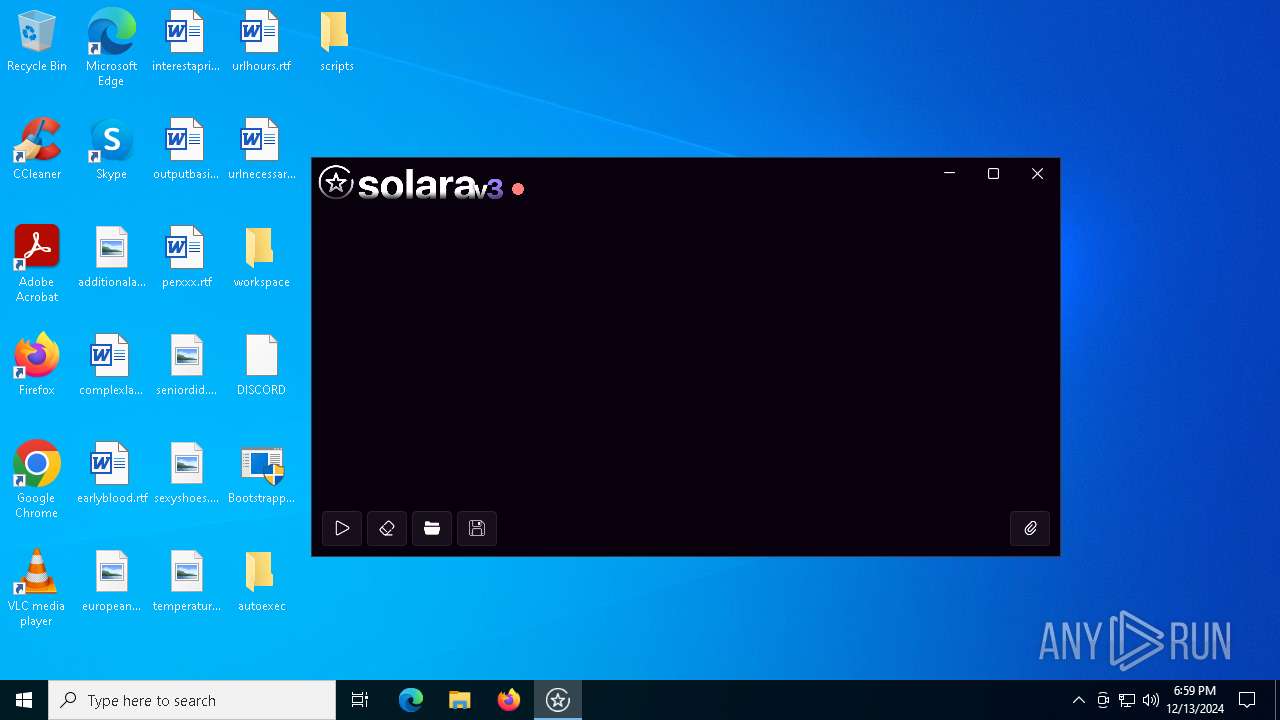
| File name: | Bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/f4deae21-bfaa-4f5c-826e-530a64a4ab1e |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 18:56:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 90FD25CED85FE6DB28D21AE7D1F02E2C |
| SHA1: | E27EFF4CD4D383F5C564CCE2BD1AAA2FFE4EC056 |
| SHA256: | 97572BD57B08B59744E4DFE6F93FB96BE4002DFE1AA78683771725401776464F |
| SSDEEP: | 24576:Ht8qGeSWotksh8mzb2oKmiQQJ17JZ8g5LYMFI+PigLAeyzUqUUUUUUUUUL8m:uWotkshXoQQJ17JZ8g5LYMVAeyM |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- Bootstrapper.exe (PID: 6772)
- BootstrapperV1.23.exe (PID: 6344)
Reads security settings of Internet Explorer
- Bootstrapper.exe (PID: 6772)
- BootstrapperV1.23.exe (PID: 6344)
- msiexec.exe (PID: 7132)
- msiexec.exe (PID: 6792)
Reads the date of Windows installation
- Bootstrapper.exe (PID: 6772)
- BootstrapperV1.23.exe (PID: 6344)
Starts CMD.EXE for commands execution
- BootstrapperV1.23.exe (PID: 6344)
- BootstrapperV1.23.exe (PID: 6868)
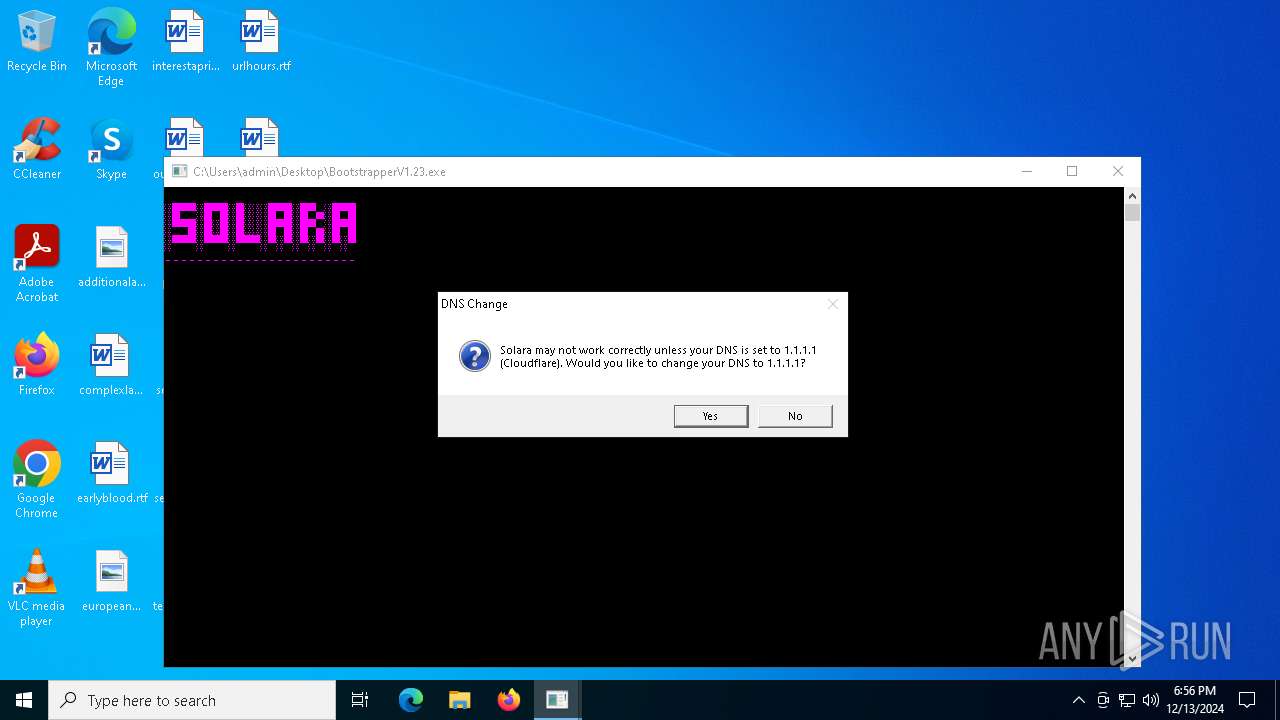
Uses WMIC.EXE to obtain information about the network interface controller
- cmd.exe (PID: 6184)
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 6472)
- cmd.exe (PID: 4972)
Checks Windows Trust Settings
- msiexec.exe (PID: 4392)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4392)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- msiexec.exe (PID: 7132)
- wevtutil.exe (PID: 7076)
The process drops C-runtime libraries
- BootstrapperV1.23.exe (PID: 6344)
Process drops legitimate windows executable
- BootstrapperV1.23.exe (PID: 6344)
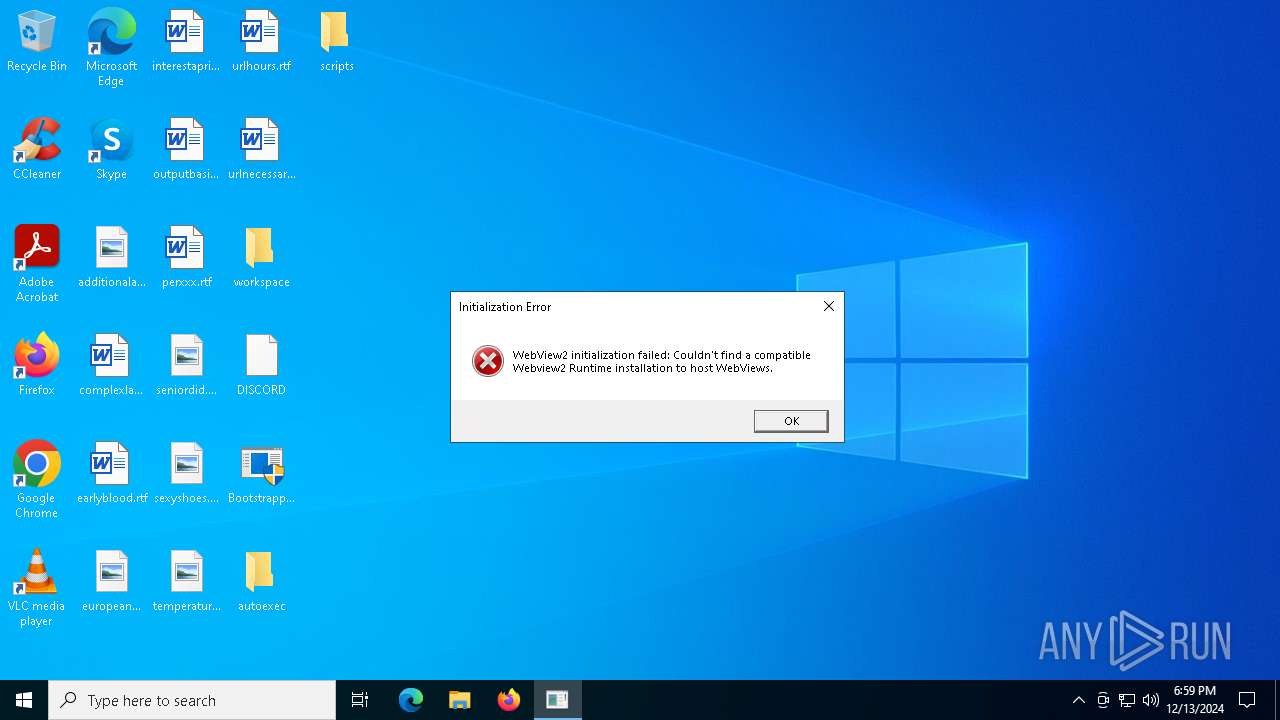
Executes application which crashes
- Solara.exe (PID: 2136)
Executes script using NodeJS
- node.exe (PID: 236)
Reads the BIOS version
- Solara.exe (PID: 6836)
INFO
Reads the computer name
- Bootstrapper.exe (PID: 6772)
- BootstrapperV1.23.exe (PID: 6344)
- msiexec.exe (PID: 4392)
- msiexec.exe (PID: 1792)
- msiexec.exe (PID: 6792)
- msiexec.exe (PID: 7132)
- BootstrapperV1.23.exe (PID: 6868)
- Solara.exe (PID: 2136)
Checks supported languages
- Bootstrapper.exe (PID: 6772)
- BootstrapperV1.23.exe (PID: 6344)
- msiexec.exe (PID: 1792)
- msiexec.exe (PID: 6792)
- msiexec.exe (PID: 7132)
- Solara.exe (PID: 2136)
- msiexec.exe (PID: 4392)
- BootstrapperV1.23.exe (PID: 6868)
- node.exe (PID: 5980)
- Solara.exe (PID: 6836)
Disables trace logs
- Bootstrapper.exe (PID: 6772)
- BootstrapperV1.23.exe (PID: 6344)
- BootstrapperV1.23.exe (PID: 6868)
- Solara.exe (PID: 2136)
- Solara.exe (PID: 6836)
Checks proxy server information
- Bootstrapper.exe (PID: 6772)
- BootstrapperV1.23.exe (PID: 6344)
- WerFault.exe (PID: 5964)
- Solara.exe (PID: 2136)
Reads Environment values
- Bootstrapper.exe (PID: 6772)
- BootstrapperV1.23.exe (PID: 6344)
- BootstrapperV1.23.exe (PID: 6868)
- Solara.exe (PID: 2136)
- Solara.exe (PID: 6836)
Reads the machine GUID from the registry
- Bootstrapper.exe (PID: 6772)
- BootstrapperV1.23.exe (PID: 6344)
- msiexec.exe (PID: 4392)
- Solara.exe (PID: 2136)
- BootstrapperV1.23.exe (PID: 6868)
- Solara.exe (PID: 6836)
Process checks computer location settings
- Bootstrapper.exe (PID: 6772)
- BootstrapperV1.23.exe (PID: 6344)
Reads the software policy settings
- Bootstrapper.exe (PID: 6772)
- msiexec.exe (PID: 4392)
- BootstrapperV1.23.exe (PID: 6344)
- Solara.exe (PID: 2136)
- WerFault.exe (PID: 5964)
- BootstrapperV1.23.exe (PID: 6868)
- Solara.exe (PID: 6836)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2132)
Create files in a temporary directory
- BootstrapperV1.23.exe (PID: 6344)
Creates files or folders in the user directory
- msiexec.exe (PID: 4392)
- WerFault.exe (PID: 5964)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4392)
Application launched itself
- msiexec.exe (PID: 4392)
The sample compiled with english language support
- BootstrapperV1.23.exe (PID: 6344)
Creates a software uninstall entry
- msiexec.exe (PID: 4392)
Creates files in the program directory
- BootstrapperV1.23.exe (PID: 6344)
The process uses the downloaded file
- BootstrapperV1.23.exe (PID: 6344)
Manual execution by a user
- BootstrapperV1.23.exe (PID: 6868)
- BootstrapperV1.23.exe (PID: 1796)
Process checks whether UAC notifications are on
- Solara.exe (PID: 6836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:09:09 21:53:37+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 8 |
| CodeSize: | 993280 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf4672 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
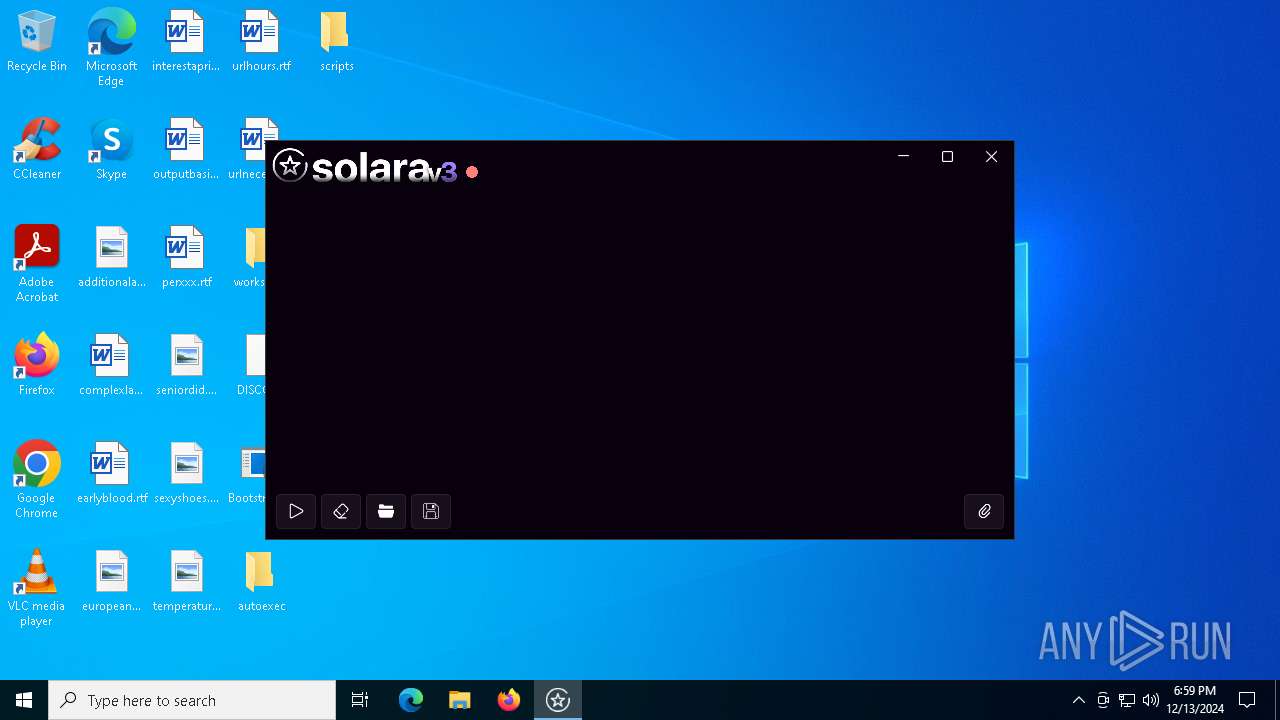
| FileDescription: | SolaraBootstrapper |
| FileVersion: | 1.0.0.0 |
| InternalName: | SolaraBootstrapper.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | SolaraBootstrapper.exe |
| ProductName: | SolaraBootstrapper |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
164
Monitored processes
33
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "node" "C:\ProgramData\Solara\Monaco\fileaccess\index.js" f3305e6c45bf46a7 | C:\Program Files\nodejs\node.exe | — | Solara.exe | |||||||||||
User: admin Company: Node.js Integrity Level: HIGH Description: Node.js JavaScript Runtime Version: 18.16.0 Modules
| |||||||||||||||
| 1612 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1792 | C:\Windows\System32\MsiExec.exe -Embedding 15214D523C6EE38C8595DA076DE5D4CE | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1796 | "C:\Users\admin\Desktop\BootstrapperV1.23.exe" | C:\Users\admin\Desktop\BootstrapperV1.23.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SolaraBootstrapper Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2132 | wmic nicconfig where (IPEnabled=TRUE) call SetDNSServerSearchOrder ("1.1.1.1", "1.0.0.1") | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\ProgramData\Solara\Solara.exe" | C:\ProgramData\Solara\Solara.exe | BootstrapperV1.23.exe | ||||||||||||
User: admin Company: CMD Softworks Integrity Level: HIGH Description: Solara V3 Exit code: 3762504530 Version: 3.0.0.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3296 | "wevtutil.exe" im "C:\Program Files\nodejs\node_etw_provider.man" /fromwow64 | C:\Windows\System32\wevtutil.exe | — | wevtutil.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Eventing Command Line Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | node.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3836 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 556
Read events
21 568
Write events
2 977
Delete events
11
Modification events
| (PID) Process: | (6772) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6772) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6772) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6772) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6772) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6772) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6772) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6772) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6772) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6772) Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
36
Suspicious files
1 734
Text files
740
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6344 | BootstrapperV1.23.exe | C:\Users\admin\AppData\Local\Temp\node-v18.16.0-x64.msi | — | |
MD5:— | SHA256:— | |||
| 4392 | msiexec.exe | C:\Windows\Installer\13af8d.msi | — | |
MD5:— | SHA256:— | |||
| 4392 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\66AE3BFDF94A732B262342AD2154B86E_CEA48AEE703922244E2530F7A011BBC6 | binary | |
MD5:1F3D166894AD4383B7F28014EB37FAF1 | SHA256:F62AD71CC2452B4A0C3438E56E8F9C0AFF5A300259E0D399C36DF0B9CD447790 | |||
| 6772 | Bootstrapper.exe | C:\Users\admin\Desktop\DISCORD | binary | |
MD5:B016DAFCA051F817C6BA098C096CB450 | SHA256:B03C8C2D2429E9DBC7920113DEDF6FC09095AB39421EE0CC8819AD412E5D67B9 | |||
| 6772 | Bootstrapper.exe | C:\Users\admin\Desktop\BootstrapperV1.23.exe | executable | |
MD5:02C70D9D6696950C198DB93B7F6A835E | SHA256:8F2E28588F2303BD8D7A9B0C3FF6A9CB16FA93F8DDC9C5E0666A8C12D6880EE3 | |||
| 4392 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\42B9A473B4DAF01285A36B4D3C7B1662_178C086B699FD6C56B804AF3EF759CB5 | binary | |
MD5:AA41B7ED540384249602712F0EE5950F | SHA256:B4559D297F4FCC2D1ED92754F8EEA889A58644856803EB5C63315C16F626C8CD | |||
| 4392 | msiexec.exe | C:\Windows\Installer\MSIBCB1.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 4392 | msiexec.exe | C:\Windows\Installer\MSIC704.tmp | executable | |
MD5:7A86CE1A899262DD3C1DF656BFF3FB2C | SHA256:B8F2D0909D7C2934285A8BE010D37C0609C7854A36562CBFCBCE547F4F4C7B0C | |||
| 4392 | msiexec.exe | C:\Windows\Installer\MSIBC71.tmp | executable | |
MD5:7A86CE1A899262DD3C1DF656BFF3FB2C | SHA256:B8F2D0909D7C2934285A8BE010D37C0609C7854A36562CBFCBCE547F4F4C7B0C | |||
| 4392 | msiexec.exe | C:\Windows\Installer\MSIB9B1.tmp | binary | |
MD5:E400C86B7D4588DFC2587DEEA10DAD05 | SHA256:3305F3AAD72429133DA49C9DA1D11DF50048EFCABFD8455E067C839DD6FB02B1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
61
DNS requests
32
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4392 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | unknown | — | — | whitelisted |
4392 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAOO2y%2FG5AVzGnYPFRYUTIU%3D | unknown | — | — | whitelisted |
6720 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6720 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5876 | SIHClient.exe | GET | 200 | 23.192.22.93:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5876 | SIHClient.exe | GET | 200 | 23.192.22.93:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
440 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.32.238.34:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.215.121.133:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.19.80.75:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6772 | Bootstrapper.exe | 172.67.203.125:443 | getsolara.dev | CLOUDFLARENET | US | malicious |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
getsolara.dev |
| malicious |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
pastebin.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2192 | svchost.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
6344 | BootstrapperV1.23.exe | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |