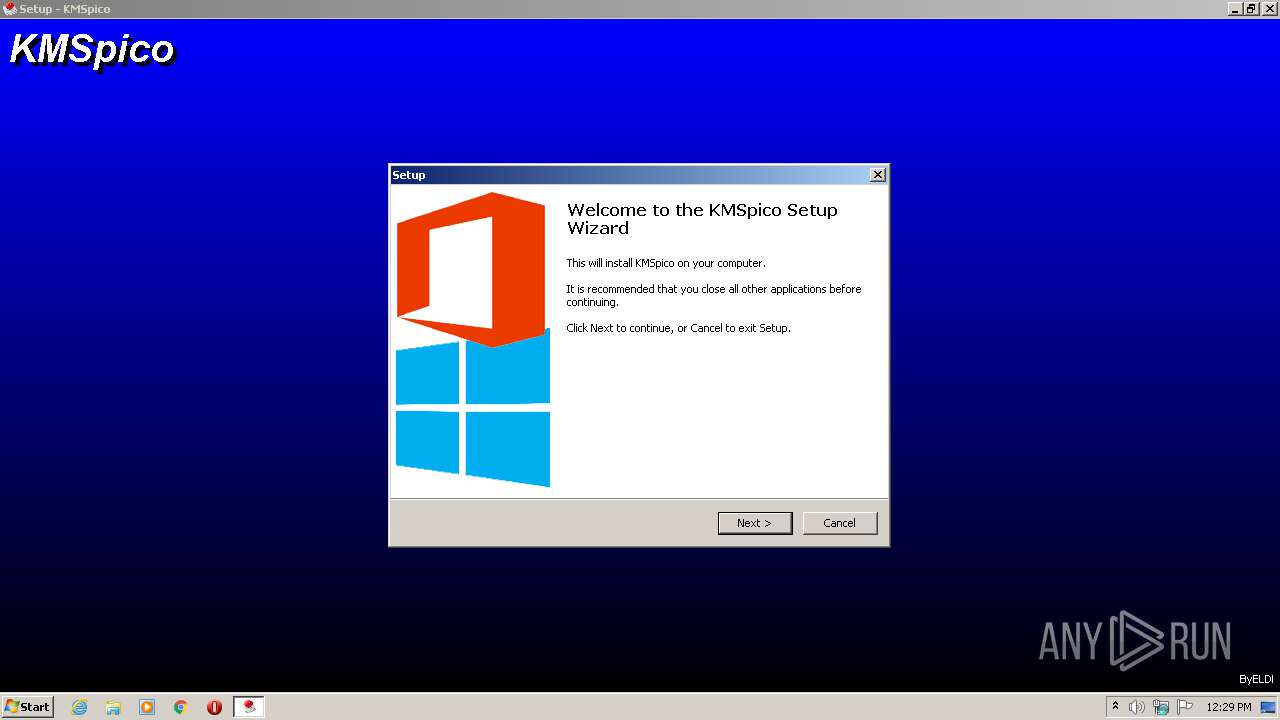
| File name: | KMSpico-setup.exe |
| Full analysis: | https://app.any.run/tasks/8c6ef5d1-9d6e-4e50-b22e-5656a3ce431d |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 11:29:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 32C5B78B878C0495F1353721896802F1 |
| SHA1: | EBA77061AB00834950234610943DB7214C3AD8BA |
| SHA256: | 9711E4EFBD1D81CAF686CCFE4A8C09A914B803730F64FA1A66D0F5FE088B9266 |
| SSDEEP: | 98304:Q5ospckWBpuA/SFwh/8Oghve39yPWwfioKLsV0Rhi4pn3AUXNoDSzWeBd:NspcNpuA/Smh/ghvKXY0RM4pnwURzv |
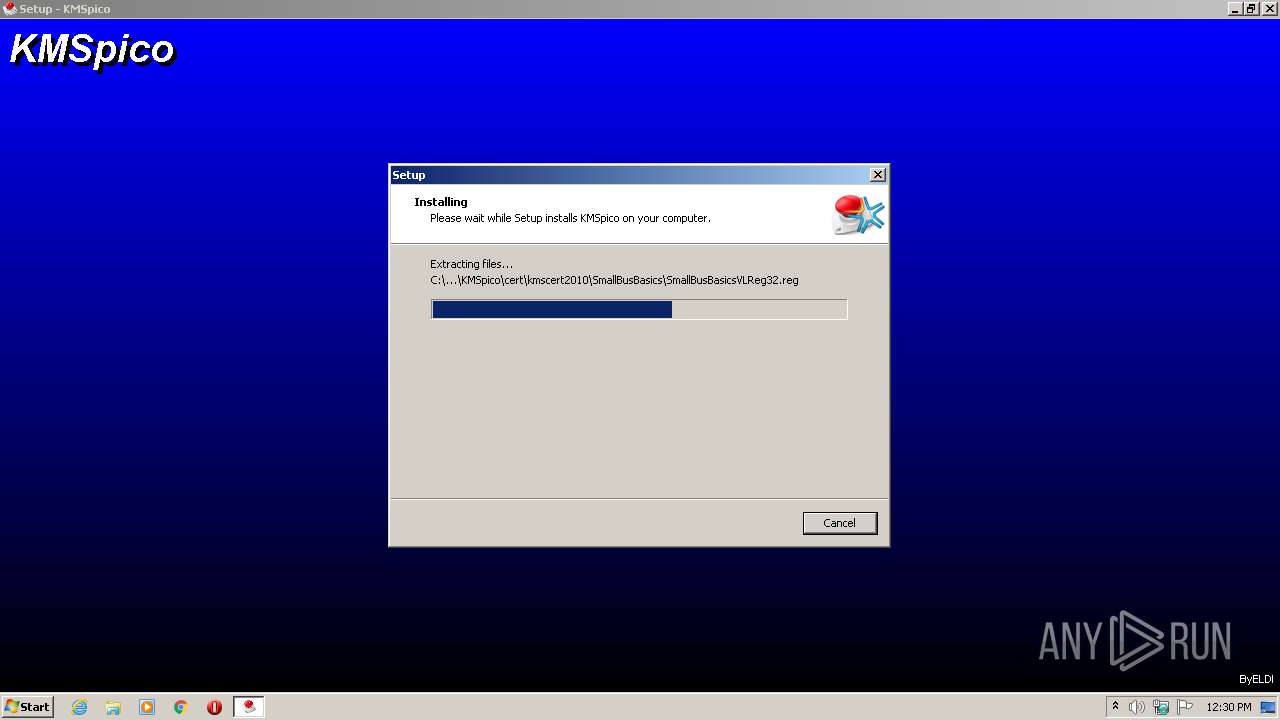
MALICIOUS
Uses Task Scheduler to run other applications
- KMSpico-setup.tmp (PID: 2416)
- cmd.exe (PID: 2152)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2792)
- schtasks.exe (PID: 1000)
- schtasks.exe (PID: 308)
- schtasks.exe (PID: 2792)
Uses Task Scheduler to autorun other applications
- KMSpico-setup.tmp (PID: 2416)
Application was dropped or rewritten from another process
- KMSELDI.exe (PID: 2916)
- UninsHs.exe (PID: 2424)
- AutoPico.exe (PID: 1016)
SUSPICIOUS
Executable content was dropped or overwritten
- KMSpico-setup.exe (PID: 2876)
- KMSpico-setup.tmp (PID: 2416)
- KMSpico-setup.exe (PID: 3360)
- KMSpico-setup.exe (PID: 3300)
- _setup.exe (PID: 3924)
- _setup.tmp (PID: 1836)
Uses TASKKILL.EXE to kill process
- KMSpico-setup.tmp (PID: 2416)
Starts SC.EXE for service management
- KMSpico-setup.tmp (PID: 2416)
- cmd.exe (PID: 2160)
Creates files in the program directory
- KMSELDI.exe (PID: 2916)
- AutoPico.exe (PID: 1016)
Creates files in the Windows directory
- _setup.tmp (PID: 1836)
Modifies the phishing filter of IE
- _setup.tmp (PID: 1836)
Starts CMD.EXE for commands execution
- _setup.tmp (PID: 1836)
Creates or modifies windows services
- KMSELDI.exe (PID: 2916)
Reads Environment values
- KMSELDI.exe (PID: 2916)
- AutoPico.exe (PID: 1016)
INFO
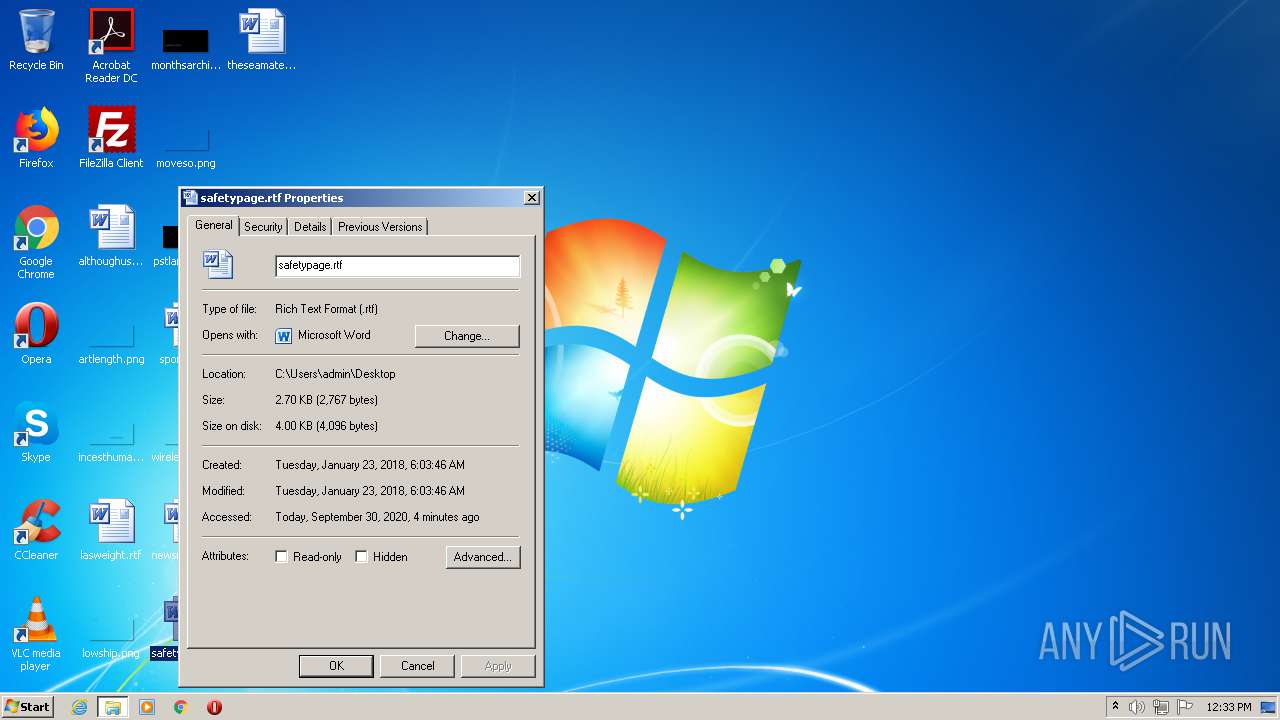
Application was dropped or rewritten from another process
- KMSpico-setup.tmp (PID: 3956)
- KMSpico-setup.tmp (PID: 3320)
- KMSpico-setup.tmp (PID: 2416)
- _setup.exe (PID: 3924)
- _setup.tmp (PID: 1836)
Creates files in the program directory
- KMSpico-setup.tmp (PID: 2416)
- _setup.tmp (PID: 1836)
Loads dropped or rewritten executable
- KMSpico-setup.tmp (PID: 3956)
- KMSpico-setup.tmp (PID: 2416)
- _setup.tmp (PID: 1836)
Creates a software uninstall entry
- _setup.tmp (PID: 1836)
Reads Microsoft Office registry keys
- KMSELDI.exe (PID: 2916)
- AutoPico.exe (PID: 1016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41472 |
| InitializedDataSize: | 80384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa98 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.2.0.0 |
| ProductVersionNumber: | 10.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
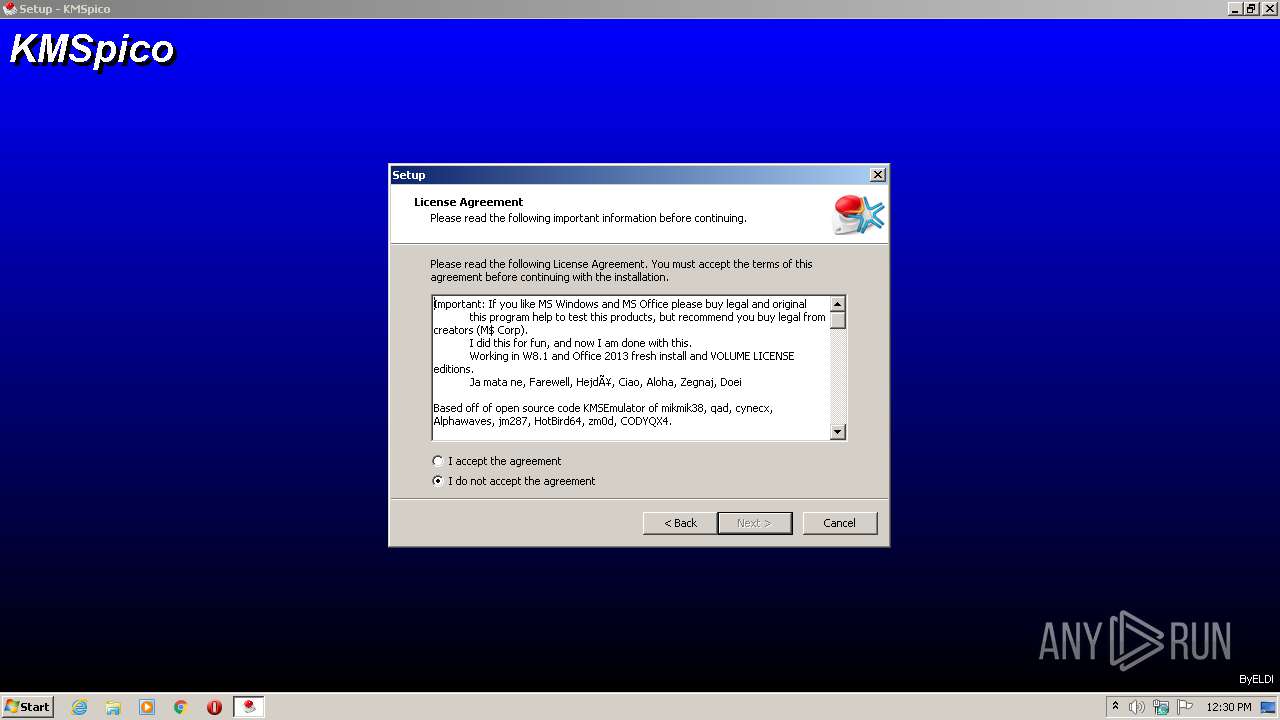
| CompanyName: | ByELDI |
| FileDescription: | KMSpico Setup |
| FileVersion: | 10.2.0.0 |
| LegalCopyright: | Copyright © 1997-2020 ByELDI |
| ProductName: | KMSpico |
| ProductVersion: | 10.2.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | ByELDI |
| FileDescription: | KMSpico Setup |
| FileVersion: | 10.2.0.0 |
| LegalCopyright: | Copyright © 1997-2020 ByELDI |
| ProductName: | KMSpico |
| ProductVersion: | 10.2.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A1D0 | 0x0000A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64375 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74012 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x0000091C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x000128E8 | 0x00012A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.07148 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | Latin 1 / Western European | UNKNOWN | RT_STRING |
11111 | 4.62922 | 44 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
MAINICON | 1.98048 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
79
Monitored processes
26
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "schtasks.exe" /Create /F /SC ONLOGON /RL HIGHEST /TN "KMSpico Automatic Update Scheduler" /TR "\"C:\Program Files\Common Files\KMSpico\kmsupd.exe\" | C:\Windows\system32\schtasks.exe | — | KMSpico-setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 492 | sc create "Service KMSELDI" binPath= "C:\Program Files\KMSpico\Service_KMS.exe" type= own error= normal start= auto DisplayName= "Service KMSELDI" | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1000 | "schtasks.exe" /Create /F /SC WEEKLY /D WED,SUN /ST 12:00 /RL HIGHEST /TN "Optimize Thumbnail Cache" /TR "\"C:\ProgramData\InstallShield\Updater\isupdate.exe\" | C:\Windows\system32\schtasks.exe | — | KMSpico-setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Program Files\KMSpico\AutoPico.exe" /silent | C:\Program Files\KMSpico\AutoPico.exe | _setup.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: AutoPico Exit code: 0 Version: 16.1.0.0 Modules
| |||||||||||||||
| 1352 | "sc.exe" delete isupdate.exe | C:\Windows\system32\sc.exe | — | KMSpico-setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1772 | "sc.exe" delete router.exe | C:\Windows\system32\sc.exe | — | KMSpico-setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | "C:\Users\admin\AppData\Local\Temp\is-C72VR.tmp\_setup.tmp" /SL5="$C016A,2952592,69120,C:\Users\admin\AppData\Local\Temp\is-4QVDK.tmp\_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-C72VR.tmp\_setup.tmp | _setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2152 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Task.cmd"" | C:\Windows\system32\cmd.exe | — | _setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2160 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Service.cmd"" | C:\Windows\system32\cmd.exe | — | _setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2284 | "sc.exe" delete ISUSPM.exe | C:\Windows\system32\sc.exe | — | KMSpico-setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 120
Read events
1 065
Write events
39
Delete events
16
Modification events
| (PID) Process: | (3956) KMSpico-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 740F0000C8811F051D97D601 | |||
| (PID) Process: | (3956) KMSpico-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: FFD48E5C909233704E041CA1E1CF15299DF39DB1C06D014461ABBFCDFEAF2AB8 | |||
| (PID) Process: | (3956) KMSpico-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3956) KMSpico-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3956) KMSpico-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3956) KMSpico-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3956) KMSpico-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: FFD48E5C909233704E041CA1E1CF15299DF39DB1C06D014461ABBFCDFEAF2AB8 | |||
| (PID) Process: | (3956) KMSpico-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 740F0000C8811F051D97D601 | |||
| (PID) Process: | (3956) KMSpico-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2416) KMSpico-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 70090000A04362051D97D601 | |||
Executable files
18
Suspicious files
2
Text files
411
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3956 | KMSpico-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-TUMJQ.tmp\idp.dll | — | |
MD5:— | SHA256:— | |||
| 2416 | KMSpico-setup.tmp | C:\Program Files\Common Files\KMSpico\is-816UA.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | KMSpico-setup.tmp | C:\ProgramData\InstallShield\Updater\is-0C032.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | KMSpico-setup.tmp | C:\Users\admin\AppData\Local\Temp\is-4QVDK.tmp\is-SL7GV.tmp | — | |
MD5:— | SHA256:— | |||
| 1836 | _setup.tmp | C:\Program Files\KMSpico\is-NNKHC.tmp | — | |
MD5:— | SHA256:— | |||
| 1836 | _setup.tmp | C:\Program Files\KMSpico\is-SGL1C.tmp | — | |
MD5:— | SHA256:— | |||
| 1836 | _setup.tmp | C:\Program Files\KMSpico\is-DI53G.tmp | — | |
MD5:— | SHA256:— | |||
| 1836 | _setup.tmp | C:\Program Files\KMSpico\is-4A19F.tmp | — | |
MD5:— | SHA256:— | |||
| 1836 | _setup.tmp | C:\Windows\system32\is-OMHFI.tmp | — | |
MD5:— | SHA256:— | |||
| 1836 | _setup.tmp | C:\Program Files\KMSpico\is-REQN9.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2916 | KMSELDI.exe | 129.70.132.36:123 | 2.pool.ntp.org | Verein zur Foerderung eines Deutschen Forschungsnetzes e.V. | DE | unknown |
1016 | AutoPico.exe | 185.17.146.64:123 | 2.pool.ntp.org | Leaseweb Deutschland GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
2.pool.ntp.org |
| whitelisted |