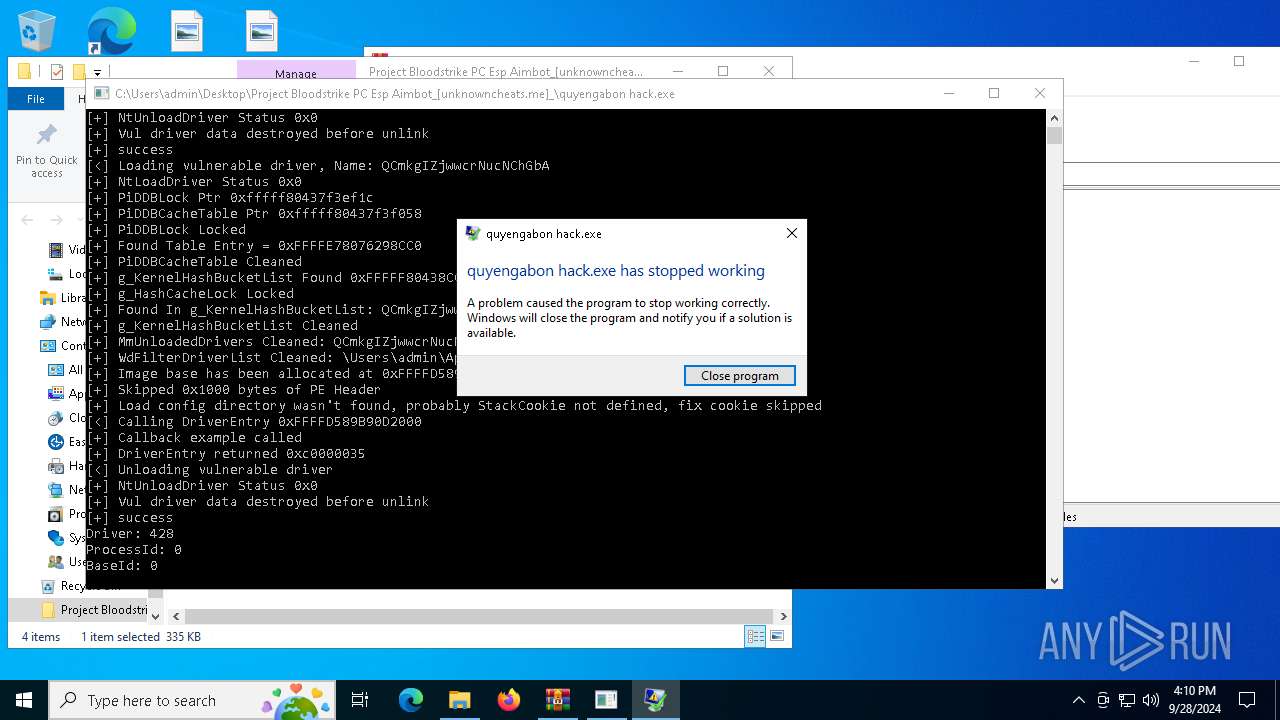
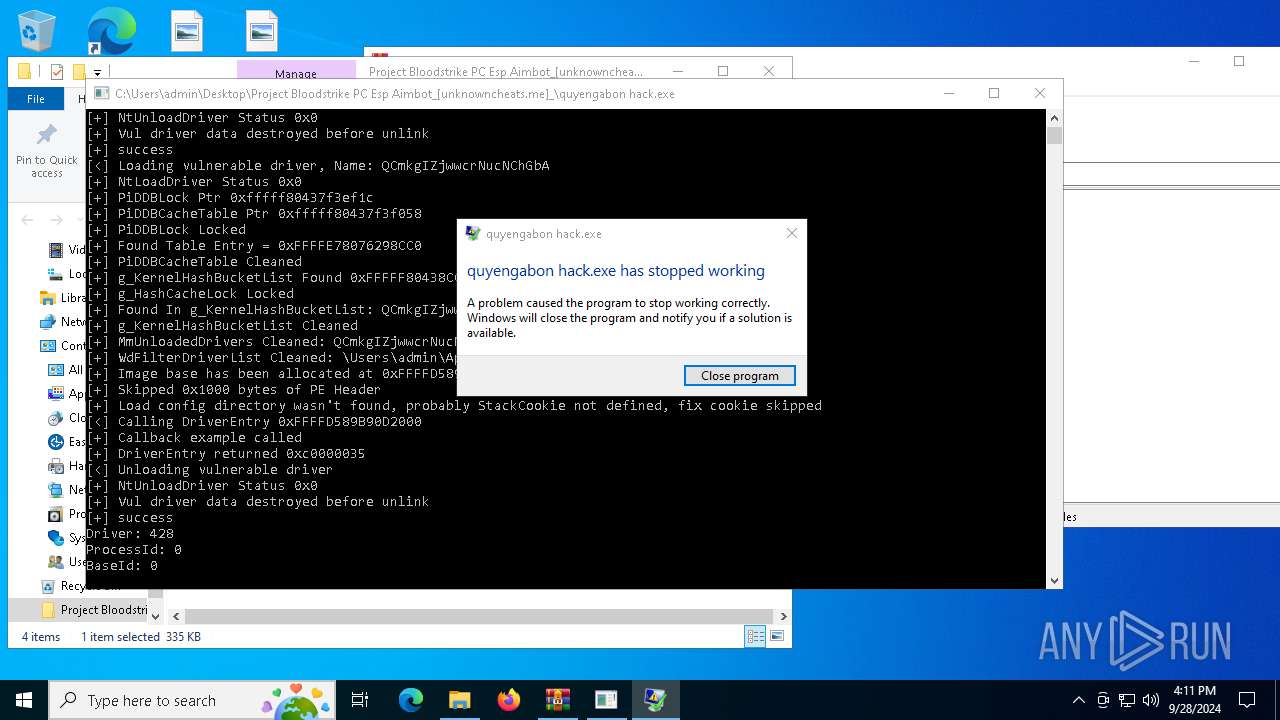
Executes application which crashes
- quyengabon hack.exe (PID: 1488)
- quyengabon hack.exe (PID: 6476)
INFO
Executable content was dropped or overwritten
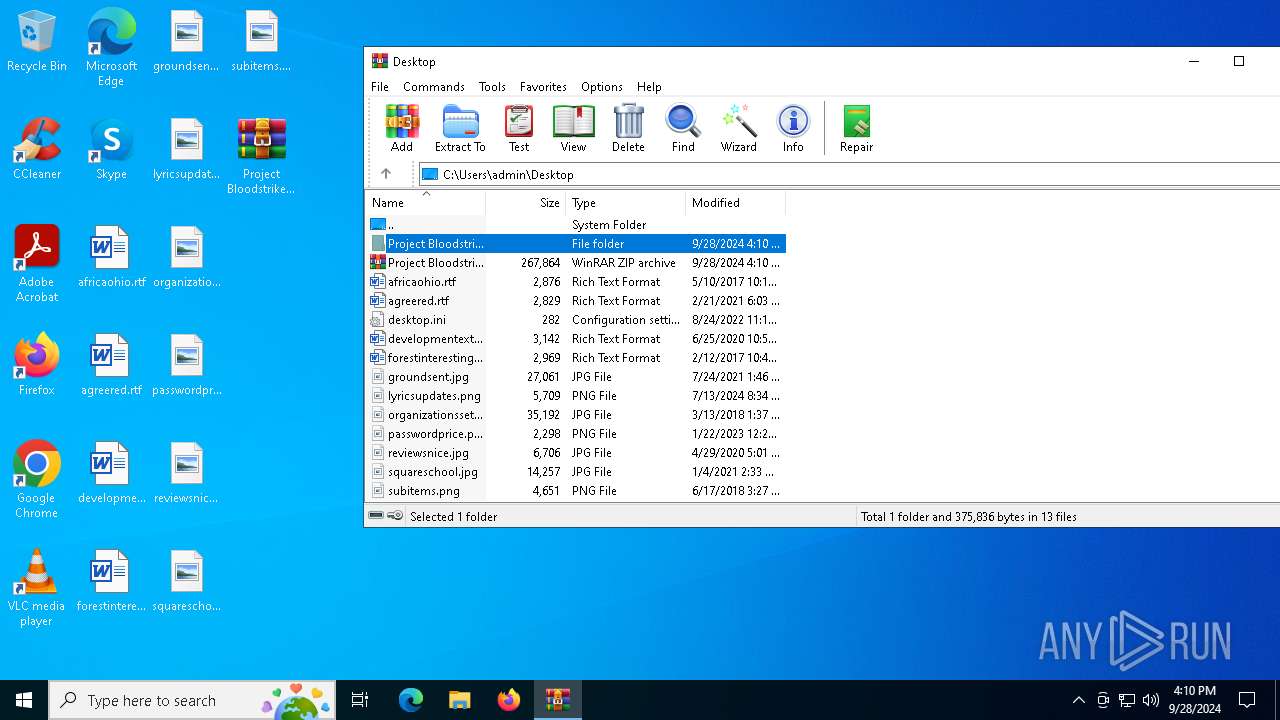
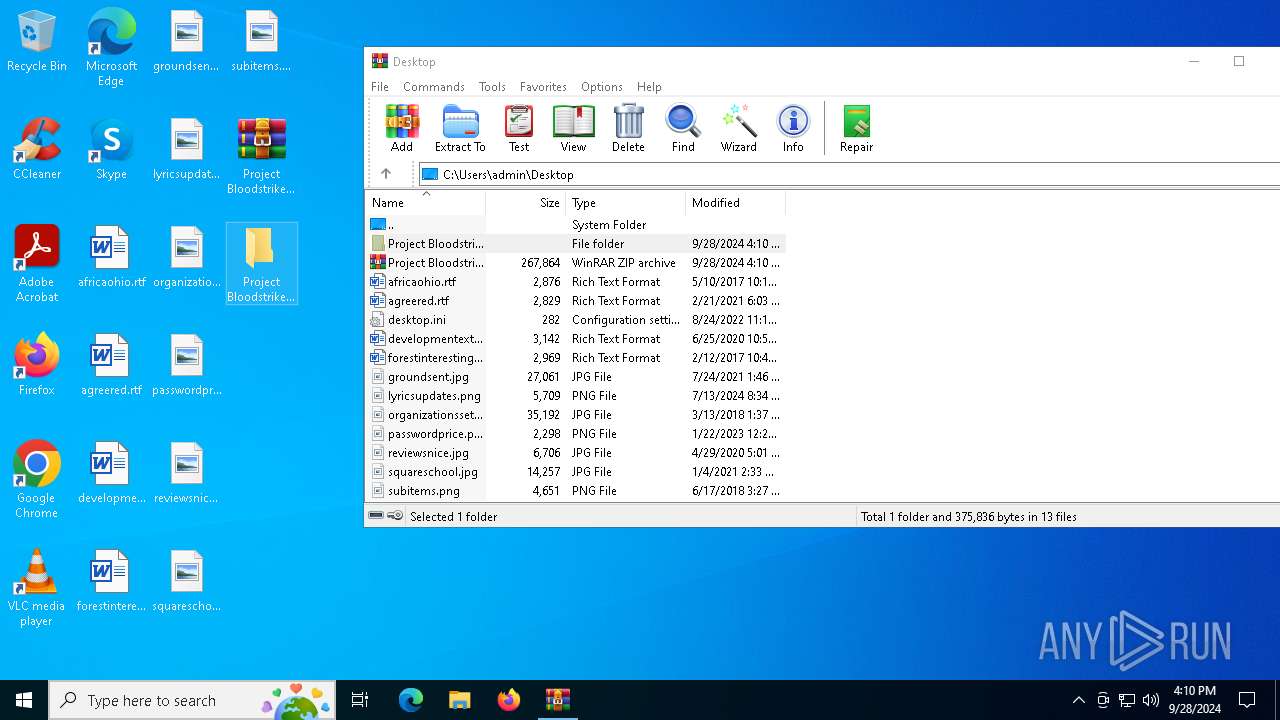
- WinRAR.exe (PID: 4172)
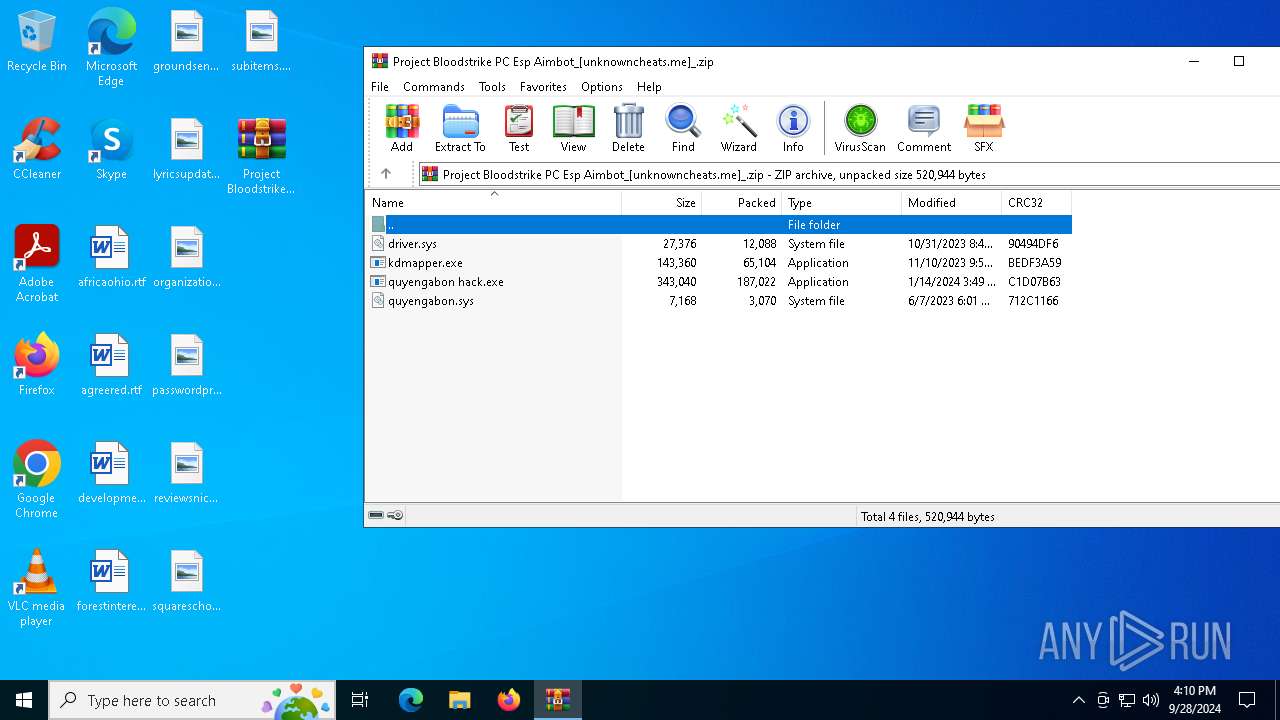
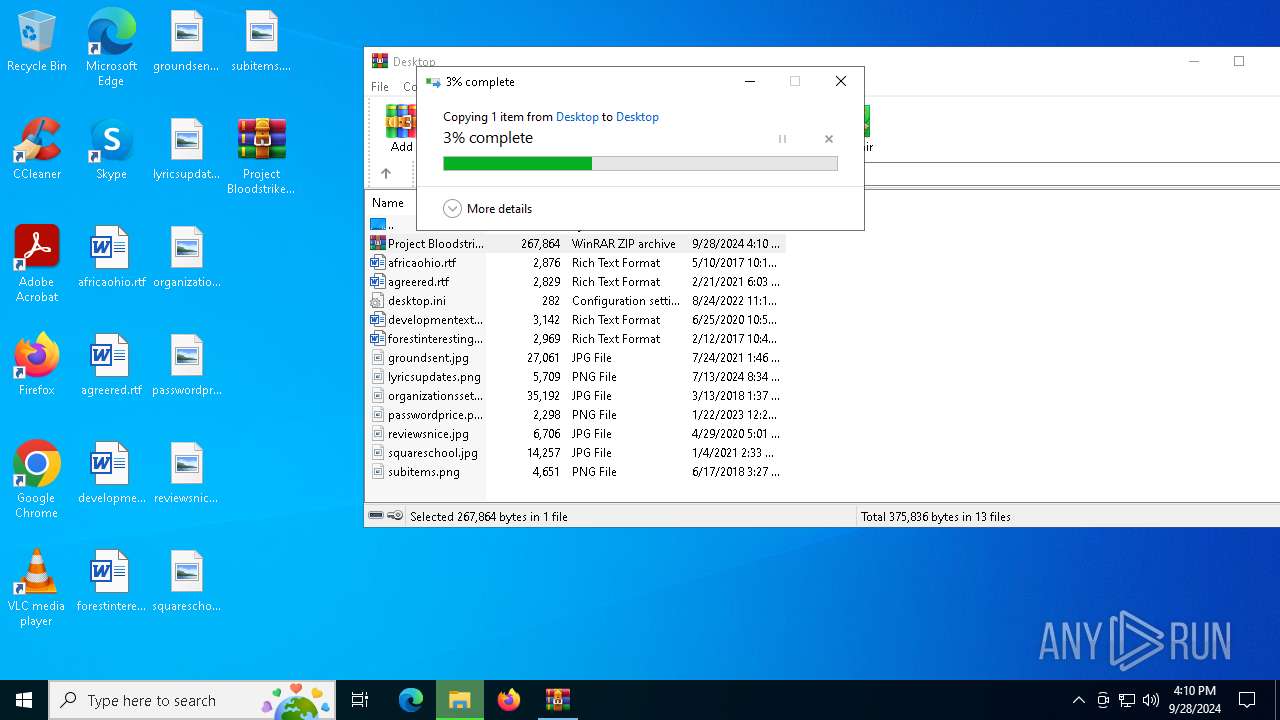
Manual execution by a user
- quyengabon hack.exe (PID: 4060)
- WinRAR.exe (PID: 4172)
- quyengabon hack.exe (PID: 1488)
- quyengabon hack.exe (PID: 6476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:06:07 13:01:38 |
| ZipCRC: | 0x712c1166 |
| ZipCompressedSize: | 3070 |
| ZipUncompressedSize: | 7168 |
| ZipFileName: | quyengabon.sys |
Total processes
155
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | "C:\Users\admin\Desktop\Project Bloodstrike PC Esp Aimbot_[unknowncheats.me]_\quyengabon hack.exe" | C:\Users\admin\Desktop\Project Bloodstrike PC Esp Aimbot_[unknowncheats.me]_\quyengabon hack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 2132 | C:\WINDOWS\system32\WerFault.exe -u -p 1488 -s 600 | C:\Windows\System32\WerFault.exe | quyengabon hack.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2328 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3144 | C:\WINDOWS\system32\cmd.exe /c kdmapper.exe quyengabon.sys | C:\Windows\System32\cmd.exe | — | quyengabon hack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3300 | C:\WINDOWS\system32\cmd.exe /c kdmapper.exe quyengabon.sys | C:\Windows\System32\cmd.exe | — | quyengabon hack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | quyengabon hack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
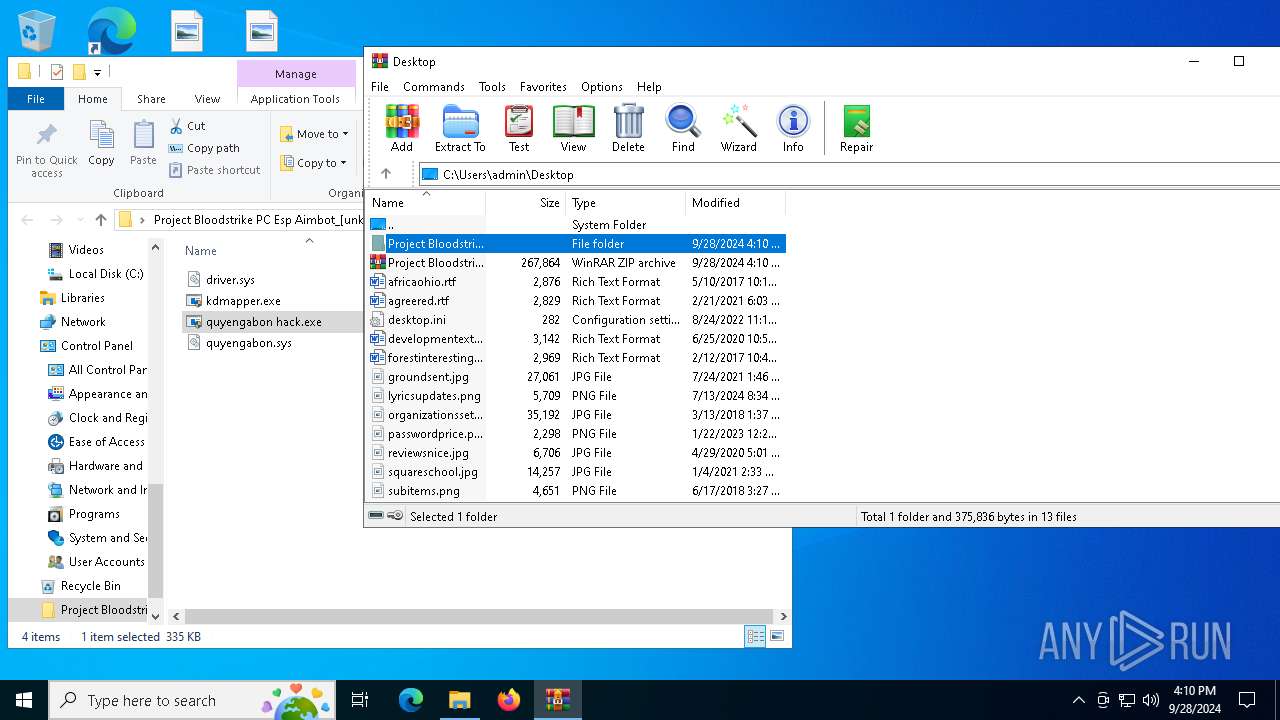
| 3800 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Project Bloodstrike PC Esp Aimbot_[unknowncheats.me]_.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3920 | C:\WINDOWS\system32\cmd.exe /c kdmapper.exe driver.sys | C:\Windows\System32\cmd.exe | — | quyengabon hack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4060 | "C:\Users\admin\Desktop\Project Bloodstrike PC Esp Aimbot_[unknowncheats.me]_\quyengabon hack.exe" | C:\Users\admin\Desktop\Project Bloodstrike PC Esp Aimbot_[unknowncheats.me]_\quyengabon hack.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4172 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Project Bloodstrike PC Esp Aimbot_[unknowncheats.me]_.zip" "C:\Users\admin\Desktop\Project Bloodstrike PC Esp Aimbot_[unknowncheats.me]_\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
9 478
Read events
9 438
Write events
30
Delete events
10
Modification events
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Project Bloodstrike PC Esp Aimbot_[unknowncheats.me]_.zip | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
8
Suspicious files
5
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_quyengabon hack._9cb92f1c9dae19c61d2512da9913efe1dc6b34_fbb52c7d_d78b7853-9793-4e91-8d50-658b8fc587eb\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4192 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_quyengabon hack._9cb92f1c9dae19c61d2512da9913efe1dc6b34_fbb52c7d_eb3ec885-1c3b-4ff5-9a8a-a247312e3d9c\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2132 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERDC53.tmp.dmp | dmp | |
MD5:A4CF41E850DB293F78601A0BA9D661A6 | SHA256:36814ED4AE0F2D52658A910833323DB4D30E345C5181443F40F79E11ED61417D | |||
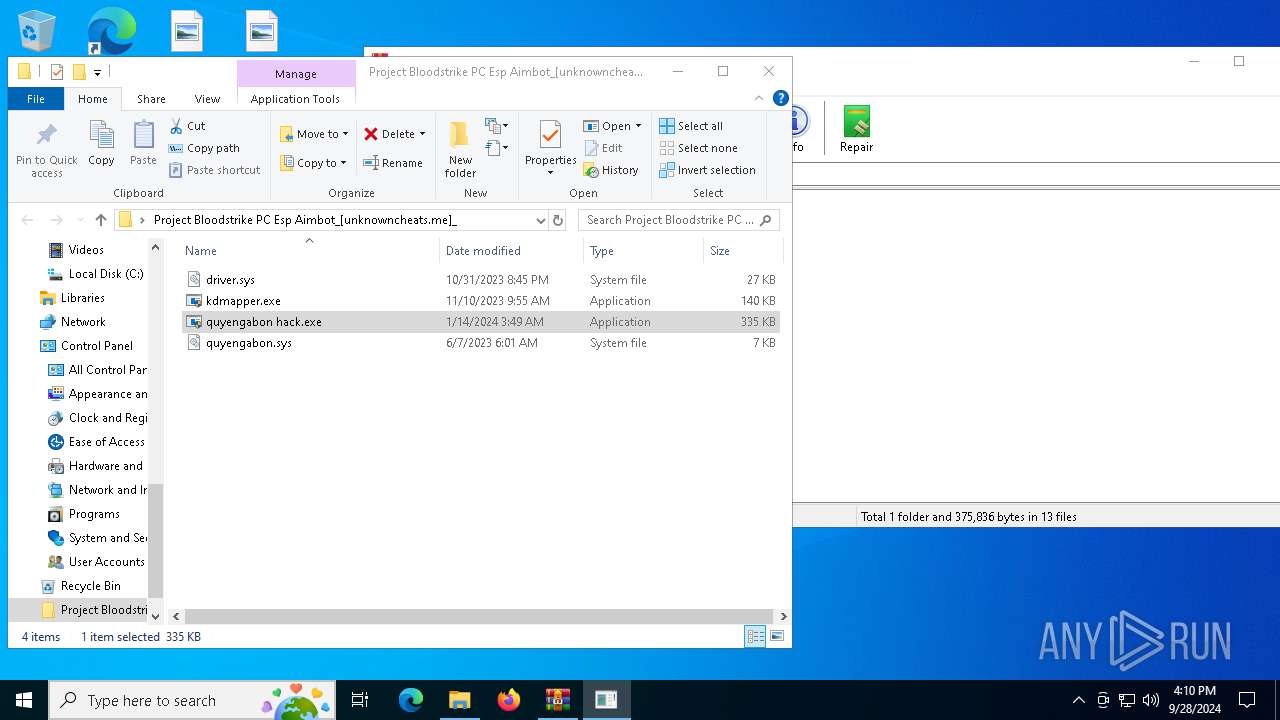
| 4172 | WinRAR.exe | C:\Users\admin\Desktop\Project Bloodstrike PC Esp Aimbot_[unknowncheats.me]_\kdmapper.exe | executable | |
MD5:27594F4D6336A24797B823AC0E8A14A7 | SHA256:0F523ACB076D94995F55A3388935556B70F94148BE5B9BAD4E93CF284A9889B1 | |||
| 4172 | WinRAR.exe | C:\Users\admin\Desktop\Project Bloodstrike PC Esp Aimbot_[unknowncheats.me]_\quyengabon hack.exe | executable | |
MD5:4C86BD4A91F3C5BFECF5C11B68A3762B | SHA256:B336095582C8E96DF864275520955A21F5742D9BBD6934D299DD178130C06DB6 | |||
| 2132 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERDCD1.tmp.WERInternalMetadata.xml | xml | |
MD5:175A55D2CC25C09CA58A0D33F70E69FD | SHA256:3B4EEF96696AF89D9C347DE90E3F76DF643C879D653D58E067F30EF1F63DEDDE | |||
| 2132 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | der | |
MD5:1B7FD5177461034E4086724C5845E927 | SHA256:065AF18C229898A1C2A8D989911ADCD9B1E2AB14B1953EBF8EAF34AE37EA1627 | |||
| 5244 | kdmapper.exe | C:\Users\admin\AppData\Local\Temp\QCmkgIZjwwcrNucNChGbA | executable | |
MD5:1898CEDA3247213C084F43637EF163B3 | SHA256:4429F32DB1CC70567919D7D47B844A91CF1329A6CD116F582305F3B7B60CD60B | |||
| 2132 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:ED6028FDD176D9FF811CBD206F2D6345 | SHA256:3B3900EA8A41CC5DB6F652EEA14313A9B49C8F5965351D6C9A3F9B053FFB5EFF | |||
| 2132 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FB64A9EBEDF48D3895381D5B7D80743D | SHA256:EA21D495930AD76F267A33A0F593DBF0C7EA75E457FCAE49A29DAAD8BD920F42 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
60
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2132 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2420 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2420 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6832 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6588 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4516 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |