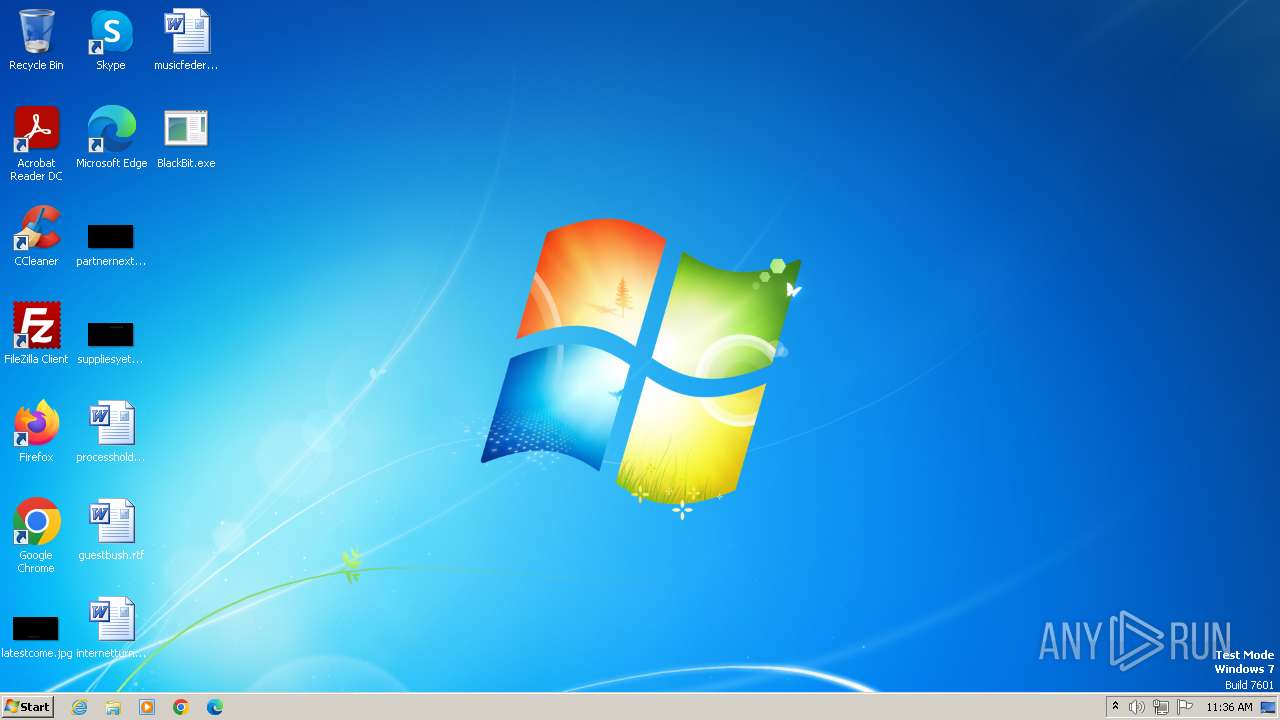
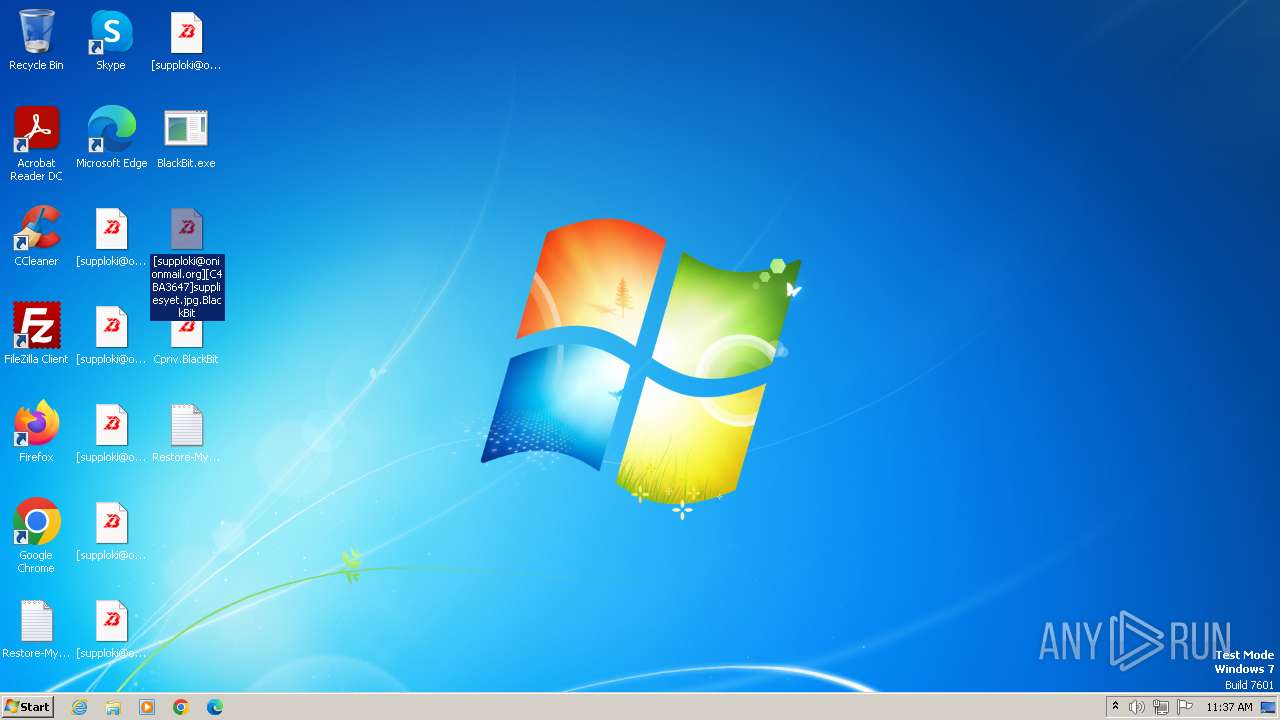
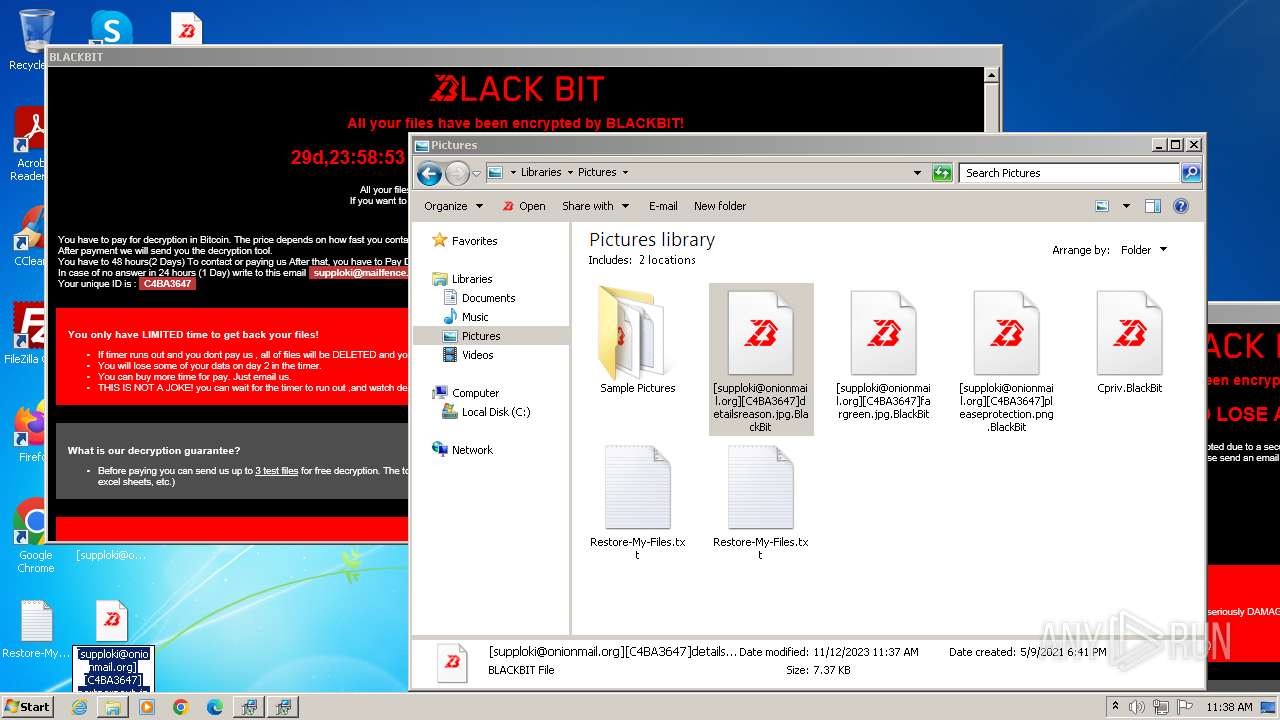
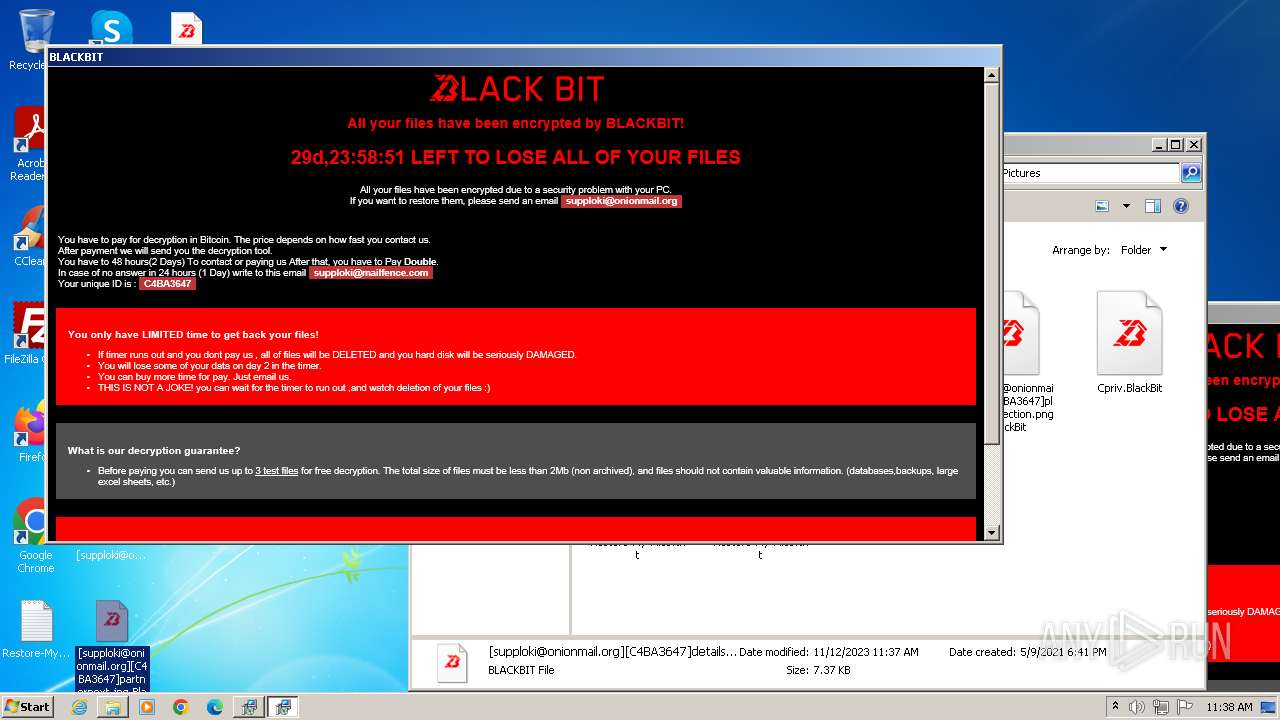
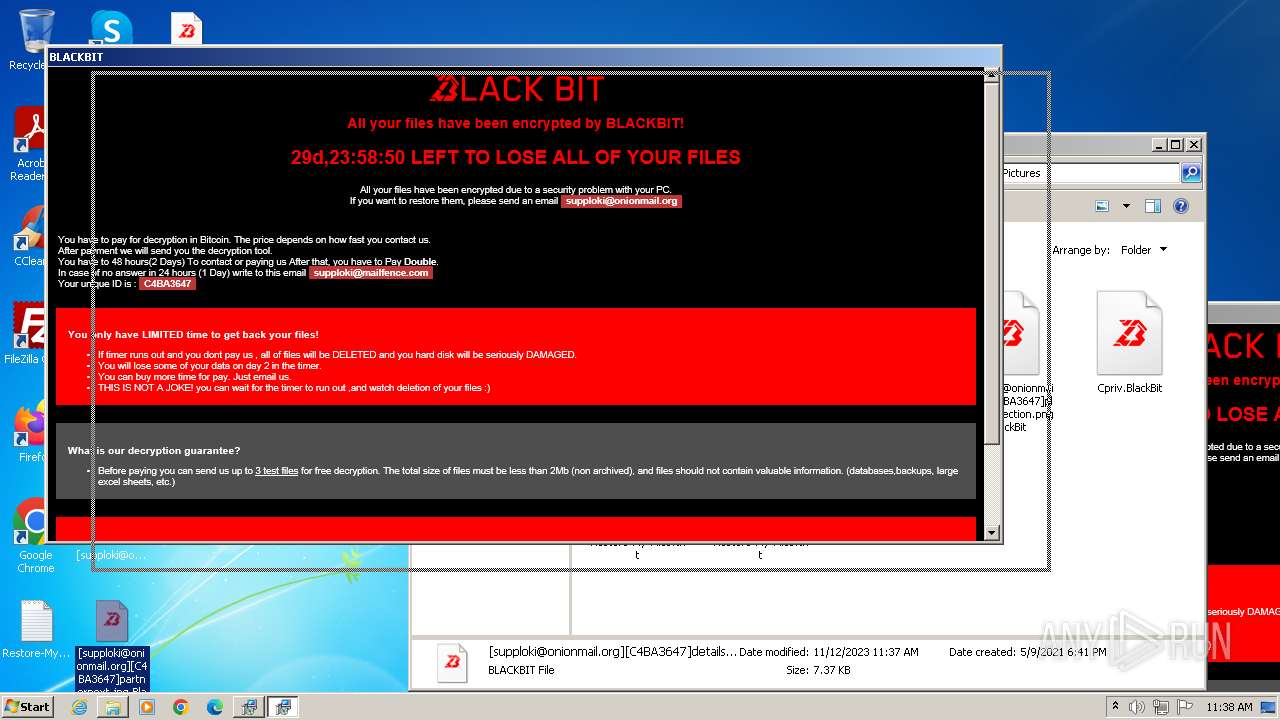
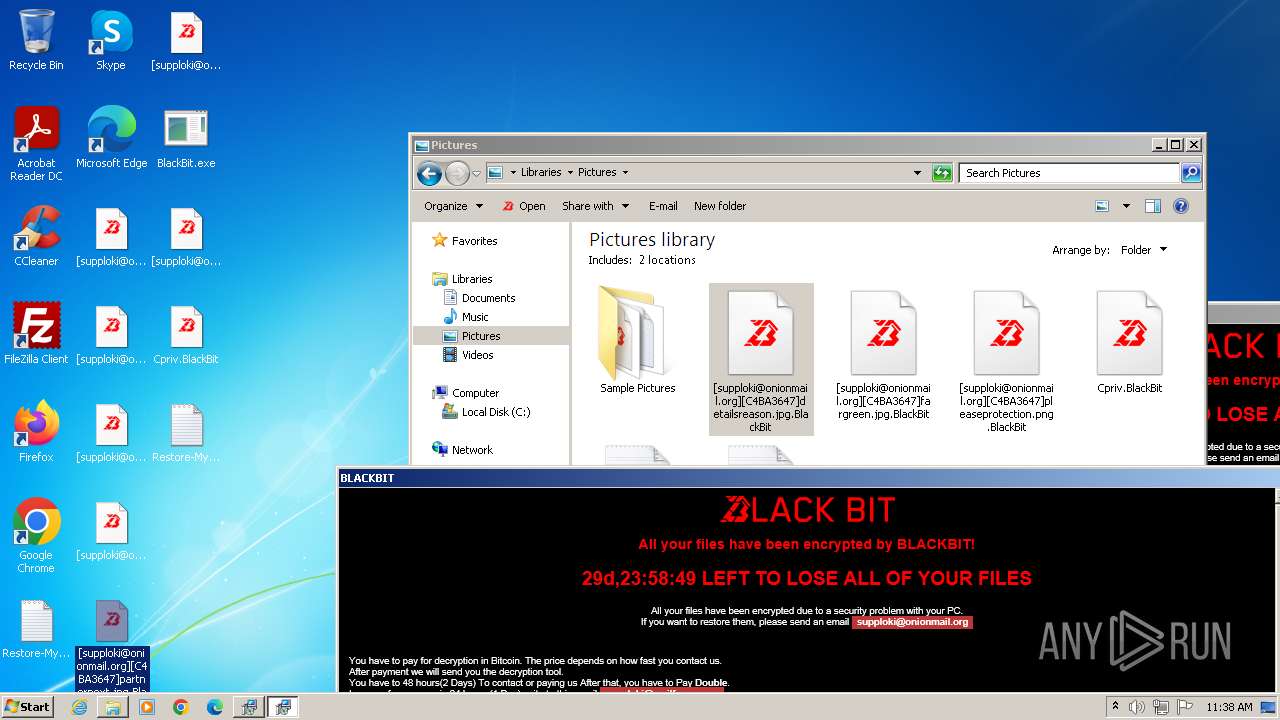
| File name: | BlackBit.exe |
| Full analysis: | https://app.any.run/tasks/19bdbd94-91ae-4e85-b30b-d44aa25060ec |
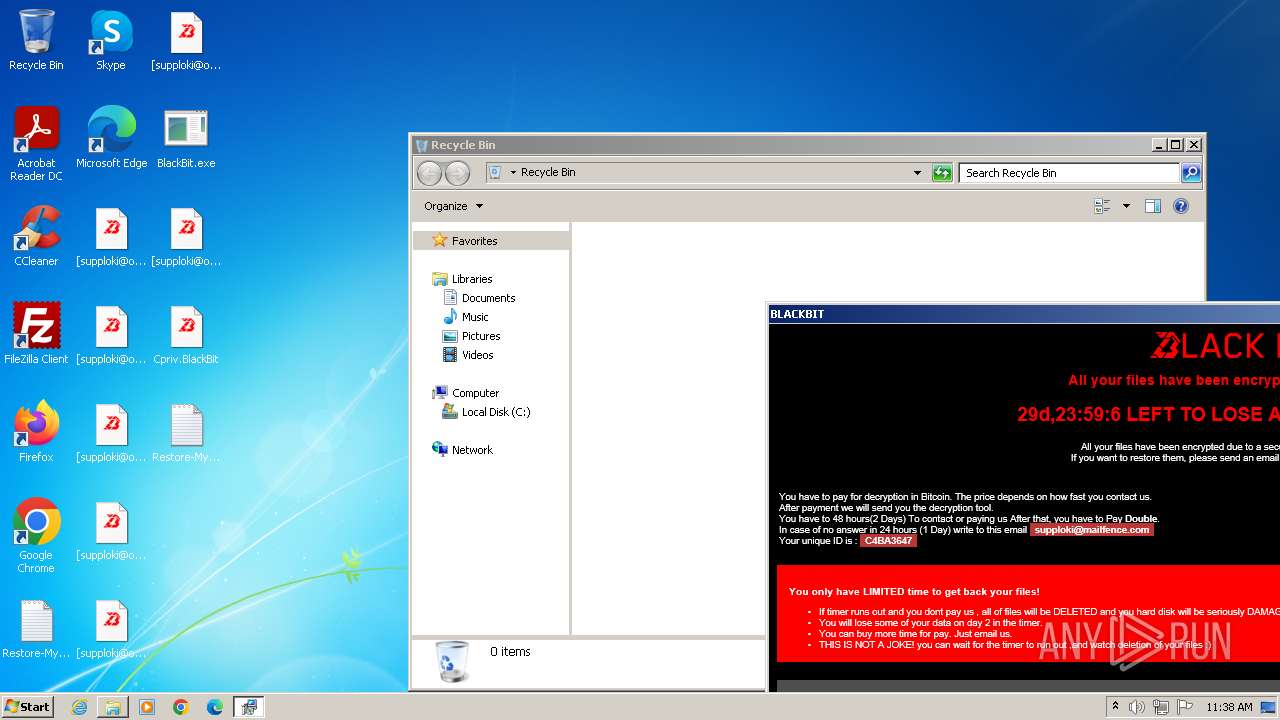
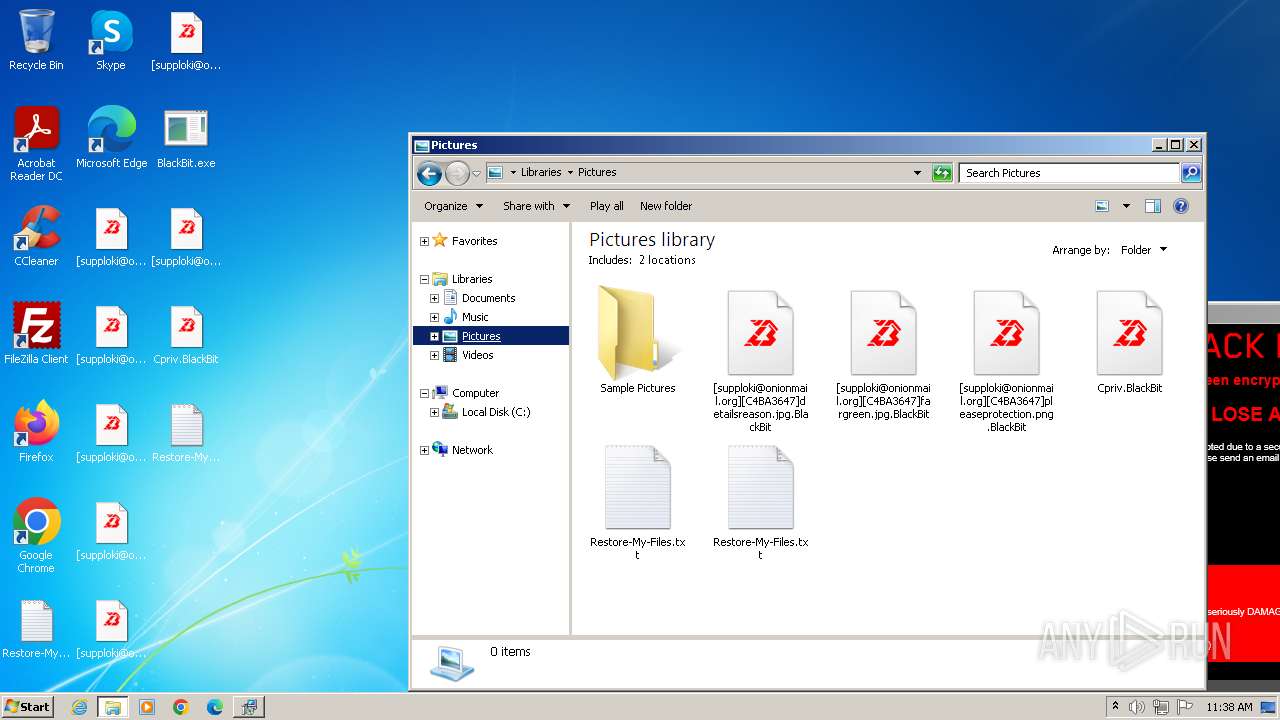
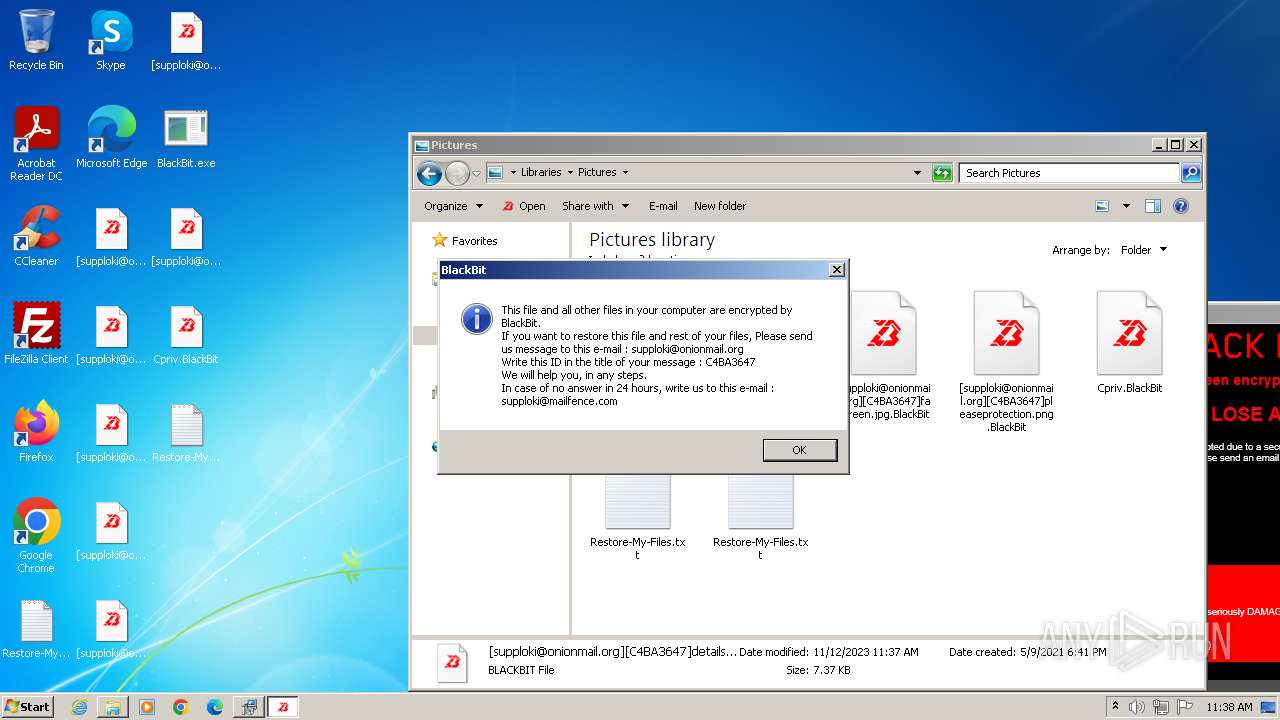
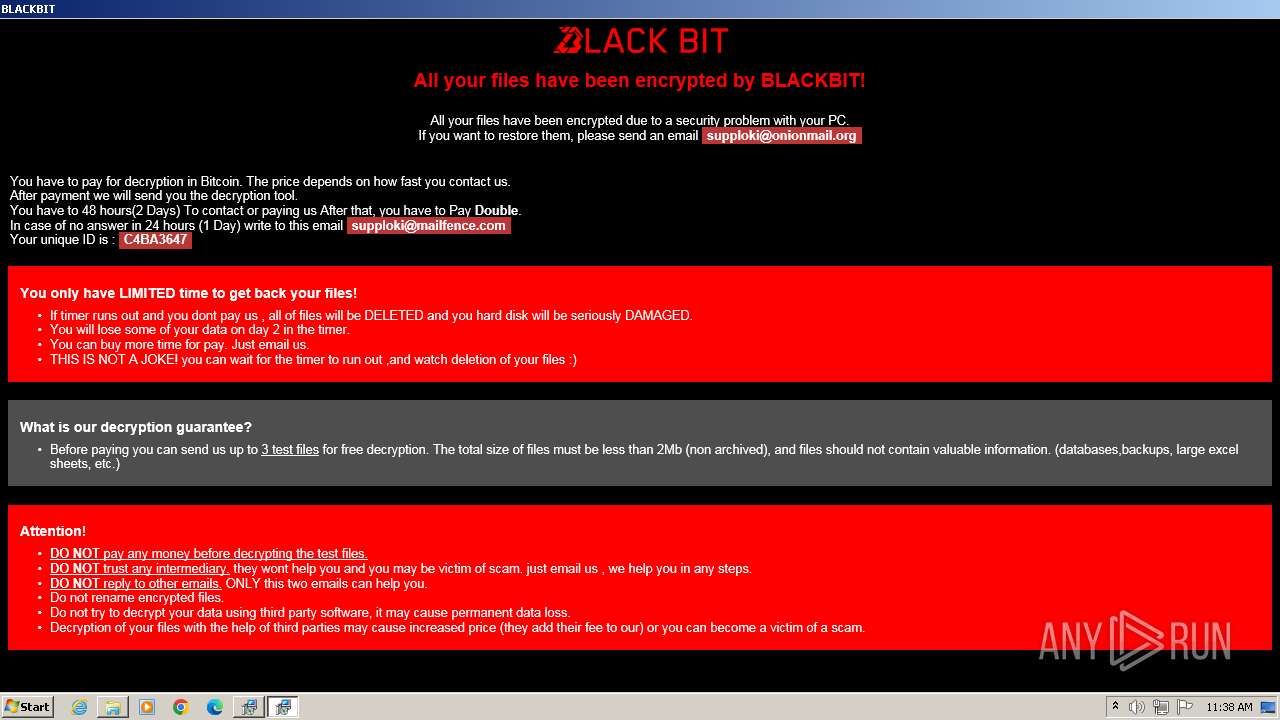
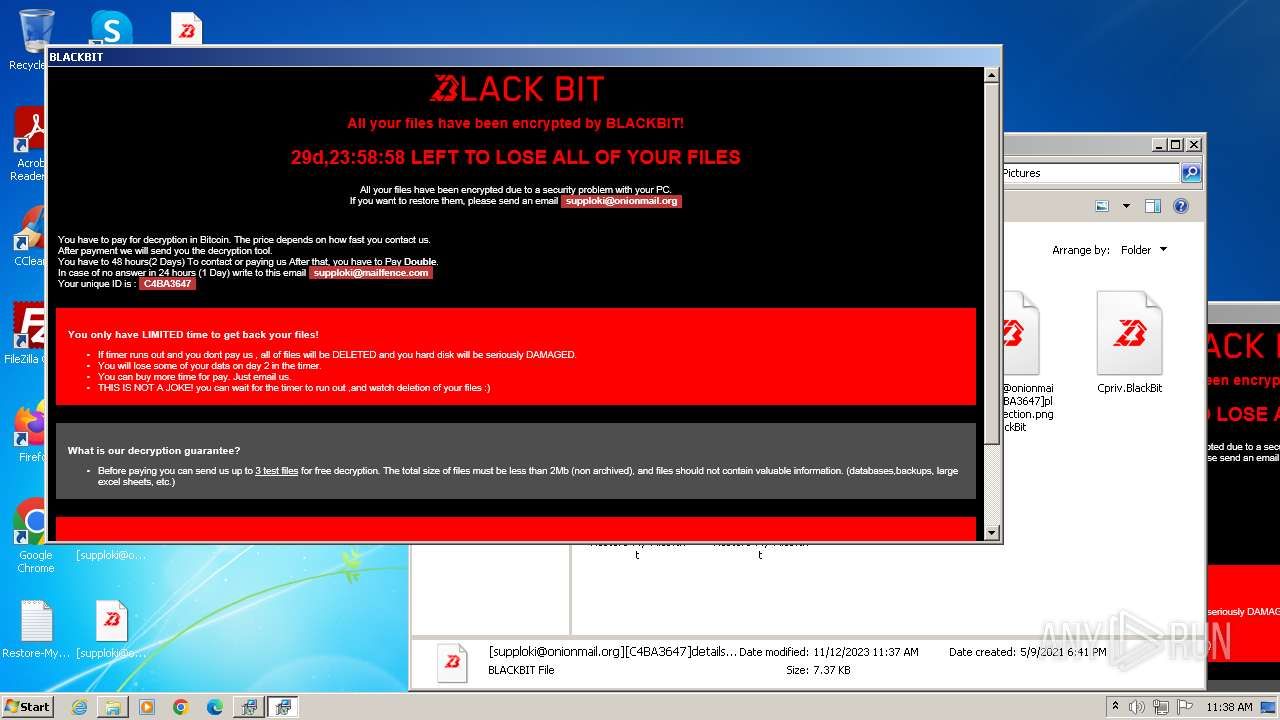
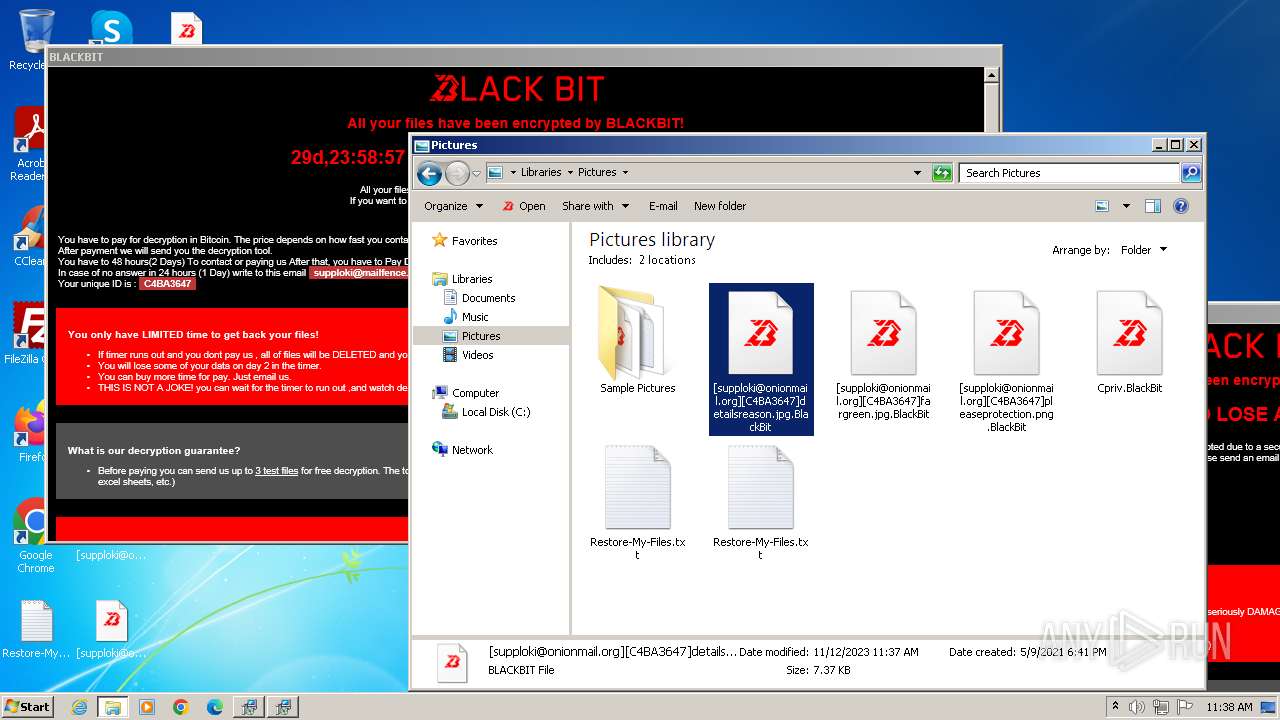
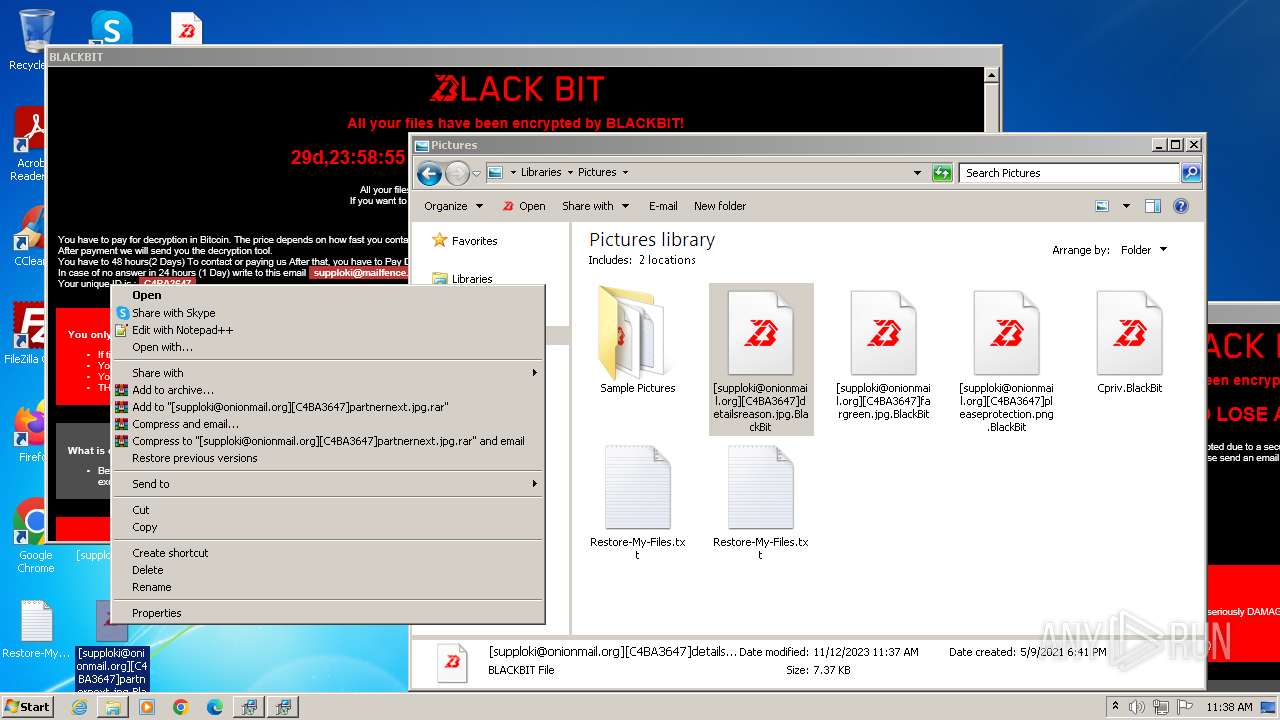
| Verdict: | Malicious activity |
| Analysis date: | November 12, 2023, 11:36:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7EF84720D7B30286BFF9483FE53BBA62 |
| SHA1: | B8DBB845CC37FA555D5A3F52E4BBB76AA2BE0933 |
| SHA256: | 9763DA5EE688A2391599A22638A84CBC7F99E32CD6865EAC4621CC427F6C3A63 |
| SSDEEP: | 12288:Dh1Lk70Tnvjcg27dWy1fX6qOLzvkLek4v+KXdPeA:fk70TrcbT56qOHv31PJv |
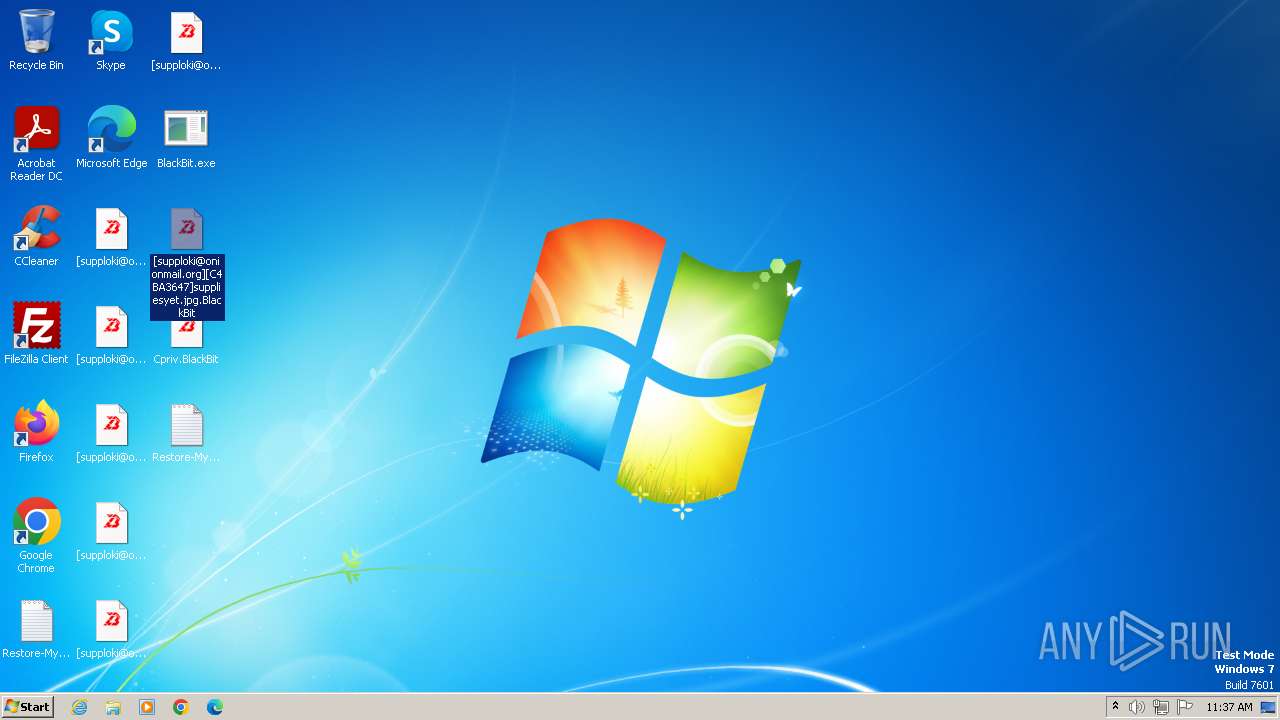
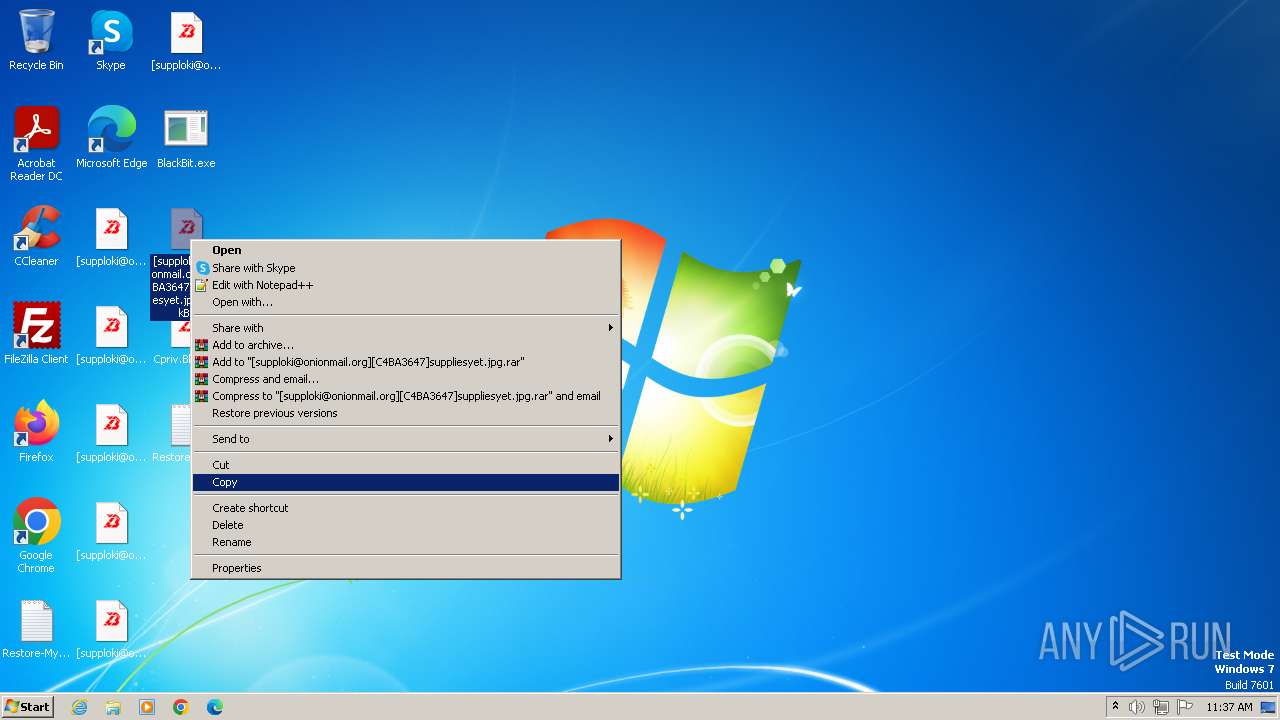
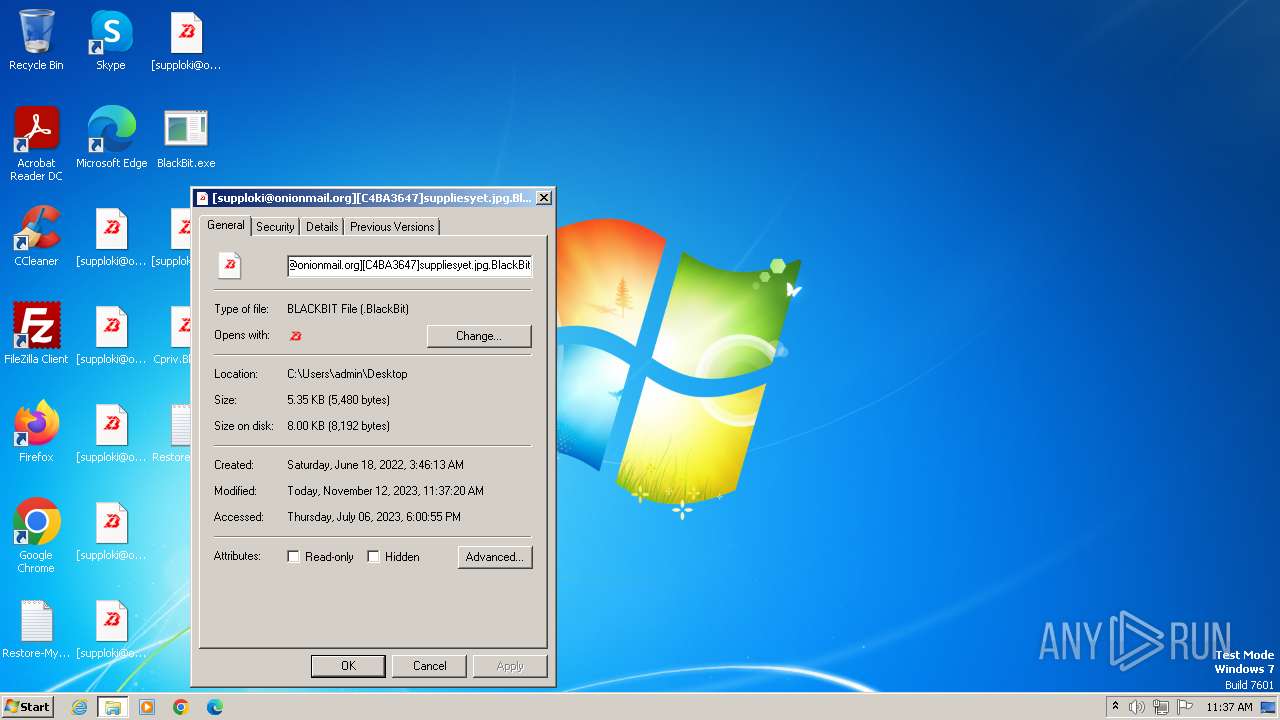
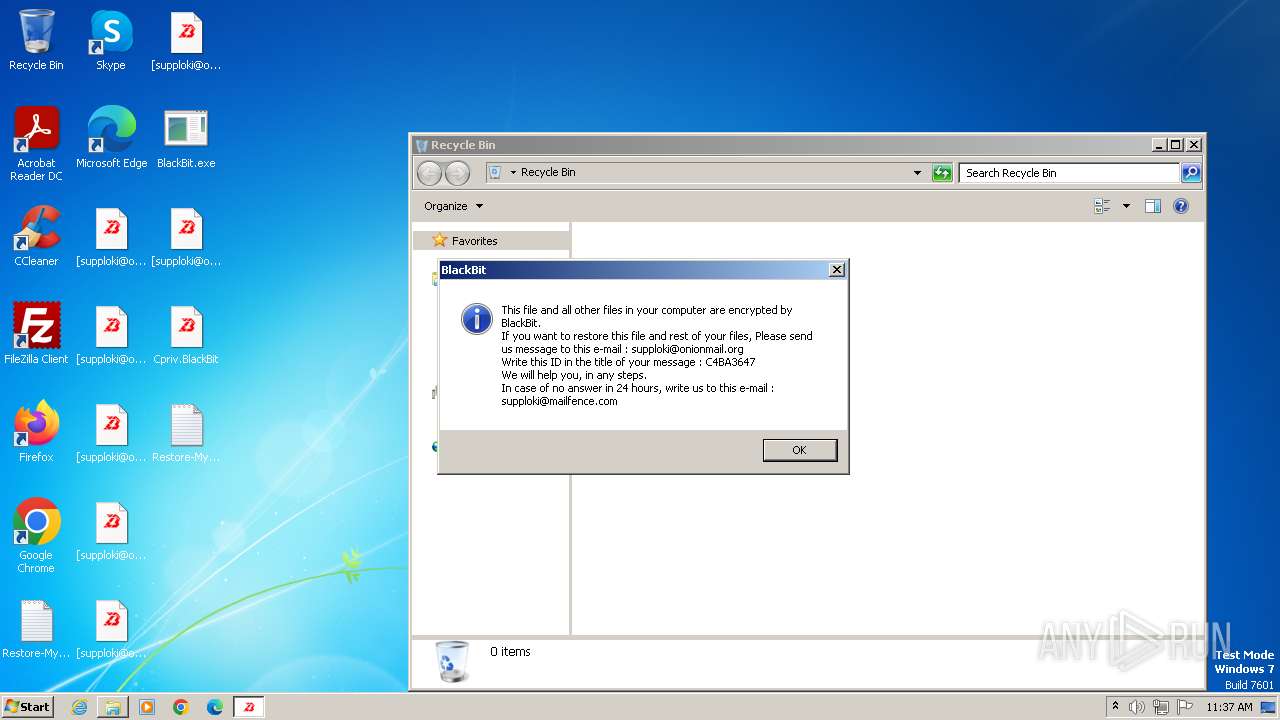
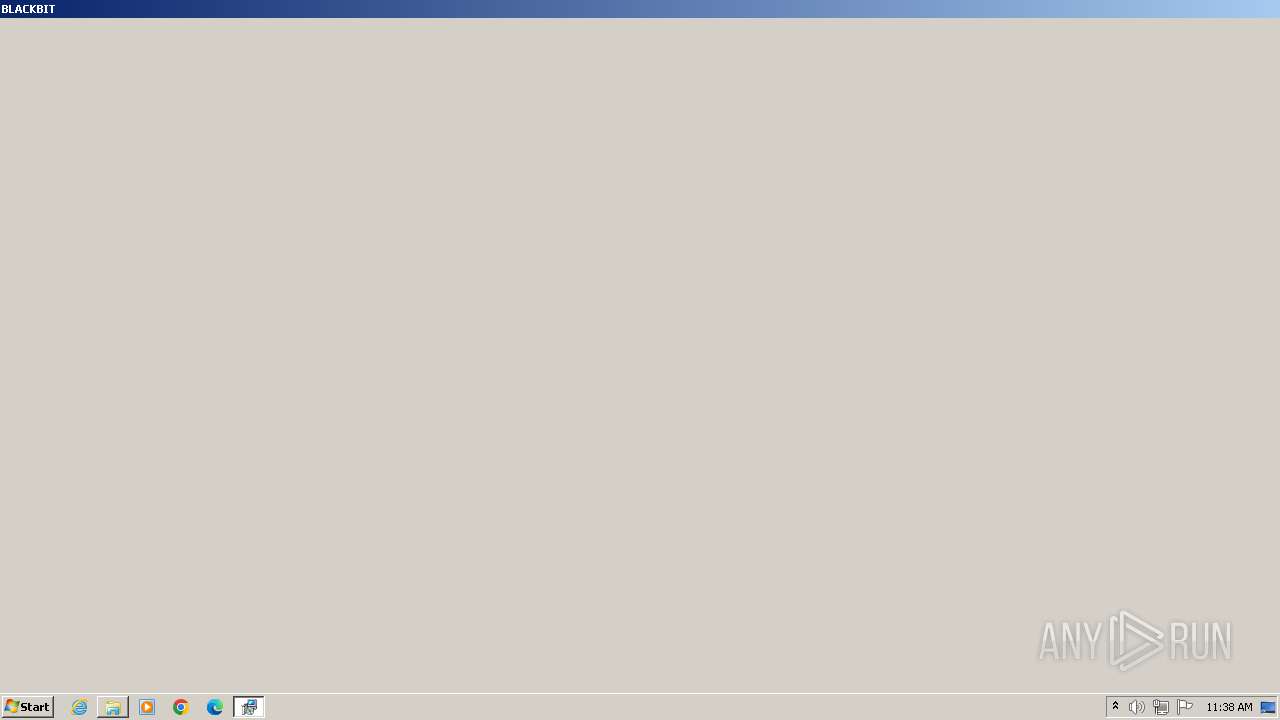
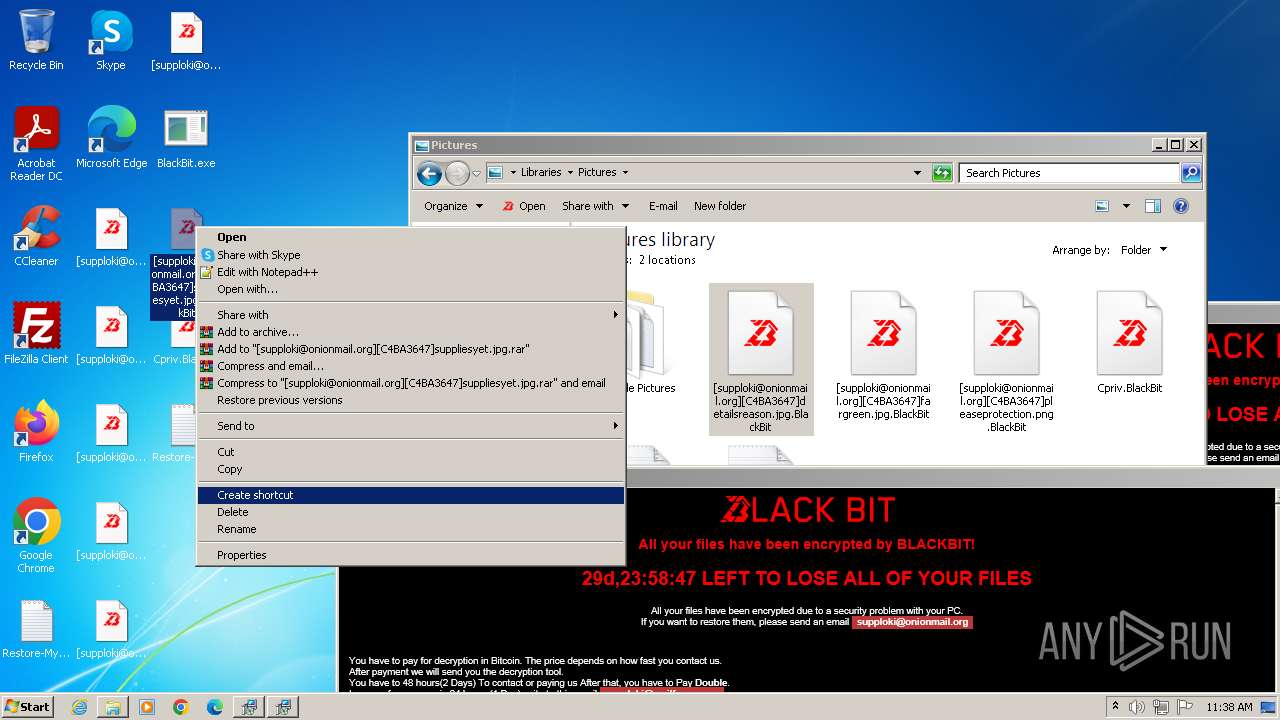
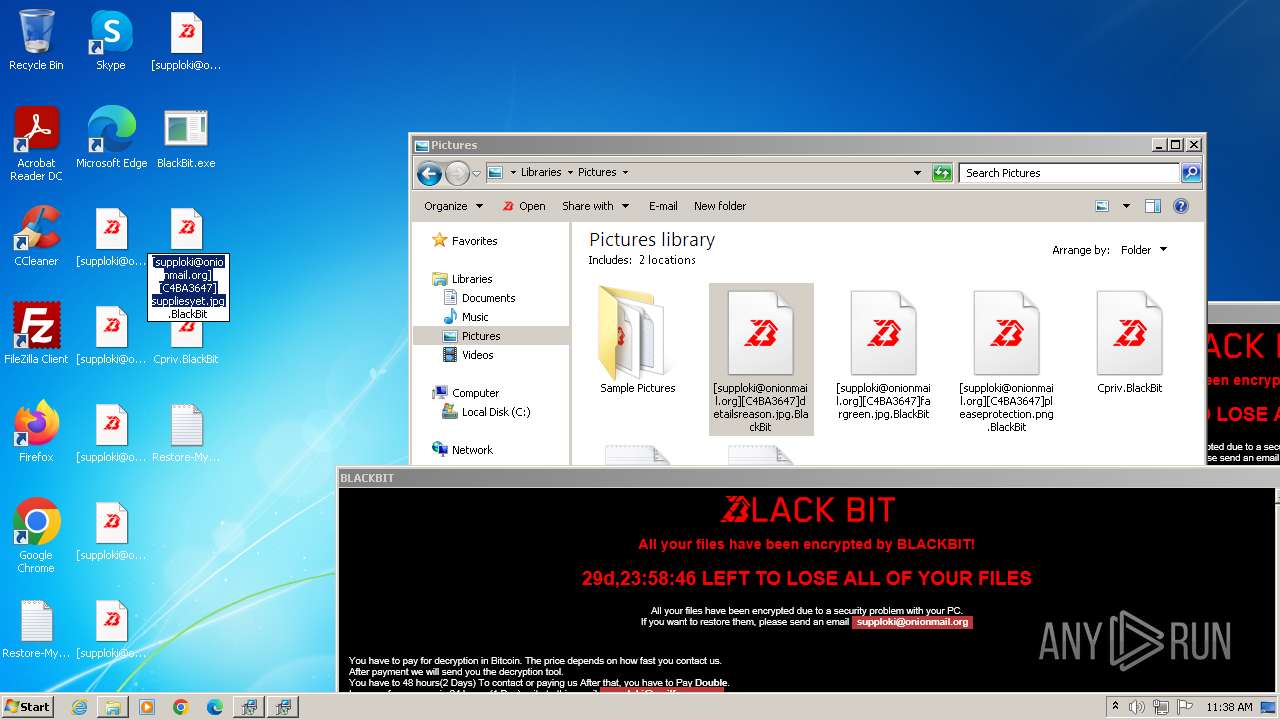
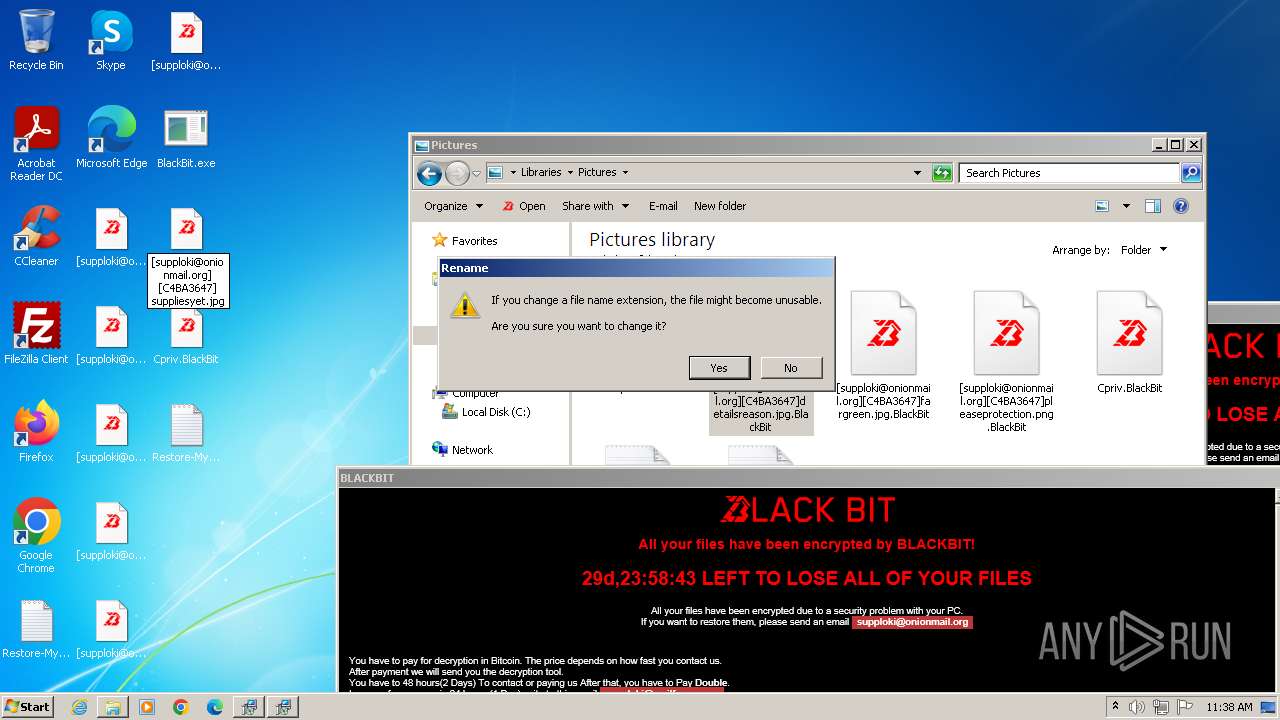
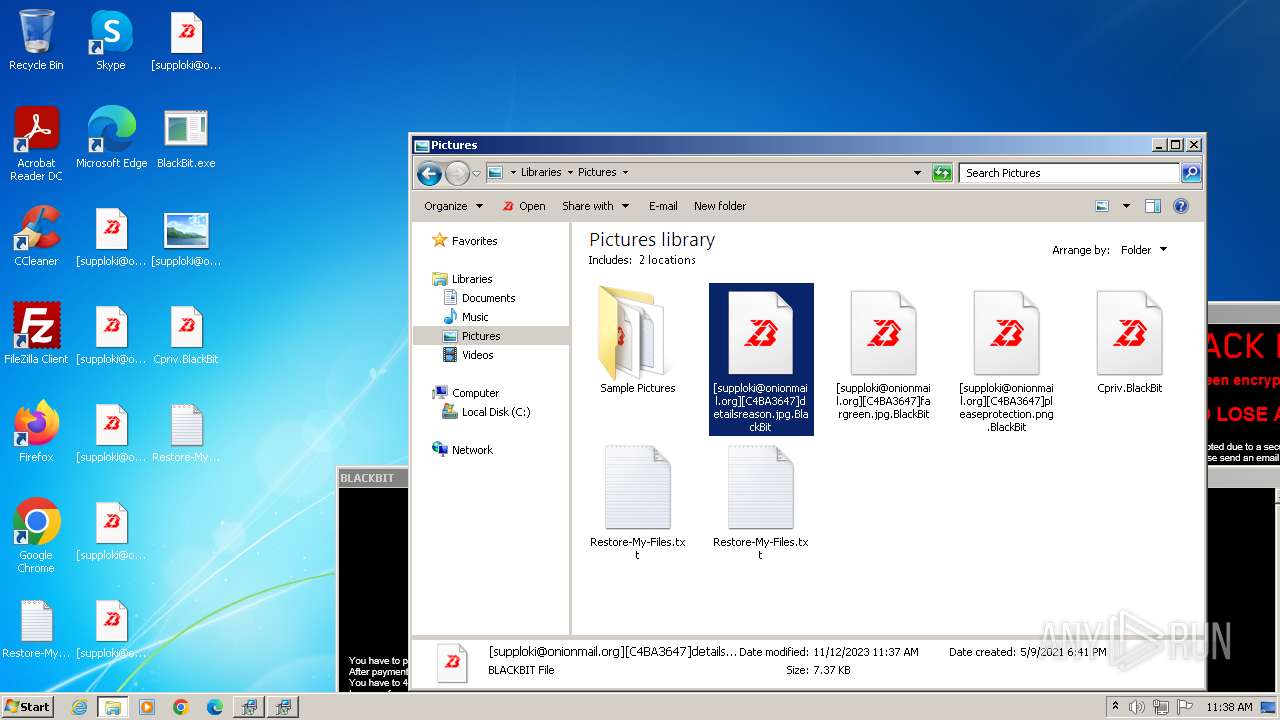
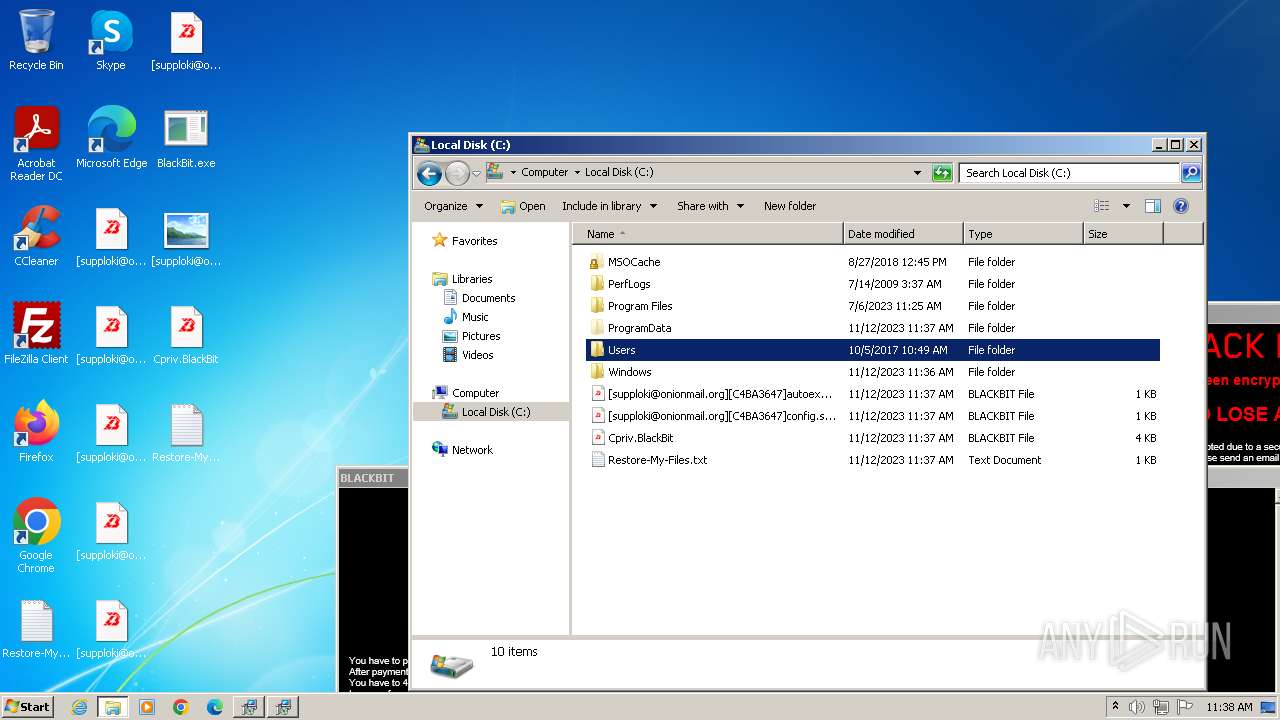
MALICIOUS
Drops the executable file immediately after the start
- BlackBit.exe (PID: 3196)
- csc.exe (PID: 3660)
- BlackBit.exe (PID: 3812)
- csc.exe (PID: 3908)
Create files in the Startup directory
- BlackBit.exe (PID: 3196)
- BlackBit.exe (PID: 3812)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 3596)
Starts Visual C# compiler
- BlackBit.exe (PID: 3196)
- BlackBit.exe (PID: 3812)
Deletes shadow copies
- cmd.exe (PID: 4016)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 3892)
- cmd.exe (PID: 3964)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 4056)
- cmd.exe (PID: 3536)
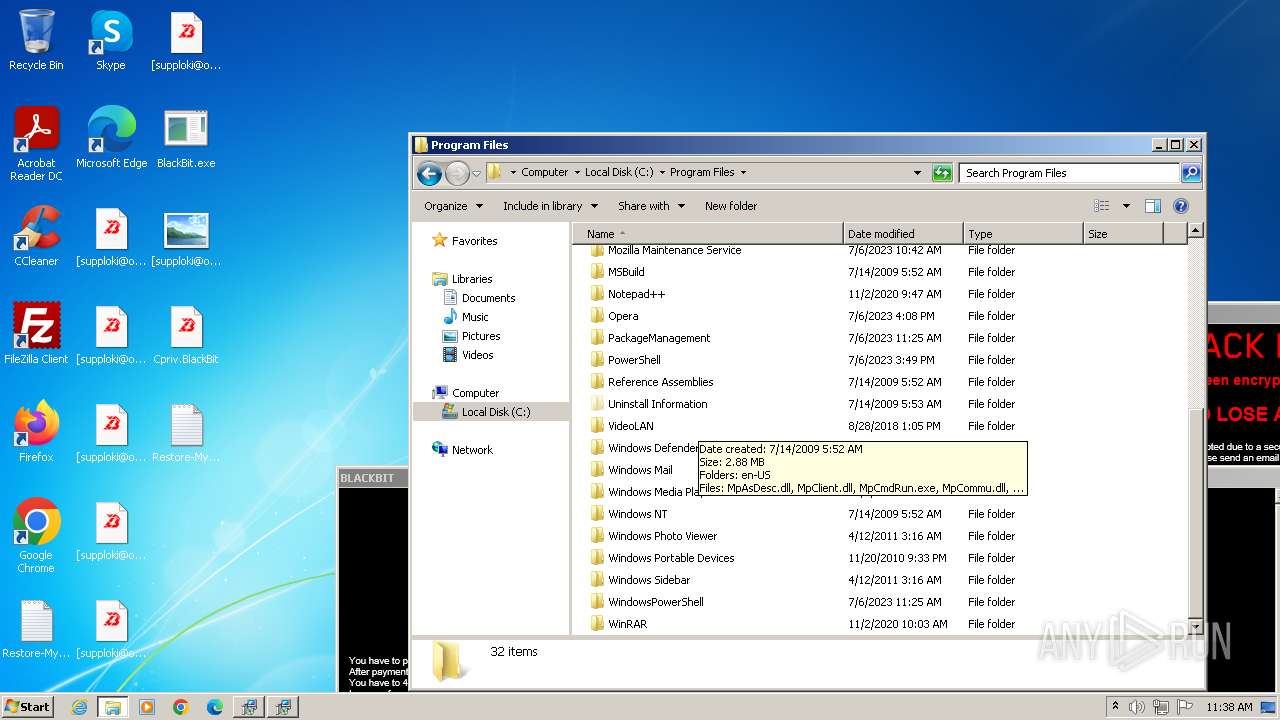
Disables Windows Defender
- BlackBit.exe (PID: 3812)
SUSPICIOUS
Application launched itself
- BlackBit.exe (PID: 3196)
Uses .NET C# to load dll
- BlackBit.exe (PID: 3812)
- BlackBit.exe (PID: 3196)
Starts CMD.EXE for commands execution
- BlackBit.exe (PID: 3196)
- BlackBit.exe (PID: 3812)
Reads the Internet Settings
- BlackBit.exe (PID: 3196)
- BlackBit.exe (PID: 3812)
- WMIC.exe (PID: 3788)
- 34z5kfkj.exe (PID: 2932)
- 34z5kfkj.exe (PID: 3264)
- mshta.exe (PID: 1904)
- mshta.exe (PID: 2460)
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 4068)
- cmd.exe (PID: 3712)
Executes as Windows Service
- VSSVC.exe (PID: 1528)
- wbengine.exe (PID: 1296)
- vds.exe (PID: 1928)
Uses pipe srvsvc via SMB (transferring data)
- BlackBit.exe (PID: 3812)
Checks for external IP
- BlackBit.exe (PID: 3812)
Write to the desktop.ini file (may be used to cloak folders)
- BlackBit.exe (PID: 3812)
INFO
Reads the computer name
- BlackBit.exe (PID: 3196)
- BlackBit.exe (PID: 3812)
- 34z5kfkj.exe (PID: 2932)
- 34z5kfkj.exe (PID: 3264)
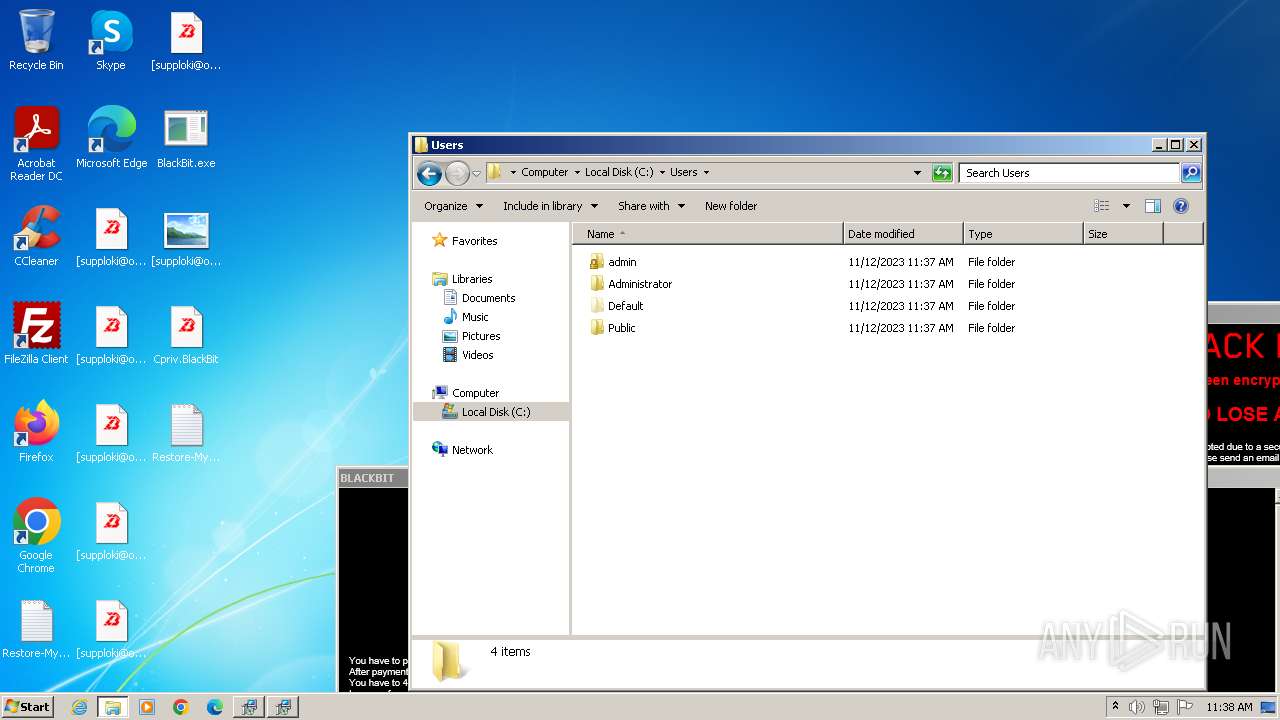
Creates files or folders in the user directory
- BlackBit.exe (PID: 3196)
Checks supported languages
- csc.exe (PID: 3660)
- cvtres.exe (PID: 3888)
- BlackBit.exe (PID: 3196)
- BlackBit.exe (PID: 3812)
- csc.exe (PID: 3908)
- cvtres.exe (PID: 3728)
- 34z5kfkj.exe (PID: 2932)
- 34z5kfkj.exe (PID: 3264)
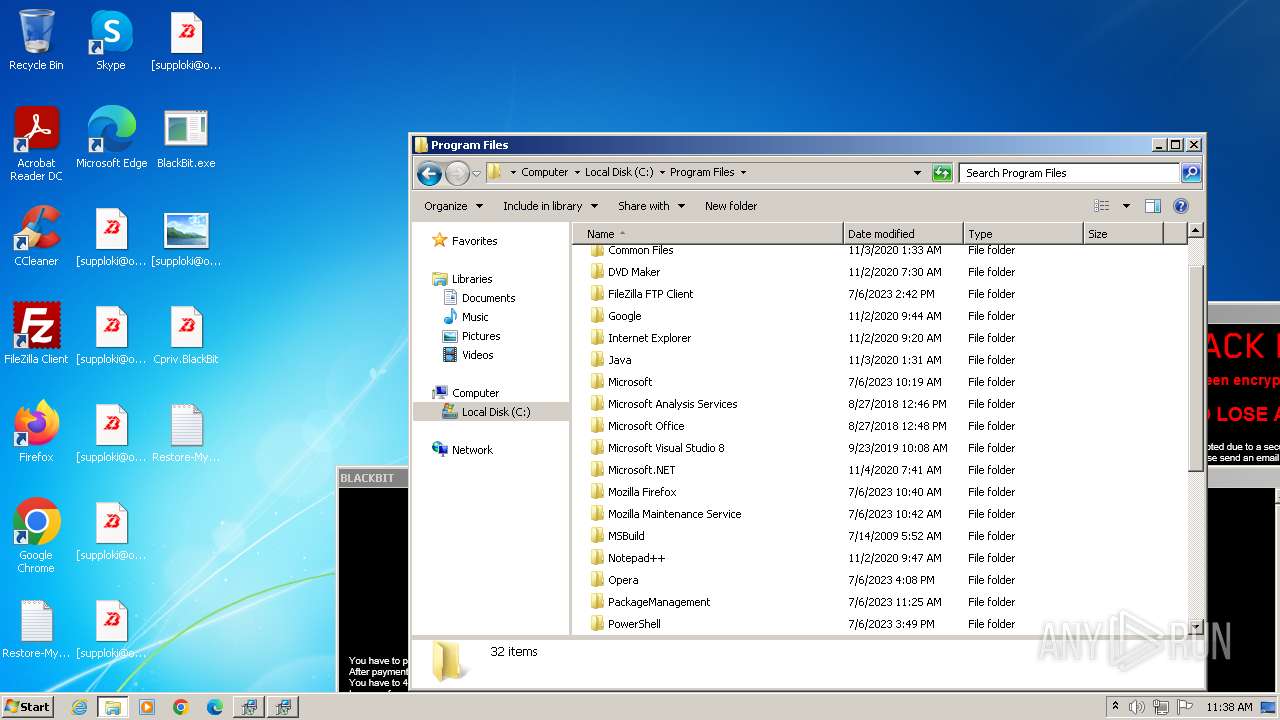
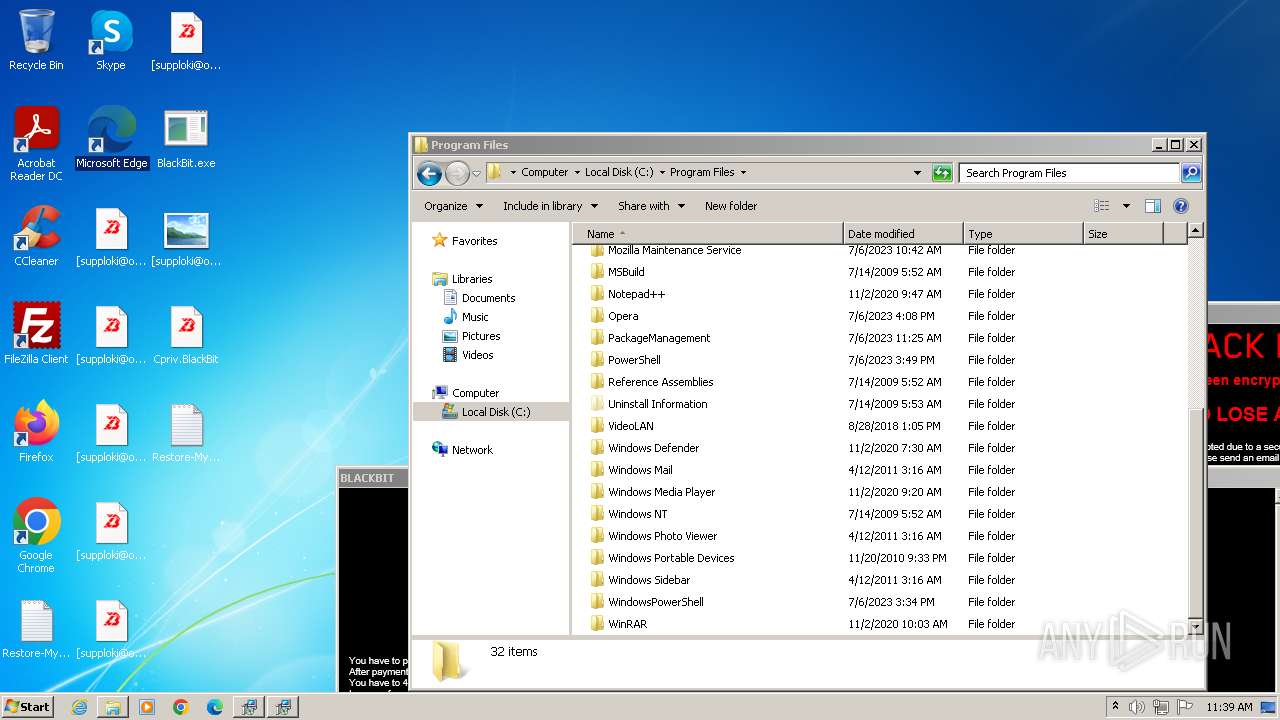
Creates files in the program directory
- BlackBit.exe (PID: 3196)
- csc.exe (PID: 3660)
- BlackBit.exe (PID: 3812)
- csc.exe (PID: 3908)
Reads the machine GUID from the registry
- csc.exe (PID: 3660)
- cvtres.exe (PID: 3888)
- BlackBit.exe (PID: 3196)
- BlackBit.exe (PID: 3812)
- cvtres.exe (PID: 3728)
- csc.exe (PID: 3908)
Create files in a temporary directory
- cvtres.exe (PID: 3888)
- BlackBit.exe (PID: 3196)
- cvtres.exe (PID: 3728)
- BlackBit.exe (PID: 3812)
Checks proxy server information
- BlackBit.exe (PID: 3812)
- mshta.exe (PID: 1904)
- mshta.exe (PID: 2460)
Manual execution by a user
- 34z5kfkj.exe (PID: 2932)
- 34z5kfkj.exe (PID: 3264)
Reads Internet Explorer settings
- mshta.exe (PID: 1904)
- mshta.exe (PID: 2460)
Reads Environment values
- BlackBit.exe (PID: 3812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:07:14 00:47:16+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 104448 |
| InitializedDataSize: | 405504 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcd2f |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft |
| FileDescription: | svchost |
| FileVersion: | 1.0.0.0 |
| InternalName: | svchost.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFileName: | svchost.exe |
| ProductName: | svchost |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.2.0.0 |
Total processes
94
Monitored processes
35
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | bcdedit /set {default} recoveryenabled no | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1296 | "C:\Windows\system32\wbengine.exe" | C:\Windows\System32\wbengine.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Block Level Backup Engine Service EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1352 | netsh firewall set opmode mode=disable | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1528 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1560 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1756 | netsh advfirewall set currentprofile state off | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | "C:\Windows\System32\mshta.exe" "C:\ProgramData\info.BlackBit" | C:\Windows\System32\mshta.exe | — | 34z5kfkj.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1928 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2196 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
5 024
Read events
4 781
Write events
243
Delete events
0
Modification events
| (PID) Process: | (3196) BlackBit.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3196) BlackBit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3196) BlackBit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3196) BlackBit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3196) BlackBit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3812) BlackBit.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3812) BlackBit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 115 | |||
| (PID) Process: | (3812) BlackBit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3812) BlackBit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3812) BlackBit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
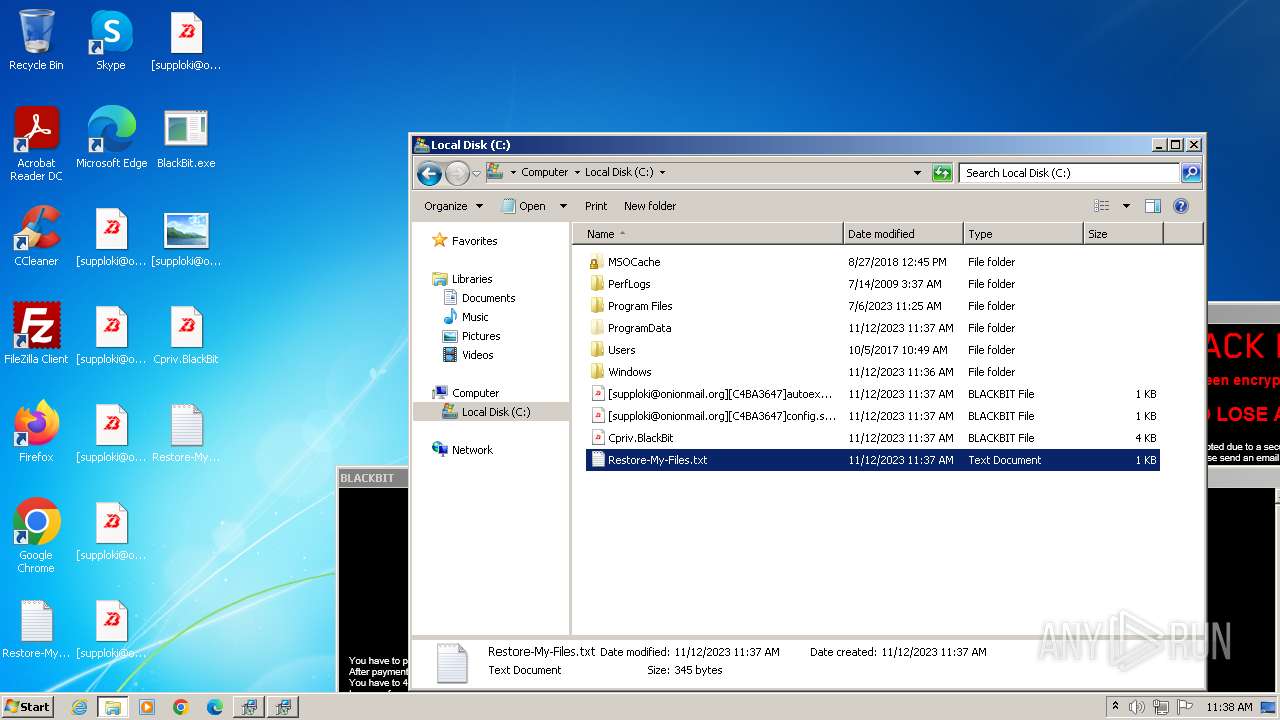
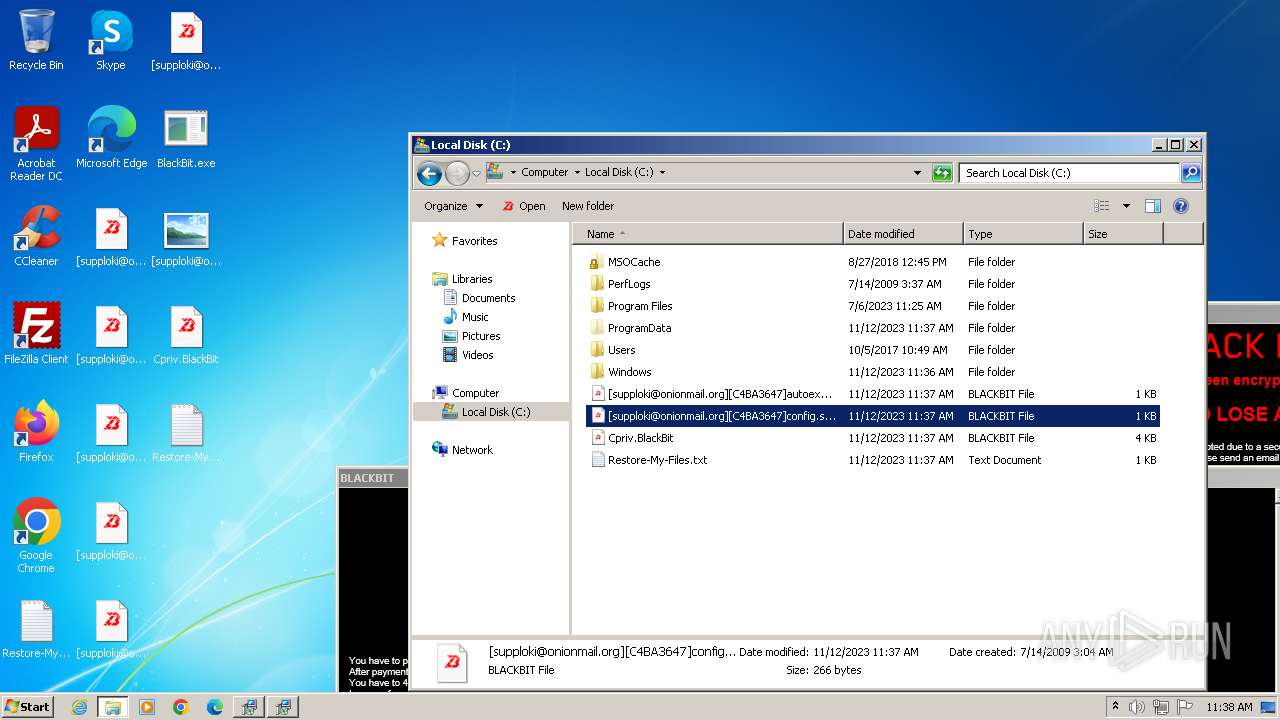
Executable files
21
Suspicious files
2 519
Text files
430
Unknown types
0
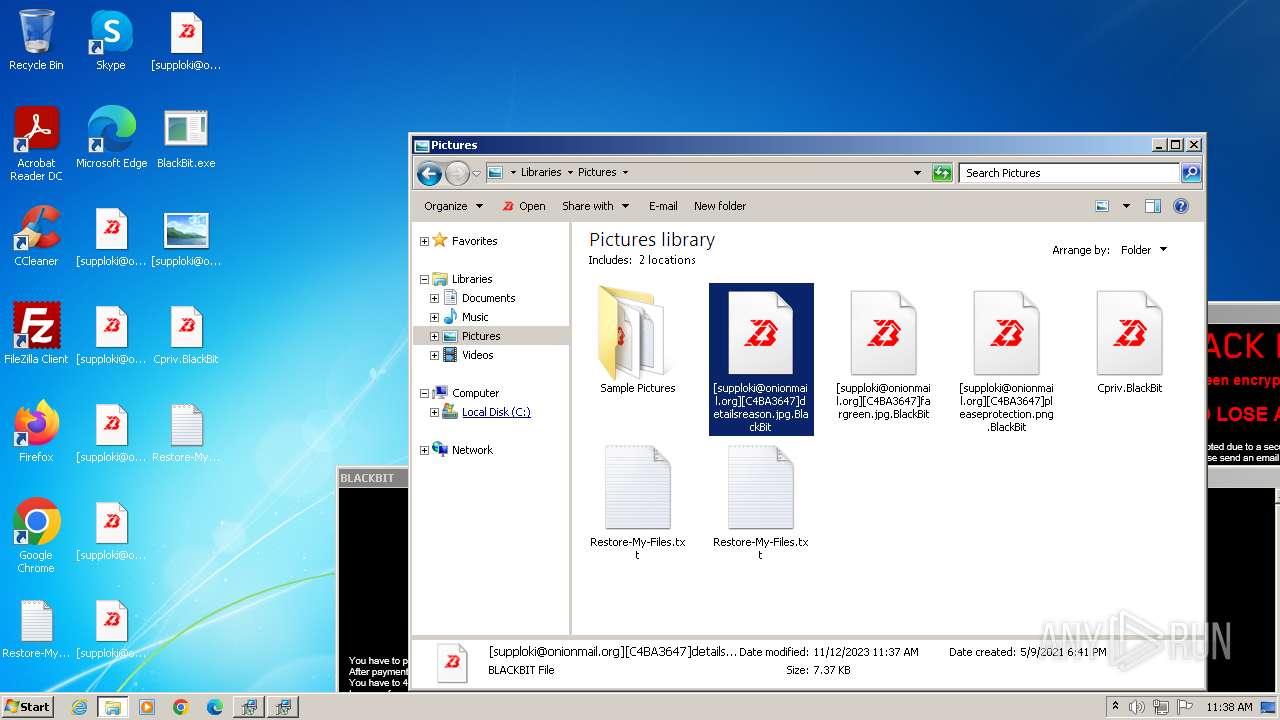
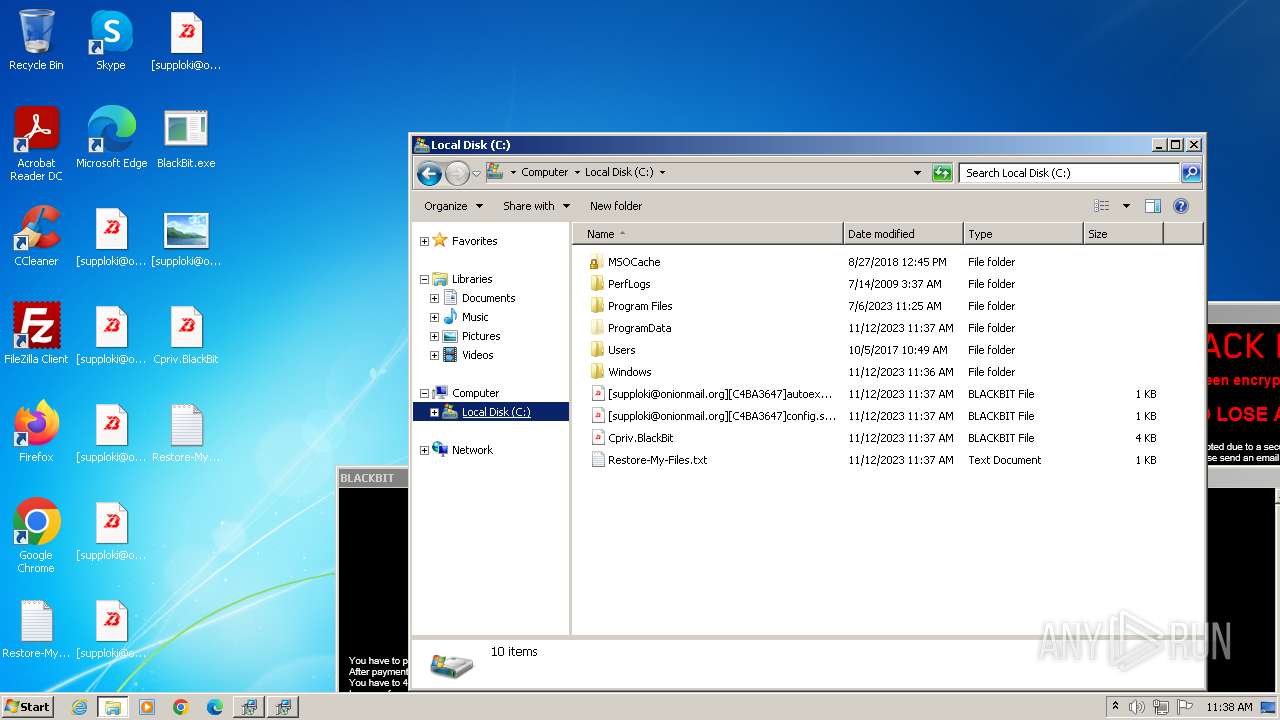
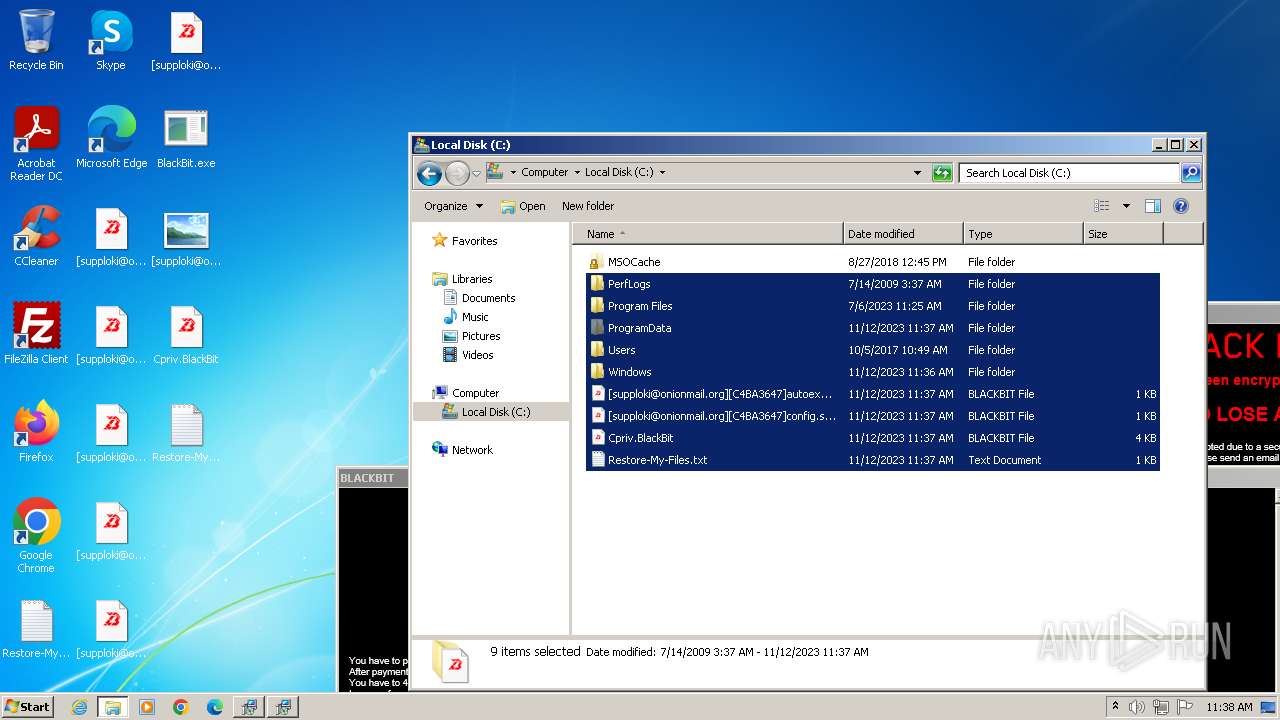
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3196 | BlackBit.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\wvtymcow.bat | text | |
MD5:3FC537B642D3756646715325299C6367 | SHA256:708511C356493E41CA103DB51B8DF3FB57898DDB2BB7CF4F11560FACDE9425ED | |||
| 3196 | BlackBit.exe | C:\Users\admin\AppData\Roaming\winlogon.exe | executable | |
MD5:7EF84720D7B30286BFF9483FE53BBA62 | SHA256:9763DA5EE688A2391599A22638A84CBC7F99E32CD6865EAC4621CC427F6C3A63 | |||
| 3196 | BlackBit.exe | C:\Users\admin\AppData\Local\Temp\dtno1n4e.0.cs | text | |
MD5:ED3B14701505E0AFC3B3601A186723B1 | SHA256:5B346C3CCD41B371738DDC925296203D504B4F5F47E2FE0D9F37533C1E6AB4E9 | |||
| 3196 | BlackBit.exe | C:\Users\admin\AppData\Local\Temp\dtno1n4e.cmdline | text | |
MD5:66AB00F8D8A0D553C90B6D55AA3AE0C7 | SHA256:B43AC3182150AA78F517D8CA4822727DC83349F5259E131EE701EABFDCDC1DDC | |||
| 3196 | BlackBit.exe | C:\Users\admin\AppData\Local\Temp\y2rtz4lf.ico | image | |
MD5:305C2042777E67710483E58ACC04AC2C | SHA256:F9DDF619CA0266055744C2BECA77673AA41702104B459A0F55DE3945196B6C50 | |||
| 3660 | csc.exe | C:\ProgramData\CSC64009A6D551740188A5FBE42EDE570A9.TMP | binary | |
MD5:E9BC8982C6F4DFFE08C13EEDF91479D2 | SHA256:AA26EFE29E2FAC2E6B07BB1784563B28CB1EF6A41BB03B383E9FB343B5742701 | |||
| 3196 | BlackBit.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\winlogon.exe | executable | |
MD5:7EF84720D7B30286BFF9483FE53BBA62 | SHA256:9763DA5EE688A2391599A22638A84CBC7F99E32CD6865EAC4621CC427F6C3A63 | |||
| 3660 | csc.exe | C:\Users\admin\AppData\Local\Temp\dtno1n4e.out | text | |
MD5:13BD771FC4B8059D0D2EB3C9EA5558F1 | SHA256:B8545DAEFCA18EED7FFBCC8A6845BBC08FFB234205A09BB714D2D45109549811 | |||
| 3196 | BlackBit.exe | C:\ProgramData\info.BlackBit | html | |
MD5:A74ADCC922088182C23915A09289BC95 | SHA256:9C1F7CEB8E95CB9580C7085BCD549F13063177AE965CDB2B50E0F1A66182D752 | |||
| 3196 | BlackBit.exe | C:\ProgramData\winlogon.exe | executable | |
MD5:7EF84720D7B30286BFF9483FE53BBA62 | SHA256:9763DA5EE688A2391599A22638A84CBC7F99E32CD6865EAC4621CC427F6C3A63 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
17
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3812 | BlackBit.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json | unknown | binary | 293 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.1:445 | — | — | — | unknown |
4 | System | 192.168.100.2:445 | — | — | — | whitelisted |
4 | System | 192.168.100.2:139 | — | — | — | whitelisted |
4 | System | 192.168.100.1:139 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.2:137 | — | — | — | whitelisted |
4 | System | 192.168.100.1:137 | — | — | — | unknown |
3812 | BlackBit.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
application-api.xyz |
| unknown |
ip-api.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3812 | BlackBit.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3812 | BlackBit.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |