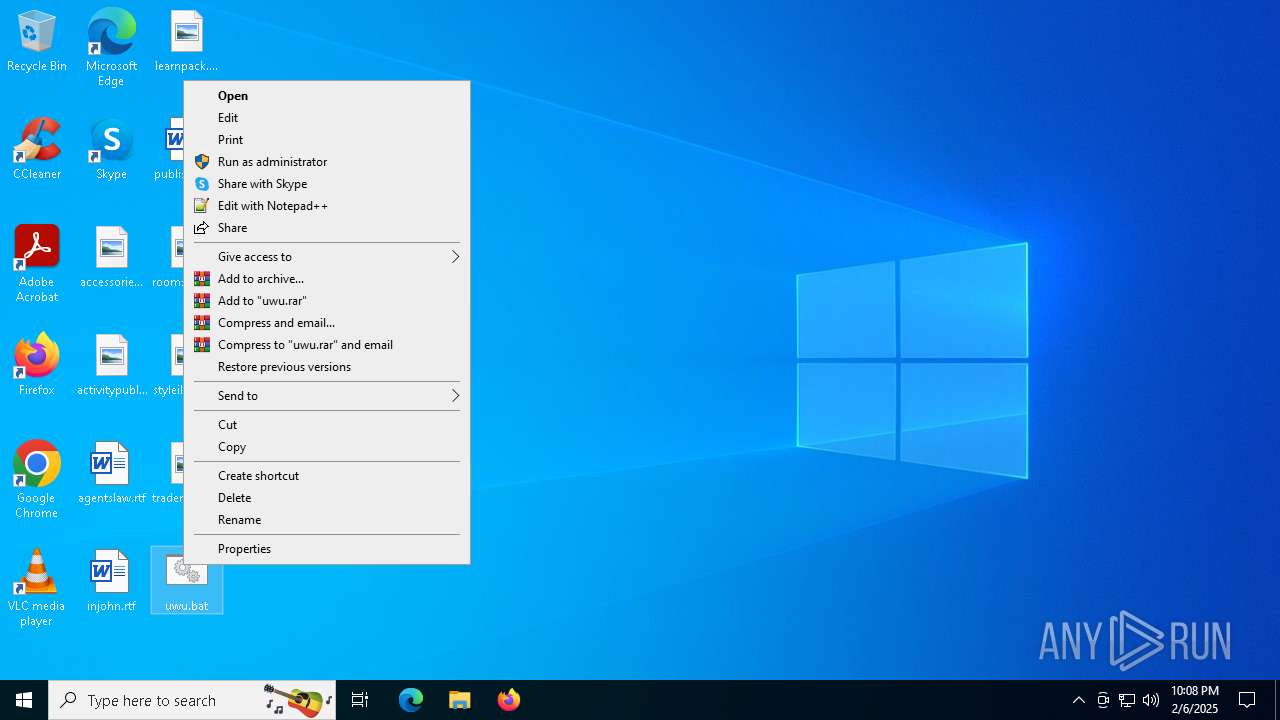
| File name: | uwu.bat |
| Full analysis: | https://app.any.run/tasks/5cf8b004-2312-4125-9e05-2bf861171e20 |
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2025, 22:07:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 6F42DDA81E30FE0502F8D9800ED43085 |
| SHA1: | 40F6D61021595323D0E0A2C6B2E1886259BBFC37 |
| SHA256: | 9724E479130A1D629396F74322C663AE46D3C98B2F60DF2AE8D174577C0F3B15 |
| SSDEEP: | 48:0WvldBNDWeldccs7GqeSIHADRVPK4xld9cK4T9Frlda9ZjOTy5PM8S:0eDLNDBsTDzPKgDuKsDSw58S |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 1556)
- net.exe (PID: 6876)
- net.exe (PID: 6224)
- cmd.exe (PID: 5752)
- net.exe (PID: 2796)
- net.exe (PID: 3560)
- cmd.exe (PID: 6492)
- net.exe (PID: 2792)
- cmd.exe (PID: 6056)
- cmd.exe (PID: 6696)
Starts process via Powershell
- powershell.exe (PID: 6276)
- powershell.exe (PID: 6252)
Executing commands from a ".bat" file
- powershell.exe (PID: 6276)
- powershell.exe (PID: 6252)
Executable content was dropped or overwritten
- curl.exe (PID: 6952)
- curl.exe (PID: 6920)
- curl.exe (PID: 3736)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5752)
- cmd.exe (PID: 1556)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6252)
- powershell.exe (PID: 6276)
INFO
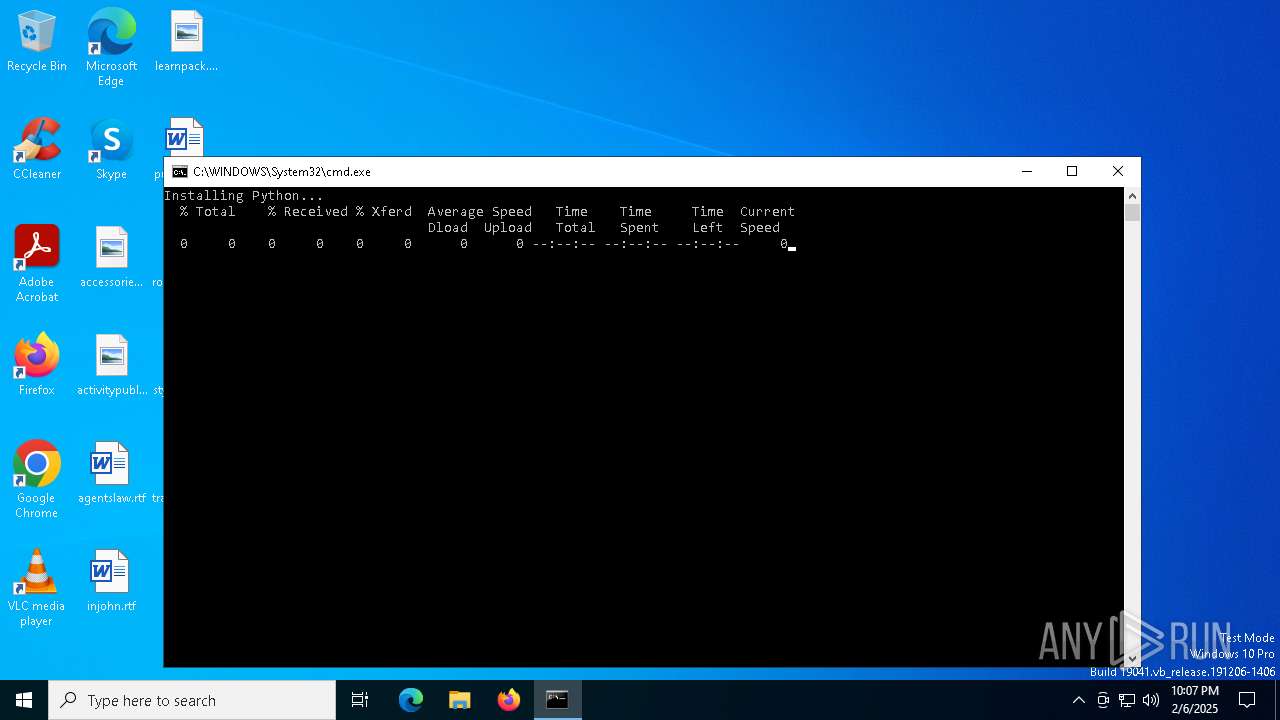
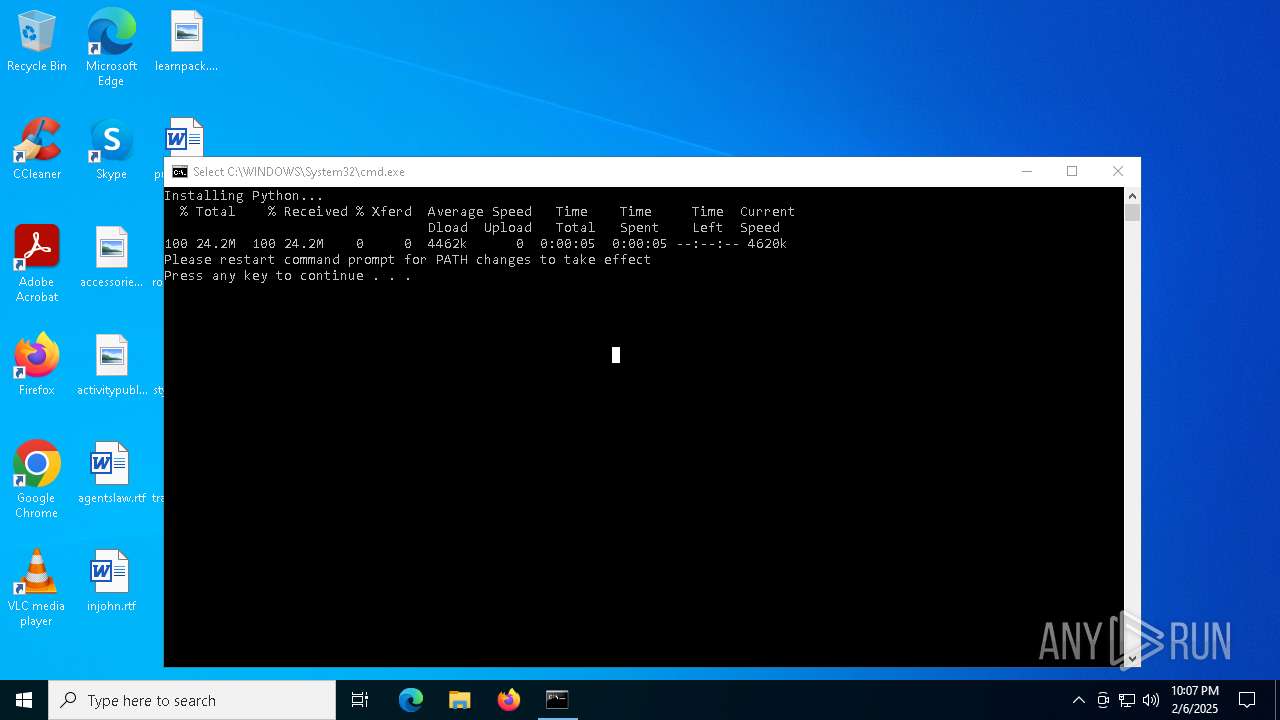
Execution of CURL command
- cmd.exe (PID: 6696)
- cmd.exe (PID: 6492)
- cmd.exe (PID: 6056)
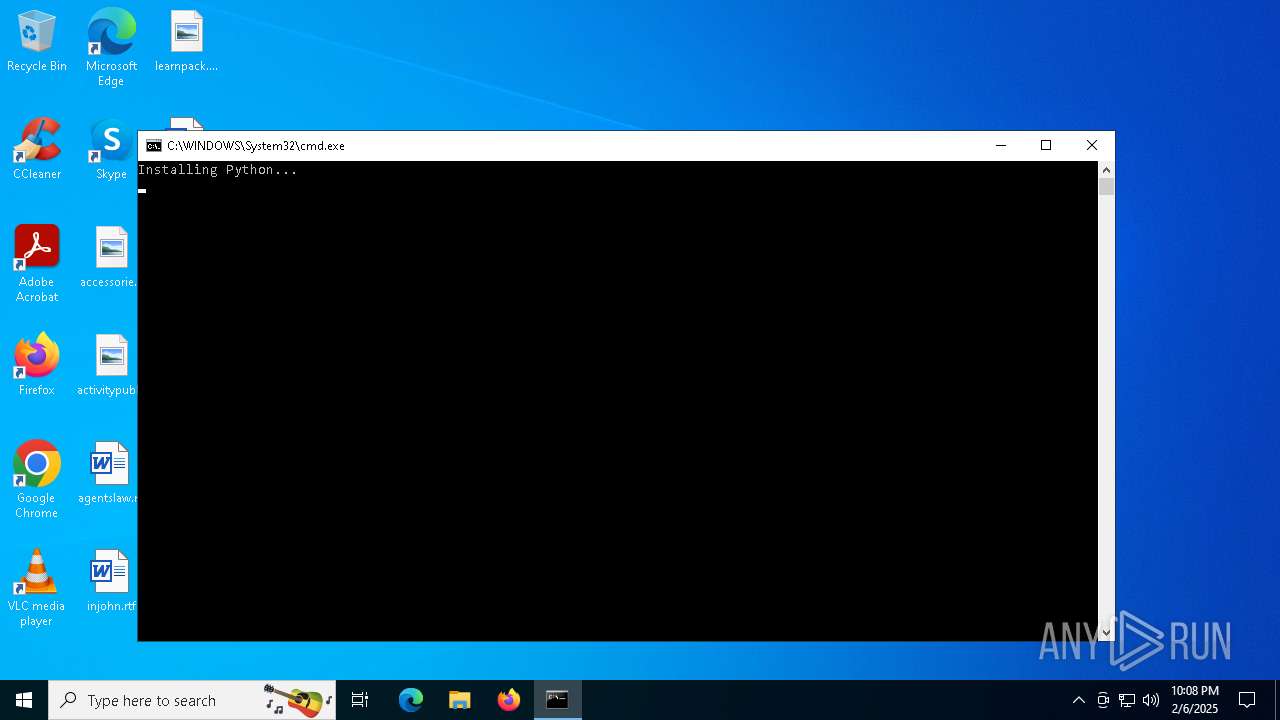
Checks supported languages
- curl.exe (PID: 6952)
- curl.exe (PID: 6920)
- python_installer.exe (PID: 6876)
- python_installer.exe (PID: 7100)
Reads the computer name
- curl.exe (PID: 6952)
- curl.exe (PID: 6920)
The sample compiled with english language support
- curl.exe (PID: 6952)
- curl.exe (PID: 6920)
- curl.exe (PID: 3736)
Create files in a temporary directory
- python_installer.exe (PID: 7100)
- python_installer.exe (PID: 6876)
- python_installer.exe (PID: 6688)
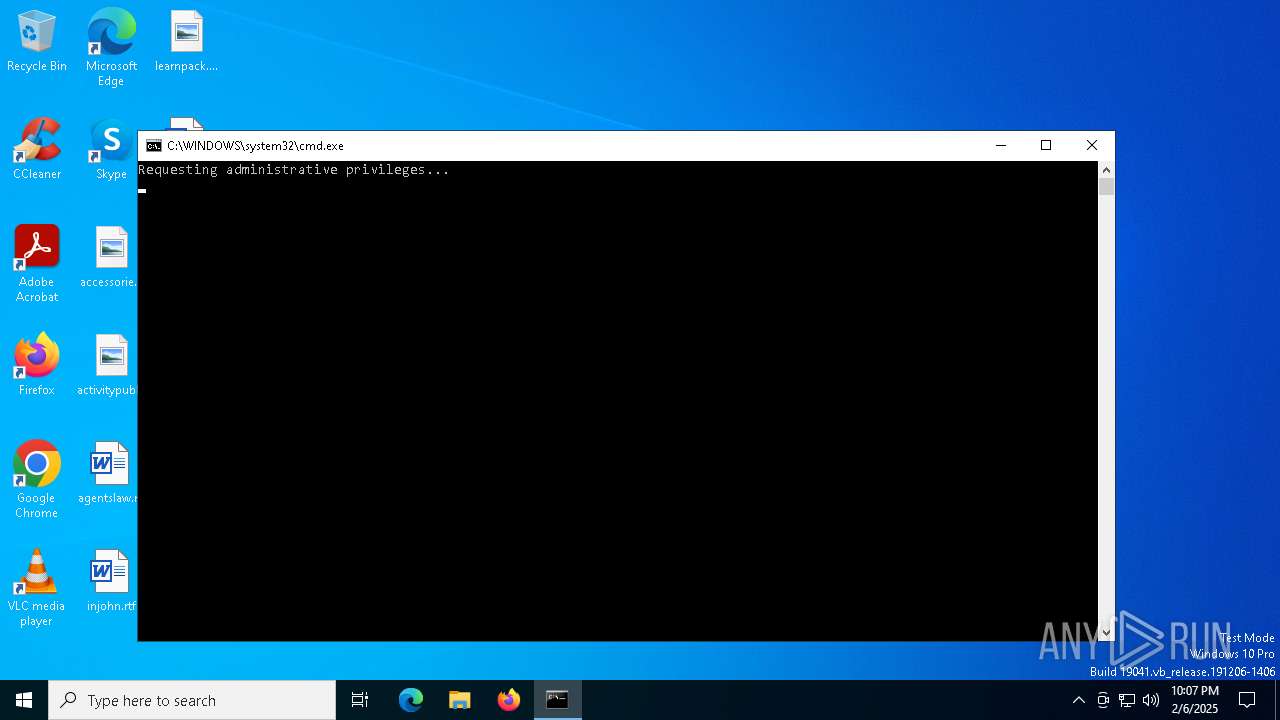
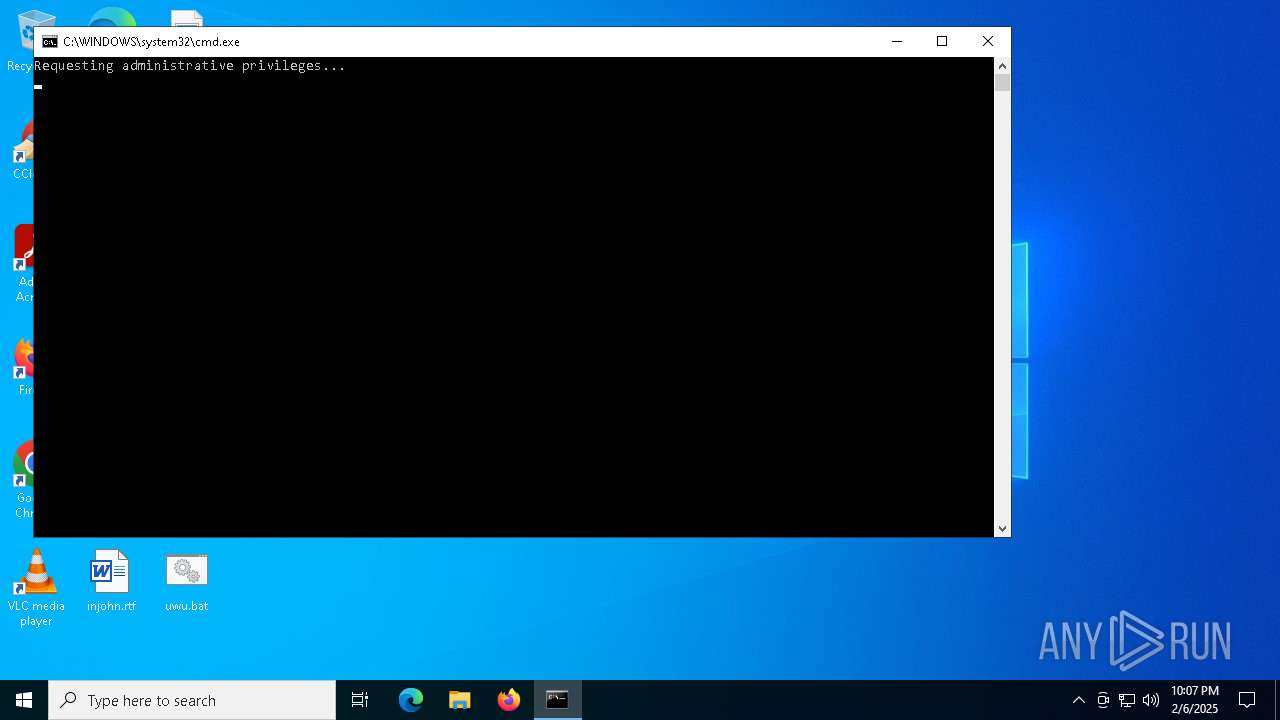
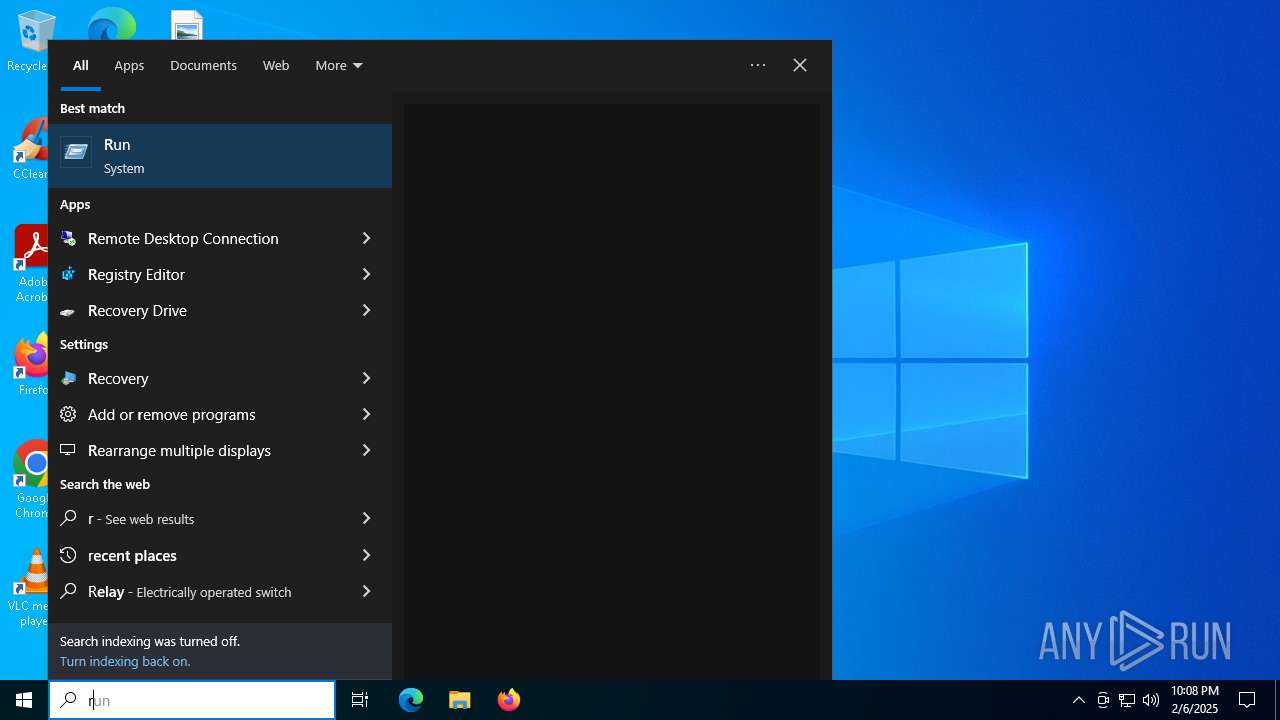
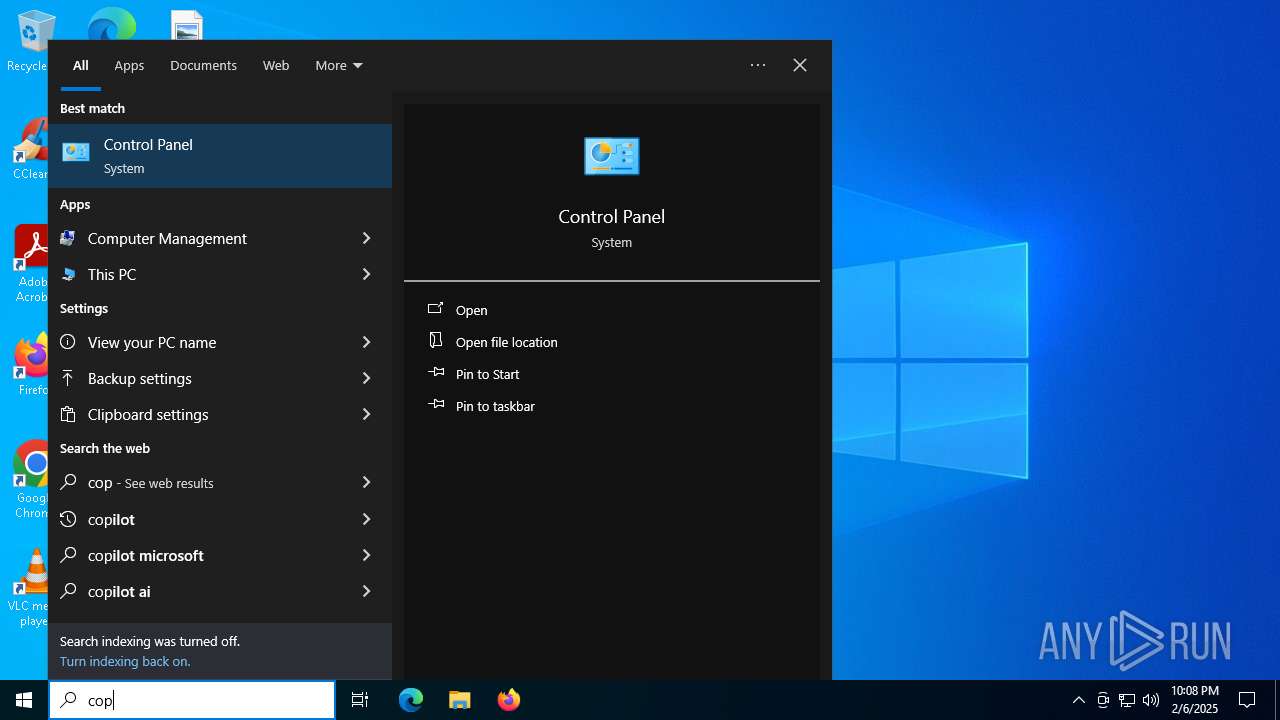
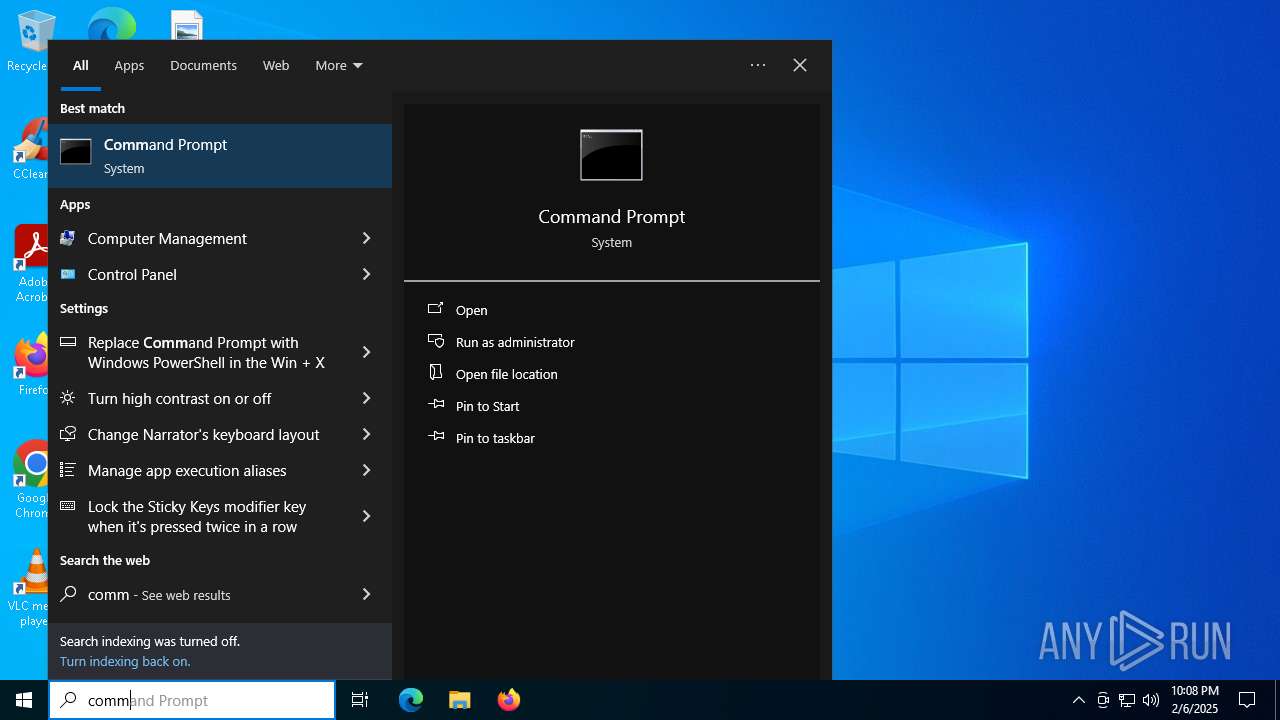
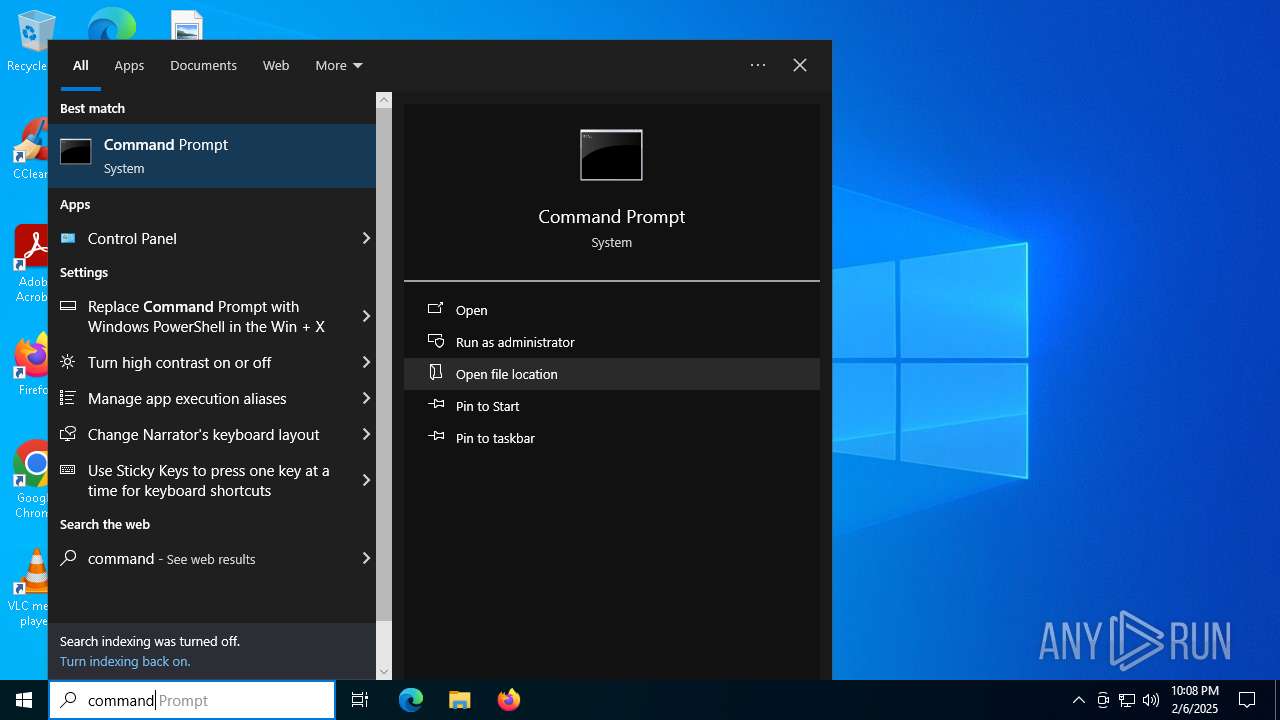
Manual execution by a user
- cmd.exe (PID: 5752)
- cmd.exe (PID: 6056)
- cmd.exe (PID: 876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
166
Monitored processes
33
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
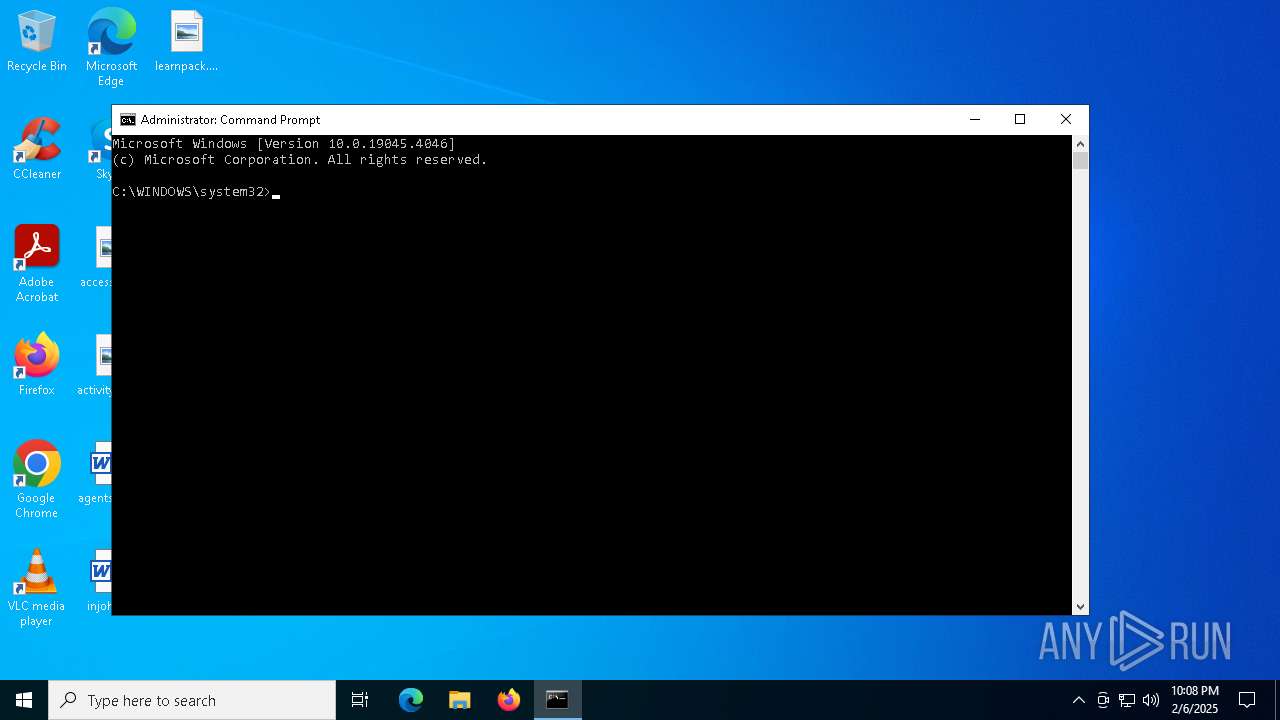
| 876 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\uwu.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | C:\WINDOWS\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2792 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2796 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3560 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
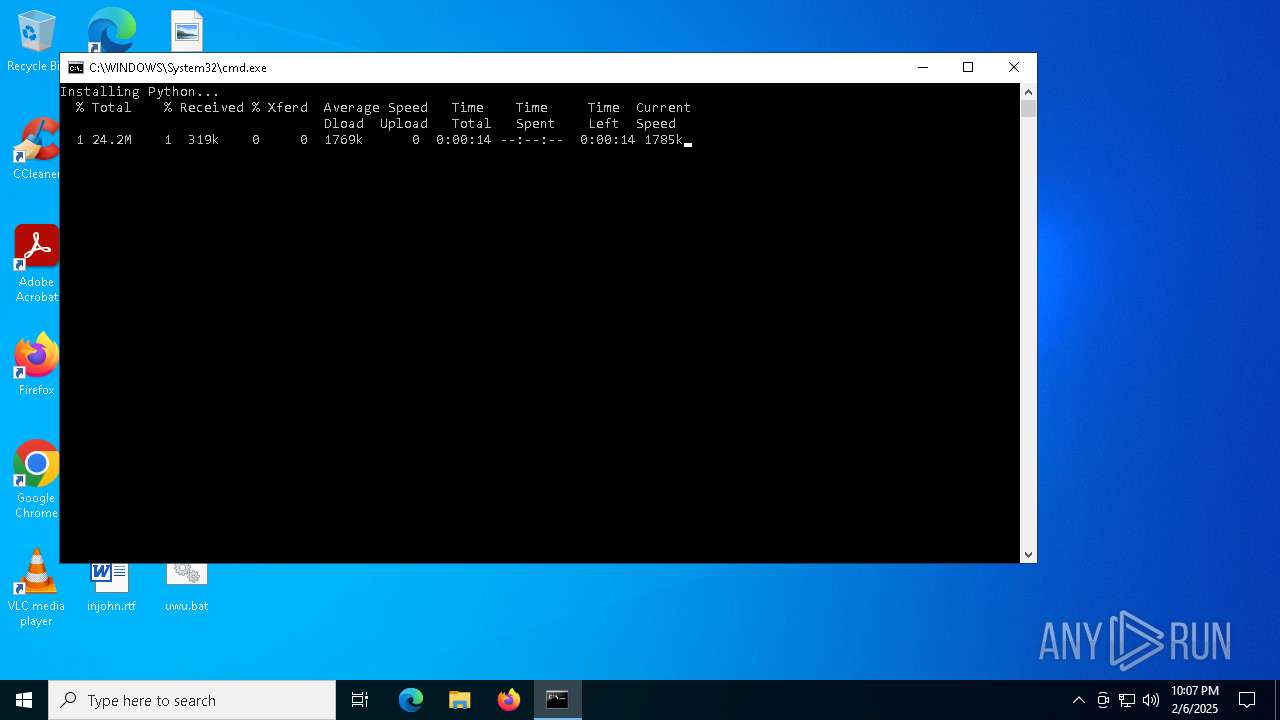
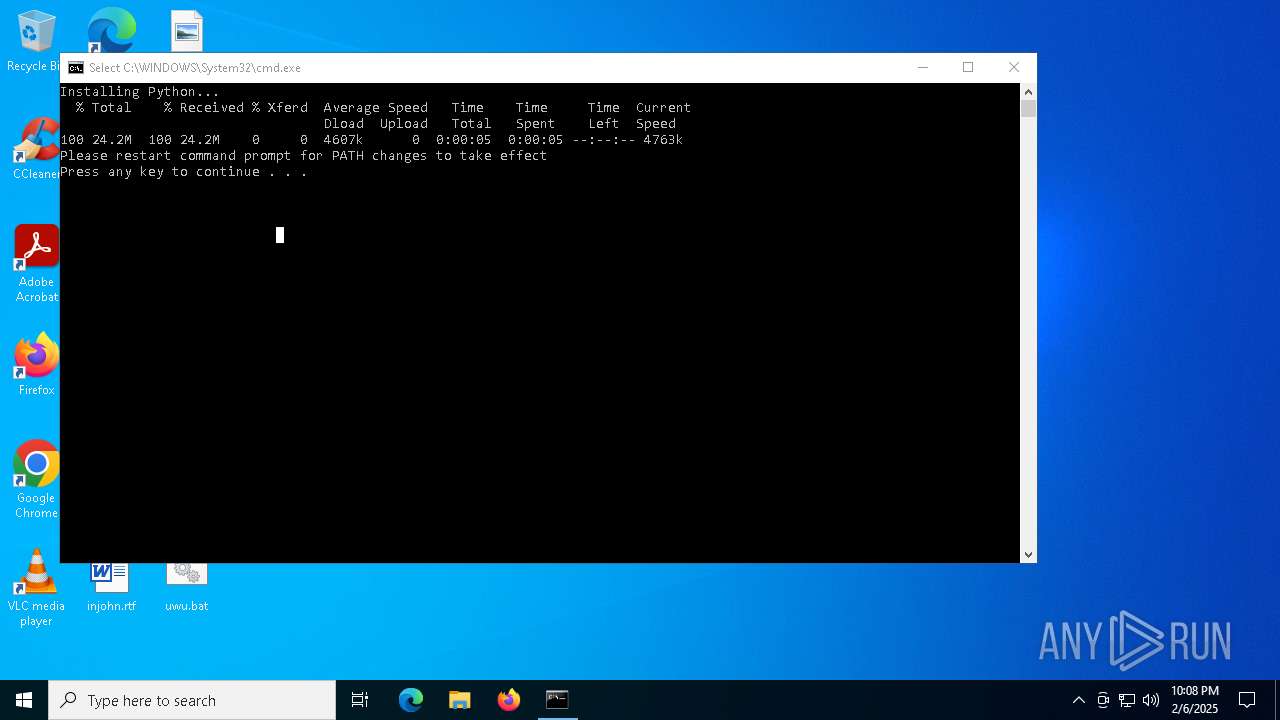
| 3736 | curl -L "https://www.python.org/ftp/python/3.11.4/python-3.11.4-amd64.exe" -o python_installer.exe | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 3796 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4228 | C:\WINDOWS\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 970
Read events
9 968
Write events
2
Delete events
0
Modification events
| (PID) Process: | (6276) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (6276) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
Executable files
3
Suspicious files
1
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6276 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lrg4am3i.xpm.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6276 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mrylkipu.1bw.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6876 | python_installer.exe | C:\Users\admin\AppData\Local\Temp\Setup_20250206220759_Failed.txt | text | |
MD5:510CE43F8E382237EE804CA1948E27F5 | SHA256:8ECF74A3E6D8970B05B741187C5568AF78611654640D48F65DF7CA1EE041D2B9 | |||
| 7100 | python_installer.exe | C:\Users\admin\AppData\Local\Temp\Setup_20250206220736_Failed.txt | text | |
MD5:7C267E1C8E77EC98E191FA26E6D0B7A0 | SHA256:38D1971E337B7BF83A774706FC56475259A34E114A3A8E5EC657A28A0FE3F42B | |||
| 6252 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ykktc1qj.cxy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6920 | curl.exe | C:\Windows\System32\python_installer.exe | executable | |
MD5:E4413BB7448CD13B437DFFFFBA294CA0 | SHA256:47BE821C0F1825D90FC40F83A3EE3D3A691A3E16C8E21AC0CD56371362AAAD50 | |||
| 6252 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_31zh3qm3.hpn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6952 | curl.exe | C:\Windows\System32\python_installer.exe | executable | |
MD5:E4413BB7448CD13B437DFFFFBA294CA0 | SHA256:47BE821C0F1825D90FC40F83A3EE3D3A691A3E16C8E21AC0CD56371362AAAD50 | |||
| 3736 | curl.exe | C:\Windows\System32\python_installer.exe | executable | |
MD5:E4413BB7448CD13B437DFFFFBA294CA0 | SHA256:47BE821C0F1825D90FC40F83A3EE3D3A691A3E16C8E21AC0CD56371362AAAD50 | |||
| 6276 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:48C7AFD44AD87FA64CC46E73255DD96B | SHA256:E78DA3DEFB13225CCBEDA9A409232EDFDC5FBE1132EA4A01CF3C9AA4135AEDF3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
43
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
760 | lsass.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEQCATgA6JyvFGONNpLH8m3gz | unknown | — | — | whitelisted |
5568 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
624 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
624 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.32:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 92.123.104.32:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.126.31.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
www.python.org |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |