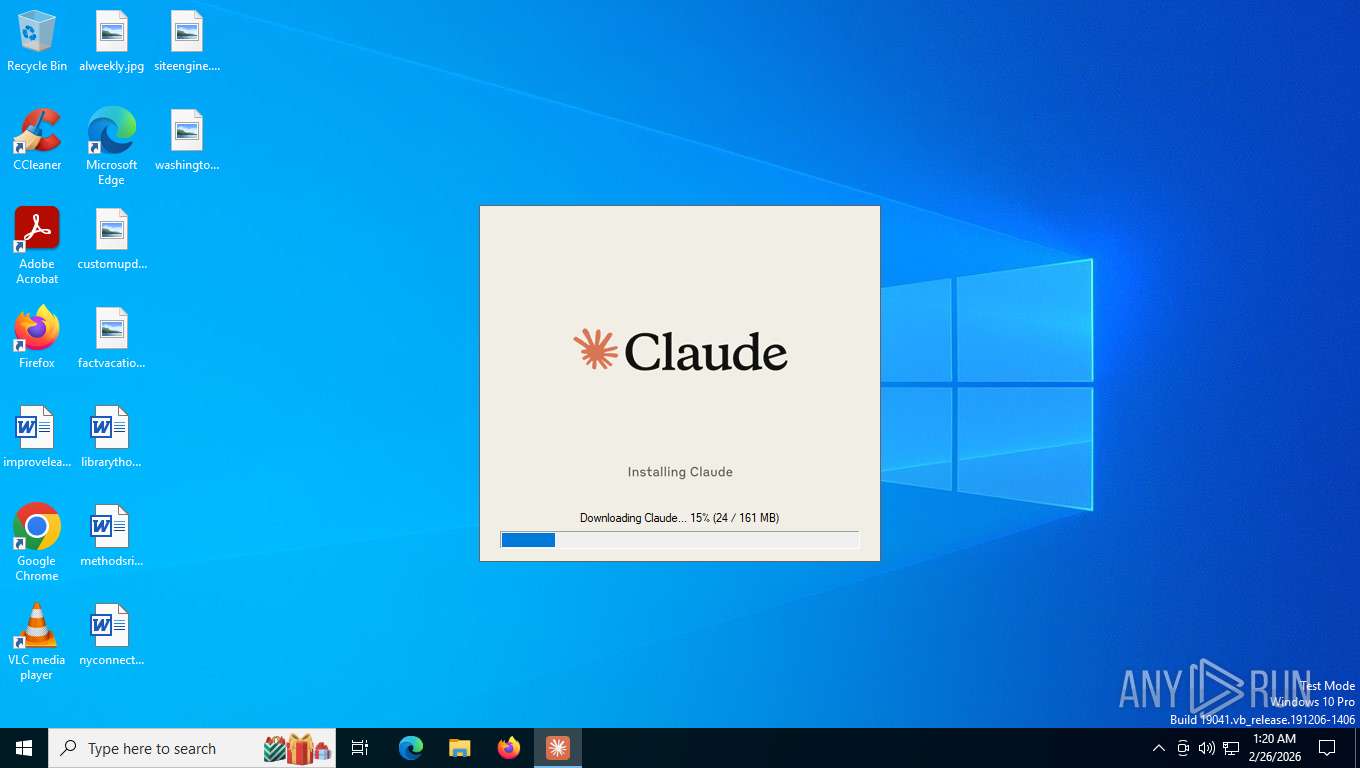
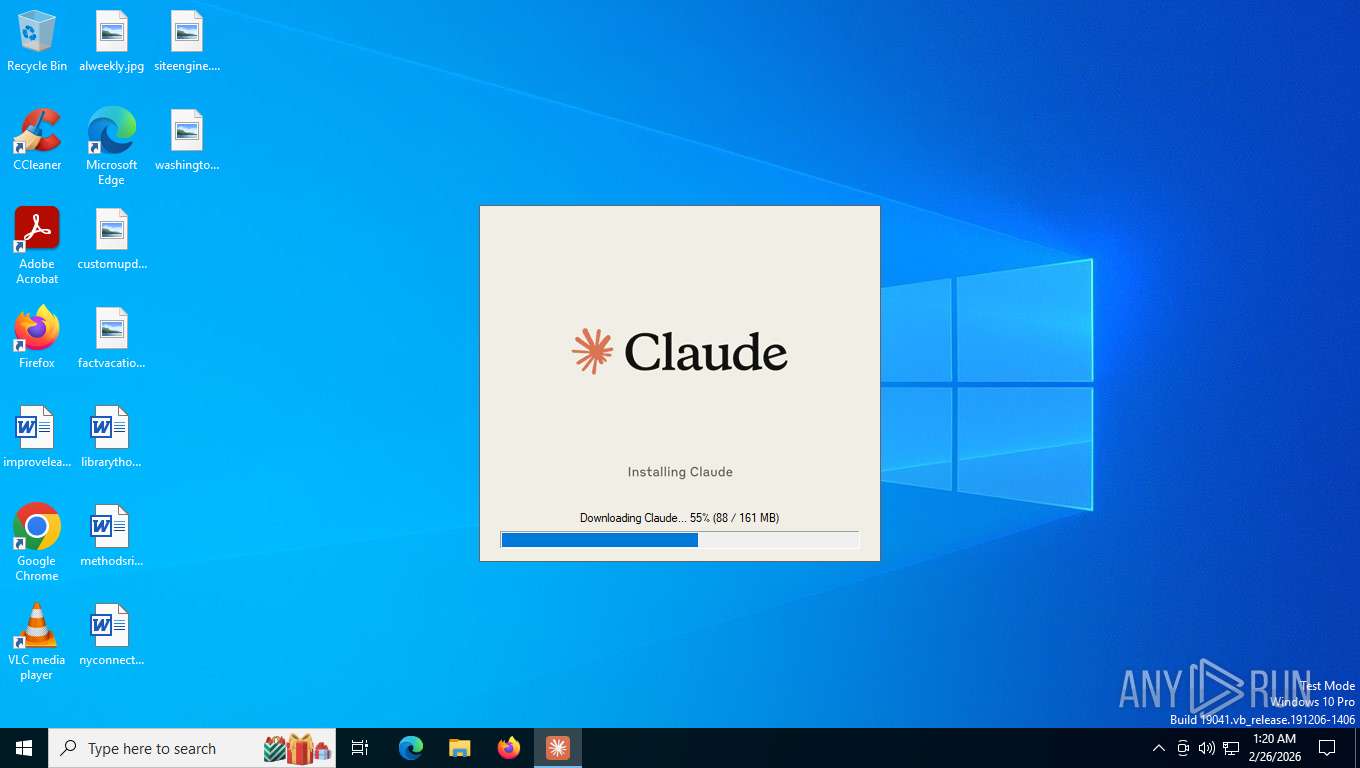
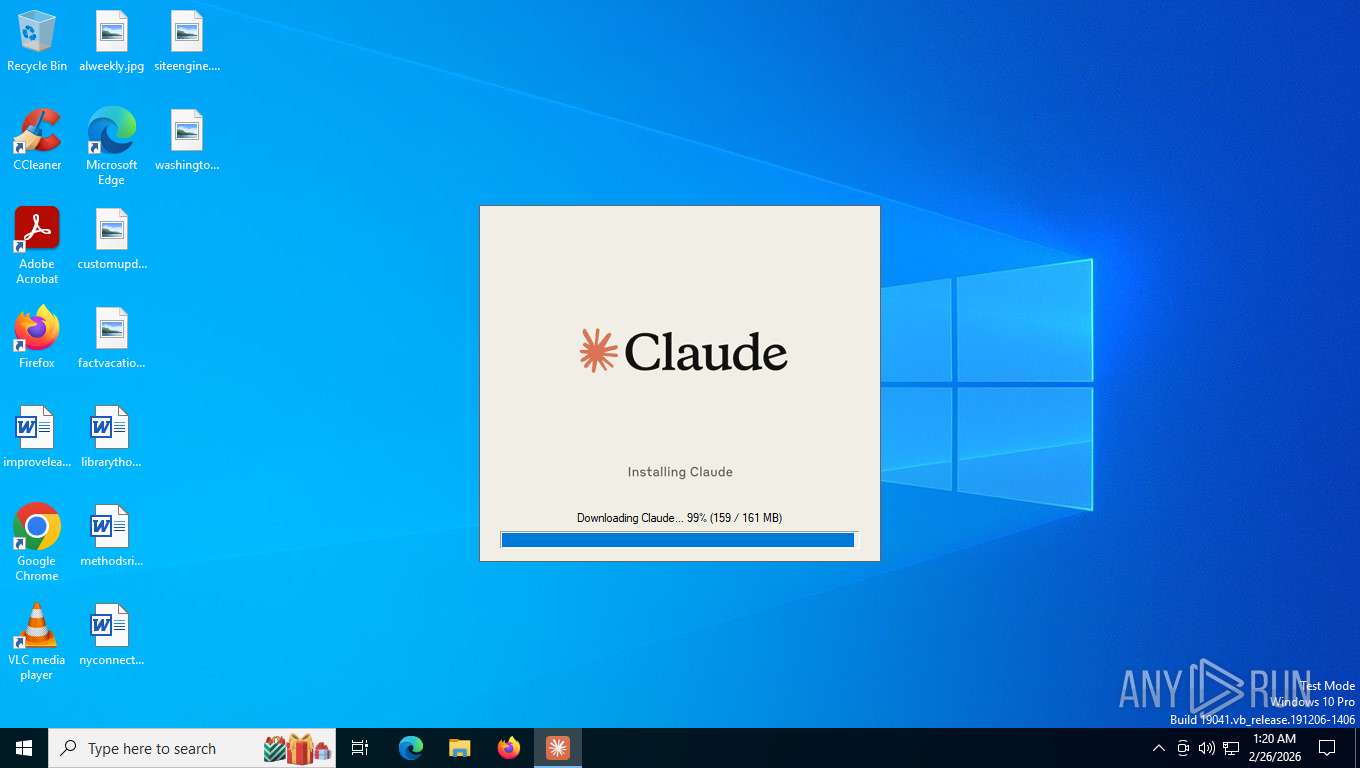
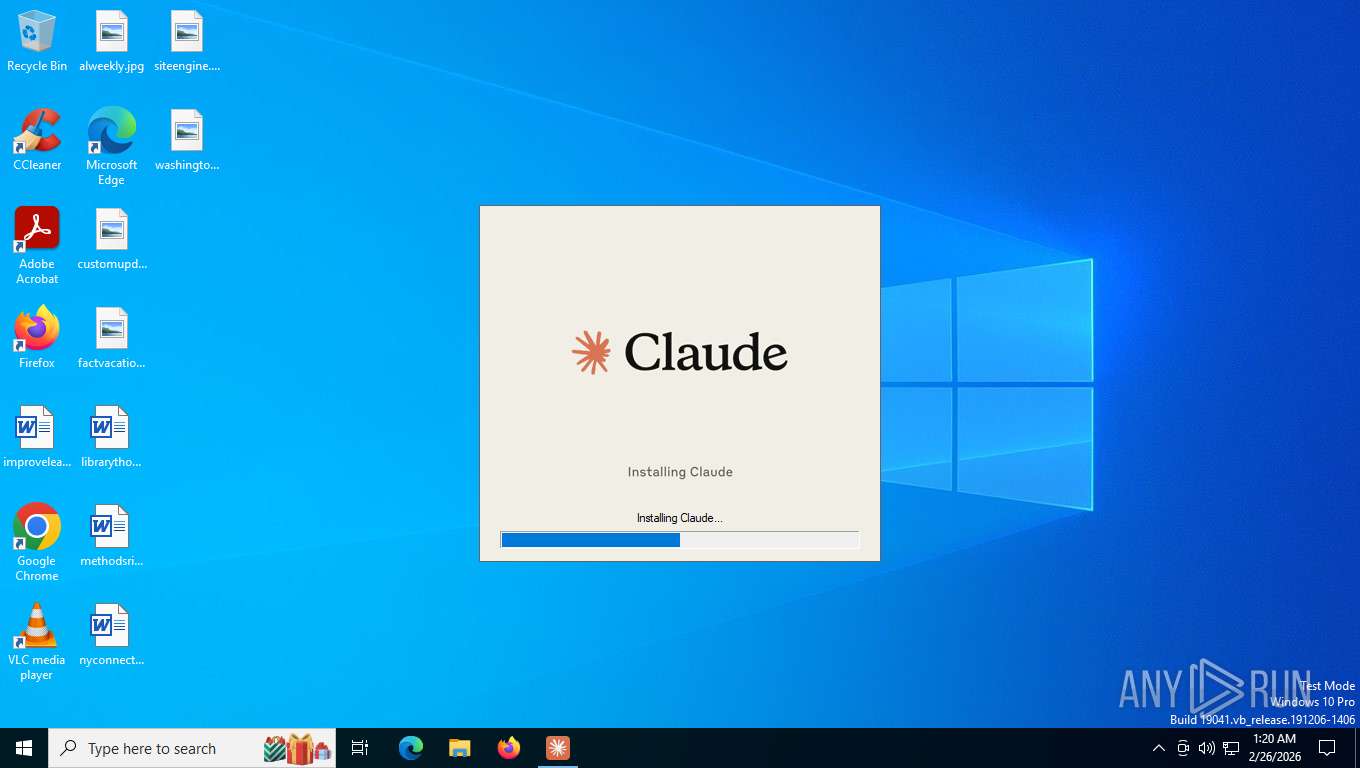
| File name: | Claude Setup.exe |
| Full analysis: | https://app.any.run/tasks/f949c8d1-efe5-45c3-af89-f6b9fb90ae86 |
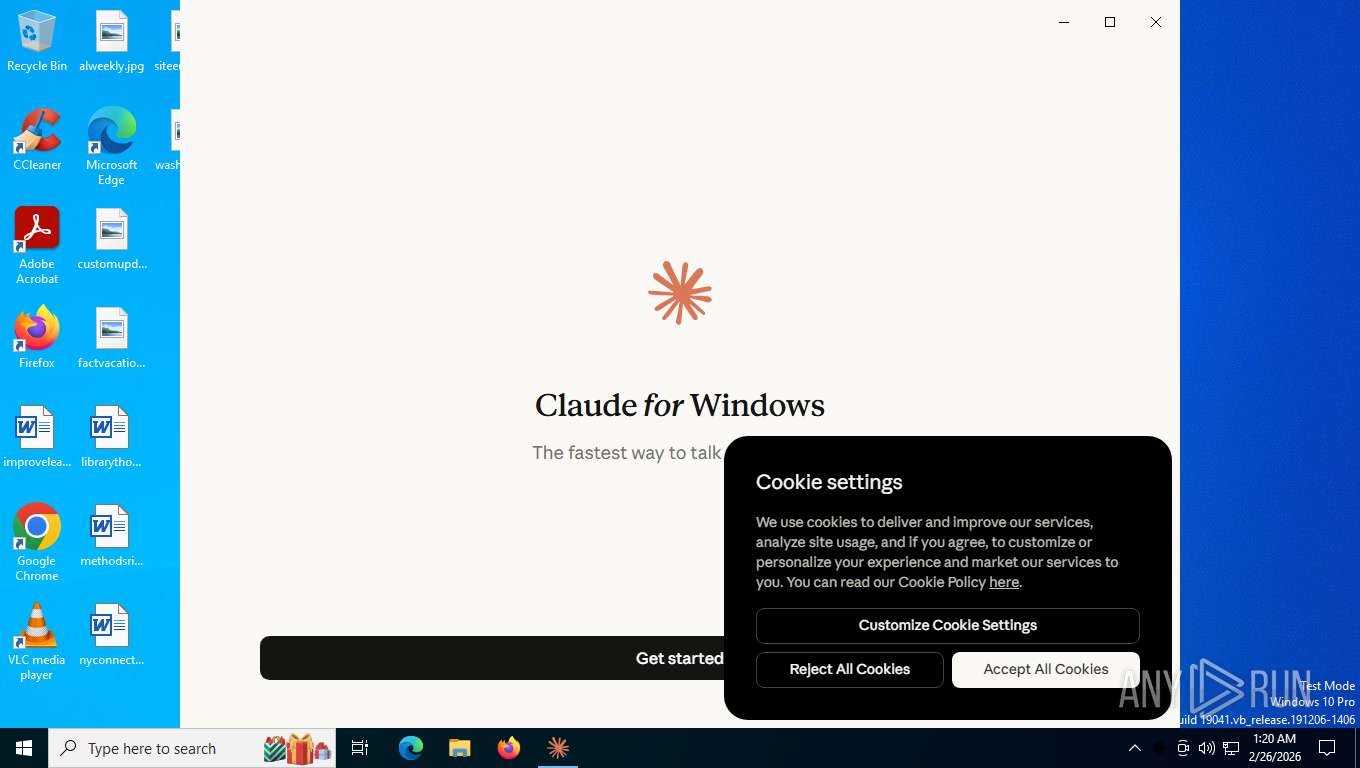
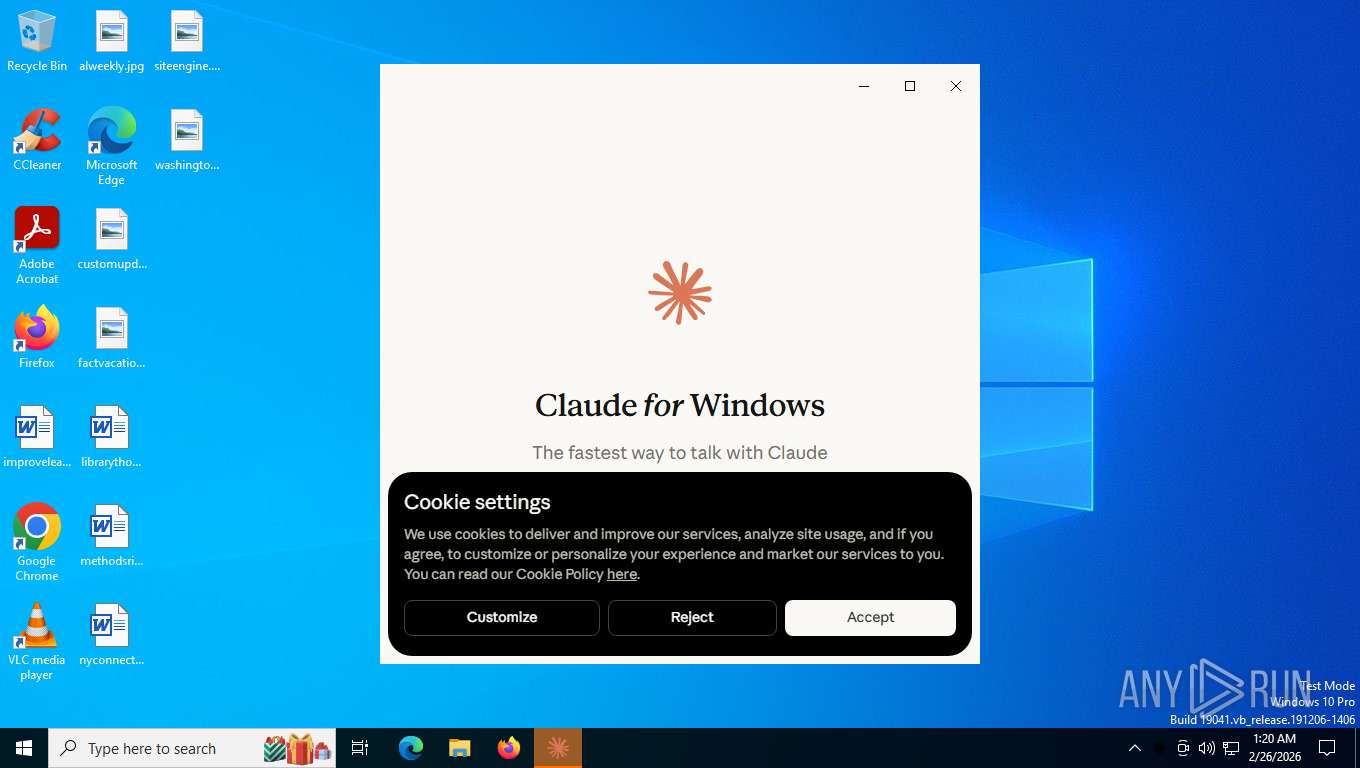
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2026, 06:20:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 9 sections |
| MD5: | B6E3201C64644D12AB91C4F909BE6F3B |
| SHA1: | 197D38C8EC9AD5815A2096FF8171CC8E42DF47FB |
| SHA256: | 975E739CD196FA1466BF28498DE3EA779D11CCE6699871C21D0EC0FD7964D14D |
| SSDEEP: | 98304:OB3nH/OL0cHjhNjJSJCf6cLAaOhVfVZYRs9FnVG/qeaK0qZSCes:T |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- Claude Setup.exe (PID: 7672)
- claude.exe (PID: 4472)
Reads the date of Windows installation
- Claude Setup.exe (PID: 7672)
Reads settings of System Certificates
- cowork-svc.exe (PID: 8532)
- claude.exe (PID: 4472)
The process checks if it is being run in the virtual environment
- cowork-svc.exe (PID: 8532)
Executes as Windows Service
- cowork-svc.exe (PID: 8532)
The process creates files with name similar to system file names
- claude.exe (PID: 4472)
Executable content was dropped or overwritten
- claude.exe (PID: 4472)
INFO
The sample compiled with english language support
- Claude Setup.exe (PID: 7672)
Checks supported languages
- Claude Setup.exe (PID: 7672)
- Claude Setup.exe (PID: 8196)
- cowork-svc.exe (PID: 8532)
- claude.exe (PID: 4472)
- claude.exe (PID: 552)
- claude.exe (PID: 2860)
- claude.exe (PID: 2944)
- claude.exe (PID: 5796)
- claude.exe (PID: 6804)
- claude.exe (PID: 3552)
- claude.exe (PID: 148)
Reads the computer name
- Claude Setup.exe (PID: 7672)
- Claude Setup.exe (PID: 8196)
- cowork-svc.exe (PID: 8532)
- claude.exe (PID: 4472)
- claude.exe (PID: 2944)
- claude.exe (PID: 2860)
Create files in a temporary directory
- Claude Setup.exe (PID: 7672)
- Claude Setup.exe (PID: 8196)
- claude.exe (PID: 4472)
Reads the machine GUID from the registry
- Claude Setup.exe (PID: 7672)
- Claude Setup.exe (PID: 8196)
- cowork-svc.exe (PID: 8532)
- claude.exe (PID: 4472)
Reads Environment values
- Claude Setup.exe (PID: 7672)
- Claude Setup.exe (PID: 8196)
- claude.exe (PID: 4472)
Process checks computer location settings
- Claude Setup.exe (PID: 7672)
- claude.exe (PID: 4472)
- claude.exe (PID: 5796)
- claude.exe (PID: 6804)
- claude.exe (PID: 148)
- claude.exe (PID: 3552)
Reads security settings of Internet Explorer
- Claude Setup.exe (PID: 7672)
- Claude Setup.exe (PID: 8196)
- explorer.exe (PID: 7752)
- explorer.exe (PID: 1040)
Application based on Golang
- Claude Setup.exe (PID: 7672)
Detects GO elliptic curve encryption (YARA)
- Claude Setup.exe (PID: 7672)
There is functionality for taking screenshot (YARA)
- Claude Setup.exe (PID: 7672)
Checks proxy server information
- Claude Setup.exe (PID: 8196)
Creates files or folders in the user directory
- Claude Setup.exe (PID: 8196)
- claude.exe (PID: 552)
- claude.exe (PID: 4472)
- claude.exe (PID: 2944)
Drops encrypted JS script (Microsoft Script Encoder)
- Claude Setup.exe (PID: 8196)
Reads product name
- claude.exe (PID: 4472)
Drops script file
- claude.exe (PID: 4472)
- Claude Setup.exe (PID: 8196)
Reads CPU info
- claude.exe (PID: 4472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 2997760 |
| InitializedDataSize: | 361984 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x77b60 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Anthropic, PBC |
| FileDescription: | Claude Setup |
| FileVersion: | 1.0.0.0 |
| InternalName: | ClaudeSetup |
| LegalCopyright: | 2025 Anthropic PBC |
| OriginalFileName: | ClaudeSetup.exe |
| ProductName: | Claude |
| ProductVersion: | 1.0.0.0 |
Total processes
163
Monitored processes
14
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\Claude.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Claude" --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --app-path="C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\resources\app.asar" --enable-sandbox --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --time-ticks-at-unix-epoch=-1772084826014291 --launch-time-ticks=2008329523 --field-trial-handle=2012,i,11625982128391679714,12515681625132041352,262144 --enable-features=DocumentPolicyIncludeJSCallStacksInCrashReports,EnableTransparentHwndEnlargement,PdfUseShowSaveFilePicker --disable-features=LocalNetworkAccessChecks,NetworkServiceSandbox,ScreenAIOCREnabled,SpareRendererForSitePerProcess,TraceSiteInstanceGetProcessCreation --variations-seed-version --trace-process-track-uuid=3190708990997080739 --mojo-platform-channel-handle=3020 --desktop-features="{\"nativeQuickEntry\":{\"status\":\"unavailable\"},\"quickEntryDictation\":{\"status\":\"unavailable\"},\"customQuickEntryDictationShortcut\":{\"status\":\"supported\"},\"plushRaccoon\":{\"status\":\"unavailable\"},\"quietPenguin\":{\"status\":\"unavailable\"},\"chillingSlothFeat\":{\"status\":\"unavailable\"},\"chillingSlothEnterprise\":{\"status\":\"supported\"},\"chillingSlothLocal\":{\"status\":\"supported\"},\"yukonSilver\":{\"status\":\"supported\"},\"yukonSilverGems\":{\"status\":\"supported\"},\"desktopTopBar\":{\"status\":\"supported\"},\"ccdPlugins\":{\"status\":\"supported\"}}" /prefetch:1 | C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\claude.exe | — | claude.exe | |||||||||||
User: admin Company: Anthropic Integrity Level: LOW Description: Claude Exit code: 0 Version: 1.1.4328 Modules
| |||||||||||||||
| 552 | "C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\Claude.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Roaming\Claude /prefetch:4 --no-rate-limit --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Roaming\Claude\Crashpad --url=https://f.a.k/e --annotation=_productName=Claude --annotation=_version=1.1.4328 --annotation=plat=Win64 --annotation=prod=Electron --annotation=ver=40.4.1 --initial-client-data=0x4bc,0x4c0,0x4c4,0x4b8,0x4c8,0x7ff643ffe774,0x7ff643ffe780,0x7ff643ffe790 | C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\claude.exe | — | claude.exe | |||||||||||
User: admin Company: Anthropic Integrity Level: MEDIUM Description: Claude Version: 1.1.4328 Modules
| |||||||||||||||
| 1040 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2572 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2860 | "C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\Claude.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\Claude" --gpu-preferences=SAAAAAAAAADgAAAEAAAAAAAAAAAAAGAAAQAAAAAAAAAAAAAAAAAAAAIAAAAAAAAAAAAAAAAAAAAQAAAAAAAAABAAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --field-trial-handle=2012,i,11625982128391679714,12515681625132041352,262144 --enable-features=DocumentPolicyIncludeJSCallStacksInCrashReports,EnableTransparentHwndEnlargement,PdfUseShowSaveFilePicker --disable-features=LocalNetworkAccessChecks,NetworkServiceSandbox,ScreenAIOCREnabled,SpareRendererForSitePerProcess,TraceSiteInstanceGetProcessCreation --variations-seed-version --trace-process-track-uuid=3190708988185955192 --mojo-platform-channel-handle=1700 /prefetch:2 | C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\claude.exe | — | claude.exe | |||||||||||
User: admin Company: Anthropic Integrity Level: LOW Description: Claude Version: 1.1.4328 Modules
| |||||||||||||||
| 2944 | "C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\Claude.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\Claude" --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --field-trial-handle=2012,i,11625982128391679714,12515681625132041352,262144 --enable-features=DocumentPolicyIncludeJSCallStacksInCrashReports,EnableTransparentHwndEnlargement,PdfUseShowSaveFilePicker --disable-features=LocalNetworkAccessChecks,NetworkServiceSandbox,ScreenAIOCREnabled,SpareRendererForSitePerProcess,TraceSiteInstanceGetProcessCreation --variations-seed-version --trace-process-track-uuid=3190708989122997041 --mojo-platform-channel-handle=2152 /prefetch:3 | C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\claude.exe | claude.exe | ||||||||||||
User: admin Company: Anthropic Integrity Level: MEDIUM Description: Claude Version: 1.1.4328 Modules
| |||||||||||||||
| 3552 | "C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\Claude.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Claude" --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --app-path="C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\resources\app.asar" --enable-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --time-ticks-at-unix-epoch=-1772084826014291 --launch-time-ticks=2008917569 --field-trial-handle=2012,i,11625982128391679714,12515681625132041352,262144 --enable-features=DocumentPolicyIncludeJSCallStacksInCrashReports,EnableTransparentHwndEnlargement,PdfUseShowSaveFilePicker --disable-features=LocalNetworkAccessChecks,NetworkServiceSandbox,ScreenAIOCREnabled,SpareRendererForSitePerProcess,TraceSiteInstanceGetProcessCreation --variations-seed-version --trace-process-track-uuid=3190708992871164437 --mojo-platform-channel-handle=3904 --desktop-features="{\"nativeQuickEntry\":{\"status\":\"unavailable\"},\"quickEntryDictation\":{\"status\":\"unavailable\"},\"customQuickEntryDictationShortcut\":{\"status\":\"supported\"},\"plushRaccoon\":{\"status\":\"unavailable\"},\"quietPenguin\":{\"status\":\"unavailable\"},\"chillingSlothFeat\":{\"status\":\"unavailable\"},\"chillingSlothEnterprise\":{\"status\":\"supported\"},\"chillingSlothLocal\":{\"status\":\"supported\"},\"yukonSilver\":{\"status\":\"supported\"},\"yukonSilverGems\":{\"status\":\"supported\"},\"desktopTopBar\":{\"status\":\"supported\"},\"ccdPlugins\":{\"status\":\"supported\"}}" /prefetch:1 | C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\claude.exe | — | claude.exe | |||||||||||
User: admin Company: Anthropic Integrity Level: LOW Description: Claude Version: 1.1.4328 Modules
| |||||||||||||||
| 4472 | "C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\Claude.exe" "claude:///" | C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\claude.exe | explorer.exe | ||||||||||||
User: admin Company: Anthropic Integrity Level: MEDIUM Description: Claude Version: 1.1.4328 Modules
| |||||||||||||||
| 5796 | "C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\Claude.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Claude" --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --app-path="C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\resources\app.asar" --enable-sandbox --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=4 --time-ticks-at-unix-epoch=-1772084826014291 --launch-time-ticks=2008306317 --field-trial-handle=2012,i,11625982128391679714,12515681625132041352,262144 --enable-features=DocumentPolicyIncludeJSCallStacksInCrashReports,EnableTransparentHwndEnlargement,PdfUseShowSaveFilePicker --disable-features=LocalNetworkAccessChecks,NetworkServiceSandbox,ScreenAIOCREnabled,SpareRendererForSitePerProcess,TraceSiteInstanceGetProcessCreation --variations-seed-version --trace-process-track-uuid=3190708990060038890 --mojo-platform-channel-handle=2720 /prefetch:1 | C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\claude.exe | — | claude.exe | |||||||||||
User: admin Company: Anthropic Integrity Level: LOW Description: Claude Version: 1.1.4328 Modules
| |||||||||||||||
| 6804 | "C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\Claude.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Claude" --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --app-path="C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\resources\app.asar" --enable-sandbox --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --time-ticks-at-unix-epoch=-1772084826014291 --launch-time-ticks=2008334824 --field-trial-handle=2012,i,11625982128391679714,12515681625132041352,262144 --enable-features=DocumentPolicyIncludeJSCallStacksInCrashReports,EnableTransparentHwndEnlargement,PdfUseShowSaveFilePicker --disable-features=LocalNetworkAccessChecks,NetworkServiceSandbox,ScreenAIOCREnabled,SpareRendererForSitePerProcess,TraceSiteInstanceGetProcessCreation --variations-seed-version --trace-process-track-uuid=3190708991934122588 --mojo-platform-channel-handle=2760 /prefetch:1 | C:\Program Files\WindowsApps\Claude_1.1.4328.0_x64__pzs8sxrjxfjjc\app\claude.exe | — | claude.exe | |||||||||||
User: admin Company: Anthropic Integrity Level: LOW Description: Claude Version: 1.1.4328 Modules
| |||||||||||||||
Total events
14 693
Read events
14 671
Write events
4
Delete events
18
Modification events
| (PID) Process: | (1040) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1040) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1040) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4472) claude.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (4472) claude.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (4472) claude.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
| (PID) Process: | (4472) claude.exe | Key: | HKEY_CLASSES_ROOT\claude |
| Operation: | write | Name: | URL Protocol |
Value: | |||
Executable files
1
Suspicious files
185
Text files
40
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7672 | Claude Setup.exe | C:\Users\admin\AppData\Local\Temp\Claude-84614505.msix.downloading | — | |
MD5:— | SHA256:— | |||
| 7672 | Claude Setup.exe | C:\Users\admin\AppData\Local\Temp\Claude-84614505.msix | — | |
MD5:— | SHA256:— | |||
| 8196 | Claude Setup.exe | C:\Users\admin\AppData\Local\Temp\APPX.lyvmmp02hbgv9c62qj4ogggy.tmp | xml | |
MD5:DC649832F9F66F6776A75F31A683609C | SHA256:913A2ACFA5260D7AFD087D9D3B281222101C4A38AD55E2DCC27F47B6C7A72B72 | |||
| 8196 | Claude Setup.exe | C:\Users\admin\AppData\Local\Temp\APPX.bgklag0u7c6pgvv35tjc7dbjc.tmp | binary | |
MD5:F8788BA412BCF7E9DD81E4968B6E5409 | SHA256:3468CC8A47557044067A14C40253149849B6F5E37BDE635FCDB224E6C726971B | |||
| 8196 | Claude Setup.exe | C:\Users\admin\AppData\Local\Temp\APPX.fp4ooz29p4onv7mvblsj4sruh.tmp | xml | |
MD5:DC649832F9F66F6776A75F31A683609C | SHA256:913A2ACFA5260D7AFD087D9D3B281222101C4A38AD55E2DCC27F47B6C7A72B72 | |||
| 8196 | Claude Setup.exe | C:\Users\admin\AppData\Local\Temp\APPX.b3zcnr0c5jgznr3sc8ac9imge.tmp | xml | |
MD5:37A95E169A783D23566E246C1D25D273 | SHA256:AC762136CB219DEFB272DEA6DE8612D2693FD4FED11371B67EAEB16A76AF39D6 | |||
| 8196 | Claude Setup.exe | C:\Users\admin\AppData\Local\Temp\APPX.4sl35vhh26rahsohtrfzx4nvb.tmp | xml | |
MD5:DC649832F9F66F6776A75F31A683609C | SHA256:913A2ACFA5260D7AFD087D9D3B281222101C4A38AD55E2DCC27F47B6C7A72B72 | |||
| 8196 | Claude Setup.exe | C:\Users\admin\AppData\Local\Temp\APPX.2uki8h6k5sbezrojekrtytvn.tmp | binary | |
MD5:F8788BA412BCF7E9DD81E4968B6E5409 | SHA256:3468CC8A47557044067A14C40253149849B6F5E37BDE635FCDB224E6C726971B | |||
| 8196 | Claude Setup.exe | C:\Users\admin\AppData\Local\Temp\APPX.8cixzl2aoeqt4nad9i2h1c5ib.tmp | xml | |
MD5:37A95E169A783D23566E246C1D25D273 | SHA256:AC762136CB219DEFB272DEA6DE8612D2693FD4FED11371B67EAEB16A76AF39D6 | |||
| 8196 | Claude Setup.exe | C:\Users\admin\AppData\Local\Temp\APPX.lv5x_o6dxx9agf70zjxpjywpg.tmp | xml | |
MD5:DC649832F9F66F6776A75F31A683609C | SHA256:913A2ACFA5260D7AFD087D9D3B281222101C4A38AD55E2DCC27F47B6C7A72B72 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
66
DNS requests
39
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8568 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
8568 | svchost.exe | GET | 200 | 23.53.41.90:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
8568 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
8196 | Claude Setup.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | US | binary | 471 b | whitelisted |
8196 | Claude Setup.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | US | binary | 727 b | whitelisted |
356 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | US | binary | 471 b | whitelisted |
5568 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 313 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/FlightSettings/FSService?ProcessorClockSpeed=3094&IsRetailOS=1&OEMManufacturerName=DELL&FlightingPolicyValue=3&EnablePreviewBuilds=4294967295&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&ManagePreviewBuilds=3&BranchReadinessLevelSource=0&AttrDataVer=186&ProcessorCores=6&BranchReadinessLevelRaw=16&TotalPhysicalRAM=6144&TPMVersion=0&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&DeviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&App=FSS&AppVer=10.0&SmartActiveHoursState=1&ActiveHoursStart=20&SecureBootCapable=0&ActiveHoursEnd=13&DeviceFamily=Windows.Desktop | US | text | 87.3 Kb | whitelisted |
5568 | SearchApp.exe | GET | 200 | 184.86.251.14:443 | https://th.bing.com/th?id=OCGE.9n7hl5s06zk0_v7_main&w=80&h=80&c=1&rs=1&p=0 | NL | image | 18.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
8568 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7304 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7672 | Claude Setup.exe | 160.79.104.10:443 | api.anthropic.com | ANTHROPIC | US | whitelisted |
7672 | Claude Setup.exe | 35.190.46.17:443 | downloads.claude.ai | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
8568 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8568 | svchost.exe | 23.53.41.90:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
8568 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
api.anthropic.com |
| whitelisted |
downloads.claude.ai |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6768 | MoUsoCoreWorker.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |