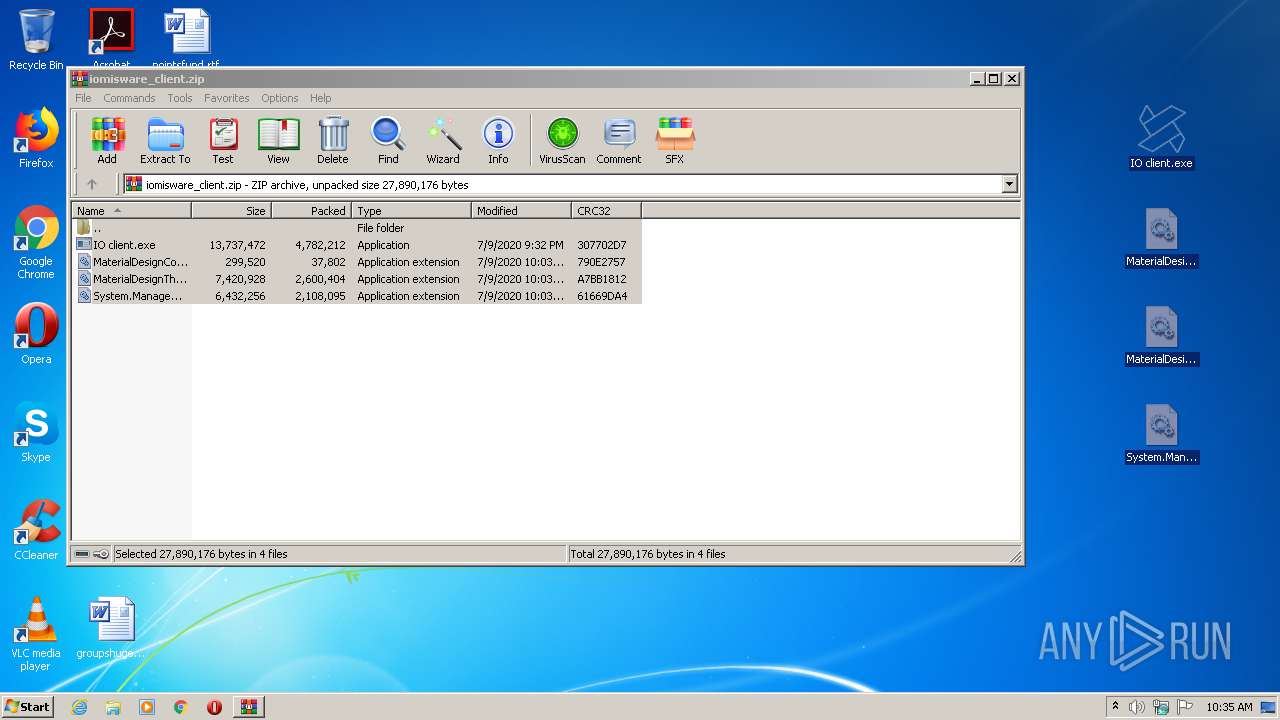
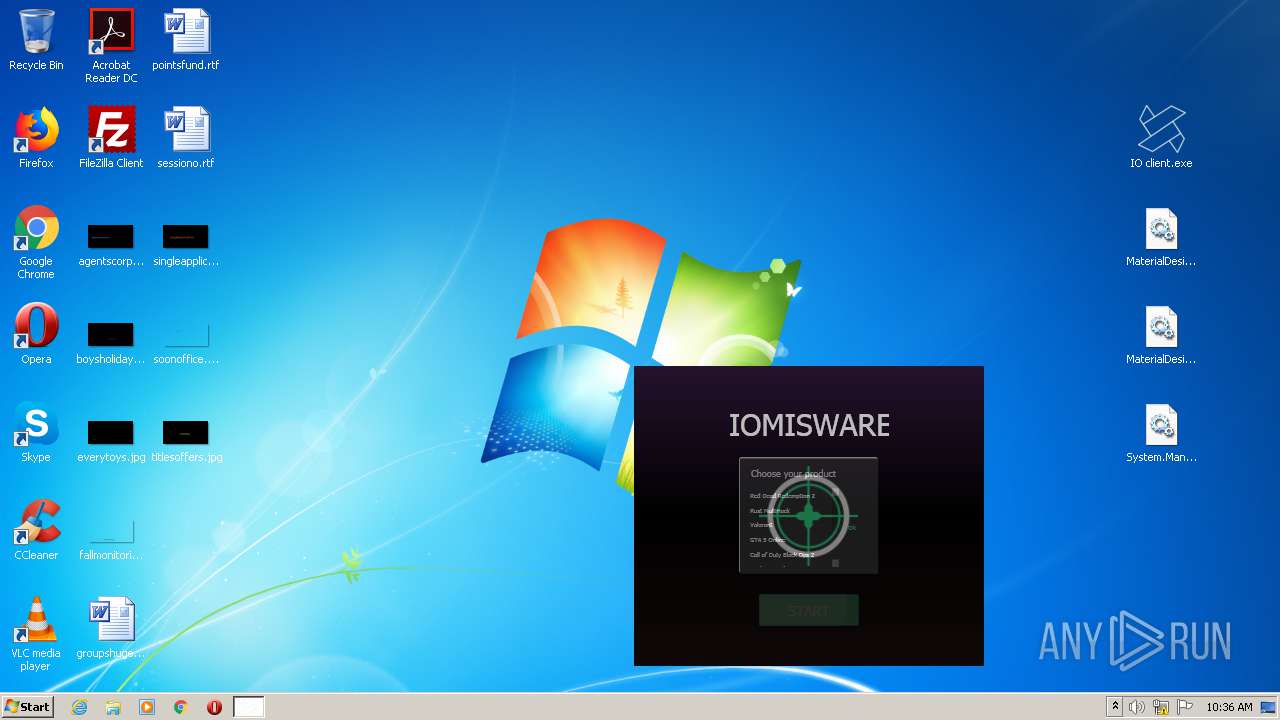
| File name: | iomisware_client.zip |
| Full analysis: | https://app.any.run/tasks/d7ac1814-4be7-4463-b81c-cbbc07325416 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 09:35:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | ADC4E55C29EB1321036BDF4FEFF46098 |
| SHA1: | FA703C5241920D900A0E17CF6207E0C44A5F3015 |
| SHA256: | 9706487F0AA445DA42FD61B6A2F9C11E366E9907478045E3115C19D4E22A7BFD |
| SSDEEP: | 196608:BYojSBIw1ZT1AqpAigXiW/Bg3kVaIipiUSR8Q7NINtFM:BLS2wrpAquiMTpnVaaGQeM |
MALICIOUS
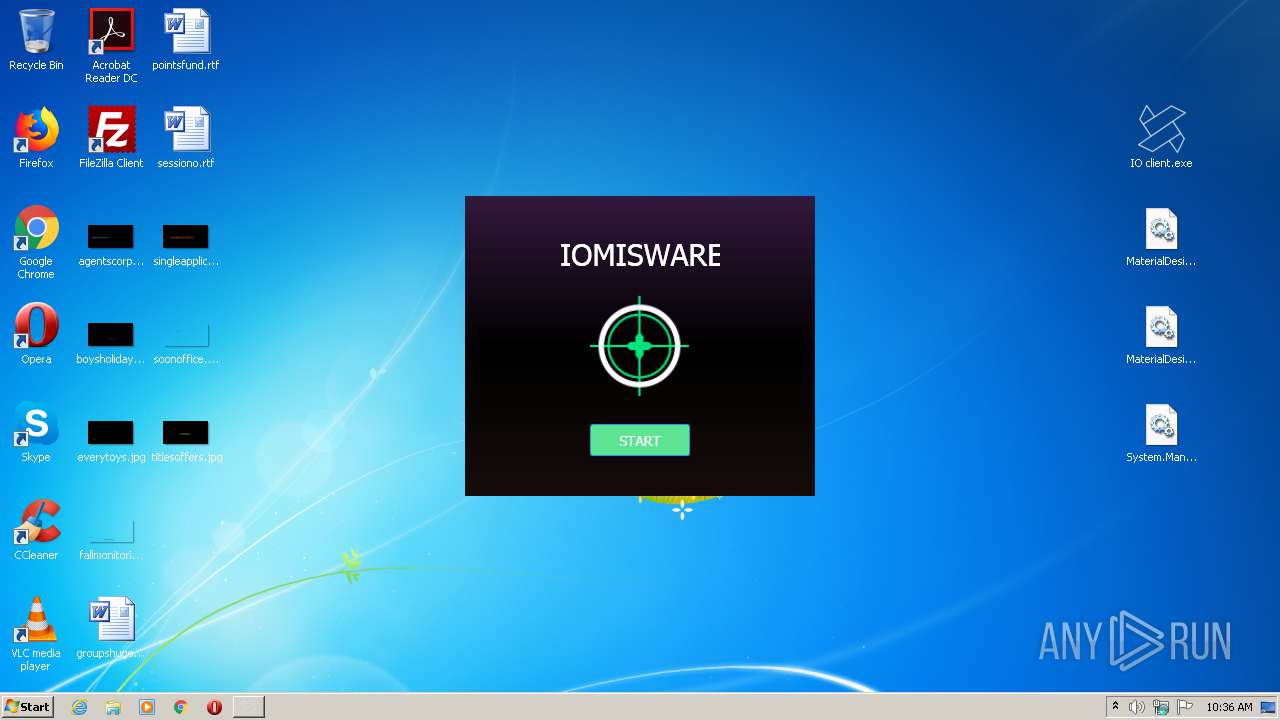
Application was dropped or rewritten from another process
- IO client.exe (PID: 696)
Loads dropped or rewritten executable
- IO client.exe (PID: 696)
- SearchProtocolHost.exe (PID: 532)
SUSPICIOUS
Executable content was dropped or overwritten
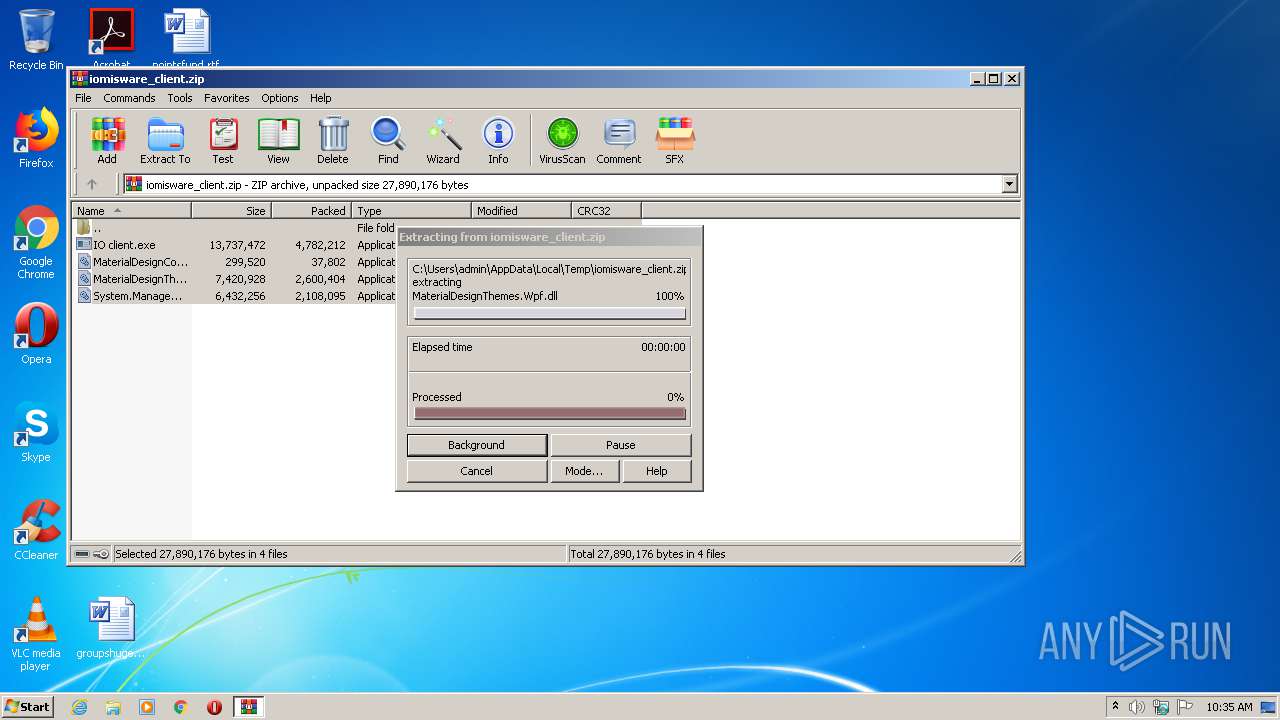
- WinRAR.exe (PID: 3088)
Reads Environment values
- IO client.exe (PID: 696)
INFO
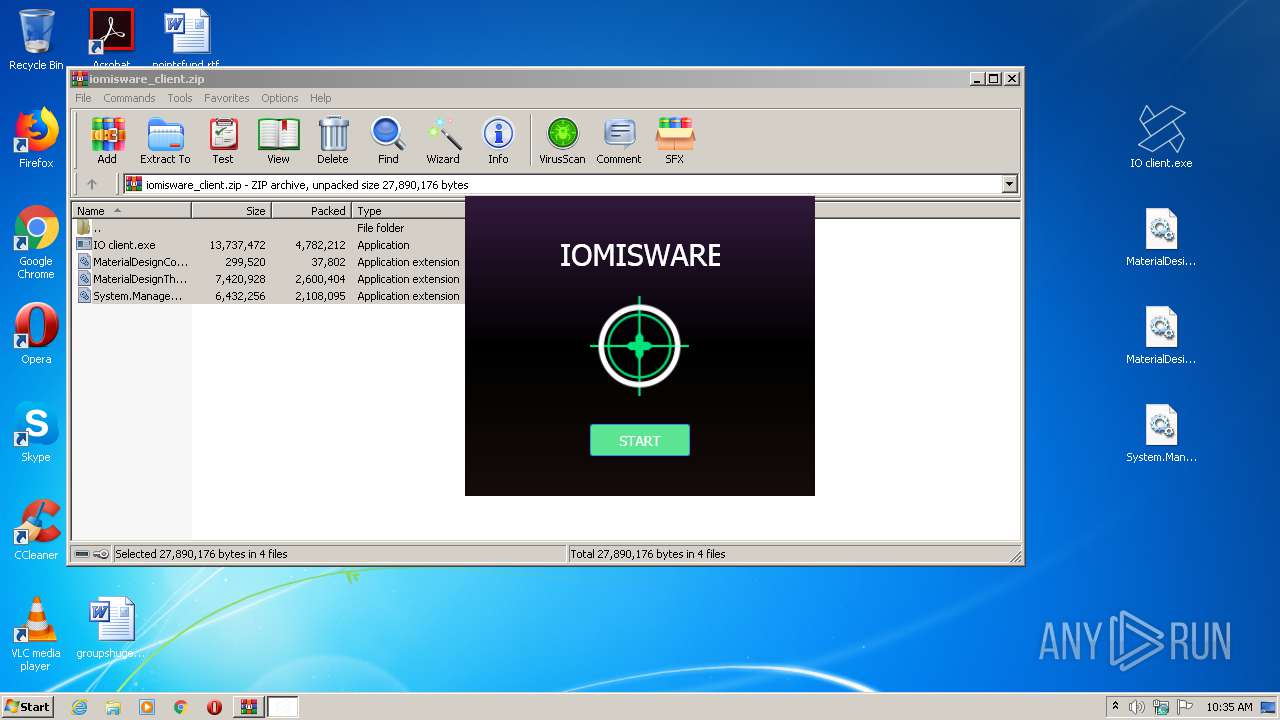
Manual execution by user
- IO client.exe (PID: 696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
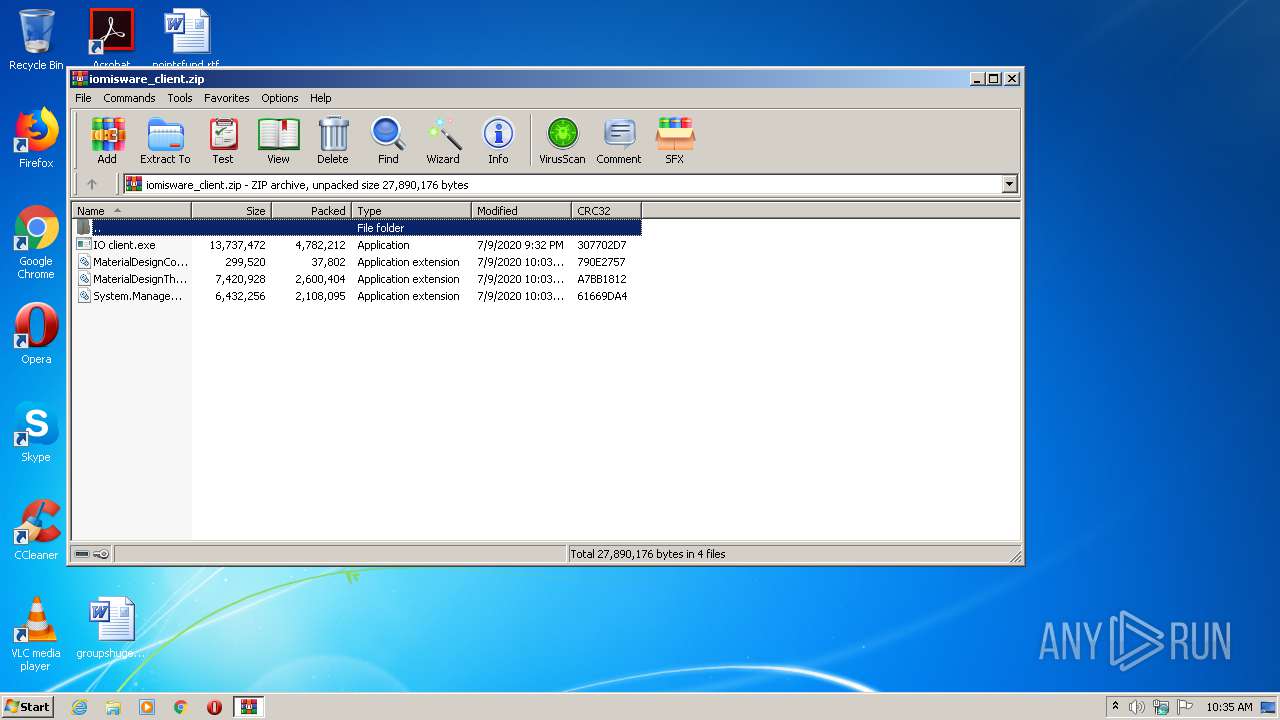
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:07:09 21:32:28 |
| ZipCRC: | 0x307702d7 |
| ZipCompressedSize: | 4782212 |
| ZipUncompressedSize: | 13737472 |
| ZipFileName: | IO client.exe |
Total processes
35
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 696 | "C:\Users\admin\Desktop\IO client.exe" | C:\Users\admin\Desktop\IO client.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: iomis loder Exit code: 0 Version: 4.5.6.8 Modules
| |||||||||||||||
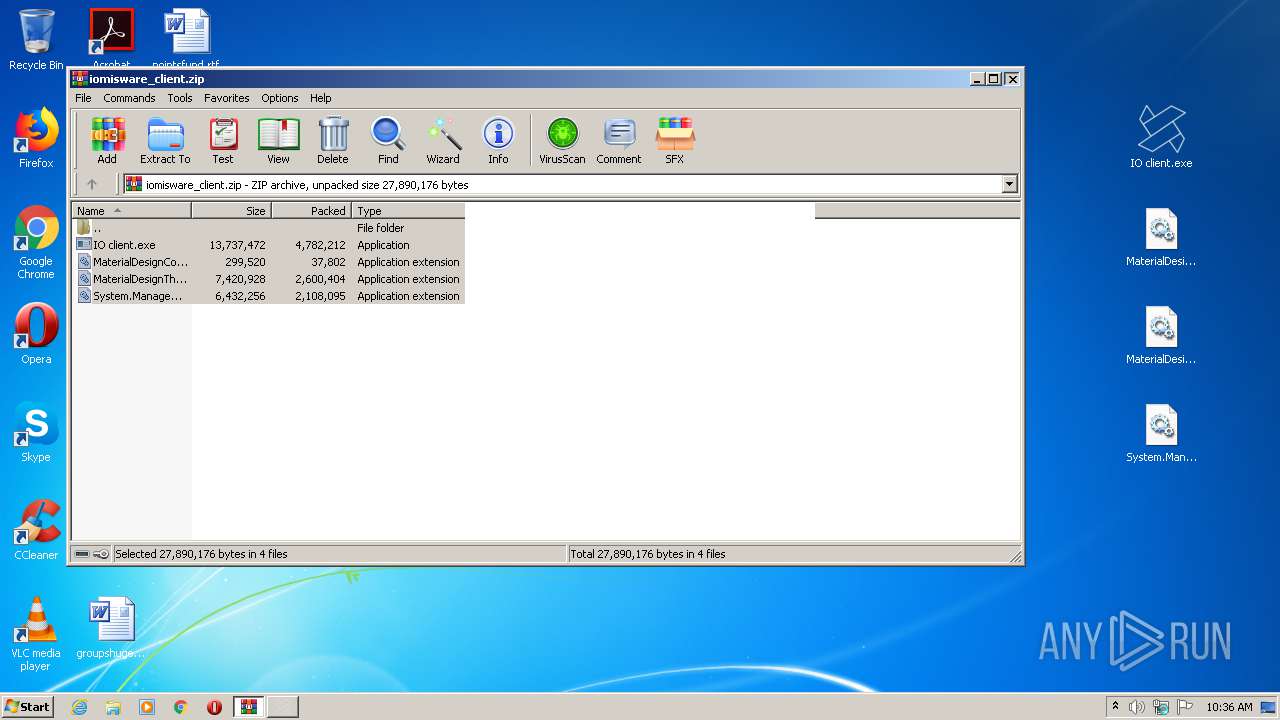
| 3088 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\iomisware_client.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
481
Read events
448
Write events
33
Delete events
0
Modification events
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\iomisware_client.zip | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (696) IO client.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: IO client.exe | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
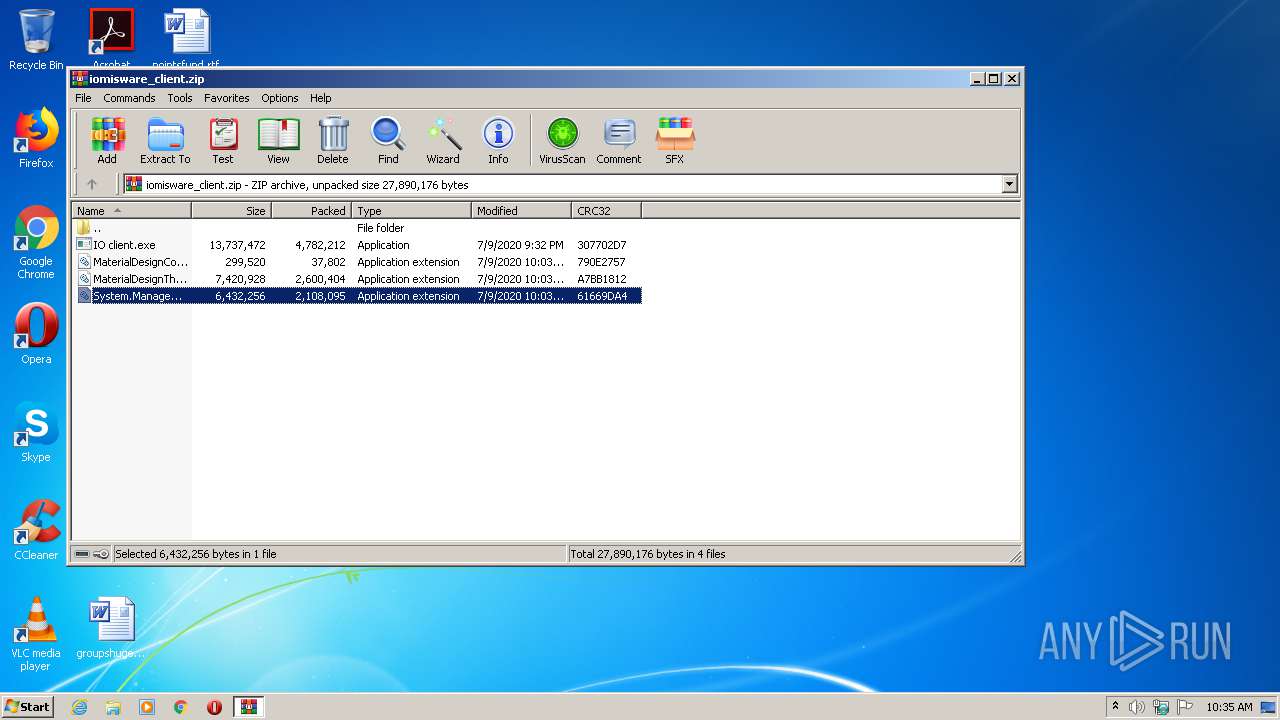
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3088.38480\System.Management.Automation.dll | — | |
MD5:— | SHA256:— | |||
| 3088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3088.38480\IO client.exe | executable | |
MD5:— | SHA256:— | |||
| 3088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3088.38480\MaterialDesignThemes.Wpf.dll | executable | |
MD5:FBD761926164043AC71EE9B83AB37FD1 | SHA256:013A42B8C6FFA29E2198EED4FAF6168247B6550A4C4ED5D82023A1D82A08E27E | |||
| 3088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3088.38480\MaterialDesignColors.dll | executable | |
MD5:39367419516F5F3DF9AB1F9E5D0BBCD5 | SHA256:976EEA4567656D536A6344B3834F958F2B9E27401B94C643681770437D5ABC68 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
696 | IO client.exe | GET | 200 | 195.2.92.143:80 | http://195.2.92.143/select_games.php | RU | text | 152 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 195.2.92.143:80 | — | Zenon N.S.P. | RU | malicious |