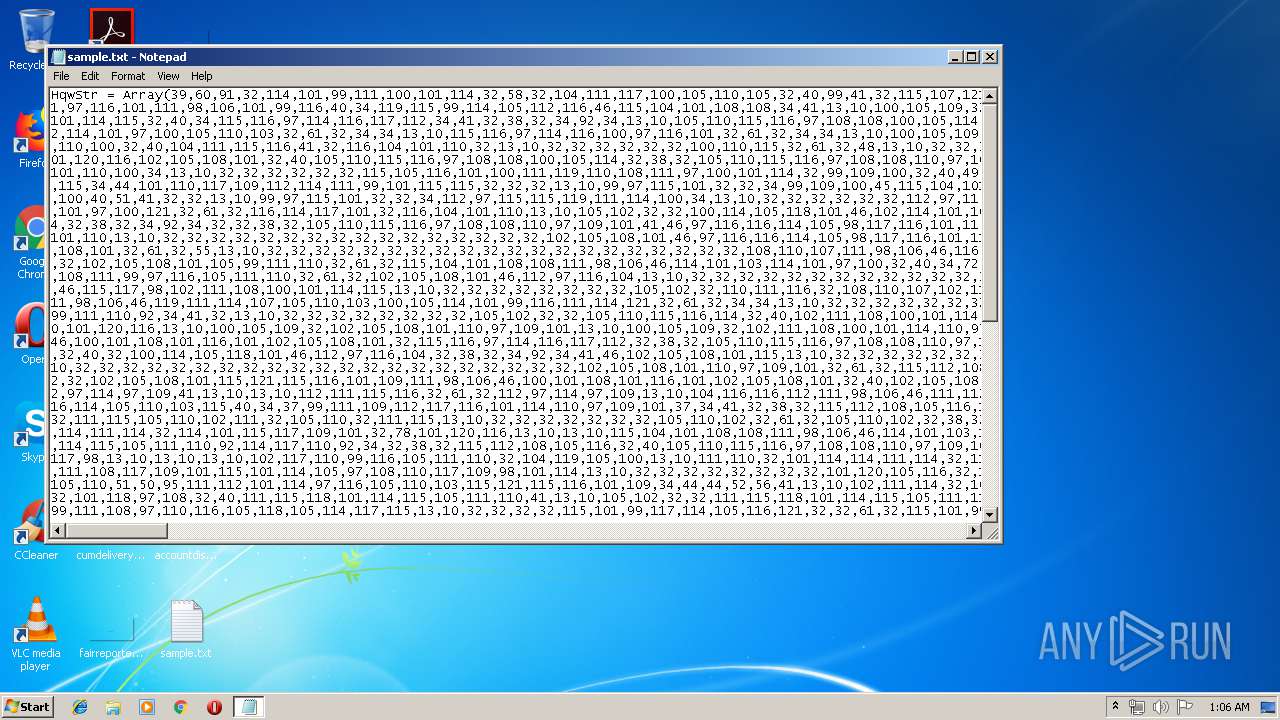
| File name: | sample.txt |
| Full analysis: | https://app.any.run/tasks/7ccefc95-d2e2-4123-af61-d8efee69dace |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 00:06:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 70E791BC277212D283900A9DA30E813C |
| SHA1: | BAEBA4EDCD4A933198562CECD7ABBB5F746561FB |
| SHA256: | 973811E862E2EEA099F511228311E12127825FB0B050F44BB46215CAF77DEBCE |
| SSDEEP: | 1536:vYfObBeYaBOnrhckWzTWkBHnnT1kftWmqo+qnHRgrr5iYfMEULP5LqQasQIsCJKG:J |
MALICIOUS
Writes to a start menu file
- WScript.exe (PID: 960)
- wscript.exe (PID: 2308)
Changes the autorun value in the registry
- WScript.exe (PID: 960)
- wscript.exe (PID: 2308)
SUSPICIOUS
Executes scripts
- WScript.exe (PID: 960)
Application launched itself
- WScript.exe (PID: 960)
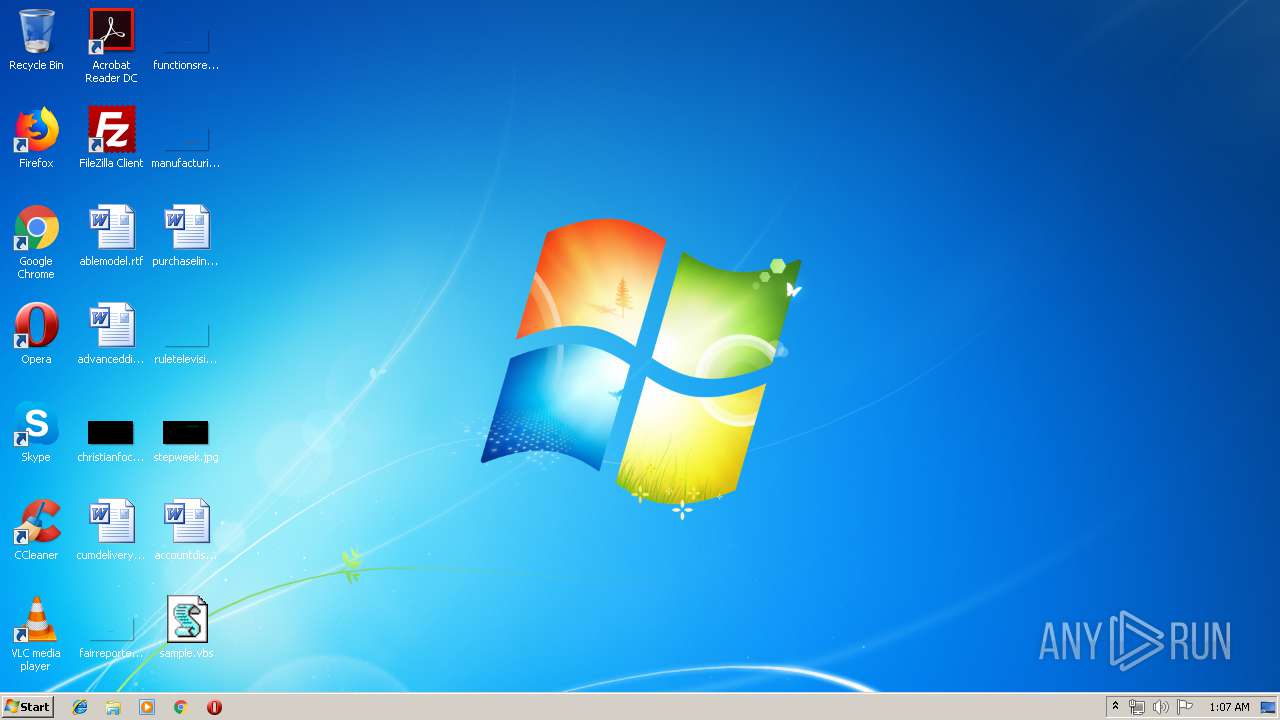
Creates files in the user directory
- WScript.exe (PID: 960)
INFO
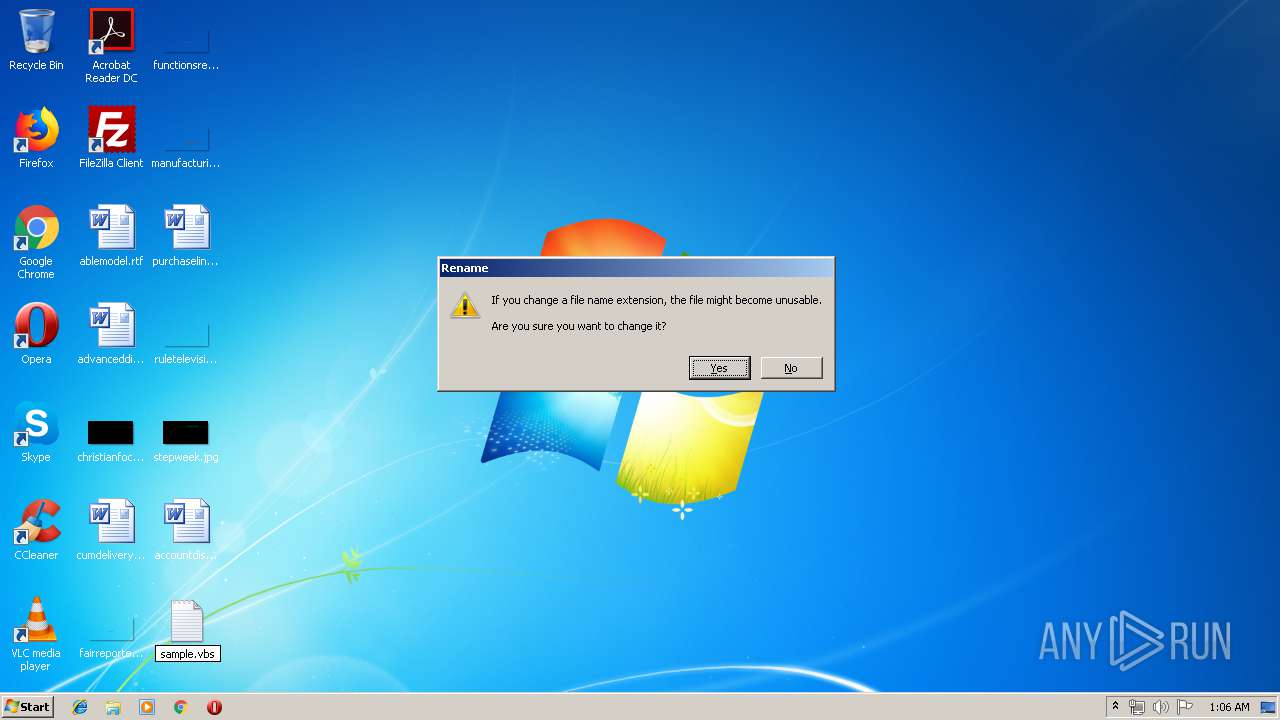
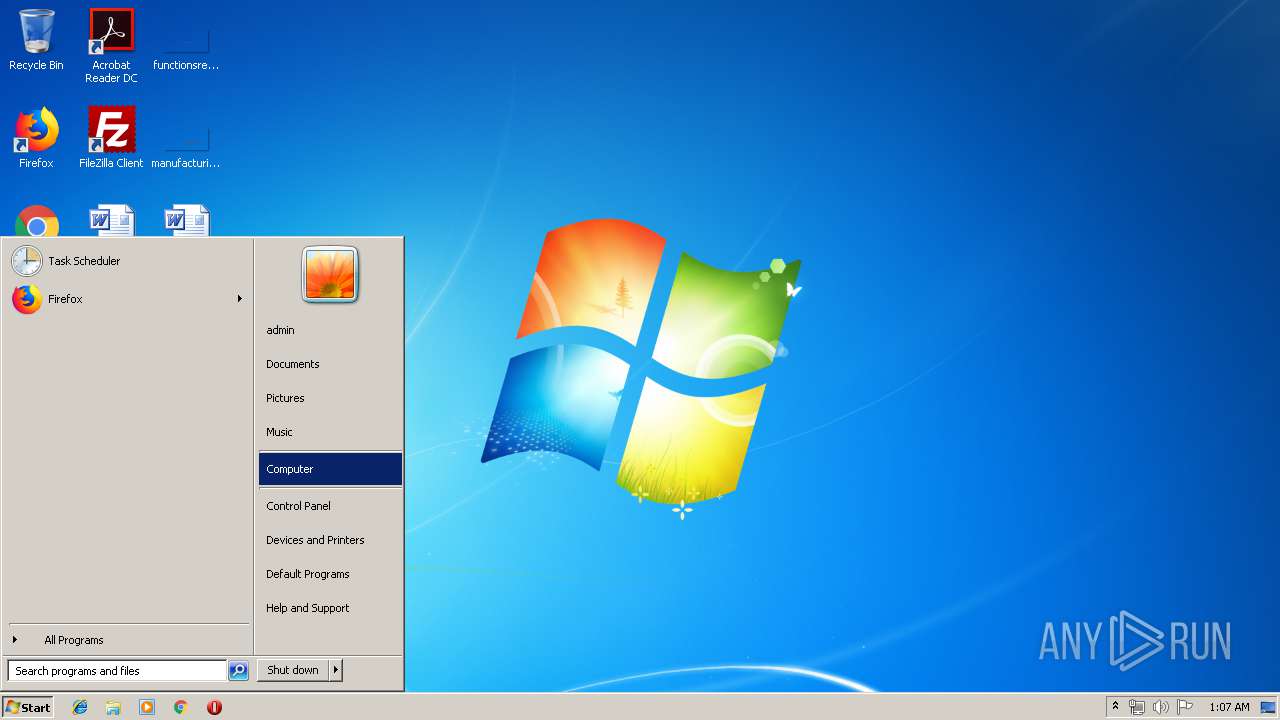
Manual execution by user
- WScript.exe (PID: 960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\sample.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2308 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Roaming\sample.vbs" | C:\Windows\System32\wscript.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2628 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\sample.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
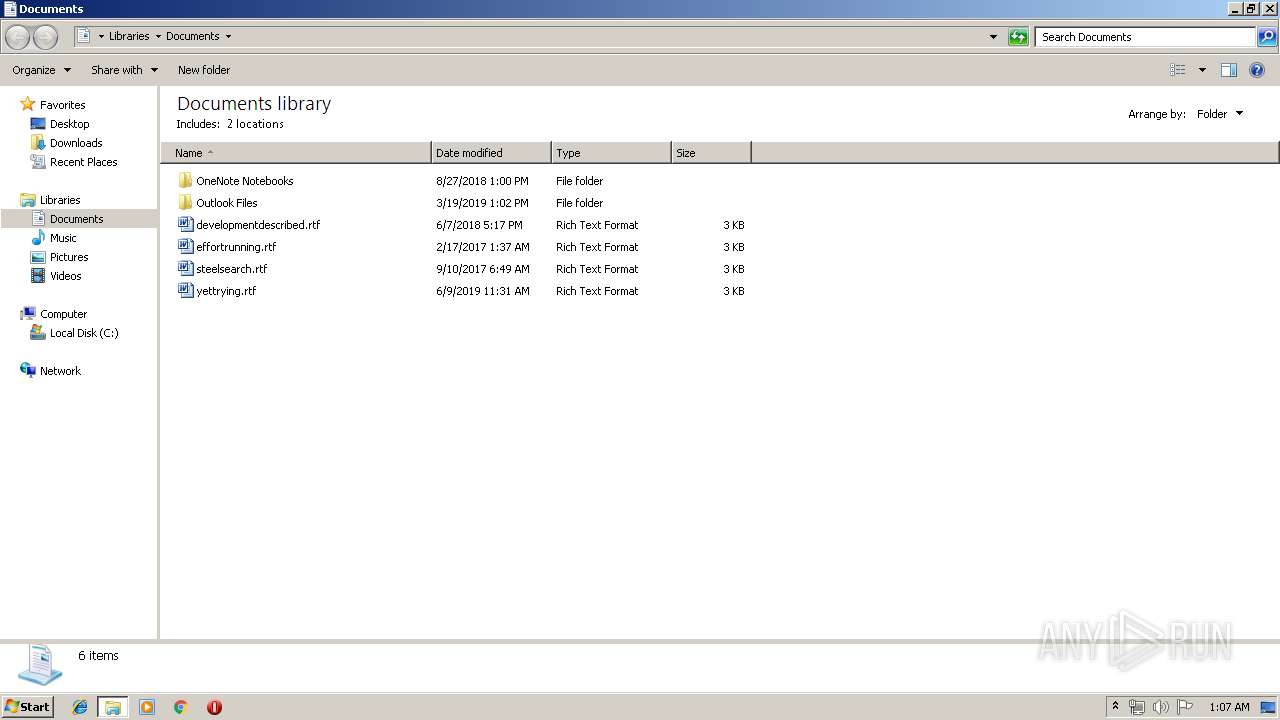
Total events
502
Read events
283
Write events
219
Delete events
0
Modification events
| (PID) Process: | (2628) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 44 | |||
| (PID) Process: | (2628) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 44 | |||
| (PID) Process: | (2628) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (2628) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (960) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\sample |
| Operation: | write | Name: | |
Value: false - 6/12/2019 | |||
| (PID) Process: | (960) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | sample |
Value: wscript.exe //B "C:\Users\admin\AppData\Roaming\sample.vbs" | |||
| (PID) Process: | (960) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | sample |
Value: wscript.exe //B "C:\Users\admin\AppData\Roaming\sample.vbs" | |||
| (PID) Process: | (960) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (960) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2308) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | sample |
Value: wscript.exe //B "C:\Users\admin\AppData\Roaming\sample.vbs" | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 960 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\sample.vbs | text | |
MD5:— | SHA256:— | |||
| 960 | WScript.exe | C:\Users\admin\AppData\Roaming\sample.vbs | text | |
MD5:— | SHA256:— | |||
| 2308 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\sample.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
wc-ltc.ddns.net |
| unknown |