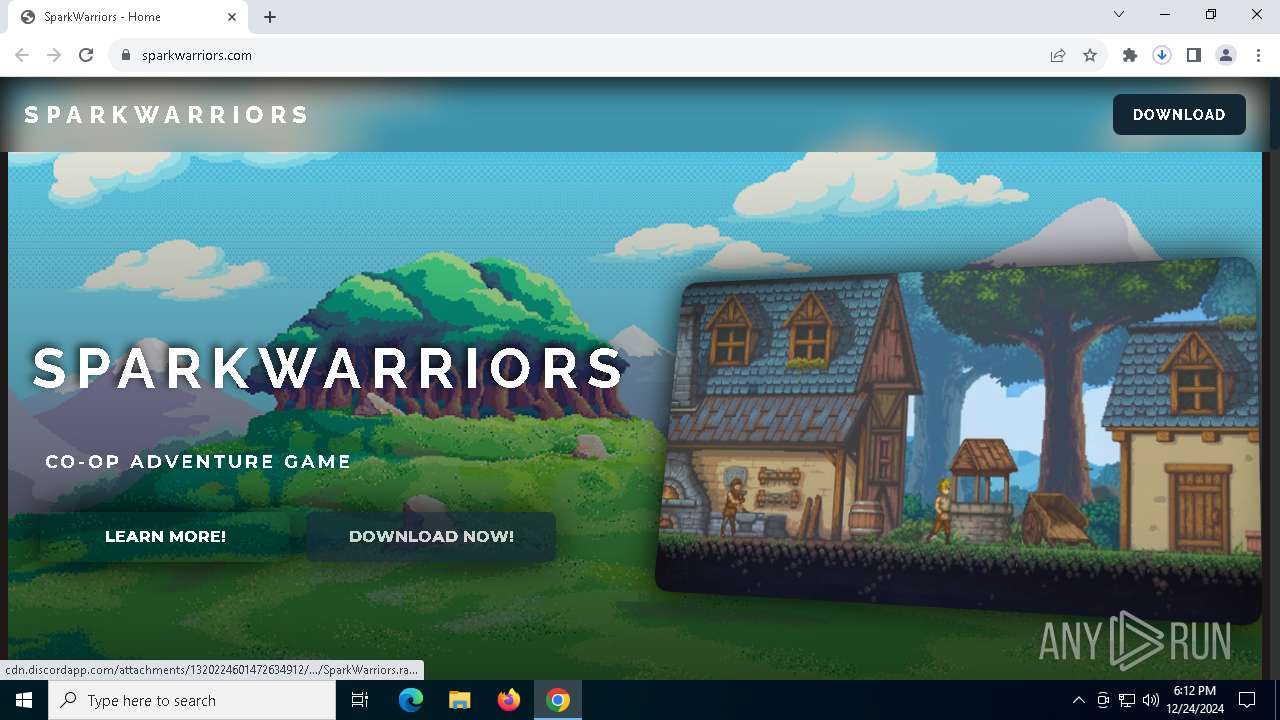
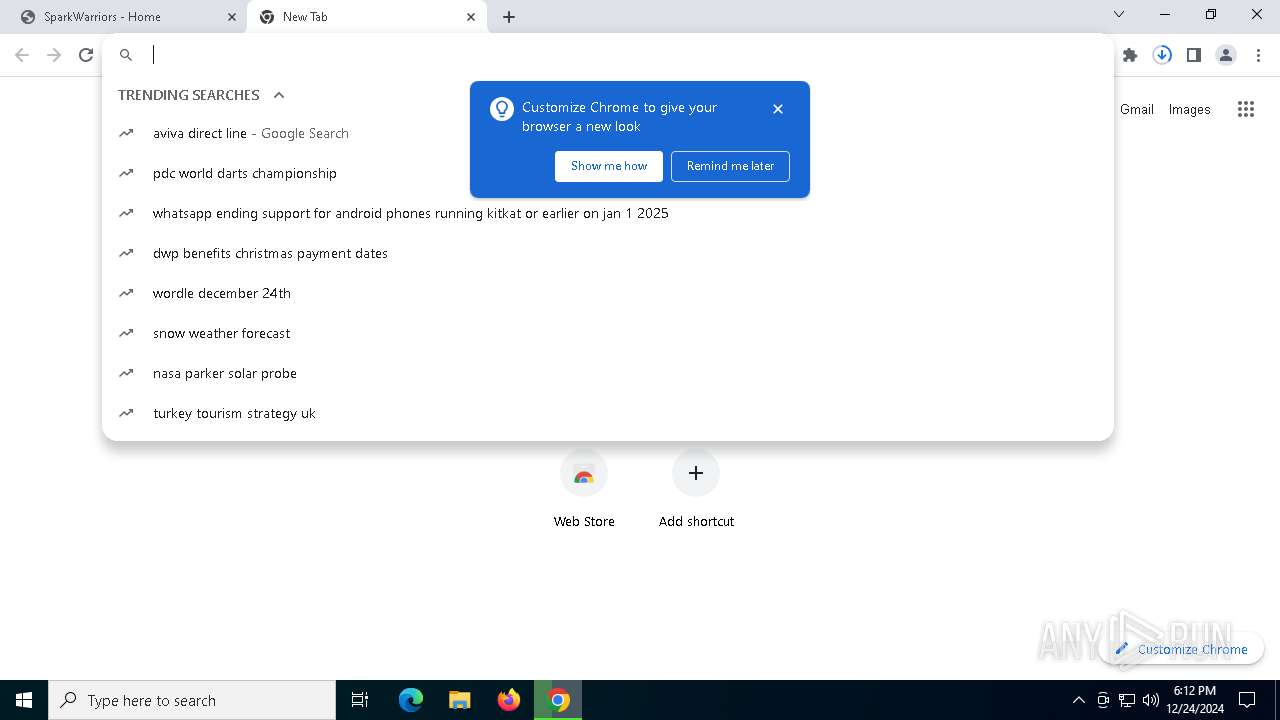
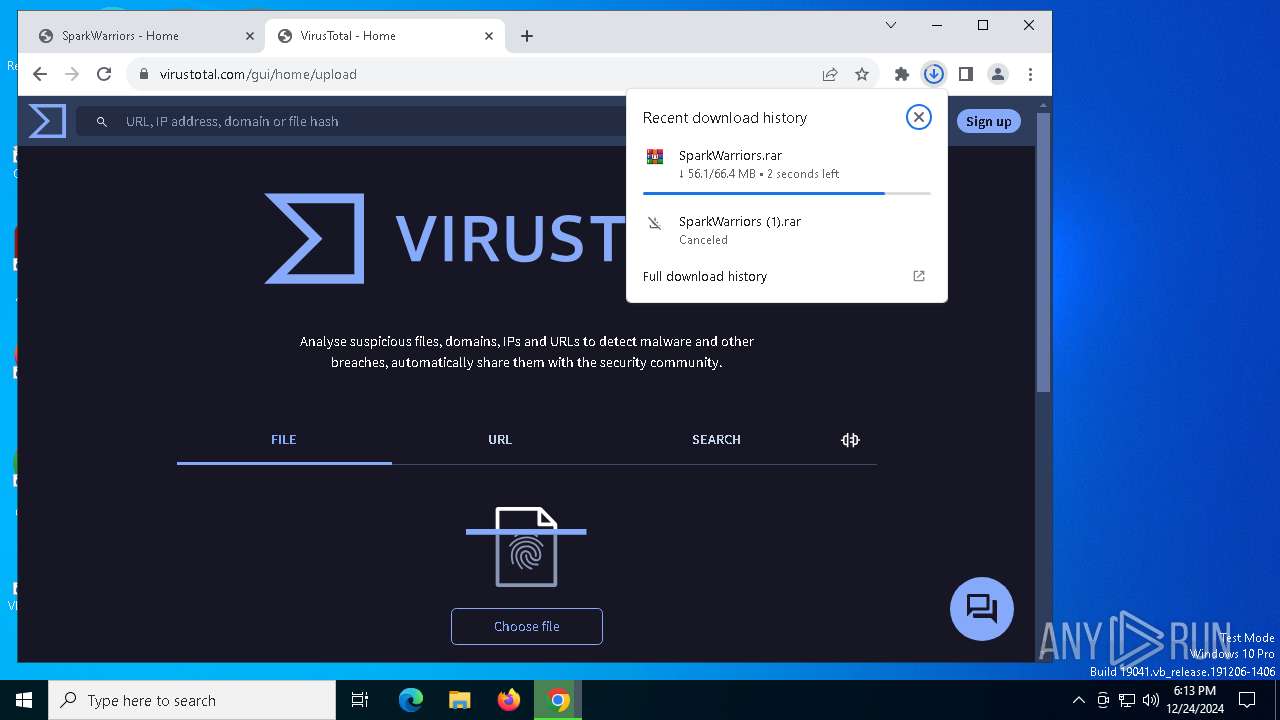
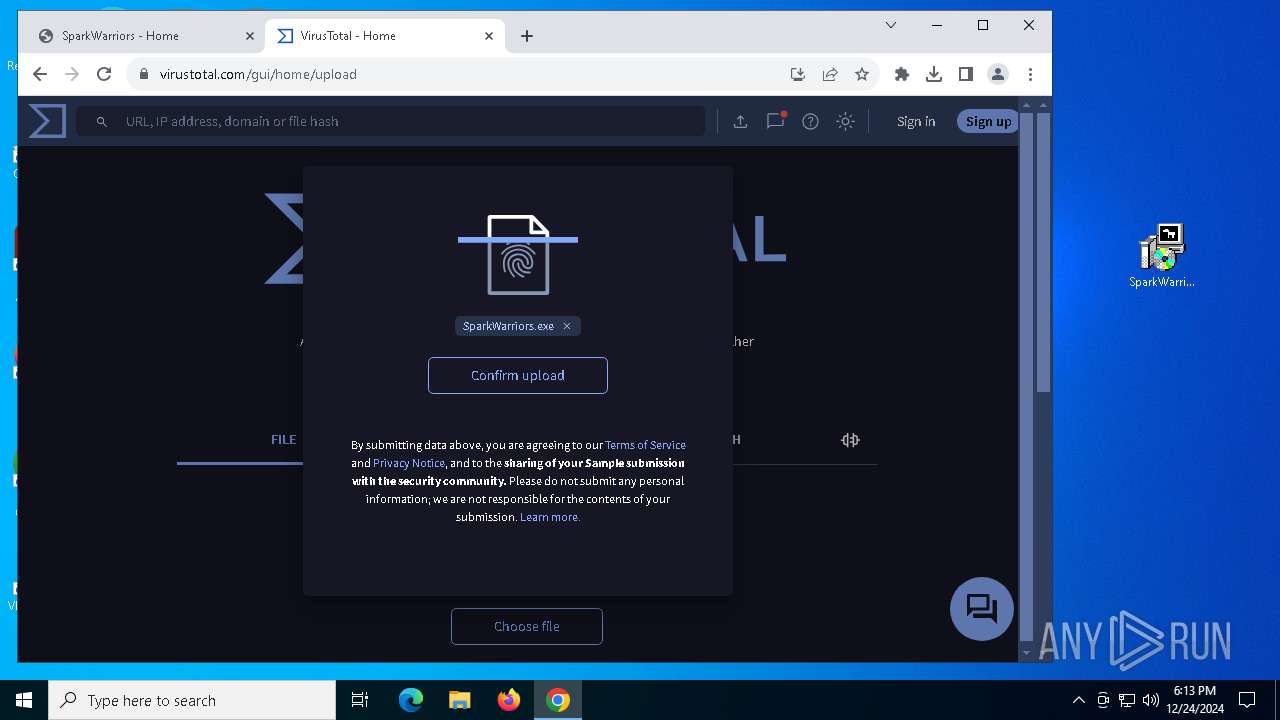
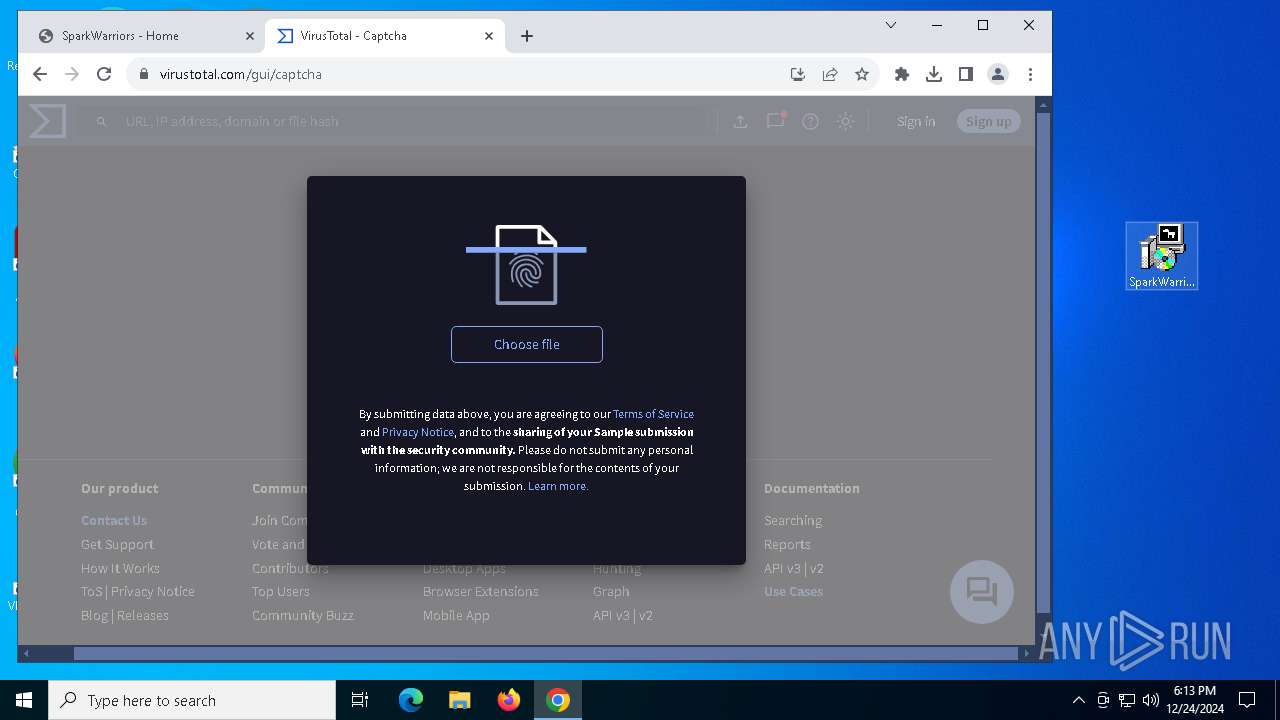
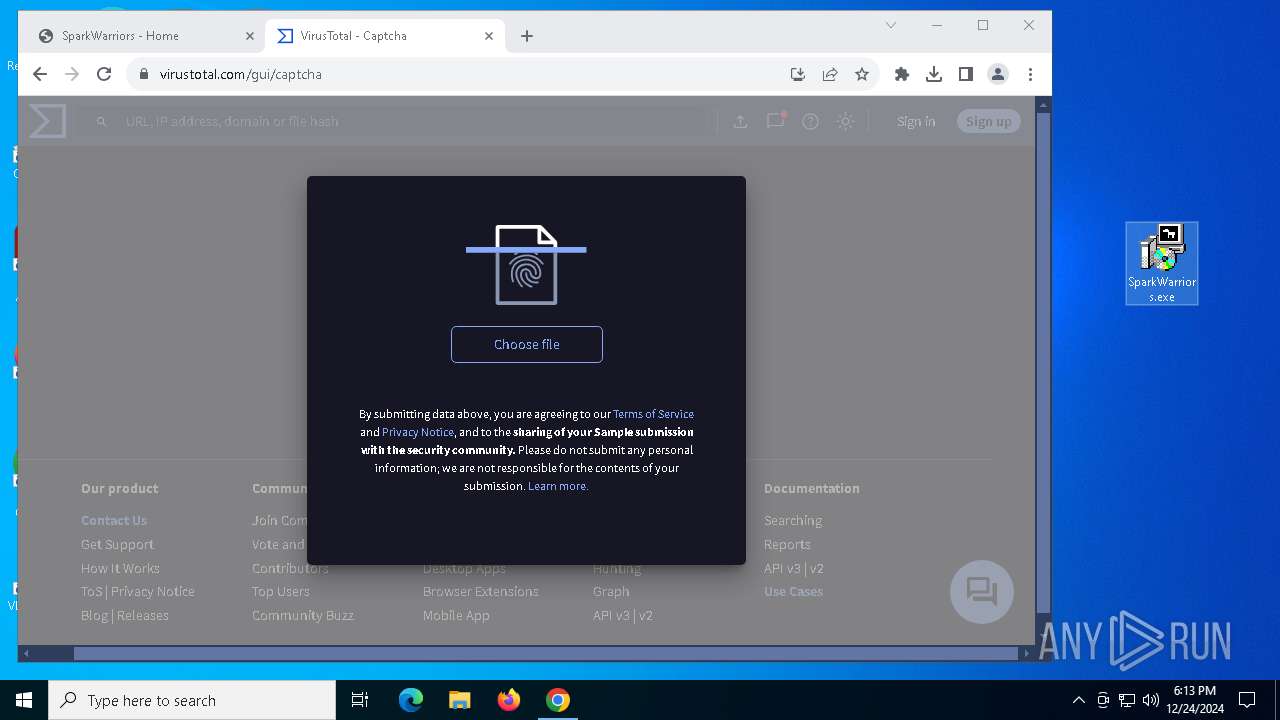
| URL: | https://www.sparkwarriors.com/ |
| Full analysis: | https://app.any.run/tasks/d3dbff15-d43b-4132-b878-13361989ab5b |
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2024, 18:12:33 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FF6C7063416B3DA47983EC1AAAA352EF |
| SHA1: | 2C11F7F9F6119CF499667209F1722F253FF070CC |
| SHA256: | 974A09AFB925E97CA539D73BC0312352A3DF6BF0504238E311151BFDAA4E9B38 |
| SSDEEP: | 3:N8DSLOnXCn:2OLOnXC |
MALICIOUS
Actions looks like stealing of personal data
- SparkWarriors.exe (PID: 6012)
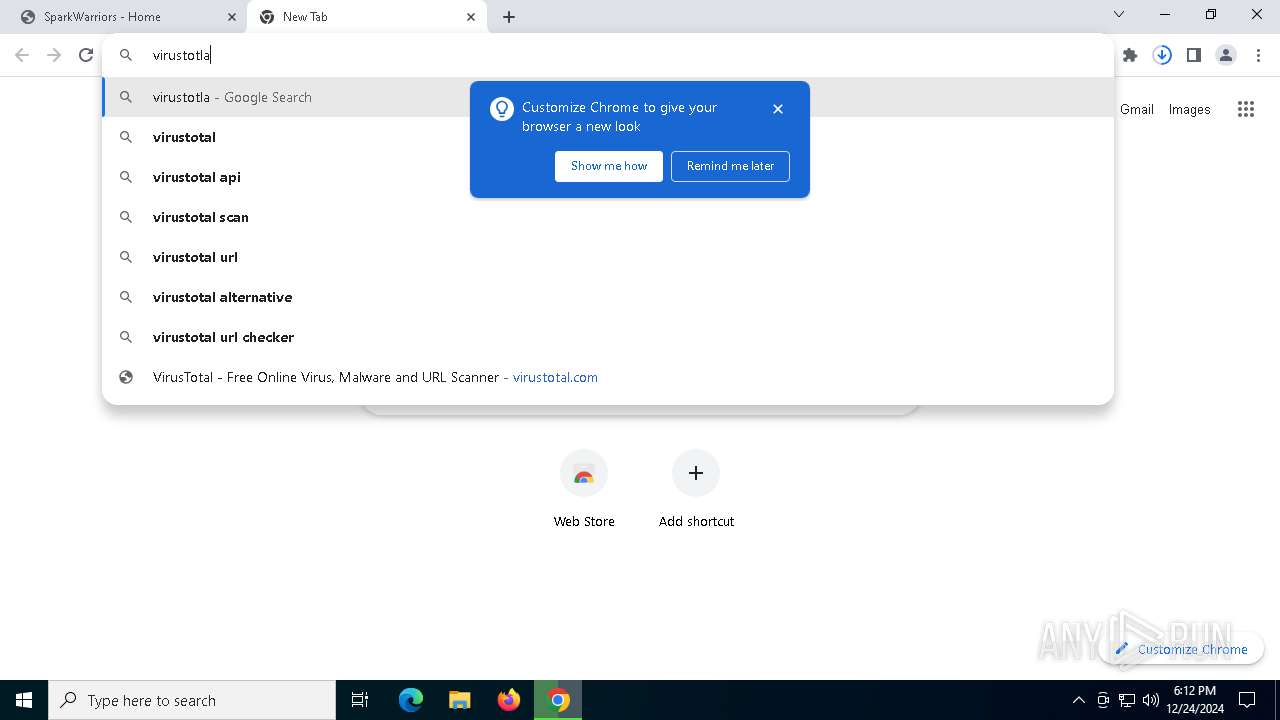
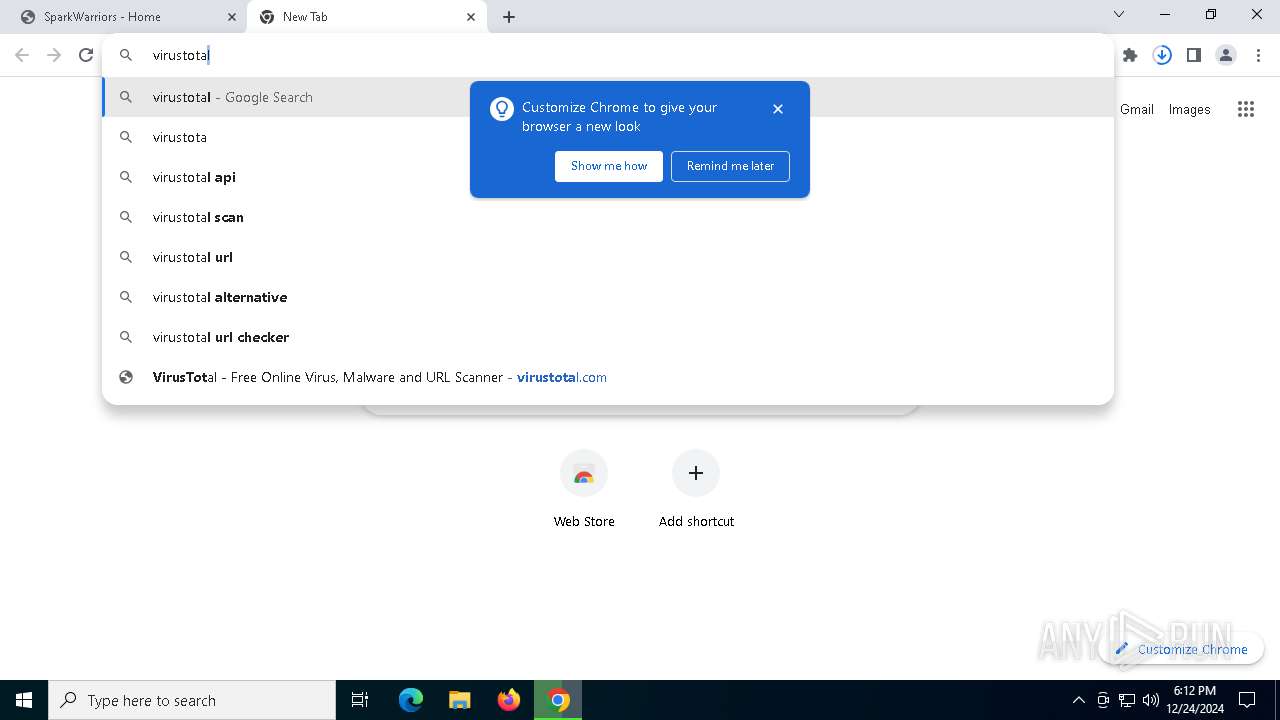
Steals credentials from Web Browsers
- SparkWarriors.exe (PID: 6012)
SUSPICIOUS
Reads security settings of Internet Explorer
- SparkWarriors.exe (PID: 5304)
Application launched itself
- SparkWarriors.exe (PID: 6012)
Process drops legitimate windows executable
- SparkWarriors.exe (PID: 5304)
Drops 7-zip archiver for unpacking
- SparkWarriors.exe (PID: 5304)
The process creates files with name similar to system file names
- SparkWarriors.exe (PID: 5304)
Starts CMD.EXE for commands execution
- SparkWarriors.exe (PID: 6012)
Uses WEVTUTIL.EXE to change log configuration
- cmd.exe (PID: 1804)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1344)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 6300)
Get information on the list of running processes
- SparkWarriors.exe (PID: 6012)
- cmd.exe (PID: 828)
- cmd.exe (PID: 4516)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 1596)
- cmd.exe (PID: 3564)
- cmd.exe (PID: 6856)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 936)
- cmd.exe (PID: 3640)
- cmd.exe (PID: 2996)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 6764)
- cmd.exe (PID: 2356)
- cmd.exe (PID: 7012)
- cmd.exe (PID: 648)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 4328)
- cmd.exe (PID: 5628)
- cmd.exe (PID: 6832)
- cmd.exe (PID: 6920)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 4264)
- cmd.exe (PID: 4724)
- cmd.exe (PID: 6676)
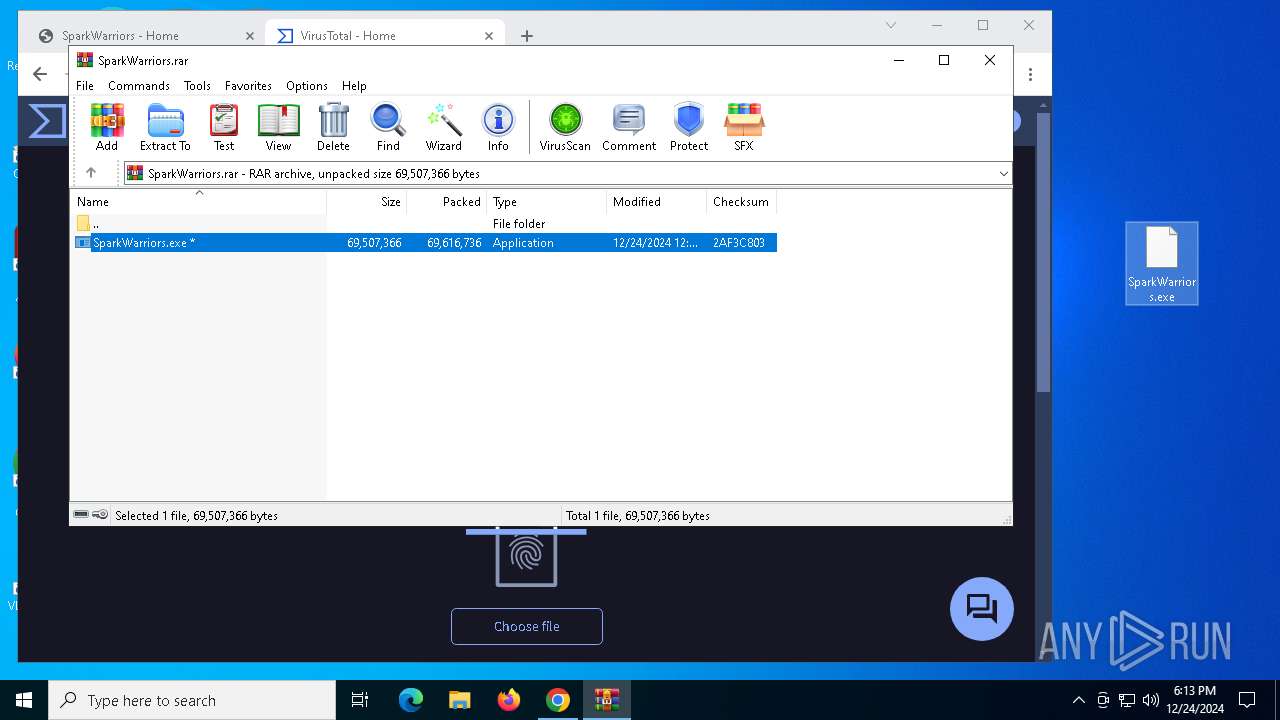
Executable content was dropped or overwritten
- SparkWarriors.exe (PID: 5304)
Malware-specific behavior (creating "System.dll" in Temp)
- SparkWarriors.exe (PID: 5304)
INFO
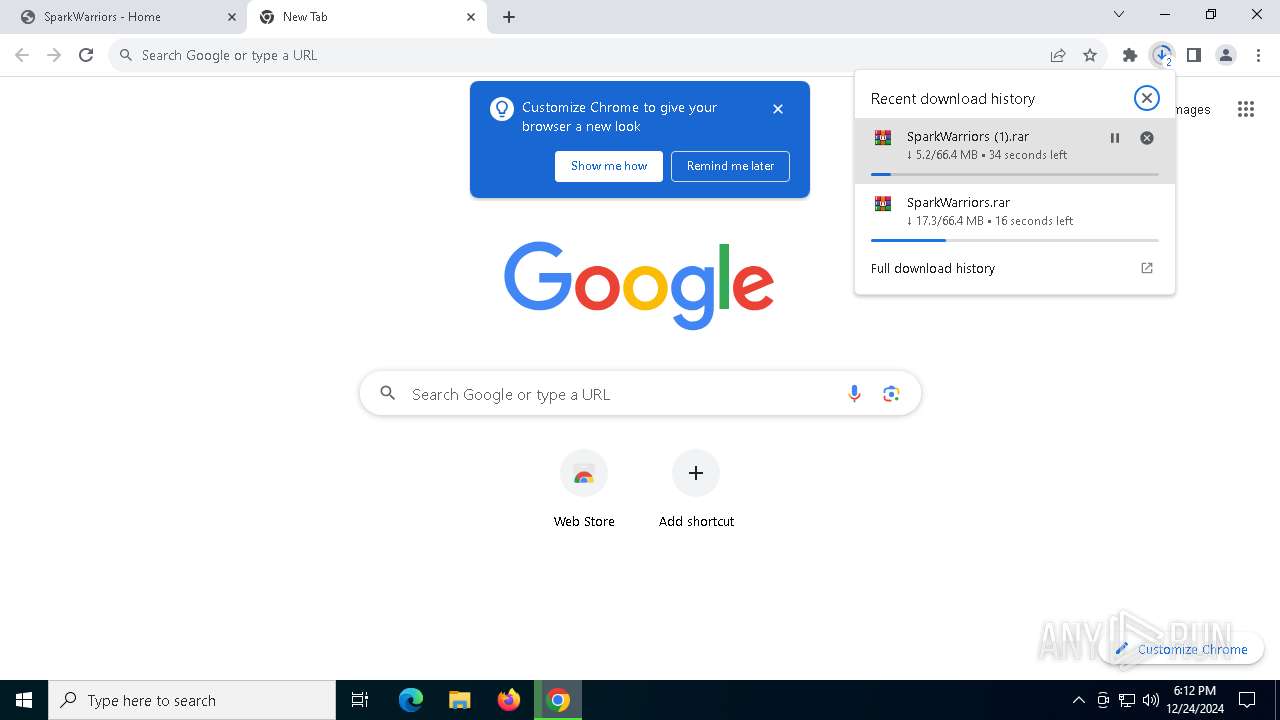
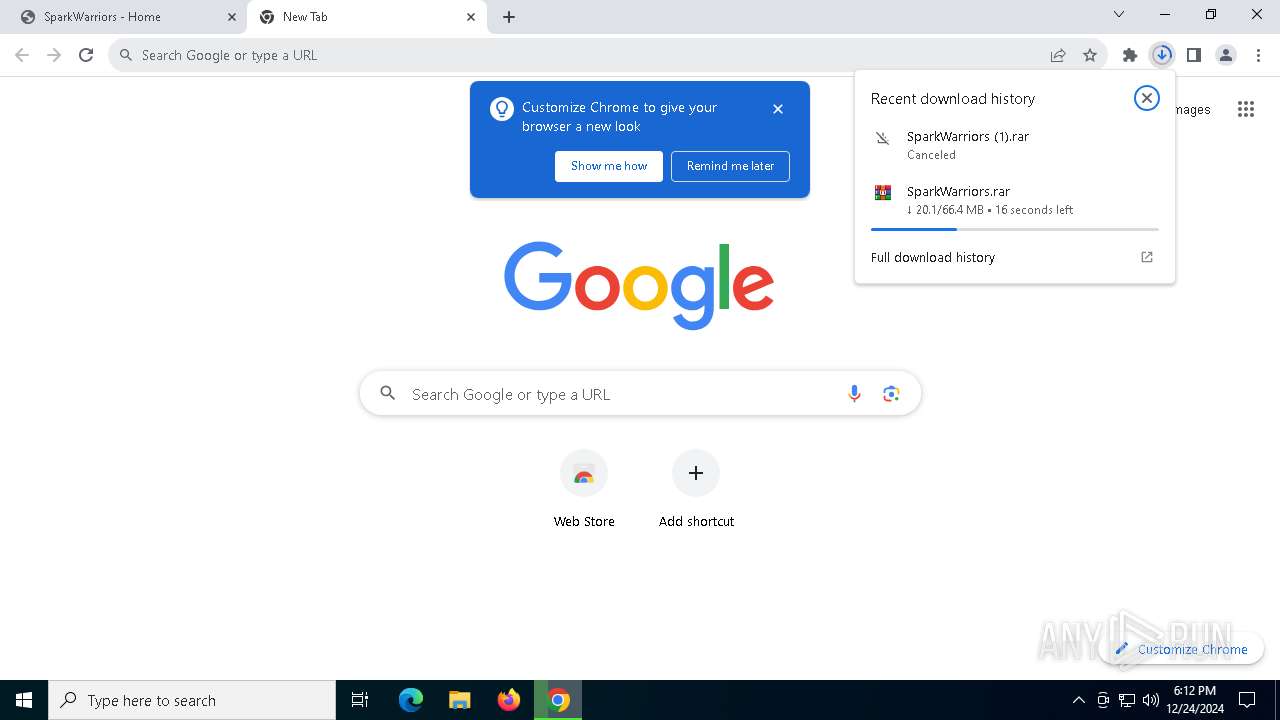
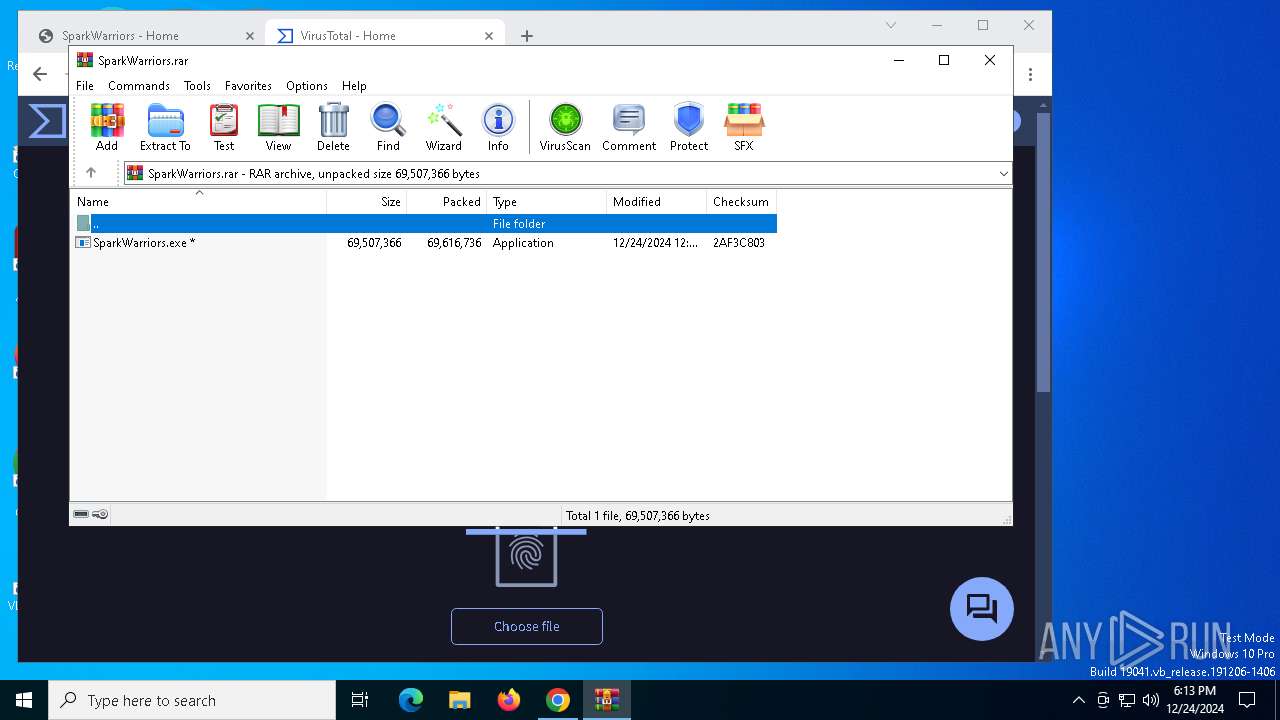
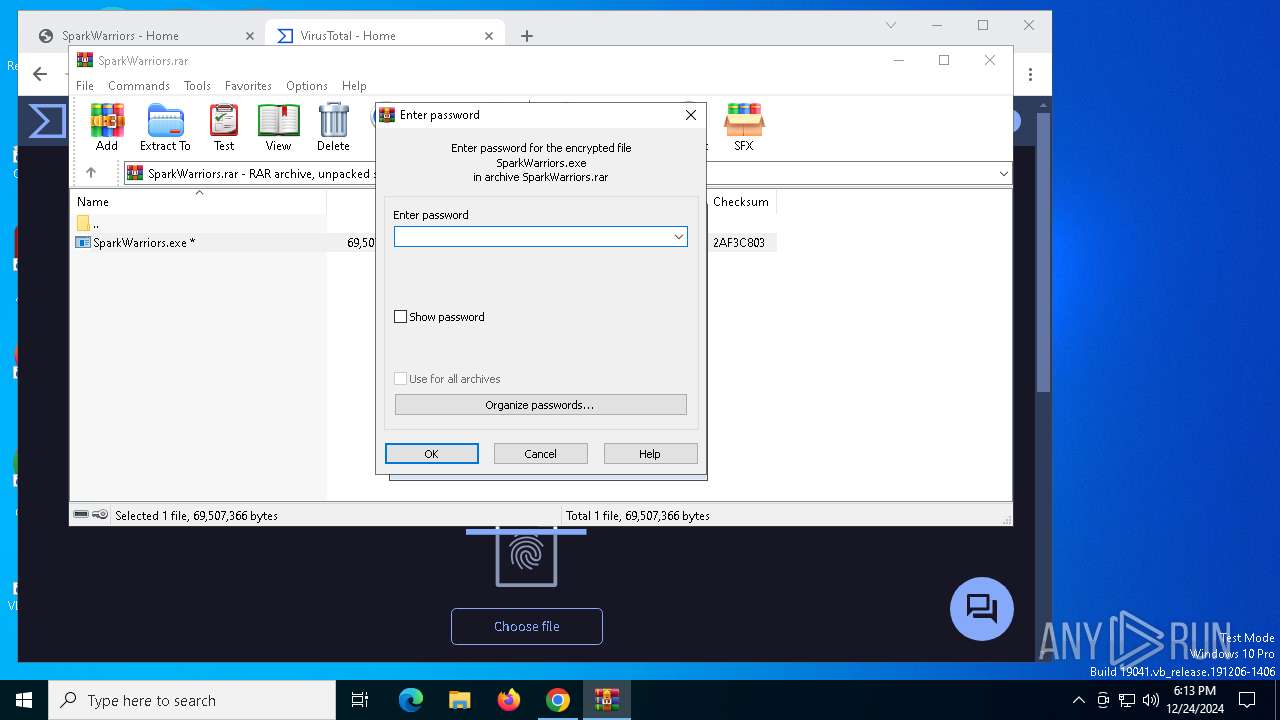
The process uses the downloaded file
- chrome.exe (PID: 5992)
- WinRAR.exe (PID: 716)
- chrome.exe (PID: 6404)
Application launched itself
- chrome.exe (PID: 6404)
- chrome.exe (PID: 7064)
- msedge.exe (PID: 648)
Reads the computer name
- SparkWarriors.exe (PID: 6012)
- SparkWarriors.exe (PID: 5304)
- SparkWarriors.exe (PID: 1796)
- SparkWarriors.exe (PID: 2144)
Attempting to use instant messaging service
- chrome.exe (PID: 6872)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6404)
Checks supported languages
- SparkWarriors.exe (PID: 5304)
- SparkWarriors.exe (PID: 1796)
- SparkWarriors.exe (PID: 6012)
- SparkWarriors.exe (PID: 2144)
Reads Environment values
- SparkWarriors.exe (PID: 6012)
Reads product name
- SparkWarriors.exe (PID: 6012)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6300)
Reads the machine GUID from the registry
- SparkWarriors.exe (PID: 6012)
Checks proxy server information
- SparkWarriors.exe (PID: 6012)
Sends debugging messages
- chrome.exe (PID: 7064)
Manual execution by a user
- SparkWarriors.exe (PID: 5304)
Create files in a temporary directory
- SparkWarriors.exe (PID: 5304)
The sample compiled with english language support
- SparkWarriors.exe (PID: 5304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
246
Monitored processes
120
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 648 | C:\WINDOWS\system32\cmd.exe /d /s /c "taskkill /PID 4328 /T /F" | C:\Windows\System32\cmd.exe | — | SparkWarriors.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 648 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --restore-last-session --remote-allow-origins=* --headless --profile-directory=Default "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --no-experiments --disable-background-networking --allow-no-sandbox-job --disable-extensions --disable-gpu --disable-webgl --disable-client-side-phishing-detection --disable-background-timer-throttling --disable-3d-apis --disable-notifications --disable-infobars --remote-debugging-port=5626 --remote-debugging-address=127.0.0.1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | SparkWarriors.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 716 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\SparkWarriors.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=5248 --field-trial-handle=1908,i,15089822143546224674,1466129883770448517,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 828 | C:\WINDOWS\system32\cmd.exe /d /s /c "tasklist" | C:\Windows\System32\cmd.exe | — | SparkWarriors.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | C:\WINDOWS\system32\cmd.exe /d /s /c "taskkill /PID 6404 /T /F" | C:\Windows\System32\cmd.exe | — | SparkWarriors.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | C:\WINDOWS\system32\cmd.exe /d /s /c "wmic csproduct get UUID" | C:\Windows\System32\cmd.exe | — | SparkWarriors.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 916
Read events
12 883
Write events
33
Delete events
0
Modification events
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (5992) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000002664E47A2F56DB01 | |||
| (PID) Process: | (6404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
Executable files
21
Suspicious files
202
Text files
97
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF13646a.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF13646a.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF13646a.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF13647a.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF13647a.TMP | — | |
MD5:— | SHA256:— | |||
| 6404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF13646a.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
100
DNS requests
107
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6620 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1144 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1144 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6404 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.sparkwarriors.com |
| unknown |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6872 | chrome.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6872 | chrome.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6872 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6872 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Google\Chrome\User Data directory exists )
|