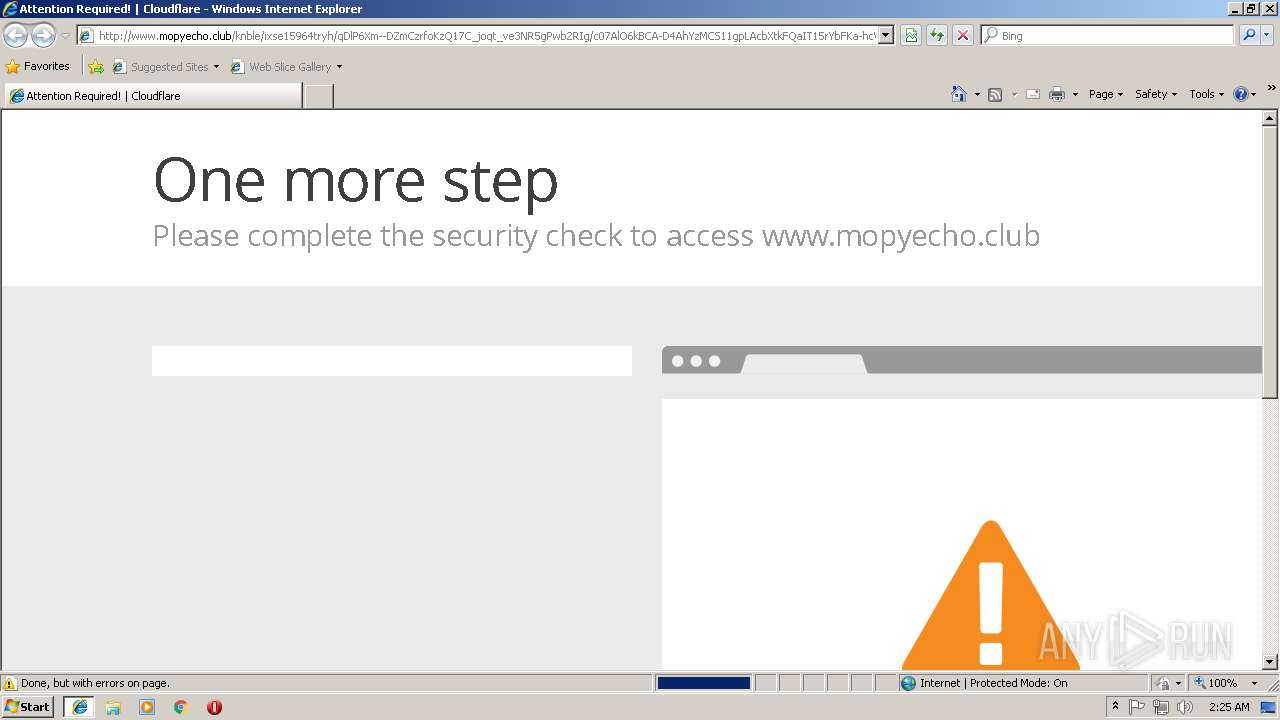
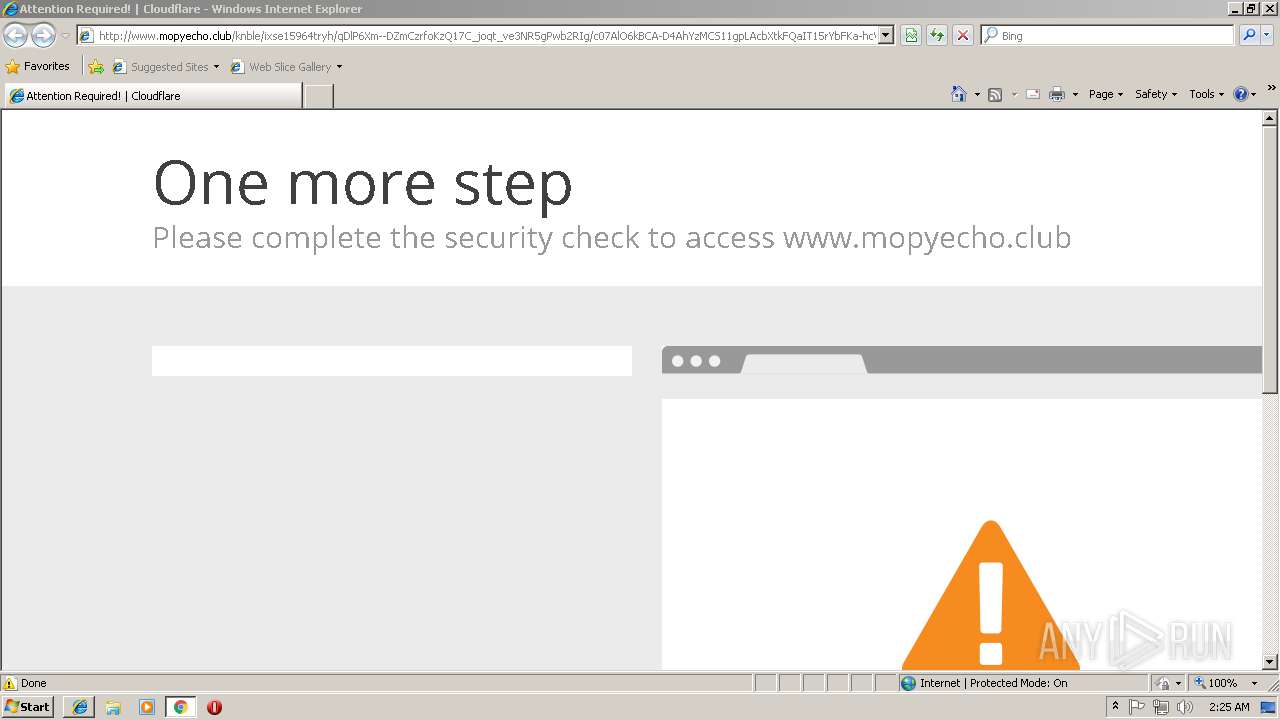
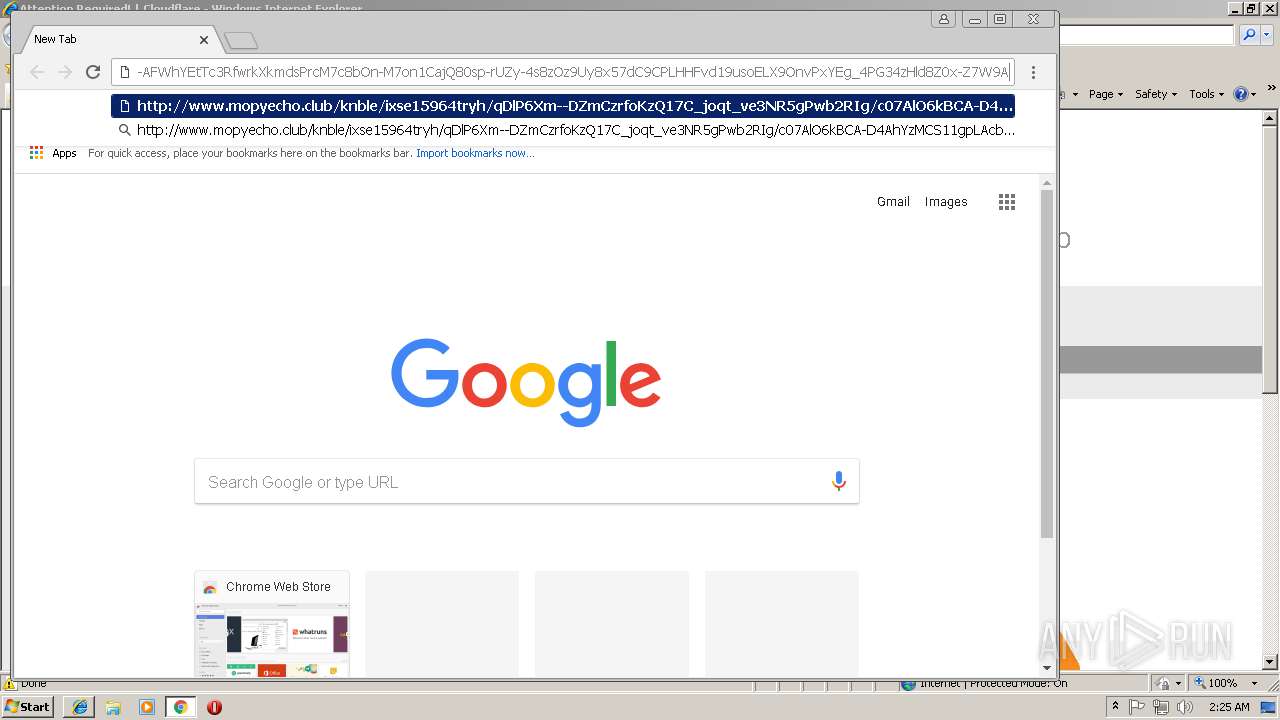
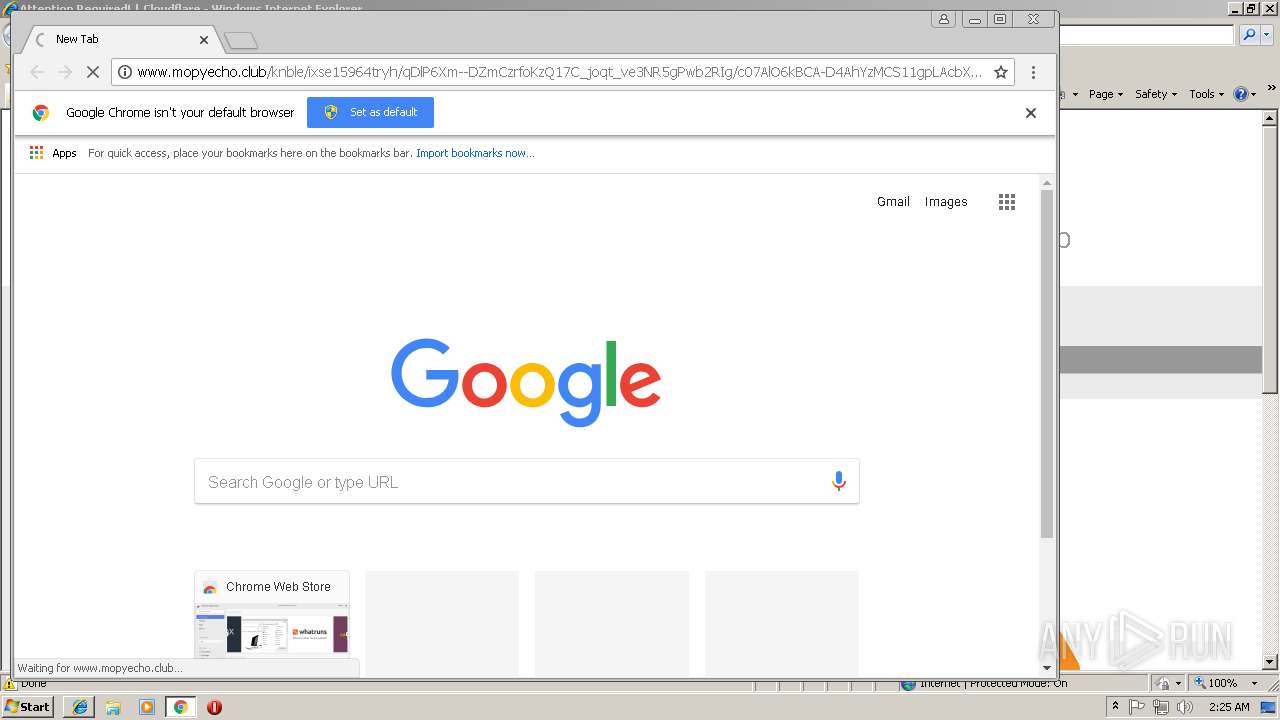
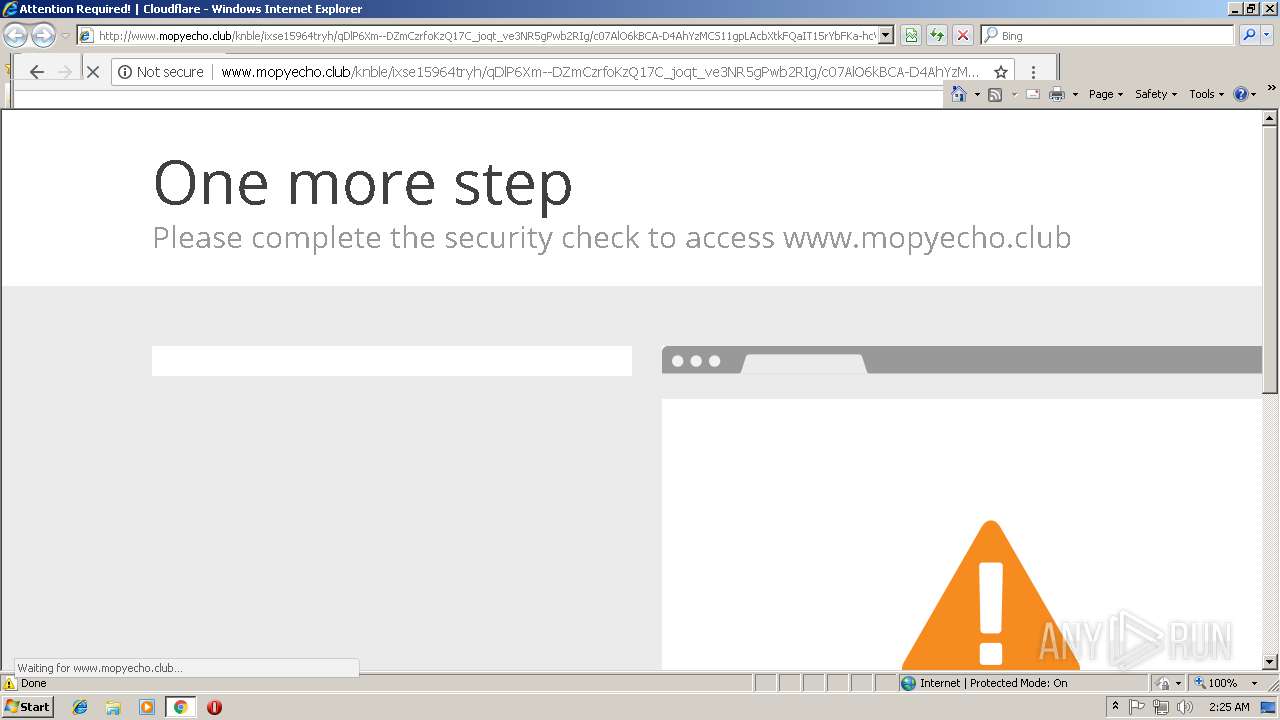
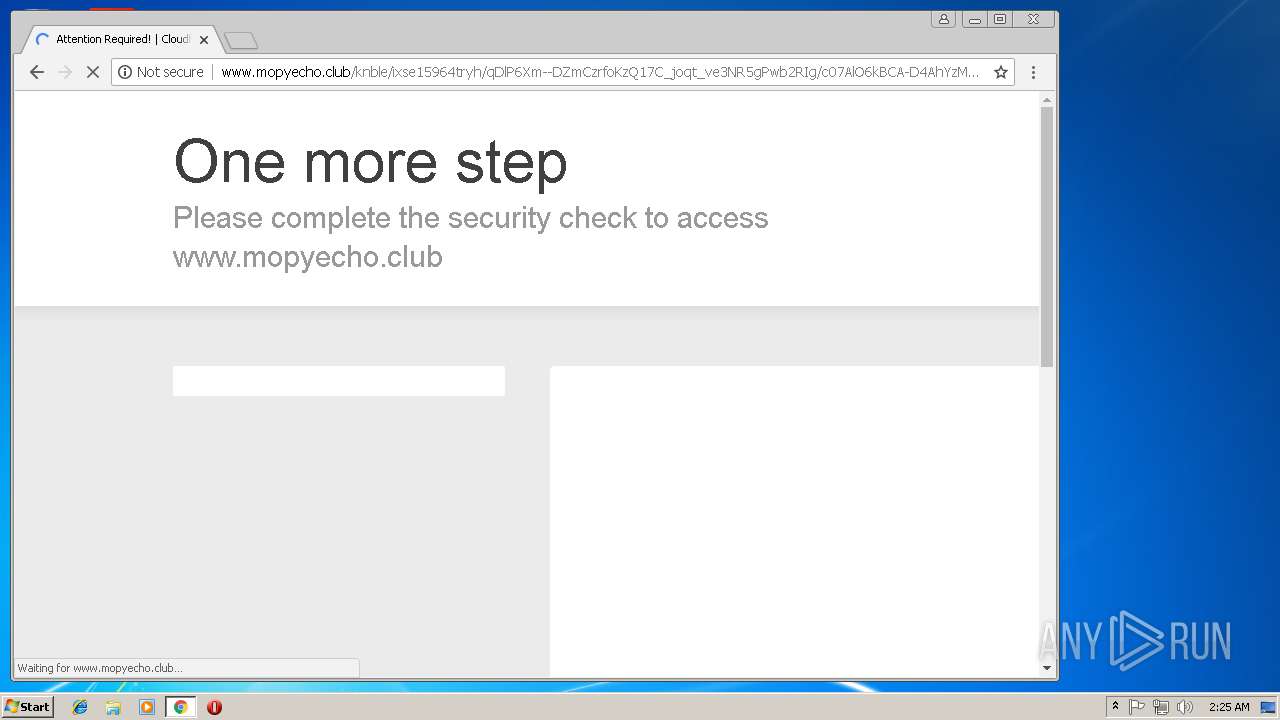
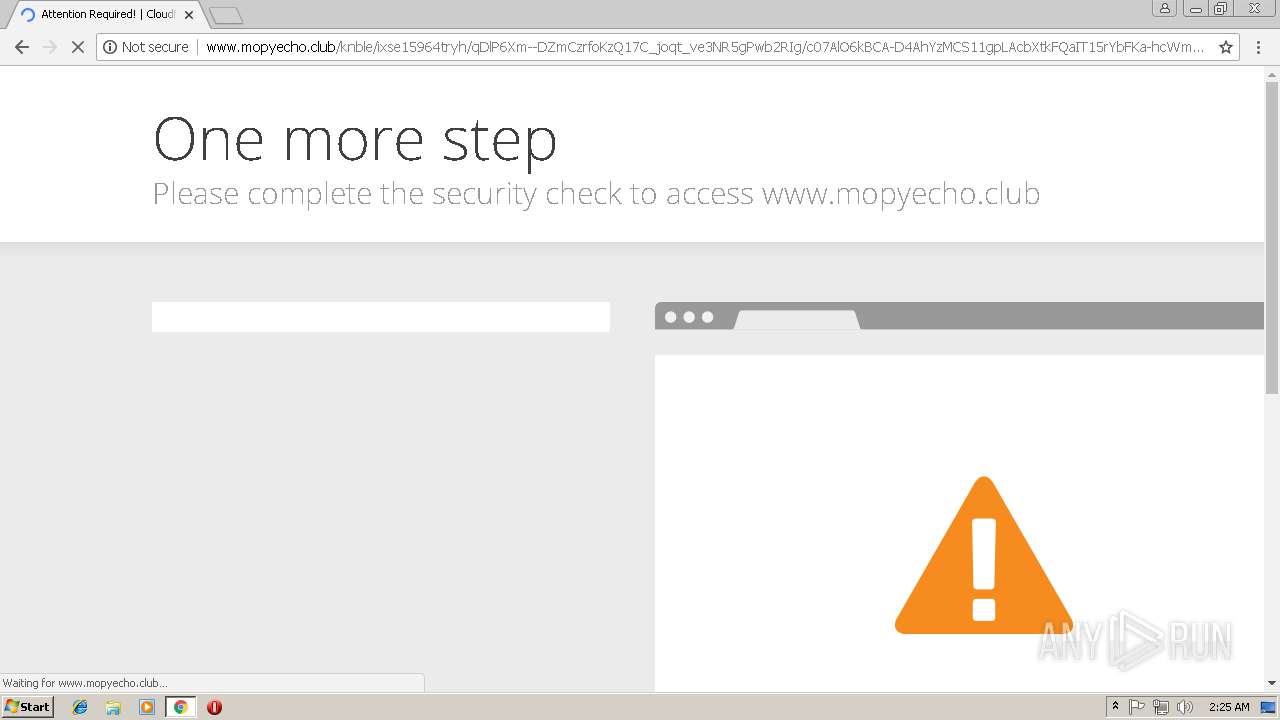
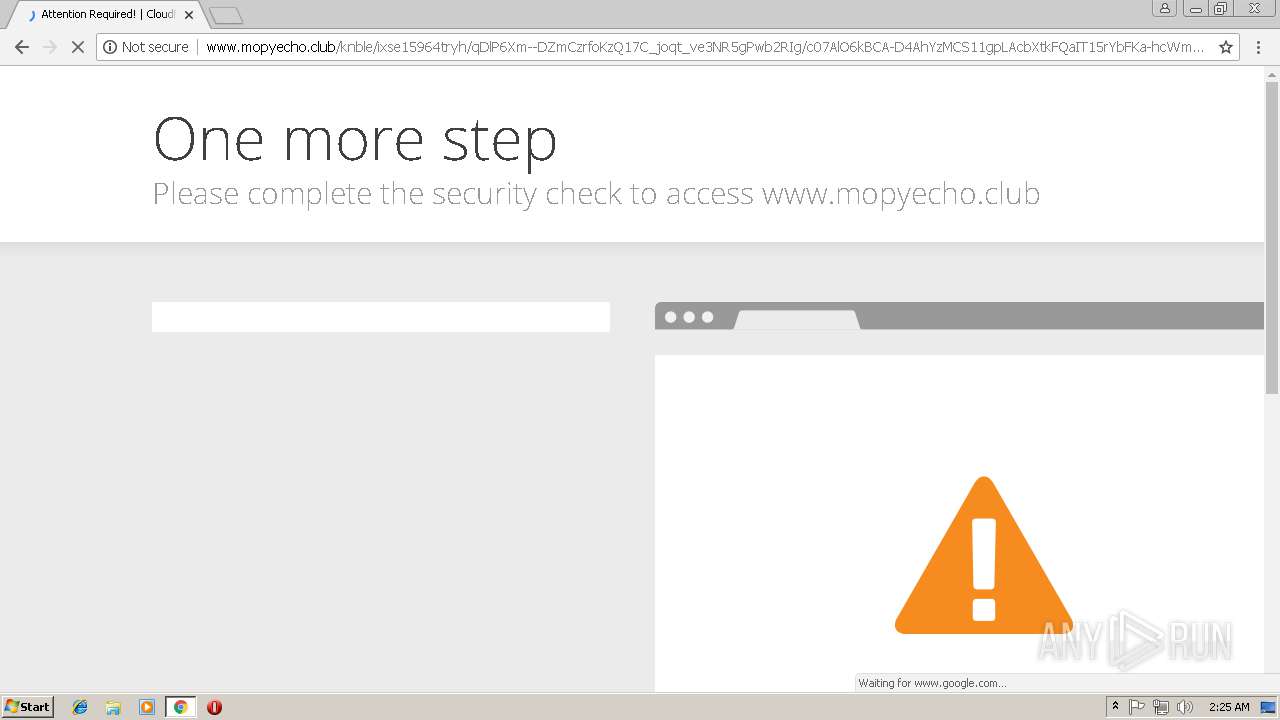
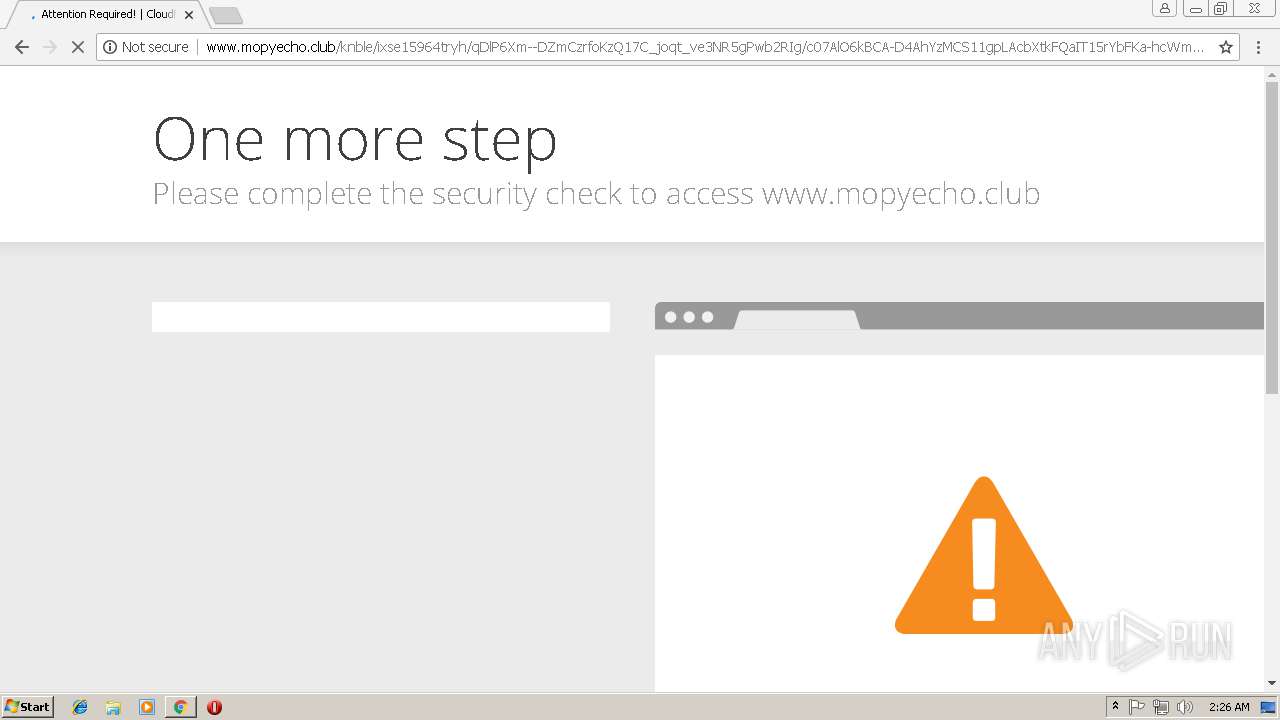
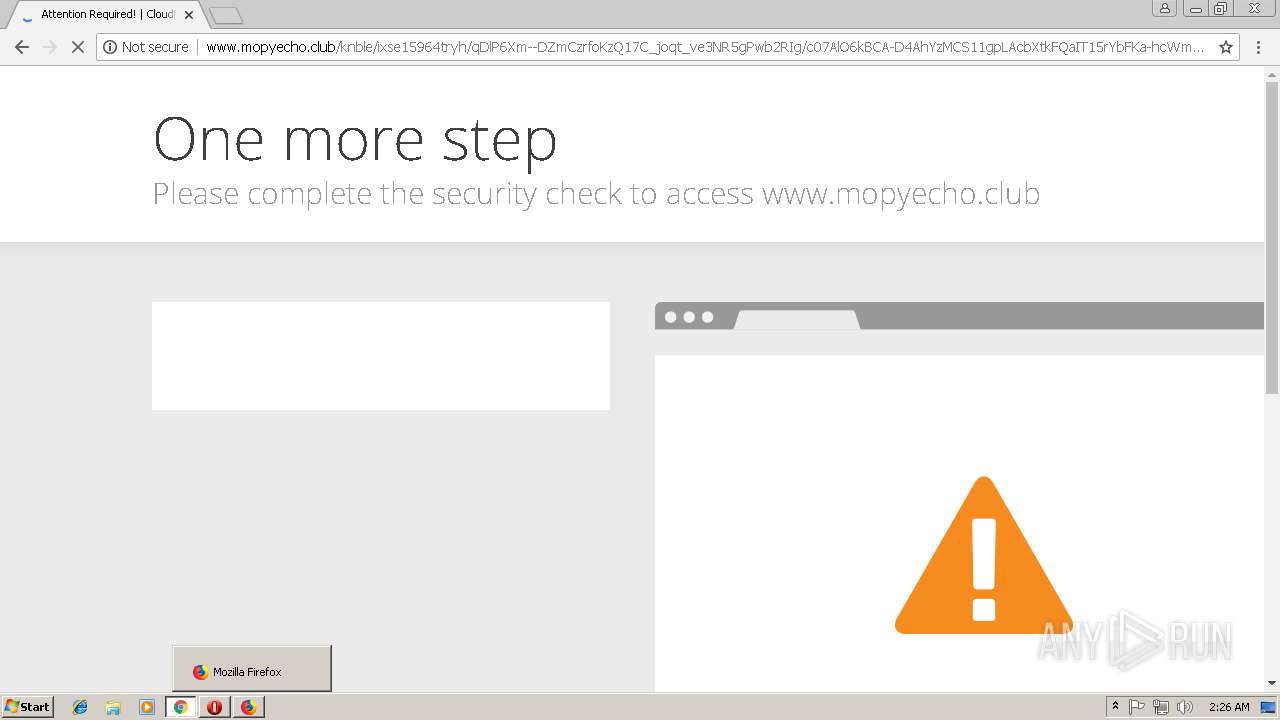
| URL: | http://www.mopyecho.club/knble/ixse15964tryh/qDlP6Xm--DZmCzrfoKzQ17C_joqt_ve3NR5gPwb2RIg/c07AlO6kBCA-D4AhYzMCS11gpLAcbXtkFQaIT15rYbFKa-hcWmTvcAUWKS0-AFWhYEtTc3RfwrkXkmdsPrcM7c8bOn-M7on1CajQ80sp-rUZy-4s8zOz9Uy8x57dC9CPLHHFvd19usoELX9OnvPxYEg_4PG34zHld8Z0x-Z7W9A |
| Full analysis: | https://app.any.run/tasks/e93646eb-4ae4-43ab-9422-c7a1249d0b55 |
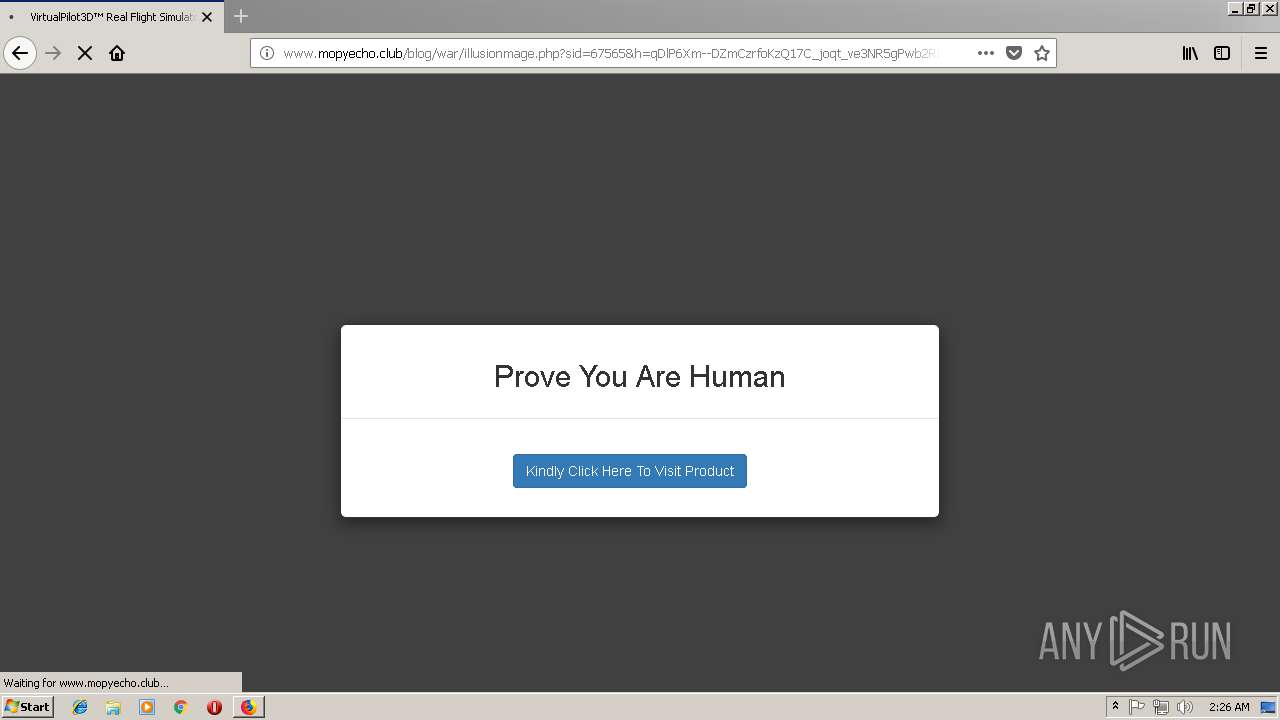
| Verdict: | Malicious activity |
| Analysis date: | October 12, 2018, 01:24:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4DFB81484C12A2621708D61963D034D9 |
| SHA1: | 6060D994D173A46333AA81F19EB711A0D4DB3AB3 |
| SHA256: | 9749A8862665B5F53B84153F02EE4CDC86E58C0369DE6B2EC3E312DC902CBCE7 |
| SSDEEP: | 6:Cc4GAYkppxiieq2dq69bGdLO8A/8JnfG46kWxcYSQh1FKYDm:VAYeitc6Udi8LtfG6uOIvKMm |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 3400)
Creates files in the user directory
- iexplore.exe (PID: 1304)
- iexplore.exe (PID: 3400)
- firefox.exe (PID: 3024)
Reads internet explorer settings
- iexplore.exe (PID: 1304)
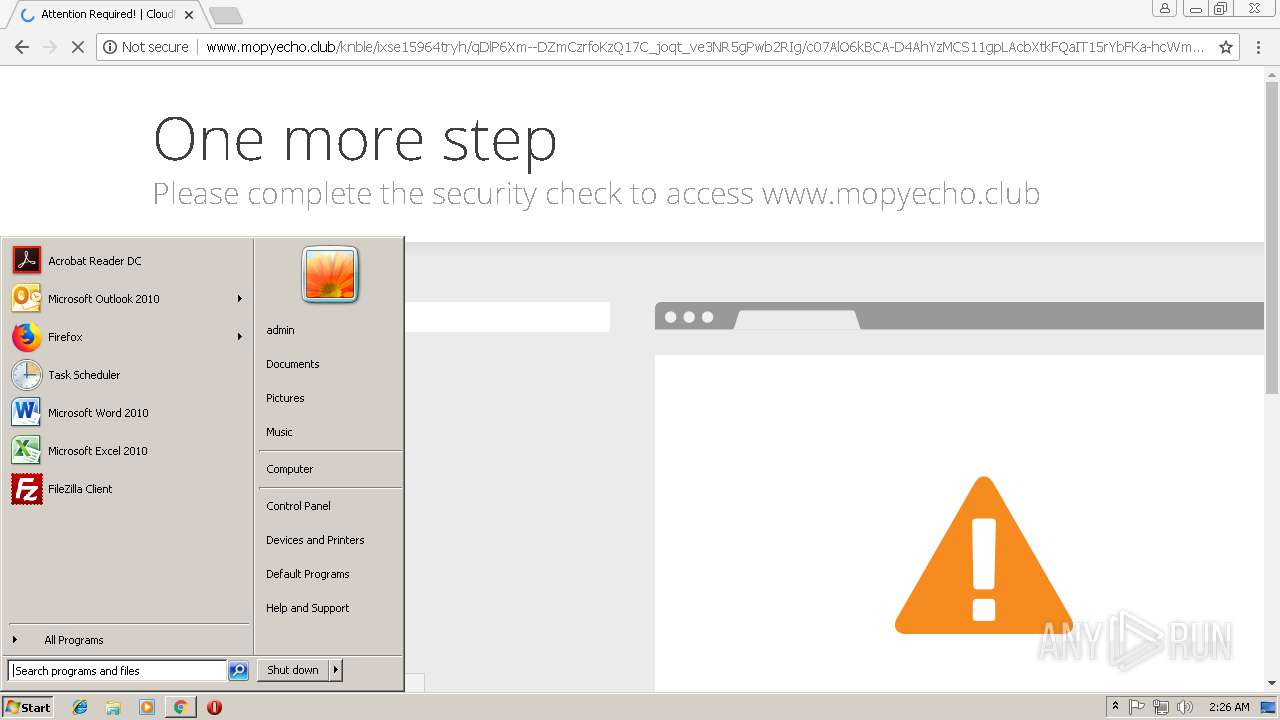
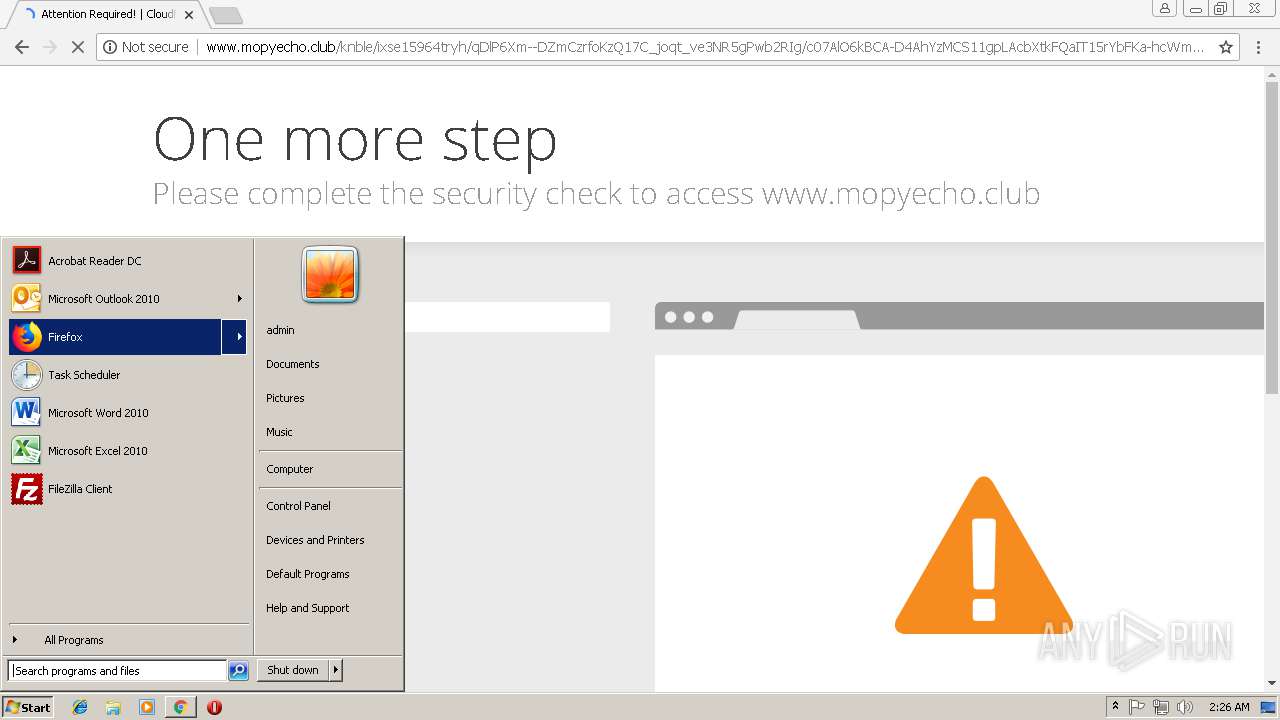
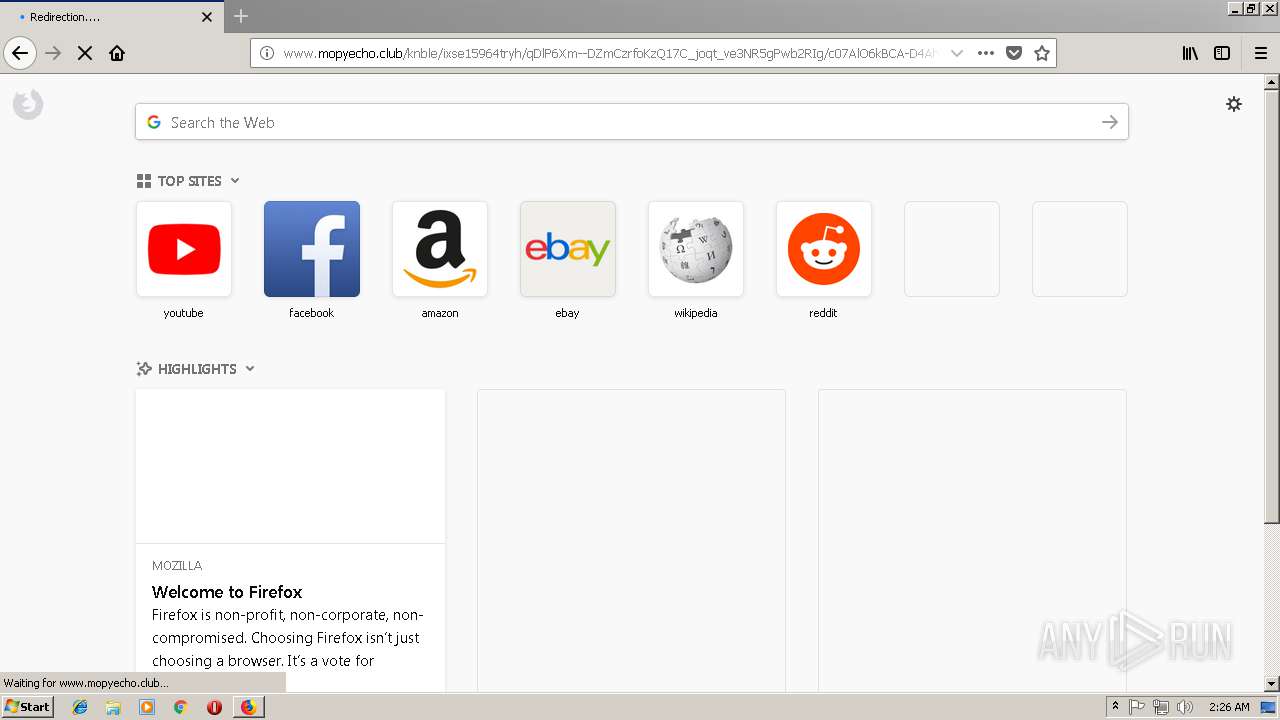
Application launched itself
- chrome.exe (PID: 116)
- iexplore.exe (PID: 3400)
- firefox.exe (PID: 3024)
Reads CPU info
- firefox.exe (PID: 3024)
- firefox.exe (PID: 2108)
- firefox.exe (PID: 1496)
- firefox.exe (PID: 3848)
Reads Internet Cache Settings
- iexplore.exe (PID: 1304)
Reads settings of System Certificates
- firefox.exe (PID: 3024)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,11287558885759409268,13831361049620686929,131072 --enable-features=PasswordImport --service-pipe-token=FCE59F663E667CA6E8347FC7C1999DC0 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=FCE59F663E667CA6E8347FC7C1999DC0 --renderer-client-id=5 --mojo-platform-channel-handle=1864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3400 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,11287558885759409268,13831361049620686929,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=689E3025699E7A4116FA1CB5FF88B4CC --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=689E3025699E7A4116FA1CB5FF88B4CC --renderer-client-id=10 --mojo-platform-channel-handle=3756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
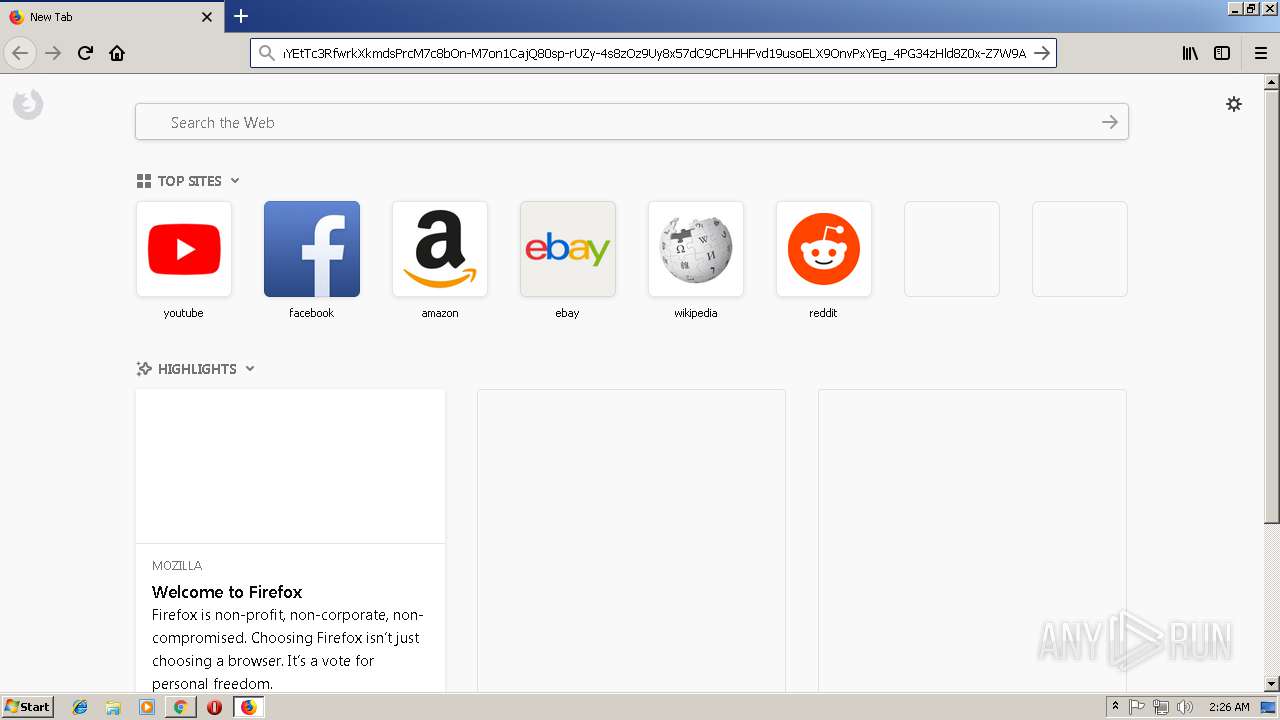
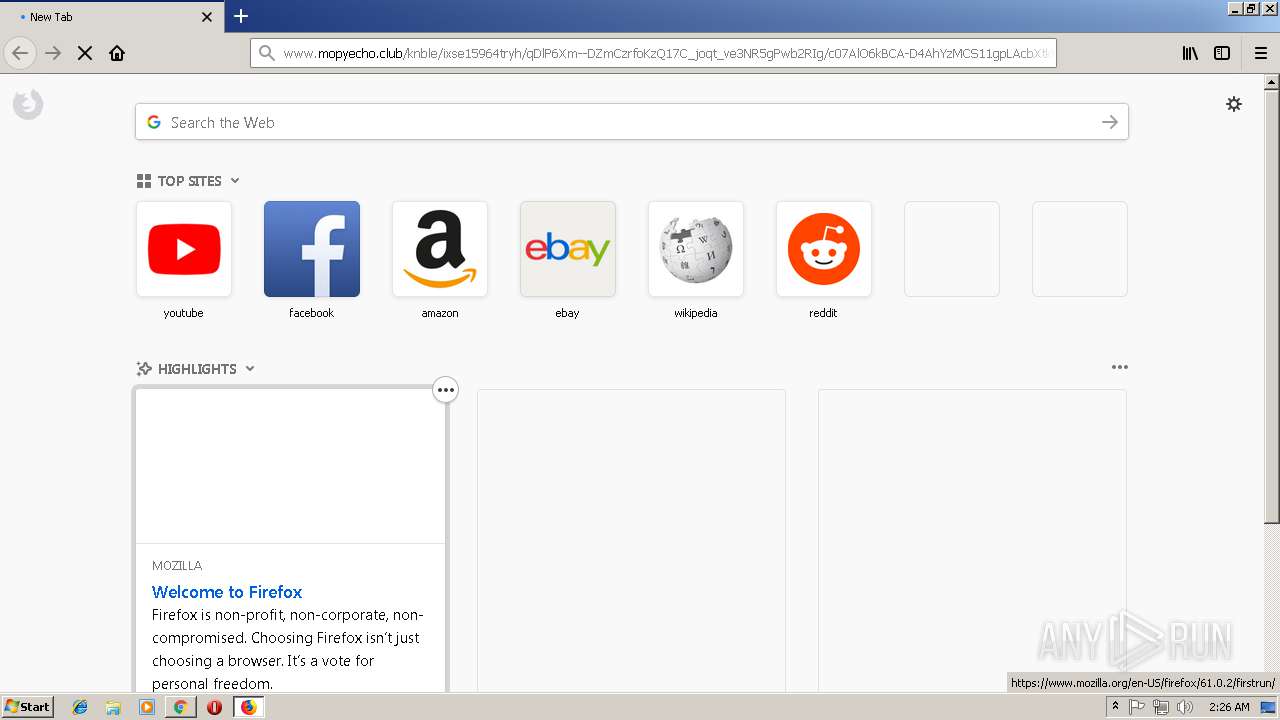
| 1496 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3024.6.1926752240\1287288032" -childID 2 -isForBrowser -prefsHandle 2368 -prefsLen 11441 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3024 "\\.\pipe\gecko-crash-server-pipe.3024" 2360 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,11287558885759409268,13831361049620686929,131072 --enable-features=PasswordImport --service-pipe-token=AD1A6E99F427544887845A4DBF4FA1AA --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=AD1A6E99F427544887845A4DBF4FA1AA --renderer-client-id=3 --mojo-platform-channel-handle=2124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3024.0.937063629\1473999128" -childID 1 -isForBrowser -prefsHandle 1352 -prefsLen 8309 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3024 "\\.\pipe\gecko-crash-server-pipe.3024" 1412 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,11287558885759409268,13831361049620686929,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0FAB73AA2AB1CC7B07F79B5D305B22FC --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0FAB73AA2AB1CC7B07F79B5D305B22FC --renderer-client-id=7 --mojo-platform-channel-handle=3436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=896,11287558885759409268,13831361049620686929,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=EA3FA6ECEA71C3DC23C70469600357B4 --mojo-platform-channel-handle=3876 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=896,11287558885759409268,13831361049620686929,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=F425461D63D7FD15D02A29FAB23E5924 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F425461D63D7FD15D02A29FAB23E5924 --renderer-client-id=6 --mojo-platform-channel-handle=3424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 504
Read events
1 403
Write events
97
Delete events
4
Modification events
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {9DEAA519-CDBD-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070A0005000C000100180034009903 | |||
Executable files
0
Suspicious files
175
Text files
170
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3400 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3400 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\cf.challenge[1].js | text | |
MD5:FA838DB2022197988C2EC8CE59880BA5 | SHA256:B7FC2FB688CF1BB7C4DE30C20B2C28142153E2F296624CB73F7C5D223E57BD08 | |||
| 1304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\opensans-700[1].eot | eot | |
MD5:5281996FC5E0B7A766EAEE928BD7123E | SHA256:368B82FDF6E99815F10EFA81120057ED3EA283C4A5ABC4E5204473578A1AC0FE | |||
| 1304 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@mopyecho[1].txt | text | |
MD5:1062E9DBD66C4B2FF98E9F616F5835D4 | SHA256:859ECDFAA285E2B695A1BB83F1661C6F67E99FFFFB2113C6622C7FC209AB0841 | |||
| 1304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\cf.errors[1].css | text | |
MD5:3D041BD798B1C6A68C1CB4F3A1FD6B8A | SHA256:E2DBA22A9EE028E3AA09BAA7C36E14C86EFFBA2516862AAD01019C06E757B375 | |||
| 1304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\opensans-400i[1].eot | eot | |
MD5:B65A44E1C6C2D42DAF9F20A8C08E067B | SHA256:2D80A84811DB8FC86DDCCAA07FD4E8DF22C33B578F674D21BC4EFBEAAAB7594B | |||
| 1304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\recaptcha__en[1].js | text | |
MD5:B09C5D4AB648BAD3DB09ABEA5D13AE30 | SHA256:57D329A6ABC2CAB77485ED67F317DD7AA4274E5DB4E051C50D3F8C481BAA2792 | |||
| 1304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\api[1].js | text | |
MD5:3BD4F44841E1178570A674EE72737906 | SHA256:70B31B887C9F71CCEED50C10DB89C371F95B57A11C30E40BC0B72BD9C92FC836 | |||
| 1304 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\opensans-300[1].eot | eot | |
MD5:566E3A1D44C9CDB02891828C686A60A6 | SHA256:A95920FF81B2BC13A269AAC4E13D17DB7303BD442E847EEE2AAD411716B04202 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
113
TCP/UDP connections
92
DNS requests
127
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1304 | iexplore.exe | GET | 200 | 104.24.110.29:80 | http://www.mopyecho.club/cdn-cgi/styles/cf.errors.css | US | text | 4.77 Kb | malicious |
1304 | iexplore.exe | GET | 403 | 104.24.110.29:80 | http://www.mopyecho.club/knble/ixse15964tryh/qDlP6Xm--DZmCzrfoKzQ17C_joqt_ve3NR5gPwb2RIg/c07AlO6kBCA-D4AhYzMCS11gpLAcbXtkFQaIT15rYbFKa-hcWmTvcAUWKS0-AFWhYEtTc3RfwrkXkmdsPrcM7c8bOn-M7on1CajQ80sp-rUZy-4s8zOz9Uy8x57dC9CPLHHFvd19usoELX9OnvPxYEg_4PG34zHld8Z0x-Z7W9A | US | html | 1.91 Kb | malicious |
1304 | iexplore.exe | GET | 200 | 104.24.110.29:80 | http://www.mopyecho.club/cdn-cgi/styles/fonts/opensans-300.eot | US | eot | 18.1 Kb | malicious |
3400 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1304 | iexplore.exe | GET | 200 | 104.24.110.29:80 | http://www.mopyecho.club/cdn-cgi/styles/cf.errors.ie.css | US | text | 799 b | malicious |
1304 | iexplore.exe | GET | 200 | 104.24.110.29:80 | http://www.mopyecho.club/cdn-cgi/styles/fonts/opensans-600.eot | US | eot | 18.8 Kb | malicious |
1304 | iexplore.exe | GET | 200 | 104.24.110.29:80 | http://www.mopyecho.club/cdn-cgi/styles/fonts/opensans-300i.eot | US | eot | 20.9 Kb | malicious |
1304 | iexplore.exe | GET | 200 | 104.24.110.29:80 | http://www.mopyecho.club/cdn-cgi/styles/fonts/opensans-700.eot | US | eot | 19.3 Kb | malicious |
116 | chrome.exe | GET | 403 | 104.24.110.29:80 | http://www.mopyecho.club/knble/ixse15964tryh/qDlP6Xm--DZmCzrfoKzQ17C_joqt_ve3NR5gPwb2RIg/c07AlO6kBCA-D4AhYzMCS11gpLAcbXtkFQaIT15rYbFKa-hcWmTvcAUWKS0-AFWhYEtTc3RfwrkXkmdsPrcM7c8bOn-M7on1CajQ80sp-rUZy-4s8zOz9Uy8x57dC9CPLHHFvd19usoELX9OnvPxYEg_4PG34zHld8Z0x-Z7W9A | US | html | 2.03 Kb | malicious |
1304 | iexplore.exe | GET | 200 | 104.24.110.29:80 | http://www.mopyecho.club/cdn-cgi/styles/fonts/opensans-400.eot | US | eot | 18.3 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
116 | chrome.exe | 216.58.215.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
116 | chrome.exe | 216.58.215.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
116 | chrome.exe | 104.24.110.29:80 | www.mopyecho.club | Cloudflare Inc | US | shared |
116 | chrome.exe | 216.58.215.68:443 | www.google.com | Google Inc. | US | whitelisted |
116 | chrome.exe | 216.58.215.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1304 | iexplore.exe | 104.24.110.29:80 | www.mopyecho.club | Cloudflare Inc | US | shared |
1304 | iexplore.exe | 216.58.215.68:443 | www.google.com | Google Inc. | US | whitelisted |
3024 | firefox.exe | 91.223.19.234:80 | detectportal.firefox.com | Allied Standart Limited LLC | UA | unknown |
3024 | firefox.exe | 35.161.241.7:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3024 | firefox.exe | 52.25.175.166:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.mopyecho.club |
| malicious |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |