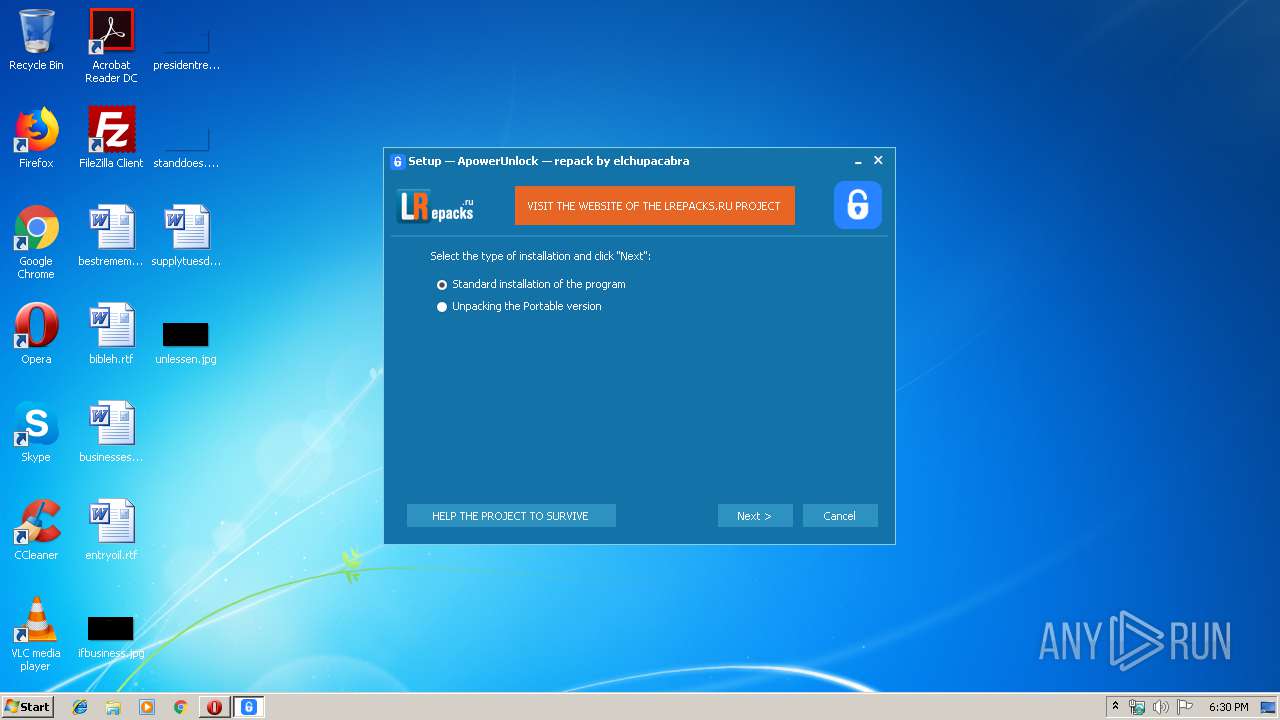
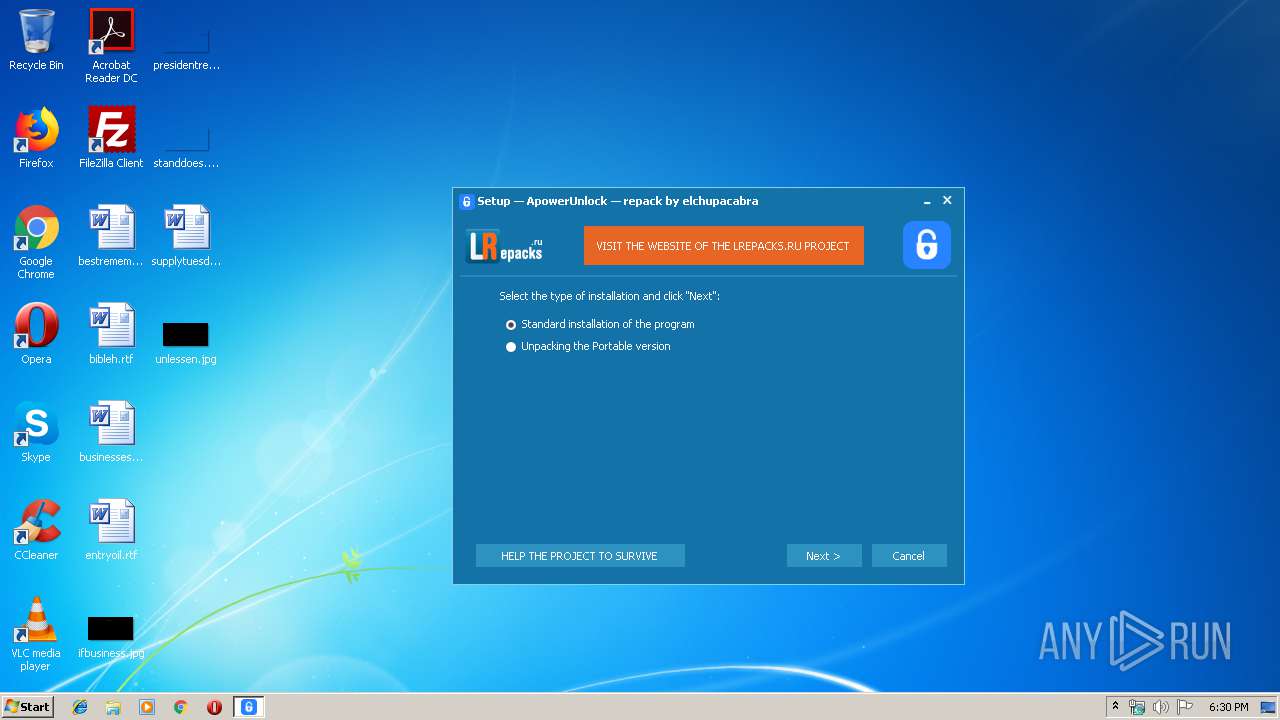
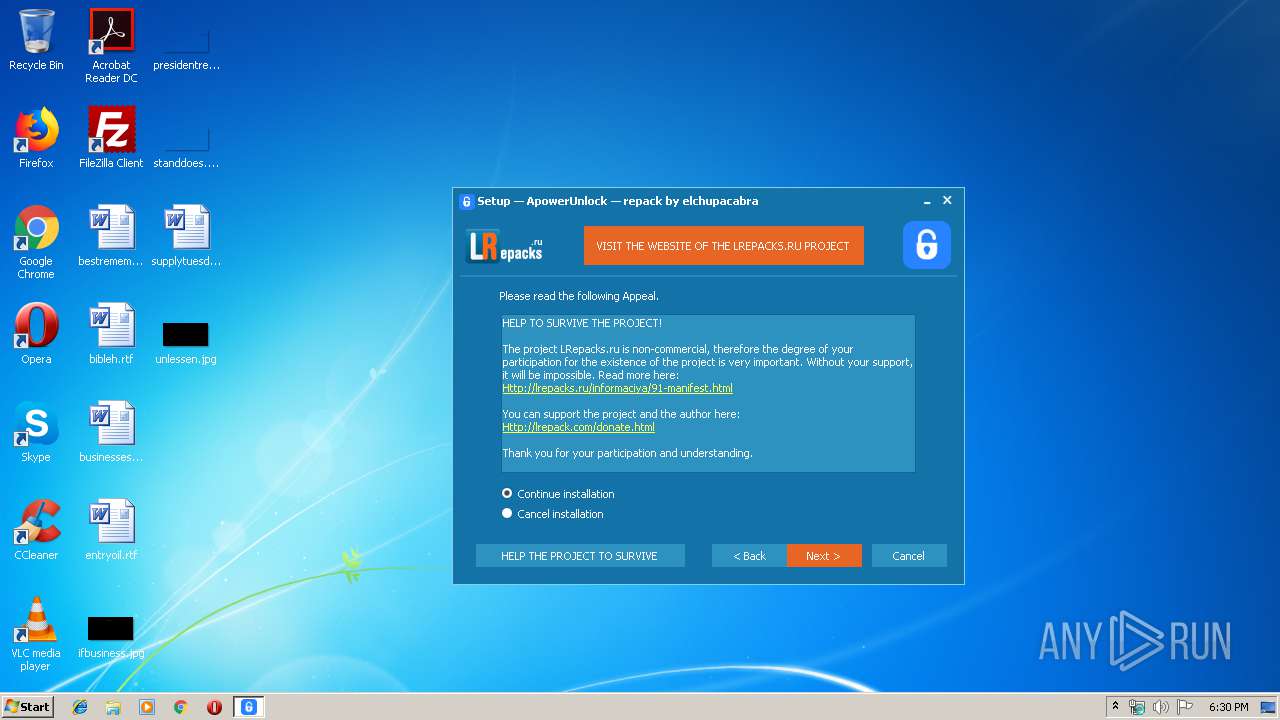
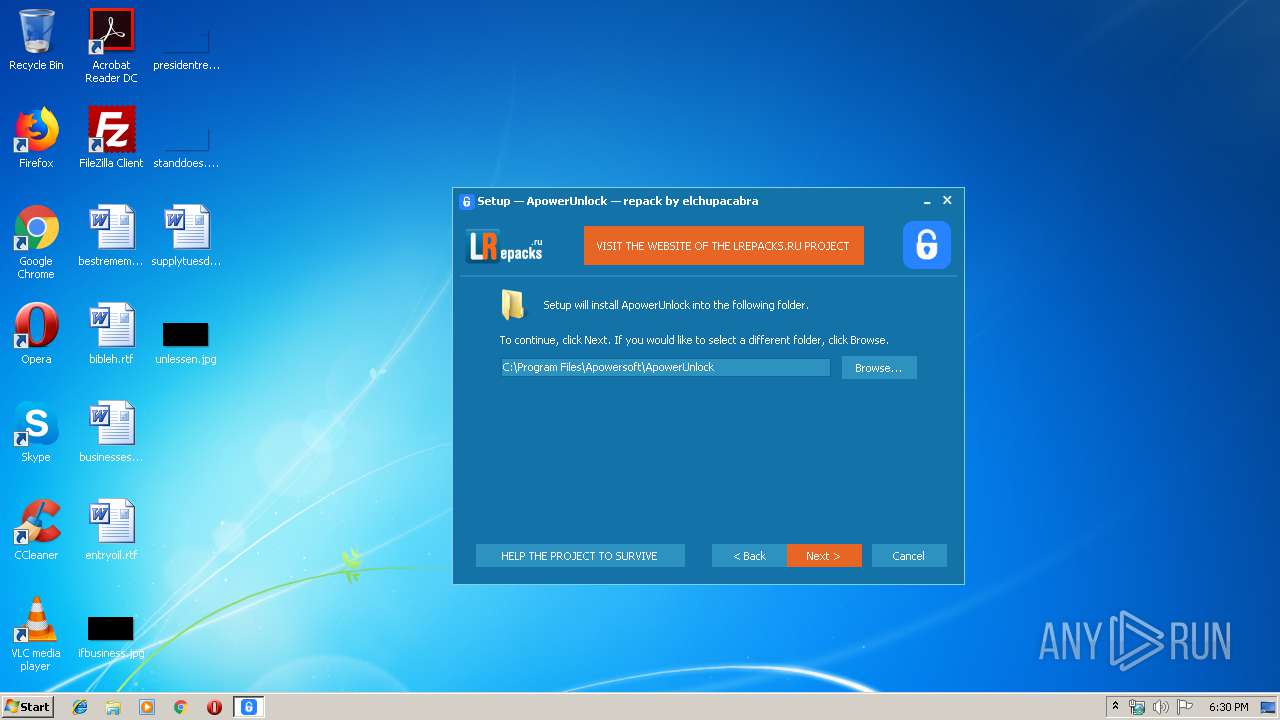
| File name: | ApowerUnlock 1.0.1.8.exe |
| Full analysis: | https://app.any.run/tasks/77ea5939-1296-4339-aa43-a20d66f47d84 |
| Verdict: | Malicious activity |
| Analysis date: | January 21, 2020, 18:30:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A88A866D400CE8907DF7061298FFBCA3 |
| SHA1: | AC6AEA44775D1A80B3C3C782EC2F5F9B604B4AE3 |
| SHA256: | 974ACC9C6064A535B9B8D7B62D71AC84514BCAB7E417AA3C0BBC18A900DD1B8B |
| SSDEEP: | 393216:pULKP9wQkZ7ro+3r5/vFeIUQ53UzgkfvDOnx8SoL+V:pV0Z78+3r9NeXqkHoxo+ |
MALICIOUS
Application was dropped or rewritten from another process
- ApowerUnlock.exe (PID: 2120)
- 7z.exe (PID: 2692)
Loads dropped or rewritten executable
- ApowerUnlock.exe (PID: 2120)
SUSPICIOUS
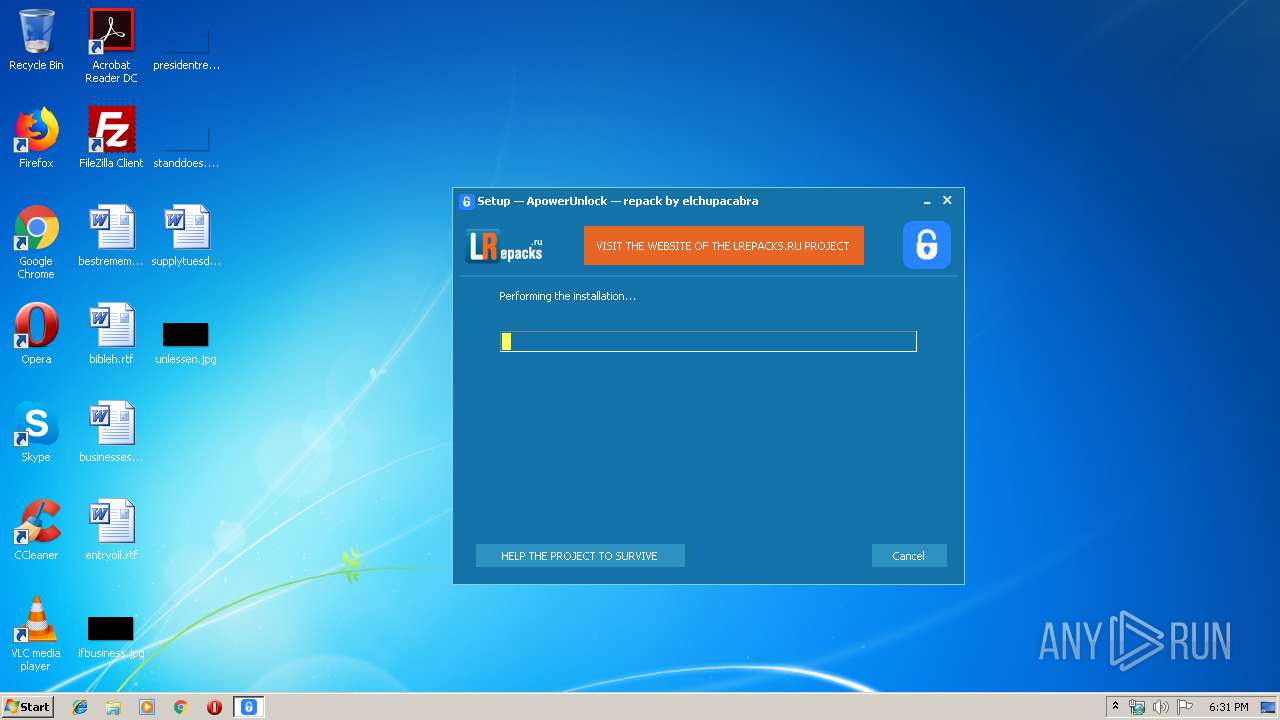
Executable content was dropped or overwritten
- ApowerUnlock 1.0.1.8.exe (PID: 2764)
- ApowerUnlock 1.0.1.8.tmp (PID: 1048)
- ApowerUnlock.exe (PID: 2120)
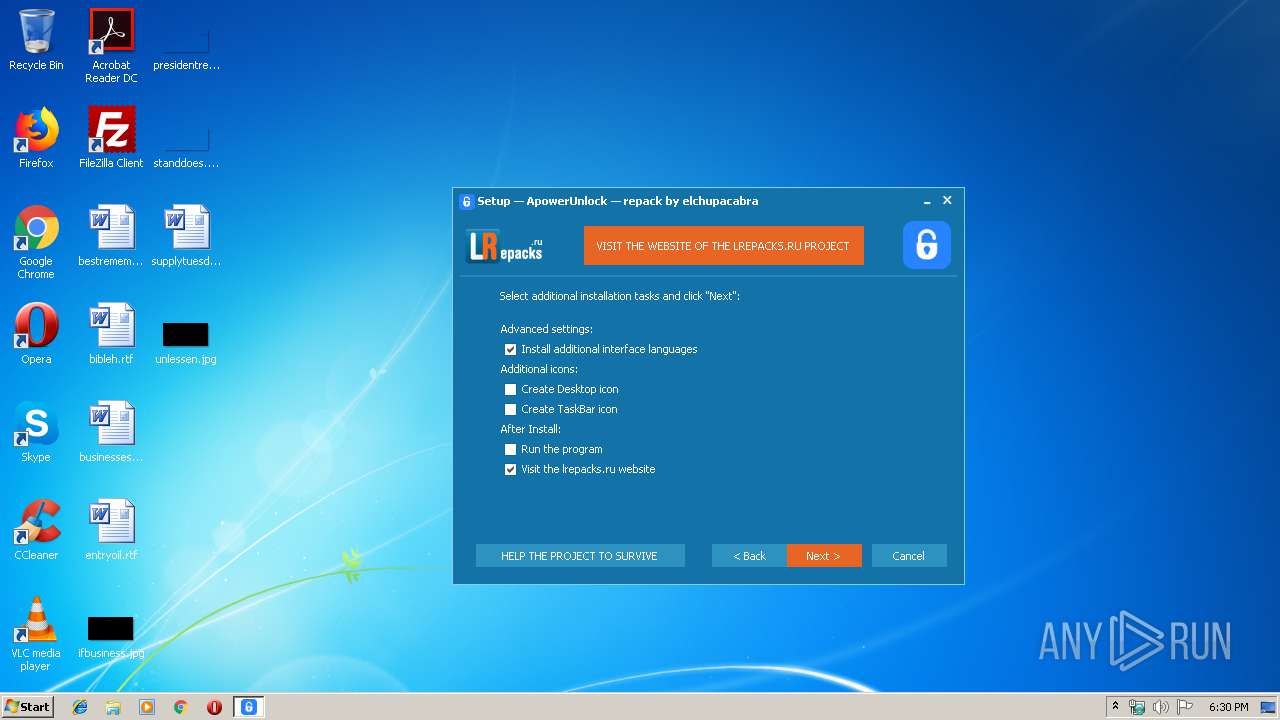
Changes IE settings (feature browser emulation)
- ApowerUnlock 1.0.1.8.tmp (PID: 1048)
Creates files in the user directory
- ApowerUnlock 1.0.1.8.tmp (PID: 1048)
- ApowerUnlock.exe (PID: 2120)
- 7z.exe (PID: 2692)
Reads Internet Cache Settings
- ApowerUnlock 1.0.1.8.tmp (PID: 1048)
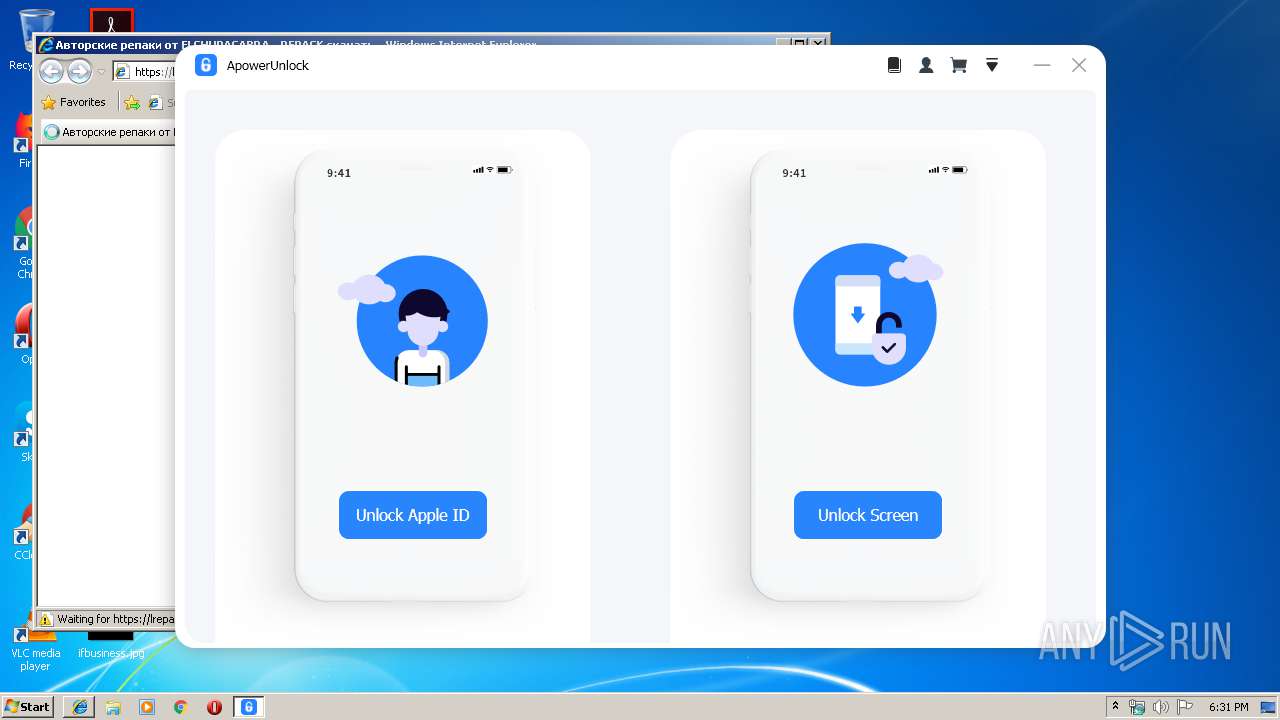
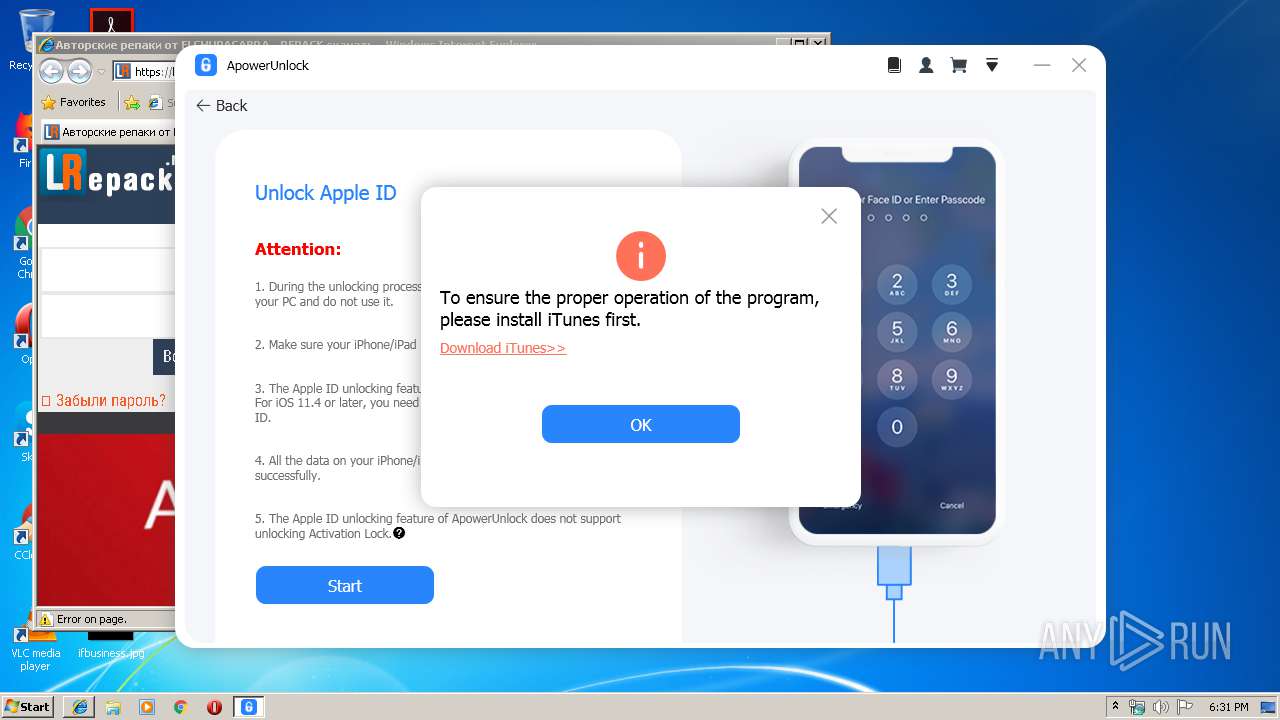
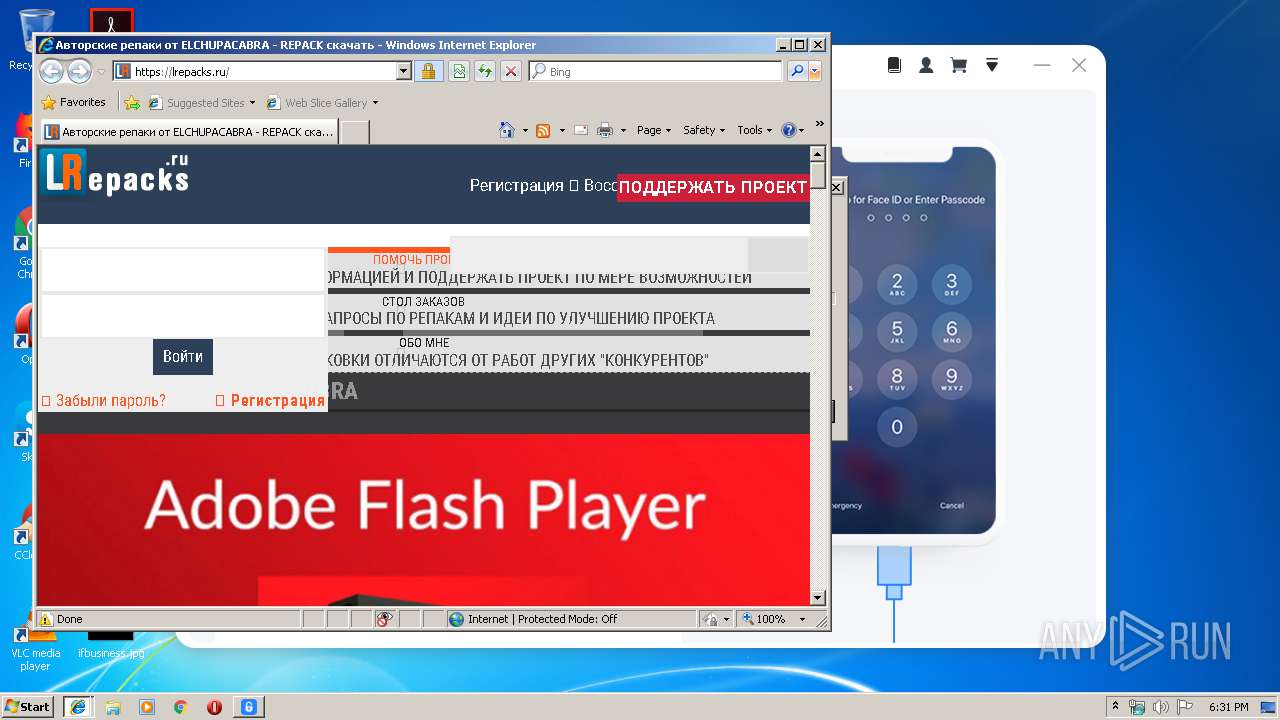
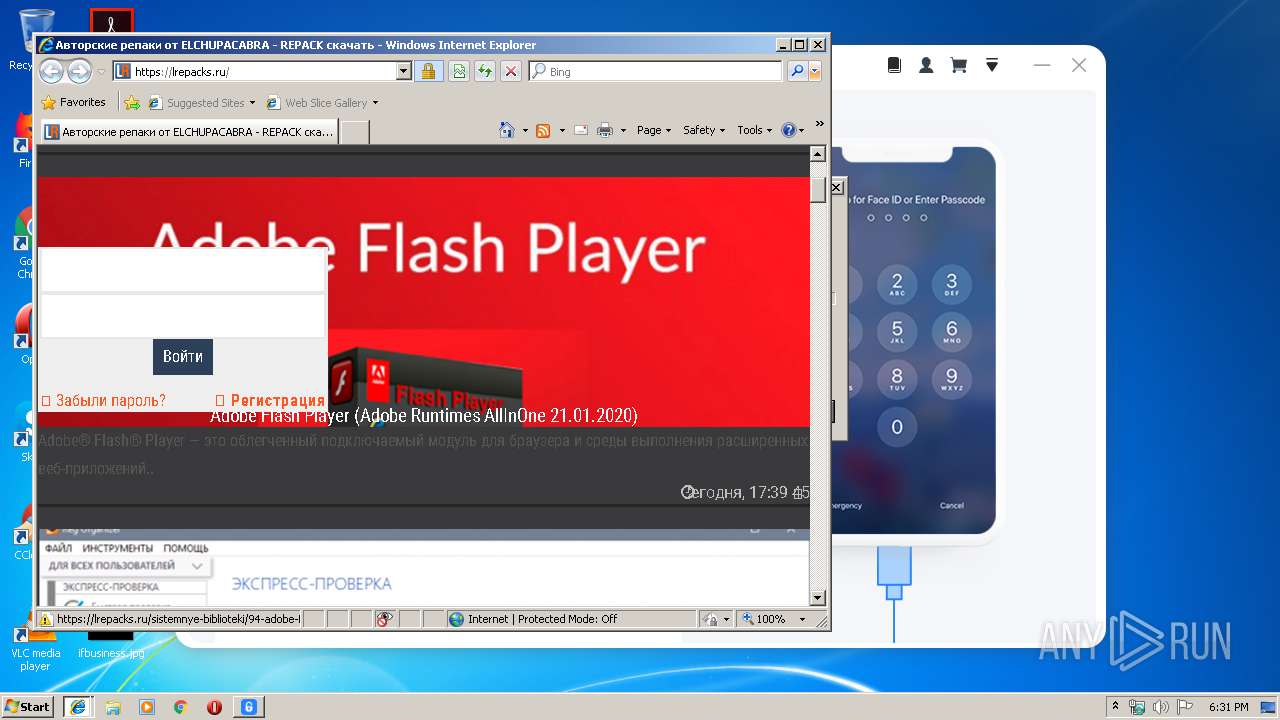
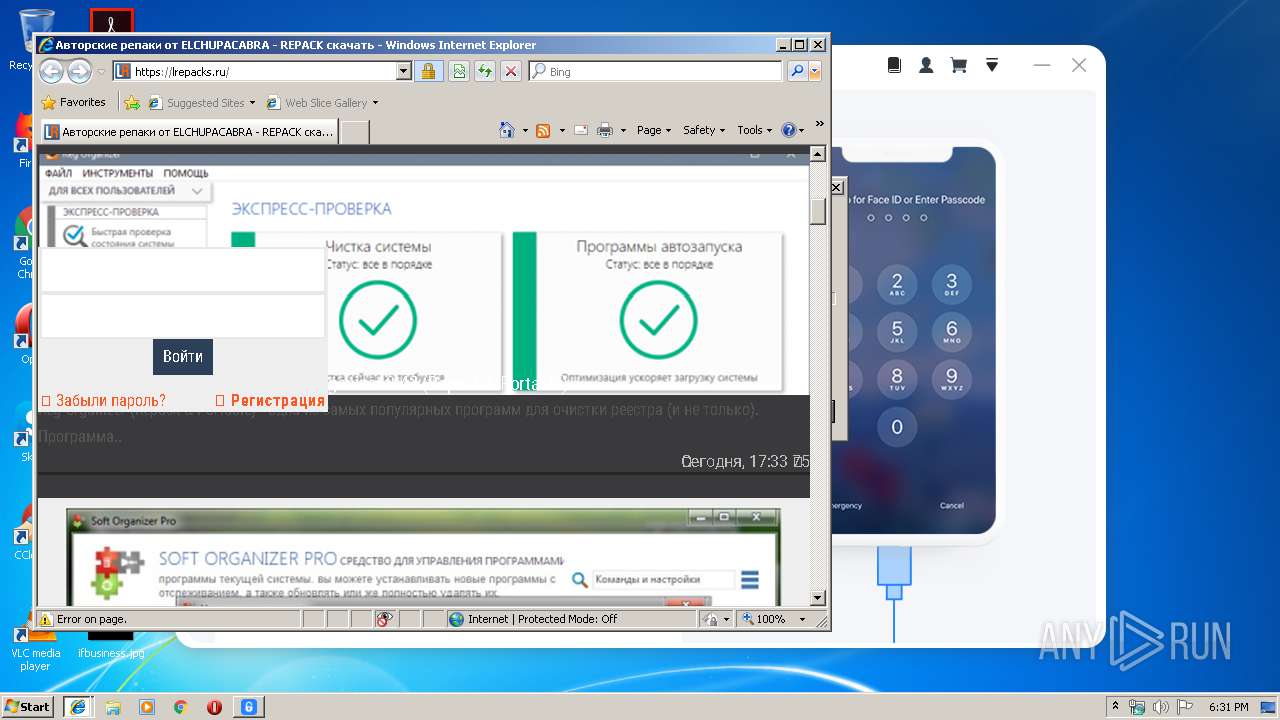
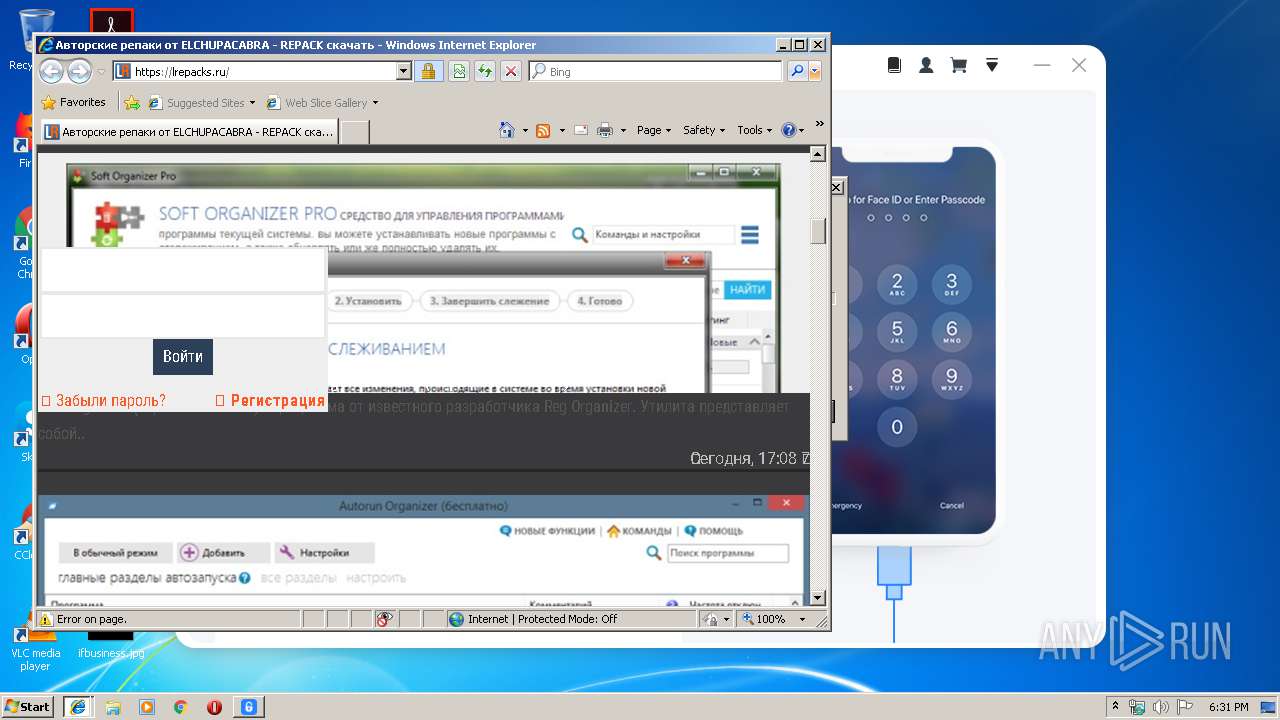
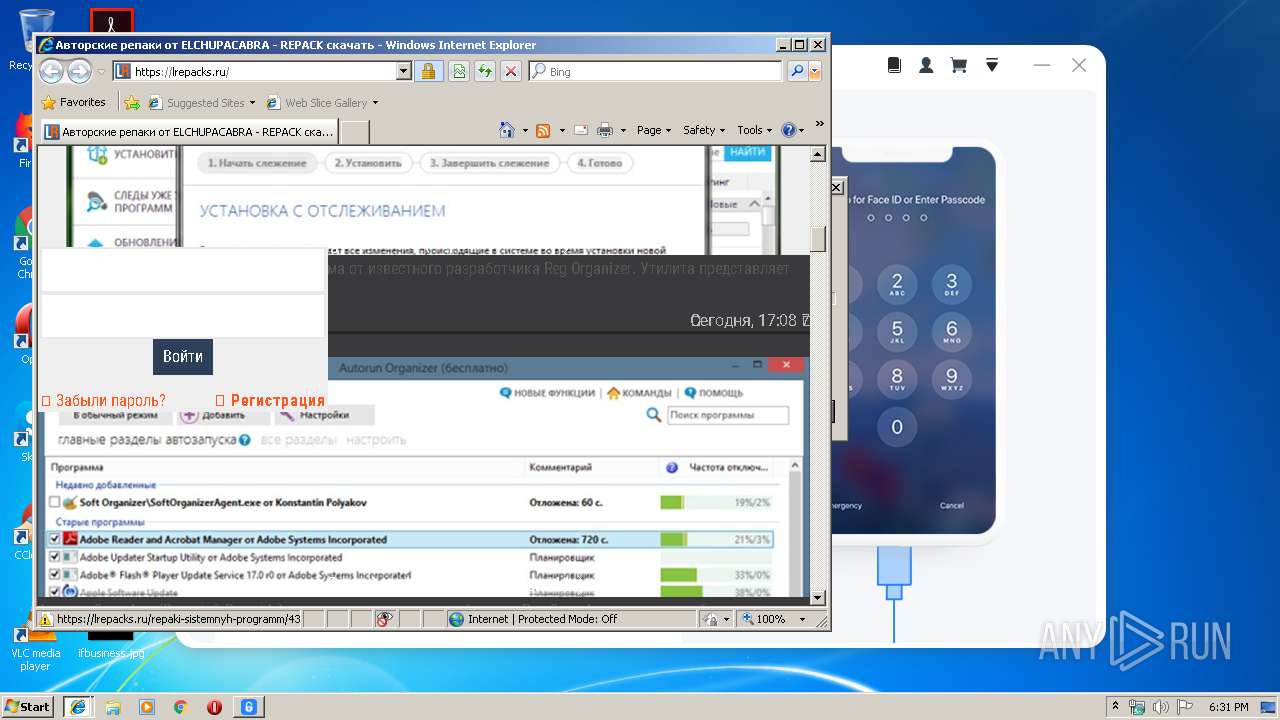
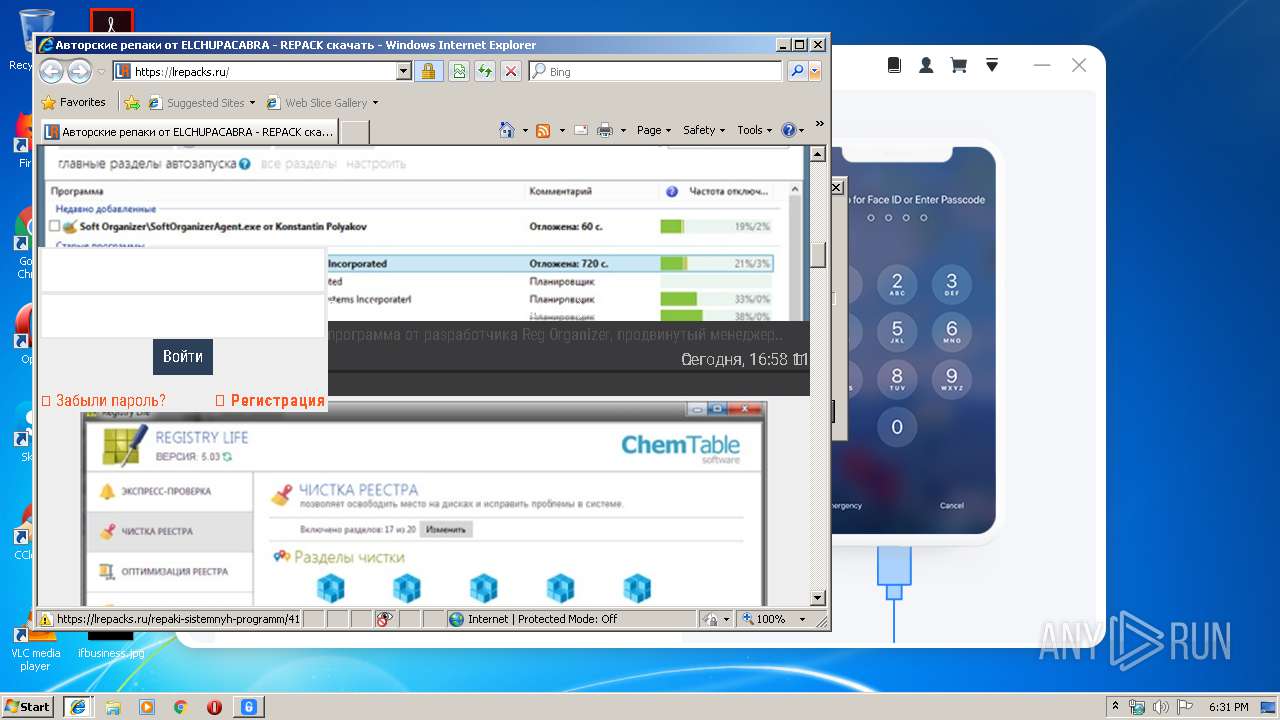
Starts Internet Explorer
- ApowerUnlock 1.0.1.8.tmp (PID: 1048)
Reads Environment values
- ApowerUnlock.exe (PID: 2120)
INFO
Application was dropped or rewritten from another process
- ApowerUnlock 1.0.1.8.tmp (PID: 1048)
Loads dropped or rewritten executable
- ApowerUnlock 1.0.1.8.tmp (PID: 1048)
Creates a software uninstall entry
- ApowerUnlock 1.0.1.8.tmp (PID: 1048)
Application launched itself
- iexplore.exe (PID: 2212)
Changes internet zones settings
- iexplore.exe (PID: 2212)
Reads internet explorer settings
- iexplore.exe (PID: 1576)
Reads Internet Cache Settings
- iexplore.exe (PID: 1576)
Creates files in the program directory
- ApowerUnlock 1.0.1.8.tmp (PID: 1048)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1576)
Reads settings of System Certificates
- iexplore.exe (PID: 2212)
- ApowerUnlock.exe (PID: 2120)
Creates files in the user directory
- iexplore.exe (PID: 1576)
Changes settings of System certificates
- iexplore.exe (PID: 1576)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 28160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c14 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.1.8 |
| ProductVersionNumber: | 1.0.1.8 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | lrepacks.ru |
| FileDescription: | ApowerUnlock Setup |
| FileVersion: | 1.0.1.8.0 |
| LegalCopyright: | |
| ProductName: | ApowerUnlock |
| ProductVersion: | 1.0.1.8 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | lrepacks.ru |
| FileDescription: | ApowerUnlock Setup |
| FileVersion: | 1.0.1.8.0 |
| LegalCopyright: | - |
| ProductName: | ApowerUnlock |
| ProductVersion: | 1.0.1.8 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009338 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55605 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73918 |
BSS | 0x0000C000 | 0x00000E8C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B0 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00005D80 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.79679 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.15342 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.65872 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.13564 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.38097 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
48
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1048 | "C:\Users\admin\AppData\Local\Temp\is-86ODF.tmp\ApowerUnlock 1.0.1.8.tmp" /SL5="$5012C,14563528,67072,C:\Users\admin\AppData\Local\Temp\ApowerUnlock 1.0.1.8.exe" | C:\Users\admin\AppData\Local\Temp\is-86ODF.tmp\ApowerUnlock 1.0.1.8.tmp | ApowerUnlock 1.0.1.8.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2212 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2004 | "C:\Windows\regedit.exe" /S "C:\Users\admin\AppData\Local\Temp\settings.reg" | C:\Windows\regedit.exe | ApowerUnlock 1.0.1.8.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
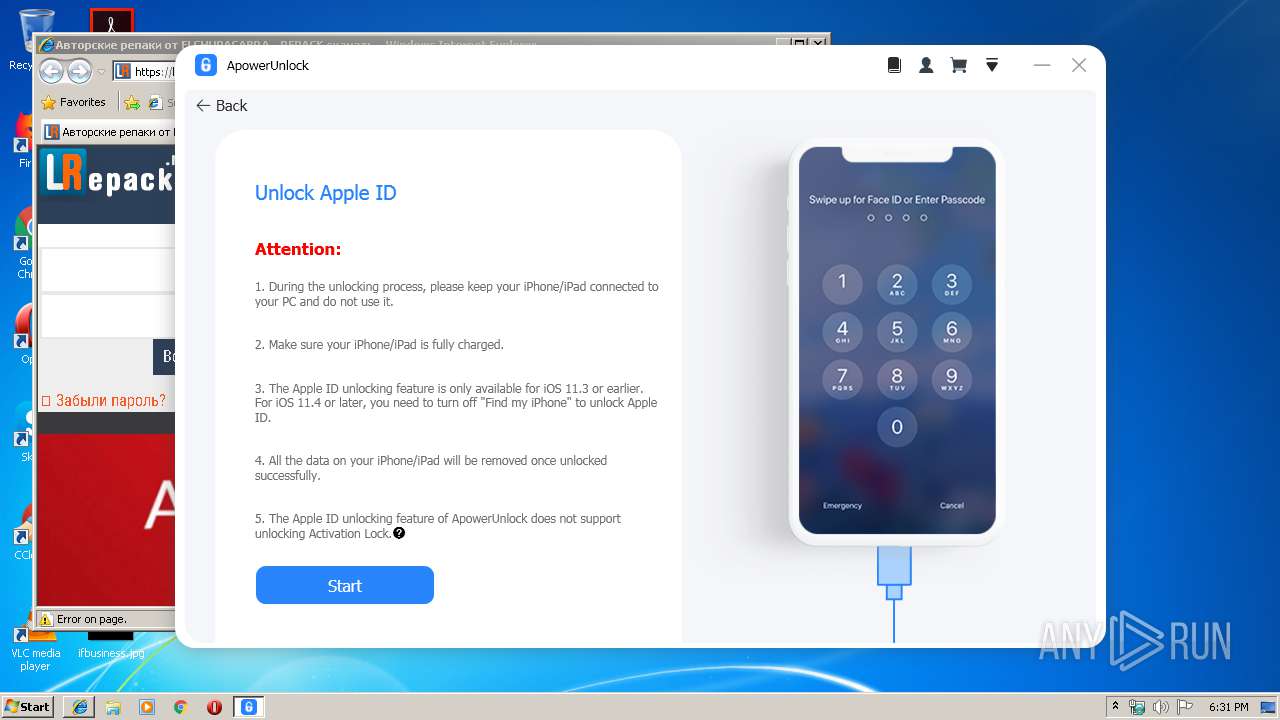
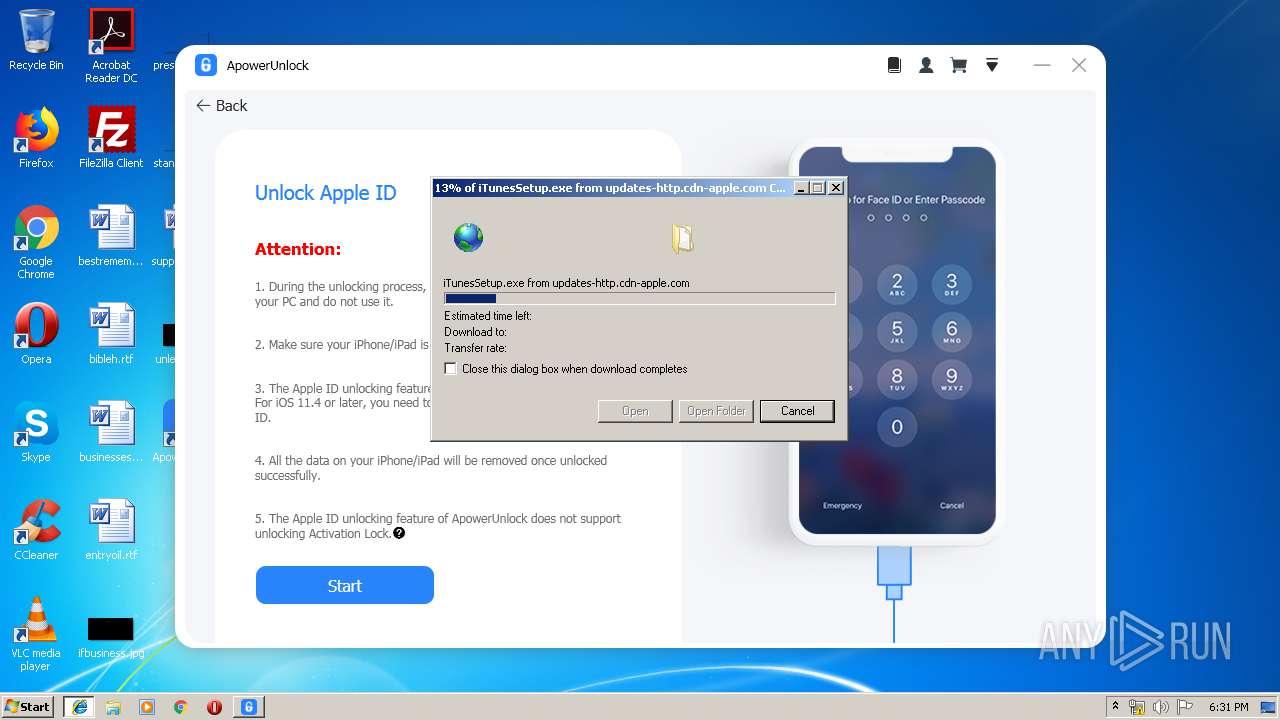
| 2120 | "C:\Program Files\Apowersoft\ApowerUnlock\ApowerUnlock.exe" | C:\Program Files\Apowersoft\ApowerUnlock\ApowerUnlock.exe | ApowerUnlock 1.0.1.8.tmp | ||||||||||||
User: admin Company: Apowersoft Integrity Level: HIGH Description: ApowerUnlock Exit code: 0 Version: 1.0.1.8 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | ApowerUnlock 1.0.1.8.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2212 CREDAT:14339 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | "C:\Users\admin\AppData\Local\Temp\Apowersoft.CommUtilities\7z.exe" x -y -o"C:\Users\admin\AppData\Roaming\Apowersoft\ApowerUnlock\data\PurchaseWebResource" "C:\Users\admin\AppData\Local\Temp\Apowersoft.CommUtilities\64c379fdf9f24613f9738a84f431dd80.zip" | C:\Users\admin\AppData\Local\Temp\Apowersoft.CommUtilities\7z.exe | — | ApowerUnlock.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\AppData\Local\Temp\ApowerUnlock 1.0.1.8.exe" | C:\Users\admin\AppData\Local\Temp\ApowerUnlock 1.0.1.8.exe | explorer.exe | ||||||||||||
User: admin Company: lrepacks.ru Integrity Level: HIGH Description: ApowerUnlock Setup Exit code: 0 Version: 1.0.1.8.0 Modules
| |||||||||||||||
| 3384 | "C:\Users\admin\AppData\Local\Temp\ApowerUnlock 1.0.1.8.exe" | C:\Users\admin\AppData\Local\Temp\ApowerUnlock 1.0.1.8.exe | — | explorer.exe | |||||||||||
User: admin Company: lrepacks.ru Integrity Level: MEDIUM Description: ApowerUnlock Setup Exit code: 3221226540 Version: 1.0.1.8.0 Modules
| |||||||||||||||
Total events
1 287
Read events
892
Write events
388
Delete events
7
Modification events
| (PID) Process: | (1048) ApowerUnlock 1.0.1.8.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 18040000A2A209E588D0D501 | |||
| (PID) Process: | (1048) ApowerUnlock 1.0.1.8.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 0F6DAEE46CCB1167C3E5F2028523F3568D292FE9C9295A6D7598F461B401EE07 | |||
| (PID) Process: | (1048) ApowerUnlock 1.0.1.8.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1048) ApowerUnlock 1.0.1.8.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Apowersoft\ApowerUnlock\Aliyun.Log.dll | |||
| (PID) Process: | (1048) ApowerUnlock 1.0.1.8.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: A907B837A3D06DE74776EB60549B920F2B815F16F9DBC6302095B661C7537DF5 | |||
| (PID) Process: | (1048) ApowerUnlock 1.0.1.8.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Lsa\FipsAlgorithmPolicy |
| Operation: | delete value | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (1048) ApowerUnlock 1.0.1.8.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Lsa\FipsAlgorithmPolicy |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (1048) ApowerUnlock 1.0.1.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\MAIN\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | ApowerUnlock.exe |
Value: 11001 | |||
| (PID) Process: | (1048) ApowerUnlock 1.0.1.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ApowerUnlock_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.1.ee2 (a) | |||
| (PID) Process: | (1048) ApowerUnlock 1.0.1.8.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ApowerUnlock_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Apowersoft\ApowerUnlock | |||
Executable files
77
Suspicious files
67
Text files
207
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1048 | ApowerUnlock 1.0.1.8.tmp | C:\Program Files\Apowersoft\ApowerUnlock\is-LU1ST.tmp | — | |
MD5:— | SHA256:— | |||
| 1048 | ApowerUnlock 1.0.1.8.tmp | C:\Program Files\Apowersoft\ApowerUnlock\is-APQ4G.tmp | — | |
MD5:— | SHA256:— | |||
| 1048 | ApowerUnlock 1.0.1.8.tmp | C:\Program Files\Apowersoft\ApowerUnlock\is-D6Q2K.tmp | — | |
MD5:— | SHA256:— | |||
| 1048 | ApowerUnlock 1.0.1.8.tmp | C:\Program Files\Apowersoft\ApowerUnlock\is-UJ3IJ.tmp | — | |
MD5:— | SHA256:— | |||
| 1048 | ApowerUnlock 1.0.1.8.tmp | C:\Program Files\Apowersoft\ApowerUnlock\is-7AC0K.tmp | — | |
MD5:— | SHA256:— | |||
| 1048 | ApowerUnlock 1.0.1.8.tmp | C:\Program Files\Apowersoft\ApowerUnlock\is-75QU4.tmp | — | |
MD5:— | SHA256:— | |||
| 1048 | ApowerUnlock 1.0.1.8.tmp | C:\Program Files\Apowersoft\ApowerUnlock\is-RI55P.tmp | — | |
MD5:— | SHA256:— | |||
| 1048 | ApowerUnlock 1.0.1.8.tmp | C:\Program Files\Apowersoft\ApowerUnlock\is-2QUH9.tmp | — | |
MD5:— | SHA256:— | |||
| 1048 | ApowerUnlock 1.0.1.8.tmp | C:\Program Files\Apowersoft\ApowerUnlock\is-DC454.tmp | — | |
MD5:— | SHA256:— | |||
| 1048 | ApowerUnlock 1.0.1.8.tmp | C:\Program Files\Apowersoft\ApowerUnlock\is-5UABI.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
21
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
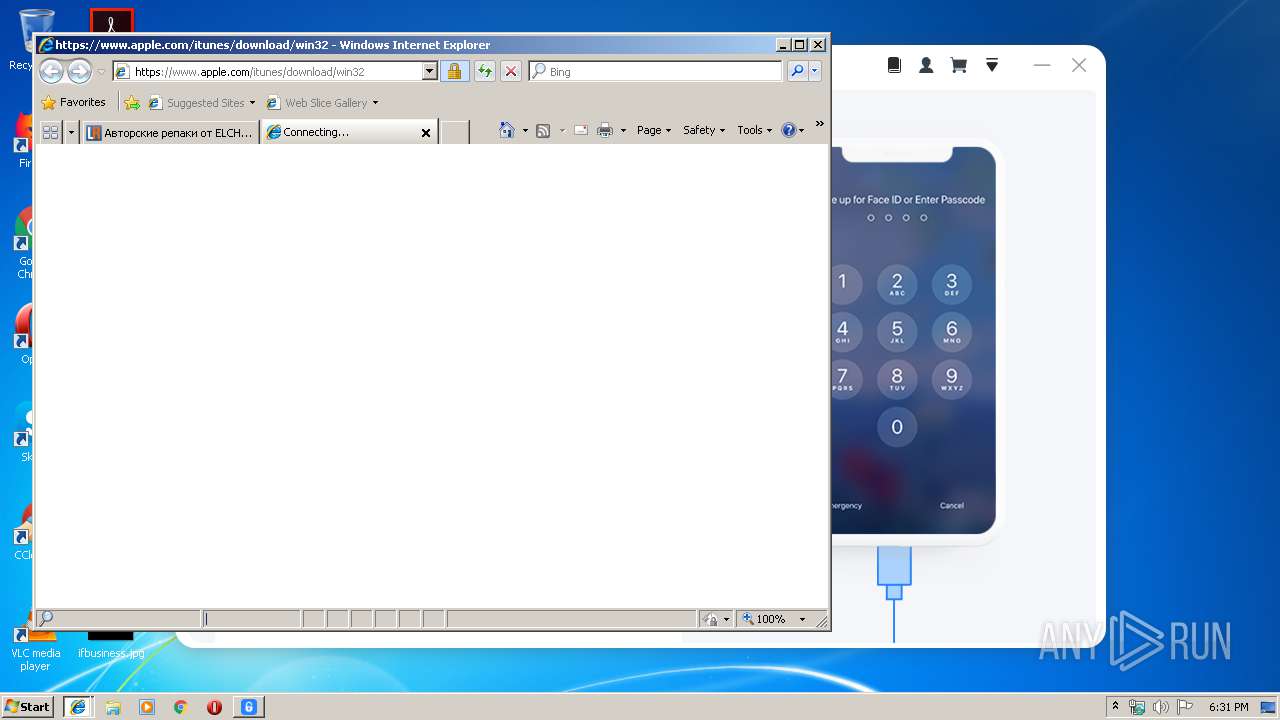
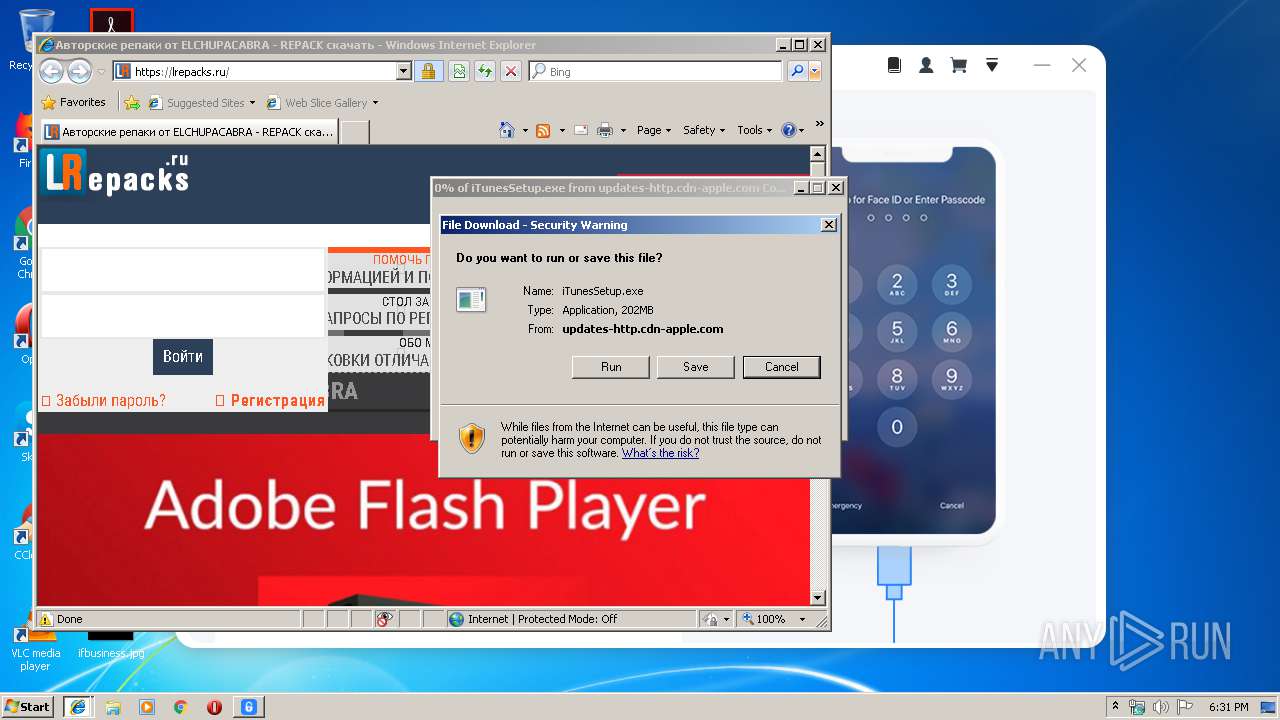
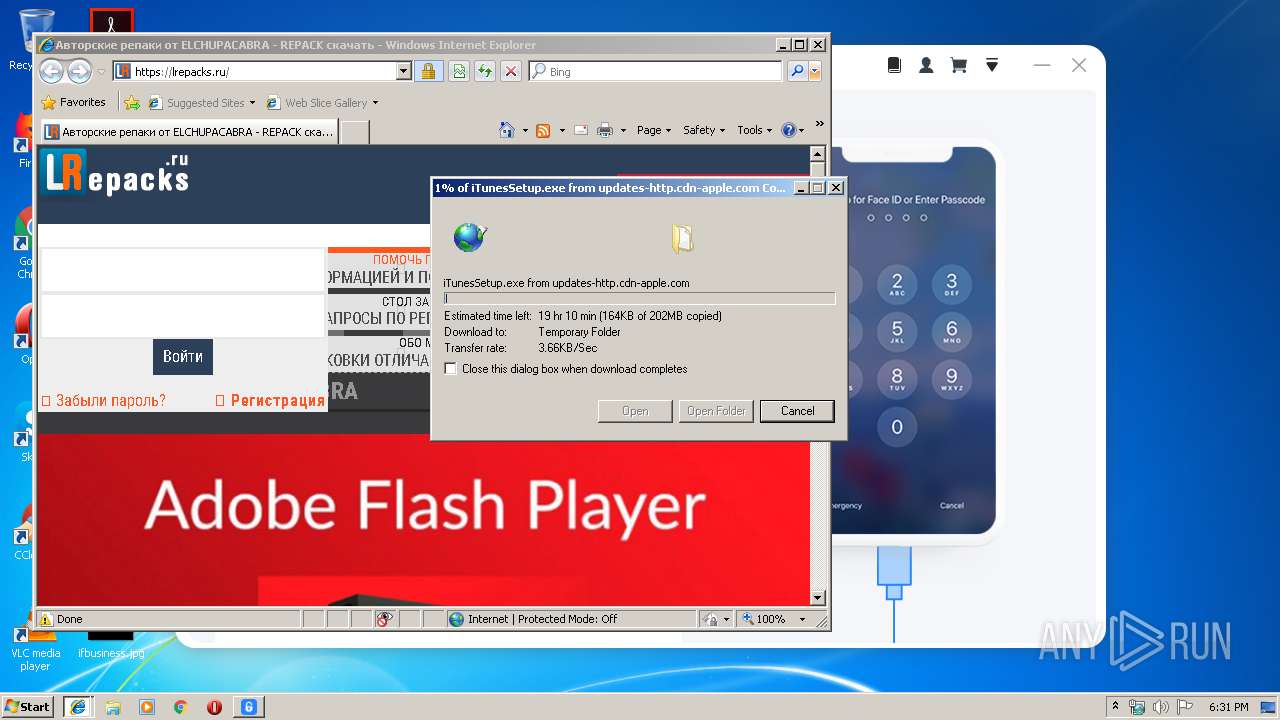
2484 | iexplore.exe | GET | — | 17.253.55.201:80 | http://updates-http.cdn-apple.com/2019/windows/061-62390-20191210-344B958C-1BAC-11EA-B424-5ECFC722D531/iTunesSetup.exe | US | — | — | whitelisted |
2212 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1576 | iexplore.exe | GET | 301 | 5.44.221.96:80 | http://lrepacks.ru/ | LV | html | 162 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | ApowerUnlock.exe | 47.91.201.11:443 | support.apowersoft.com | Alibaba (China) Technology Co., Ltd. | HK | suspicious |
1576 | iexplore.exe | 5.44.221.96:443 | lrepacks.ru | Camelhost Sia | LV | suspicious |
1576 | iexplore.exe | 104.24.104.241:443 | pagiwp.com | Cloudflare Inc | US | suspicious |
1576 | iexplore.exe | 88.212.201.210:443 | counter.yadro.ru | United Network LLC | RU | suspicious |
1576 | iexplore.exe | 172.217.18.174:443 | translate.google.com | Google Inc. | US | whitelisted |
1576 | iexplore.exe | 172.217.23.170:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
1576 | iexplore.exe | 87.250.251.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
1576 | iexplore.exe | 5.44.221.96:80 | lrepacks.ru | Camelhost Sia | LV | suspicious |
2212 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2212 | iexplore.exe | 5.44.221.96:443 | lrepacks.ru | Camelhost Sia | LV | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lrepacks.ru |
| whitelisted |
www.bing.com |
| whitelisted |
support.apowersoft.com |
| suspicious |
pagiwp.com |
| whitelisted |
translate.google.com |
| whitelisted |
counter.yadro.ru |
| whitelisted |
serconius.com |
| unknown |
translate.googleapis.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
www.apple.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2484 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
regedit.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|