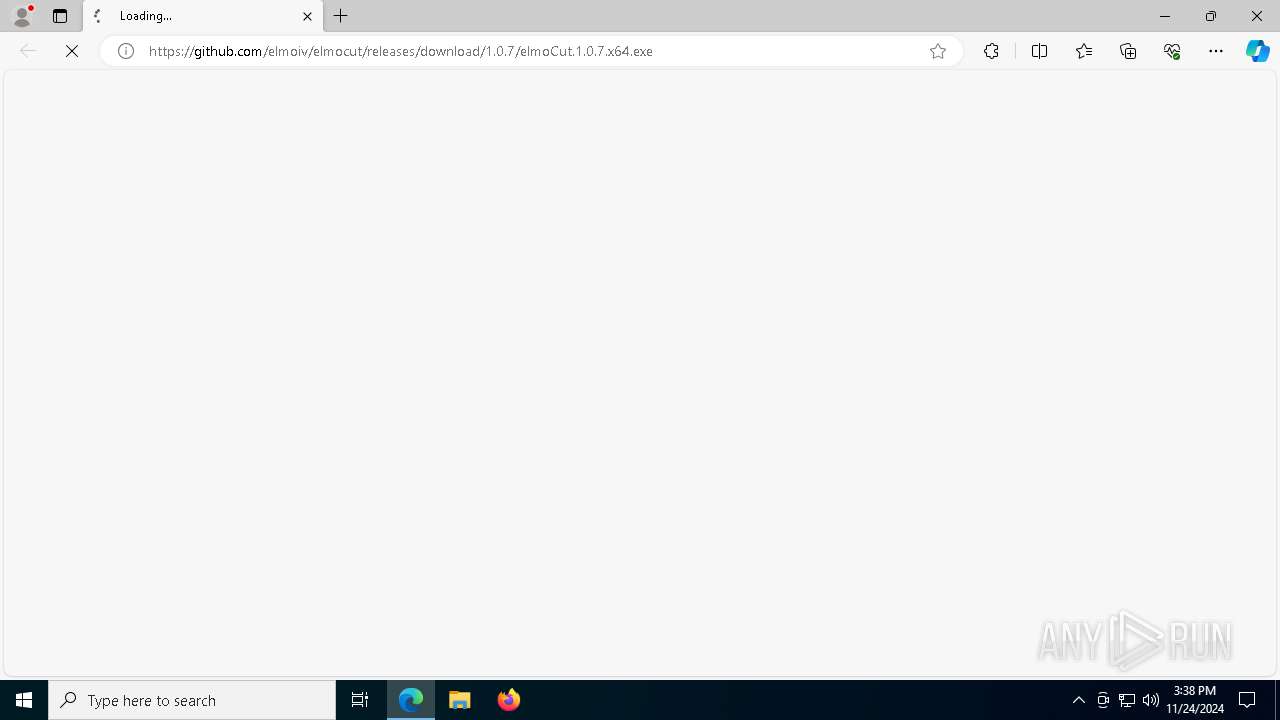
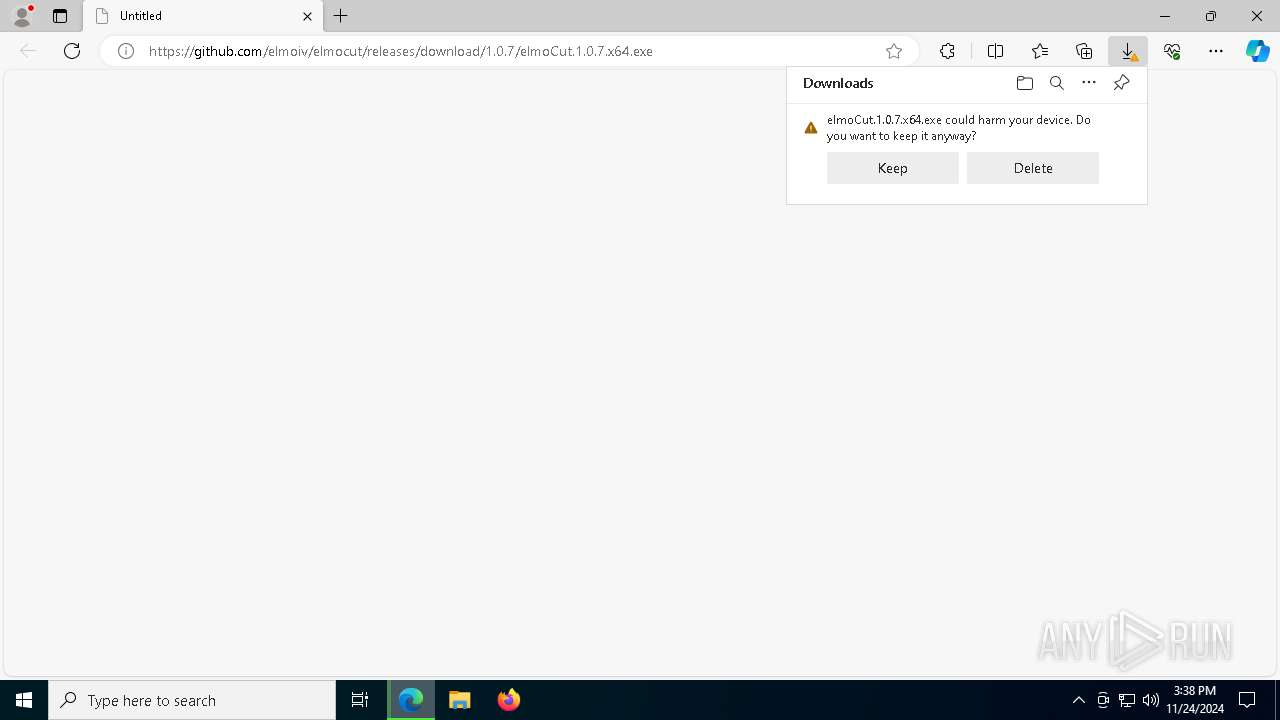
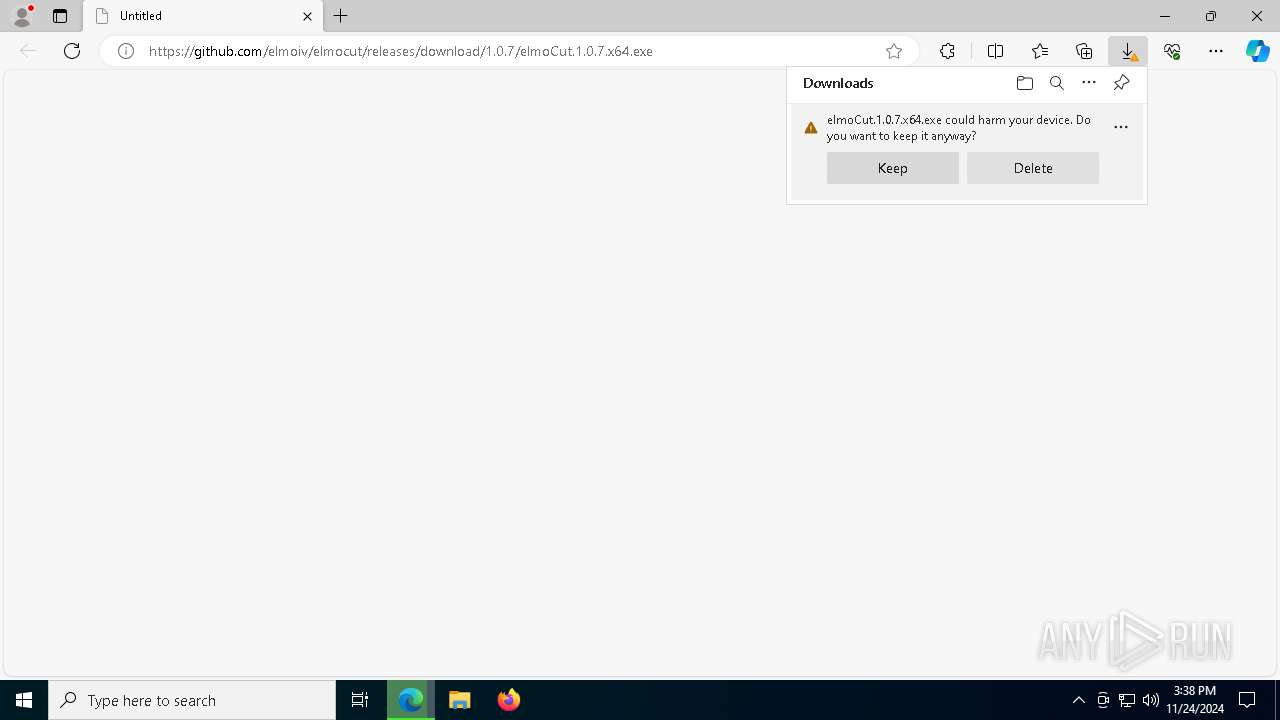
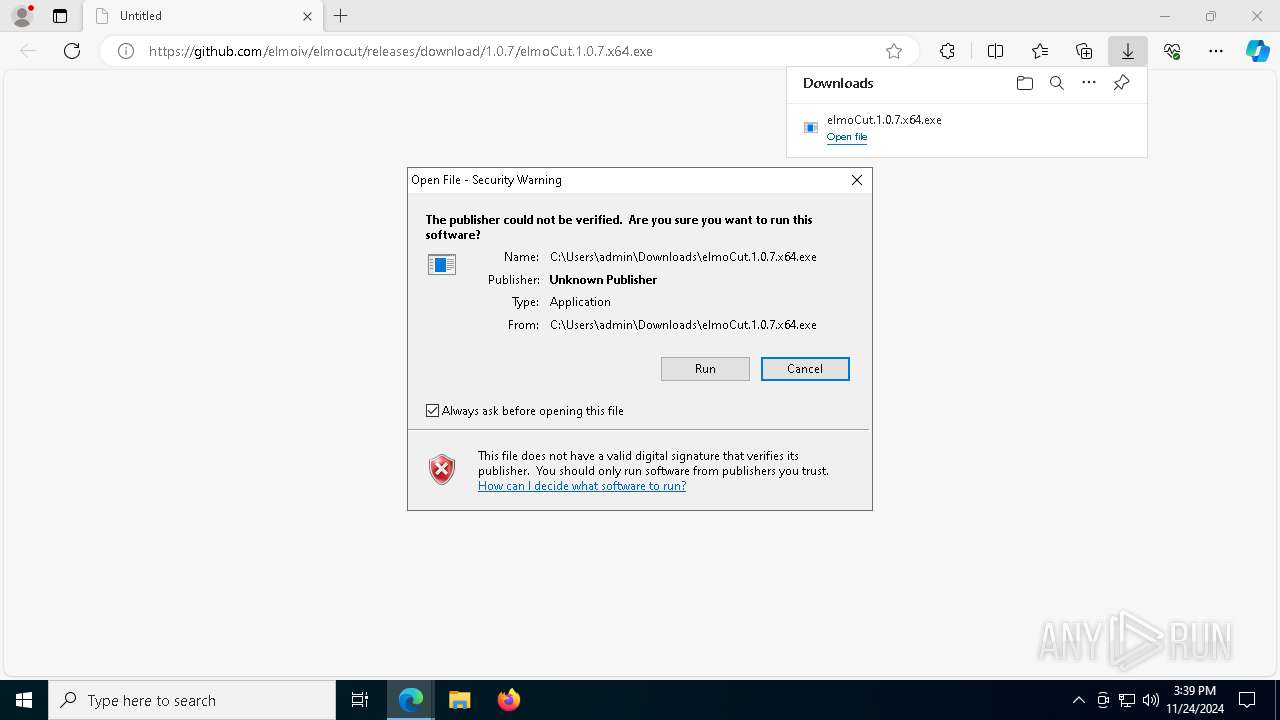
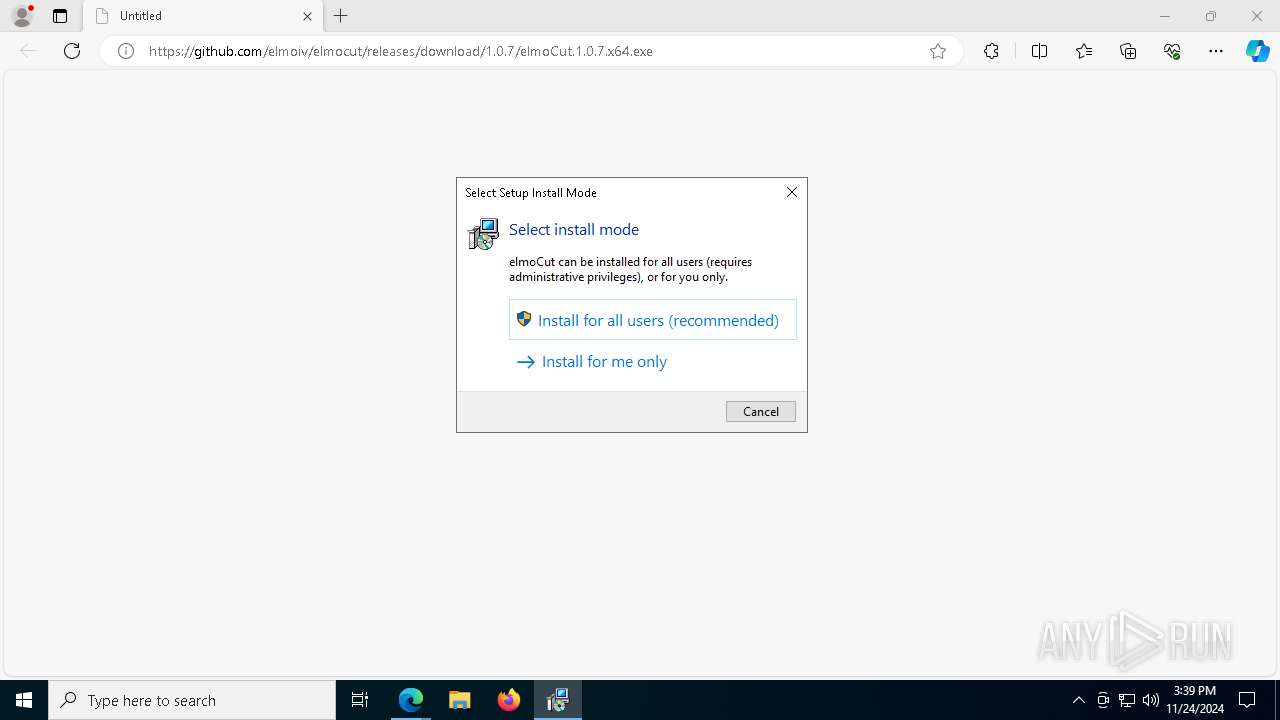
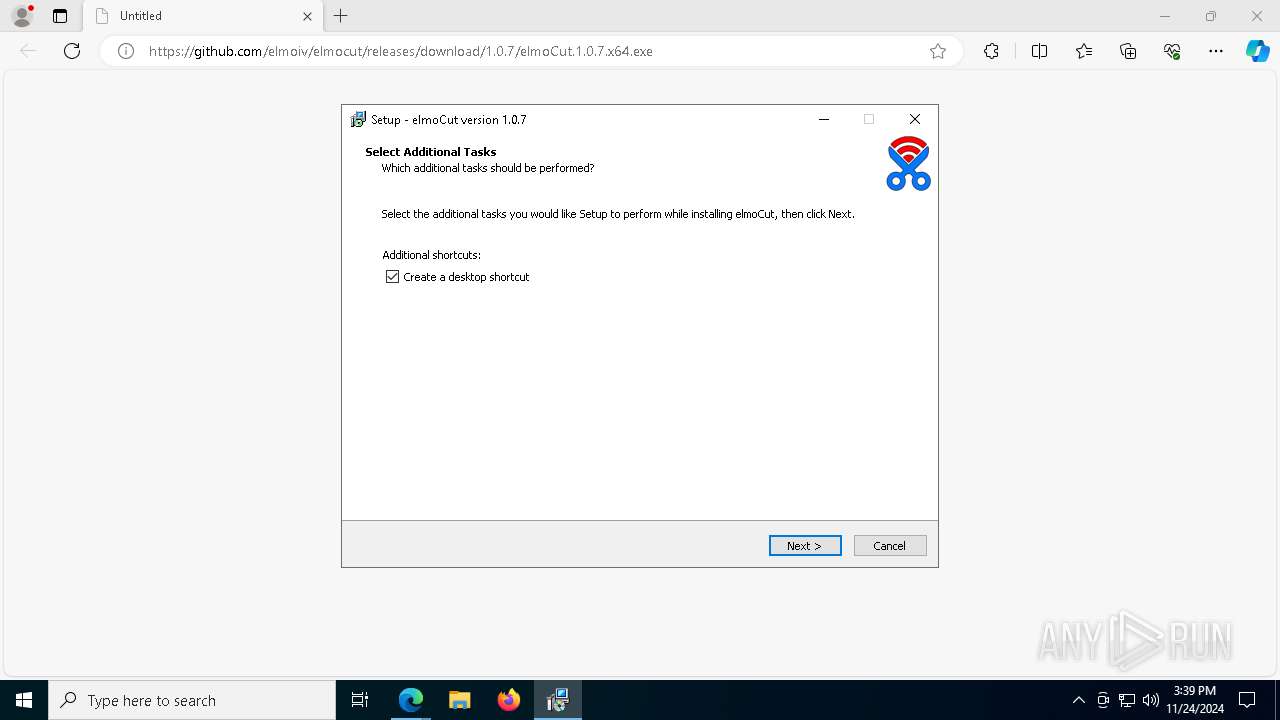
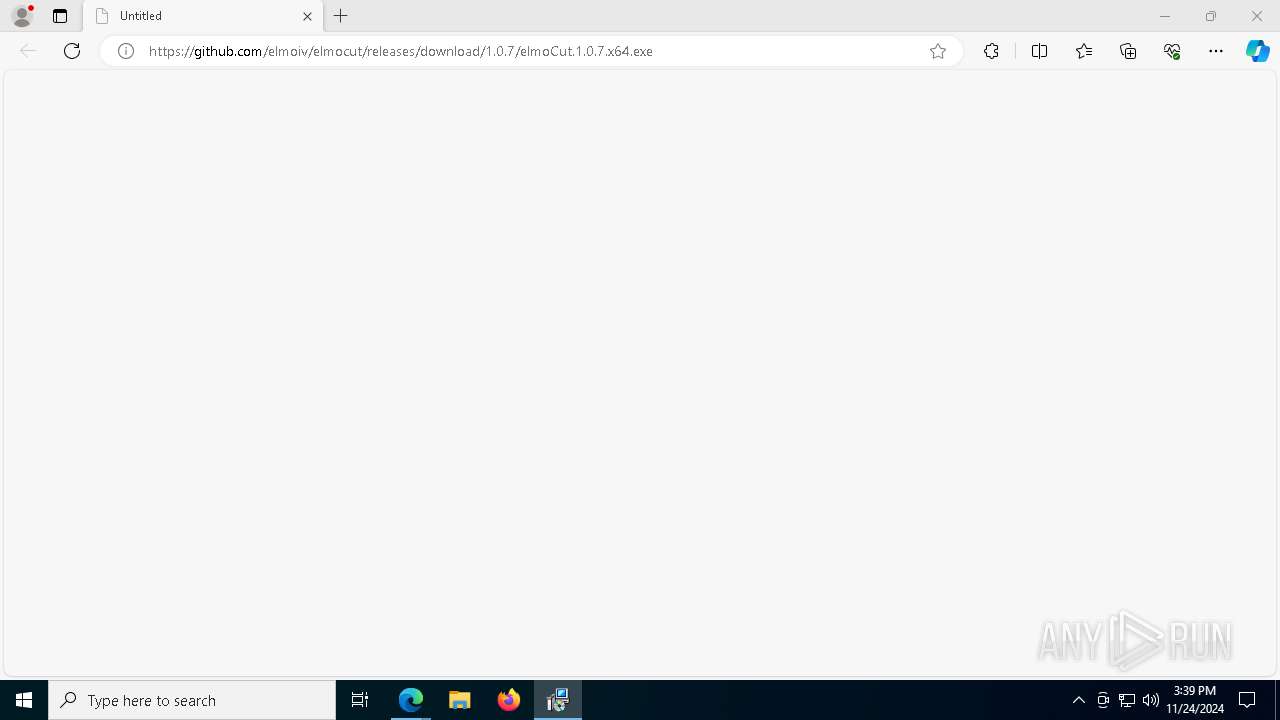
| URL: | https://github.com/elmoiv/elmocut/releases/download/1.0.7/elmoCut.1.0.7.x64.exe |
| Full analysis: | https://app.any.run/tasks/dd86979b-8987-4e90-b481-892a072fedf9 |
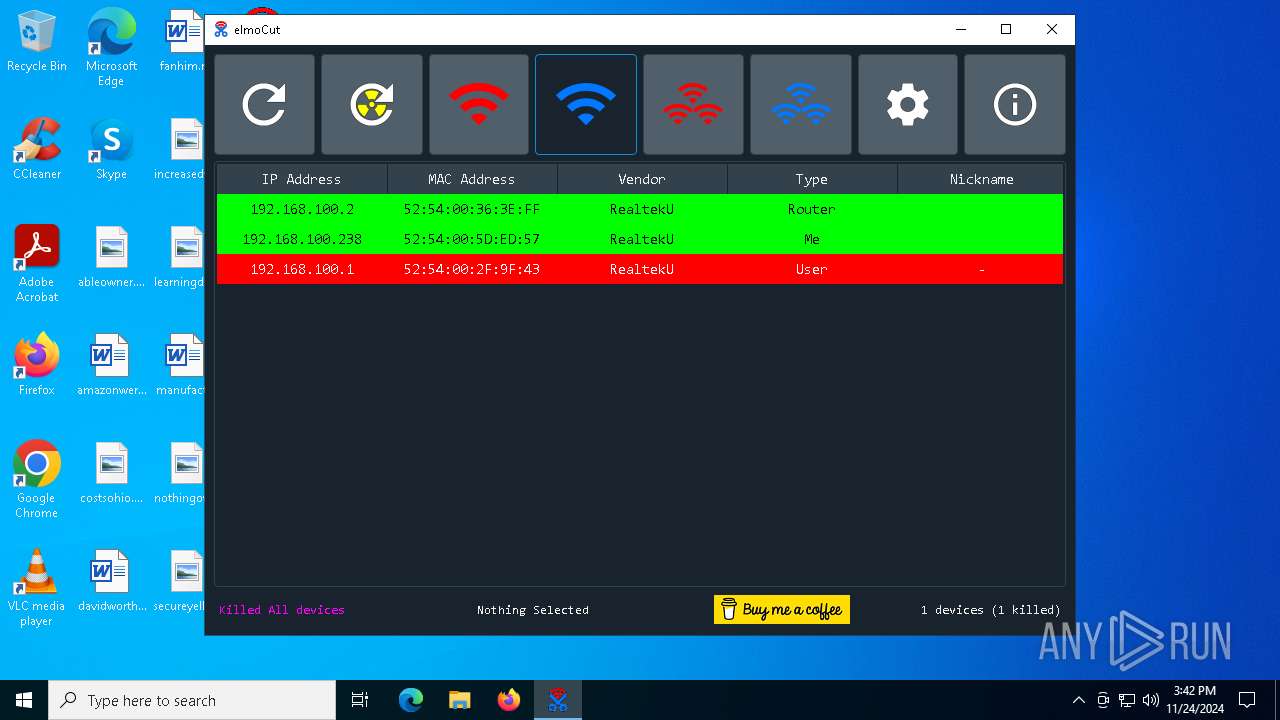
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2024, 15:38:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 8D4A0557E019662B793511FAC20EFA4D |
| SHA1: | 78007527E2F4E9173759CC000EE4C99038847884 |
| SHA256: | 9701E35CCB0511963F13063AD43E1C29632B2135ED059600ABED1FB208B63CF0 |
| SSDEEP: | 3:N8tEdwGKyxKXhrkCUfqUhdC:2umG9MXhr6fvhdC |
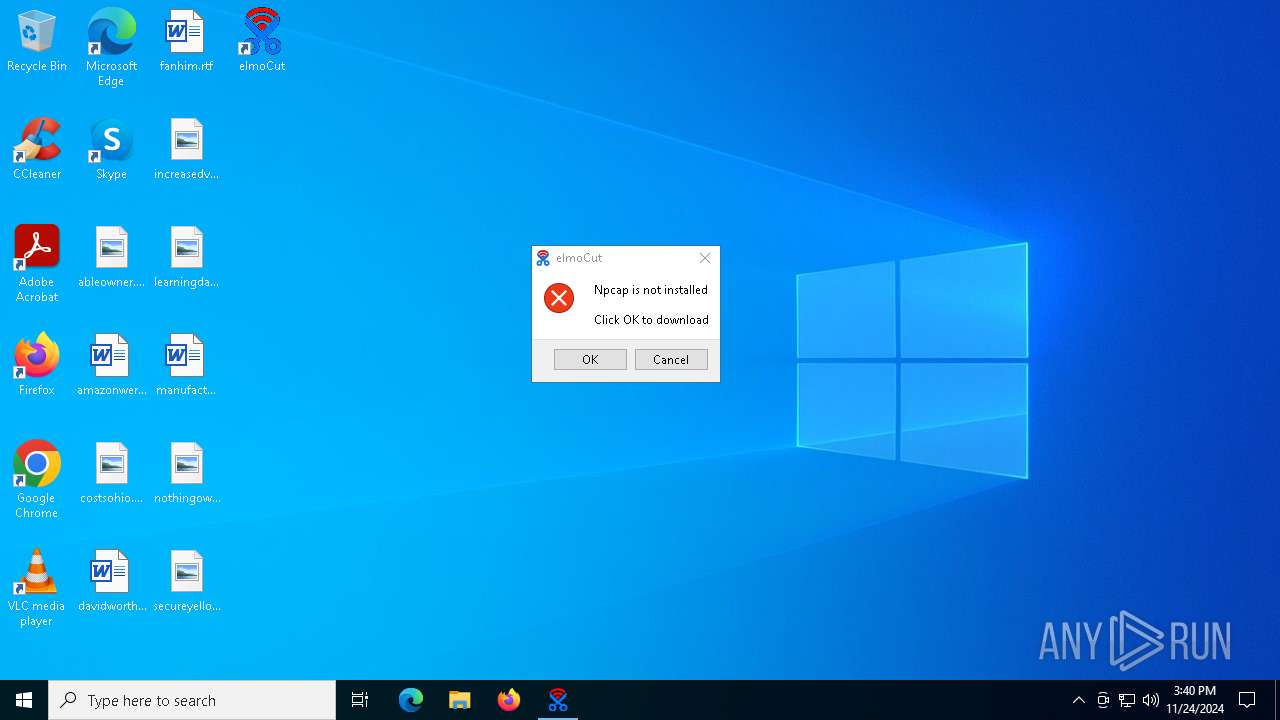
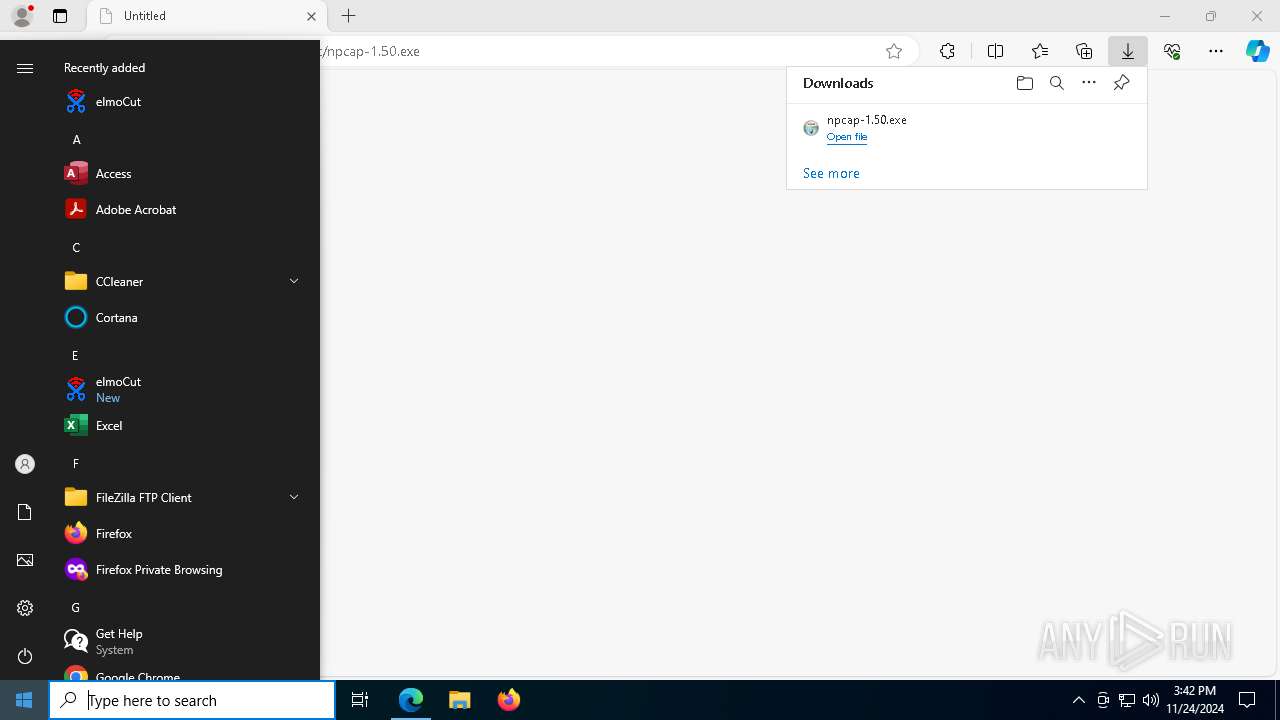
MALICIOUS
Changes powershell execution policy (AllSigned)
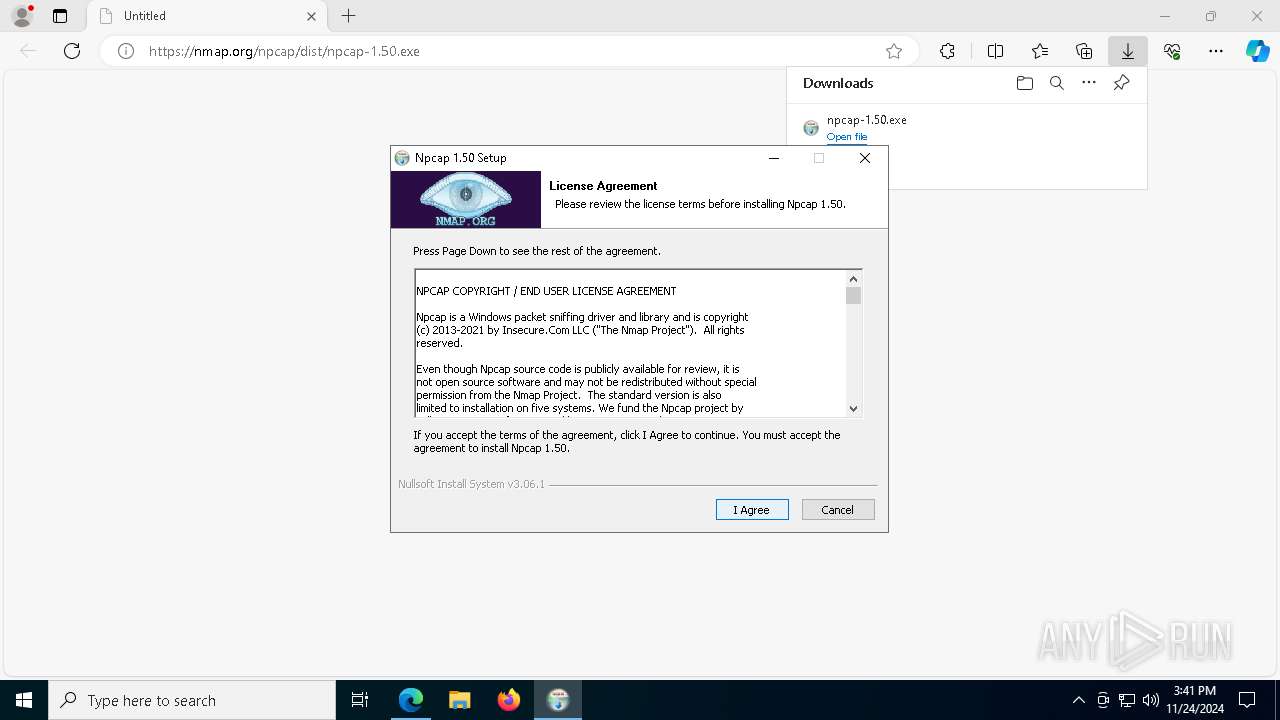
- npcap-1.50.exe (PID: 6708)
- npcap-1.50.exe (PID: 6672)
Run PowerShell with an invisible window
- powershell.exe (PID: 6284)
- powershell.exe (PID: 6364)
SUSPICIOUS
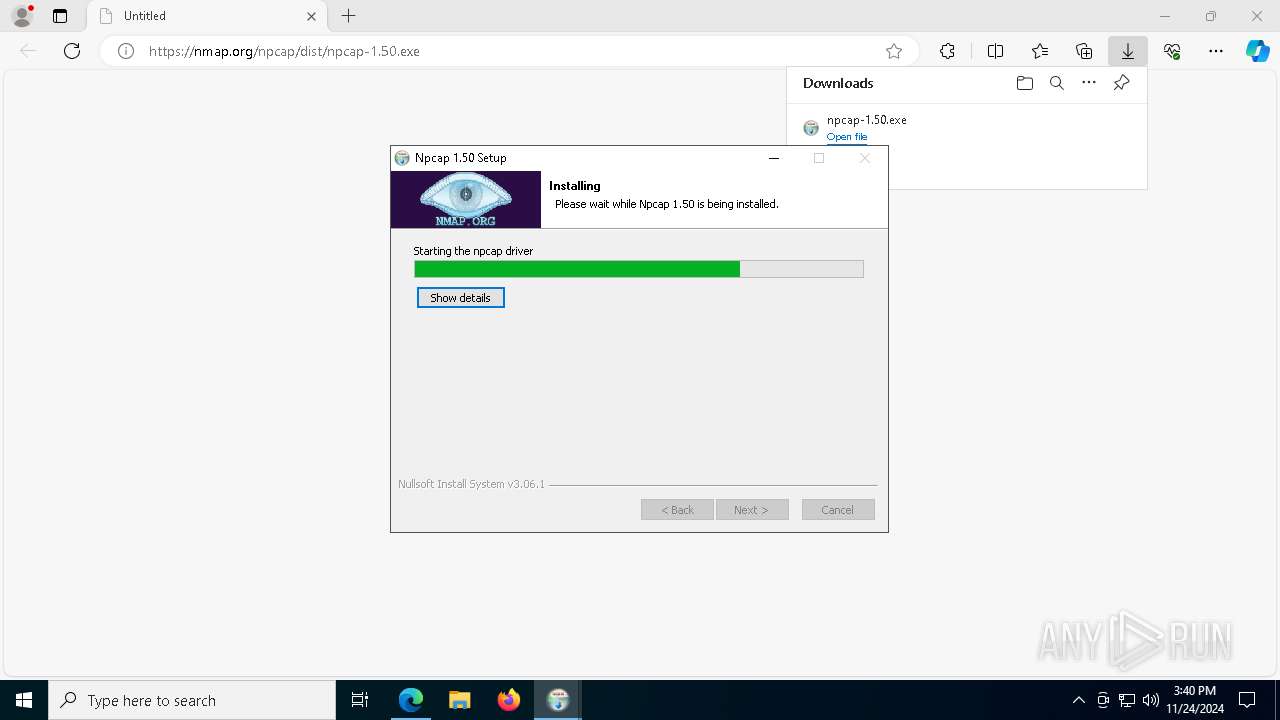
Executable content was dropped or overwritten
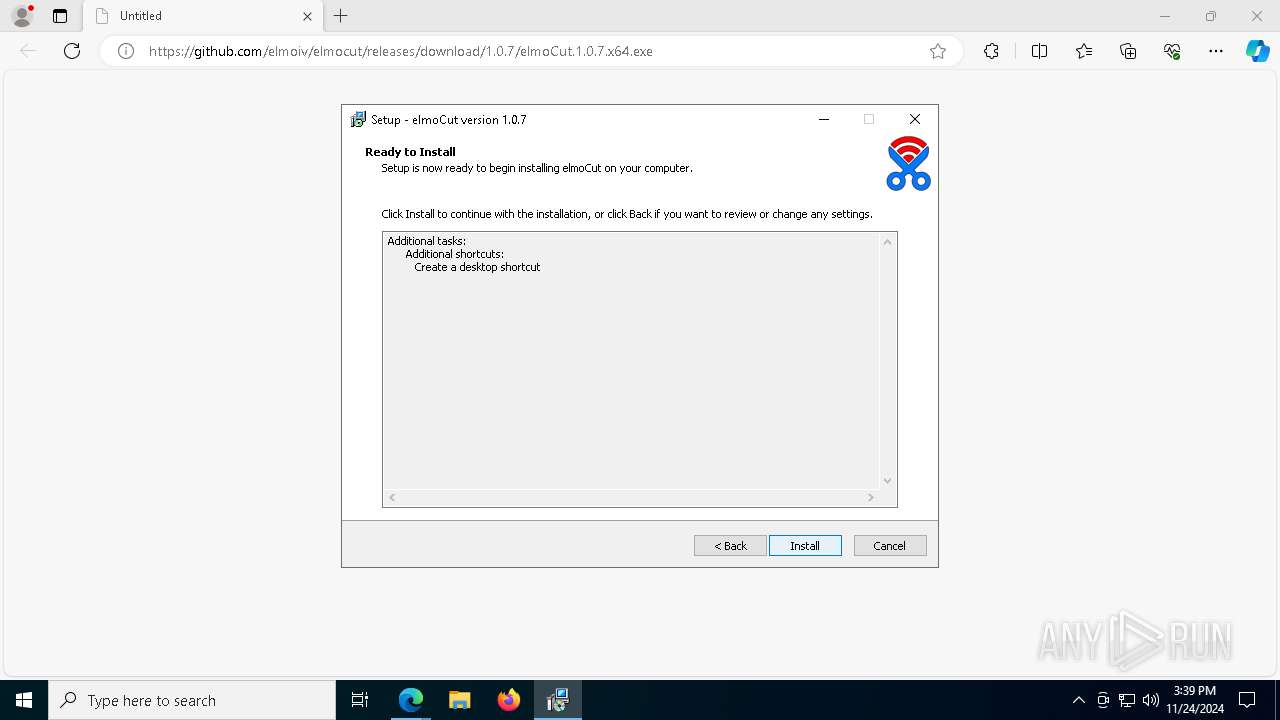
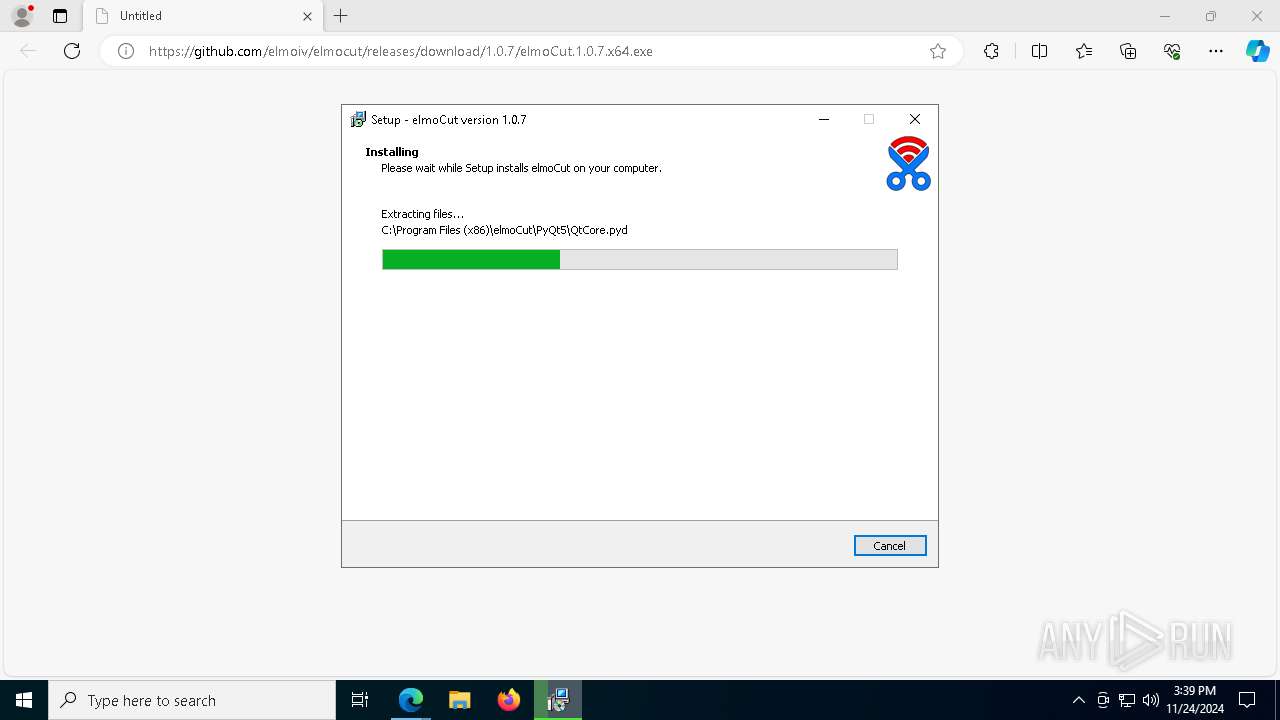
- elmoCut.1.0.7.x64.exe (PID: 8168)
- elmoCut.1.0.7.x64.exe (PID: 8064)
- elmoCut.1.0.7.x64.tmp (PID: 7272)
- npcap-1.50.exe (PID: 6672)
- npcap-1.50.exe (PID: 6708)
- drvinst.exe (PID: 5300)
- NPFInstall.exe (PID: 6348)
- NPFInstall.exe (PID: 7116)
- drvinst.exe (PID: 4596)
Process drops legitimate windows executable
- elmoCut.1.0.7.x64.tmp (PID: 7272)
The process drops C-runtime libraries
- elmoCut.1.0.7.x64.tmp (PID: 7272)
Process drops python dynamic module
- elmoCut.1.0.7.x64.tmp (PID: 7272)
Loads Python modules
- elmoCut.exe (PID: 5316)
- elmoCut.exe (PID: 4556)
Reads the Windows owner or organization settings
- elmoCut.1.0.7.x64.tmp (PID: 7272)
Starts CMD.EXE for commands execution
- elmoCut.exe (PID: 5316)
- elmoCut.exe (PID: 4556)
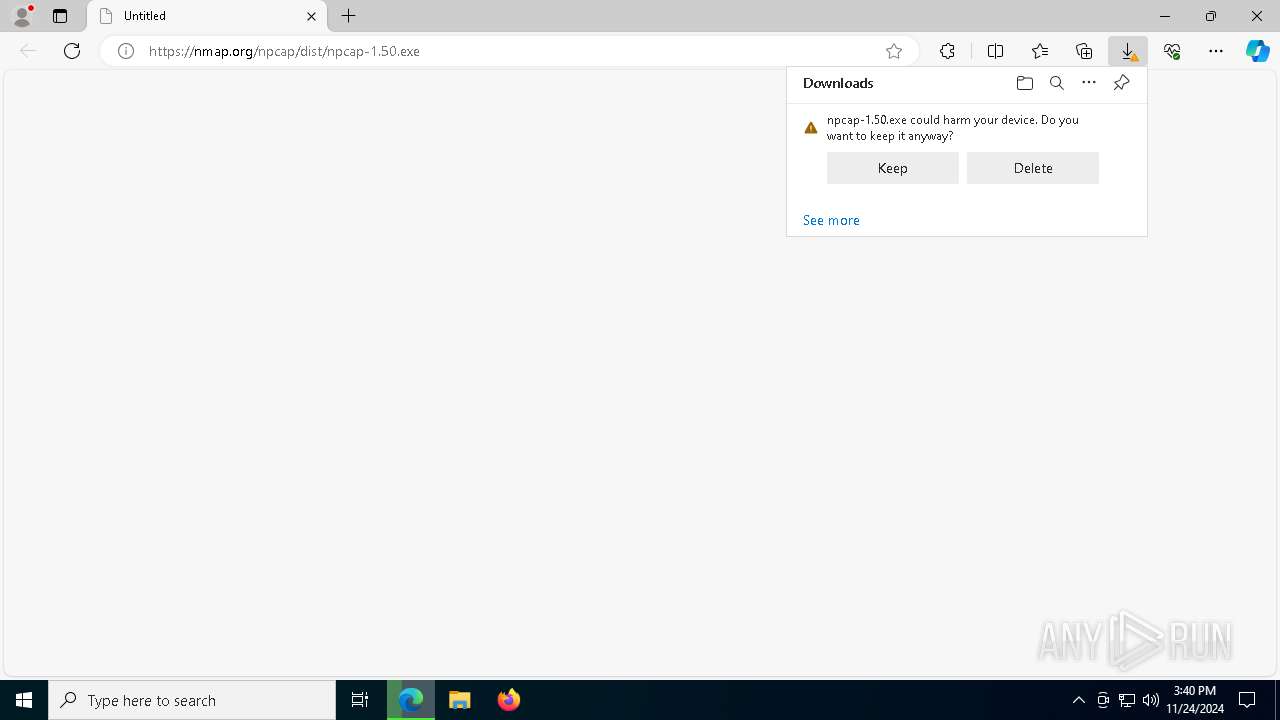
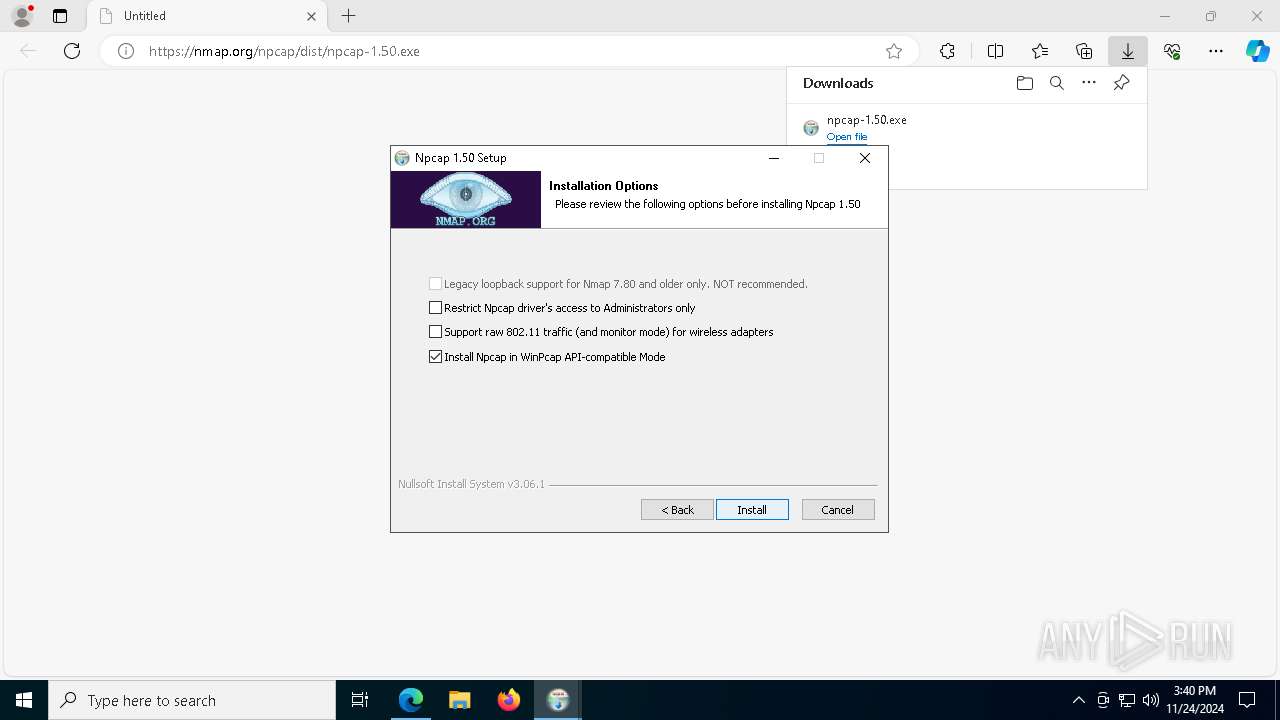
Malware-specific behavior (creating "System.dll" in Temp)
- npcap-1.50.exe (PID: 6672)
- npcap-1.50.exe (PID: 6708)
The process creates files with name similar to system file names
- npcap-1.50.exe (PID: 6672)
- npcap-1.50.exe (PID: 6708)
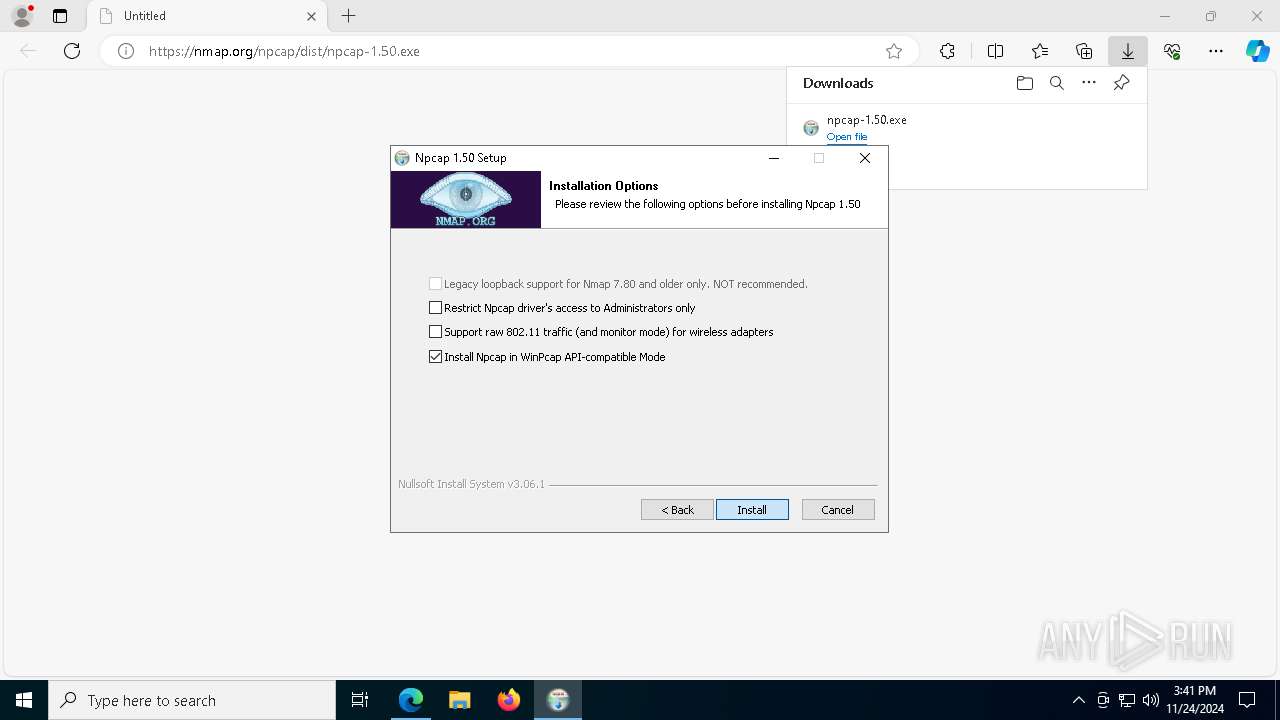
Drops a system driver (possible attempt to evade defenses)
- npcap-1.50.exe (PID: 6708)
- drvinst.exe (PID: 5300)
- NPFInstall.exe (PID: 6348)
- NPFInstall.exe (PID: 7116)
- drvinst.exe (PID: 4596)
Creates a software uninstall entry
- npcap-1.50.exe (PID: 6708)
- npcap-1.50.exe (PID: 6672)
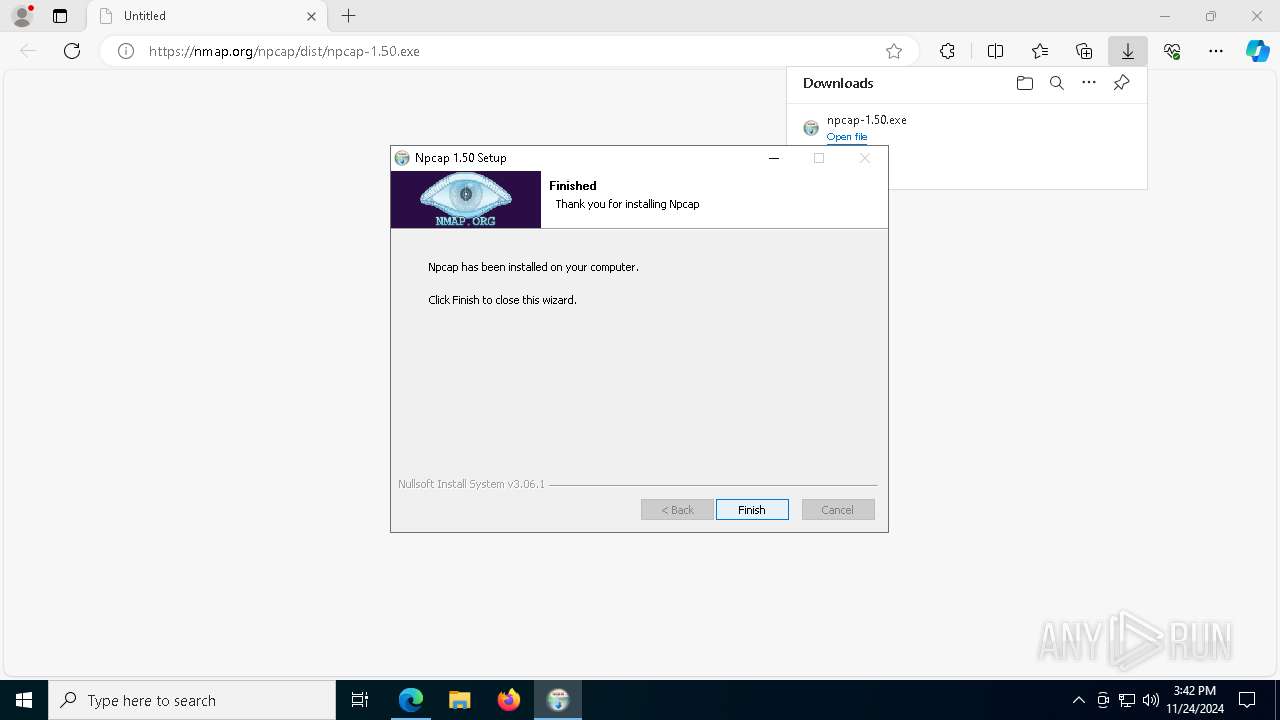
Creates files in the driver directory
- drvinst.exe (PID: 5300)
- NPFInstall.exe (PID: 6348)
- drvinst.exe (PID: 7120)
- drvinst.exe (PID: 4596)
Adds/modifies Windows certificates
- certutil.exe (PID: 6456)
- powershell.exe (PID: 6284)
Checks Windows Trust Settings
- drvinst.exe (PID: 5300)
- drvinst.exe (PID: 4596)
Creates or modifies Windows services
- npcap-1.50.exe (PID: 6708)
- npcap-1.50.exe (PID: 6672)
The process hide an interactive prompt from the user
- npcap-1.50.exe (PID: 6708)
- npcap-1.50.exe (PID: 6672)
The process executes Powershell scripts
- npcap-1.50.exe (PID: 6708)
- npcap-1.50.exe (PID: 6672)
Starts POWERSHELL.EXE for commands execution
- npcap-1.50.exe (PID: 6708)
- npcap-1.50.exe (PID: 6672)
Reads security settings of Internet Explorer
- elmoCut.1.0.7.x64.tmp (PID: 8088)
Get information on the list of running processes
- cmd.exe (PID: 6764)
- elmoCut.exe (PID: 4556)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6328)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 3560)
- cmd.exe (PID: 2496)
- cmd.exe (PID: 6380)
- cmd.exe (PID: 5212)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 4648)
- cmd.exe (PID: 7540)
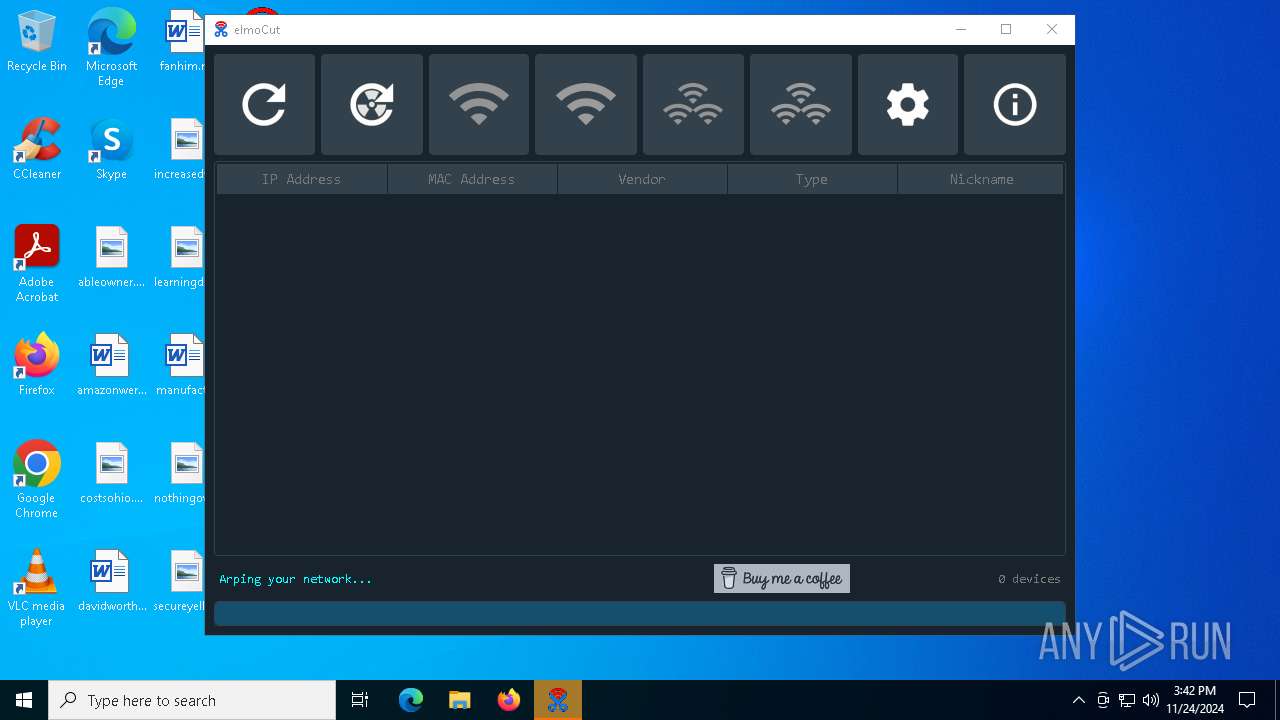
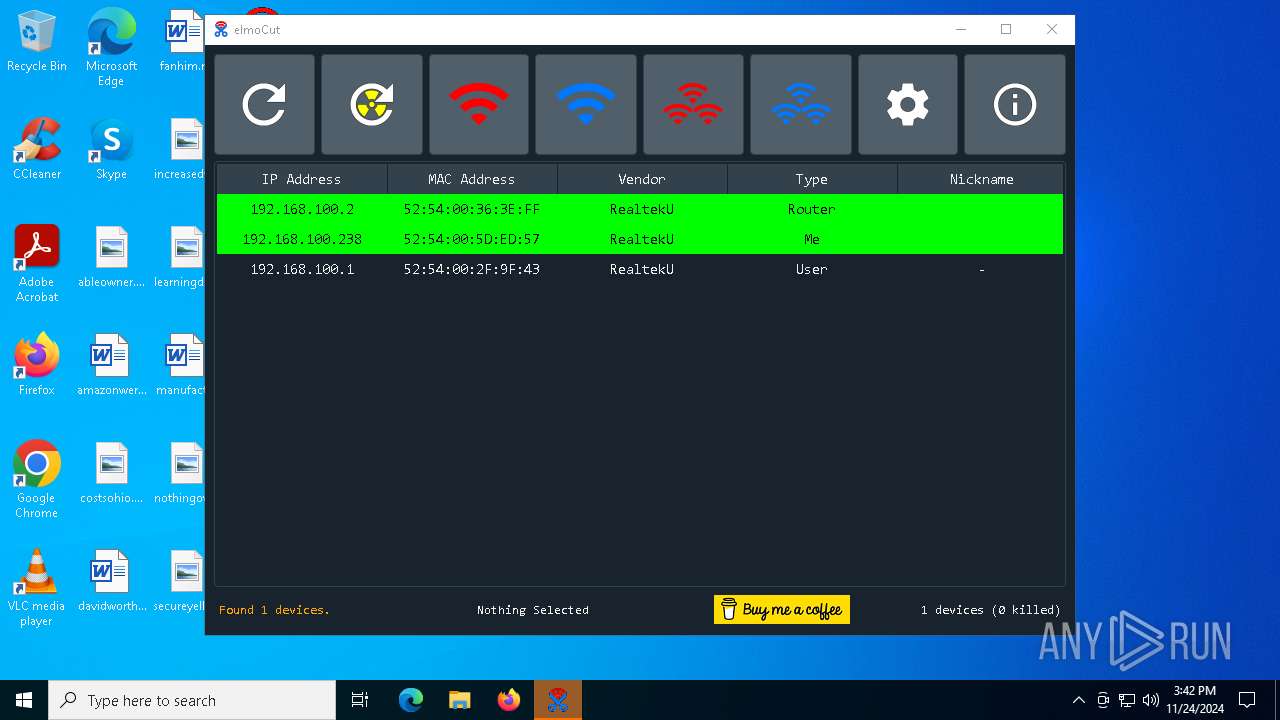
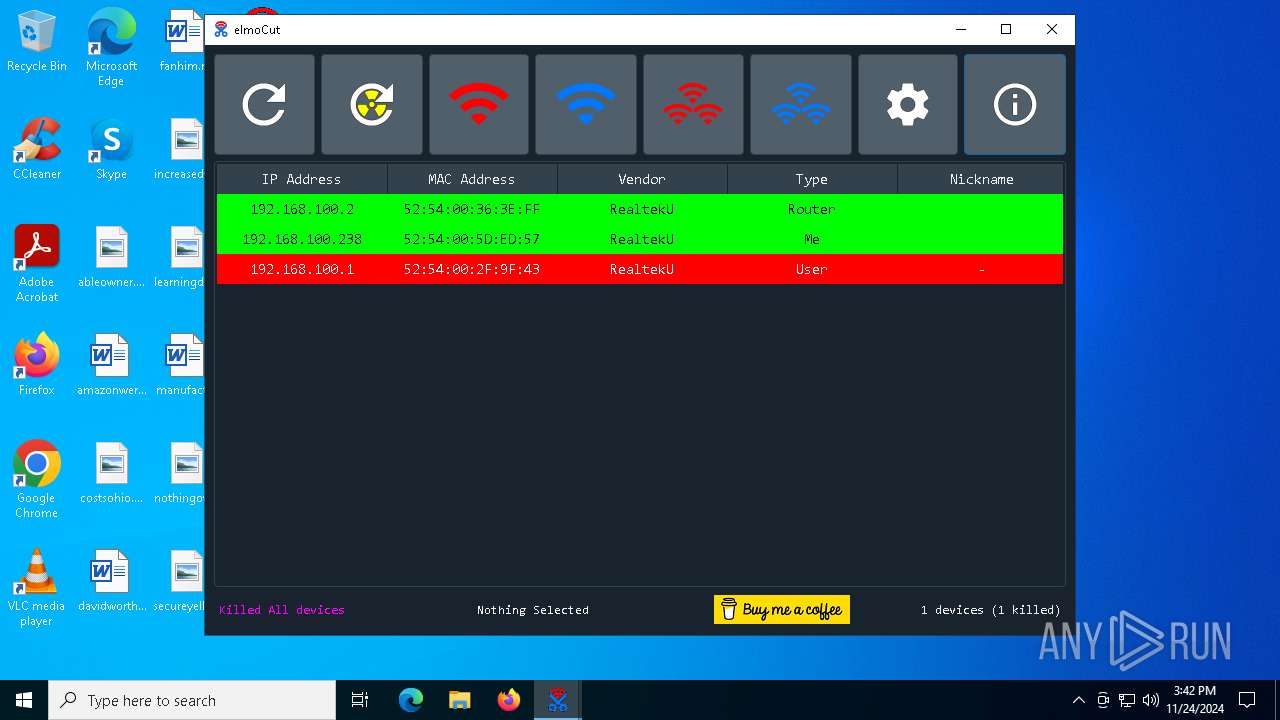
Process uses ARP to discover network configuration
- cmd.exe (PID: 6328)
- cmd.exe (PID: 4648)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 7388)
- cmd.exe (PID: 3560)
- cmd.exe (PID: 5212)
- cmd.exe (PID: 8016)
Process uses IPCONFIG to get network configuration information
- cmd.exe (PID: 2496)
- cmd.exe (PID: 6380)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 7540)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 4540)
- msedge.exe (PID: 6156)
- msedge.exe (PID: 7828)
- msedge.exe (PID: 3836)
Checks supported languages
- identity_helper.exe (PID: 6668)
- elmoCut.1.0.7.x64.exe (PID: 8168)
- elmoCut.1.0.7.x64.exe (PID: 8064)
- identity_helper.exe (PID: 8008)
- elmoCut.exe (PID: 5316)
- npcap-1.50.exe (PID: 6672)
- NPFInstall.exe (PID: 7112)
- npcap-1.50.exe (PID: 6708)
- NPFInstall.exe (PID: 6420)
- NPFInstall.exe (PID: 6212)
- NPFInstall.exe (PID: 6348)
- drvinst.exe (PID: 5300)
- NPFInstall.exe (PID: 5748)
- drvinst.exe (PID: 7120)
- NPFInstall.exe (PID: 7660)
- elmoCut.1.0.7.x64.tmp (PID: 8088)
- elmoCut.1.0.7.x64.tmp (PID: 7272)
- NPFInstall.exe (PID: 7116)
- NPFInstall.exe (PID: 7400)
- drvinst.exe (PID: 4596)
- elmoCut.exe (PID: 4556)
Reads the computer name
- elmoCut.1.0.7.x64.tmp (PID: 7272)
- identity_helper.exe (PID: 6668)
- elmoCut.exe (PID: 5316)
- identity_helper.exe (PID: 8008)
- npcap-1.50.exe (PID: 6672)
- npcap-1.50.exe (PID: 6708)
- NPFInstall.exe (PID: 7112)
- NPFInstall.exe (PID: 6348)
- drvinst.exe (PID: 5300)
- NPFInstall.exe (PID: 7400)
- drvinst.exe (PID: 7120)
- elmoCut.1.0.7.x64.tmp (PID: 8088)
- NPFInstall.exe (PID: 7116)
- drvinst.exe (PID: 4596)
- elmoCut.exe (PID: 4556)
Reads Environment values
- identity_helper.exe (PID: 6668)
- identity_helper.exe (PID: 8008)
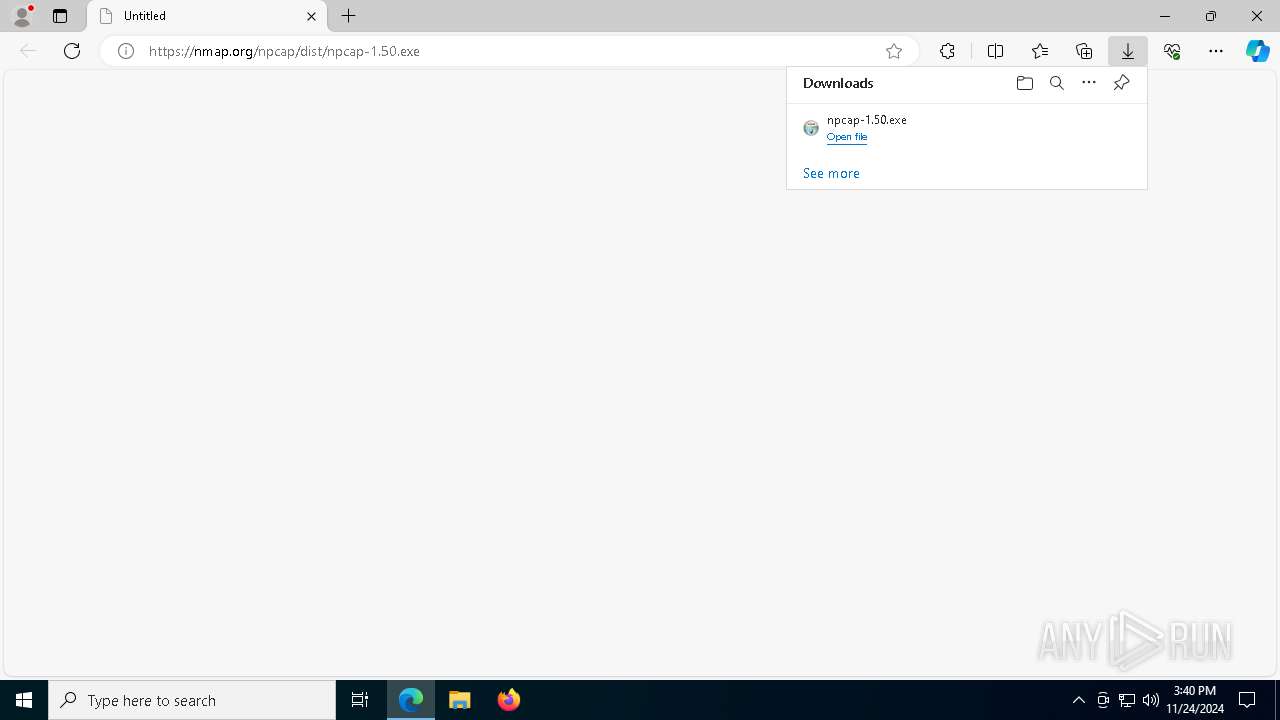
The process uses the downloaded file
- msedge.exe (PID: 7532)
- msedge.exe (PID: 4540)
- msedge.exe (PID: 3836)
- msedge.exe (PID: 8104)
- powershell.exe (PID: 6284)
- powershell.exe (PID: 6364)
Create files in a temporary directory
- elmoCut.1.0.7.x64.exe (PID: 8064)
- elmoCut.1.0.7.x64.tmp (PID: 7272)
- npcap-1.50.exe (PID: 6672)
- npcap-1.50.exe (PID: 6708)
- NPFInstall.exe (PID: 6348)
- elmoCut.1.0.7.x64.exe (PID: 8168)
- NPFInstall.exe (PID: 7116)
Application launched itself
- msedge.exe (PID: 4540)
- msedge.exe (PID: 3836)
- msedge.exe (PID: 5032)
Creates files in the program directory
- elmoCut.1.0.7.x64.tmp (PID: 7272)
- npcap-1.50.exe (PID: 6672)
- NPFInstall.exe (PID: 7112)
- npcap-1.50.exe (PID: 6708)
Reads the machine GUID from the registry
- elmoCut.exe (PID: 5316)
- drvinst.exe (PID: 5300)
- drvinst.exe (PID: 4596)
- elmoCut.exe (PID: 4556)
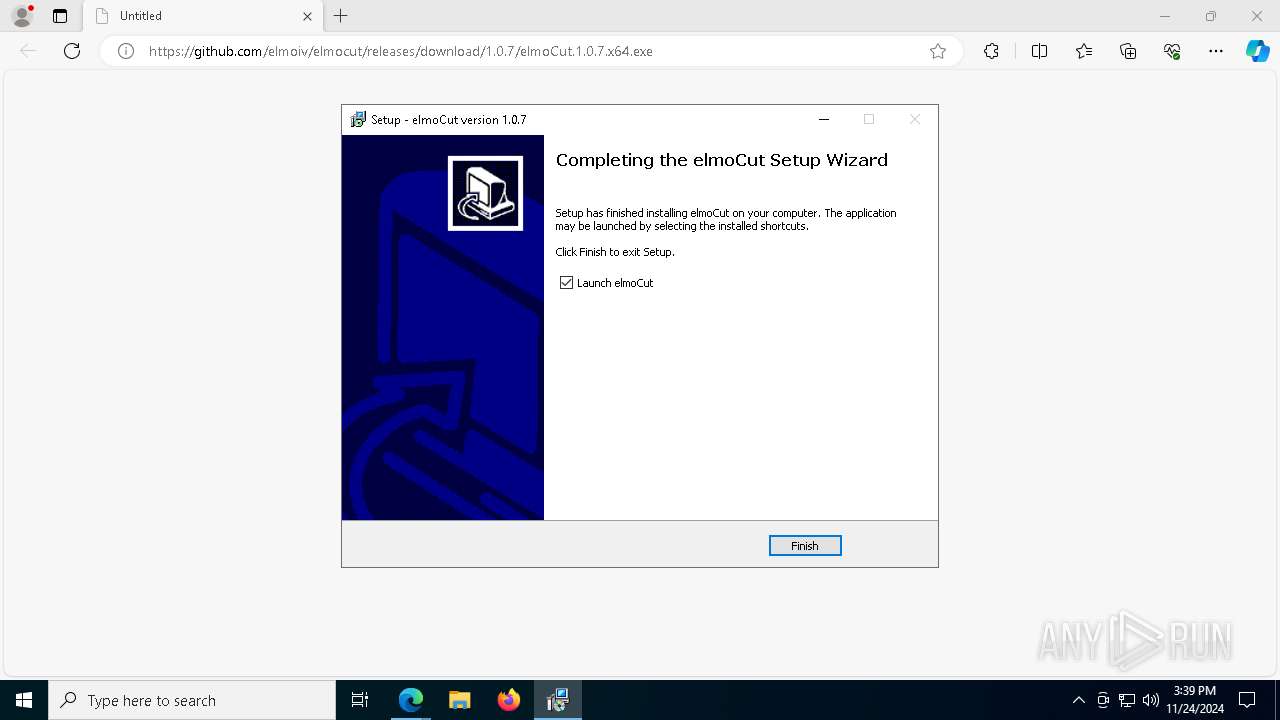
Creates a software uninstall entry
- elmoCut.1.0.7.x64.tmp (PID: 7272)
Reads the software policy settings
- pnputil.exe (PID: 6320)
- drvinst.exe (PID: 5300)
- pnputil.exe (PID: 7644)
- drvinst.exe (PID: 4596)
Reads security settings of Internet Explorer
- pnputil.exe (PID: 6320)
- pnputil.exe (PID: 7644)
Checks proxy server information
- powershell.exe (PID: 6284)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6284)
- powershell.exe (PID: 6364)
Process checks computer location settings
- elmoCut.1.0.7.x64.tmp (PID: 8088)
Manual execution by a user
- elmoCut.exe (PID: 4556)
Creates files or folders in the user directory
- elmoCut.exe (PID: 4556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
315
Monitored processes
175
Malicious processes
10
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | netsh interface ip show address "Connection" | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 396 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5096 --field-trial-handle=2268,i,10764687651229943934,4055792298433958184,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
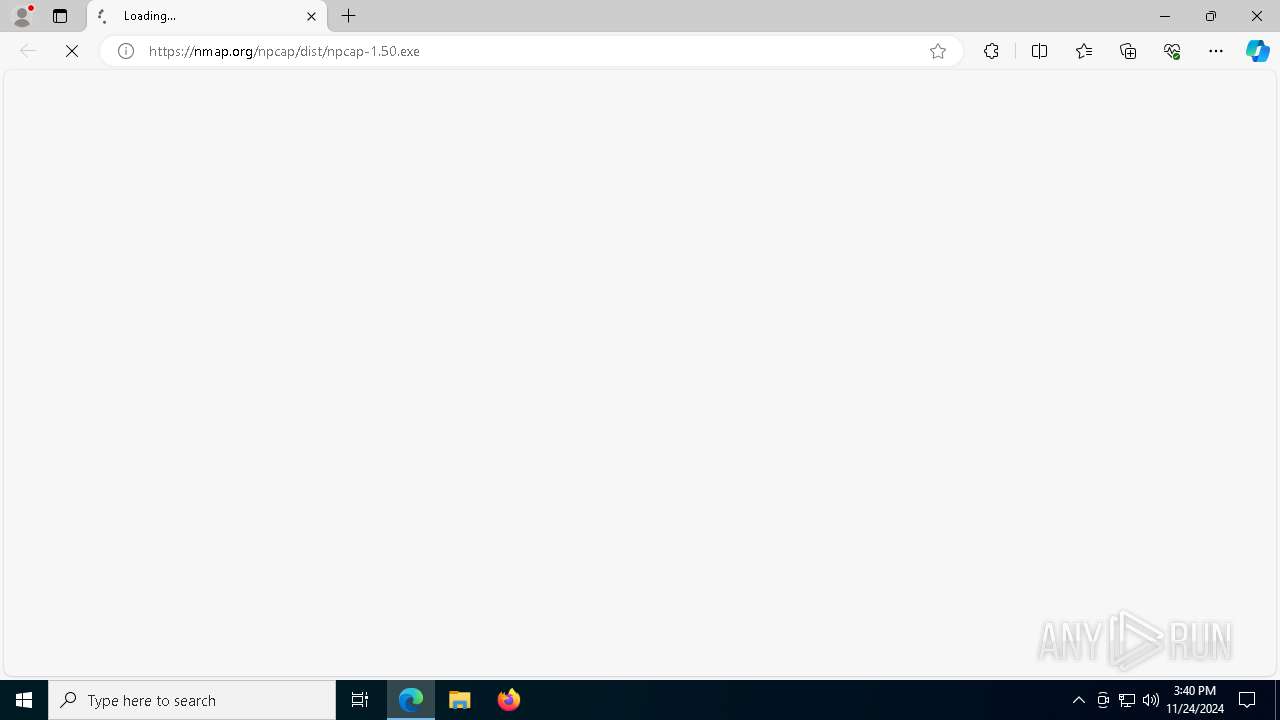
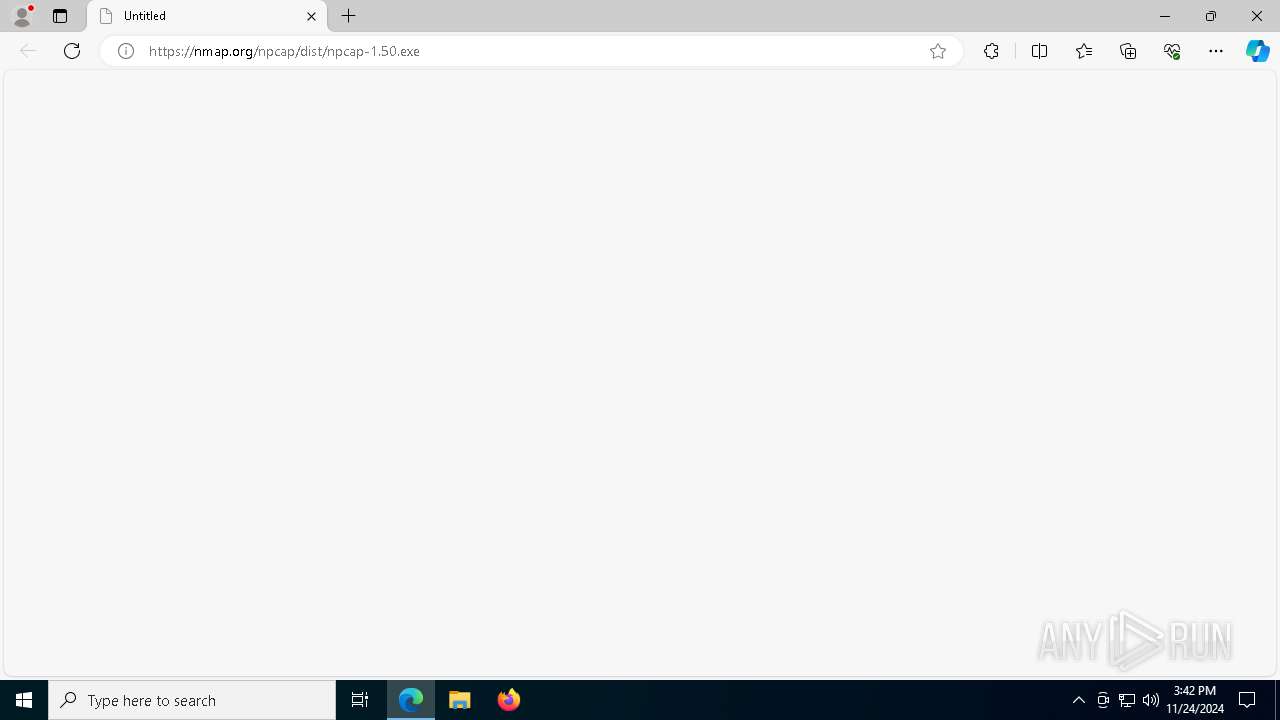
| 432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://nmap.org/npcap/dist/npcap-1.50.exe | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 444 | findstr "IP" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
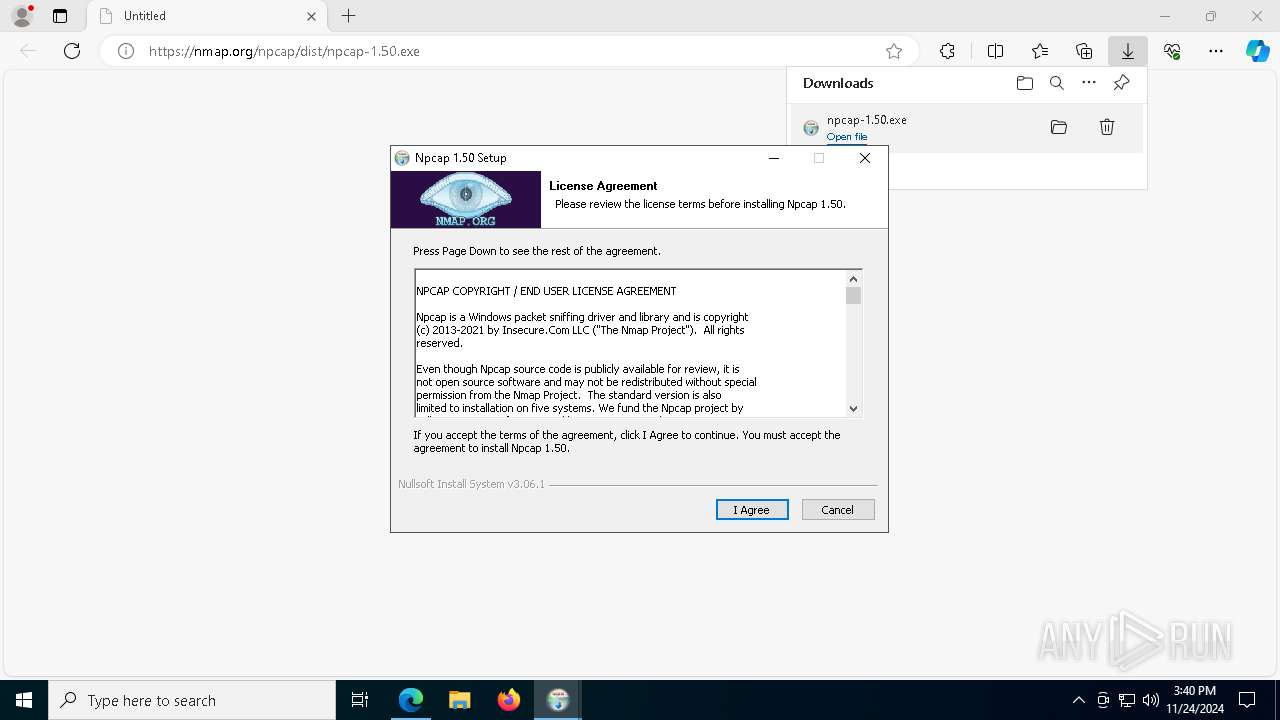
| 836 | "C:\Users\admin\Downloads\npcap-1.50.exe" | C:\Users\admin\Downloads\npcap-1.50.exe | — | msedge.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Npcap 1.50 installer Exit code: 3221226540 Version: 1.50 Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5564 --field-trial-handle=2268,i,10764687651229943934,4055792298433958184,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1576 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1632 --field-trial-handle=2268,i,10764687651229943934,4055792298433958184,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1596 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | NPFInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2100 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | pnputil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
42 812
Read events
42 647
Write events
153
Delete events
12
Modification events
| (PID) Process: | (4540) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4540) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4540) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4540) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4540) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D4E8E3B140862F00 | |||
| (PID) Process: | (4540) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2C04ECB140862F00 | |||
| (PID) Process: | (4540) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328462 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {02A89C00-FA8E-408D-B65C-D88607261963} | |||
| (PID) Process: | (4540) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328462 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0B9EE32A-FE24-42D8-83D3-B177C44D351A} | |||
| (PID) Process: | (4540) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6E831BB240862F00 | |||
| (PID) Process: | (4540) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
114
Suspicious files
261
Text files
156
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4540 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135854.TMP | — | |
MD5:— | SHA256:— | |||
| 4540 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135854.TMP | — | |
MD5:— | SHA256:— | |||
| 4540 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4540 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4540 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135854.TMP | — | |
MD5:— | SHA256:— | |||
| 4540 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135864.TMP | — | |
MD5:— | SHA256:— | |||
| 4540 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4540 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135874.TMP | — | |
MD5:— | SHA256:— | |||
| 4540 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4540 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
83
DNS requests
94
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1468 | svchost.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7688 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7688 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7448 | svchost.exe | HEAD | 200 | 104.124.11.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/be1098f2-af7c-46fa-9fb6-e1f0043ecb69?P1=1732622134&P2=404&P3=2&P4=ClcxJY6aKFH0lenHVkf3WCgptO47XxtiJn2ptYYBMKpVMMyoqaho5QUocGeigaTjsiMPruEWcYUNOLBJ%2ffYbYg%3d%3d | unknown | — | — | whitelisted |
7448 | svchost.exe | GET | 206 | 104.124.11.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/be1098f2-af7c-46fa-9fb6-e1f0043ecb69?P1=1732622134&P2=404&P3=2&P4=ClcxJY6aKFH0lenHVkf3WCgptO47XxtiJn2ptYYBMKpVMMyoqaho5QUocGeigaTjsiMPruEWcYUNOLBJ%2ffYbYg%3d%3d | unknown | — | — | whitelisted |
7448 | svchost.exe | GET | 206 | 104.124.11.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/be1098f2-af7c-46fa-9fb6-e1f0043ecb69?P1=1732622134&P2=404&P3=2&P4=ClcxJY6aKFH0lenHVkf3WCgptO47XxtiJn2ptYYBMKpVMMyoqaho5QUocGeigaTjsiMPruEWcYUNOLBJ%2ffYbYg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.16.204.146:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1468 | svchost.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |