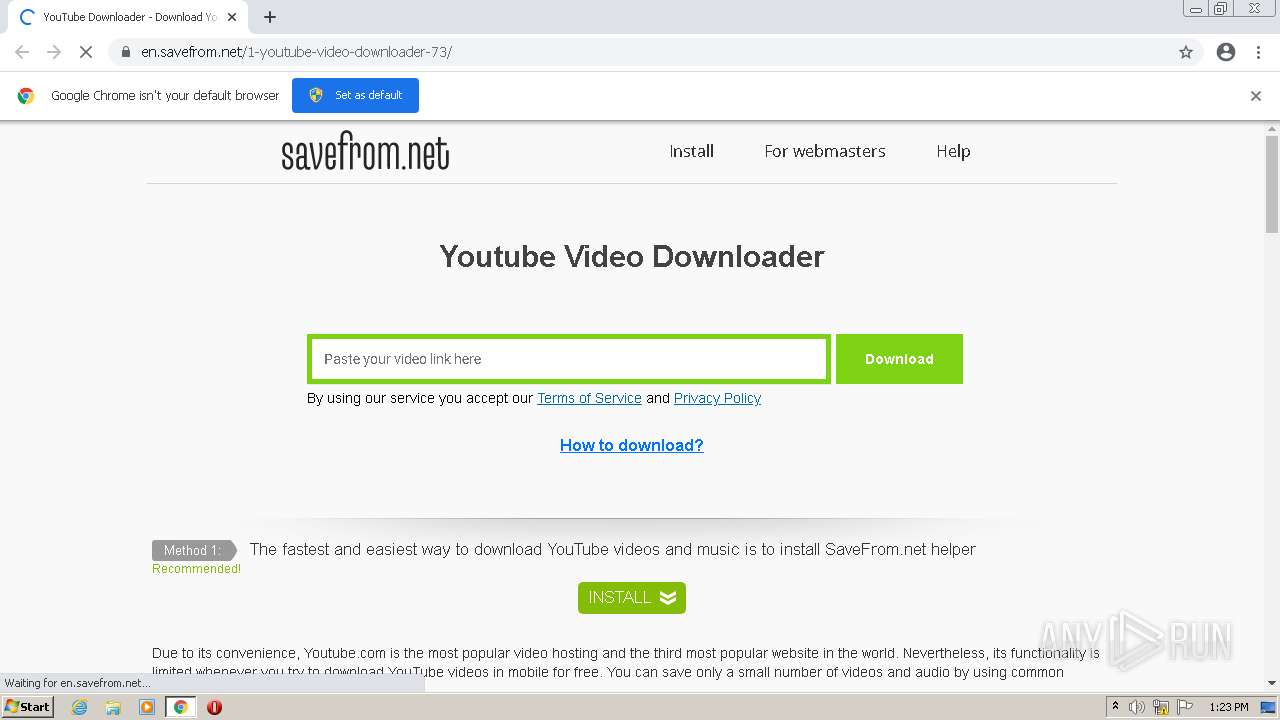
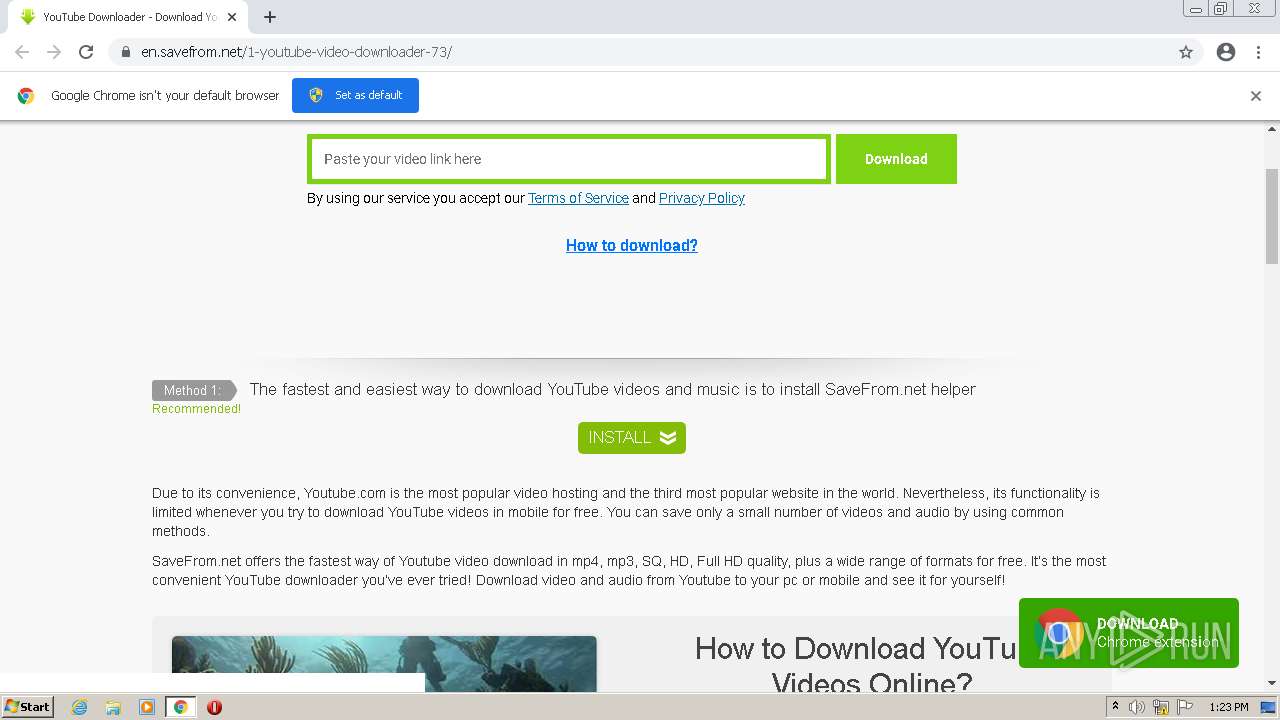
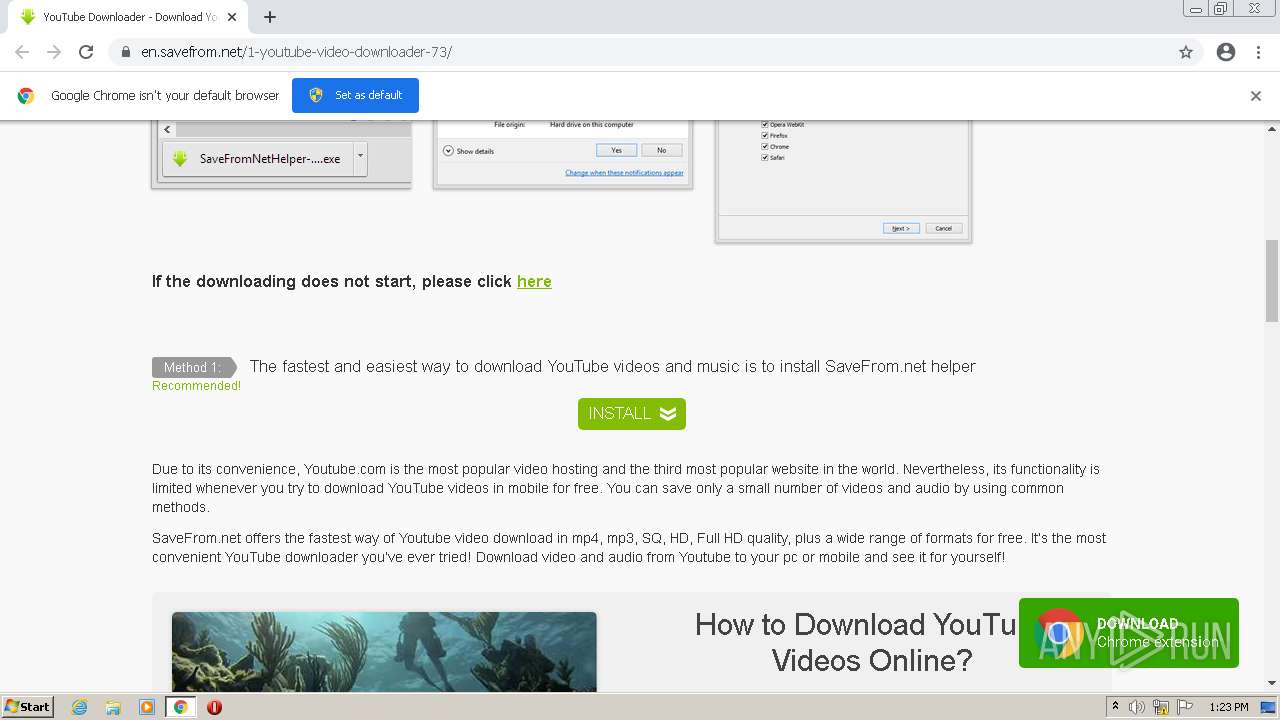
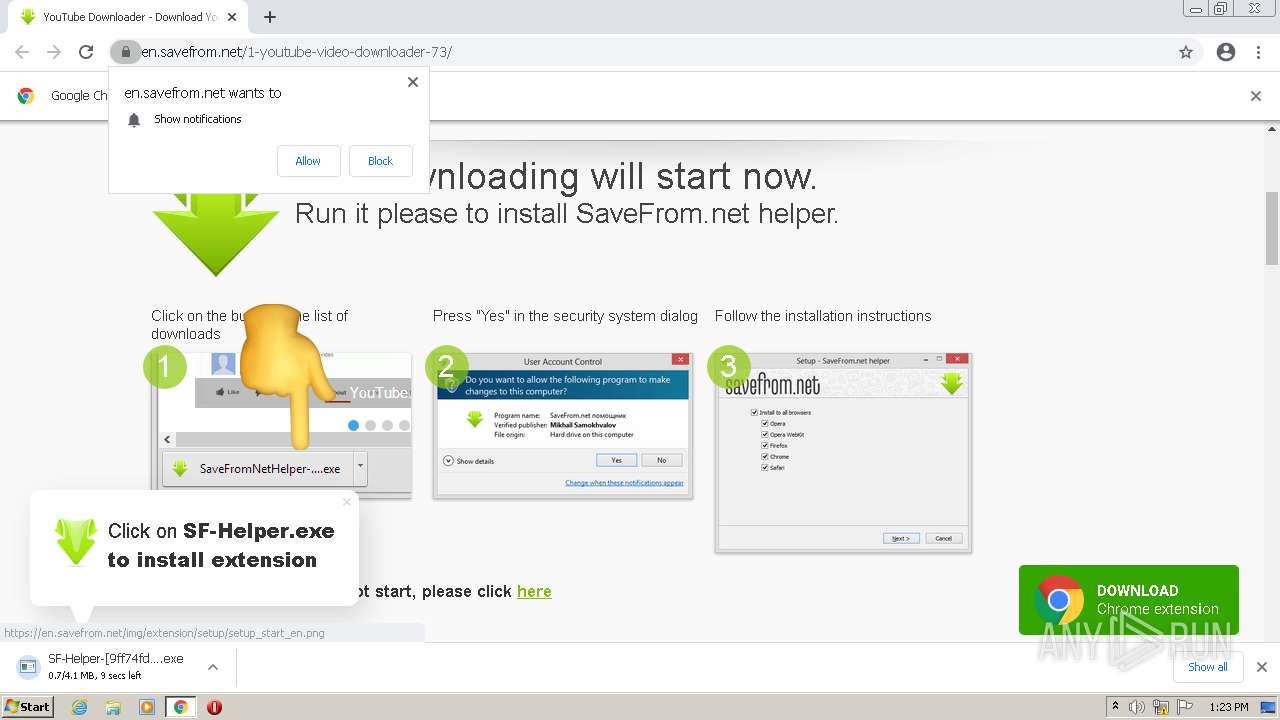
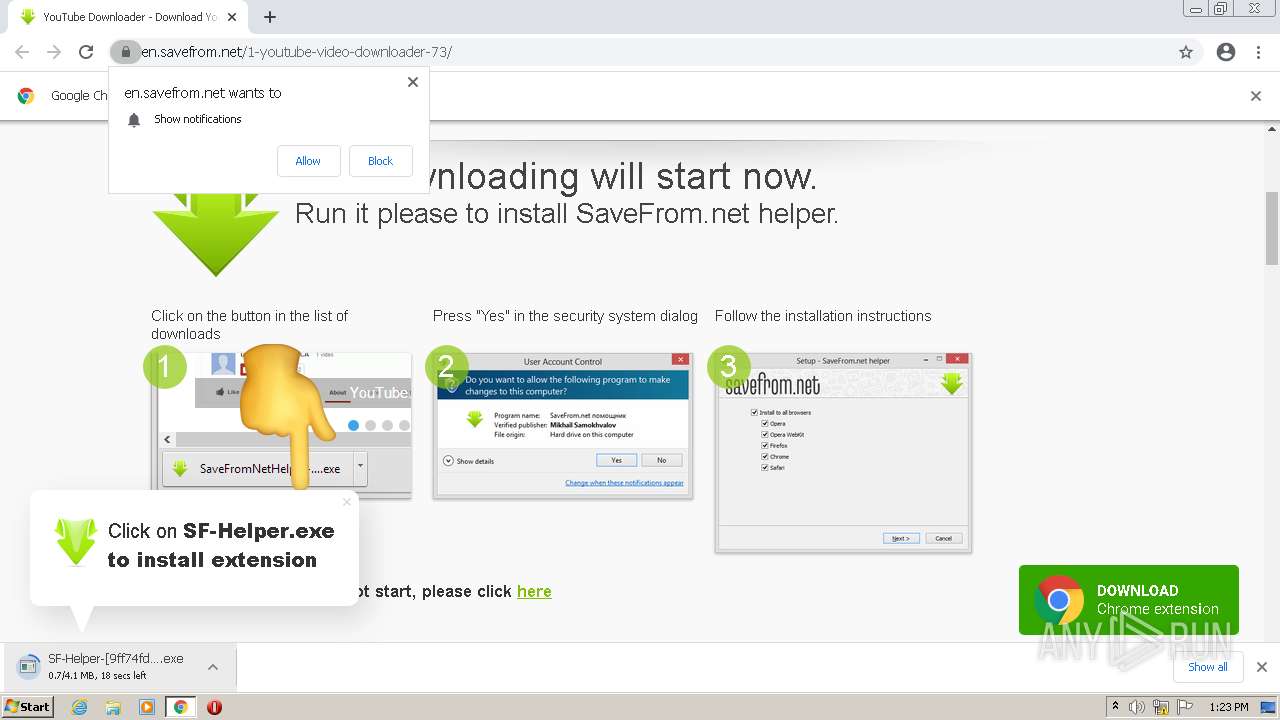
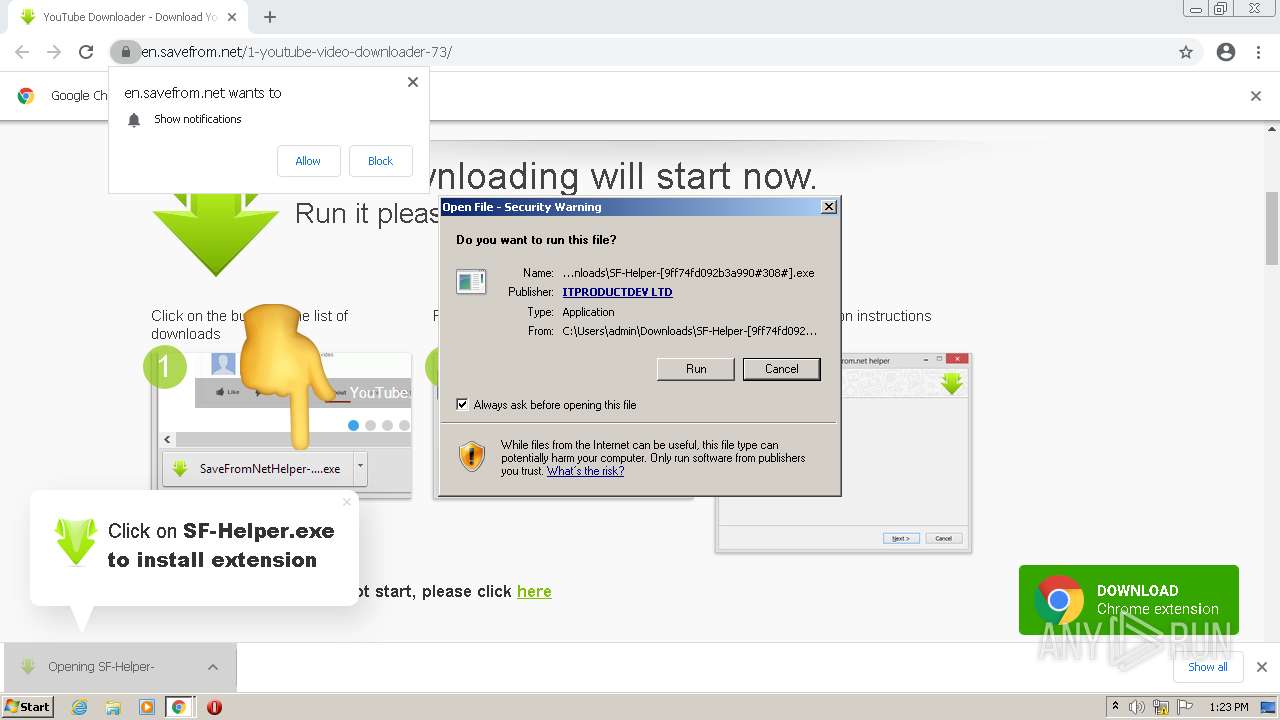
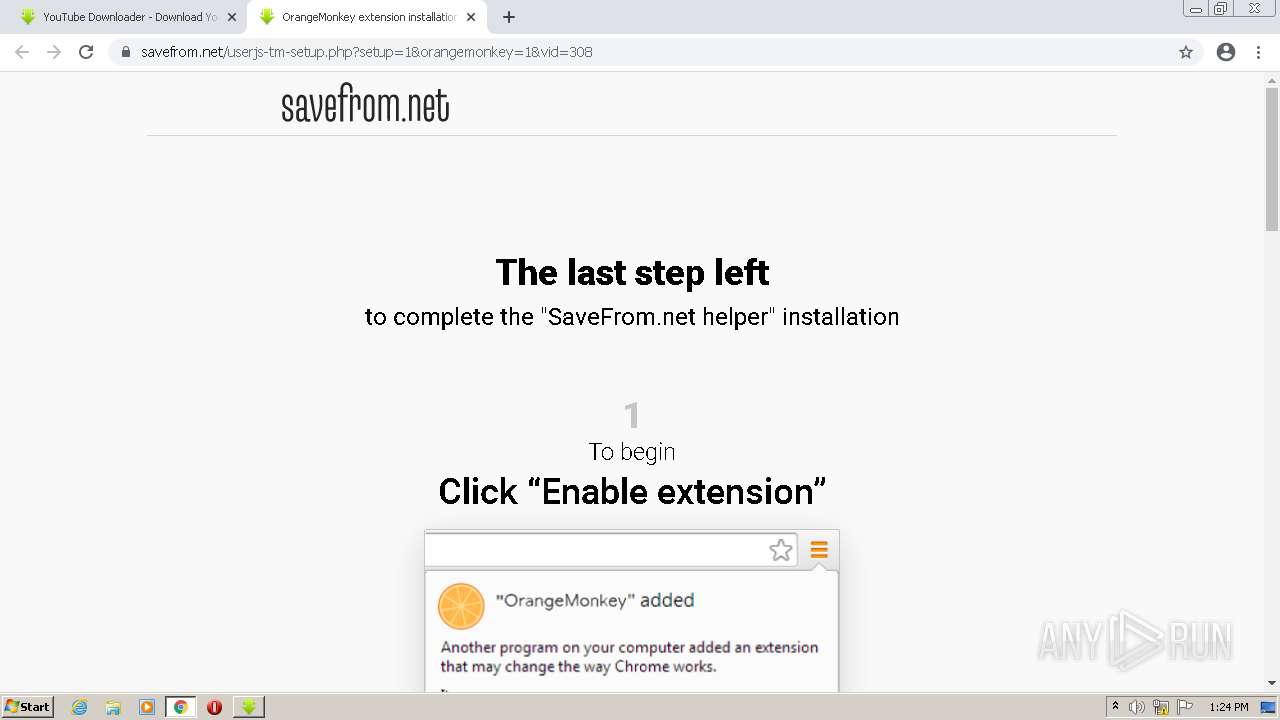
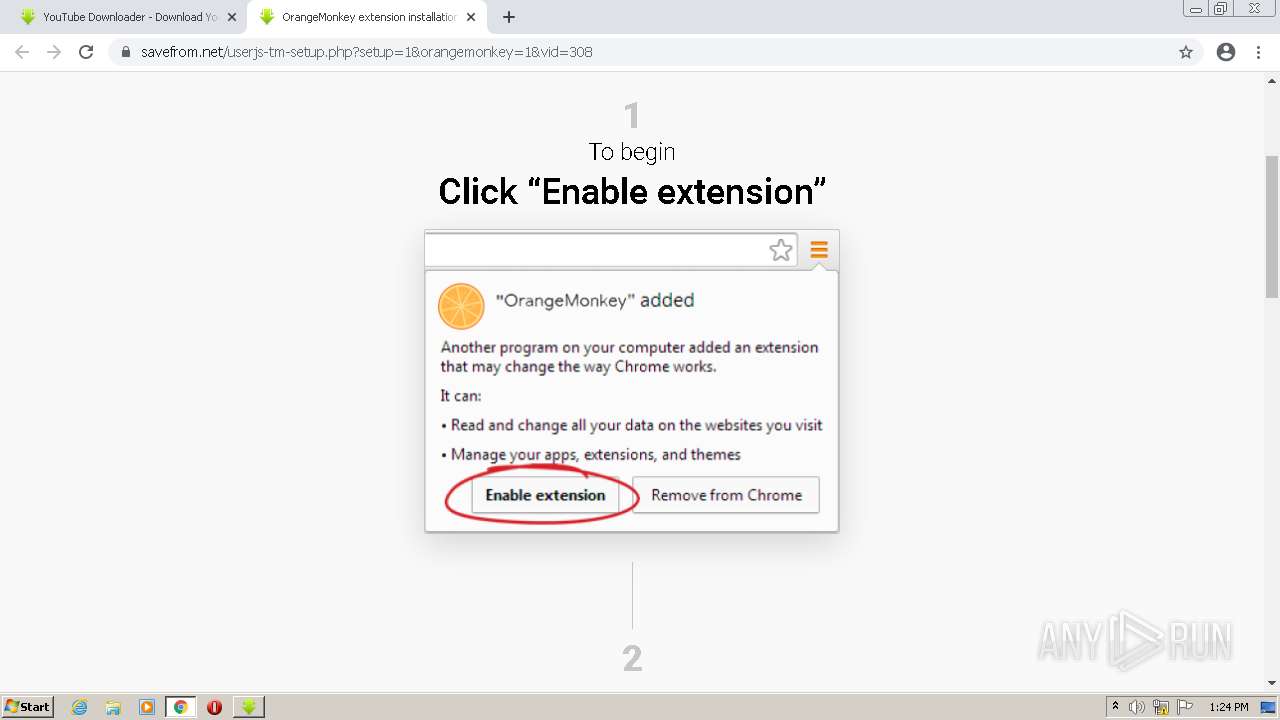
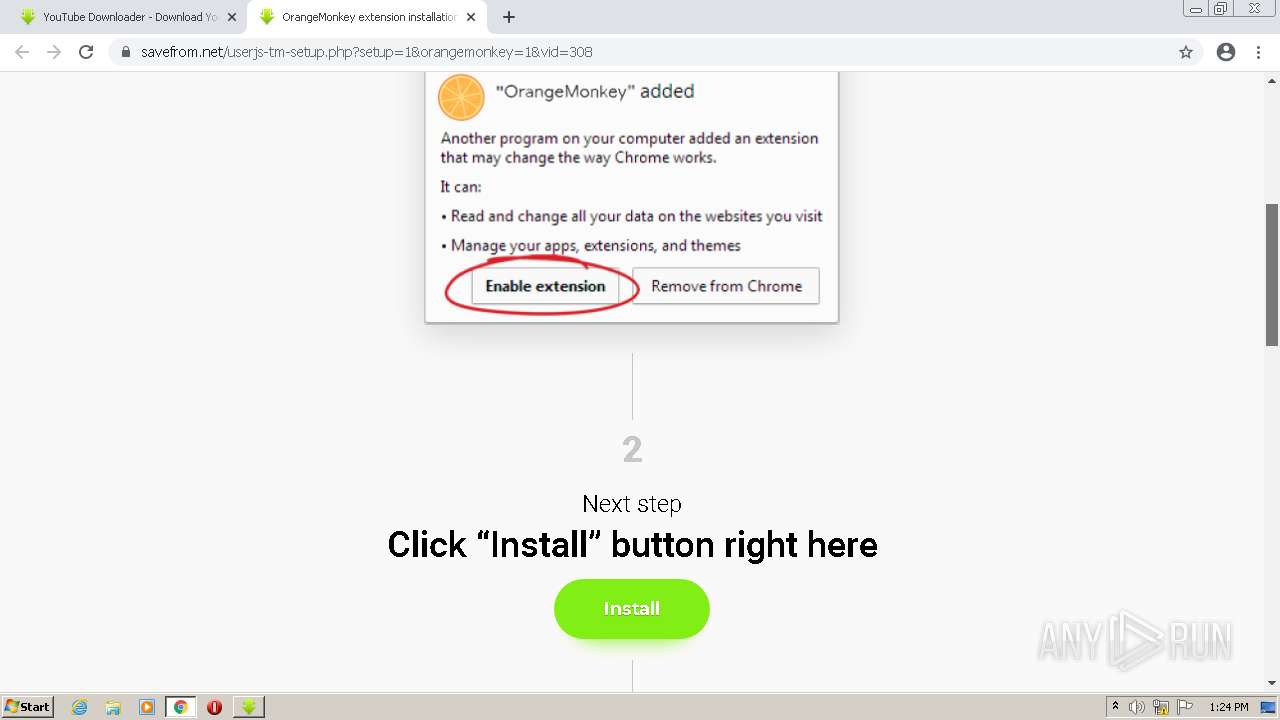
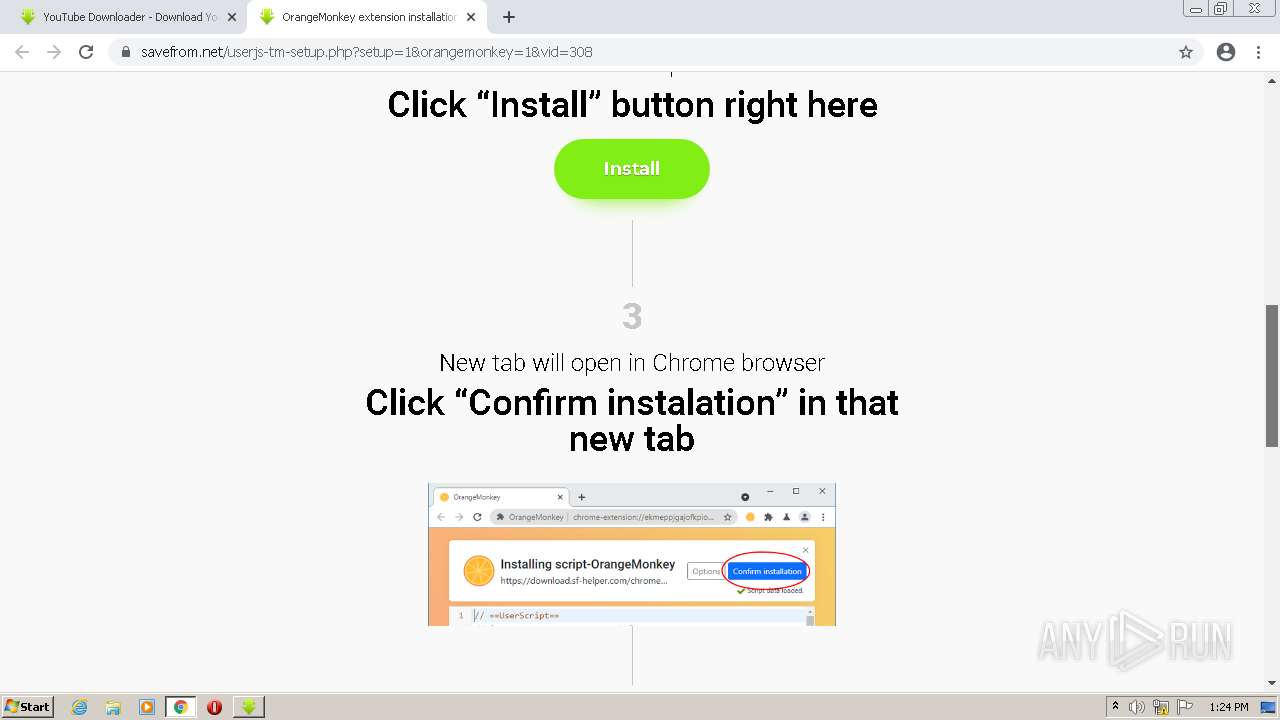
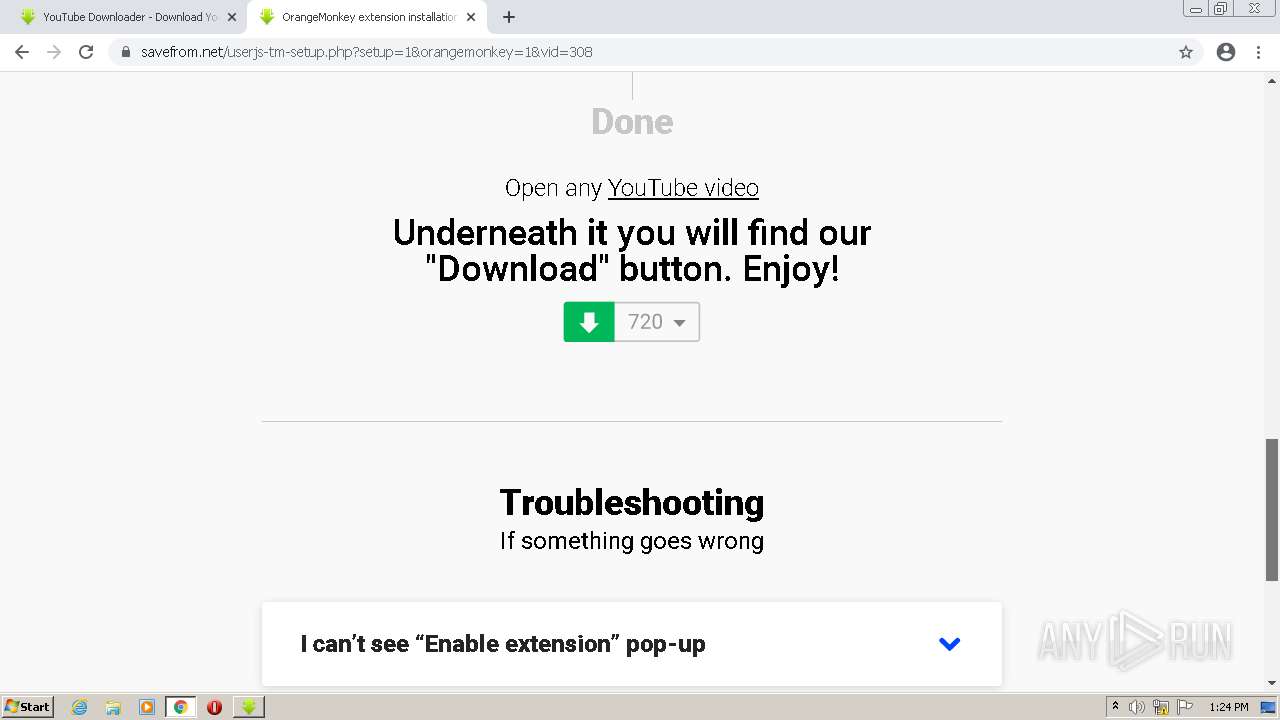
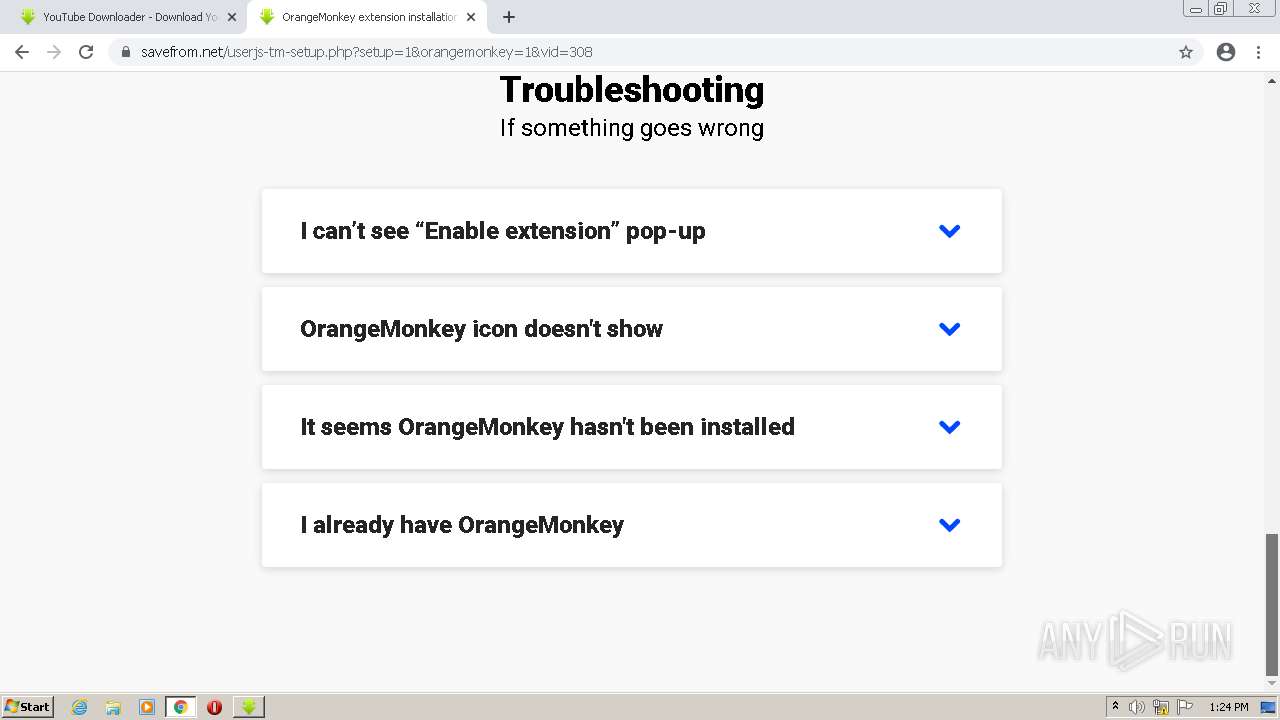
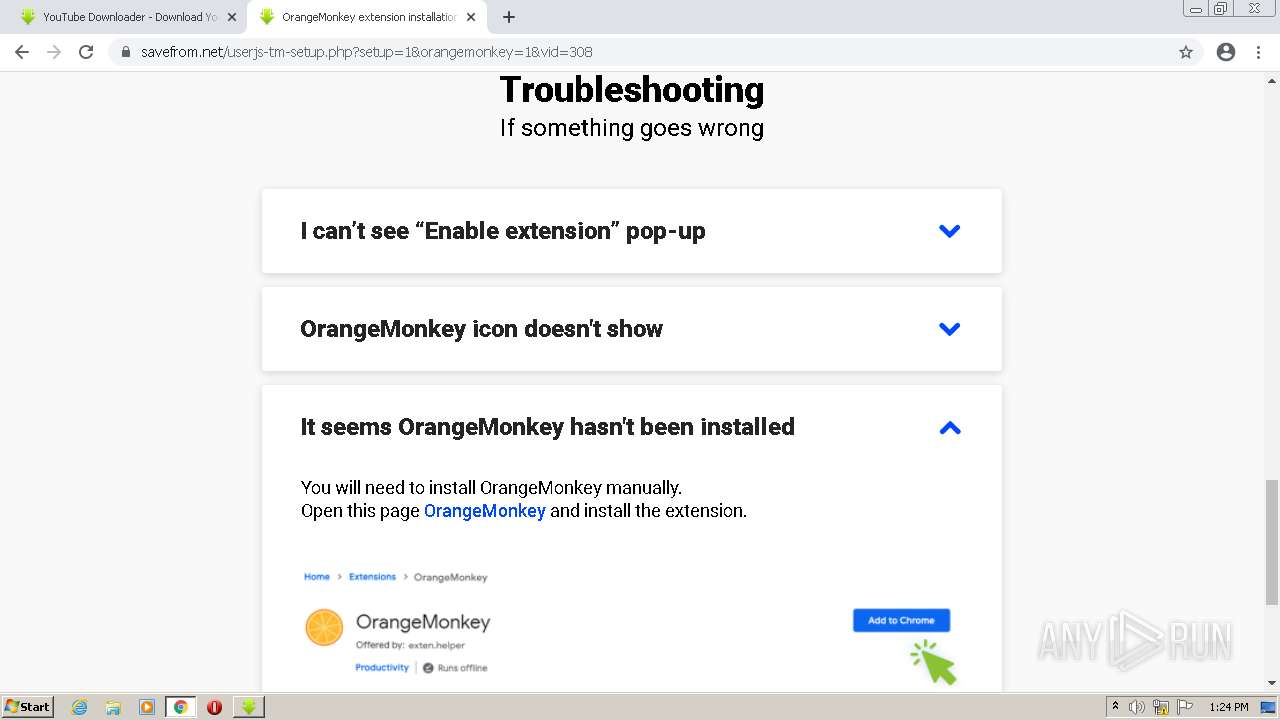
| URL: | https://en.savefrom.net/1-youtube-video-downloader-73/ |
| Full analysis: | https://app.any.run/tasks/79ab9d26-495f-46a0-bfce-61a66dd6b57f |
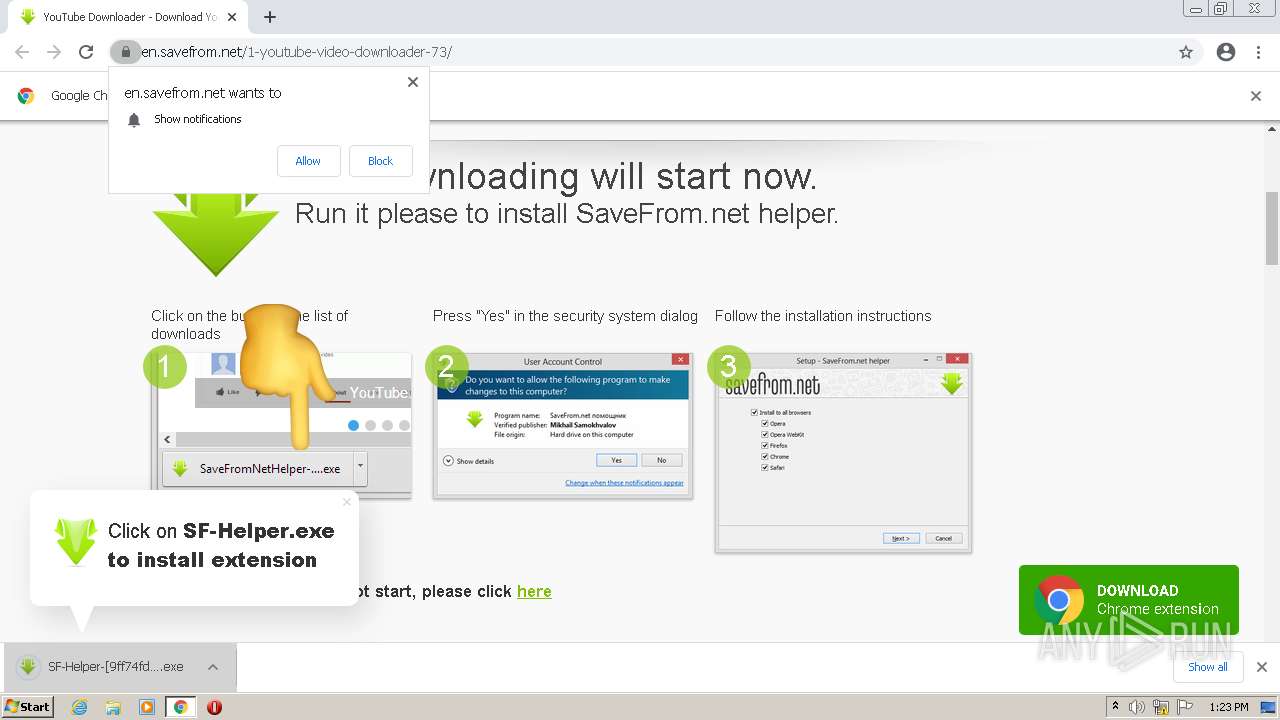
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2022, 13:23:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
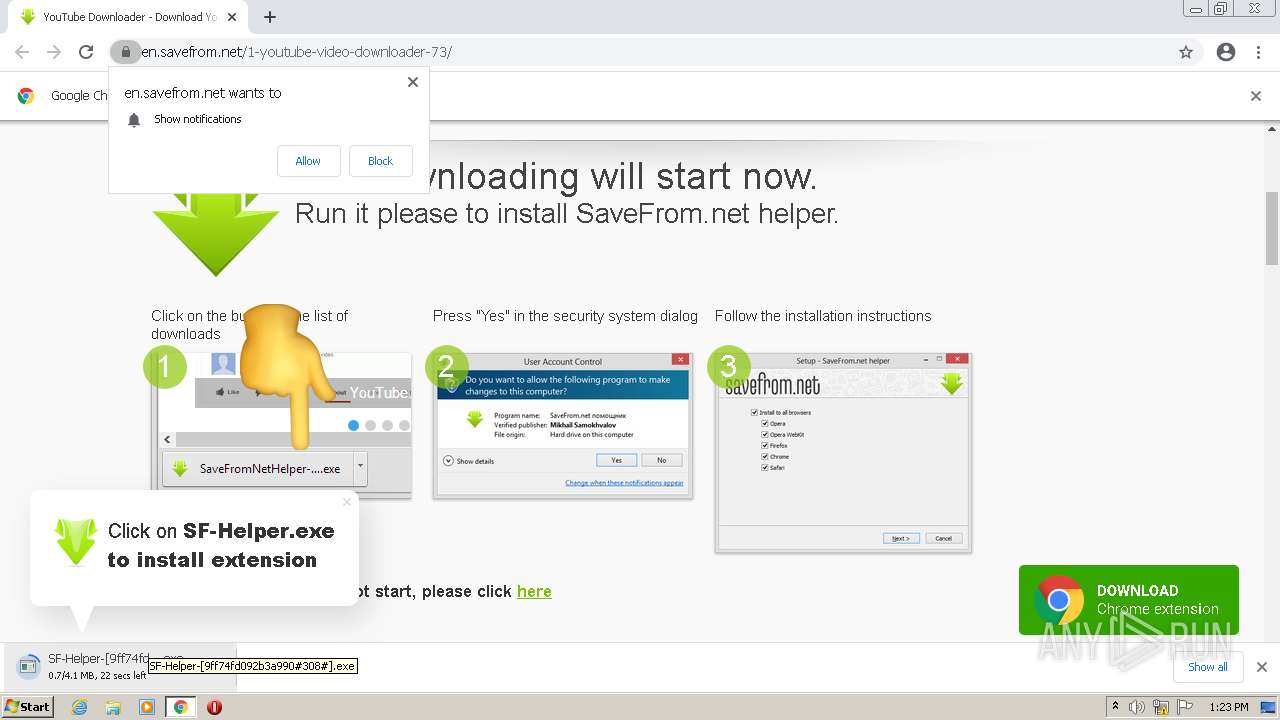
| MD5: | 3570679E56662F52995B3B3BBF6D868D |
| SHA1: | B65BD180D2C3EF8D69B1E719960EE7EE6287D452 |
| SHA256: | 97652DB4C0CEE0E05BA5C151BE90F1C16A30CF785795BF34214FC5FE1E4C6967 |
| SSDEEP: | 3:N8NK2XRcLyE8zuXOKn:2NKiC |
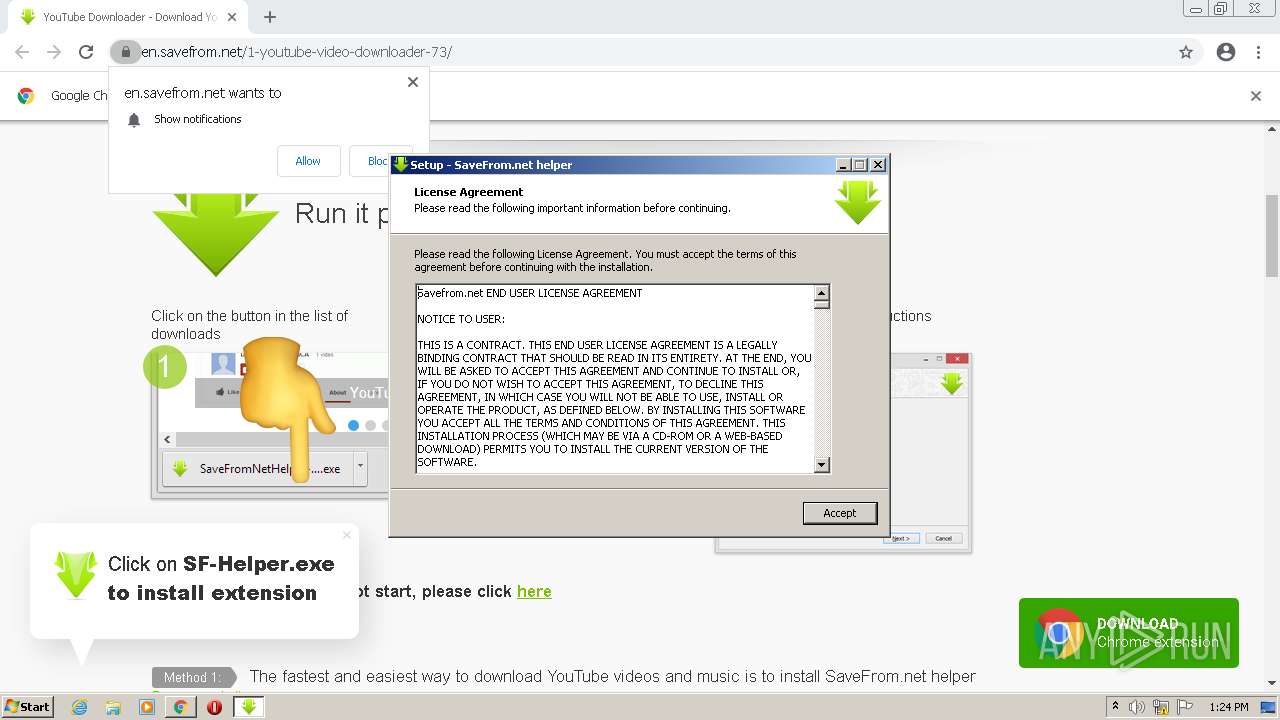
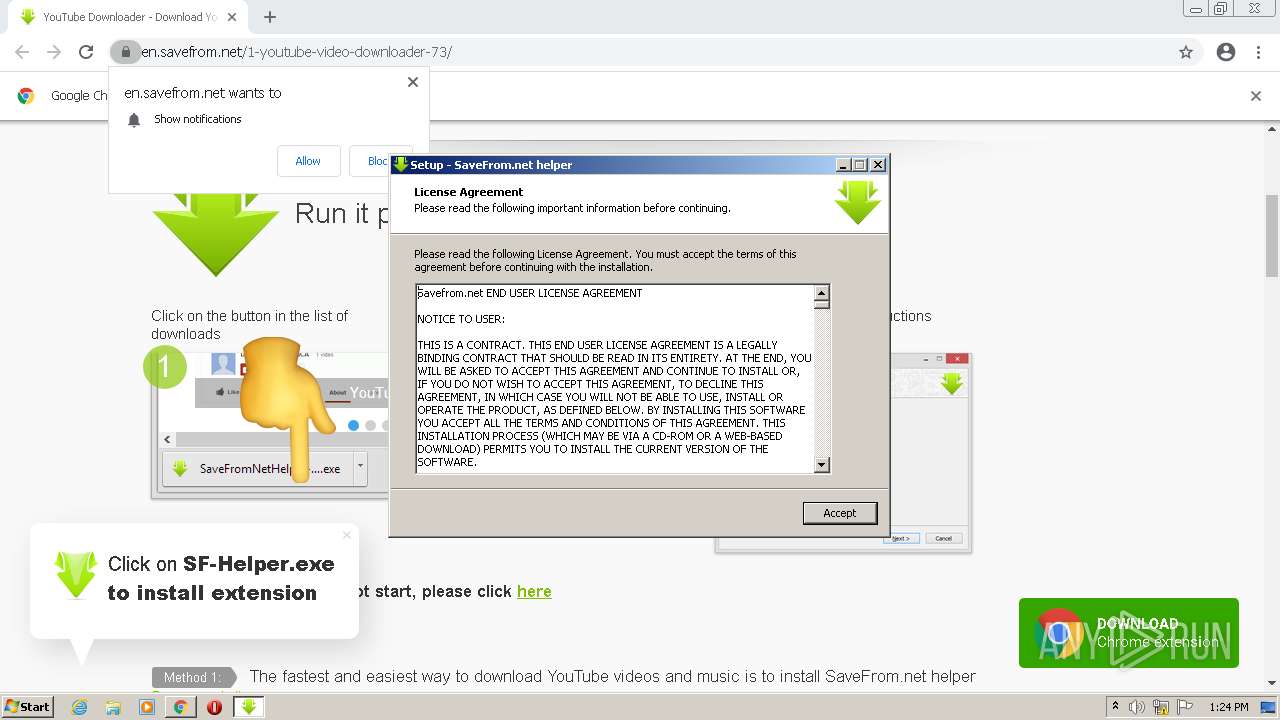
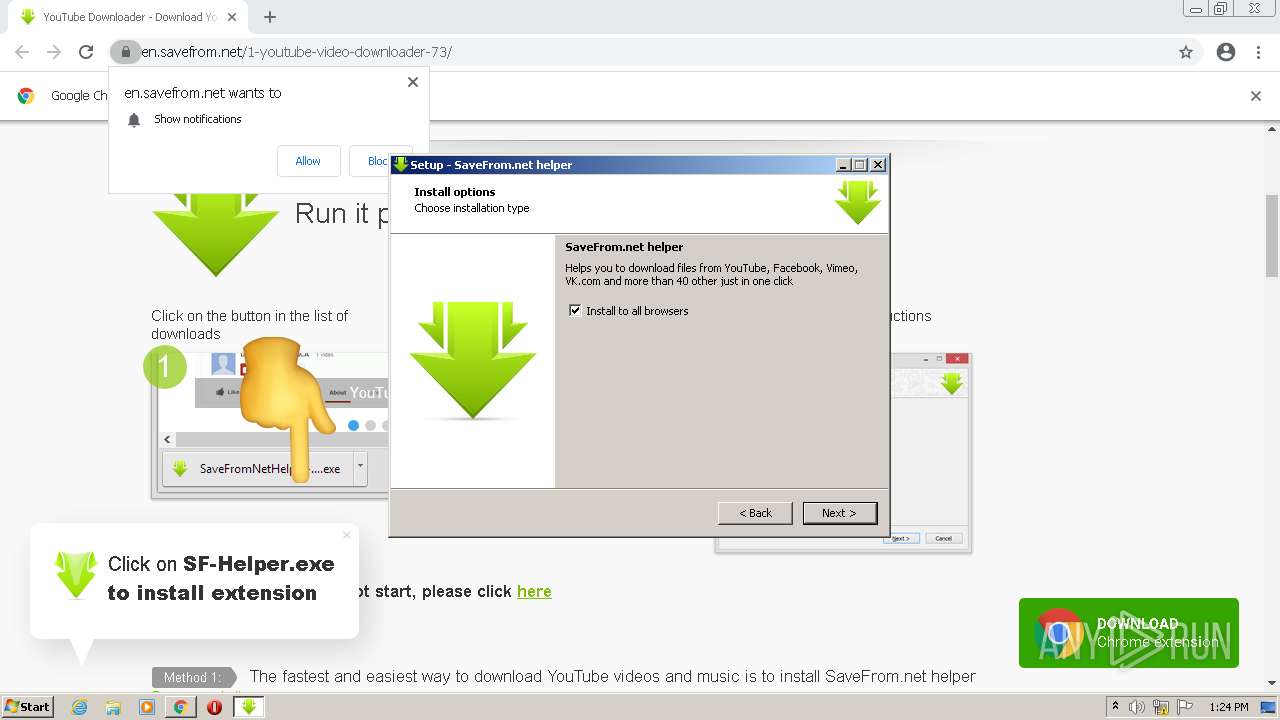
MALICIOUS
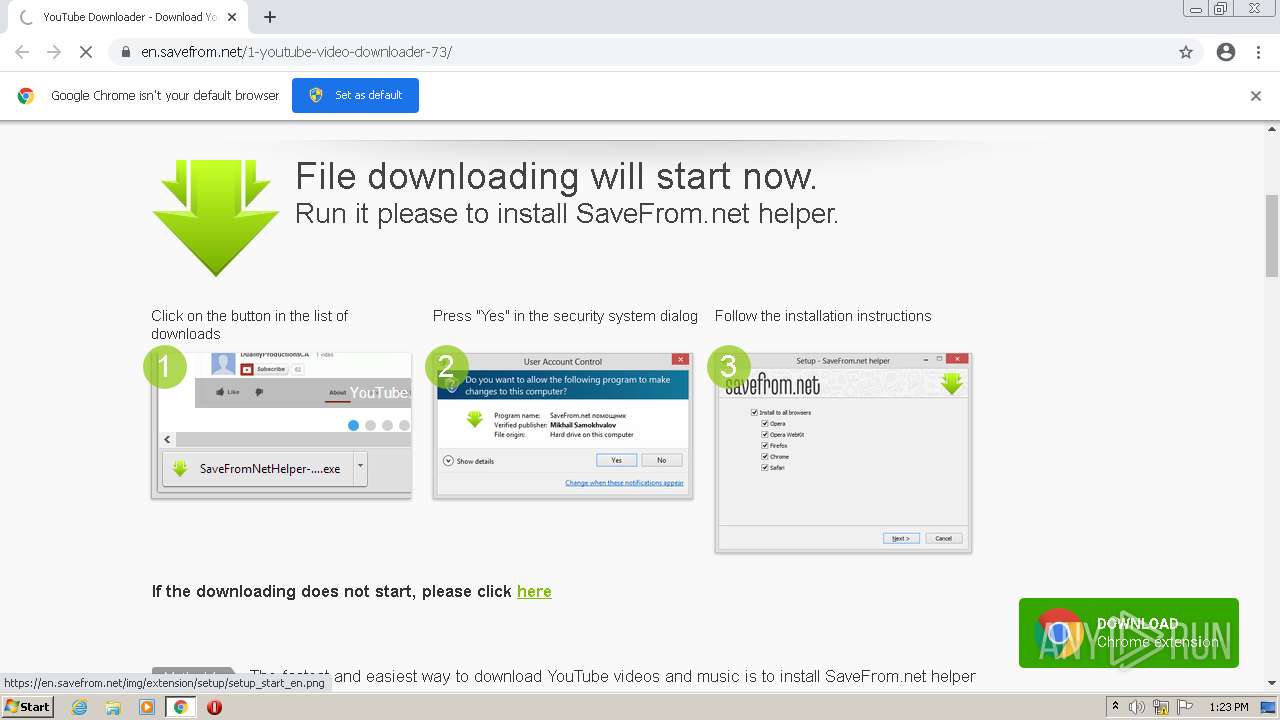
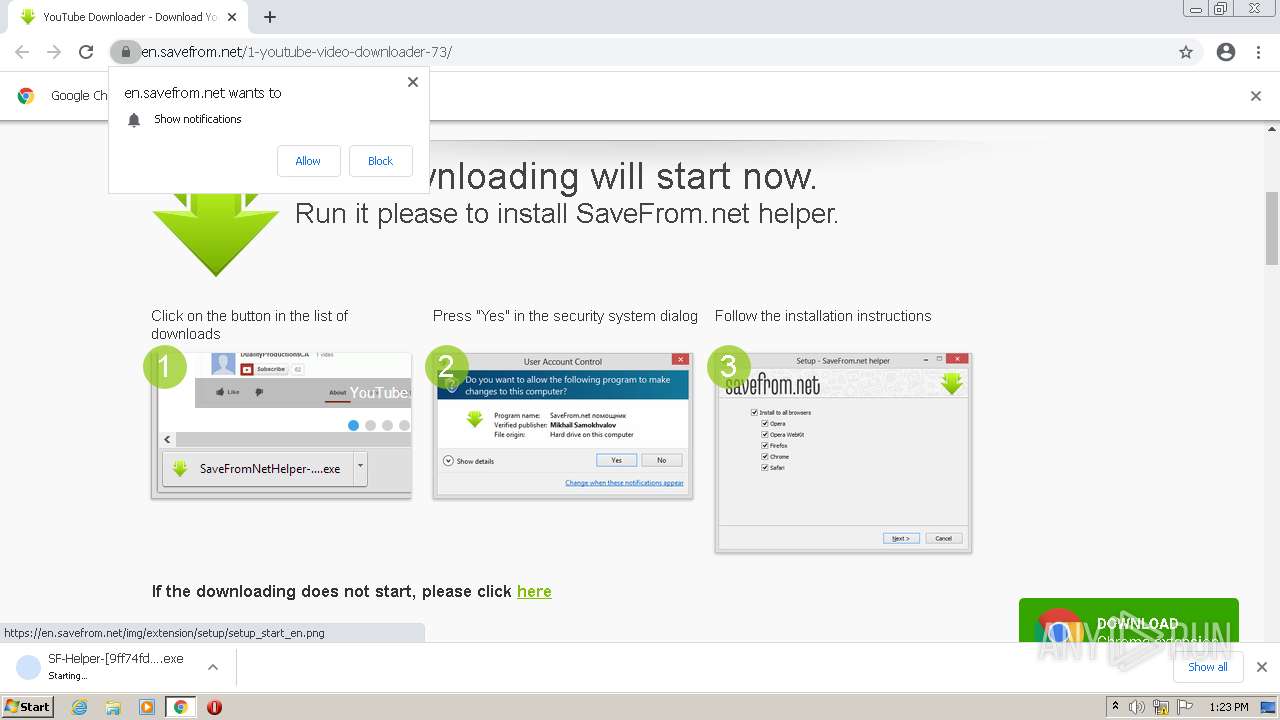
Drops executable file immediately after starts
- SF-Helper-[9ff74fd092b3a990#308#].exe (PID: 4056)
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
- SF-Helper-[9ff74fd092b3a990#308#].exe (PID: 2960)
Application was dropped or rewritten from another process
- SF-Helper-[9ff74fd092b3a990#308#].exe (PID: 2960)
- SF-Helper-[9ff74fd092b3a990#308#].exe (PID: 4056)
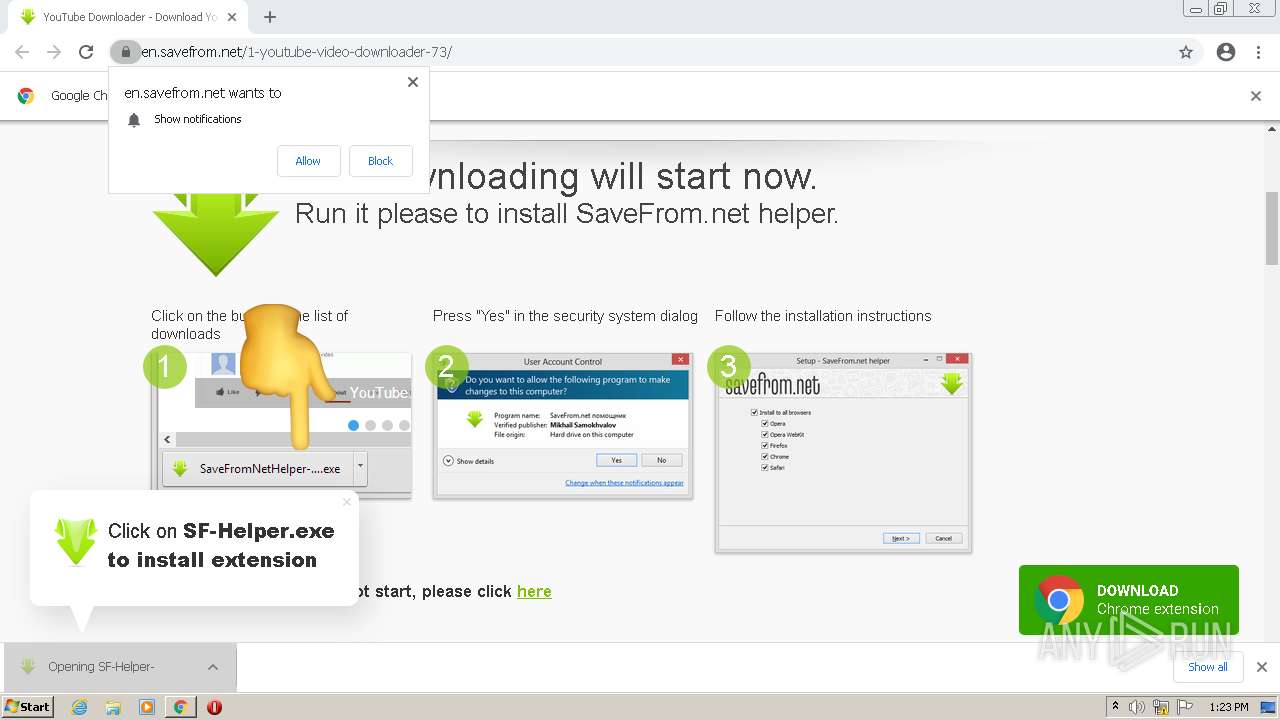
Actions looks like stealing of personal data
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
Steals credentials from Web Browsers
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
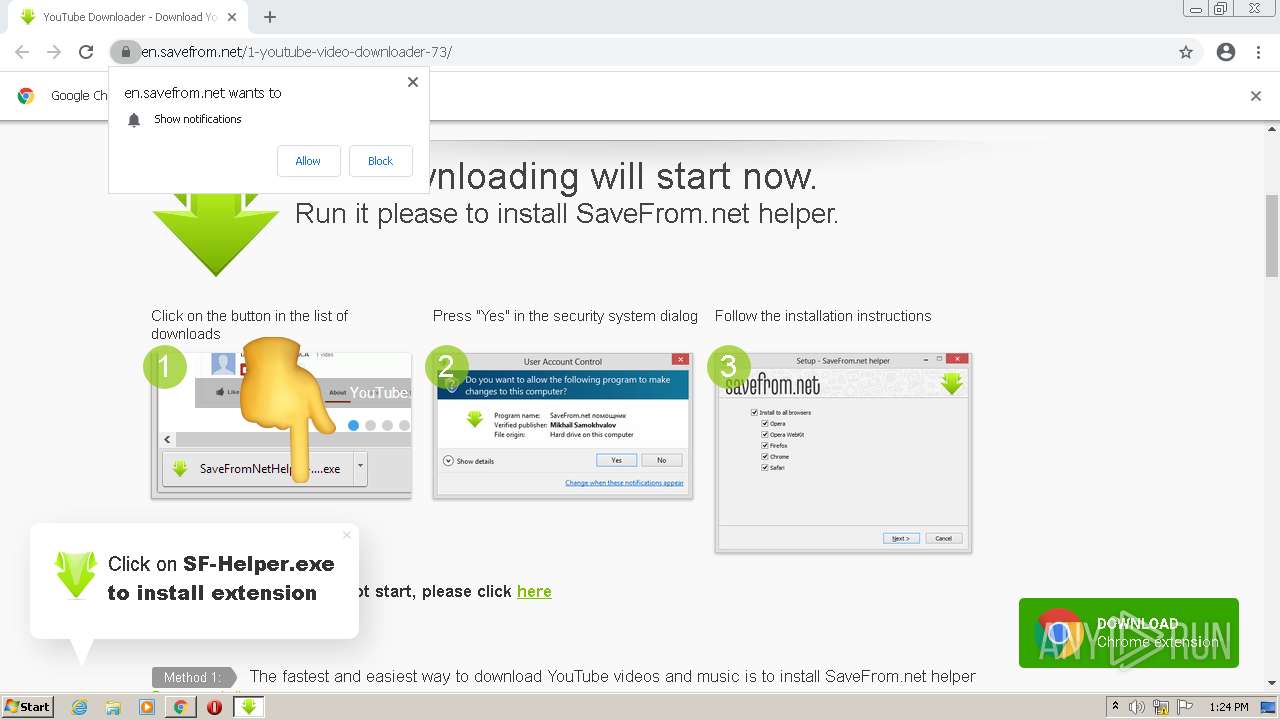
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3456)
- SF-Helper-[9ff74fd092b3a990#308#].exe (PID: 4056)
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
- SF-Helper-[9ff74fd092b3a990#308#].exe (PID: 2960)
Checks supported languages
- SF-Helper-[9ff74fd092b3a990#308#].exe (PID: 4056)
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
- SF-Helper-[9ff74fd092b3a990#308#].exe (PID: 2960)
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2296)
Reads the computer name
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2296)
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
Reads the Windows organization settings
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
Reads Windows owner or organization settings
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
Creates a directory in Program Files
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
INFO
Checks supported languages
- chrome.exe (PID: 3704)
- chrome.exe (PID: 1652)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 468)
- chrome.exe (PID: 1468)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 1176)
- chrome.exe (PID: 2748)
- chrome.exe (PID: 1852)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 624)
- chrome.exe (PID: 1920)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 3896)
Application launched itself
- chrome.exe (PID: 3456)
- chrome.exe (PID: 624)
Reads the computer name
- chrome.exe (PID: 2252)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 468)
- chrome.exe (PID: 1652)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 624)
- chrome.exe (PID: 3788)
Reads the hosts file
- chrome.exe (PID: 3456)
- chrome.exe (PID: 1652)
Reads settings of System Certificates
- chrome.exe (PID: 1652)
- chrome.exe (PID: 3456)
Checks Windows Trust Settings
- chrome.exe (PID: 3456)
Application was dropped or rewritten from another process
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2296)
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
Creates files in the program directory
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
Loads dropped or rewritten executable
- SF-Helper-[9ff74fd092b3a990#308#].tmp (PID: 2056)
Reads the date of Windows installation
- chrome.exe (PID: 3788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
27
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
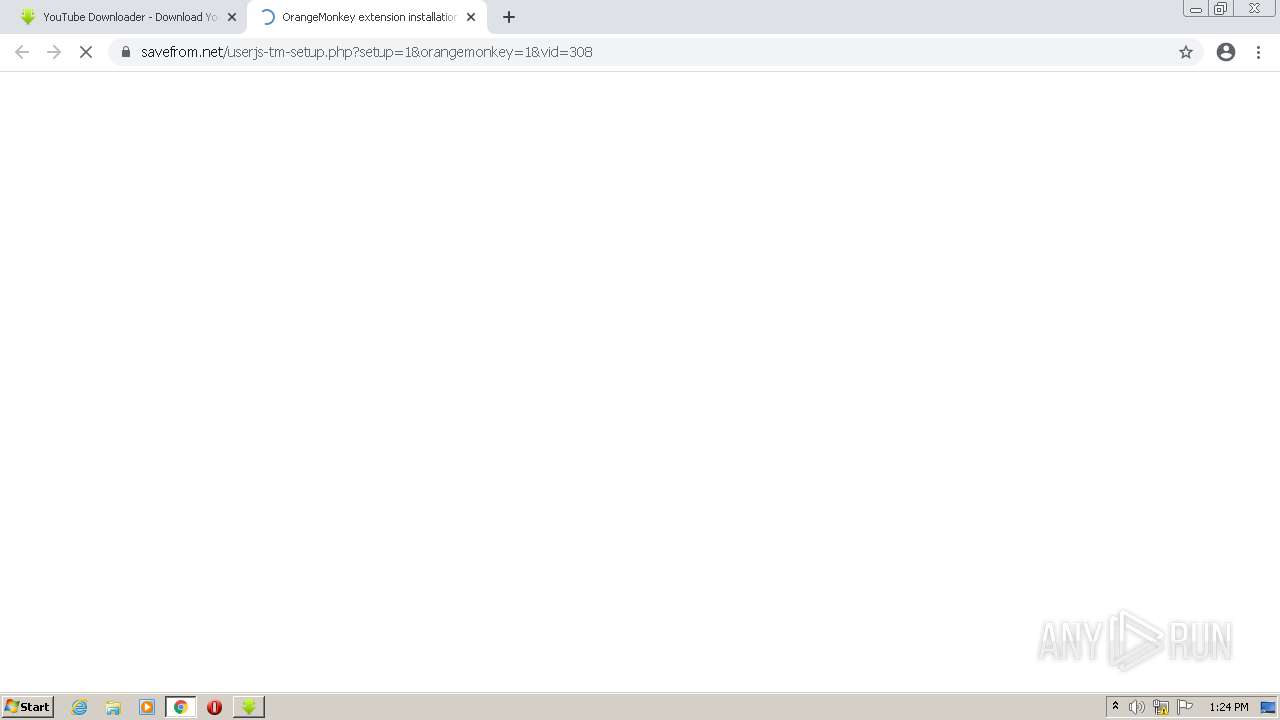
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://savefrom.net/userjs-tm-setup.php?setup=1&orangemonkey=1&vid=308 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | SF-Helper-[9ff74fd092b3a990#308#].tmp | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1256 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3440 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\AppData\Local\Temp\is-IOIE5.tmp\SF-Helper-[9ff74fd092b3a990#308#].tmp" /SL5="$30176,3823175,229888,C:\Users\admin\Downloads\SF-Helper-[9ff74fd092b3a990#308#].exe" /SPAWNWND=$20178 /NOTIFYWND=$40160 | C:\Users\admin\AppData\Local\Temp\is-IOIE5.tmp\SF-Helper-[9ff74fd092b3a990#308#].tmp | SF-Helper-[9ff74fd092b3a990#308#].exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3588 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,740755733832595321,2811958202481010034,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2696 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
13 222
Read events
13 097
Write events
125
Delete events
0
Modification events
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
7
Suspicious files
33
Text files
82
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-623B1F53-D80.pma | — | |
MD5:— | SHA256:— | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1261a531-cb5e-4021-a124-26cb8cd85af1.tmp | text | |
MD5:— | SHA256:— | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ef0034bd-a5a6-4e93-9257-172462753229.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF11534d.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF115551.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
56
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2056 | SF-Helper-[9ff74fd092b3a990#308#].tmp | GET | 200 | 142.250.184.228:80 | http://google-analytics.com/collect?v=1&tid=UA-181312972-6&cid=156622FA-5B87-44E3-BB66-AE114B2644AD&an=helper_clear&av=0.19.12&t=event&ec=browsers&ea=none&el=Safari&ev=1&cd=invite&aiid=308&ua=Opera%2F9.80%20%28Windows%20NT%206.1%29%20Presto%2F2.12.388%20Version%2F12.14&ul=en-us | US | image | 35 b | whitelisted |
2056 | SF-Helper-[9ff74fd092b3a990#308#].tmp | GET | 200 | 142.250.184.228:80 | http://google-analytics.com/collect?v=1&tid=UA-181312972-6&cid=156622FA-5B87-44E3-BB66-AE114B2644AD&an=helper_clear&av=0.19.12&t=event&ec=browsers&ea=none&el=OperaWK&ev=1&cd=invite&aiid=308&ua=Opera%2F9.80%20%28Windows%20NT%206.1%29%20Presto%2F2.12.388%20Version%2F12.14&ul=en-us | US | image | 35 b | whitelisted |
2056 | SF-Helper-[9ff74fd092b3a990#308#].tmp | GET | 200 | 142.250.184.228:80 | http://google-analytics.com/collect?v=1&tid=UA-181312972-6&cid=156622FA-5B87-44E3-BB66-AE114B2644AD&an=helper_clear&av=0.19.12&t=screenview&cd=license&aiid=308&ua=Opera%2F9.80%20%28Windows%20NT%206.1%29%20Presto%2F2.12.388%20Version%2F12.14&ul=en-us | US | image | 35 b | whitelisted |
2056 | SF-Helper-[9ff74fd092b3a990#308#].tmp | GET | 200 | 142.250.184.228:80 | http://google-analytics.com/collect?v=1&tid=UA-181312972-6&cid=156622FA-5B87-44E3-BB66-AE114B2644AD&an=helper_clear&av=0.19.12&t=event&ec=browsers&ea=yes&el=all&ev=1&cd=invite&aiid=308&ua=Opera%2F9.80%20%28Windows%20NT%206.1%29%20Presto%2F2.12.388%20Version%2F12.14&ul=en-us | US | image | 35 b | whitelisted |
2056 | SF-Helper-[9ff74fd092b3a990#308#].tmp | GET | 200 | 142.250.184.228:80 | http://google-analytics.com/collect?v=1&tid=UA-181312972-6&cid=156622FA-5B87-44E3-BB66-AE114B2644AD&an=helper_clear&av=0.19.12&t=event&ec=browsers&ea=yes&el=Firefox&ev=1&cd=invite&aiid=308&ua=Opera%2F9.80%20%28Windows%20NT%206.1%29%20Presto%2F2.12.388%20Version%2F12.14&ul=en-us | US | image | 35 b | whitelisted |
2056 | SF-Helper-[9ff74fd092b3a990#308#].tmp | GET | 200 | 142.250.184.228:80 | http://google-analytics.com/collect?v=1&tid=UA-181312972-6&cid=156622FA-5B87-44E3-BB66-AE114B2644AD&an=helper_clear&av=0.19.12&t=event&ec=browsers&ea=none&el=MailRu&ev=1&cd=invite&aiid=308&ua=Opera%2F9.80%20%28Windows%20NT%206.1%29%20Presto%2F2.12.388%20Version%2F12.14&ul=en-us | US | image | 35 b | whitelisted |
2056 | SF-Helper-[9ff74fd092b3a990#308#].tmp | GET | 200 | 142.250.184.228:80 | http://google-analytics.com/collect?v=1&tid=UA-181312972-6&cid=156622FA-5B87-44E3-BB66-AE114B2644AD&an=helper_clear&av=0.19.12&t=event&ec=browsers&ea=none&el=Yawser&ev=1&cd=invite&aiid=308&ua=Opera%2F9.80%20%28Windows%20NT%206.1%29%20Presto%2F2.12.388%20Version%2F12.14&ul=en-us | US | image | 35 b | whitelisted |
2056 | SF-Helper-[9ff74fd092b3a990#308#].tmp | GET | 200 | 142.250.184.228:80 | http://google-analytics.com/collect?v=1&tid=UA-181312972-6&cid=156622FA-5B87-44E3-BB66-AE114B2644AD&an=helper_clear&av=0.19.12&t=event&ec=browsers&ea=yes&el=Chrome&ev=1&cd=invite&aiid=308&ua=Opera%2F9.80%20%28Windows%20NT%206.1%29%20Presto%2F2.12.388%20Version%2F12.14&ul=en-us | US | image | 35 b | whitelisted |
1652 | chrome.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1decde550fc78283 | US | compressed | 59.5 Kb | whitelisted |
2056 | SF-Helper-[9ff74fd092b3a990#308#].tmp | GET | 200 | 142.250.184.228:80 | http://google-analytics.com/collect?v=1&tid=UA-181312972-6&cid=156622FA-5B87-44E3-BB66-AE114B2644AD&an=helper_clear&av=0.19.12&t=event&ec=browsers&ea=open-page&el=true&ev=1&cd=license&aiid=308&ua=Opera%2F9.80%20%28Windows%20NT%206.1%29%20Presto%2F2.12.388%20Version%2F12.14&ul=en-us | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1652 | chrome.exe | 104.26.12.61:443 | sfstatic.net | Cloudflare Inc | US | shared |
1652 | chrome.exe | 141.95.99.59:443 | en.savefrom.net | — | GB | unknown |
1652 | chrome.exe | 172.217.18.106:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
1652 | chrome.exe | 64.233.167.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
1652 | chrome.exe | 142.250.185.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1652 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | Google Inc. | US | suspicious |
1652 | chrome.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1652 | chrome.exe | 139.45.197.236:443 | besmeargleor.com | — | US | malicious |
1652 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 144.76.67.90:443 | rek5.savefrom.net | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
en.savefrom.net |
| unknown |
sfstatic.net |
| malicious |
www.google-analytics.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
besmeargleor.com |
| malicious |