| File name: | PO_GPO-R015061NEW.pdf |
| Full analysis: | https://app.any.run/tasks/e86bc0a8-5a1f-42a6-bbba-e649eb06cd76 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 04:47:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.7 |
| MD5: | E56C22103762C4FF3C9322347E716686 |
| SHA1: | 02F5571F57561411ADB3C1D1E94E5980CDC8FA98 |
| SHA256: | 973428991A798573361FF358449E994FFB97E1D4C39FA9B00269DBD21A108A29 |
| SSDEEP: | 1536:eQCr679fQYeSpZEfFQQ+RjNdfZlAoXja/eNW5vW+qn0CvMw9C:3fQYbTENQ3XZX2/IWgn0Cv/9C |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2292)
- chrome.exe (PID: 3848)
SUSPICIOUS
Checks supported languages
- AdobeARM.exe (PID: 3756)
- Reader_sl.exe (PID: 3884)
Reads the computer name
- AdobeARM.exe (PID: 3756)
Starts Internet Explorer
- AcroRd32.exe (PID: 2916)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2240)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3960)
Creates files in the program directory
- AdobeARM.exe (PID: 3756)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 3756)
- chrome.exe (PID: 3848)
Drops a file with a compile date too recent
- chrome.exe (PID: 2292)
- chrome.exe (PID: 3848)
INFO
Reads the computer name
- AcroRd32.exe (PID: 2916)
- AcroRd32.exe (PID: 3256)
- RdrCEF.exe (PID: 3680)
- iexplore.exe (PID: 128)
- iexplore.exe (PID: 2240)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 3872)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 2904)
- chrome.exe (PID: 2388)
- chrome.exe (PID: 1016)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 2292)
Searches for installed software
- AcroRd32.exe (PID: 2916)
- AcroRd32.exe (PID: 3256)
Checks supported languages
- AcroRd32.exe (PID: 3256)
- AcroRd32.exe (PID: 2916)
- RdrCEF.exe (PID: 3680)
- RdrCEF.exe (PID: 1396)
- RdrCEF.exe (PID: 3864)
- RdrCEF.exe (PID: 2208)
- RdrCEF.exe (PID: 1256)
- RdrCEF.exe (PID: 4072)
- RdrCEF.exe (PID: 3212)
- RdrCEF.exe (PID: 3032)
- RdrCEF.exe (PID: 4060)
- iexplore.exe (PID: 128)
- iexplore.exe (PID: 2240)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 928)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 3872)
- chrome.exe (PID: 660)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 2976)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 2904)
- chrome.exe (PID: 656)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 788)
- chrome.exe (PID: 1468)
- chrome.exe (PID: 1016)
- chrome.exe (PID: 2388)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 2672)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 992)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 872)
- chrome.exe (PID: 3848)
- chrome.exe (PID: 3512)
- chrome.exe (PID: 1256)
Application launched itself
- AcroRd32.exe (PID: 2916)
- RdrCEF.exe (PID: 3680)
- iexplore.exe (PID: 128)
- chrome.exe (PID: 3960)
Reads CPU info
- AcroRd32.exe (PID: 3256)
Reads the hosts file
- RdrCEF.exe (PID: 3680)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 3960)
Checks Windows Trust Settings
- AcroRd32.exe (PID: 2916)
- iexplore.exe (PID: 128)
- iexplore.exe (PID: 2240)
- AdobeARM.exe (PID: 3756)
Reads settings of System Certificates
- AcroRd32.exe (PID: 2916)
- RdrCEF.exe (PID: 3680)
- iexplore.exe (PID: 128)
- iexplore.exe (PID: 2240)
- chrome.exe (PID: 2292)
- AdobeARM.exe (PID: 3756)
Changes internet zones settings
- iexplore.exe (PID: 128)
Reads internet explorer settings
- iexplore.exe (PID: 2240)
Adds / modifies Windows certificates
- iexplore.exe (PID: 128)
Changes settings of System certificates
- iexplore.exe (PID: 128)
Manual execution by user
- chrome.exe (PID: 3960)
Reads the date of Windows installation
- chrome.exe (PID: 2904)
- iexplore.exe (PID: 128)
Creates files in the user directory
- iexplore.exe (PID: 128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
XMP
| InstanceID: | uuid:67C7D320-69F8-4EA9-B7CE-FA731F4C99E0 |
|---|---|
| DocumentID: | uuid:67C7D320-69F8-4EA9-B7CE-FA731F4C99E0 |
| ModifyDate: | 2022:05:03 08:50:29-07:00 |
| CreateDate: | 2022:05:03 08:50:29-07:00 |
| CreatorTool: | Microsoft Word |
| Creator: | Sam Smith |
| XMPToolkit: | 3.1-701 |
| Producer: | 2.4.8 (4.3.4) |
|---|---|
| ModifyDate: | 2022:05:18 14:25:52+02:00 |
| CreateDate: | 2022:05:03 08:50:29-07:00 |
| Creator: | Microsoft Word |
| Author: | Sam Smith |
| HasXFA: | No |
| TaggedPDF: | Yes |
| Language: | en-US |
| PageCount: | 1 |
| Linearized: | No |
| PDFVersion: | 1.7 |
Total processes
85
Monitored processes
44
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
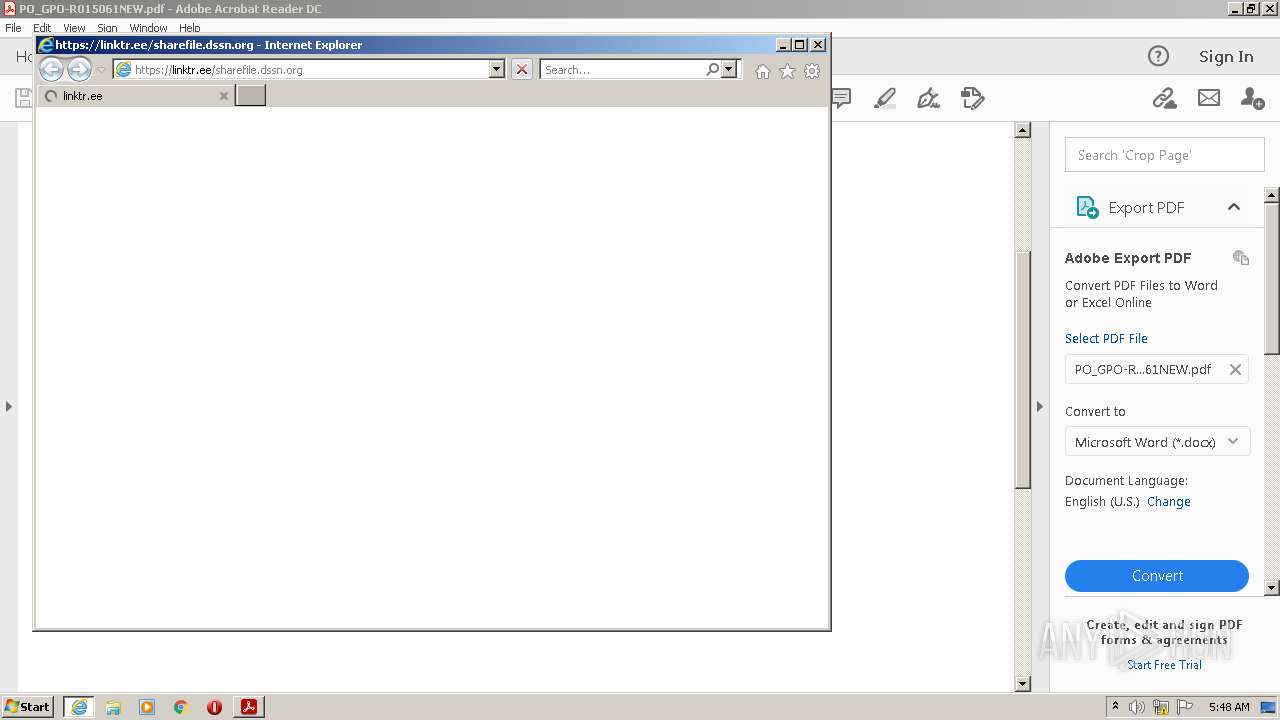
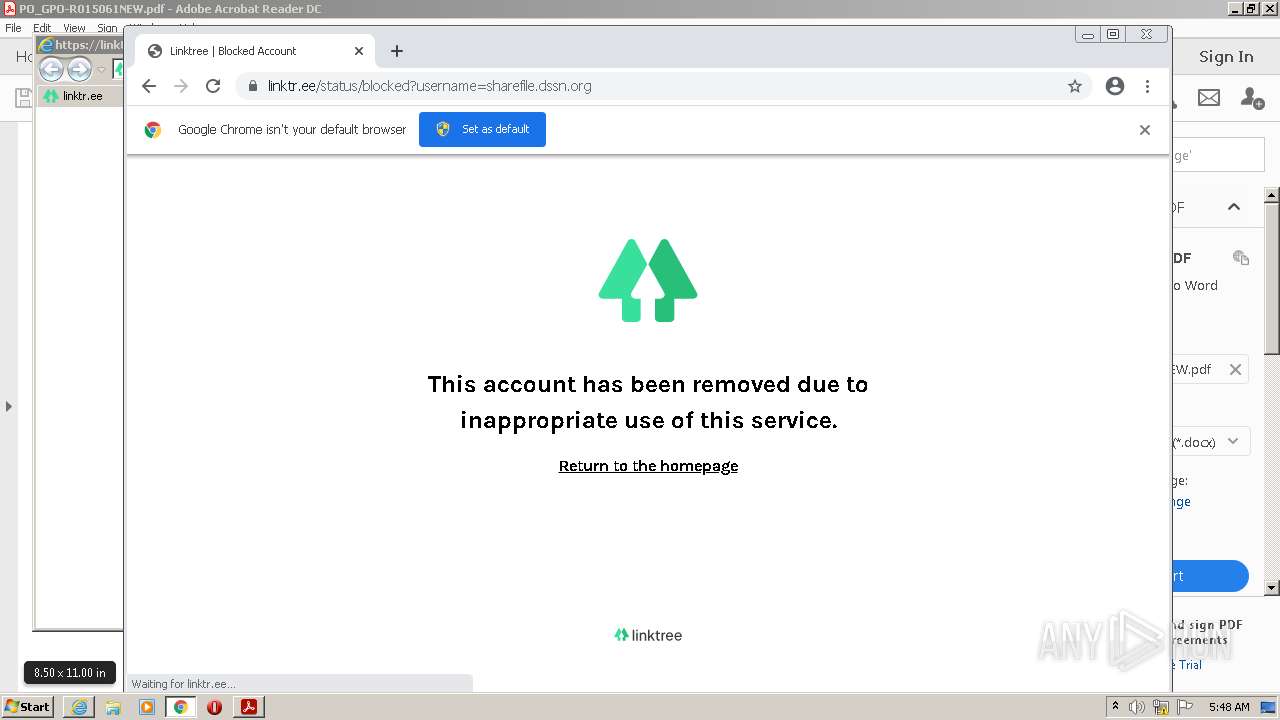
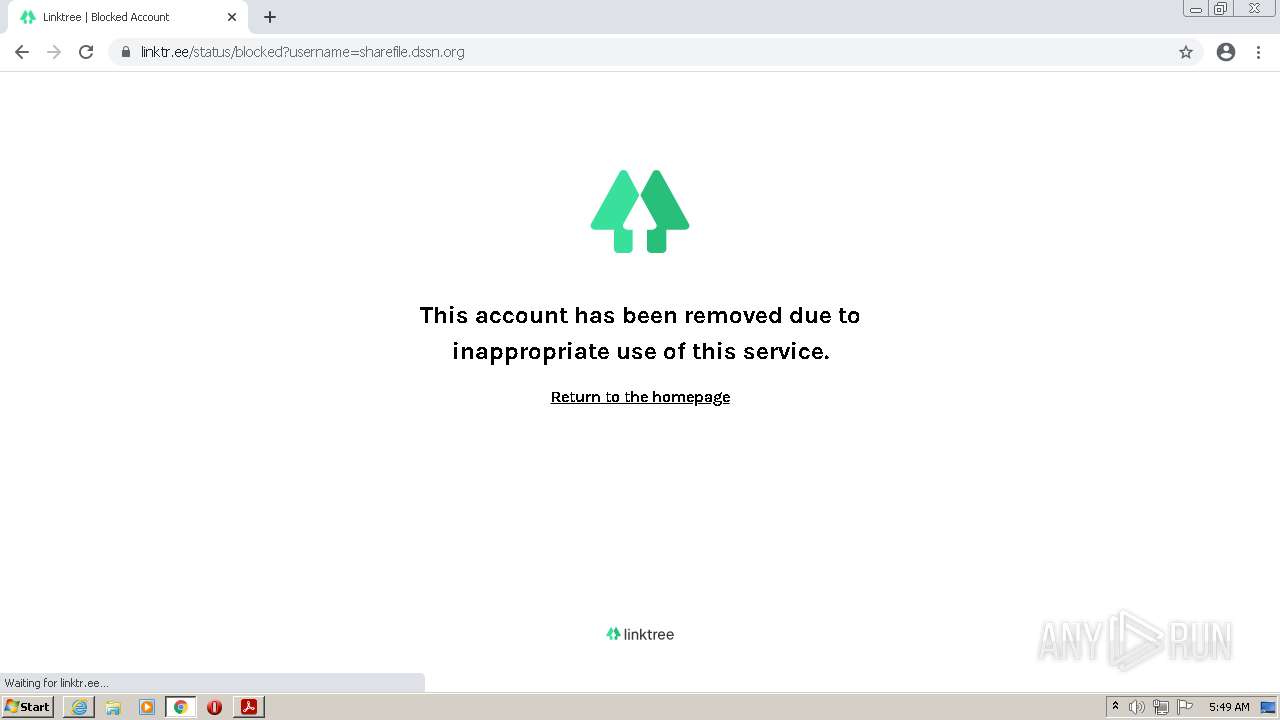
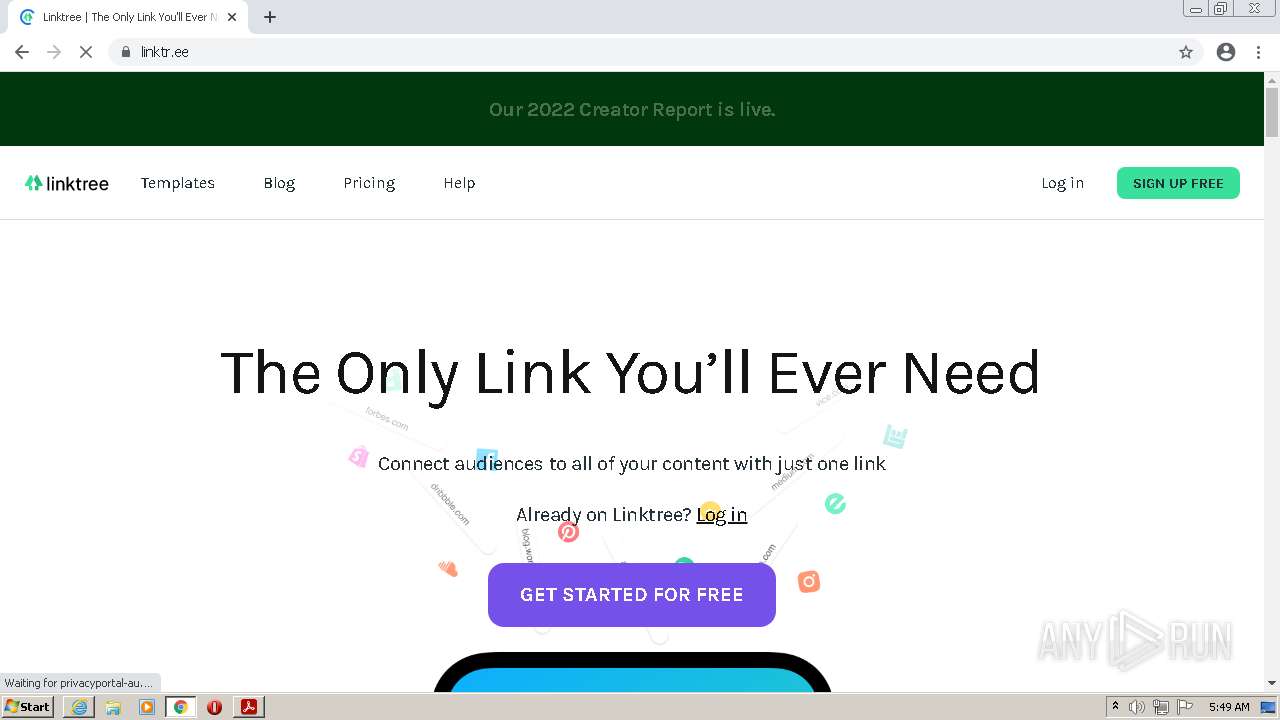
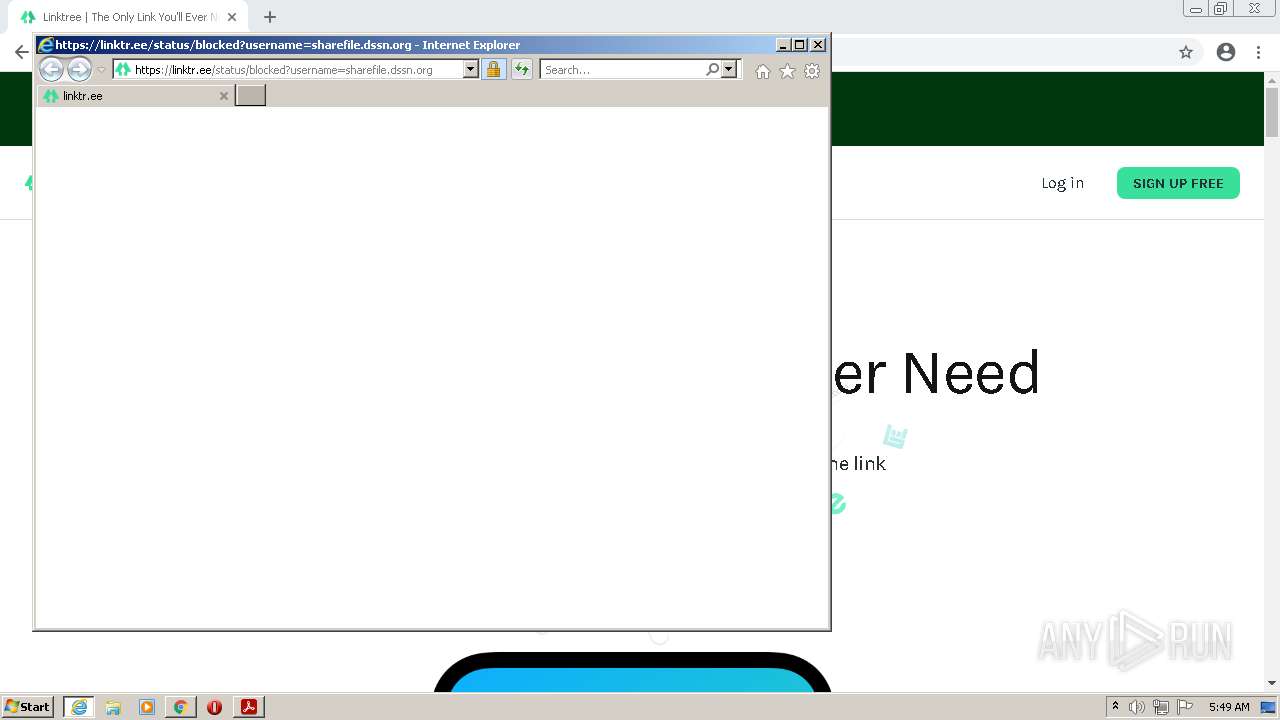
| 128 | "C:\Program Files\Internet Explorer\iexplore.exe" https://linktr.ee/sharefile.dssn.org | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1064,6121032097237131422,7549902339697655349,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3220 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,6121032097237131422,7549902339697655349,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2836 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1064,6121032097237131422,7549902339697655349,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1064,6121032097237131422,7549902339697655349,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3104 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,6121032097237131422,7549902339697655349,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,6121032097237131422,7549902339697655349,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1064,6121032097237131422,7549902339697655349,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=1688 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1068,3756202488483941697,12424030307839058168,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=10562509675121887085 --mojo-platform-channel-handle=1212 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,6121032097237131422,7549902339697655349,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
49 563
Read events
49 193
Write events
353
Delete events
17
Modification events
| (PID) Process: | (3256) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (3256) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | iNumReaderLaunches |
Value: 2 | |||
| (PID) Process: | (3256) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\FTEDialog |
| Operation: | write | Name: | bShowUpdateFTE |
Value: 1 | |||
| (PID) Process: | (3256) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\HomeWelcome |
| Operation: | write | Name: | bIsAcrobatUpdated |
Value: 1 | |||
| (PID) Process: | (3256) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\HomeWelcomeFirstMileReader |
| Operation: | write | Name: | iCardCountShown |
Value: 2 | |||
| (PID) Process: | (3256) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\FTEDialog |
| Operation: | delete value | Name: | iLastCardShown |
Value: 0 | |||
| (PID) Process: | (2916) AcroRd32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3256) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Adobe Acrobat\DC\DiskCabs |
| Operation: | write | Name: | bForms_AdhocWorkflowBackup |
Value: 0 | |||
| (PID) Process: | (3256) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\SessionManagement |
| Operation: | write | Name: | bNormalExit |
Value: 0 | |||
| (PID) Process: | (3256) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\SessionManagement\cWindowsCurrent\cWin0 |
| Operation: | write | Name: | iTabCount |
Value: 0 | |||
Executable files
2
Suspicious files
447
Text files
193
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3680 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\bba29d2e6197e2f4_0 | binary | |
MD5:— | SHA256:— | |||
| 3680 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\4a0e94571d979b3c_0 | binary | |
MD5:— | SHA256:— | |||
| 3680 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\8e417e79df3bf0e9_0 | binary | |
MD5:— | SHA256:— | |||
| 3680 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\2a426f11fd8ebe18_0 | binary | |
MD5:— | SHA256:— | |||
| 3680 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\560e9c8bff5008d8_0 | binary | |
MD5:— | SHA256:— | |||
| 3680 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\92c56fa2a6c4d5ba_0 | binary | |
MD5:— | SHA256:— | |||
| 3680 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\0786087c3c360803_0 | binary | |
MD5:— | SHA256:— | |||
| 3680 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\983b7a3da8f39a46_0 | binary | |
MD5:— | SHA256:— | |||
| 3680 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\8c84d92a9dbce3e0_0 | binary | |
MD5:— | SHA256:— | |||
| 3680 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\72d9f526d2e2e7c8_0 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
119
DNS requests
76
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
2916 | AcroRd32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2240 | iexplore.exe | GET | 200 | 18.64.100.21:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2240 | iexplore.exe | GET | 200 | 18.66.242.62:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2240 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?484abd3473abf4d4 | US | compressed | 60.0 Kb | whitelisted |
2240 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f30d039003610910 | US | compressed | 60.0 Kb | whitelisted |
128 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6uhcfbxlex6uvq35lxbiuo4pua_9.35.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.35.0_all_ou4l2poiq7vz5pxjtnyxcnyqx4.crx3 | US | binary | 9.73 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6uhcfbxlex6uvq35lxbiuo4pua_9.35.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.35.0_all_ou4l2poiq7vz5pxjtnyxcnyqx4.crx3 | US | binary | 7.38 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac6uhcfbxlex6uvq35lxbiuo4pua_9.35.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.35.0_all_ou4l2poiq7vz5pxjtnyxcnyqx4.crx3 | US | binary | 9.73 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3680 | RdrCEF.exe | 23.35.236.137:443 | geo2.adobe.com | Zayo Bandwidth Inc | US | suspicious |
3680 | RdrCEF.exe | 3.219.243.226:443 | p13n.adobe.io | — | US | unknown |
2916 | AcroRd32.exe | 23.48.23.34:443 | acroipm2.adobe.com | TRUE INTERNET Co.,Ltd. | US | suspicious |
3680 | RdrCEF.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
2916 | AcroRd32.exe | 23.216.77.69:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
2916 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2240 | iexplore.exe | 151.101.130.133:443 | linktr.ee | Fastly | US | malicious |
2240 | iexplore.exe | 13.224.198.19:443 | assets.production.linktr.ee | — | US | unknown |
2240 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2240 | iexplore.exe | 104.90.178.254:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
geo2.adobe.com |
| whitelisted |
p13n.adobe.io |
| whitelisted |
armmf.adobe.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
linktr.ee |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
assets.production.linktr.ee |
| whitelisted |
o.ss2.us |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO TLS Handshake Failure |