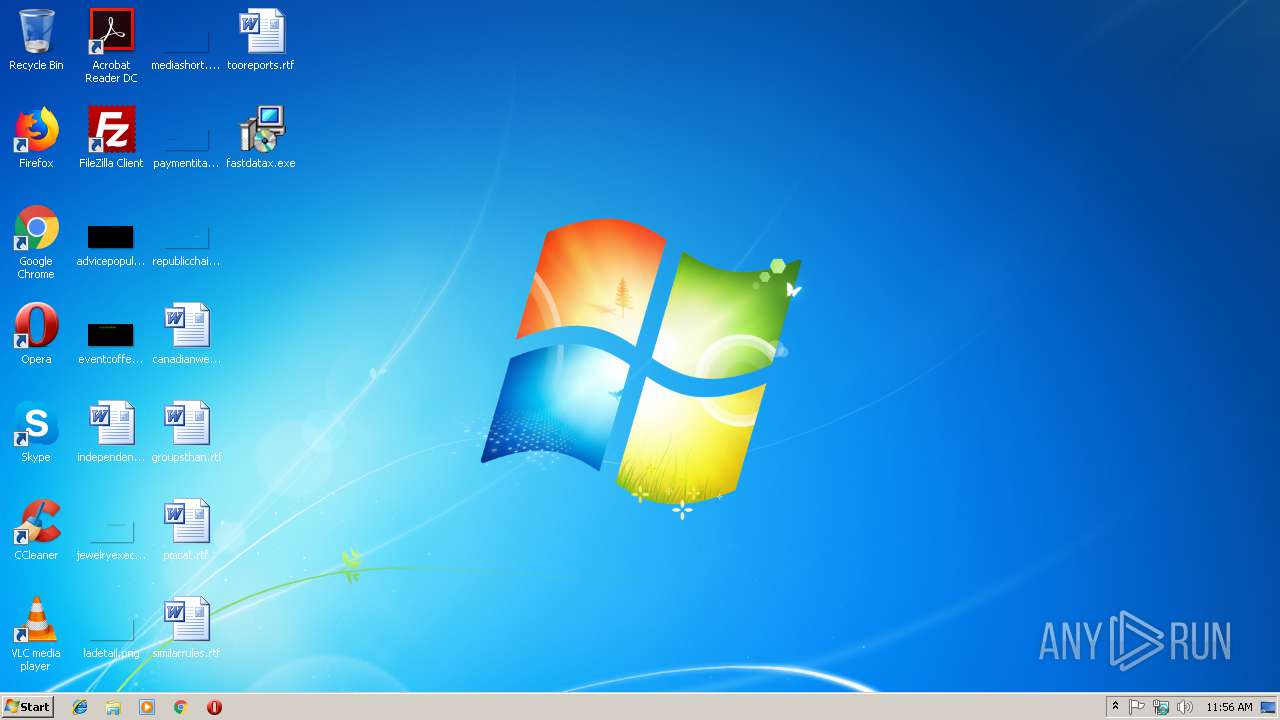
| File name: | fastdatax.exe |
| Full analysis: | https://app.any.run/tasks/ccc3f31f-c44b-4f8c-8534-370b43f37483 |
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2019, 11:55:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C265B60933EE5BB2BA02743D545286B8 |
| SHA1: | CE34CA37E3B23CE1A1BC5FD12ABDBC9541C50C13 |
| SHA256: | 97823A367E1F7BC7DE6D9657395ECE9034E2E98B3BB7796CCC9411AF541AC491 |
| SSDEEP: | 24576:qBWJ/7A4IiDMi2MnWgHHCYF+0CkZY90FMGFc9YCPlqmuBYKq7I6Khyk0t:vdAuhHPFwZ9xlqnLSKhj0 |
MALICIOUS
Connects to CnC server
- fastdatax.tmp (PID: 2896)
- fastdatax.tmp (PID: 4080)
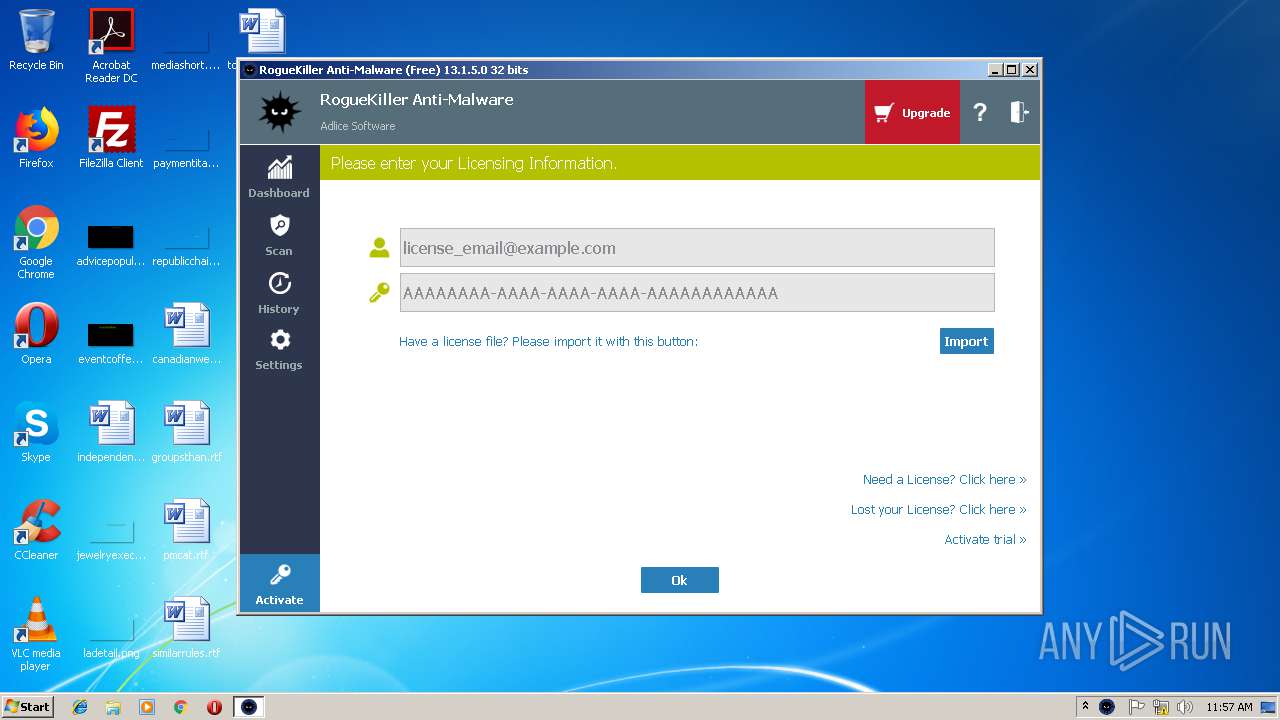
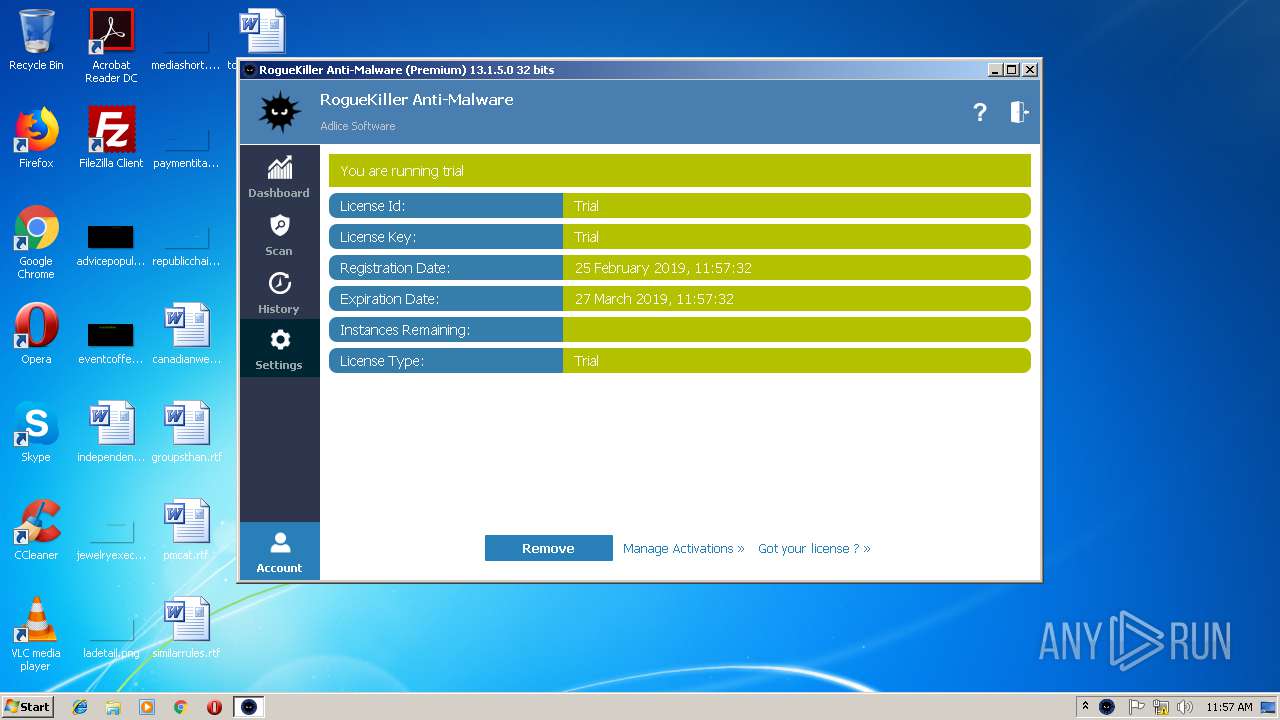
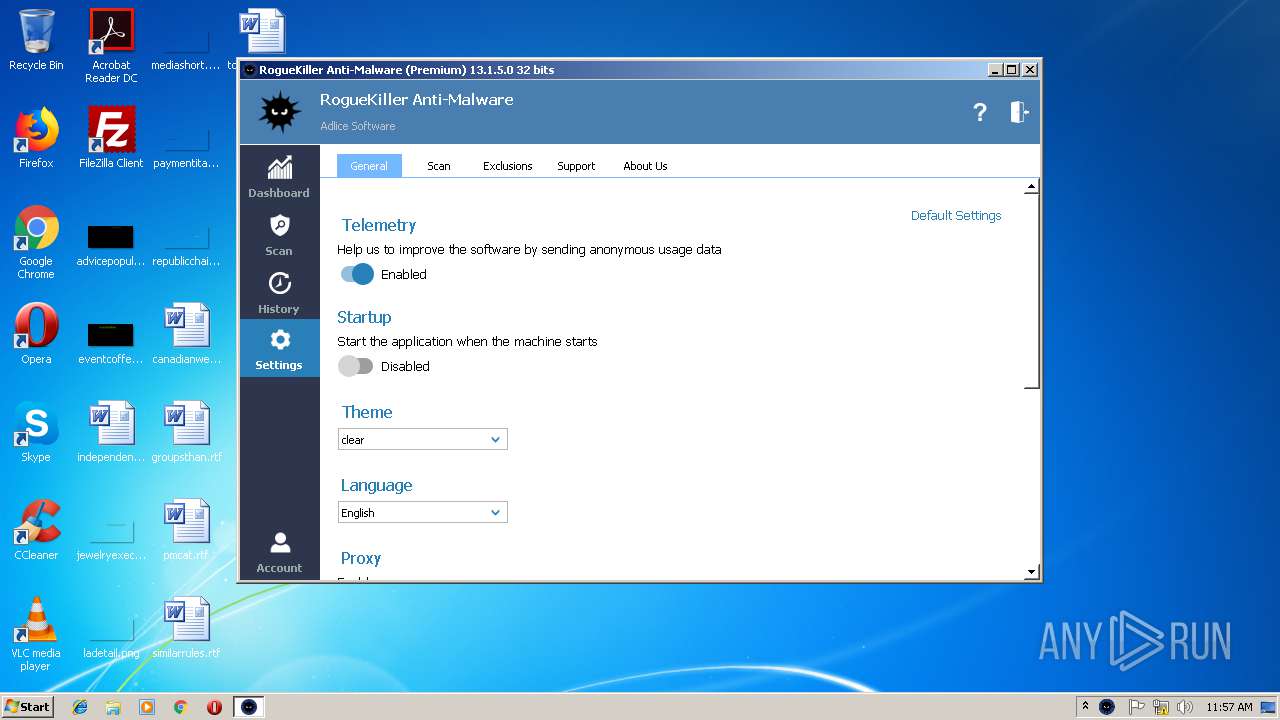
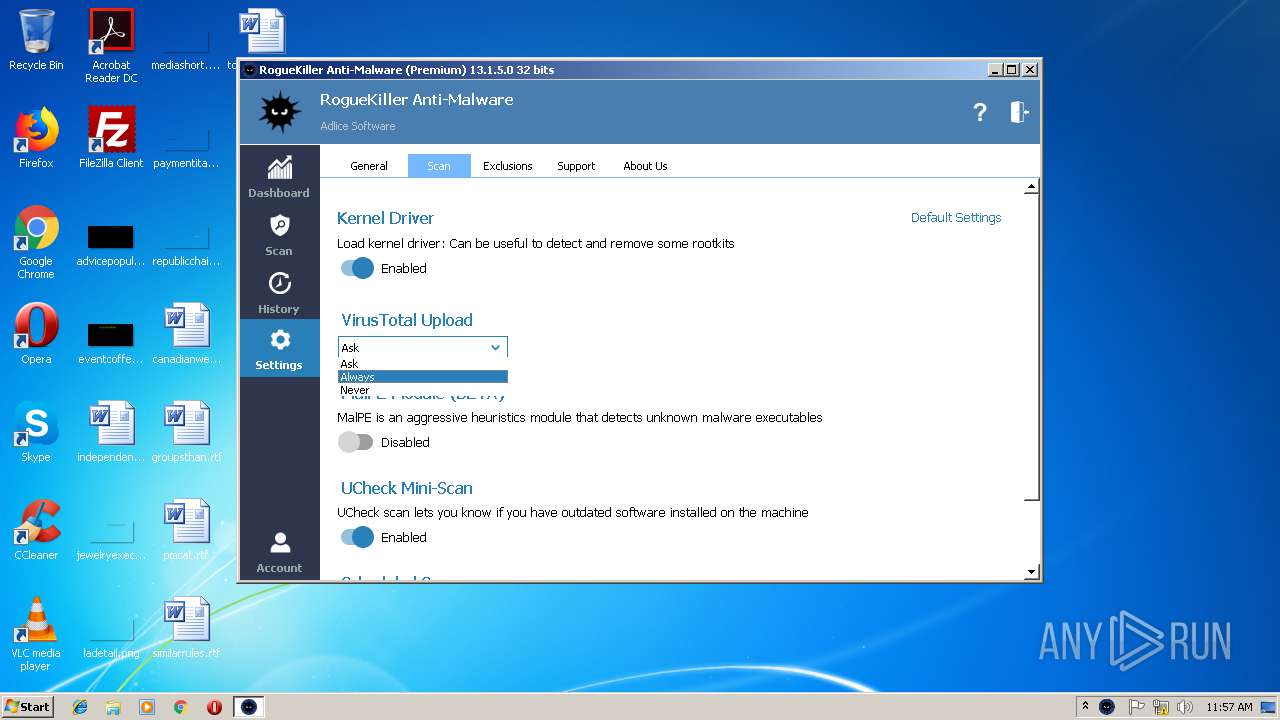
Application was dropped or rewritten from another process
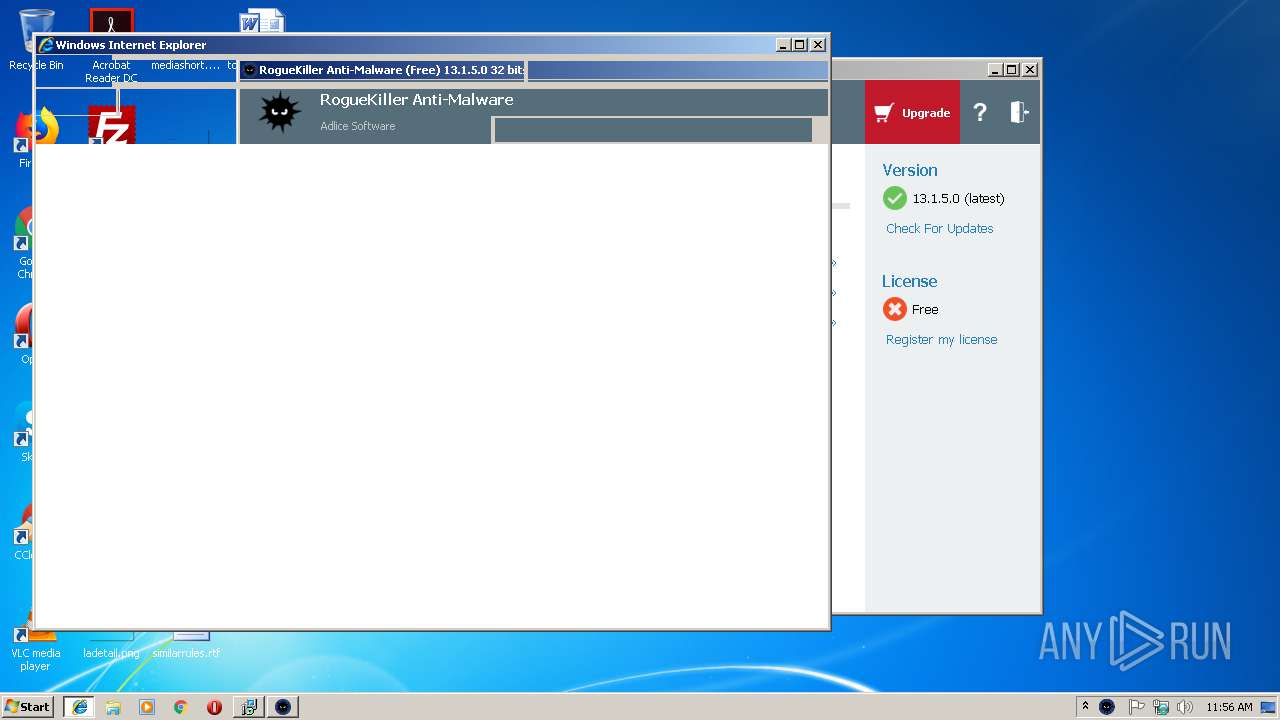
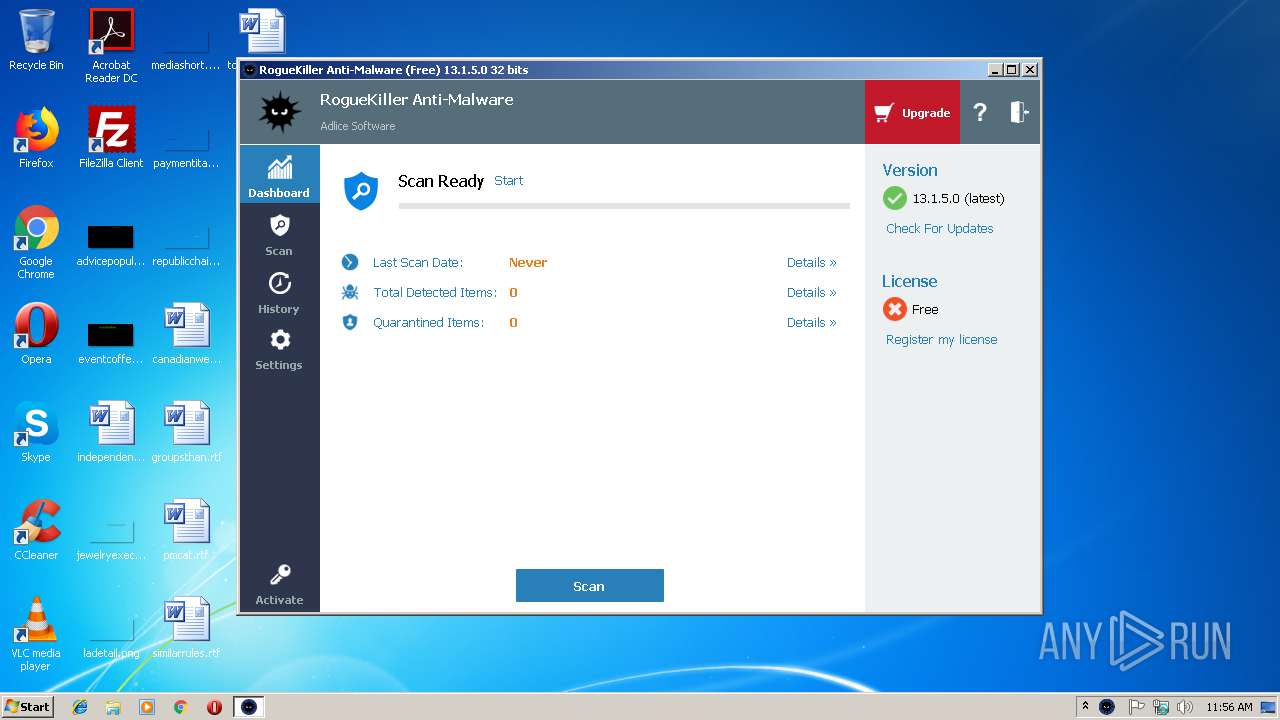
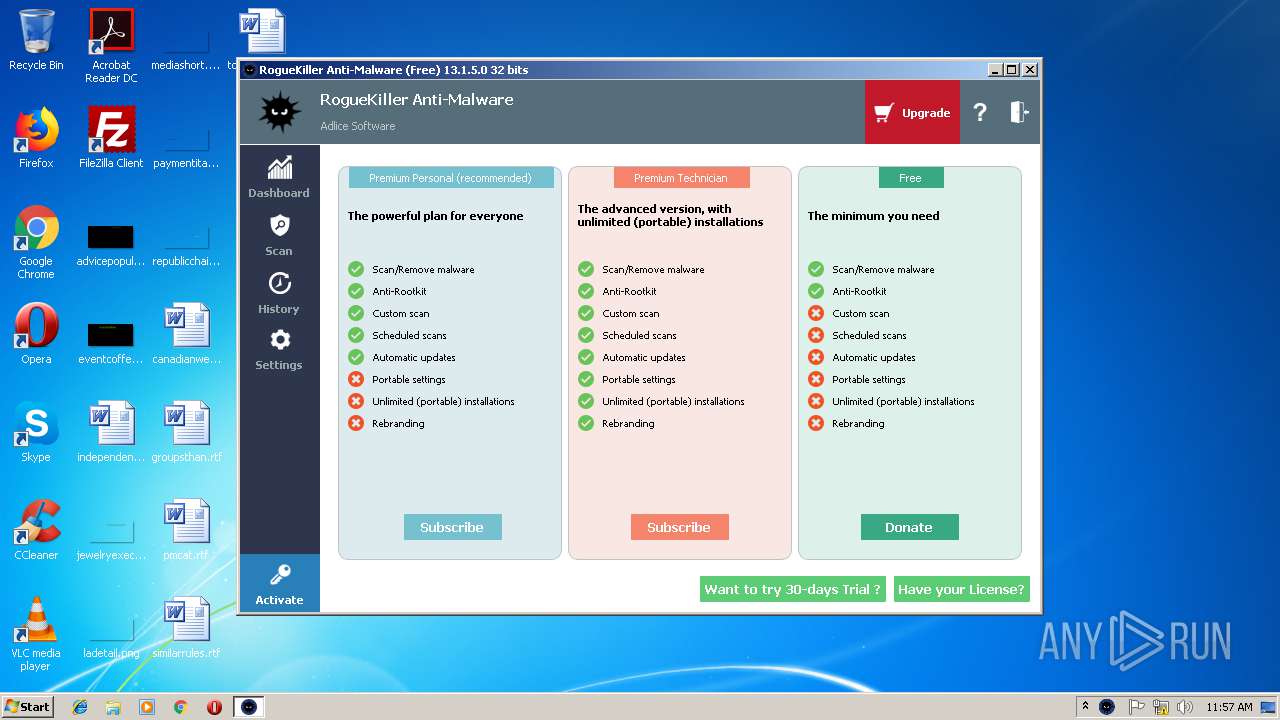
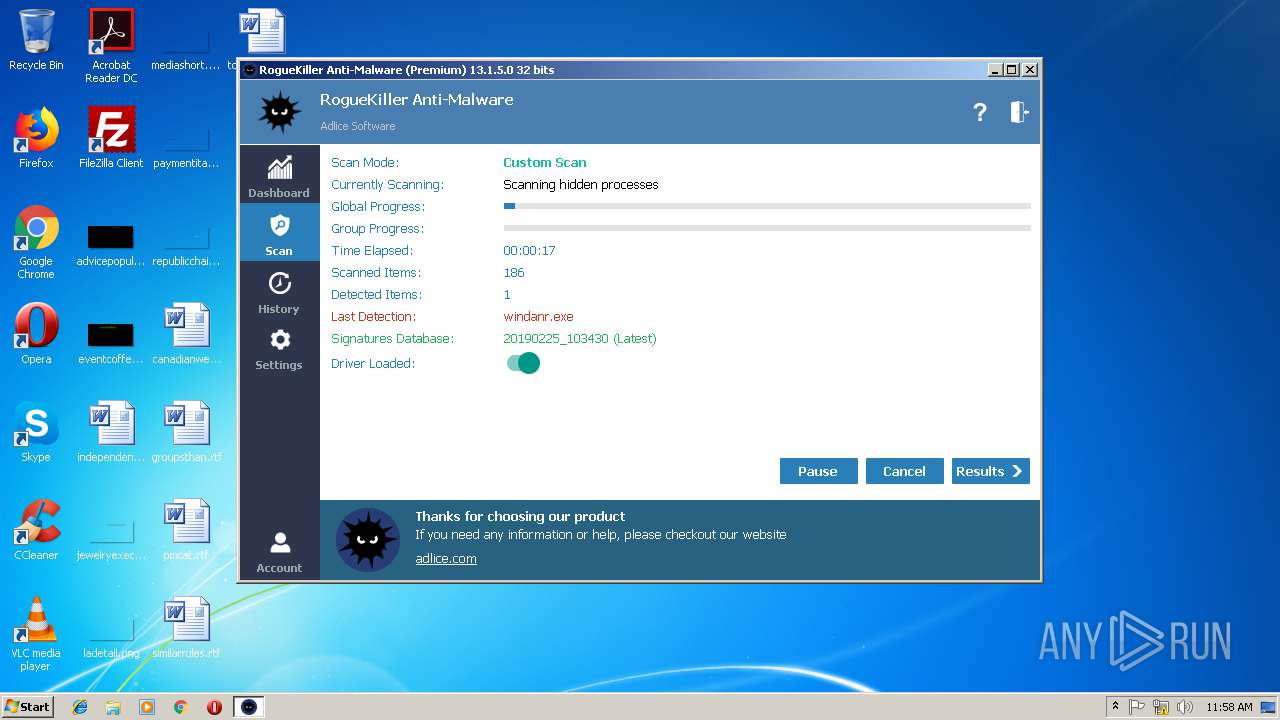
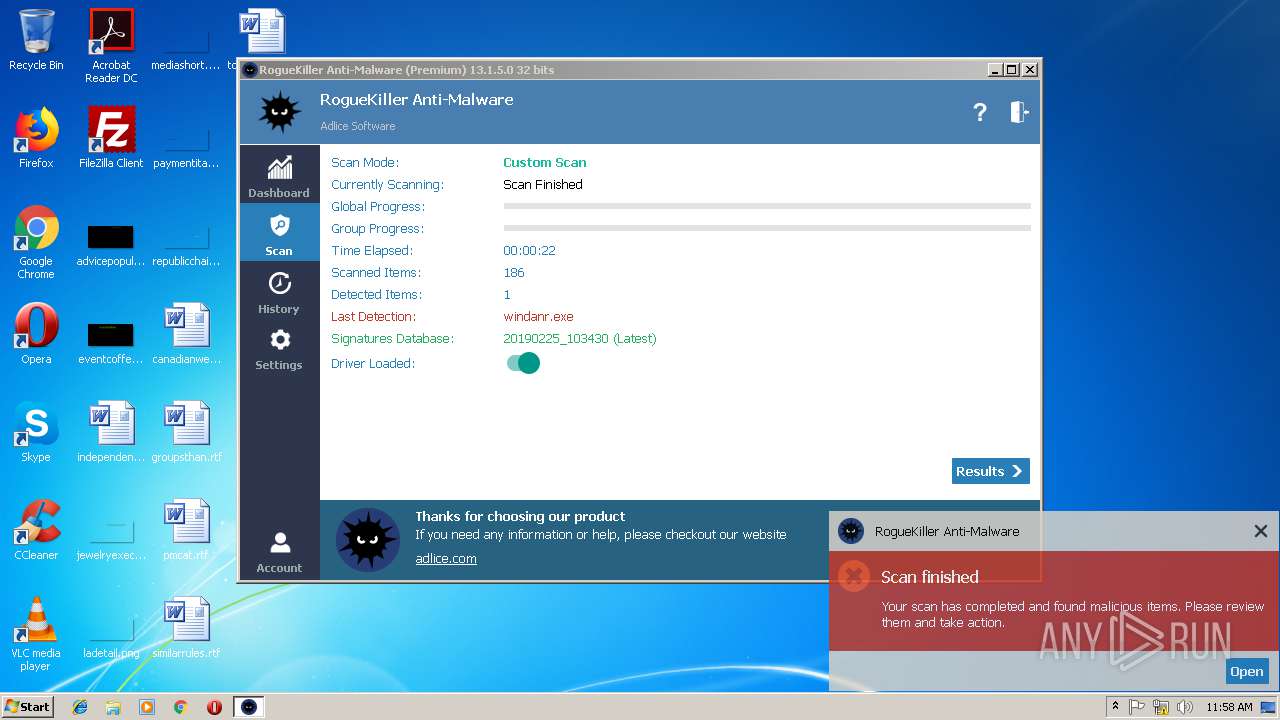
- RogueKiller_portable32.exe (PID: 2228)
- RogueKiller_portable32.exe (PID: 3956)
- _iu14D2N.tmp (PID: 2164)
- unins000.exe (PID: 2476)
Loads the Task Scheduler COM API
- RogueKiller_portable32.exe (PID: 3956)
Loads dropped or rewritten executable
- _iu14D2N.tmp (PID: 2164)
Loads the Task Scheduler DLL interface
- RogueKiller_portable32.exe (PID: 3956)
SUSPICIOUS
Executable content was dropped or overwritten
- fastdatax.exe (PID: 3028)
- fastdatax.exe (PID: 2288)
- fastdatax.tmp (PID: 2896)
- fastdatax.tmp (PID: 4080)
- chrome.exe (PID: 3608)
- unins000.exe (PID: 2476)
- _iu14D2N.tmp (PID: 2164)
- fastdatax.exe (PID: 3496)
- RogueKiller_portable32.exe (PID: 3956)
Reads Windows owner or organization settings
- fastdatax.tmp (PID: 2896)
- _iu14D2N.tmp (PID: 2164)
- fastdatax.tmp (PID: 4080)
Reads the Windows organization settings
- fastdatax.tmp (PID: 4080)
- _iu14D2N.tmp (PID: 2164)
- fastdatax.tmp (PID: 2896)
Reads Internet Cache Settings
- RogueKiller_portable32.exe (PID: 3956)
Starts application with an unusual extension
- unins000.exe (PID: 2476)
Creates files in the program directory
- RogueKiller_portable32.exe (PID: 3956)
Low-level read access rights to disk partition
- RogueKiller_portable32.exe (PID: 3956)
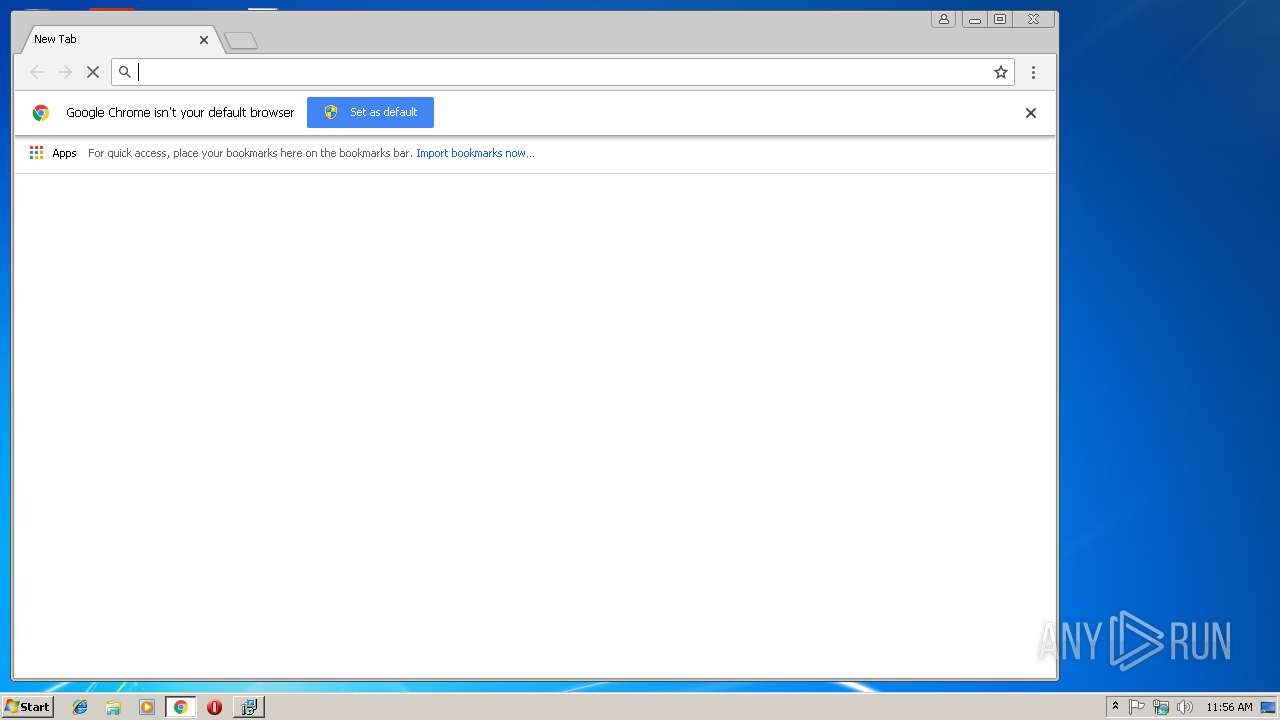
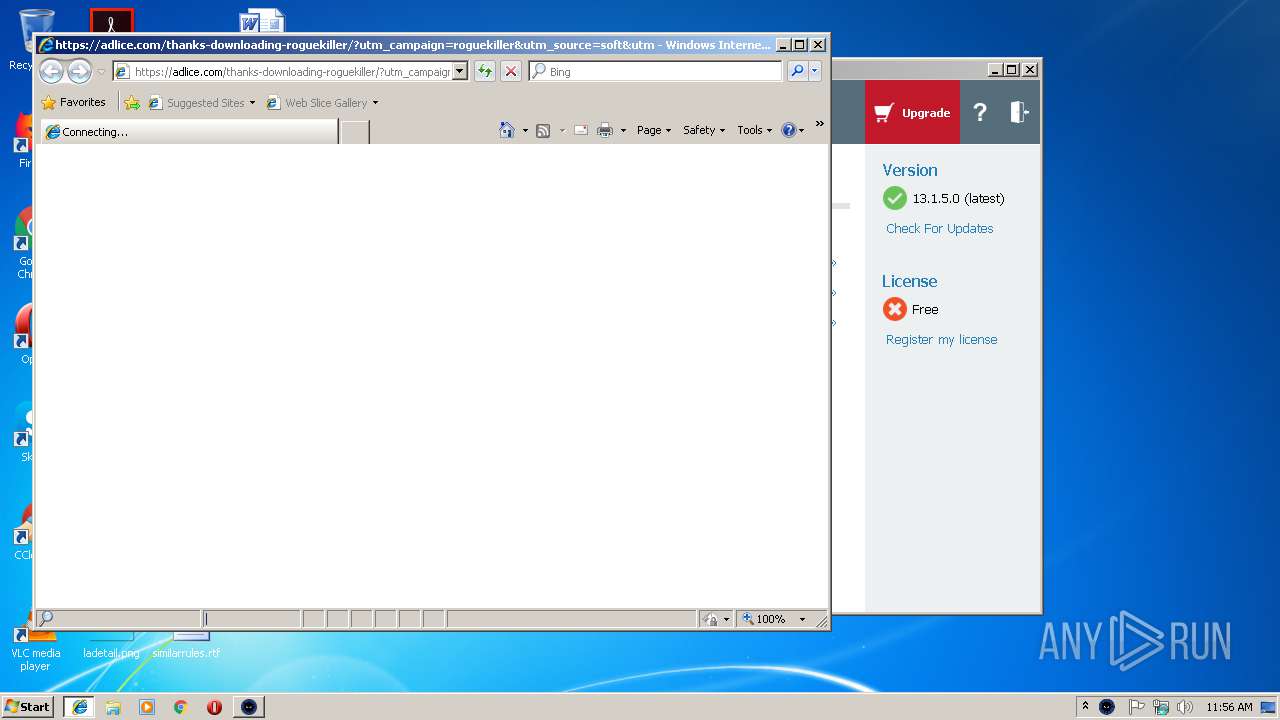
Starts Internet Explorer
- RogueKiller_portable32.exe (PID: 3956)
Starts CMD.EXE for commands execution
- fastdatax.tmp (PID: 4080)
- fastdatax.tmp (PID: 2896)
Creates a software uninstall entry
- _iu14D2N.tmp (PID: 2164)
Creates files in the Windows directory
- RogueKiller_portable32.exe (PID: 3956)
Creates files in the driver directory
- RogueKiller_portable32.exe (PID: 3956)
Creates or modifies windows services
- RogueKiller_portable32.exe (PID: 3956)
INFO
Application was dropped or rewritten from another process
- fastdatax.tmp (PID: 2908)
- fastdatax.tmp (PID: 2896)
- fastdatax.tmp (PID: 4080)
Loads dropped or rewritten executable
- fastdatax.tmp (PID: 4080)
- fastdatax.tmp (PID: 2896)
Application launched itself
- chrome.exe (PID: 3608)
- iexplore.exe (PID: 2772)
Creates a software uninstall entry
- fastdatax.tmp (PID: 4080)
- fastdatax.tmp (PID: 2896)
Creates files in the program directory
- fastdatax.tmp (PID: 4080)
Reads Internet Cache Settings
- chrome.exe (PID: 3608)
Changes internet zones settings
- iexplore.exe (PID: 2772)
Reads settings of System Certificates
- RogueKiller_portable32.exe (PID: 3956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | - |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.13778 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
76
Monitored processes
34
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1820 | timeout /t 5 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1824 | cmd /c for /l %x in (1, 1, 2) do del /Q "C:\Users\admin\Desktop\fastdatax.exe" & timeout /t 5 | C:\Windows\system32\cmd.exe | — | fastdatax.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2164 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Program Files\FastDataX\unins000.exe" /FIRSTPHASEWND=$101B2 /sn=QmE_NcSx0aubLWtyDwM4GiW68r98rA_XTtM3UhQk2je8sivIDJl92kViu-aPhzRkdoG5DQpK0Y3H4C5tEr5gEhQRjNPU6tYtwzlVkFCbomUX5edElnYfm3mbozITMMz-r7ojpsOz4-QI4CI006UyHTSBbq4rFXdDPfed7y5I5pNeAq51A_98f1HhMst65MwkCyQIhAHcP_gH9q0So6OBaCiBkaDktPlaexMgRNYV7NyEpb4CXrUe9LHKUkttSxBZ4_tkOpkoxRjjkMalS2hsRygEfgQMEe7PBv-EZvq0W13R80w6AwSphx2JcazVtvGLKoudscNMD66zYKW8xrgvoSobCWYcYeNN1VfCdhB0Sp6D-SS_fmwP_-ygI31_h-etFT5LwGBlnK-y1UMWS_CwoKtfaDVCLex9nYcyx9X00Yyn99fWl7YX1ds1_-tcfOTRFhTT5Pp1yPqKLayji3eLPfHv1ksVMiTpt8Z9XeoG7pxs0u6C67SWCNEzybDYPMi6dcv1rhyvcDPyNq68H418TclDs0lOms-5hYljmpHfur9Z7Fl8uS_1DxNsOsP0OT1VP_MTnJM9pbdI4x42HNIKVU97dDco0R4T8ClRp-O0Jv5AMEhfD11G-6SfQLR5izVZ | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
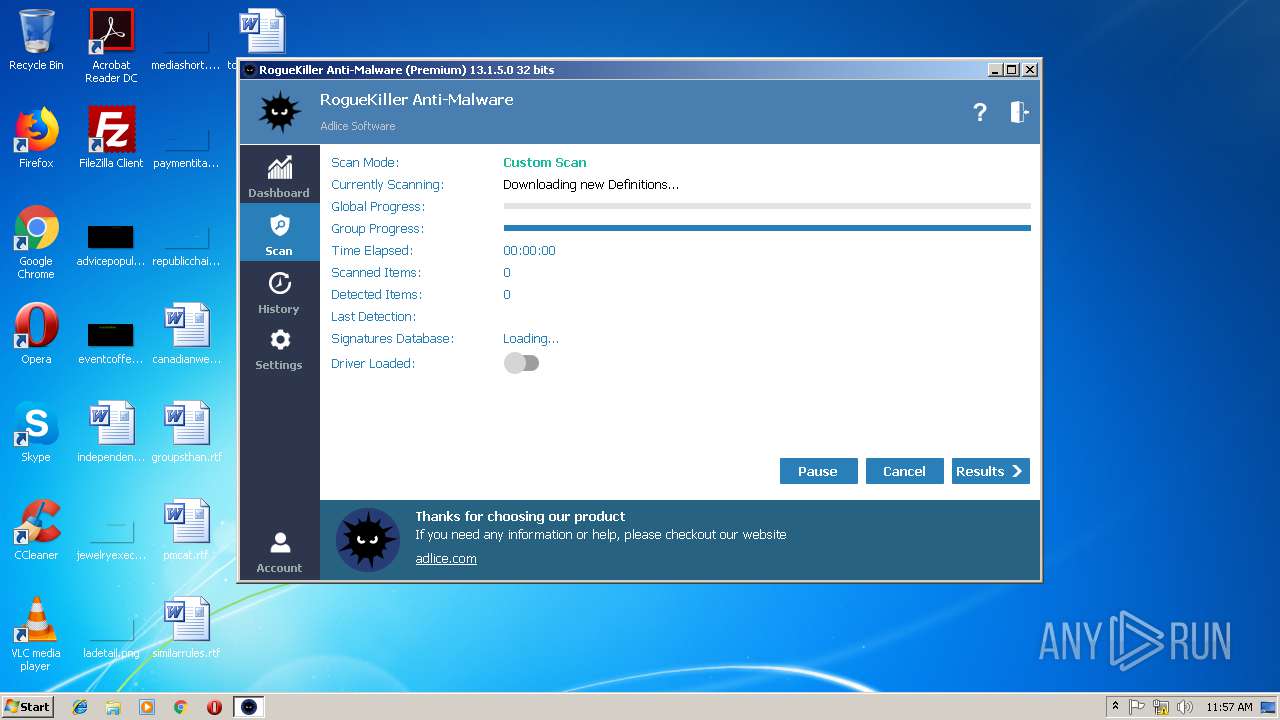
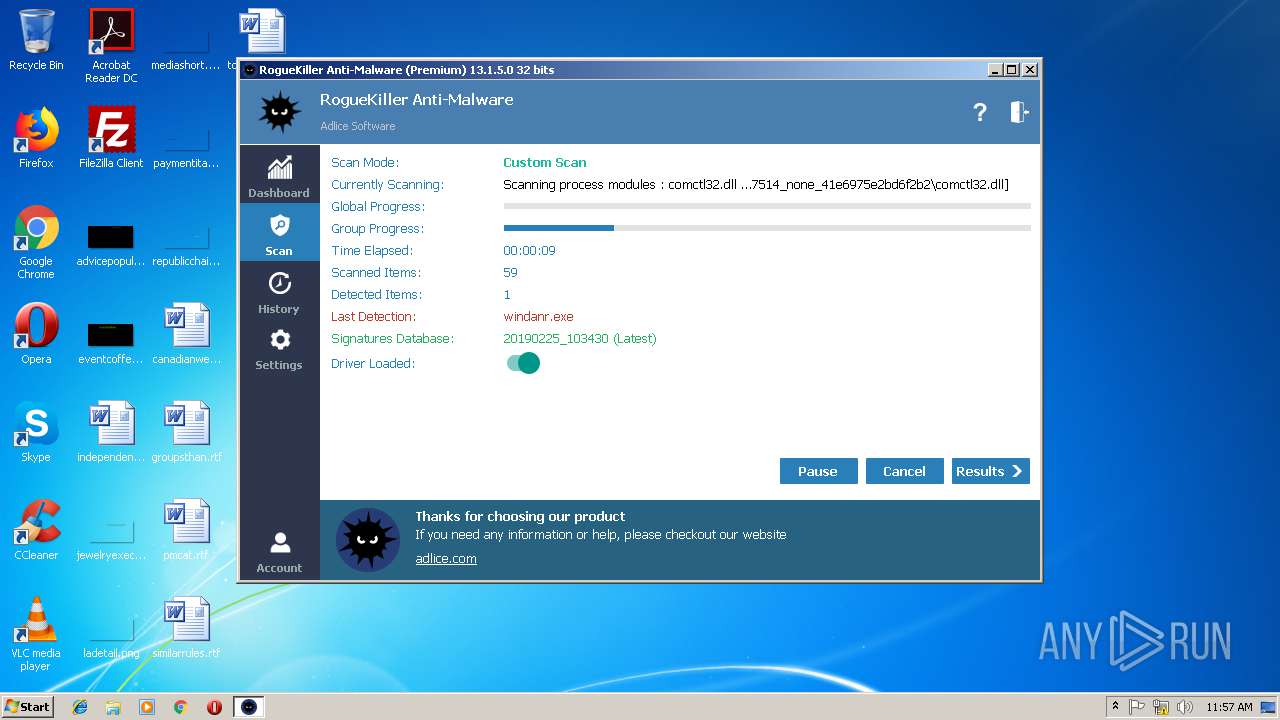
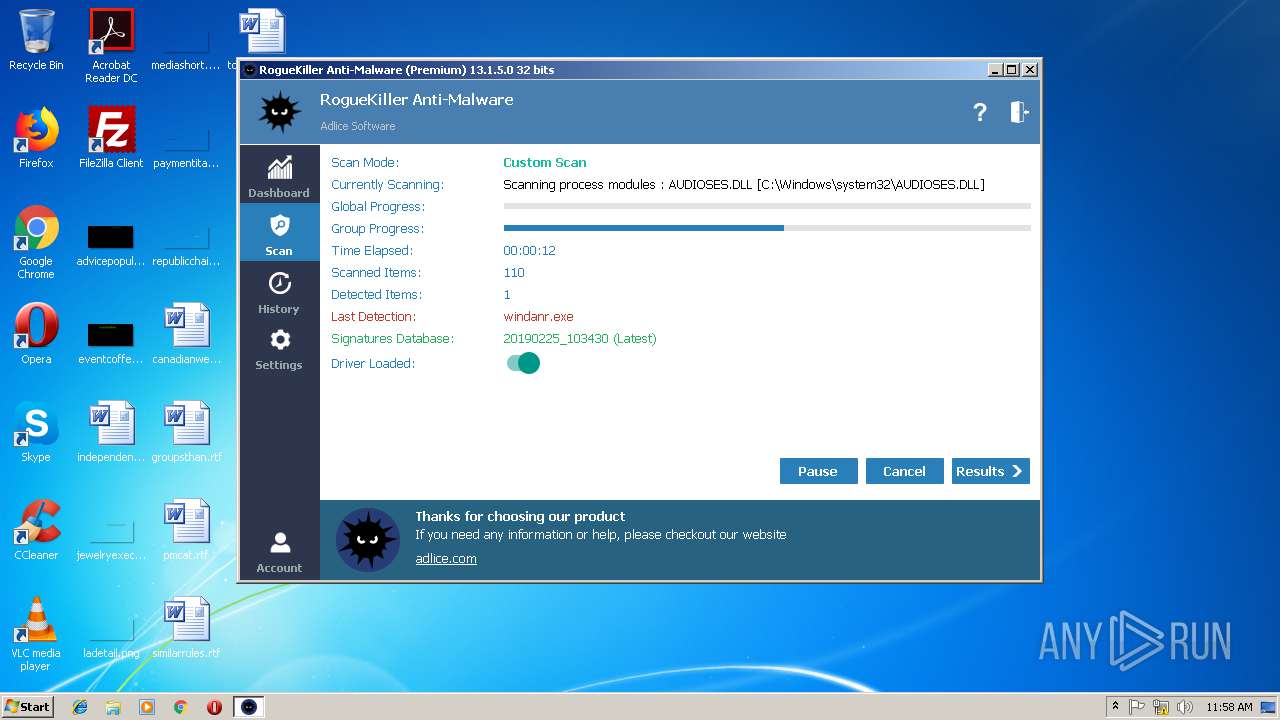
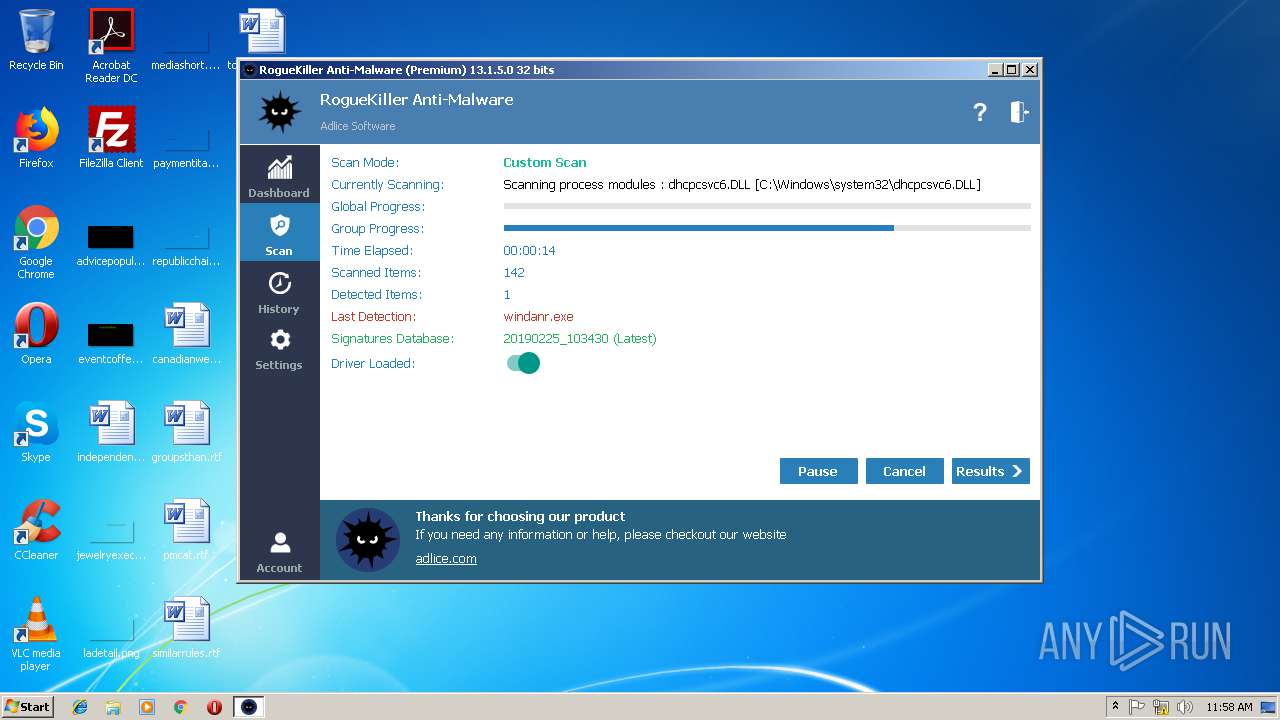
| 2228 | "C:\Users\admin\Downloads\RogueKiller_portable32.exe" | C:\Users\admin\Downloads\RogueKiller_portable32.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,2041502633711197072,16544547729795888394,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=832FD2E790931CCA717D46C671133612 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=832FD2E790931CCA717D46C671133612 --renderer-client-id=6 --mojo-platform-channel-handle=3516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\Desktop\fastdatax.exe" /SPAWNWND=$10122 /NOTIFYWND=$50108 | C:\Users\admin\Desktop\fastdatax.exe | fastdatax.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Exit code: 0 Version: Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,2041502633711197072,16544547729795888394,131072 --enable-features=PasswordImport --service-pipe-token=CAC380078A44B07F7A66CBDB38E0669D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=CAC380078A44B07F7A66CBDB38E0669D --renderer-client-id=5 --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f4c00b0,0x6f4c00c0,0x6f4c00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2456 | cmd /c for /l %x in (1, 1, 2) do rmdir /S /Q "C:\Users\admin\AppData\Local\Temp\is-51GNV.tmp" & timeout /t 5 | C:\Windows\system32\cmd.exe | — | fastdatax.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2476 | "C:\Program Files\FastDataX\unins000.exe" /sn=QmE_NcSx0aubLWtyDwM4GiW68r98rA_XTtM3UhQk2je8sivIDJl92kViu-aPhzRkdoG5DQpK0Y3H4C5tEr5gEhQRjNPU6tYtwzlVkFCbomUX5edElnYfm3mbozITMMz-r7ojpsOz4-QI4CI006UyHTSBbq4rFXdDPfed7y5I5pNeAq51A_98f1HhMst65MwkCyQIhAHcP_gH9q0So6OBaCiBkaDktPlaexMgRNYV7NyEpb4CXrUe9LHKUkttSxBZ4_tkOpkoxRjjkMalS2hsRygEfgQMEe7PBv-EZvq0W13R80w6AwSphx2JcazVtvGLKoudscNMD66zYKW8xrgvoSobCWYcYeNN1VfCdhB0Sp6D-SS_fmwP_-ygI31_h-etFT5LwGBlnK-y1UMWS_CwoKtfaDVCLex9nYcyx9X00Yyn99fWl7YX1ds1_-tcfOTRFhTT5Pp1yPqKLayji3eLPfHv1ksVMiTpt8Z9XeoG7pxs0u6C67SWCNEzybDYPMi6dcv1rhyvcDPyNq68H418TclDs0lOms-5hYljmpHfur9Z7Fl8uS_1DxNsOsP0OT1VP_MTnJM9pbdI4x42HNIKVU97dDco0R4T8ClRp-O0Jv5AMEhfD11G-6SfQLR5izVZ | C:\Program Files\FastDataX\unins000.exe | fastdatax.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
1 186
Read events
990
Write events
182
Delete events
14
Modification events
| (PID) Process: | (2896) fastdatax.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 500B00009C22CC2001CDD401 | |||
| (PID) Process: | (2896) fastdatax.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 2705700BDDB2C84A834D27544F9B2670A2F9786B3B38534A8B75700A6A4E5243 | |||
| (PID) Process: | (2896) fastdatax.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2896) fastdatax.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2314558E-BA6D-4152-FBF1-E9BB18486C44} |
| Operation: | write | Name: | cd77f991 |
Value: 01EF84EDF805000100000040000000400000004D2A3A008F6D5AAD931D3538EDC67DC3CE8EBB053214E638203547DB7BB2AB576F8CBF83CBC5514353F4CA4F773BCB61E0F3C5CAC430968940E2E2AE45931A012BE8CF922B25B777EAB41E48C686D0B0 | |||
| (PID) Process: | (2896) fastdatax.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2314558E-BA6D-4152-FBF1-E9BB18486C44} |
| Operation: | write | Name: | cd77f991 |
Value: 0183900167050001000000400000004000000013104CA3699B1C2BECA350C78743B4C2A69E46B1C37F6C72B4BC1E8D406C7D11E722A4D0DF42B884472582892664DE831BFBF04D12D2F495936B3D3DBCDFC6EB8BE5E4CCD7BF30EE26CEAC41961D0CEC | |||
| (PID) Process: | (2896) fastdatax.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{2314558E-BA6D-4152-FBF1-E9BB18486C44} |
| Operation: | write | Name: | 7e34172e |
Value: 0170124F180500010000001C0000001C000000C6869BD6E91A9F9A847E29C82FB6D27E28C75D6F534D9092230A48235BDC0CB88D67F08B854C608233EC73D5 | |||
| (PID) Process: | (2896) fastdatax.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{282D8EF8-3404-BF5F-0E2A-BF3DDB91D98B} |
| Operation: | write | Name: | cd77f991 |
Value: 011D65CBCF050001000000400000004000000000ABD48131F289145695AEDA3CFA5F9355DCB50059A63041C8E5C00C378F63AE698CF0A21360A9E3AEE7CCBEDF7DEE4712D89B8FBBC87D52DA8F5CFBA318EDD29BBD8AA26B491F47E357F6D45C8D5035 | |||
| (PID) Process: | (4080) fastdatax.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: F00F0000AAFD972501CDD401 | |||
| (PID) Process: | (4080) fastdatax.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: 20572F6D136BCFC42CFD48E11C5501ABEE78B72A5A989968DA36DCF16858BADF | |||
| (PID) Process: | (4080) fastdatax.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
Executable files
16
Suspicious files
71
Text files
66
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a1c60211-4d02-4610-be63-e18f436a8975.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19ceb0.TMP | text | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 4080 | fastdatax.tmp | C:\Users\admin\AppData\Local\Temp\is-51GNV.tmp\xehcmjc.dll | executable | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF19ce81.TMP | text | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5a06cc20-6481-48de-9370-7d3179f06f58.tmp | — | |
MD5:— | SHA256:— | |||
| 2896 | fastdatax.tmp | C:\Users\admin\AppData\Local\Temp\is-JOG41.tmp\xehcmjc.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
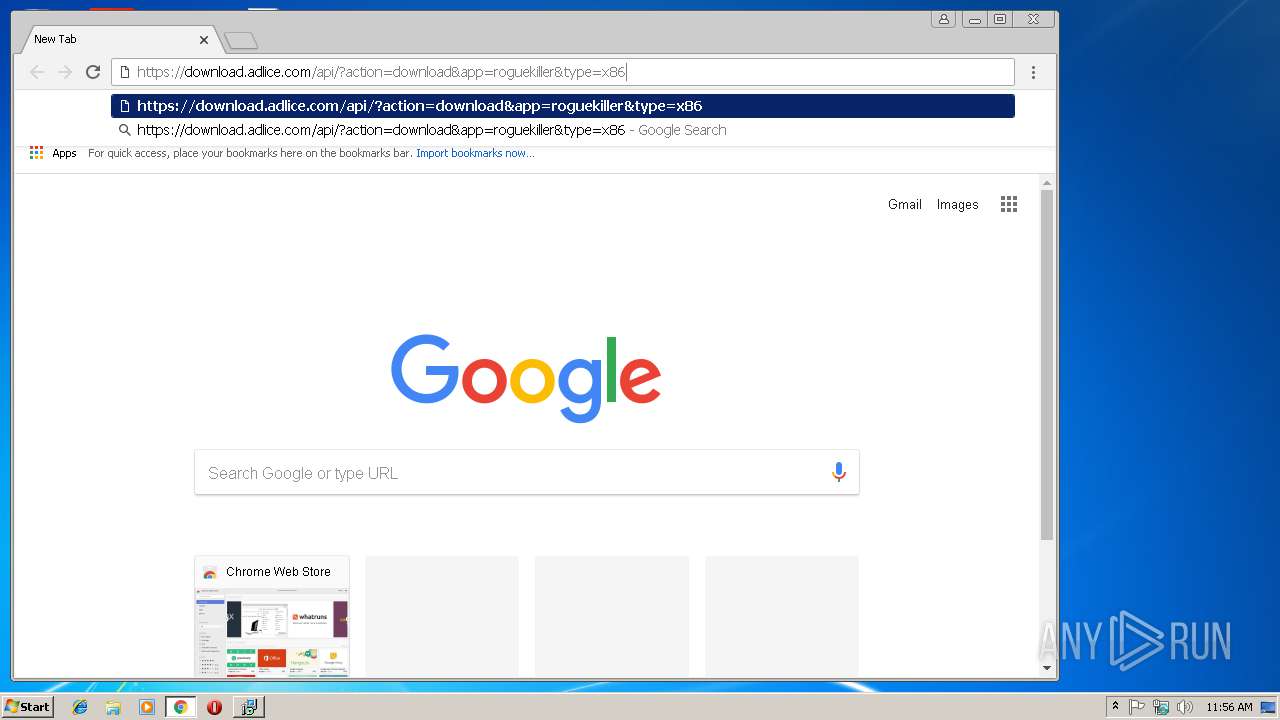
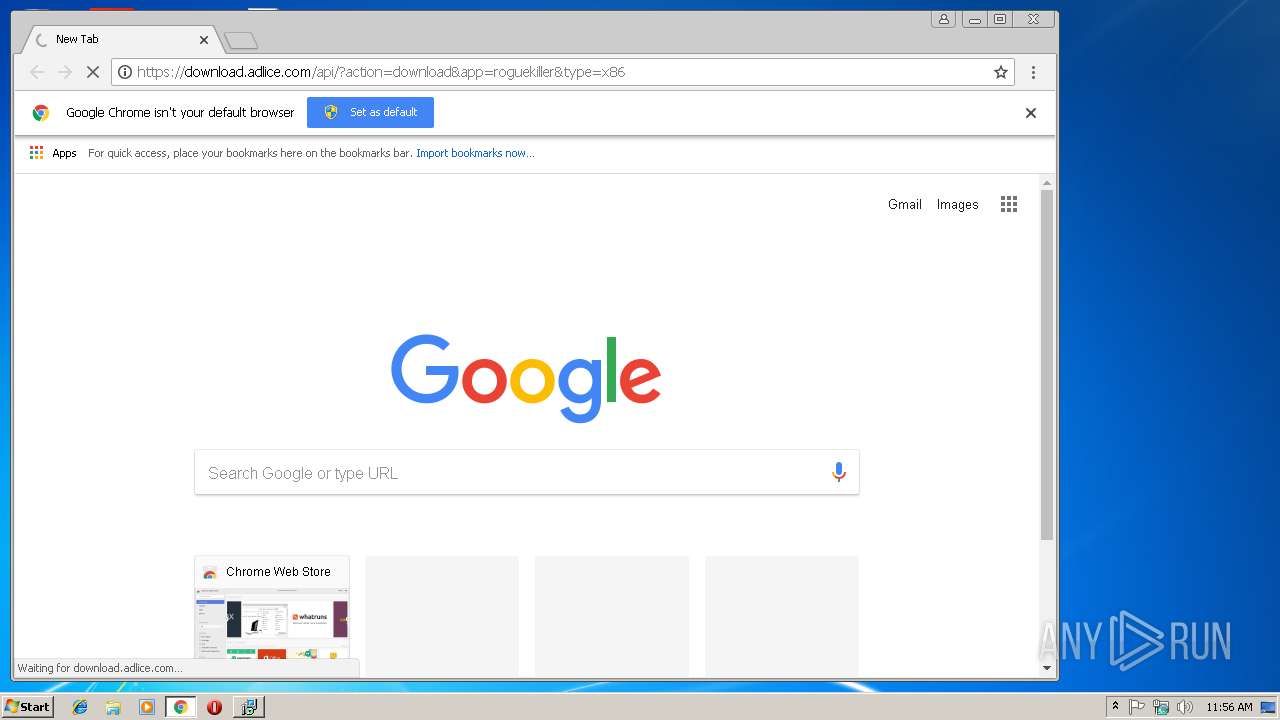
HTTP(S) requests
7
TCP/UDP connections
37
DNS requests
27
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 503 | 81.171.17.144:80 | http://downloadhostnow.info/?ch=TD4tNv69awI9eKdVsJwg9oi5WcTJy2BYzUztq1EtsuoEXhjk4AZ1pI6rSqbBox0oUE985__MsCMwpC8ZUE4n9GOeDjwBZHqpaA5nR-cZf6qy-QXOD7Yjes3VLkZ34BVq0-Sq0BqvqGPzo8k0&ac=RAb_wg8oZPbbGPxtaYVh4JB3sKMif-6TG_pg8z_QxR1Wjxw53suLb2589Gs6mQwG9KSHXeXGDJeoo2eRmZEk5dSrzfmx6FfDDNLah-_NWZgYCwKZFfIfgihDA-C81kVtRiAeihu426ww3MTlWcg93qS06s6tAlrZ1eYxiLi8_1lfij82lPbPZ5qyHVWCTg1V93L29OSX9HhVAKWUPzWB4y-9IJ6Qt8wGAWMniFFM8sbHx7SI0GLKAiopxIXw6QqhB7xfkXD3uWcEuaUNDYDRXuKaOnrxP8X9X7A9HSzQfKo0ozSeAm6pCIvWhpFtWFhiTrpqIR7W23kMpcp3l778aYT1fXqviGrI-PSqcVvLoNg07a24aFTIgEYLnPSdK-QWsNF6WpTMIwzA8k1xPyHWwTAIwng6MA3E7YaMgAhCU5dGWtu1HuJvjoAbesHVpY_O3DLvnCkaYYnObX6k6xOmDhGRPrWOTTxuYzhmpu047lhBh3r0Q52LT3xzwLURHo1raaUFVIIIhjokgUItHKei_ubmIaMkJDFap4VM-yHH1321o2oyf51E4apKkjMVryqfGuert6gLqG83yBnzgZHDe2m75L-pyOGFAy-gPnkp8ZV13elUeBl0xIhSfPJucarYh5mcN3r1ATukh6d81ymPJLuaDtAlXvGduJNnE6caf6QEl_Kc3XdHNBOUDot8_nO9f9E6EXnPSDt_90DeXwTuo4eKvGPV5OXnNhVQqaUBH_tTPu-3qNW4QnWuUuZYwJU-2u-9RMCO9eAkM-GRbfnnan6SoNZP29APctBjV6MHiXnfetcmAsCn0f6wr4NwSltk3rLYil0sevLATw-htPAhNtjnJLazXyKZ84pL66VHAp3V4T5kEgB_jpHPeKel7_o-1MeuvcyLbdgnKqEnDHhyXaIBxIN_6kEFC9Bsu5yy6NYf4f9T_LZ8mq4SAQiFxgGUR9wwKObYN-vIY-JvfXOz5UoK_noUhOPXI9wHCKxGmlxjvWgsaU0WGfzpLRV2tWxcamp69Hb399ZPjcmdH_VHkSRfJkTzx201MWBZ742DKQ-CI_SdZhDSoBJFlueZbTgb3BgM9d9eApPUDC6PM_FfW4Kv0QW1XprIJzA-QHtaKBbeqxcLLrL-NsVxgOGSle8IjlfJ1UxPBIukk2ai&tr=u-6Tvf5vcc79HhcnYXoMmQOENmGRwfTvZ_xZaxotBv30v8swq3Kj77qDdZ_DMI-munHgTN_C2iAd1WPlXx7b-ZiPMY9zV1y5uyzcMPWw0A5RBFqfgjf7hp8xBxij7tszdbn3XfWKIg3AAK3kHMI5guggv-QTXi5NQffWA7IJ0QS4fJJodJEF7dgkY0V6I3SsrYF6K9PWAnzt7O3bjcxQO5HAHjiEiQ5d97YgbQXVZ3ZEJc554LFFWVsTfKFbvw55V0FHHLAb-mfhrf6Ul8dYvSN4CSQnpnDH-NIGgBRkA0yUAn8bETHPAubJaaC5ON4AFs9gDMyNxI6NV99UiYl4qfJd | NL | — | — | suspicious |
— | — | HEAD | 503 | 81.171.17.144:80 | http://downloadportal123.info/?ch=RgUN-p_WHi2A-Sjijc4ShgDv57zaiOGGee2xUnX97sGBRb1Tlf3rKX3dWMYxYMA9Moqyr2hhd7utRj-iAff9zgnhPqqPQsMdbNeoYnYsFbjAJT3fv7LSt-CTeyD6NYmPsmwe9PSmhv6bk2ai&ac=tny_8Jnxz2vIA3nehdRyyMR5stzOMOKJwqahfl3G2qmRHl6BRjzNDmc7GPvKwimrqq_6URPdAIMYCfzWnhAeHA_CFQxw5tf0D5FAL01wlBgvVTto77s3rfR0nwDOf25av-wZrcDQDmawTn9_B6yI3YgrzUaKdOX9hEeD4YfHaAGFJ5Gnxy2X1DJCO_cAqFhD5TGT_ONuCAkxZZycEonuCkcq54jUUJCwFG0R0tbvBbozlyjtwsy5xtxGzomESdN0zJuwV8C0Gzp5gf0mgTQUXLnZThcNI1-YVOEfyNSLlKTuUpeTz1XgTOc5NLNaqVu7ONyjhx-N4KcShR07xJEp1bUidP3KBNCOw2oe9pfzdoE4gRo5H0h2oQ31zDifmVjh_pMu3GqHU6PYdFQ2XJhg5VFww8DyP0uUbffR1UDCP2KNpUA-s2vwkv55VdnbLBcbbiq8x8d2scmy3djHotKVPdNRfK9XfCAQcQsFjwkT9-7M_GxhoRtSa_gCyGRUarjwaK6VuczcfBPjeZk_C91ejPbEAScBTG1CUcvnIxgqnLaVBO2LFoESmqLz8mHv3991xxnpVyj8166TqFmgxWhw25hWrWQ9Nw8w48WA4dyoCZYe4zoDtDm-4F6UoRcaShO195wX1Jjtk-xv7osHqzp08_TPQIAAy3SrgefXfVz6PUMwlUOWoE-pB8iM0q94Vg2oekF48C0lYCE5VcPUVfK9so3EtwA1ecG6hVzOF4ez8mnTQFmQDjIpGLfl5INp9Gw7shAUPqoYwJ4YKzYyMzVbXUJziGHHom3yqsyGO2WFjV8RmgtSA42z2yrJxLjtsHdeRRche2JznuylKXun6ZZ78pHWTbss519GiYiY0_ti6dalNjGH3Fkb5GUwx7zUSiQy0LyehvmTlFlRUgAt_ukKsRjQPd8nAbiRYwFz-31nVYFBxuDhqa51Jg5-7Au7pGJL-vgc3Y8YjOW4t_0XsIVE5pr4dpe4ah8NHMicr65g-qUIXOQx2P_U-PK-NHktqwp5JmQXfFBop-h413WEShavp7UI3EBkyNCE0TqxqFTxjE7qbwVyC_D9H5wz0IjMdDSCq97xVKyGHIcwNfUQplKWuw_15dH7pLSXlBHUTAlUzO0ZkEbFYBVWCumbP_1s-0sQUj-3aLbTocEU&tr=hIskk4Yv1zJJmIWlOY0ARcfF4RerVI0HDybZr2TiWl2Nw3HC-ks8QTNjX7ijgdwsk7LoYb0OpCe_6F5DQsN7vhaXLHd0pTZThzAeiSu4cl42_FZGm6ifdjp9fOqpISL9zs2d4oP27qOds5uX9WMPzst0Q6_2jpjw5DhmHpLNXrAApY45xjf4qXjCzELHlZvS2EOPB79UEpDLds7zRl_6pWuYqiKhVcaY8wljj0te8JCgzSAVGg-98naYikimcaf4f1YEGQ6zd7fbvxYJz-DQQgqe2bSLuRPR_lLi8S-Hs1FiJVOVX4ZBcitq-N8REmksyz7qJUrCwlJvSx50672uQ4Io | NL | — | — | suspicious |
2896 | fastdatax.tmp | POST | 200 | 104.18.38.90:80 | http://tm1.fastdataxew.info/ | US | text | 152 b | malicious |
4080 | fastdatax.tmp | POST | 200 | 104.18.38.90:80 | http://inf1.fastdataxew.info/ | US | text | 2 b | malicious |
2772 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
4080 | fastdatax.tmp | POST | 200 | 104.18.38.90:80 | http://ins2.fastdataxew.info/ | US | text | 2 b | malicious |
4080 | fastdatax.tmp | POST | 200 | 104.18.38.90:80 | http://tm1.fastdataxew.info/ | US | text | 152 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3608 | chrome.exe | 216.58.208.35:443 | www.google.de | Google Inc. | US | whitelisted |
4080 | fastdatax.tmp | 104.18.38.90:80 | tm1.fastdataxew.info | Cloudflare Inc | US | shared |
3608 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3608 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3608 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3608 | chrome.exe | 216.58.212.174:443 | apis.google.com | Google Inc. | US | whitelisted |
3608 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3608 | chrome.exe | 172.217.16.206:443 | play.google.com | Google Inc. | US | whitelisted |
3608 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
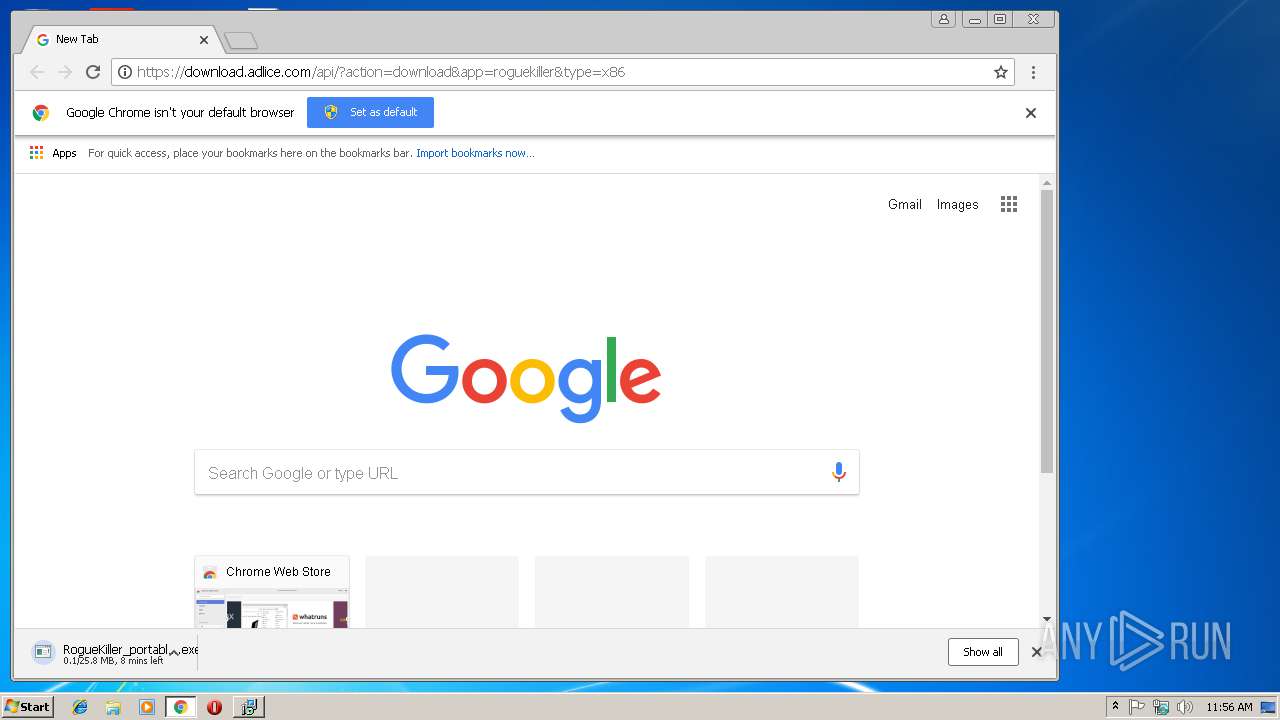
3608 | chrome.exe | 178.33.106.117:443 | download.adlice.com | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tm1.fastdataxew.info |
| malicious |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ins1.fastdataxew.info |
| malicious |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
download.adlice.com |
| whitelisted |
Threats
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|
RogueKiller_portable32.exe | libpng warning: iCCP: known incorrect sRGB profile
|