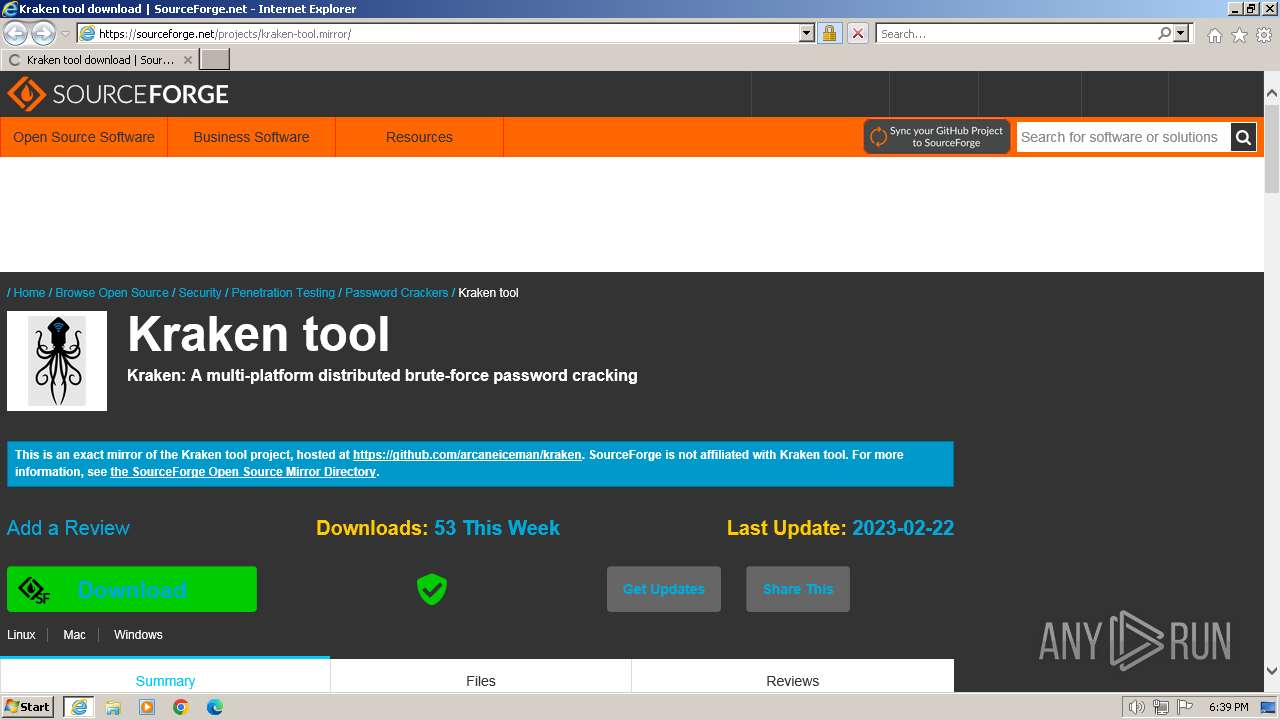
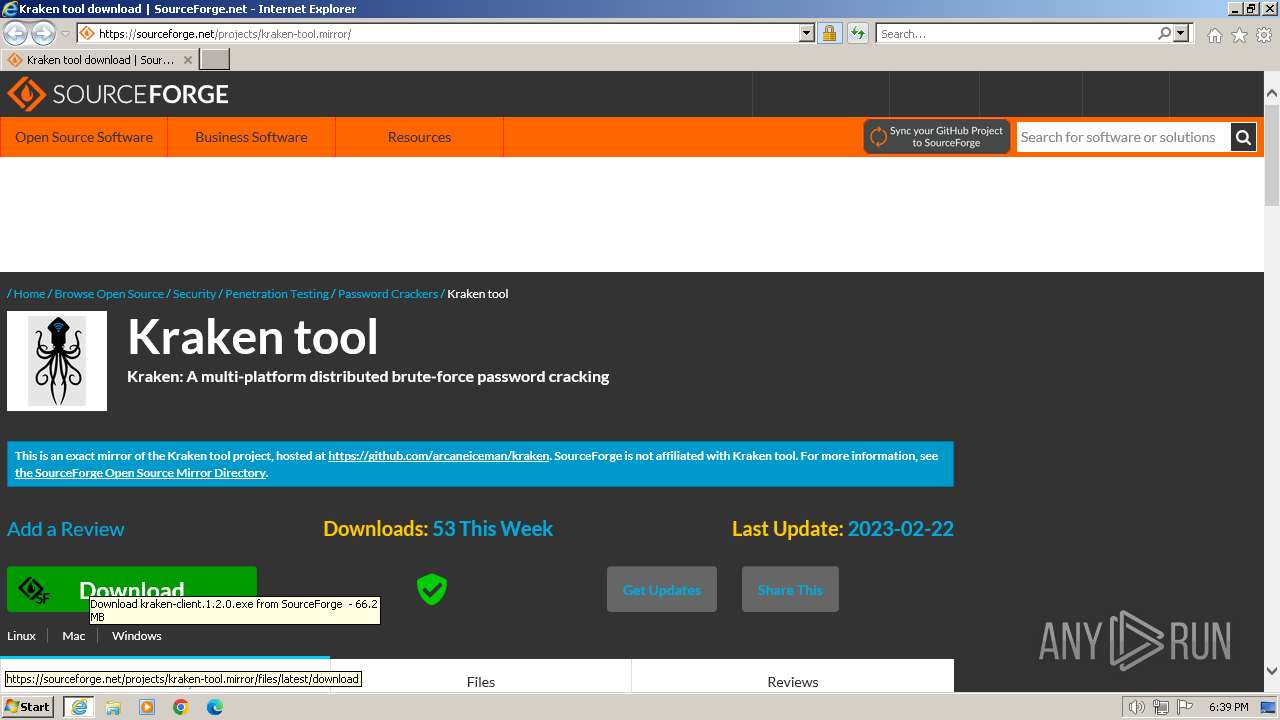
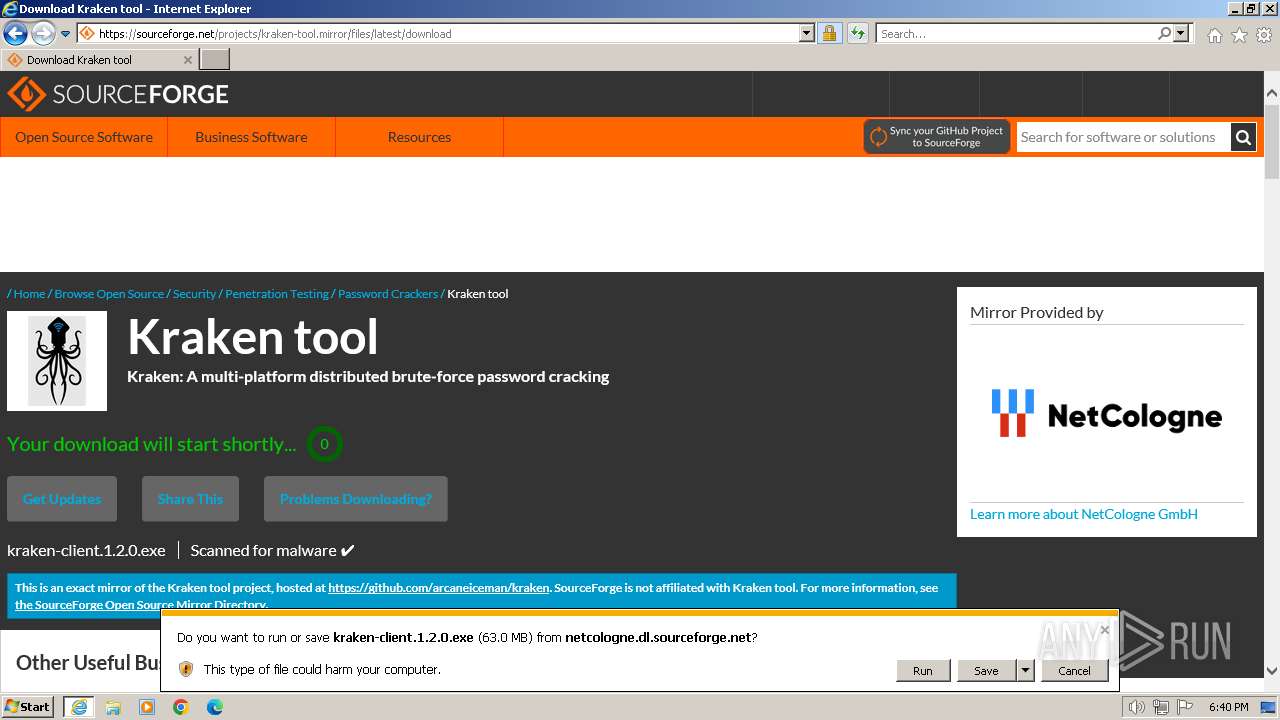
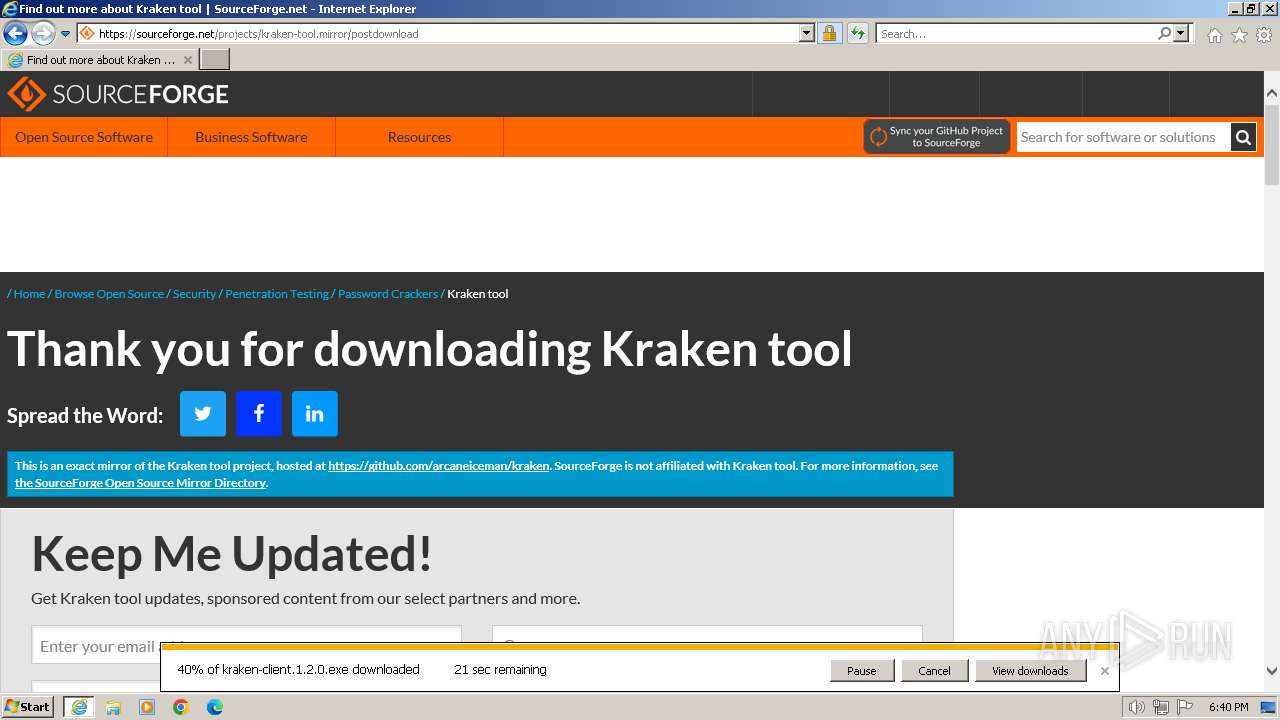
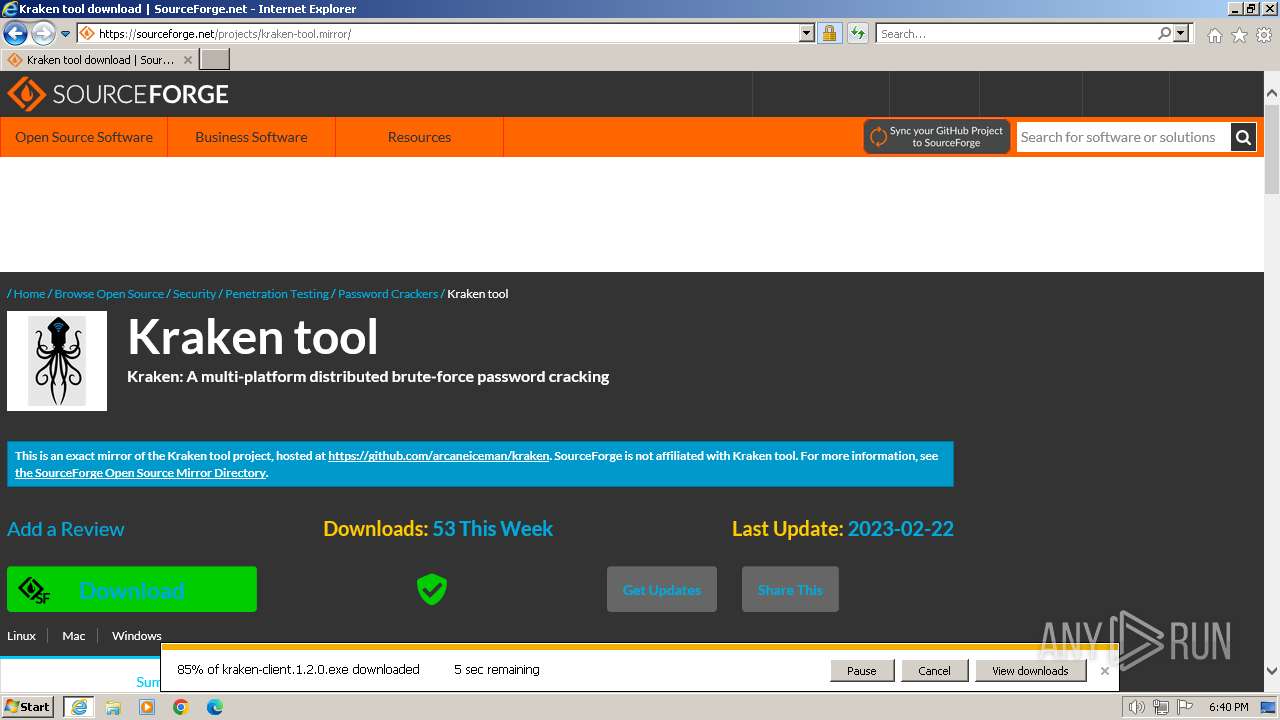
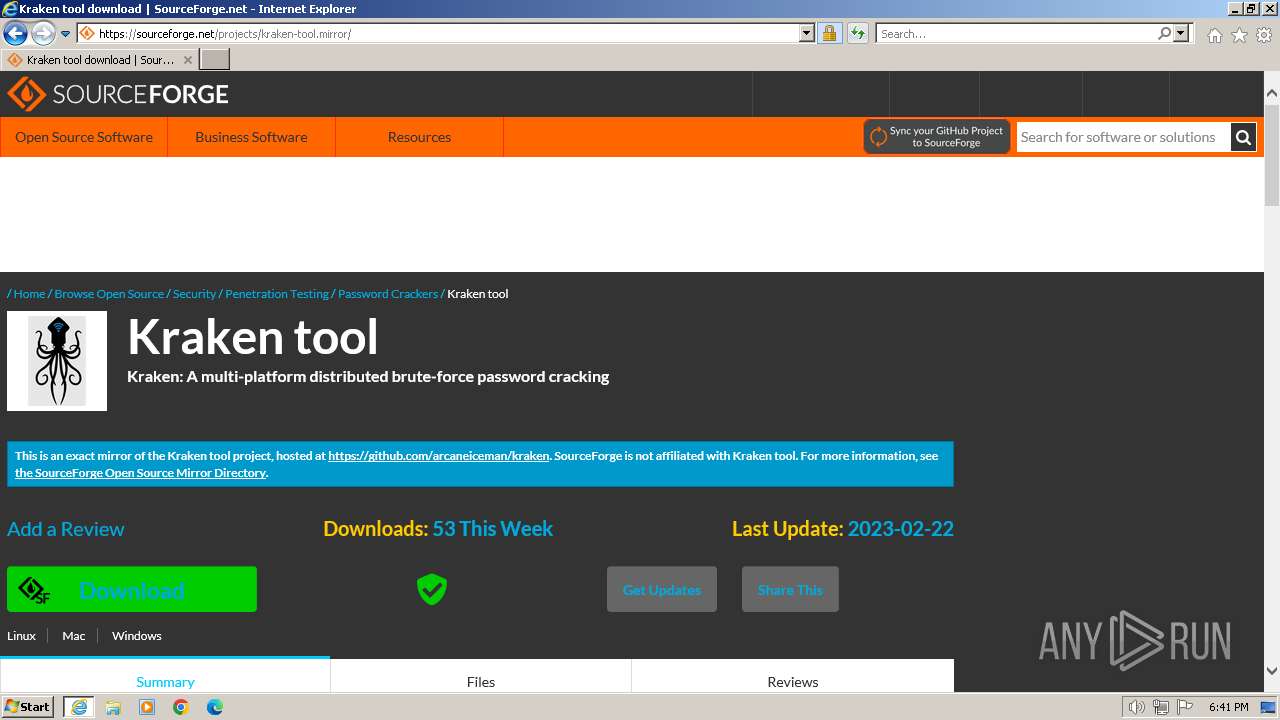
| URL: | https://sourceforge.net/projects/kraken-tool.mirror/ |
| Full analysis: | https://app.any.run/tasks/96378f91-735e-4eb8-8040-b06c01eedd36 |
| Verdict: | Malicious activity |
| Threats: | Kraken is a trojan malware with infostealing capabilities that was first spotted in May of 2023. The malware can perform a wide range of malicious activities, including logging users’ keystrokes. The data then can be sent to the attacker using several protocols. The operators behind the Kraken stealer usually distribute it via phishing emails. |
| Analysis date: | January 14, 2024, 18:39:16 |
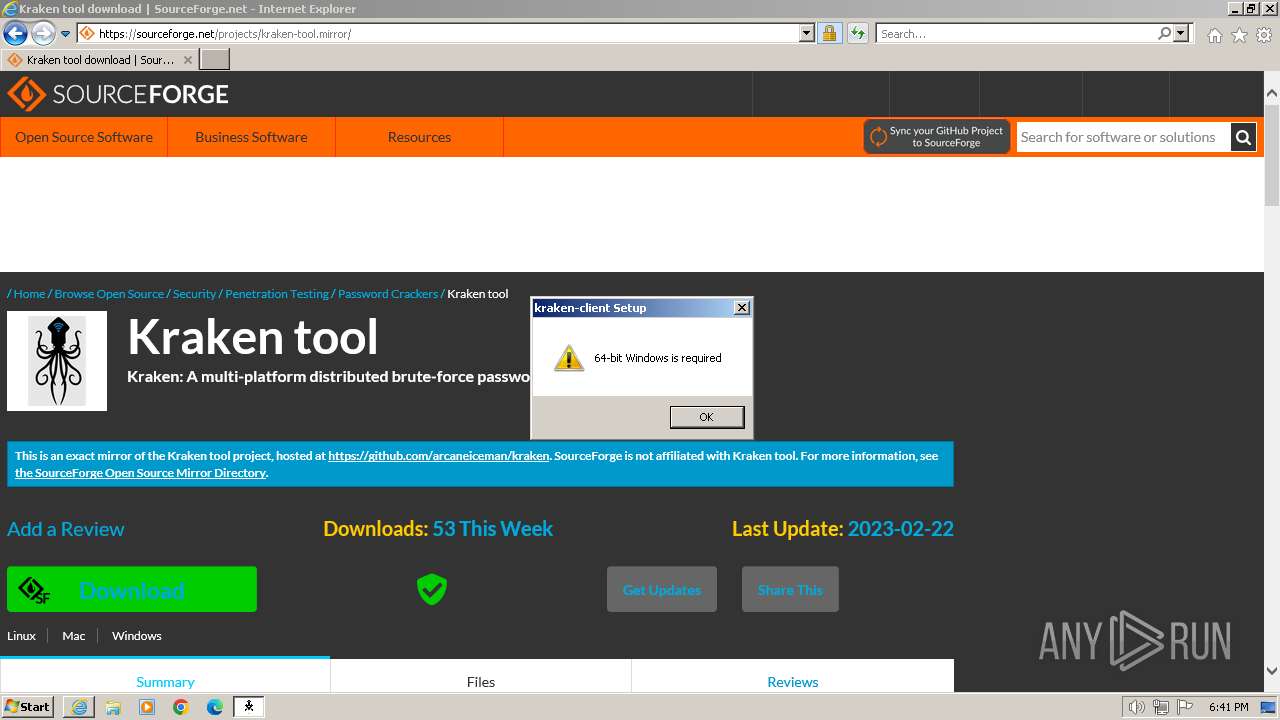
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1029B1000482D30E061311CFA7B3B130 |
| SHA1: | 3222441409F88C7888313FB90535DAD2184CDA04 |
| SHA256: | 975DBA3D34E7475844785DD19E7C5F380BC31E983F81651E551224ED7277D629 |
| SSDEEP: | 3:N8HCGSuLAuUtjLswXK:2iGnCtjLsp |
MALICIOUS
Kraken Ransomware is detected
- iexplore.exe (PID: 2204)
- iexplore.exe (PID: 116)
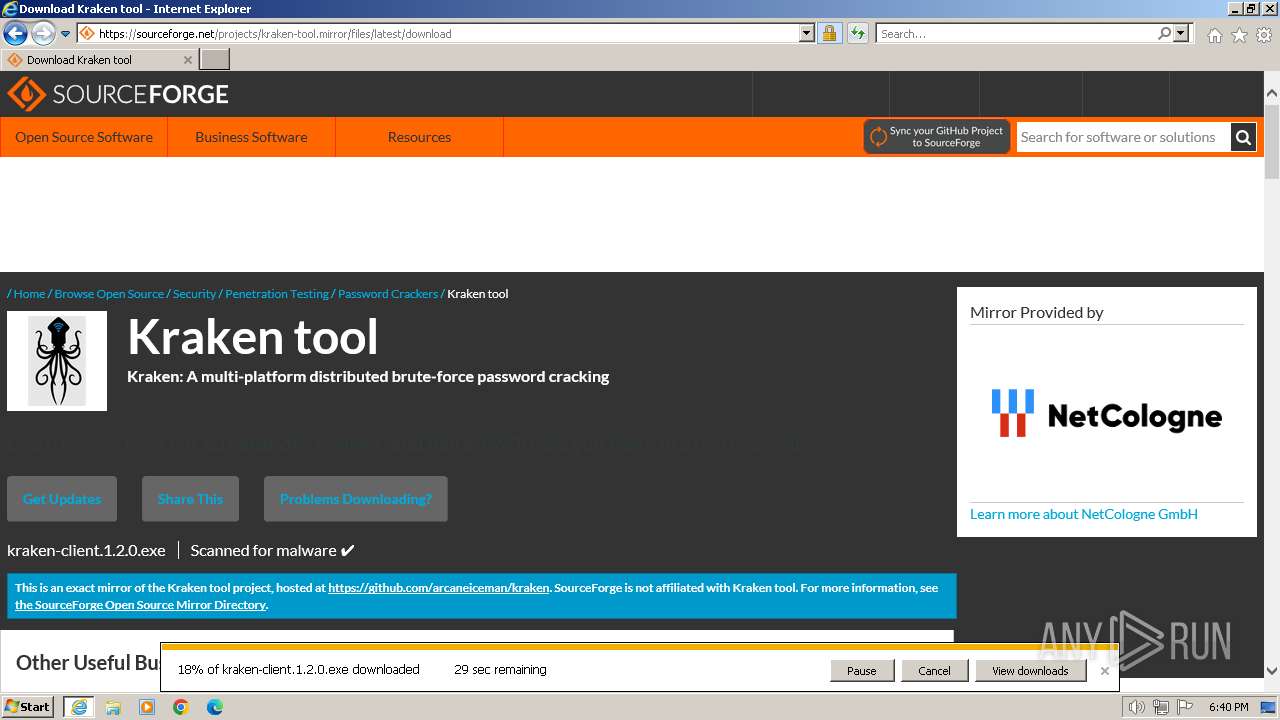
Drops the executable file immediately after the start
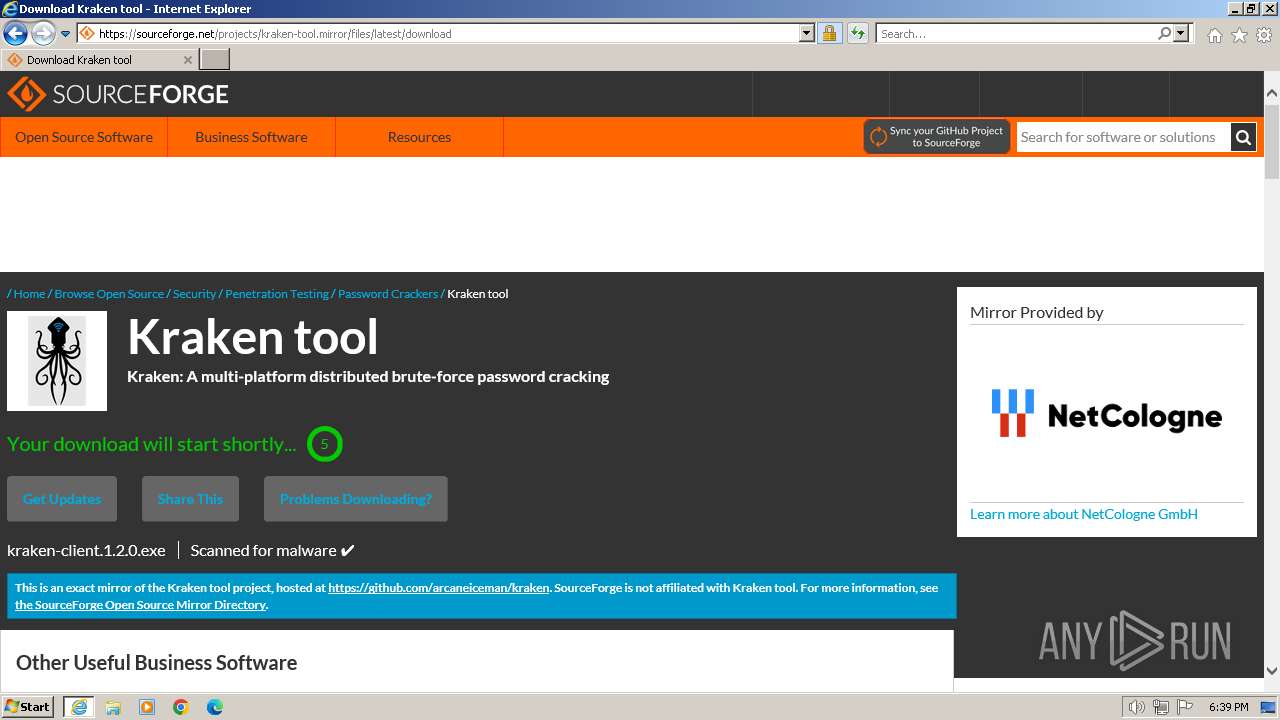
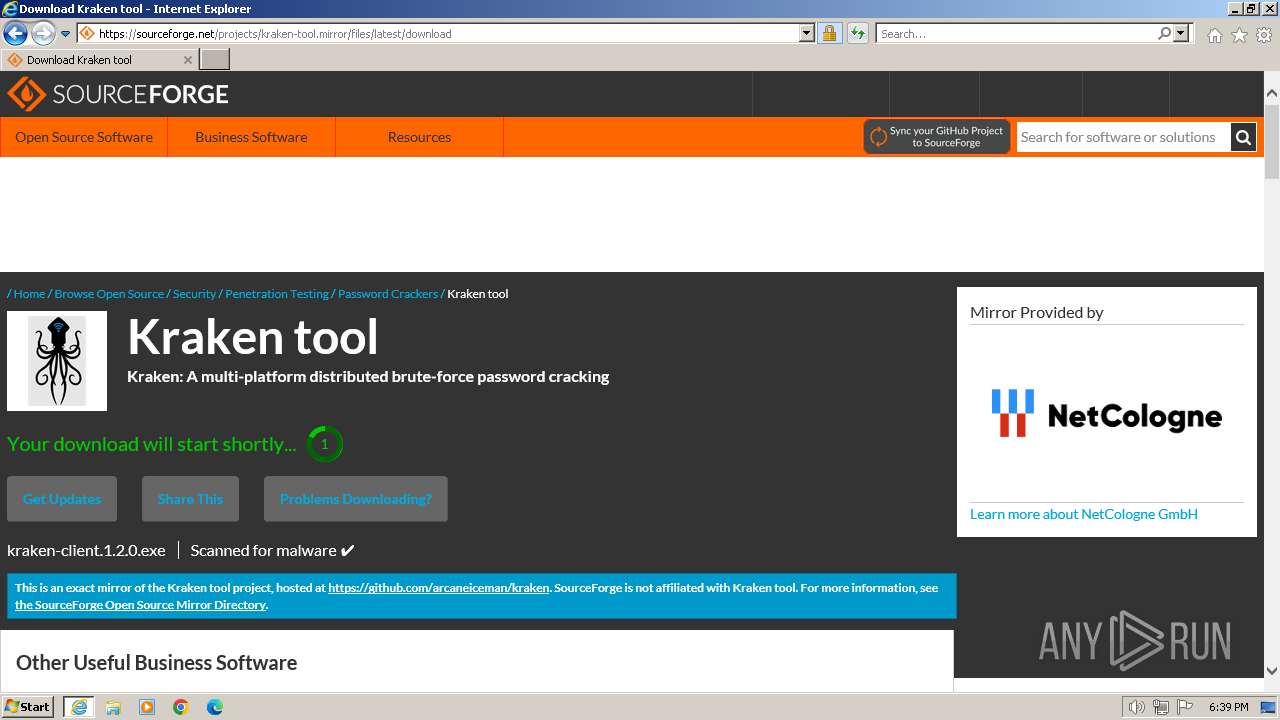
- kraken-client.1.2.0.exe (PID: 2440)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- kraken-client.1.2.0.exe (PID: 2440)
The process creates files with name similar to system file names
- kraken-client.1.2.0.exe (PID: 2440)
Executable content was dropped or overwritten
- kraken-client.1.2.0.exe (PID: 2440)
INFO
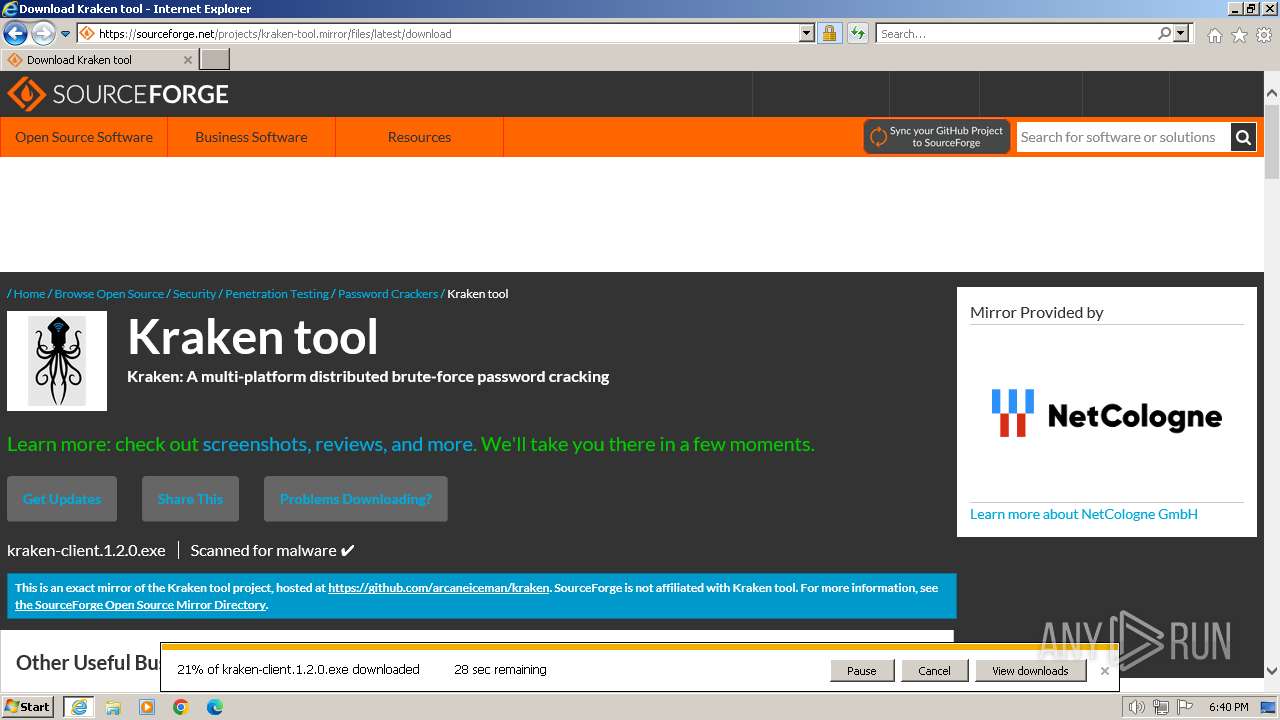
Application launched itself
- iexplore.exe (PID: 116)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2204)
Create files in a temporary directory
- kraken-client.1.2.0.exe (PID: 2440)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2204)
Reads the computer name
- kraken-client.1.2.0.exe (PID: 2440)
Checks supported languages
- kraken-client.1.2.0.exe (PID: 2440)
The process uses the downloaded file
- iexplore.exe (PID: 116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://sourceforge.net/projects/kraken-tool.mirror/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:116 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\kraken-client.1.2.0.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\kraken-client.1.2.0.exe | iexplore.exe | ||||||||||||
User: admin Company: arcaneiceman Integrity Level: MEDIUM Exit code: 2 Version: 1.2.0 Modules
| |||||||||||||||
Total events
19 693
Read events
19 586
Write events
105
Delete events
2
Modification events
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
41
Text files
122
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\cmp[1].css | text | |
MD5:38C8ACF2B4EF7DEF65BACFB6E9A26E8E | SHA256:4BAAE150A27BC5716BA8F5160FBD2414F5B731C470D8EE0956612DAFA106E950 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:AA83DEB686032C5C7B5743DDD6C05744 | SHA256:9A24DC7D80FCC90C0DB37EEA76219E90C09AF0650717874D101280ECA2BE226A | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\sf.sandiego-cmp-top[1].js | html | |
MD5:C3C9DA61F2361CC9A5CC5FB102565F53 | SHA256:1D48F195B9979C2845D7E803A67DD5ADD33B7CF136770ECE36C9F78EEAA593D3 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\sf.sandiego-head[1].js | text | |
MD5:D05F98B211F1AC879F9378468F3D6649 | SHA256:981BB3EEE156C83AFDED72FAD8F7CD5ECCE65B769E1FA842AC9E356CBA4530D9 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\sf.sandiego-foundation-base[1].js | text | |
MD5:F23FBD469BB0D9569486B62E2C50D996 | SHA256:D30C030593AEE31E4BDD1A458E6739DF804F6D50012D2E3141D585B4ACF91A08 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\owl.carousel.min[1].js | text | |
MD5:B7B9C97CD68EC336D01A79D5BE48C58D | SHA256:B394D33B2A7EC654A6B037EBFDA6618341B3F897A362BE624C923C2711B54A43 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\kraken-tool[1].htm | html | |
MD5:8804E15CD48A516FDA8E9972307DAA72 | SHA256:A83788C841E6D18A2D91150D04CF674C112BC2F89DD5E96C1E86BCC18FA9F882 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\lato[1].css | text | |
MD5:8F61F228AD51184B5F8BBBF14B436DF9 | SHA256:DA04907546EDDC4640039BB9EFBBB483D220B1E4EC553F9830A9510B7FF14899 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\sf-logo-full[1].svg | image | |
MD5:535DE5A927A8EB5A004CDC0A6B6320DD | SHA256:1744FB413B91B276F5E17347382B664D6CA6C4EA4DB69825CAA97C16DD5D37C3 | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\adsbanner[1].js | text | |
MD5:1A9F5B5D41007226049E6EF054C9F935 | SHA256:E3E69CC01AD15179EB67E1F90E1774ED5A5DA075F85420A1D9B01029B28B14DC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
68
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2204 | iexplore.exe | GET | 200 | 2.19.126.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?16e53a13f7f2d96f | unknown | compressed | 4.66 Kb | unknown |
2204 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
2204 | iexplore.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2204 | iexplore.exe | GET | 200 | 2.19.126.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7a9d8baceff24343 | unknown | compressed | 4.66 Kb | unknown |
2204 | iexplore.exe | GET | 200 | 2.19.126.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?616966124ddd90da | unknown | compressed | 65.2 Kb | unknown |
116 | iexplore.exe | GET | 304 | 2.19.126.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?67308e0939100114 | unknown | — | — | unknown |
2204 | iexplore.exe | GET | 200 | 2.16.241.15:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgR%2B5rJNDRLPmf6wKNriwkmuQQ%3D%3D | unknown | binary | 503 b | unknown |
2204 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
116 | iexplore.exe | GET | 304 | 2.19.126.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?85105a2067e5fff2 | unknown | — | — | unknown |
116 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 314 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2204 | iexplore.exe | 104.18.37.111:443 | sourceforge.net | CLOUDFLARENET | — | unknown |
2204 | iexplore.exe | 2.19.126.163:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2204 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2204 | iexplore.exe | 172.64.147.47:443 | a.fsdn.com | CLOUDFLARENET | US | unknown |
2204 | iexplore.exe | 104.16.57.101:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | unknown |
2204 | iexplore.exe | 87.230.98.76:443 | d.delivery.consentmanager.net | PlusServer GmbH | DE | unknown |
2204 | iexplore.exe | 212.102.56.178:443 | cdn.consentmanager.net | Datacamp Limited | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sourceforge.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
a.fsdn.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
d.delivery.consentmanager.net |
| unknown |
cdn.consentmanager.net |
| malicious |
x1.c.lencr.org |
| whitelisted |
c.sf-syn.com |
| whitelisted |
r3.o.lencr.org |
| shared |