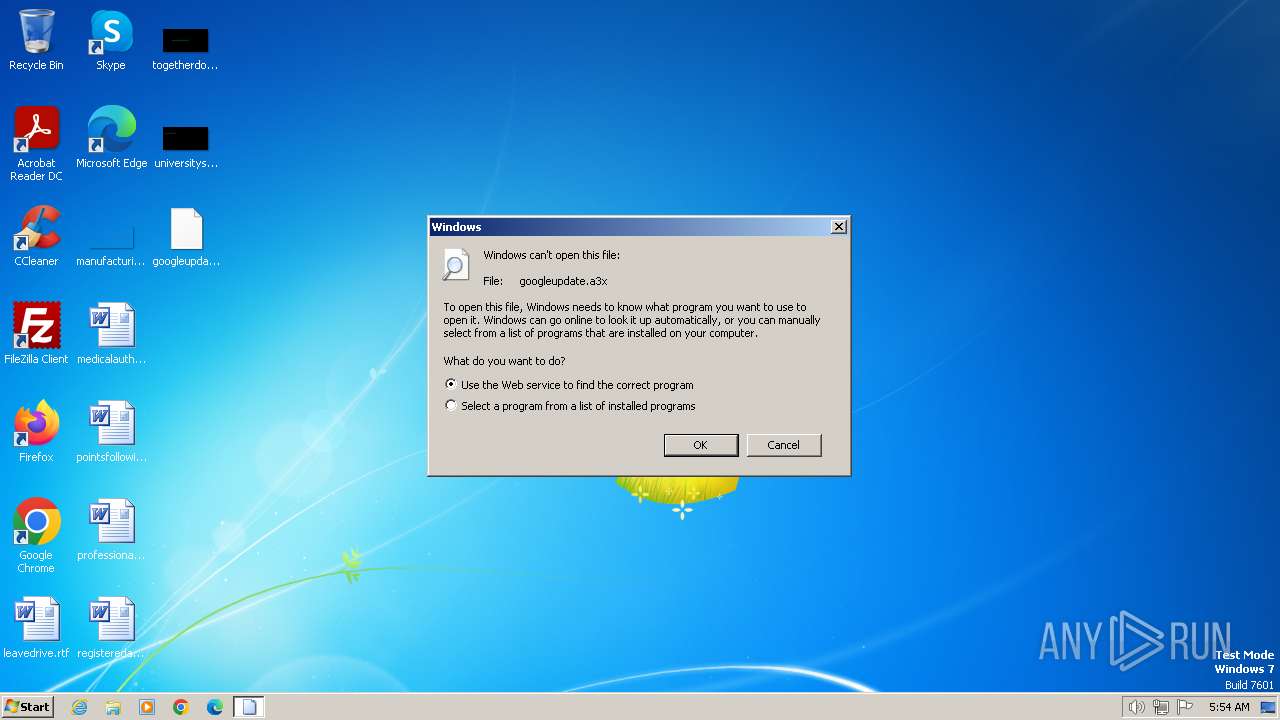
| File name: | googleupdate.a3x |
| Full analysis: | https://app.any.run/tasks/c8447179-305a-4808-8ede-040d94a5e8b4 |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2024, 04:54:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
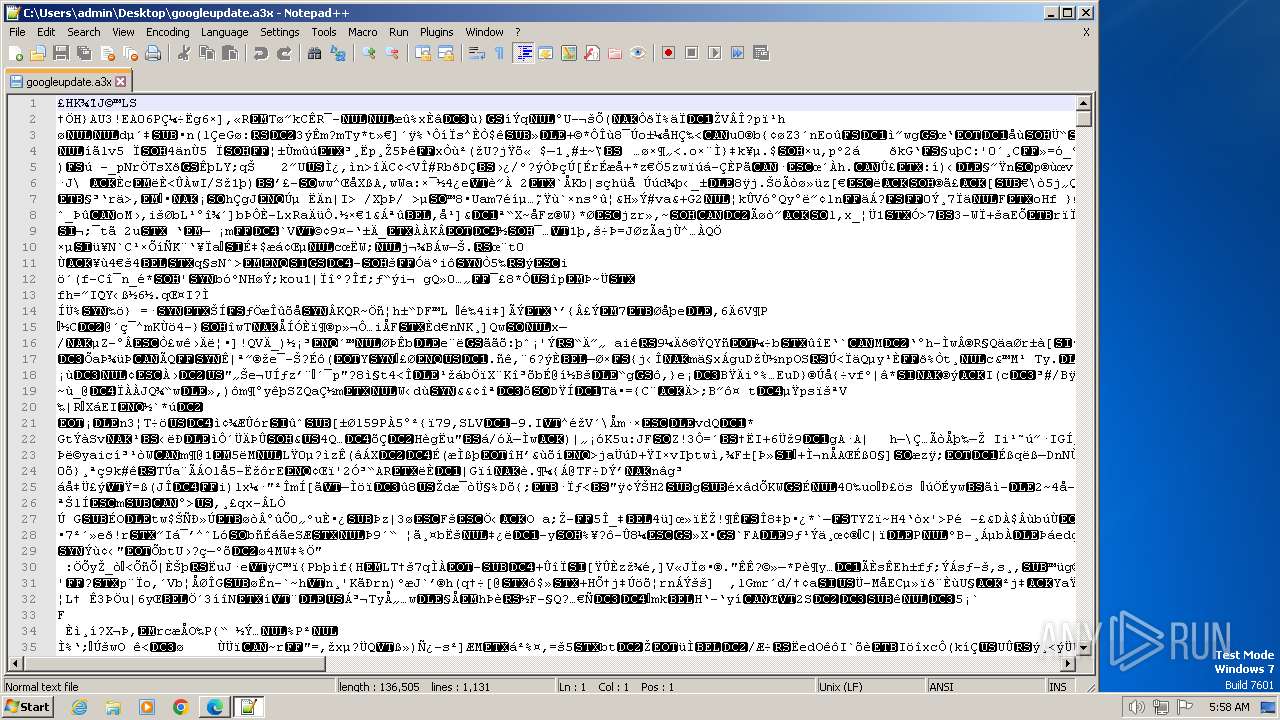
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 84A5746202DECEE74D907A37015A01D4 |
| SHA1: | 872B8D1F2269E645237BB8303EA96012482F9FC2 |
| SHA256: | 97549D52F601A27B336660E8D4983BA10504E371162C64B36077A7670CA0D032 |
| SSDEEP: | 3072:QuNSBBCTqhjAhnOazEDzyEXIq8+Uolv0xB3KsXus5TNjGJ:p0BBMuonOyE/MslvaJBtQ |
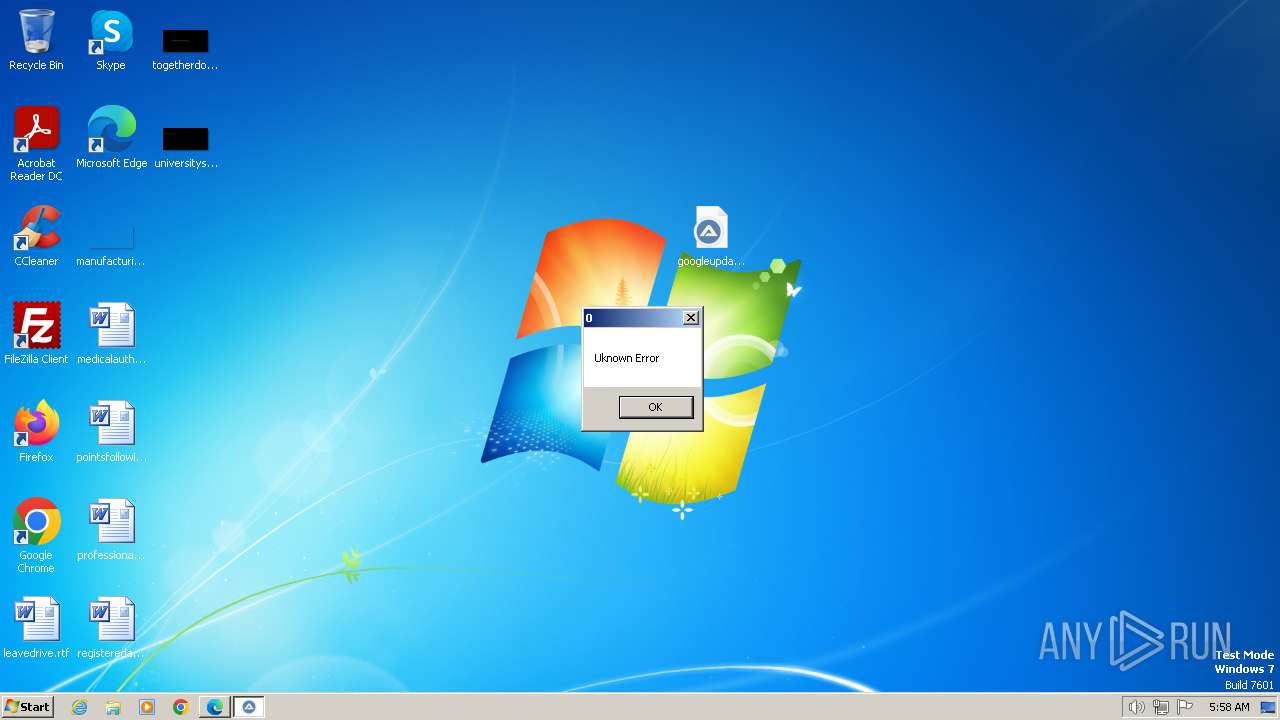
MALICIOUS
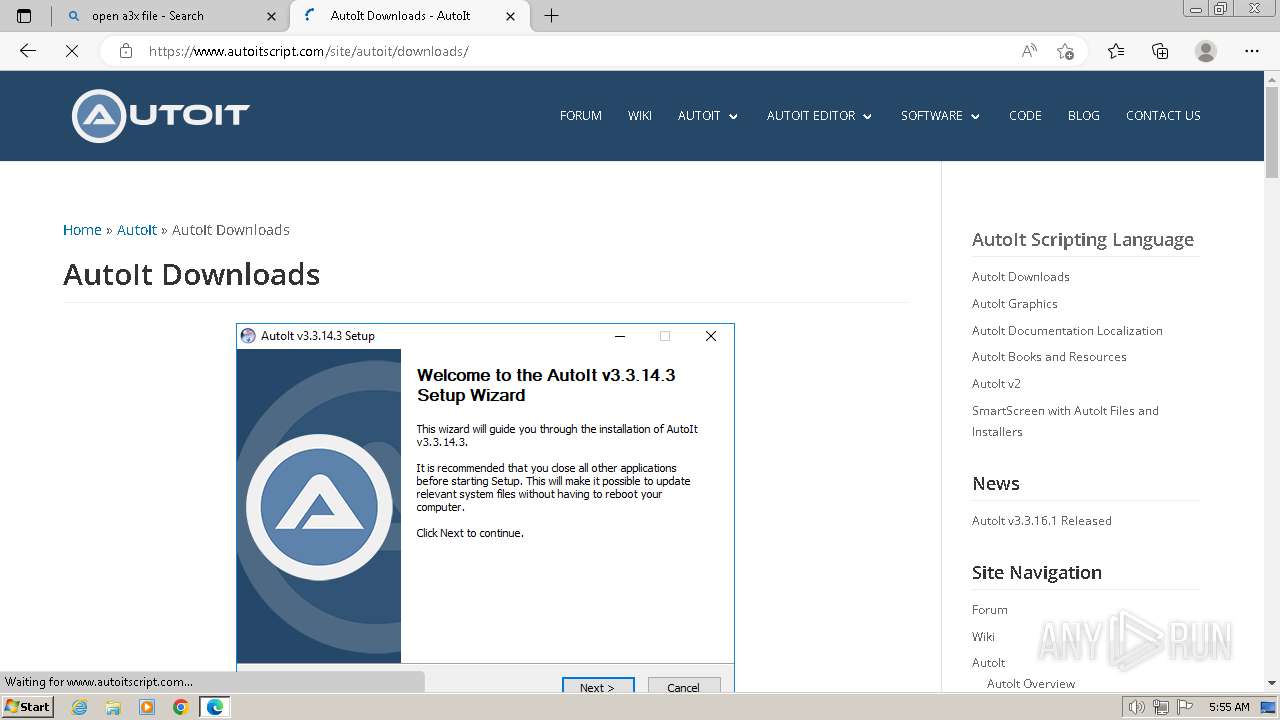
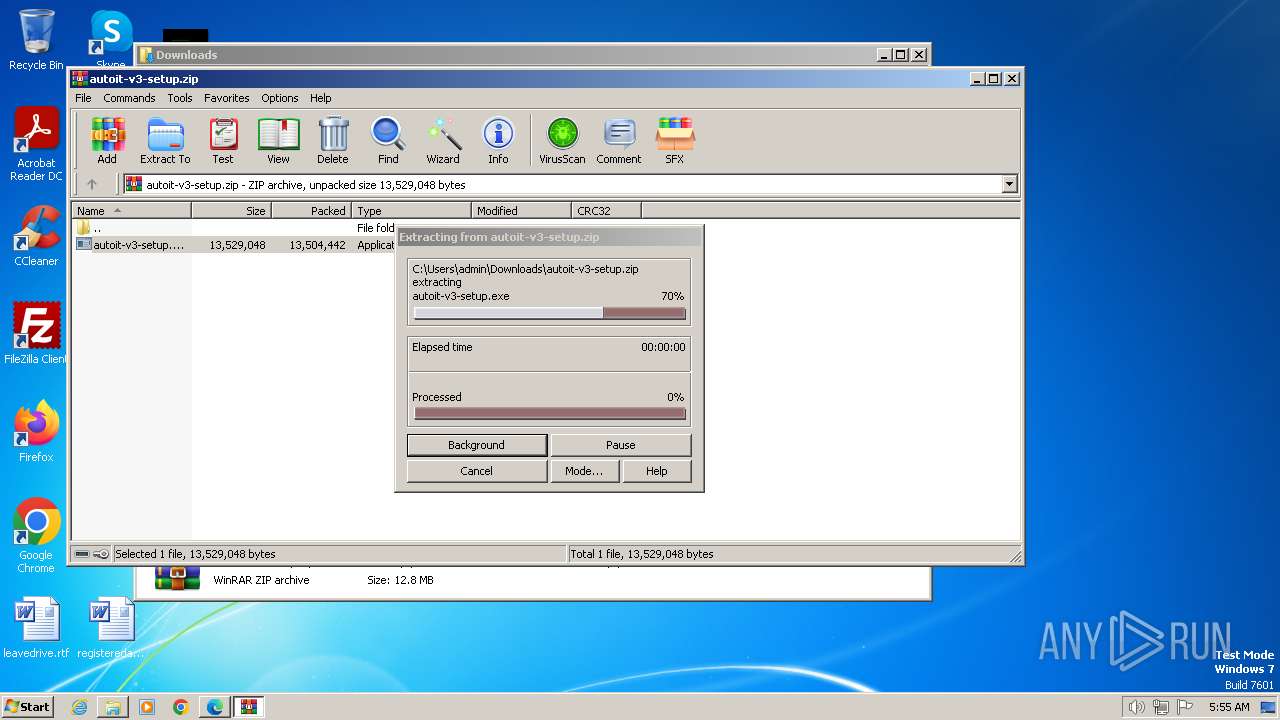
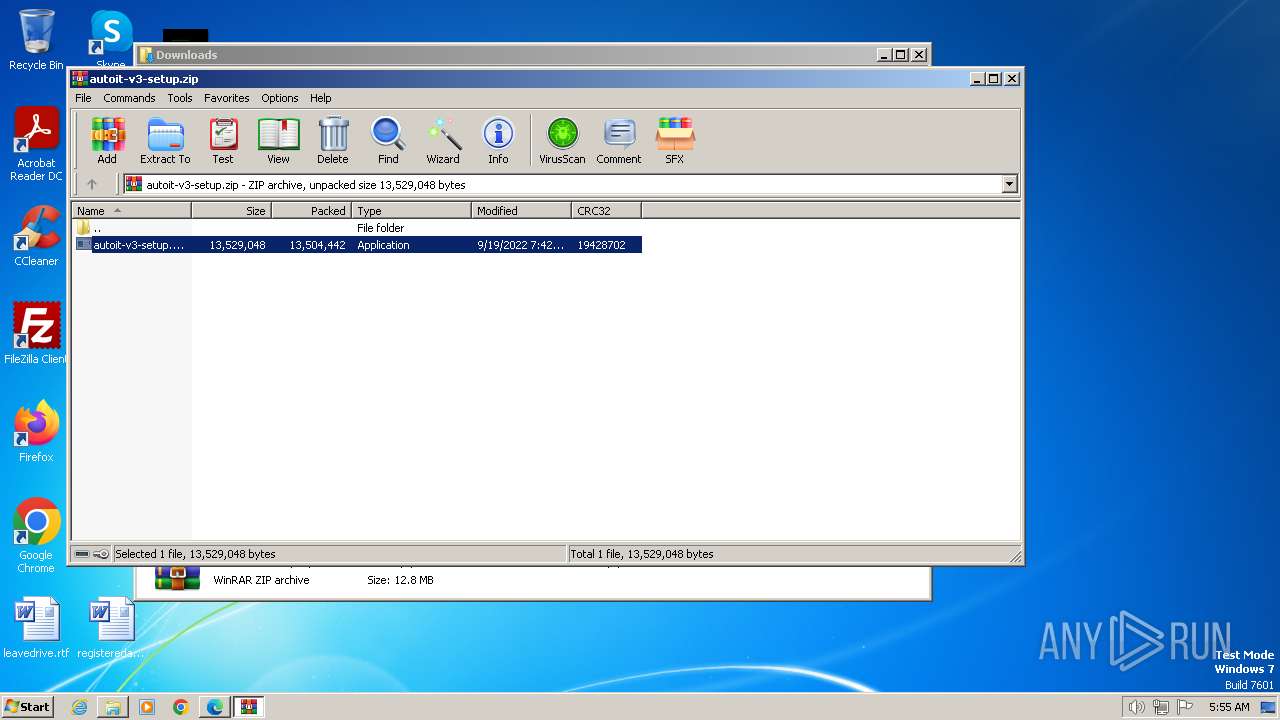
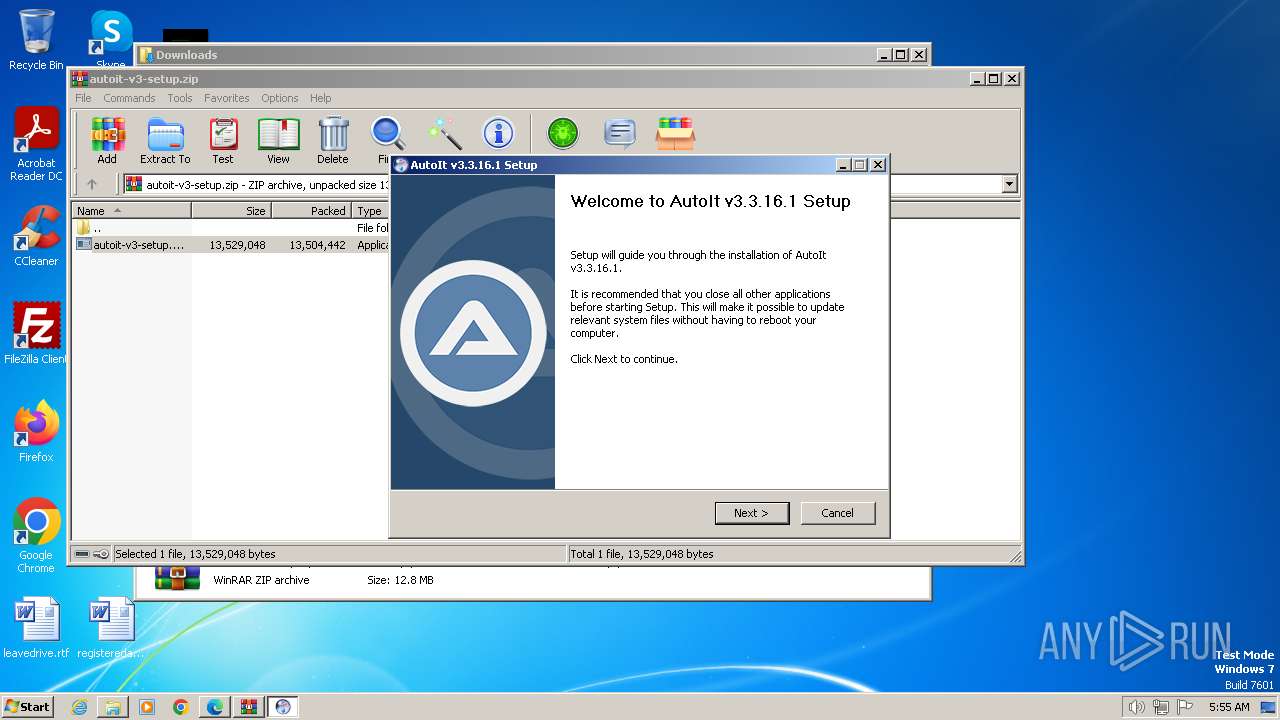
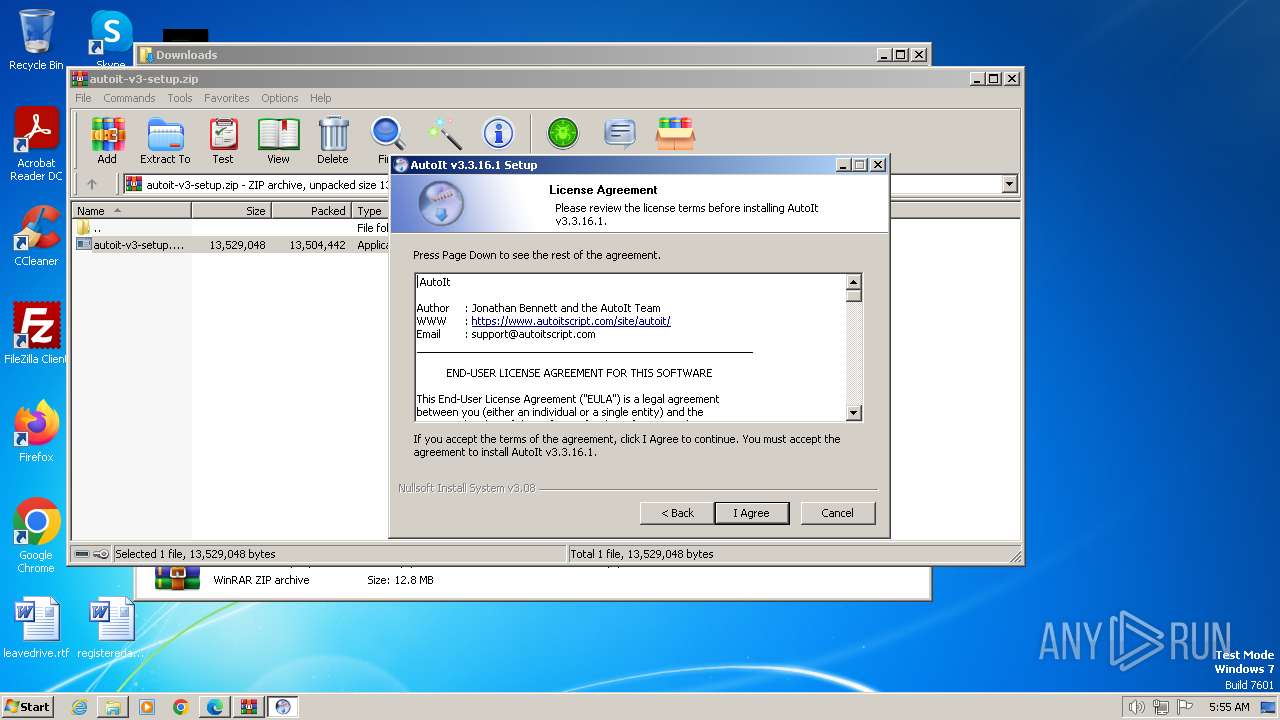
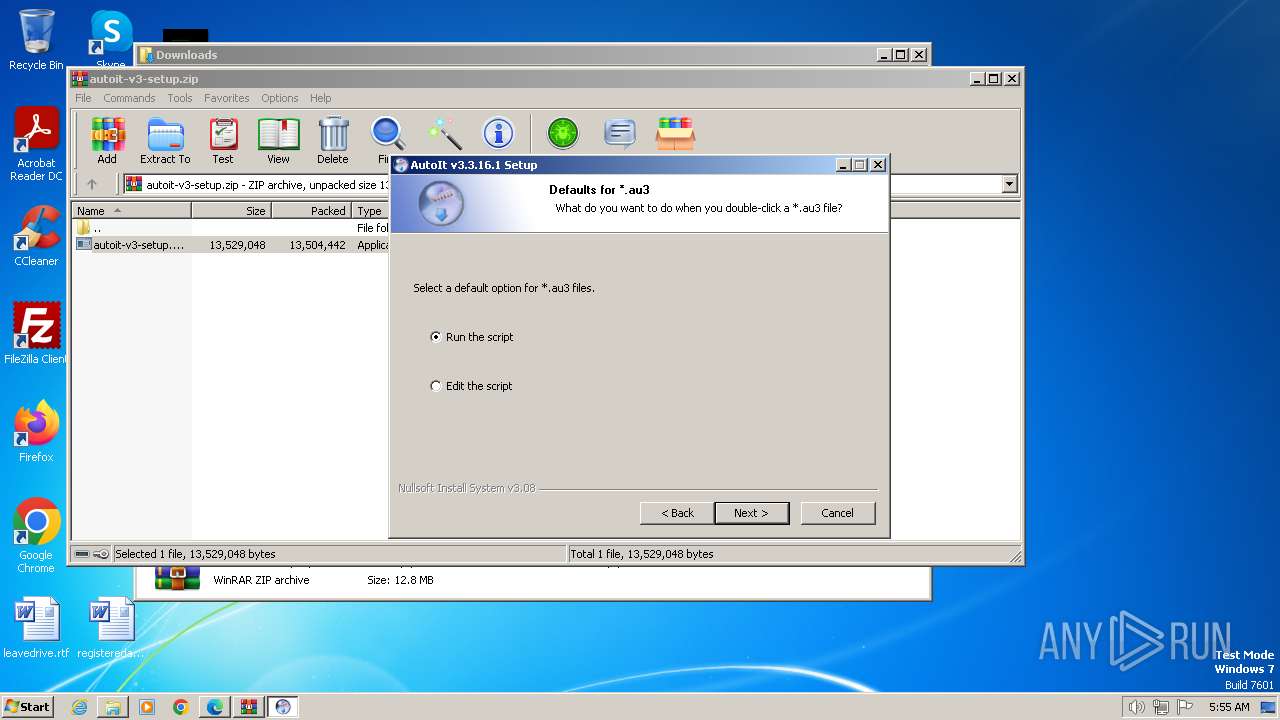
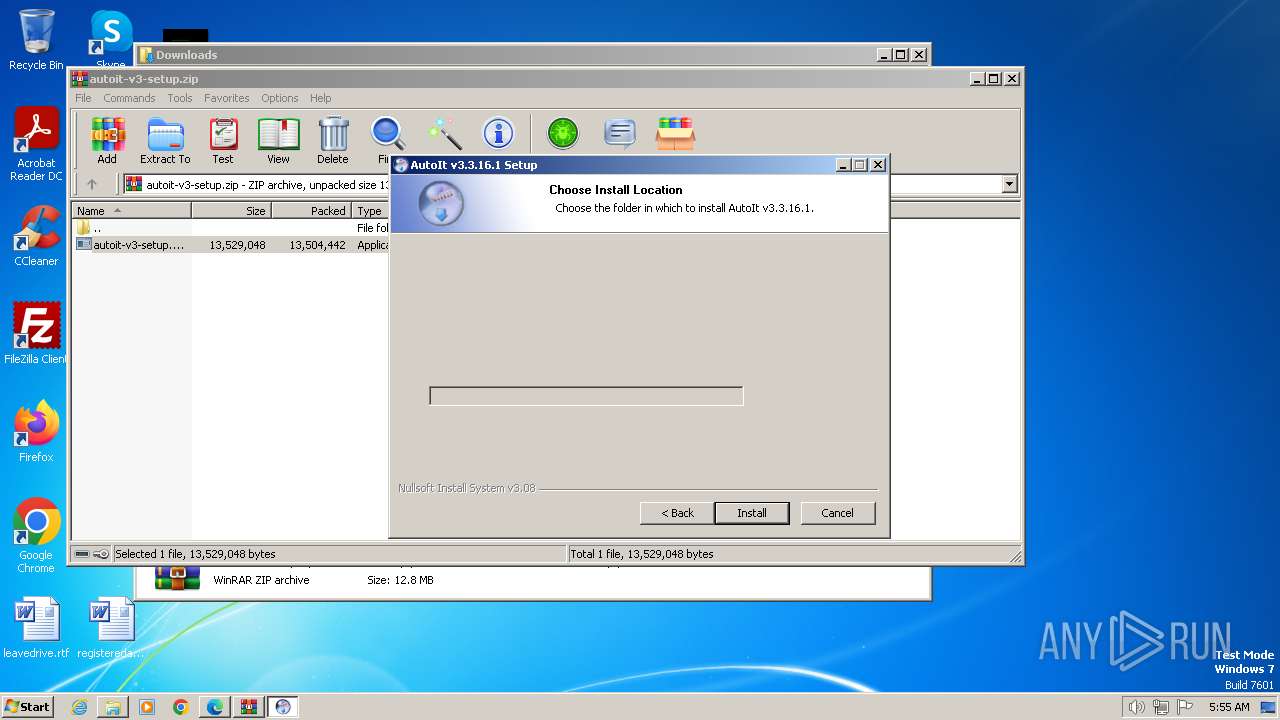
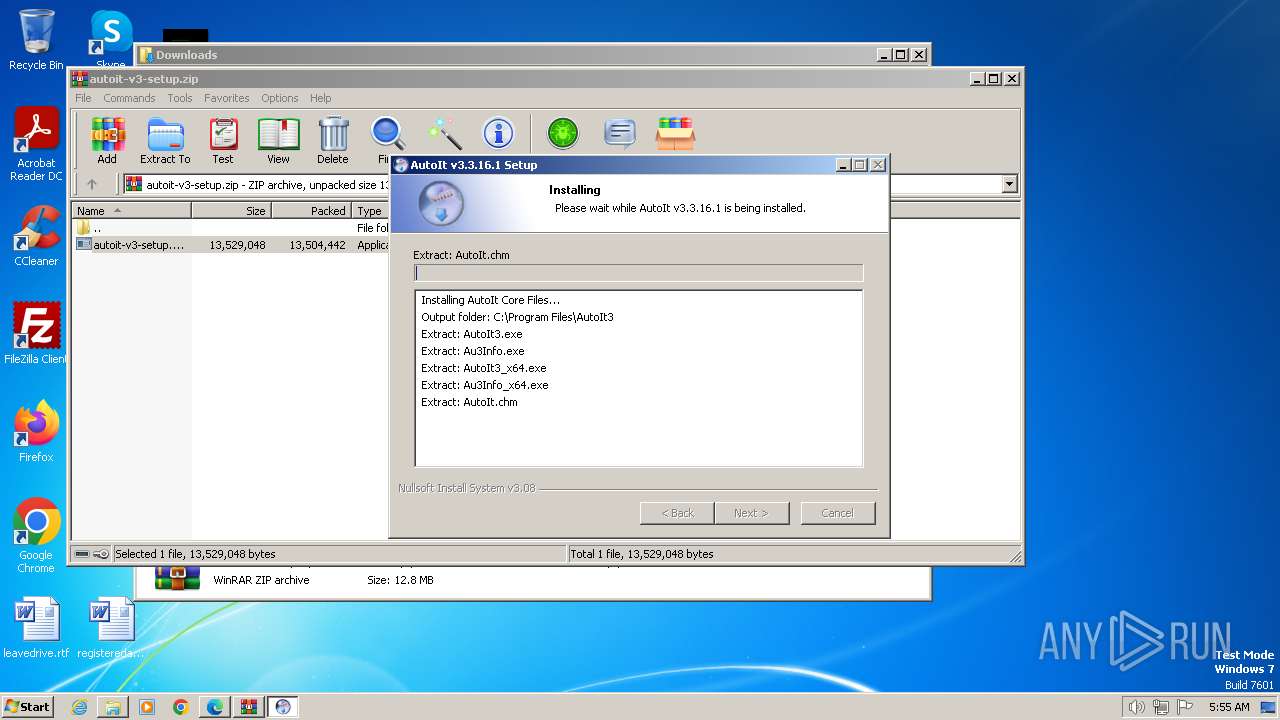
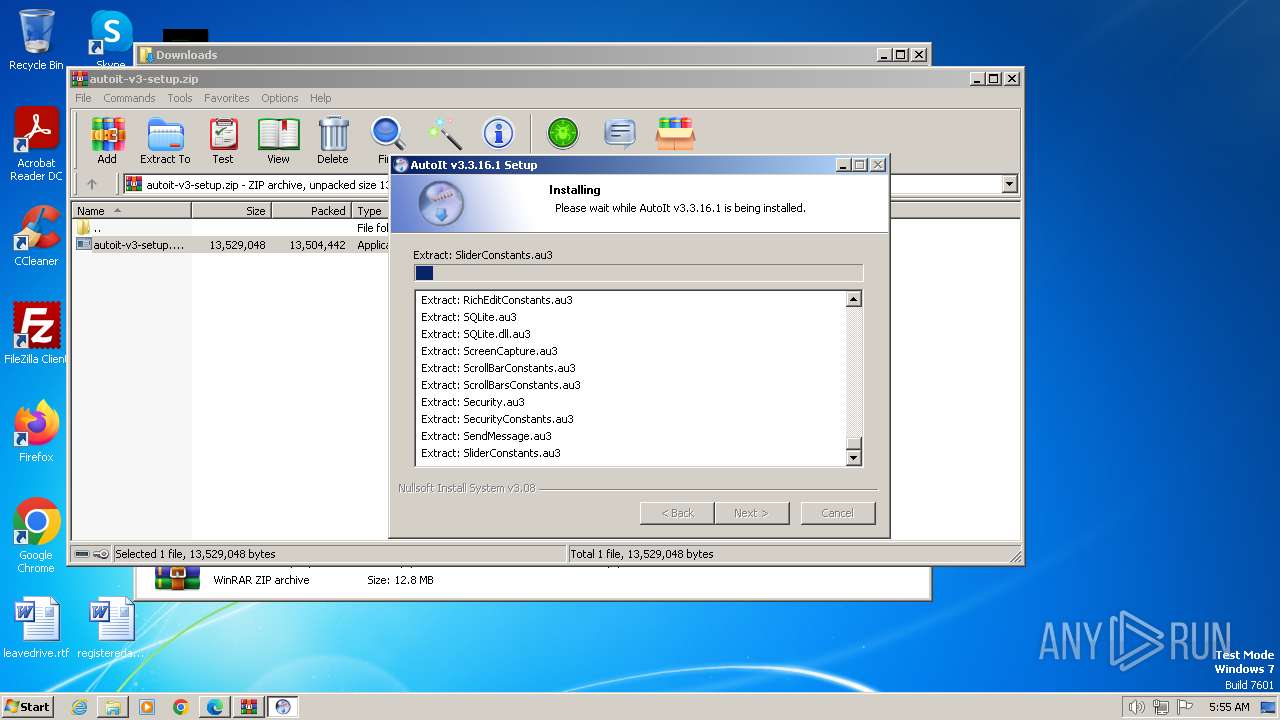
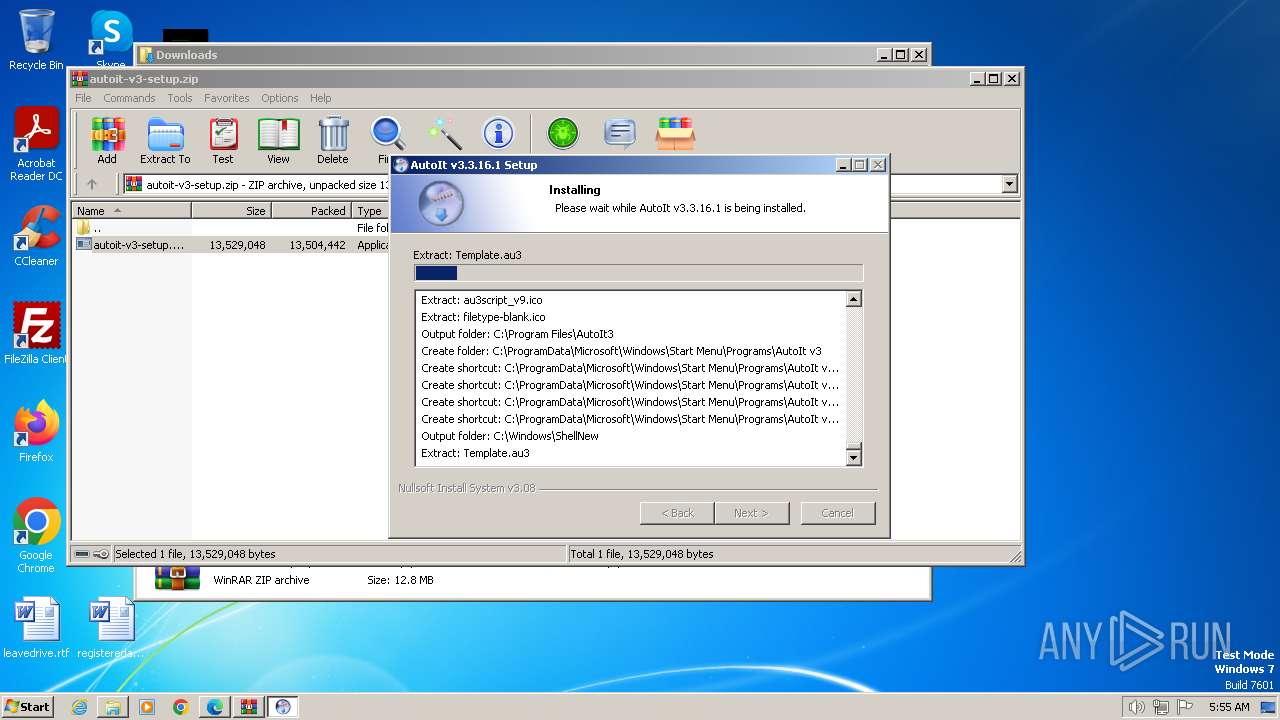
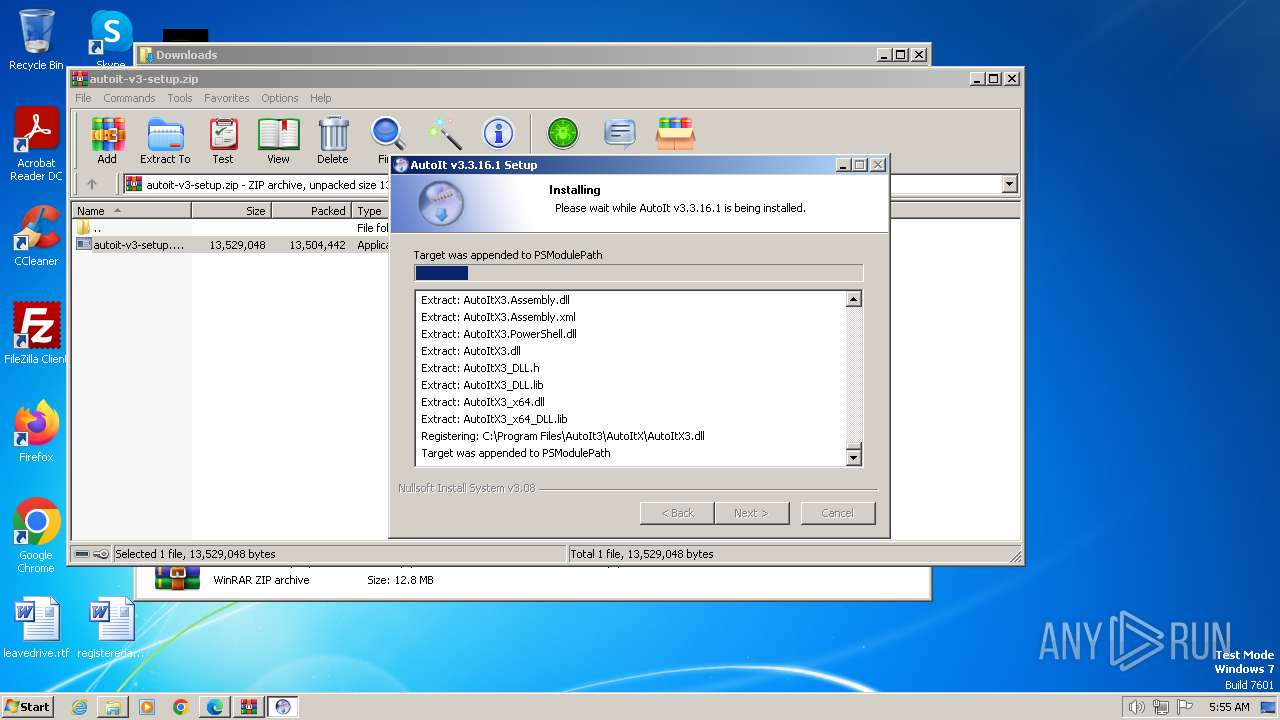
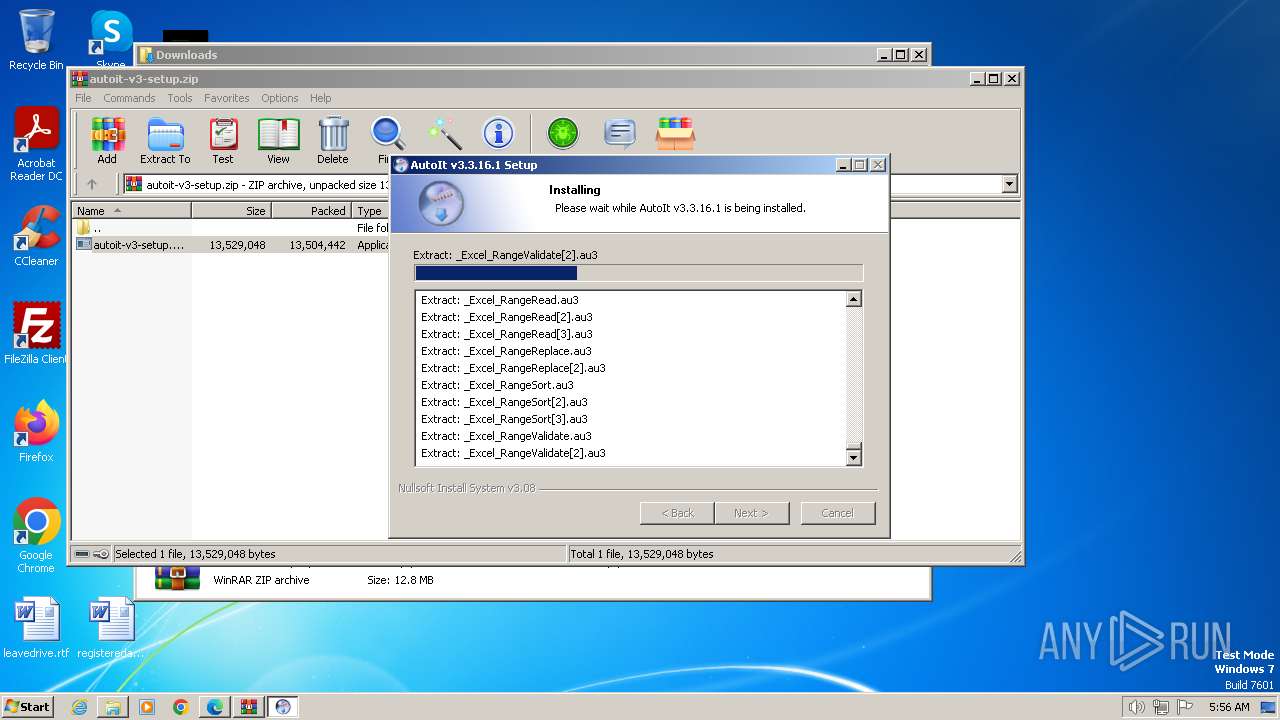
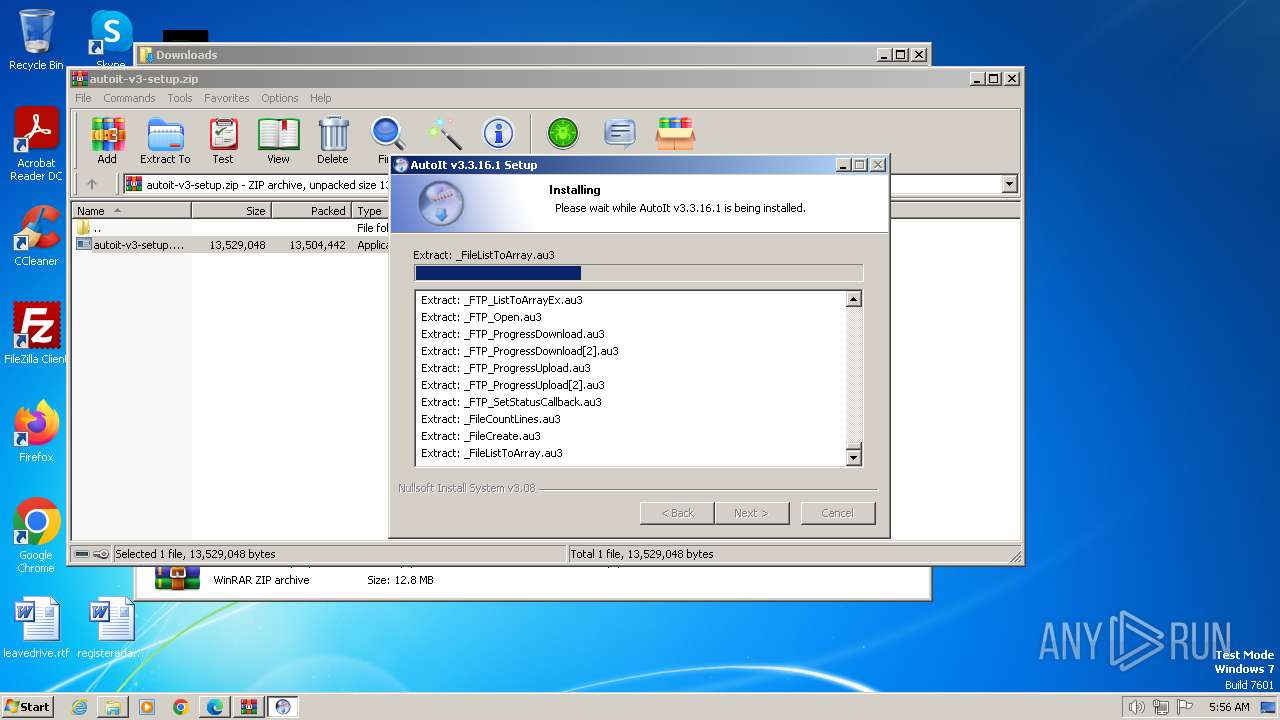
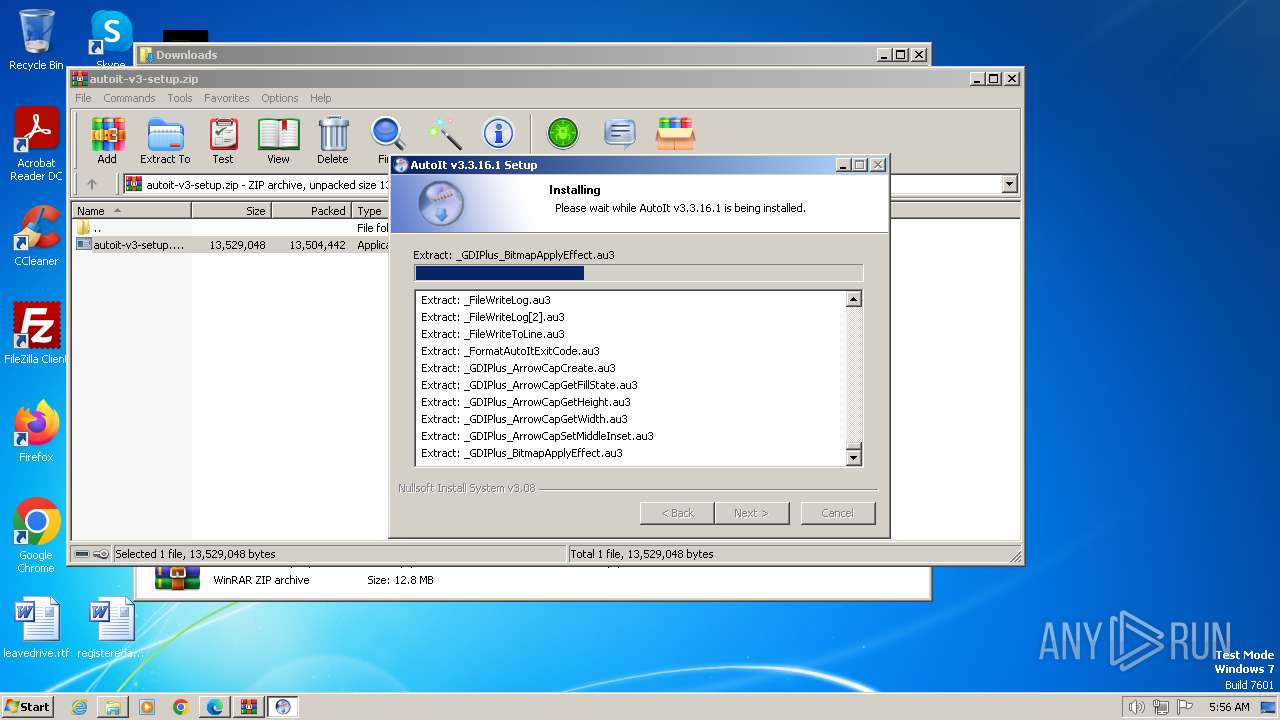
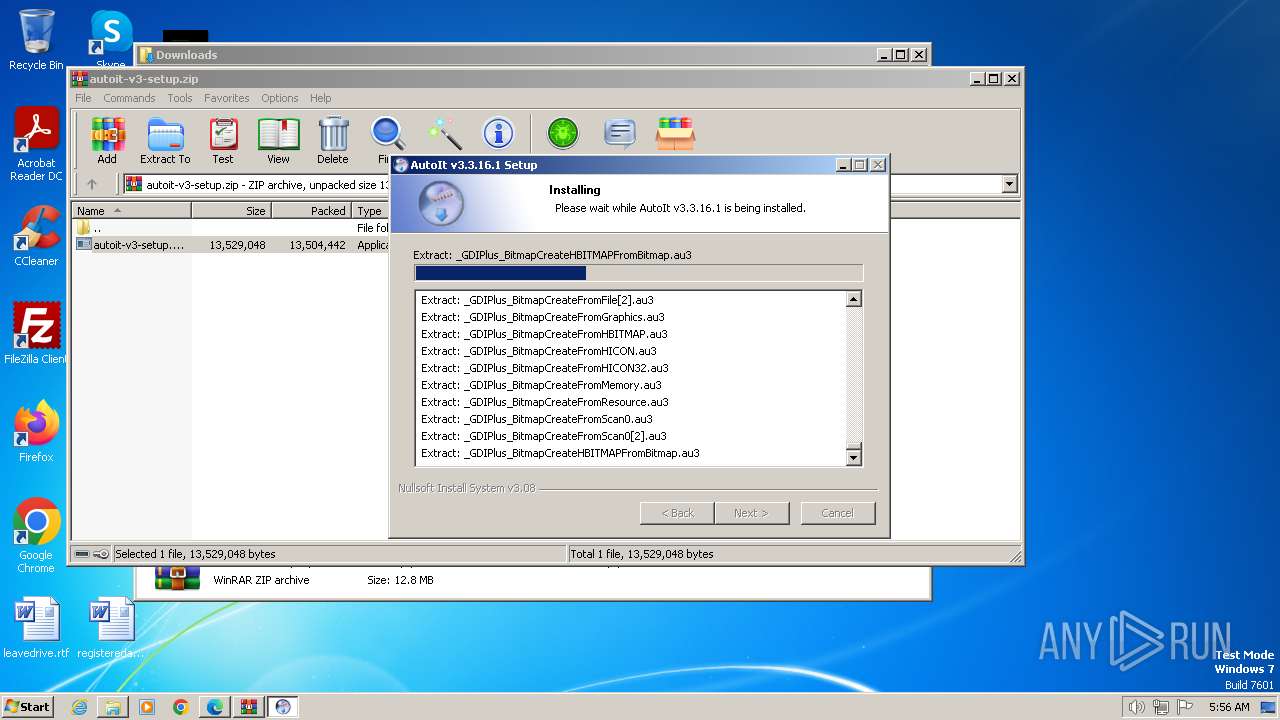
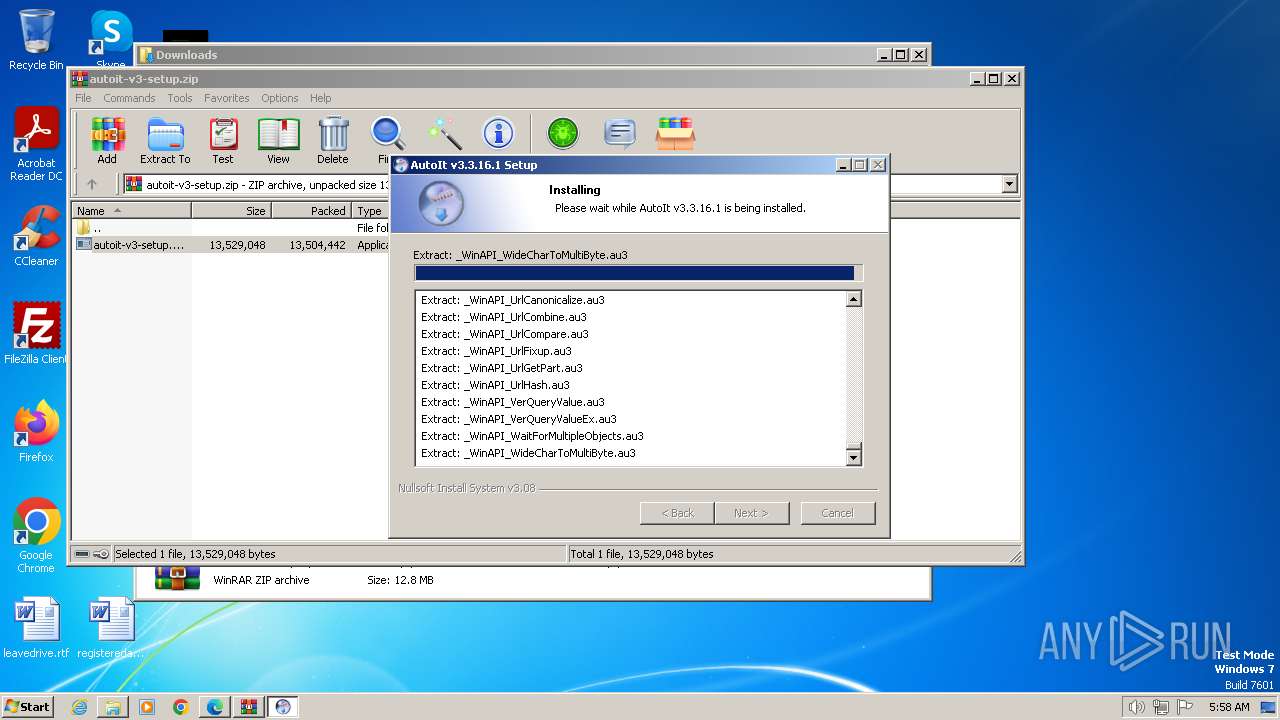
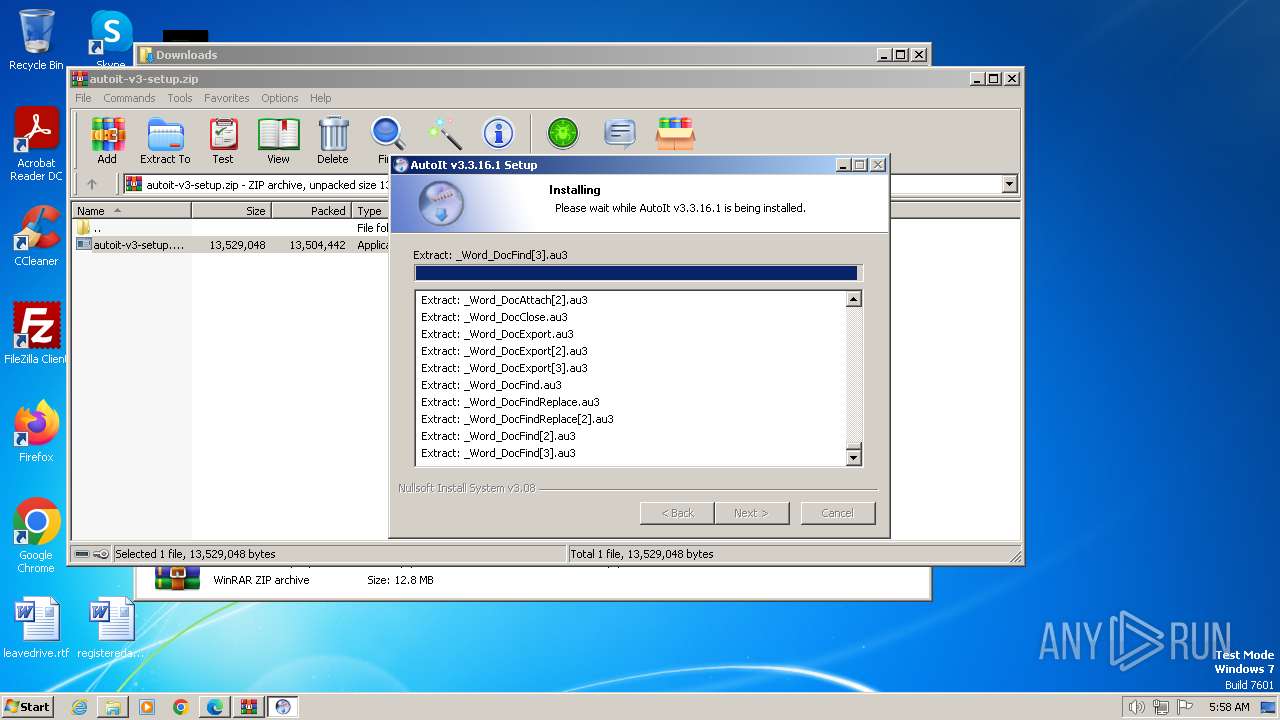
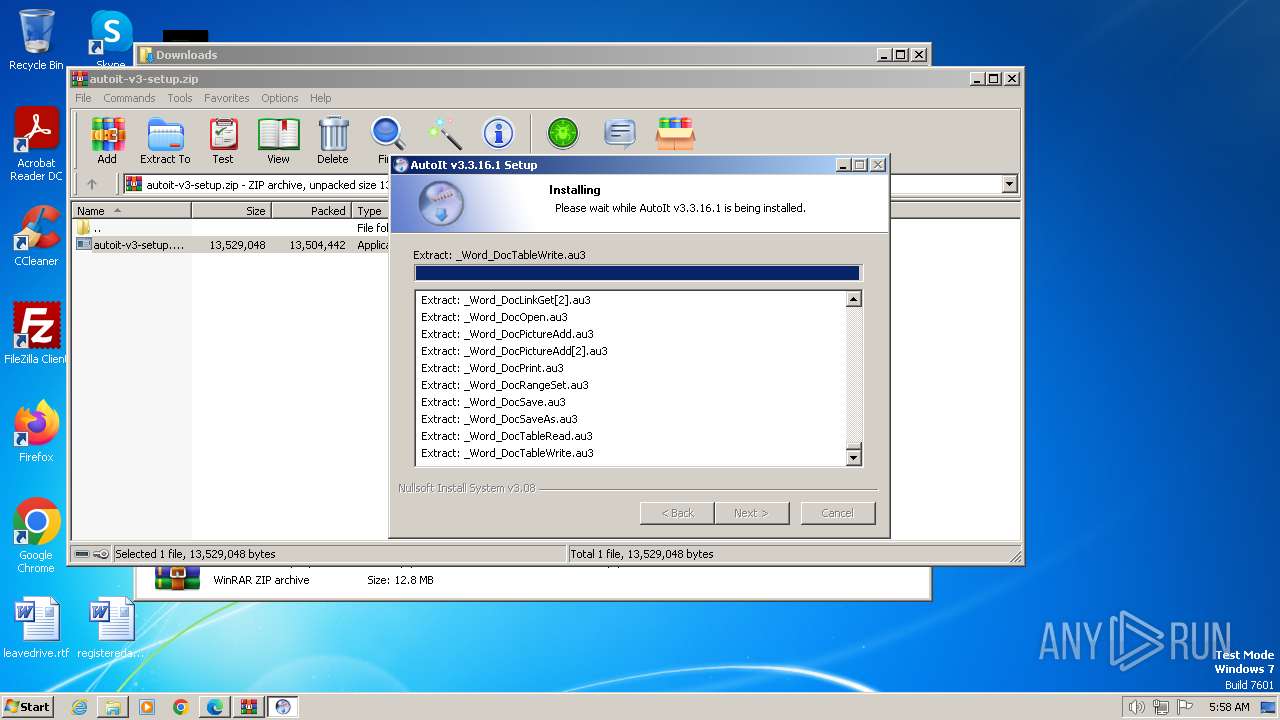
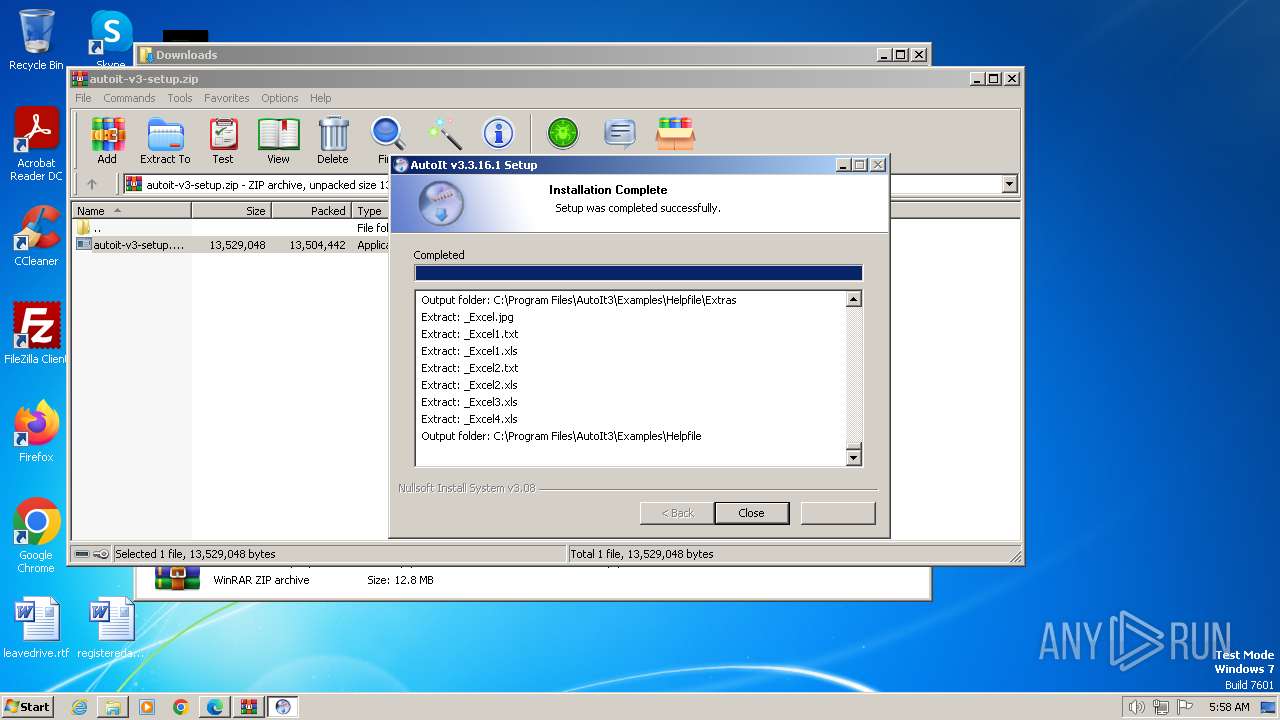
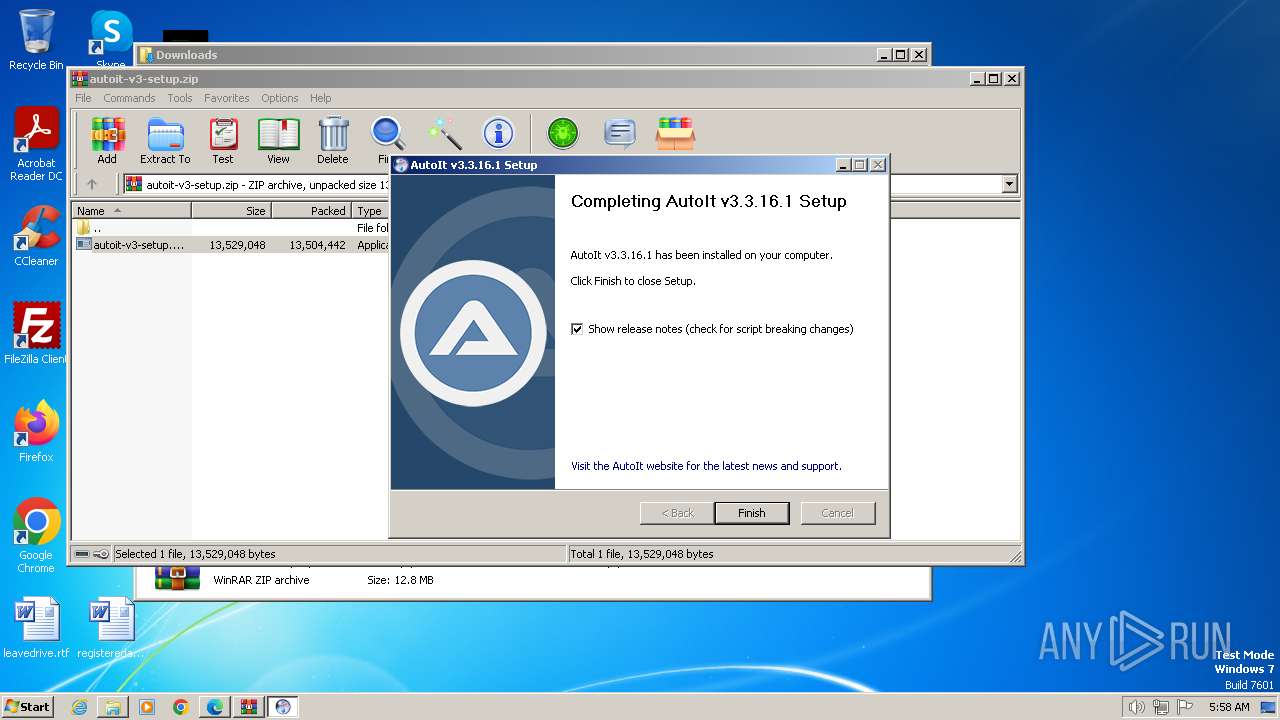
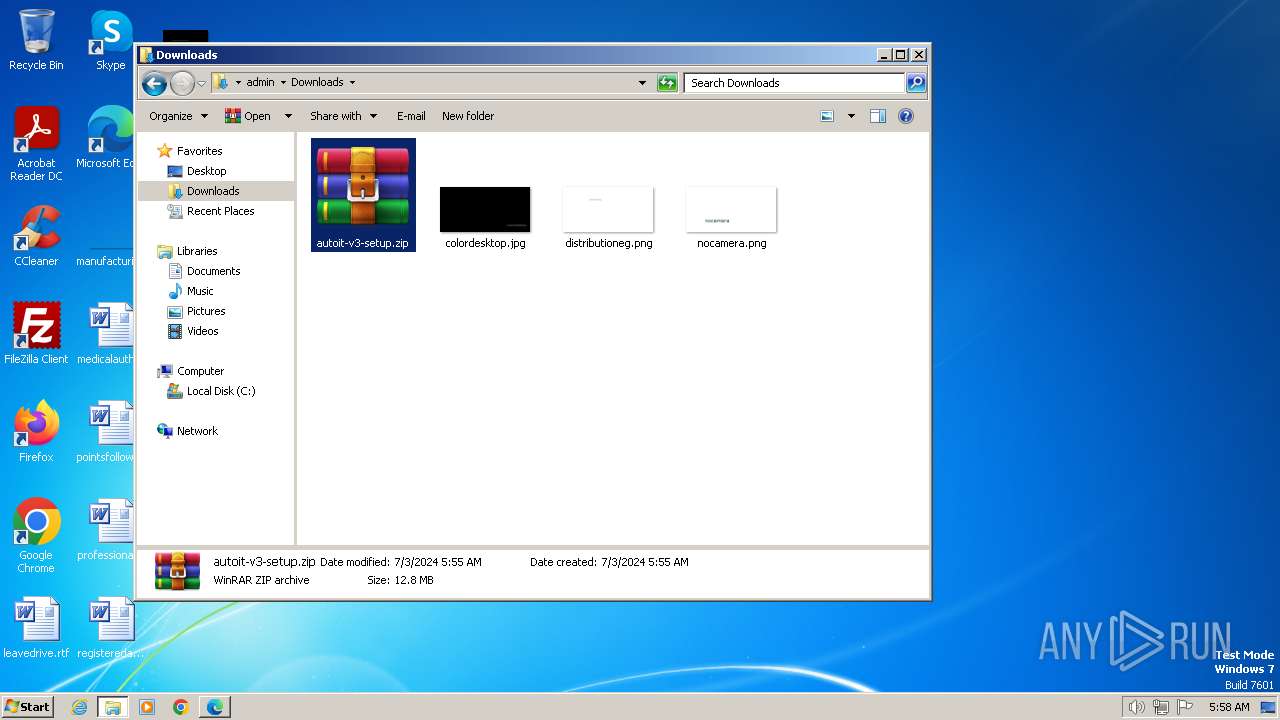
Drops the executable file immediately after the start
- autoit-v3-setup.exe (PID: 3240)
SUSPICIOUS
Reads the Internet Settings
- rundll32.exe (PID: 3280)
- hh.exe (PID: 2012)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2880)
Executable content was dropped or overwritten
- autoit-v3-setup.exe (PID: 3240)
The process creates files with name similar to system file names
- autoit-v3-setup.exe (PID: 3240)
Malware-specific behavior (creating "System.dll" in Temp)
- autoit-v3-setup.exe (PID: 3240)
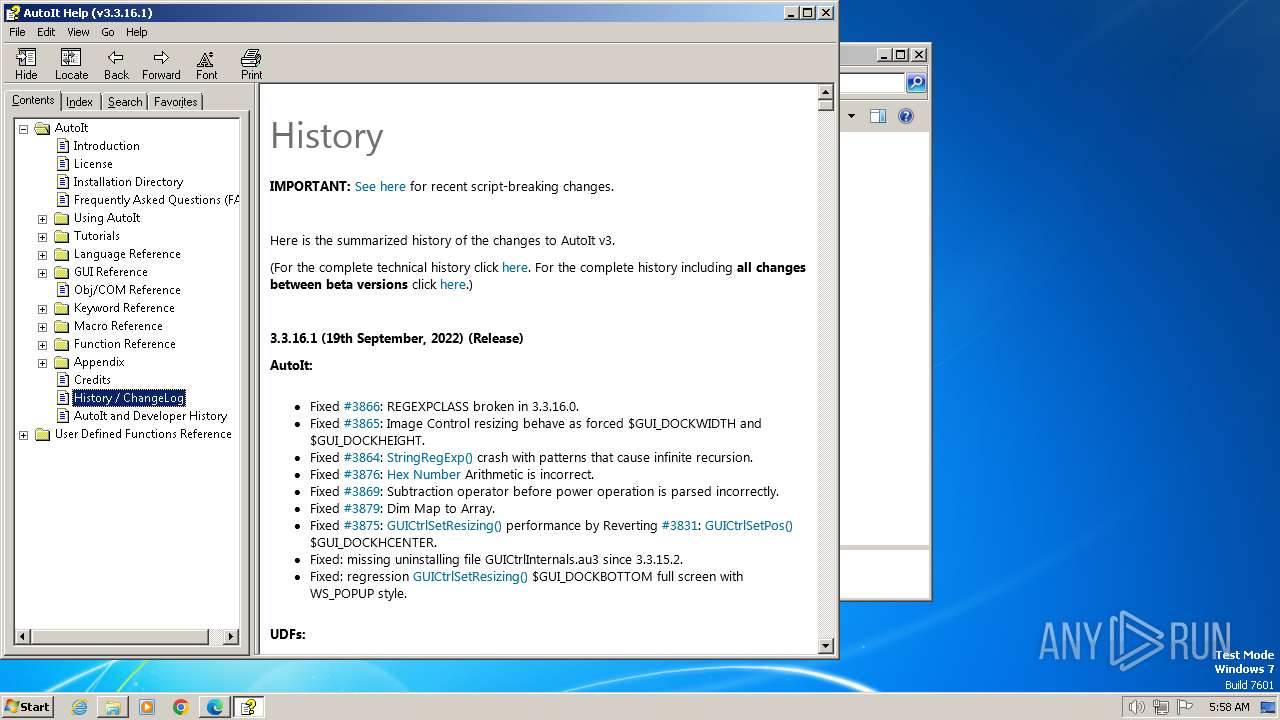
Creates/Modifies COM task schedule object
- autoit-v3-setup.exe (PID: 3240)
Creates a software uninstall entry
- autoit-v3-setup.exe (PID: 3240)
Reads Internet Explorer settings
- hh.exe (PID: 2012)
Reads Microsoft Outlook installation path
- hh.exe (PID: 2012)
INFO
Drops the executable file immediately after the start
- msedge.exe (PID: 3396)
- msedge.exe (PID: 3164)
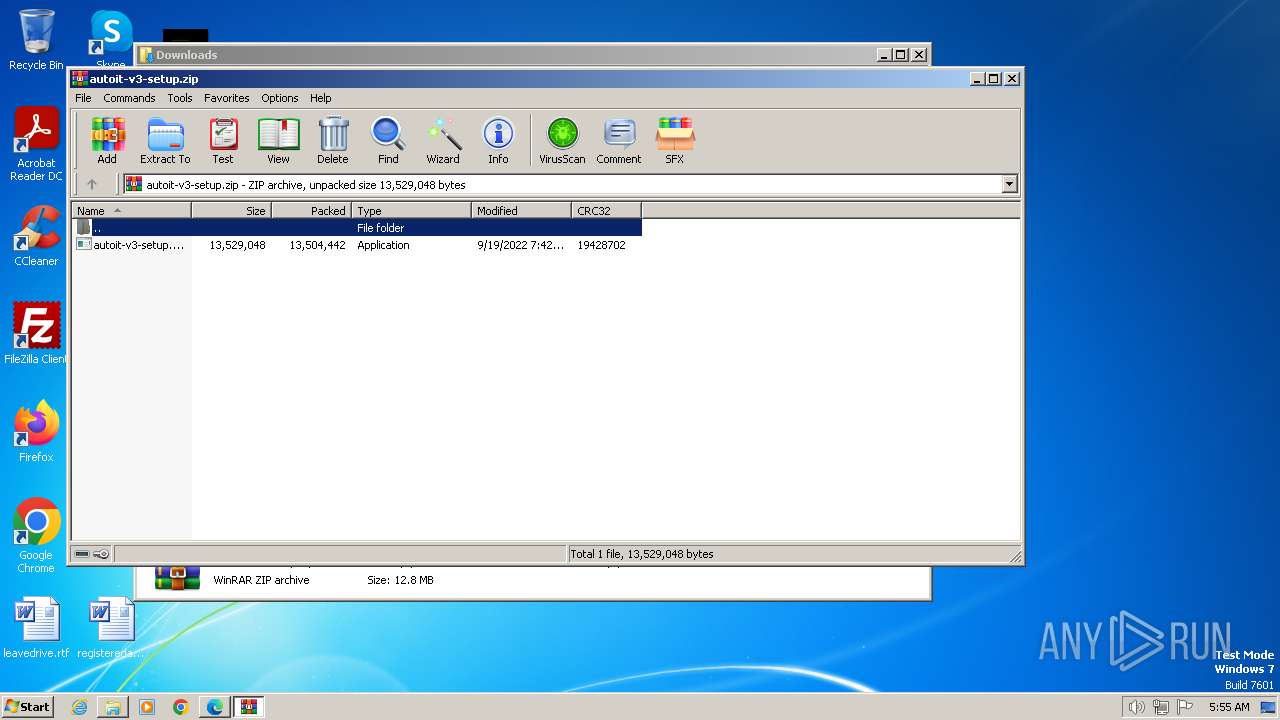
- WinRAR.exe (PID: 2880)
The process uses the downloaded file
- msedge.exe (PID: 3188)
- WinRAR.exe (PID: 2880)
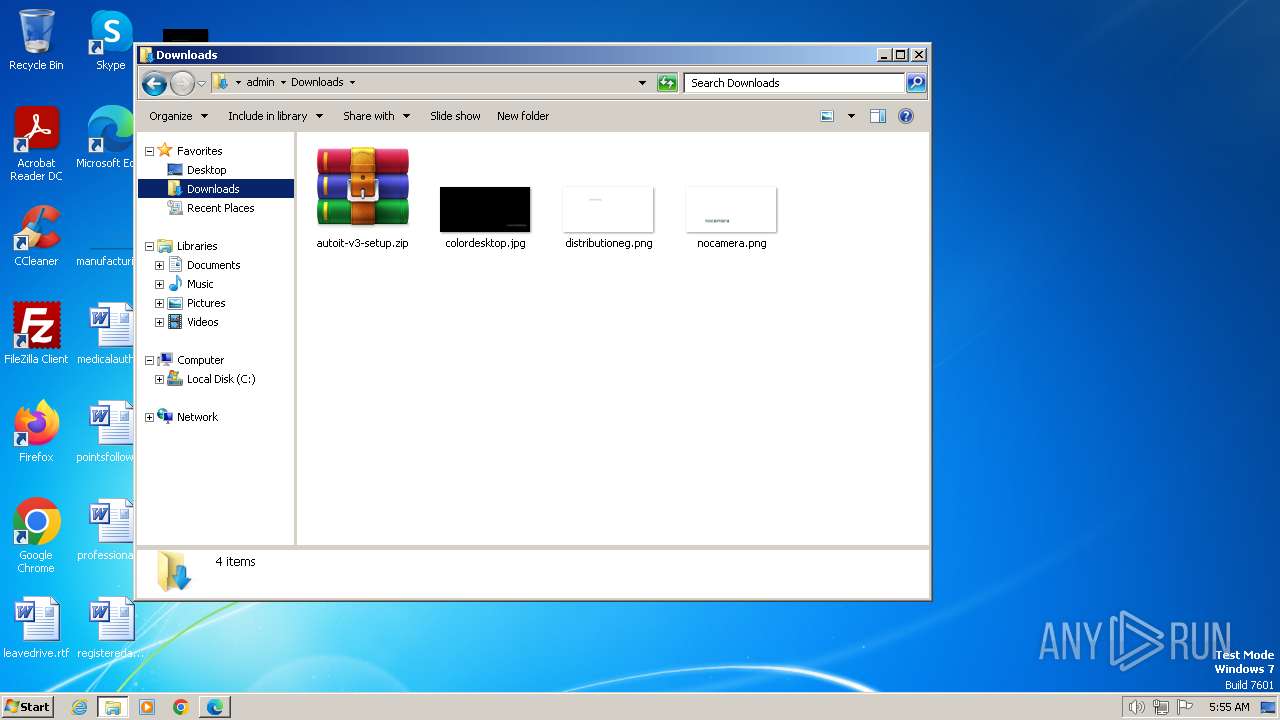
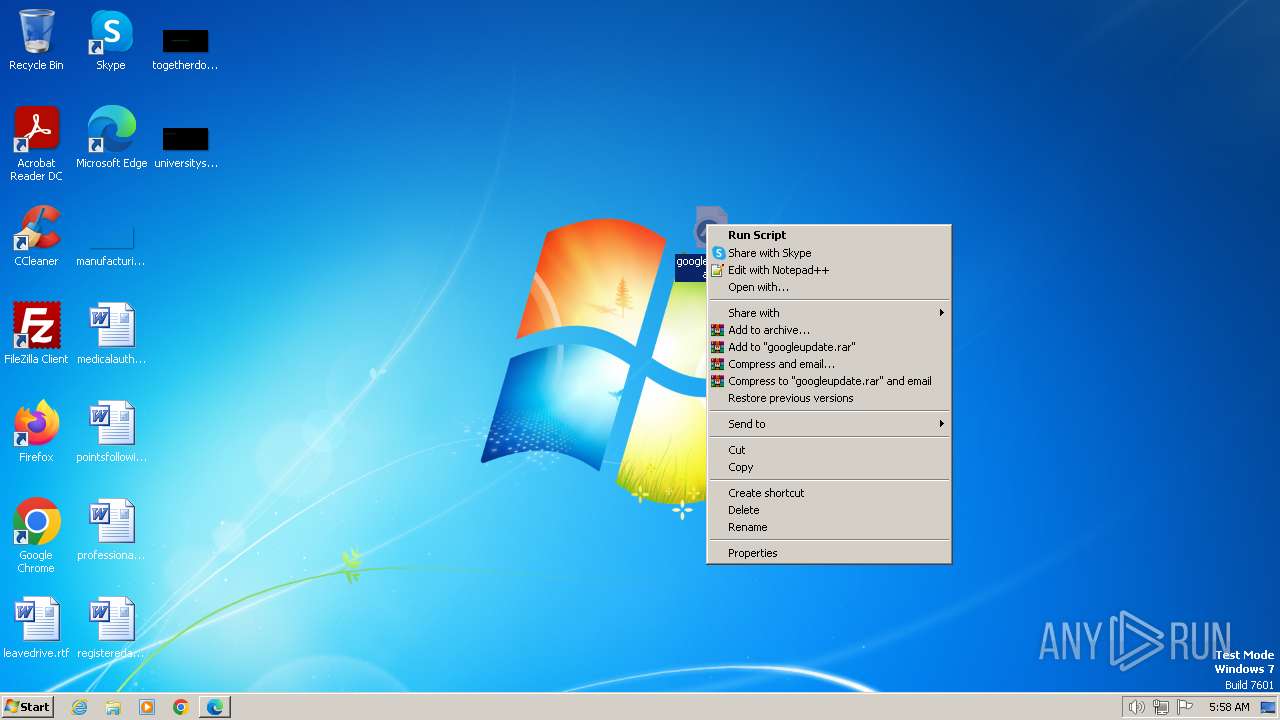
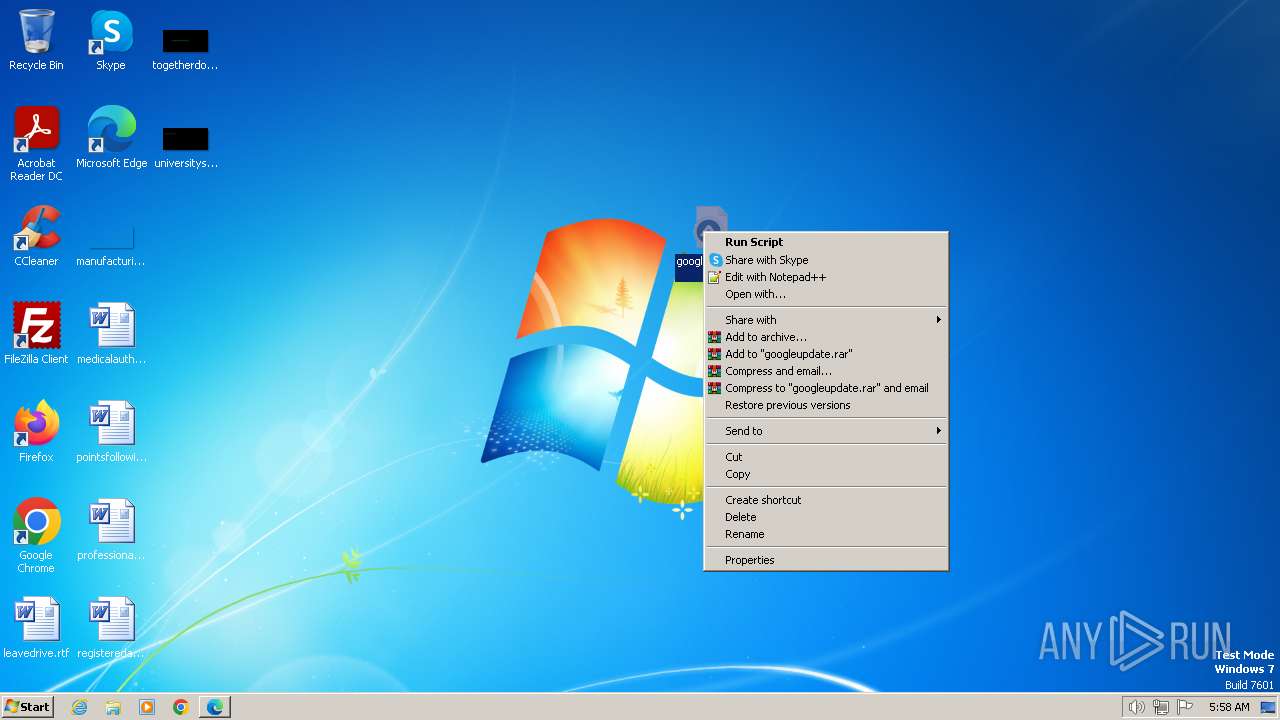
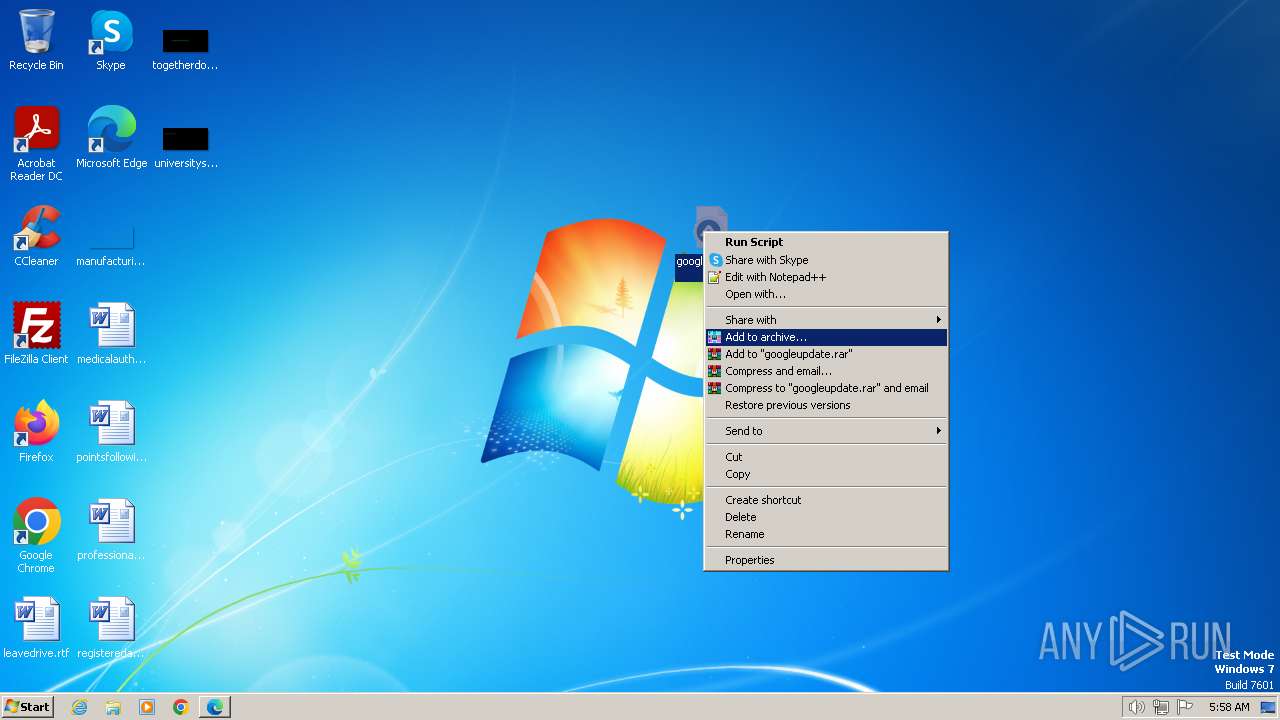
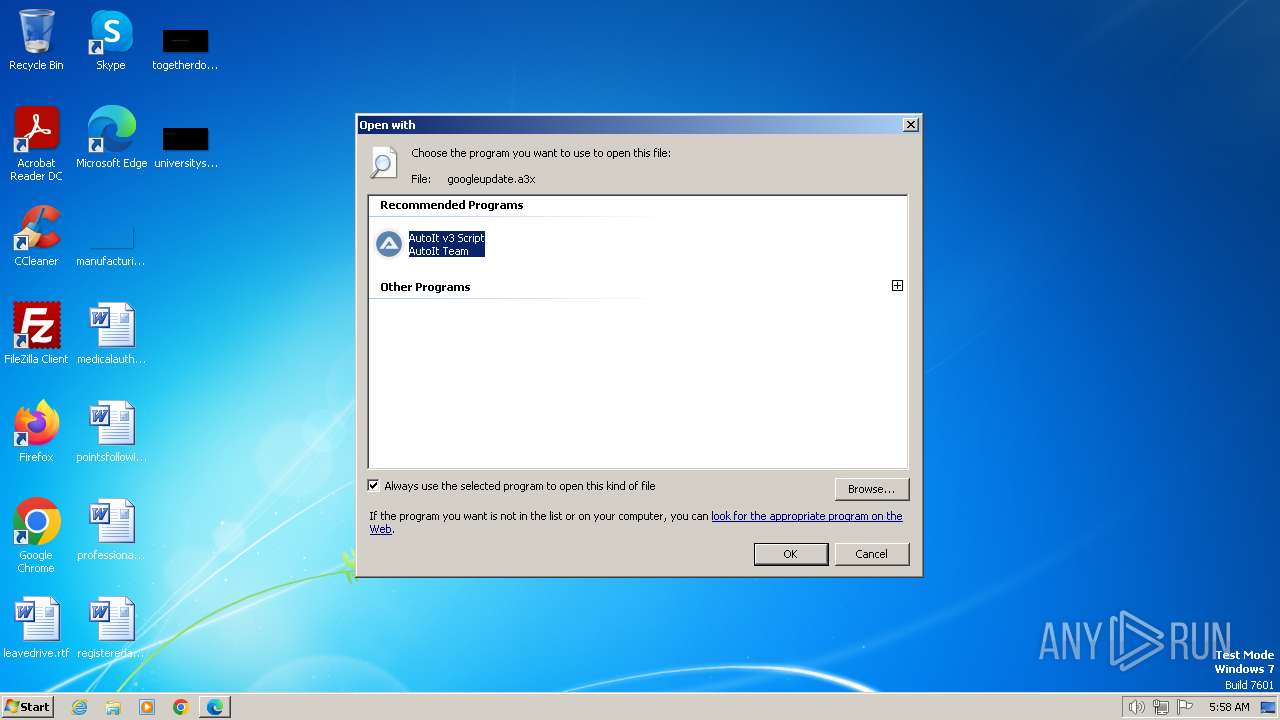
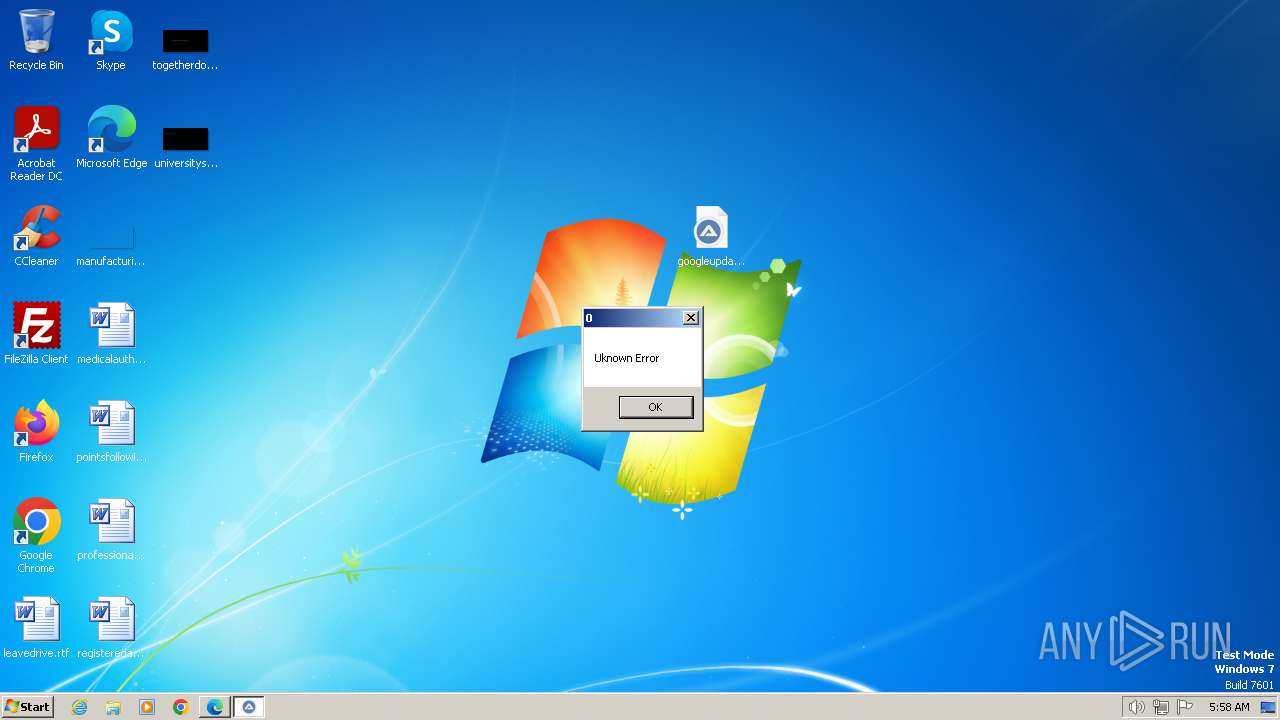
Manual execution by a user
- explorer.exe (PID: 2836)
- WinRAR.exe (PID: 2880)
- AutoIt3.exe (PID: 1036)
- notepad++.exe (PID: 2852)
- AutoIt3.exe (PID: 1020)
- rundll32.exe (PID: 1468)
Application launched itself
- msedge.exe (PID: 3396)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2880)
Checks supported languages
- autoit-v3-setup.exe (PID: 3240)
- AutoIt3.exe (PID: 1036)
- AutoIt3.exe (PID: 1020)
- AutoIt3.exe (PID: 1568)
Reads the computer name
- autoit-v3-setup.exe (PID: 3240)
Create files in a temporary directory
- autoit-v3-setup.exe (PID: 3240)
- hh.exe (PID: 2012)
Creates files in the program directory
- autoit-v3-setup.exe (PID: 3240)
- hh.exe (PID: 2012)
Reads mouse settings
- AutoIt3.exe (PID: 1568)
- AutoIt3.exe (PID: 1036)
- AutoIt3.exe (PID: 1020)
Reads the machine GUID from the registry
- hh.exe (PID: 2012)
Reads security settings of Internet Explorer
- hh.exe (PID: 2012)
Checks proxy server information
- hh.exe (PID: 2012)
Creates files or folders in the user directory
- hh.exe (PID: 2012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .a3x | | | AutoIt v3 compiled script (100) |
|---|
Total processes
85
Monitored processes
40
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 940 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1620 --field-trial-handle=1324,i,12144161913650051428,2428642706698127797,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=4376 --field-trial-handle=1324,i,12144161913650051428,2428642706698127797,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1020 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2880.34397\autoit-v3-setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2880.34397\autoit-v3-setup.exe | — | WinRAR.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Setup Exit code: 3221226540 Version: 3.3.16.1 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\AutoIt3\AutoIt3.exe" "C:\Users\admin\Desktop\googleupdate.a3x" | C:\Program Files\AutoIt3\AutoIt3.exe | — | explorer.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 16, 1 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\AutoIt3\AutoIt3.exe" "C:\Users\admin\Desktop\googleupdate.a3x" | C:\Program Files\AutoIt3\AutoIt3.exe | — | explorer.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 16, 1 Modules
| |||||||||||||||
| 1468 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\googleupdate.a3x | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1568 | "C:\Program Files\AutoIt3\AutoIt3.exe" "C:\Users\admin\Desktop\googleupdate.a3x" | C:\Program Files\AutoIt3\AutoIt3.exe | — | rundll32.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 16, 1 Modules
| |||||||||||||||
| 2012 | "C:\Windows\hh.exe" -mapid 1000 "C:\Program Files\AutoIt3\AutoIt.chm" | C:\Windows\hh.exe | — | autoit-v3-setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2020 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=3784 --field-trial-handle=1324,i,12144161913650051428,2428642706698127797,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --mojo-platform-channel-handle=3880 --field-trial-handle=1324,i,12144161913650051428,2428642706698127797,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
29 941
Read events
29 706
Write events
222
Delete events
13
Modification events
| (PID) Process: | (3396) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3396) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3396) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3396) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3396) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3396) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3396) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3396) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: BF825BEAE67A2F00 | |||
| (PID) Process: | (3396) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3396) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
25
Suspicious files
268
Text files
2 868
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF4f6c0.TMP | — | |
MD5:— | SHA256:— | |||
| 3396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4f6ef.TMP | — | |
MD5:— | SHA256:— | |||
| 3396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4f6ff.TMP | — | |
MD5:— | SHA256:— | |||
| 3396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF4f74d.TMP | — | |
MD5:— | SHA256:— | |||
| 3396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma | binary | |
MD5:886E82F2CA62ECCCE64601B30592078A | SHA256:E5E13D53601100FF3D6BB71514CBCCC4C73FE9B7EF5E930100E644187B42948E | |||
| 3396 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State | binary | |
MD5:F4DBB55B41C781F998F55A32A0C7200A | SHA256:67B22F277D3B87C82C5941FE0167E83FE092BD1B3F2C28F2BC095023287DDB00 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
68
DNS requests
60
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
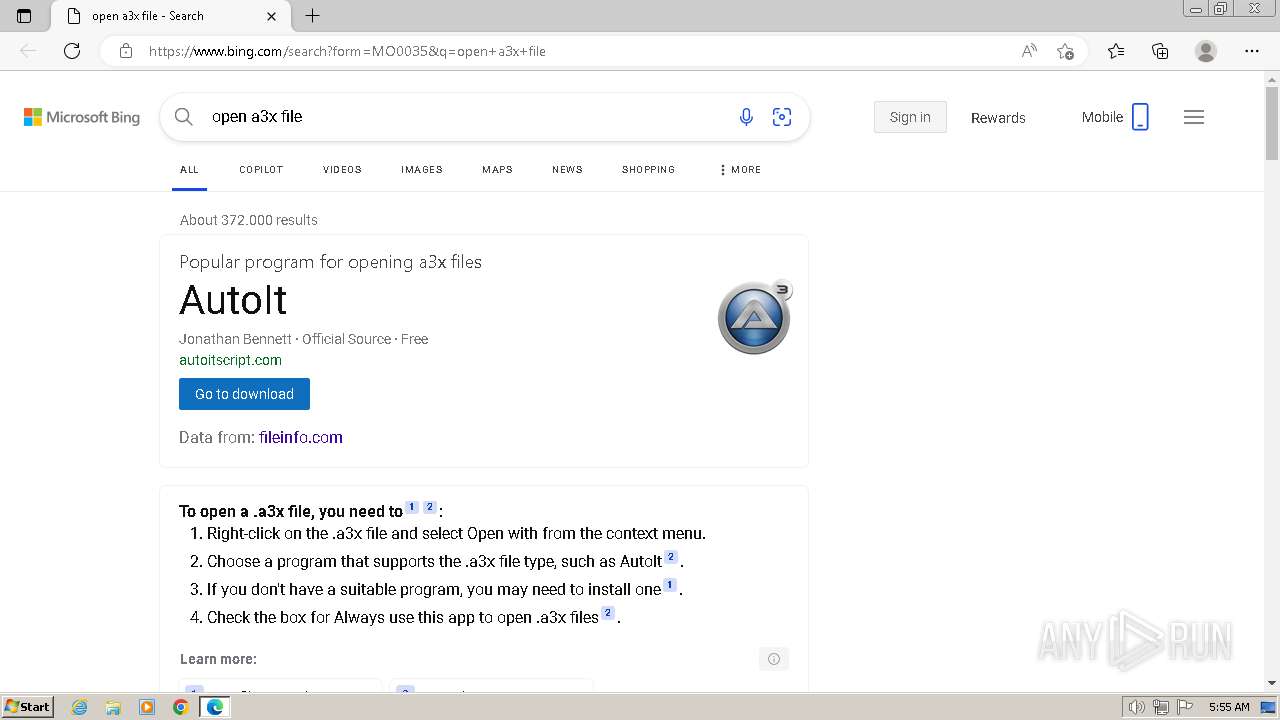
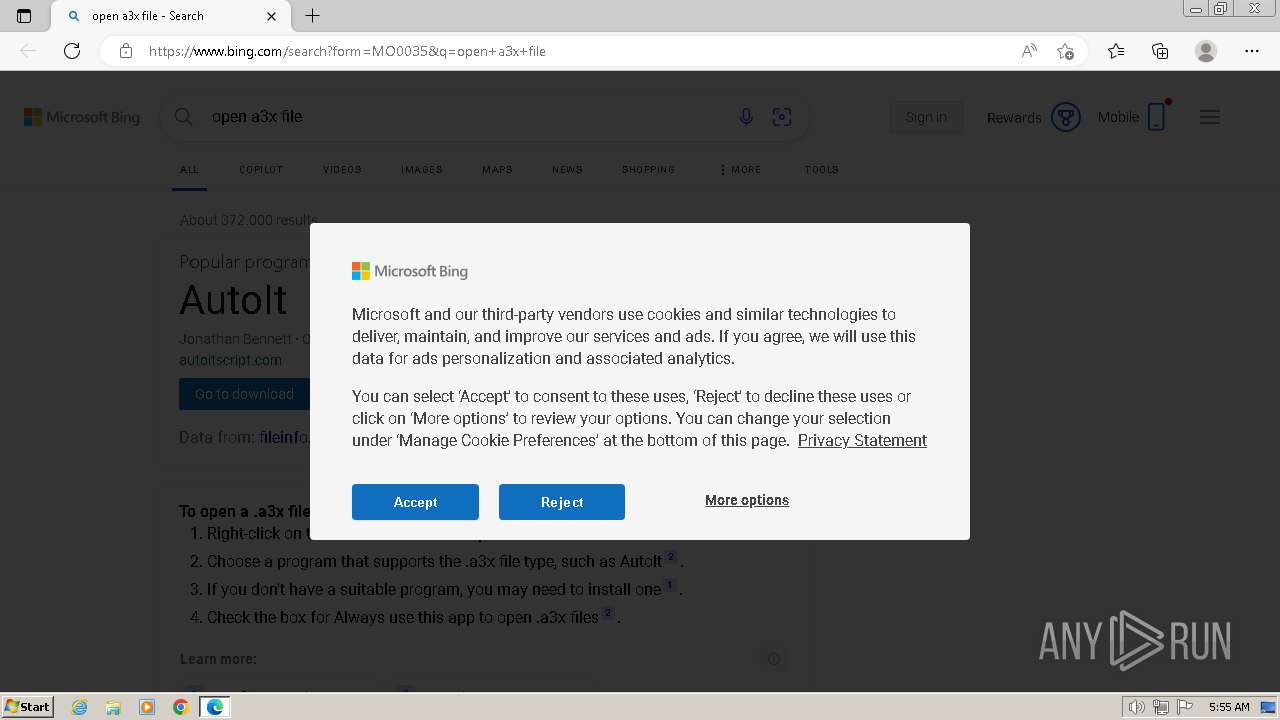
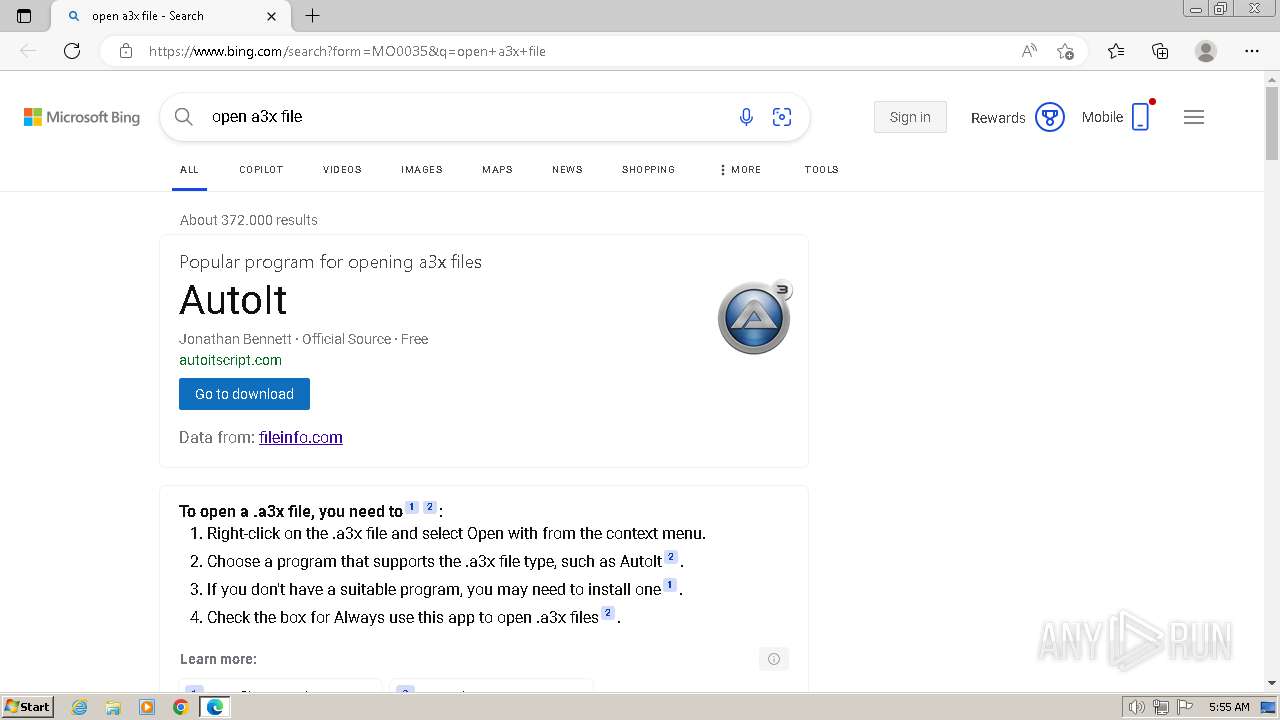
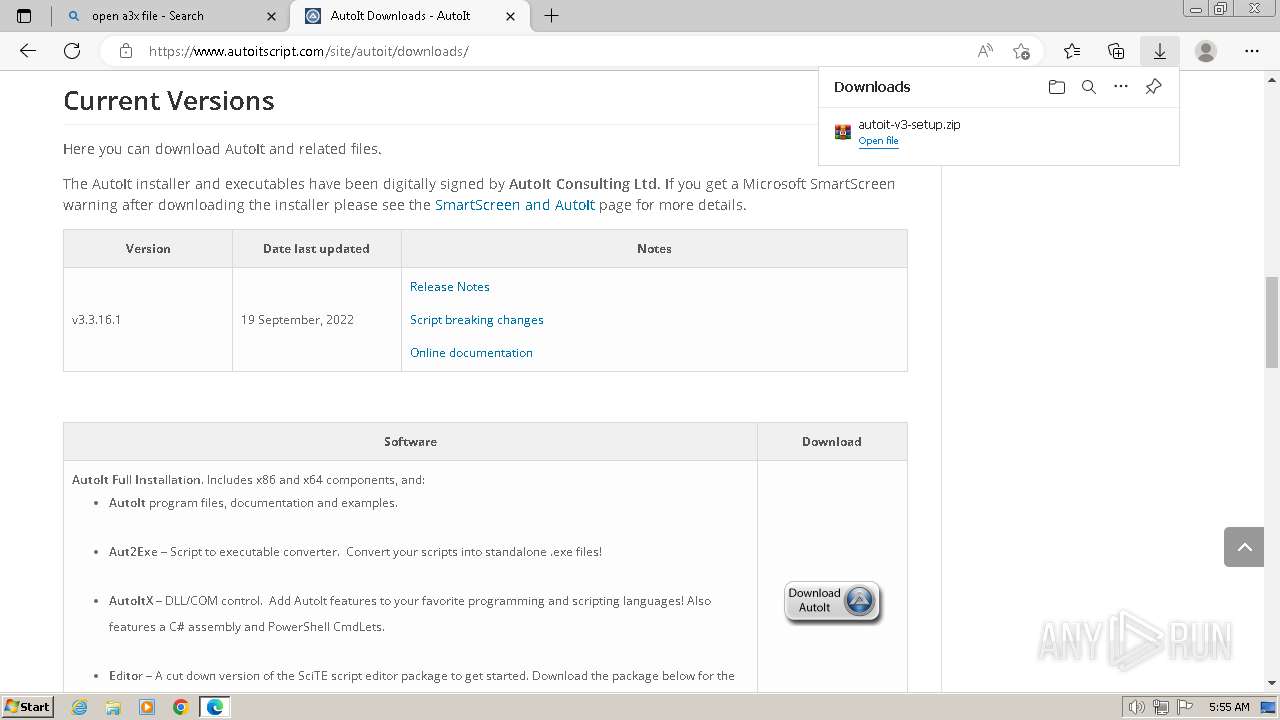
3164 | msedge.exe | GET | 301 | 2.21.20.141:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=a3x | DE | — | — | unknown |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | GB | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | unknown |
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | GB | — | — | unknown |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3396 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3164 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3164 | msedge.exe | 184.30.17.189:80 | go.microsoft.com | AKAMAI-AS | DE | unknown |
3164 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3164 | msedge.exe | 184.30.17.189:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
3164 | msedge.exe | 2.21.20.141:80 | shell.windows.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
aefd.nelreports.net |
| whitelisted |
www.autoitscript.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3164 | msedge.exe | Misc activity | ET HUNTING Observed DNS Query to autoitscript .com |
3164 | msedge.exe | Misc activity | ET HUNTING Observed Domain (autoitscript .com) in TLS SNI |
3164 | msedge.exe | Misc activity | ET HUNTING Observed DNS Query to autoitscript .com |
3164 | msedge.exe | Misc activity | ET HUNTING Observed Domain (autoitscript .com) in TLS SNI |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|