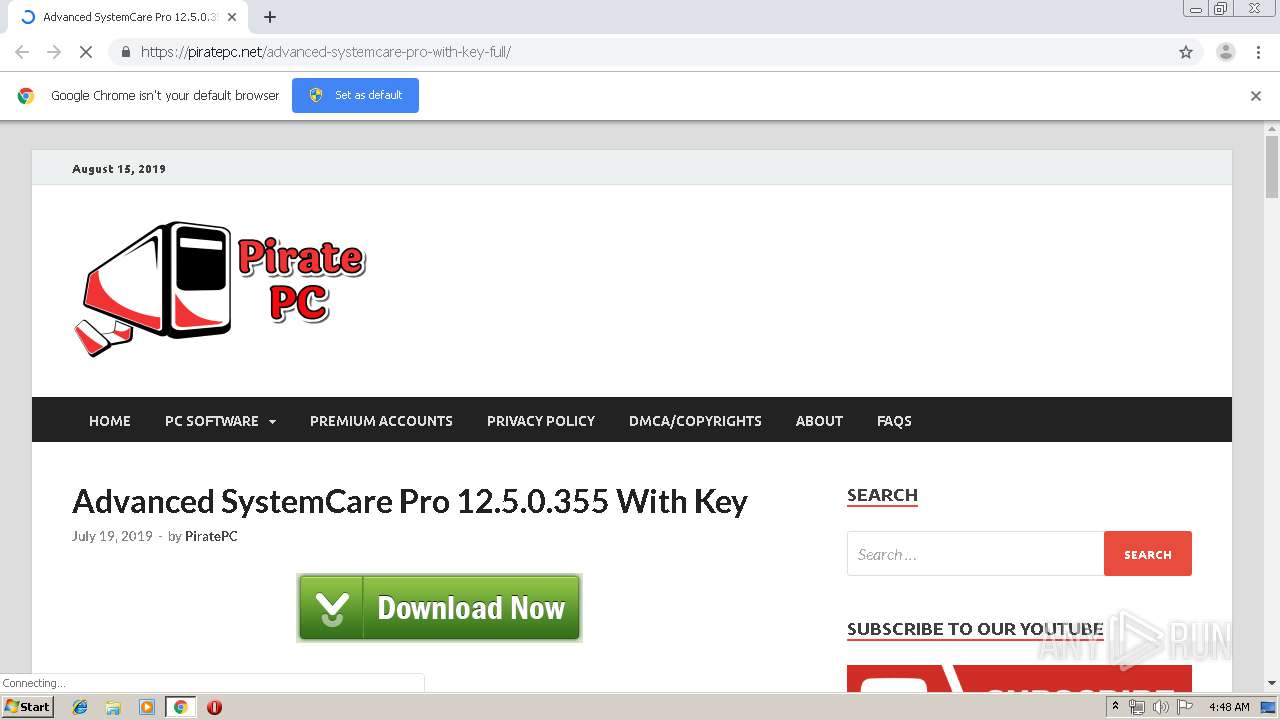
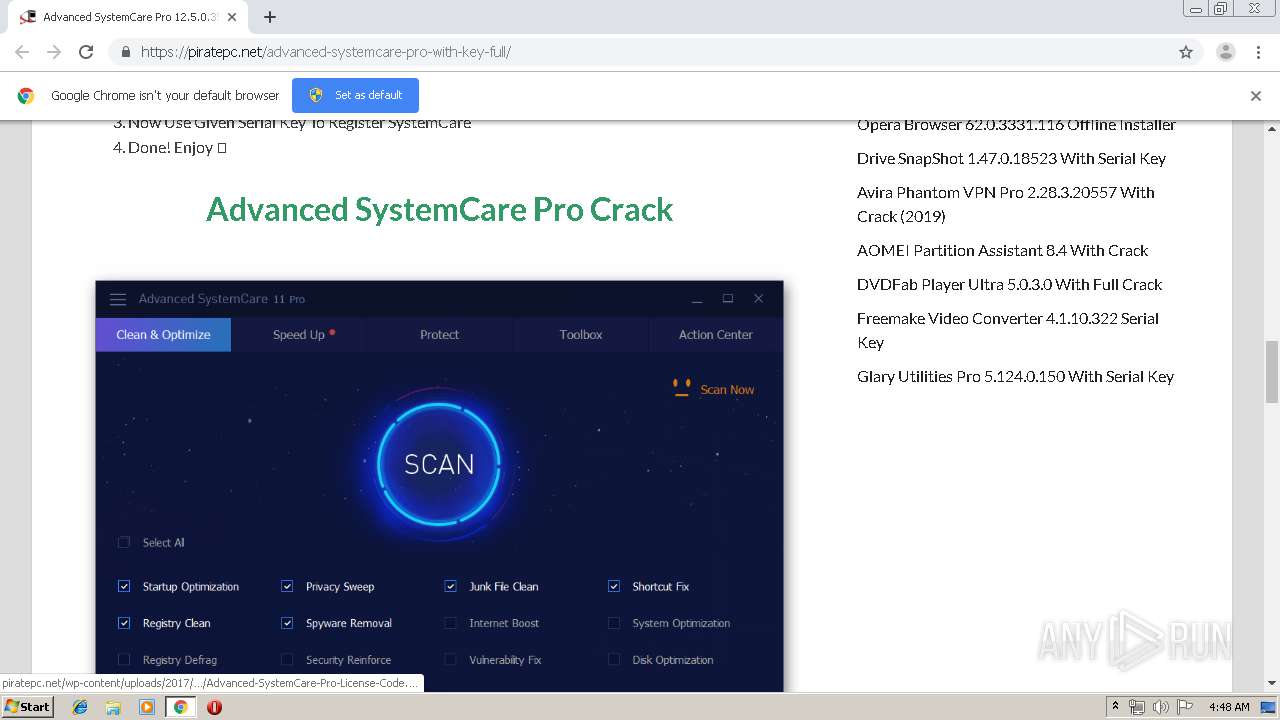
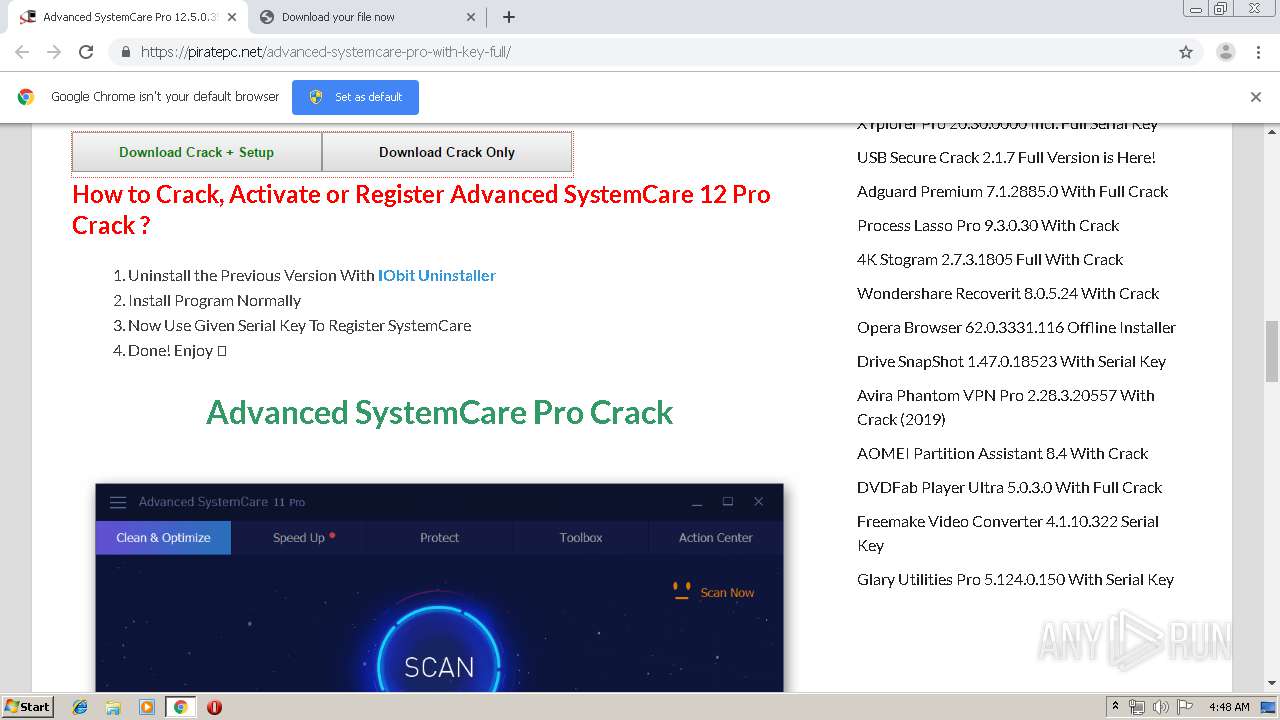
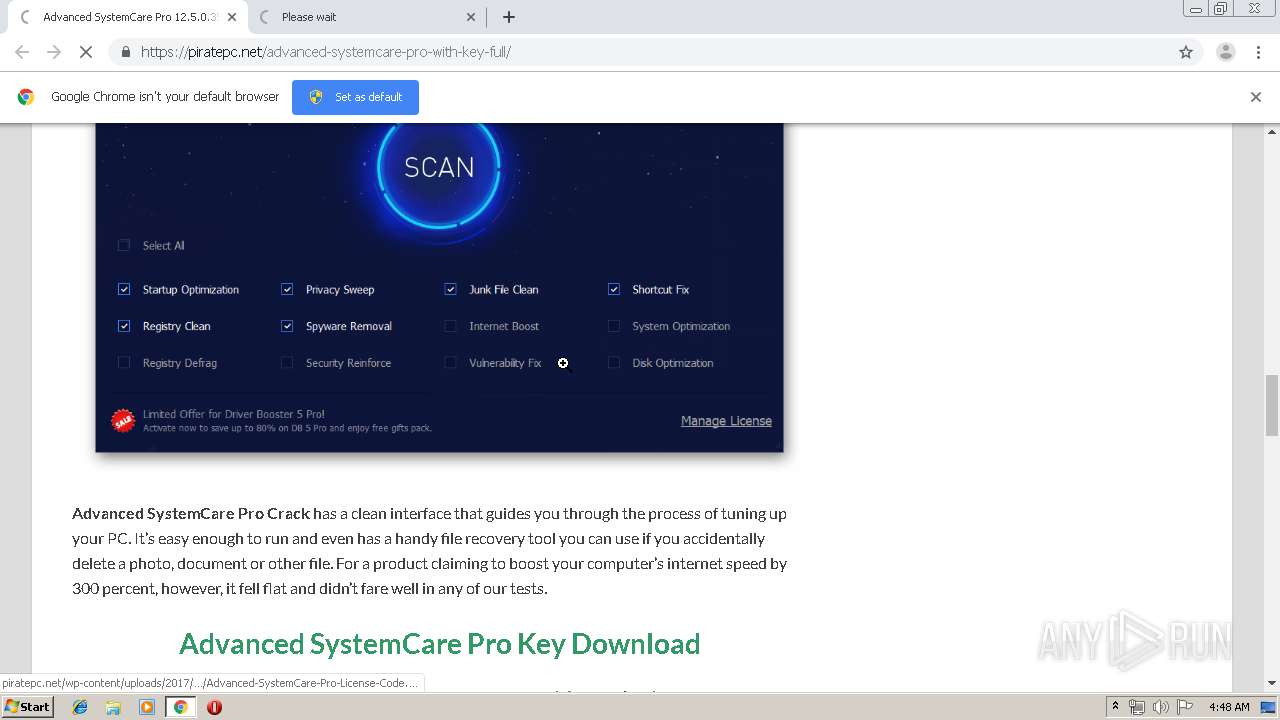
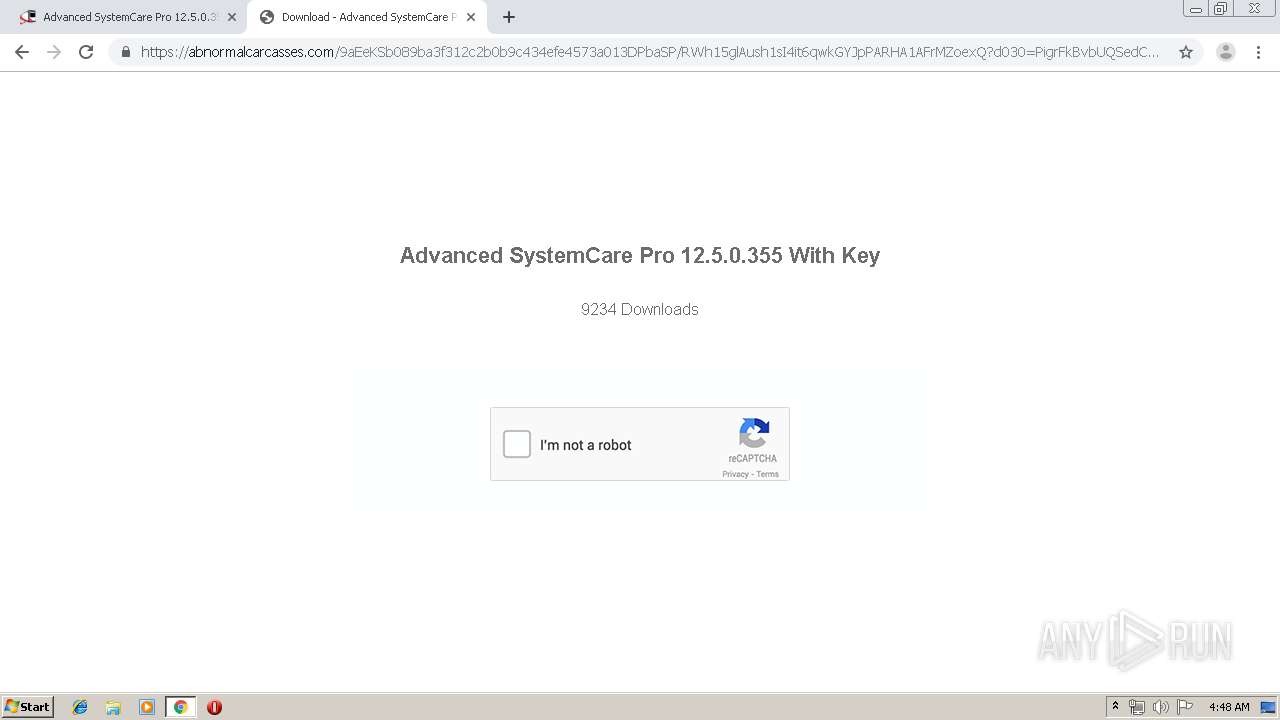
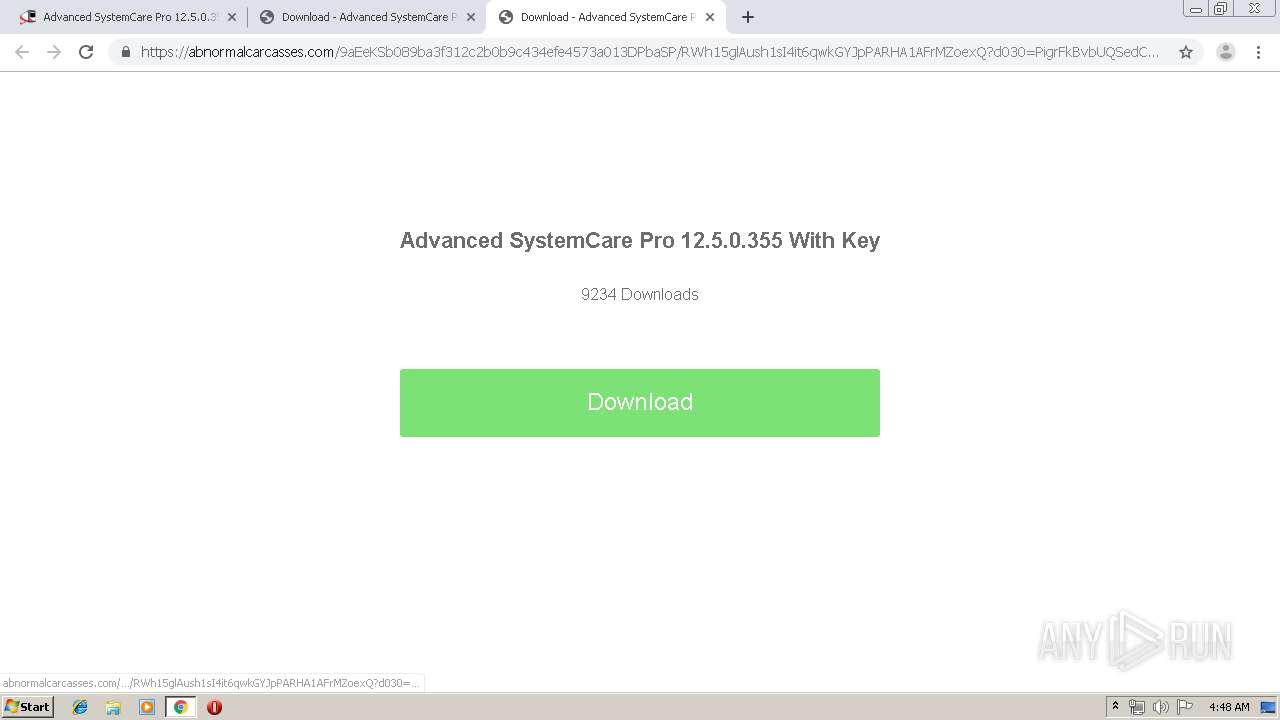
| URL: | https://piratepc.net/advanced-systemcare-pro-with-key-full/ |
| Full analysis: | https://app.any.run/tasks/83816008-ce0d-4e75-9b2c-979c002b21cb |
| Verdict: | No threats detected |
| Analysis date: | August 15, 2019, 03:47:45 |
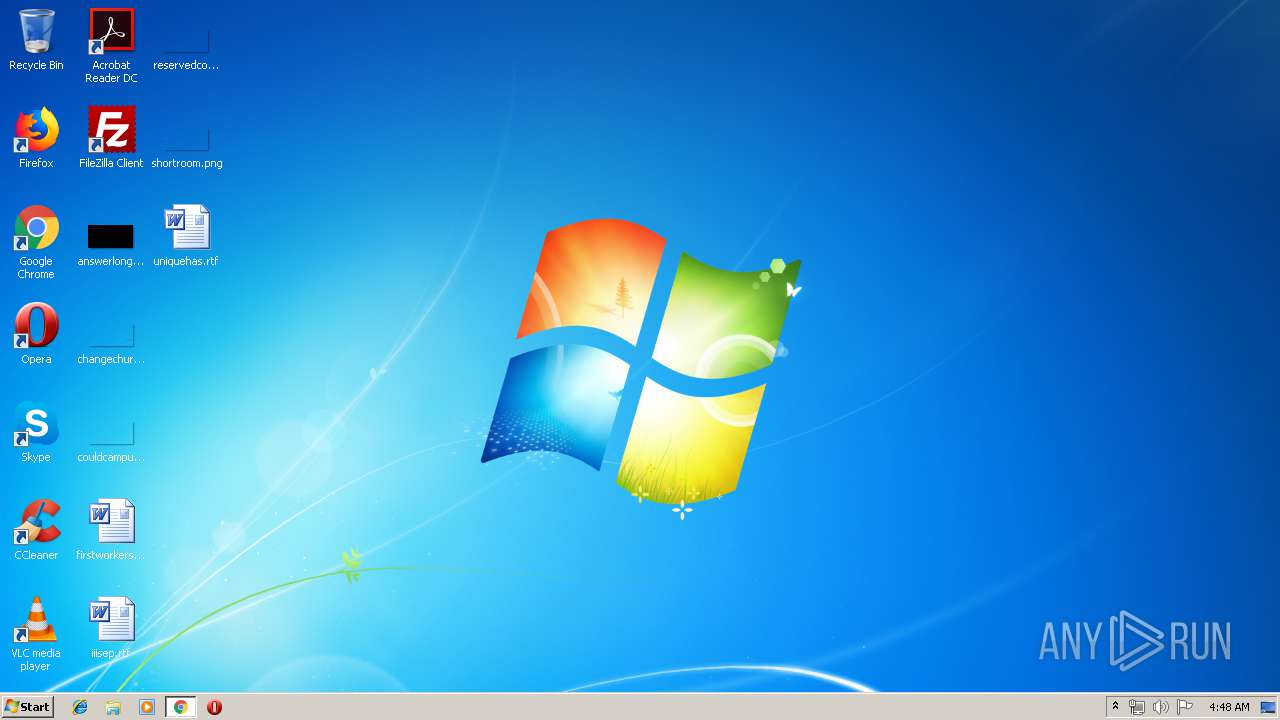
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 71D0FAC5AE34761A22BAA7594F8CD463 |
| SHA1: | 74C52F95EEB61558E772E2F9A98A1227B7131D26 |
| SHA256: | 96FC4F08768787A9260E59EF2B20816845A08859296A66F1FA6164406275C934 |
| SSDEEP: | 3:N8IURzsKfXP9Kvlx:2IIzsQQlx |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3668)
INFO
Application launched itself
- chrome.exe (PID: 3668)
Creates files in the user directory
- chrome.exe (PID: 3668)
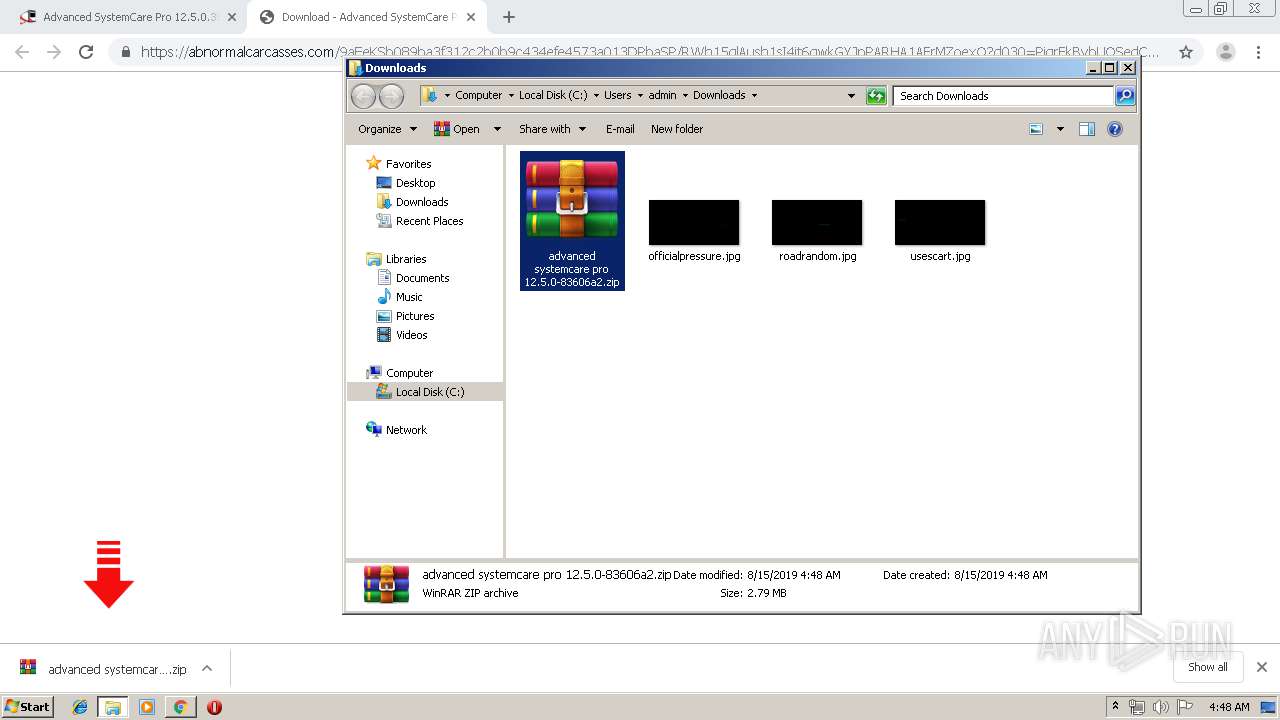
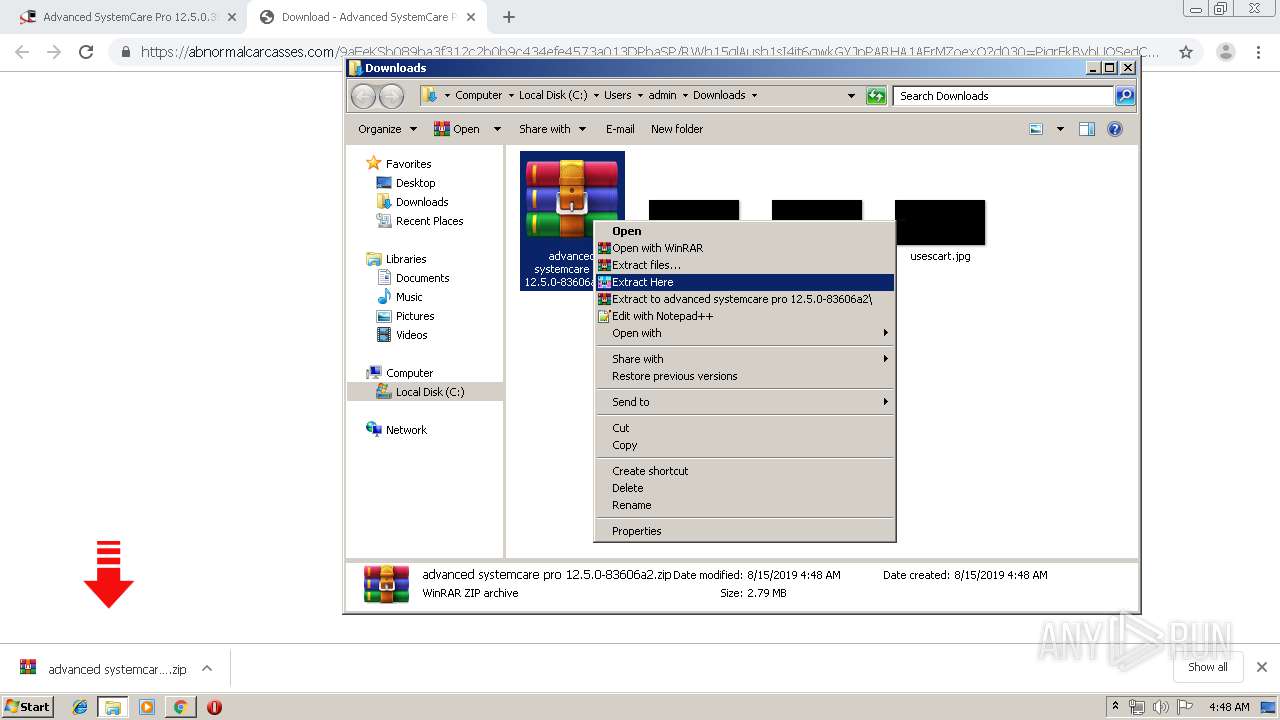
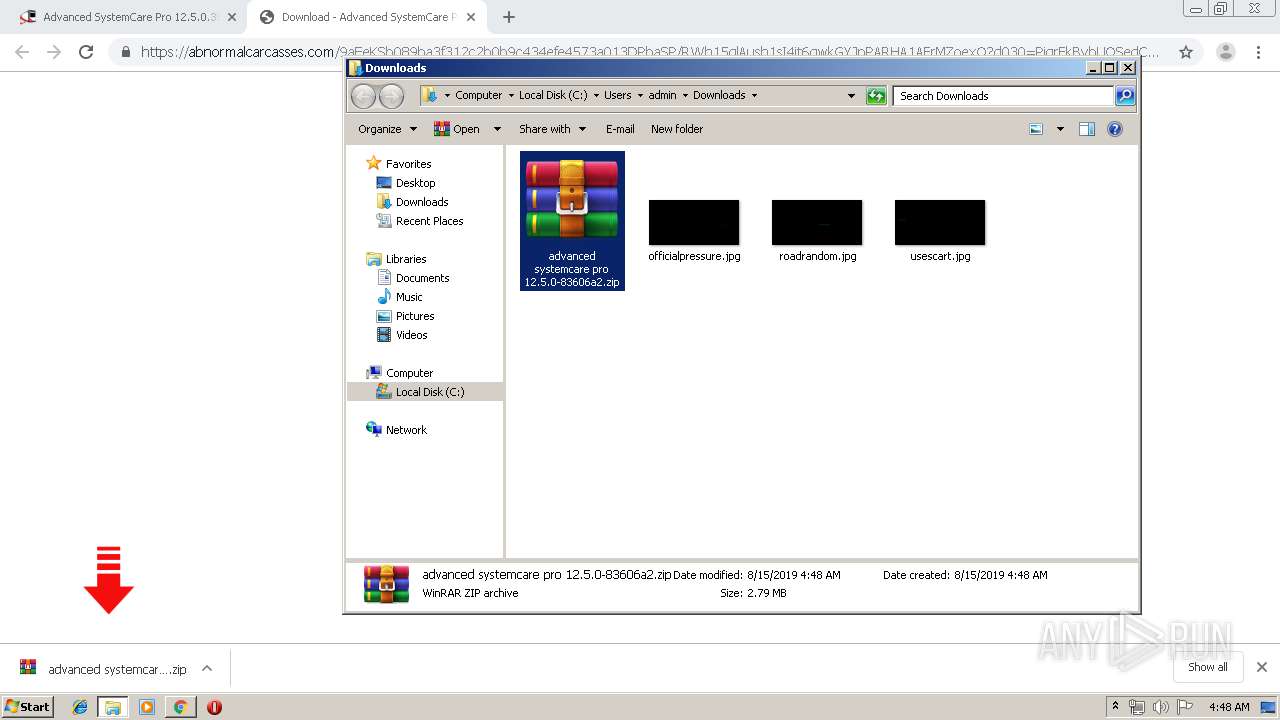
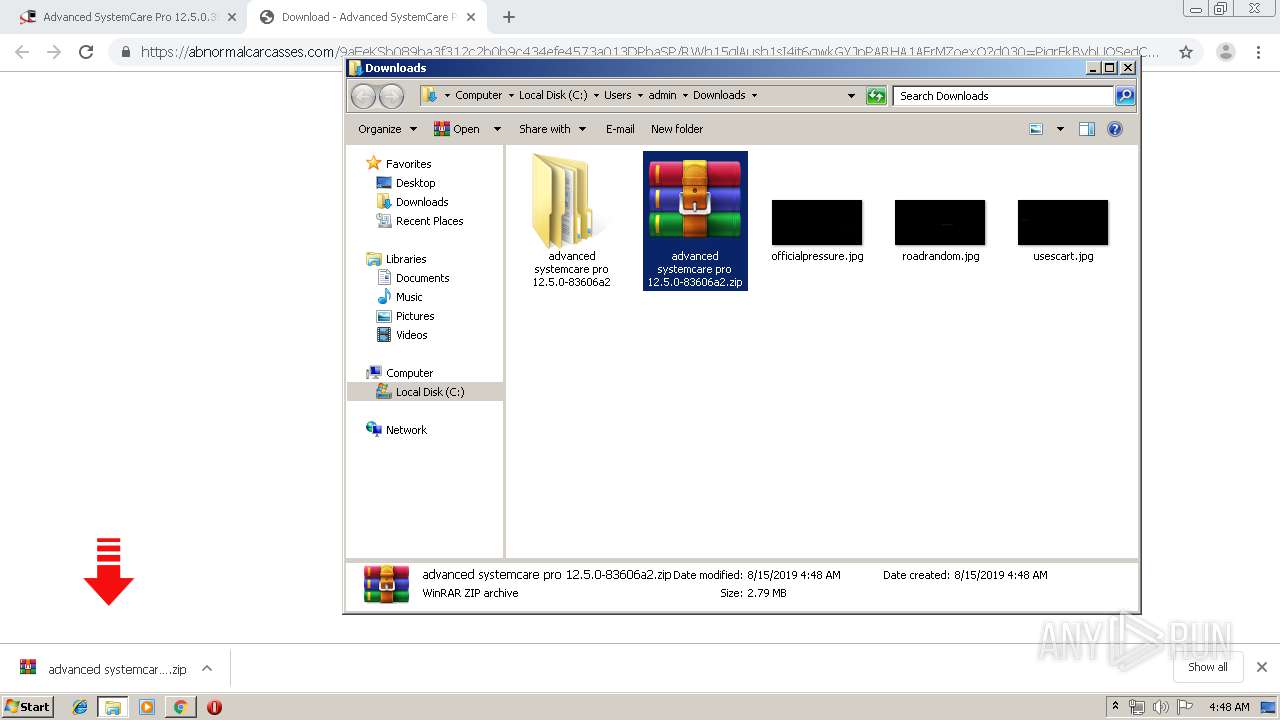
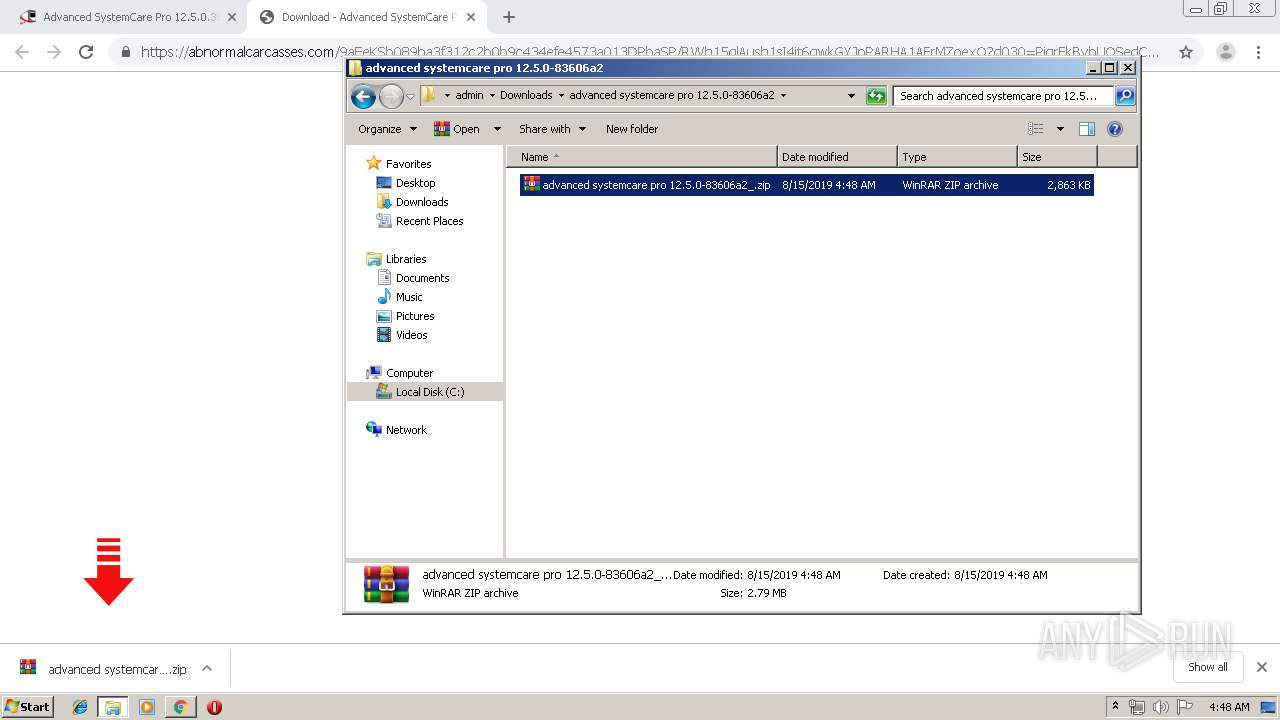
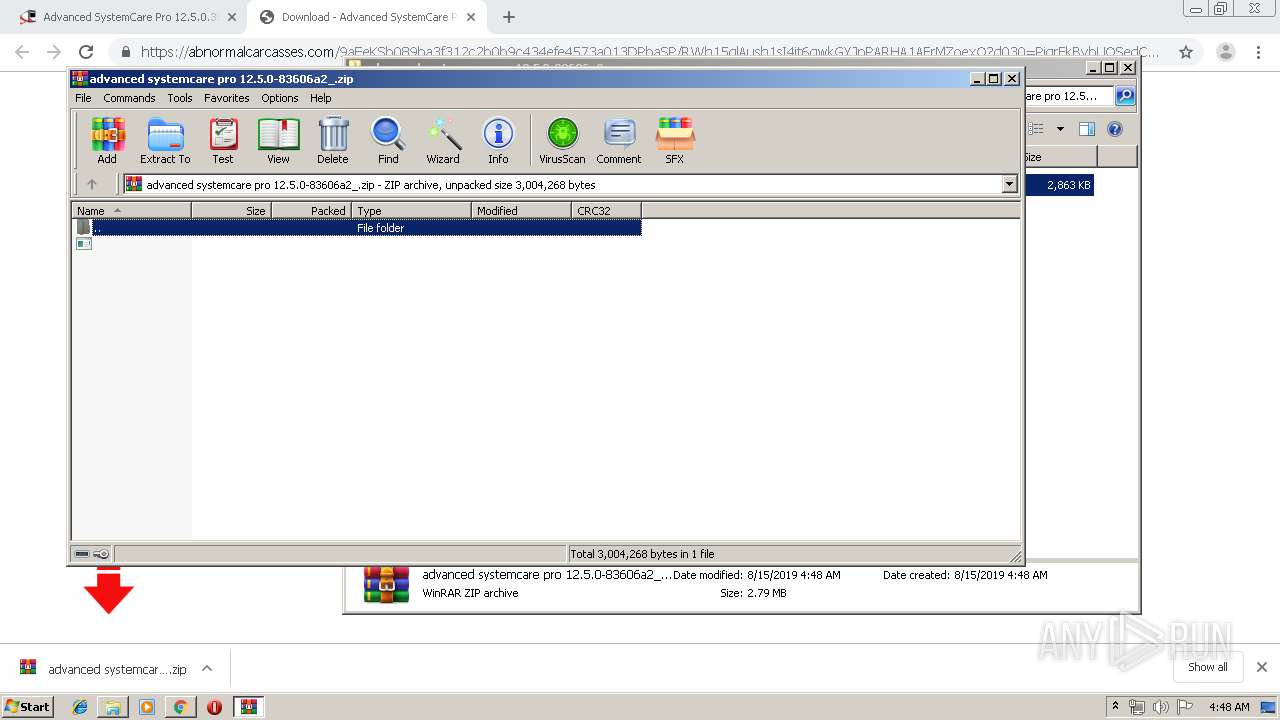
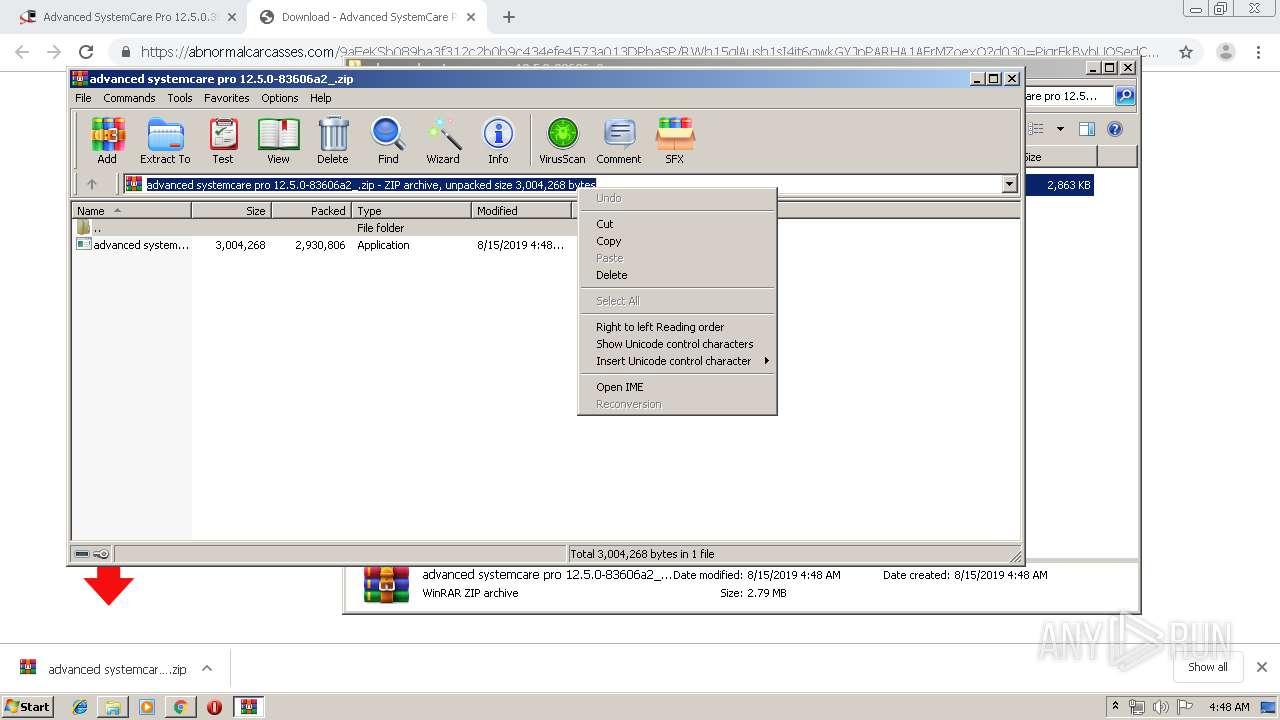
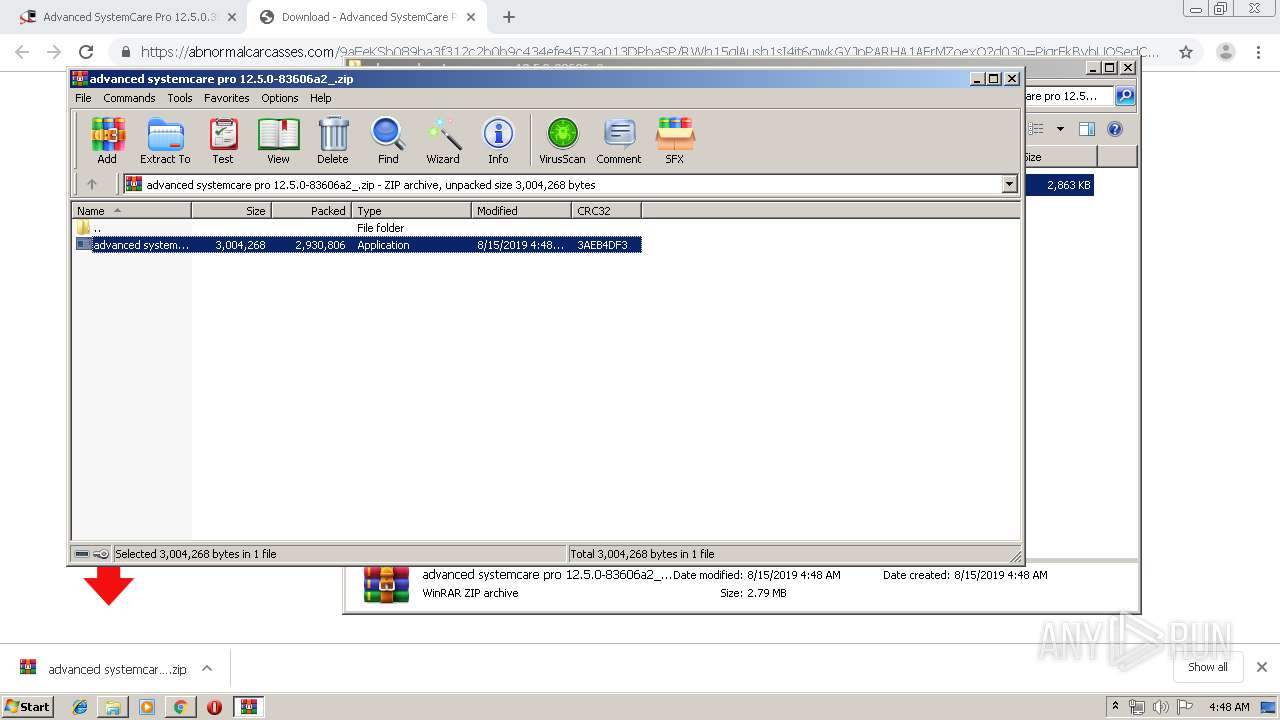
Manual execution by user
- WinRAR.exe (PID: 3584)
- WinRAR.exe (PID: 3600)
- WinRAR.exe (PID: 1492)
- WinRAR.exe (PID: 3992)
- WinRAR.exe (PID: 3832)
Reads Internet Cache Settings
- chrome.exe (PID: 3668)
Reads settings of System Certificates
- chrome.exe (PID: 3624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
32
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,10164608095345053607,13951059651674937475,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11862580940422065656 --mojo-platform-channel-handle=3340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6eafa9d0,0x6eafa9e0,0x6eafa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,10164608095345053607,13951059651674937475,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13496319538441688198 --mojo-platform-channel-handle=3600 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,10164608095345053607,13951059651674937475,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11295445549217718732 --mojo-platform-channel-handle=3684 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
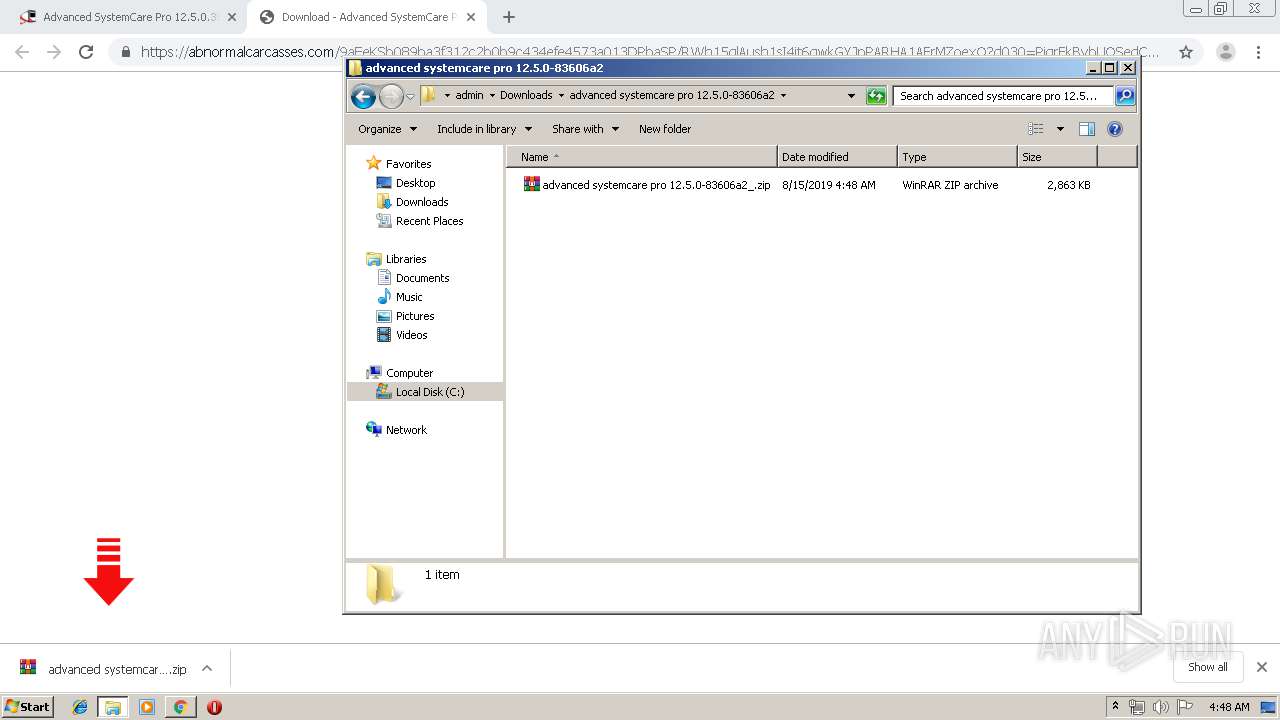
| 1492 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\advanced systemcare pro 12.5.0-83606a2\advanced systemcare pro 12.5.0-83606a2_.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,10164608095345053607,13951059651674937475,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15011145362882659883 --mojo-platform-channel-handle=2092 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,10164608095345053607,13951059651674937475,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16183003489107098437 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3720 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3988 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,10164608095345053607,13951059651674937475,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10062607152585150102 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,10164608095345053607,13951059651674937475,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1141006724710373936 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 655
Read events
1 537
Write events
113
Delete events
5
Modification events
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3668-13210314480757375 |
Value: 259 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3668) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3668-13210314480757375 |
Value: 259 | |||
Executable files
0
Suspicious files
38
Text files
152
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8ca9ee13-e641-4643-b36d-c9af1f9cfa23.tmp | — | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF36d599.TMP | text | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF36d56a.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
47
DNS requests
31
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3624 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
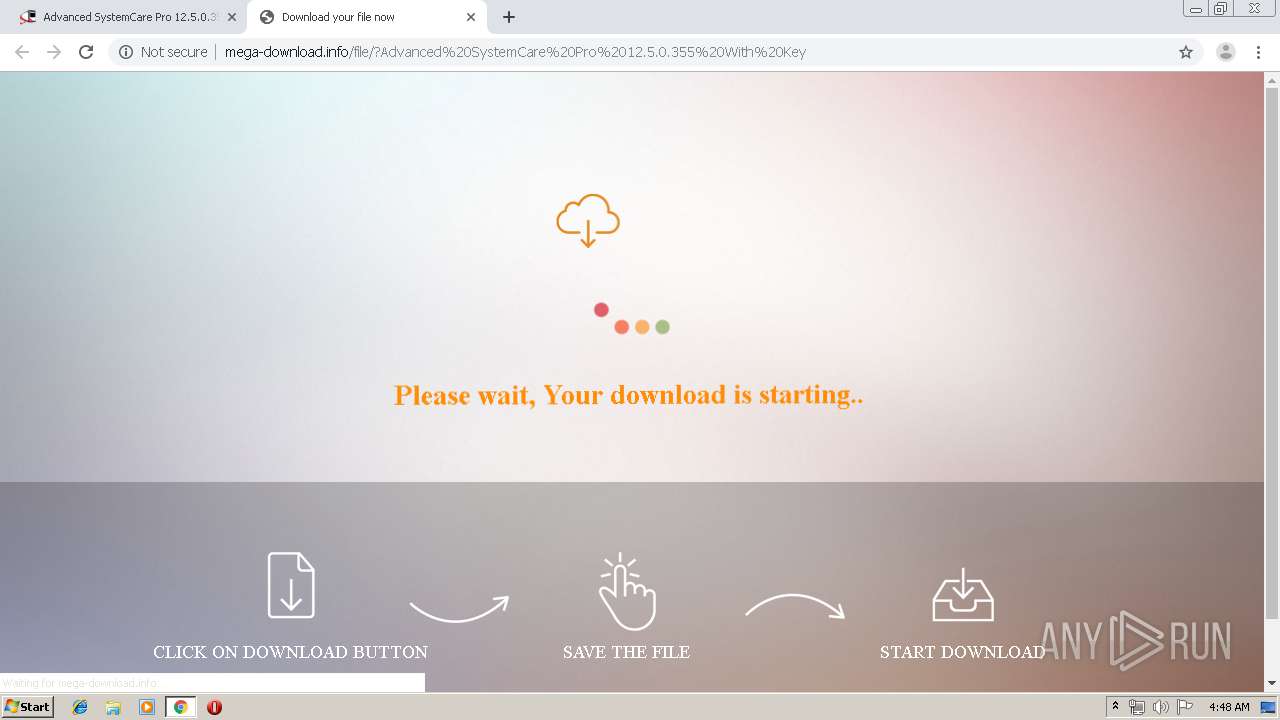
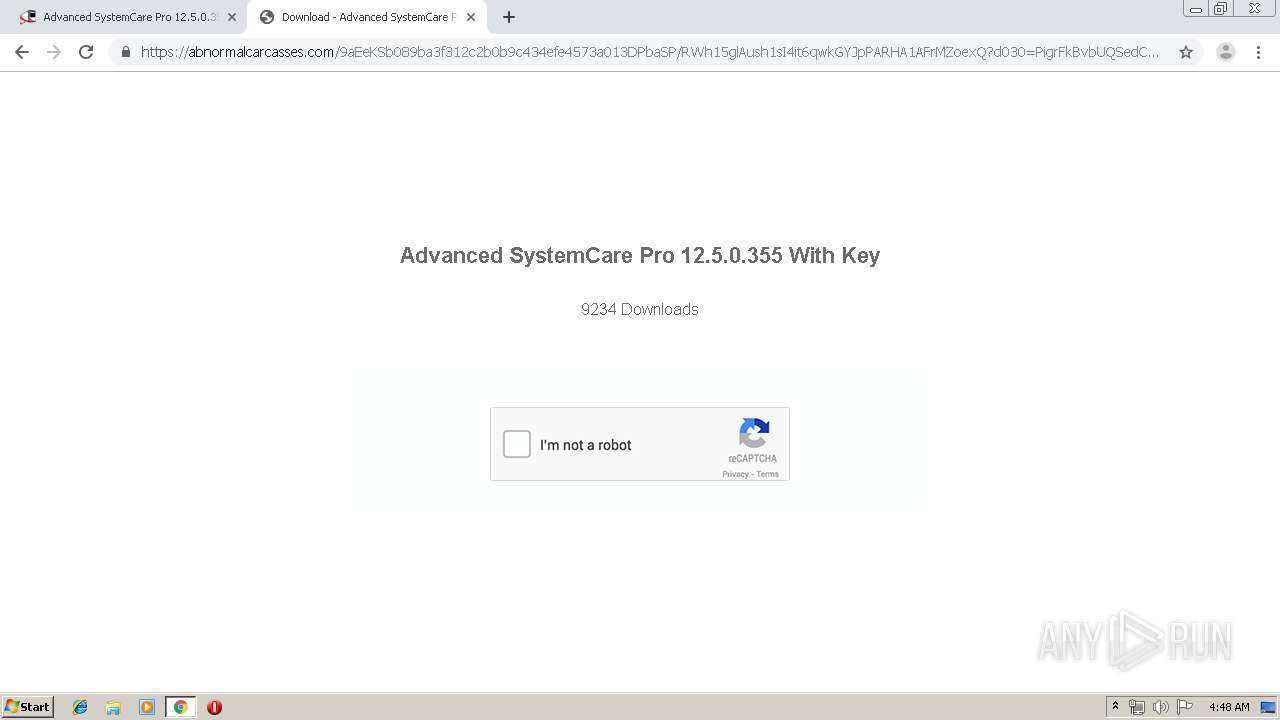
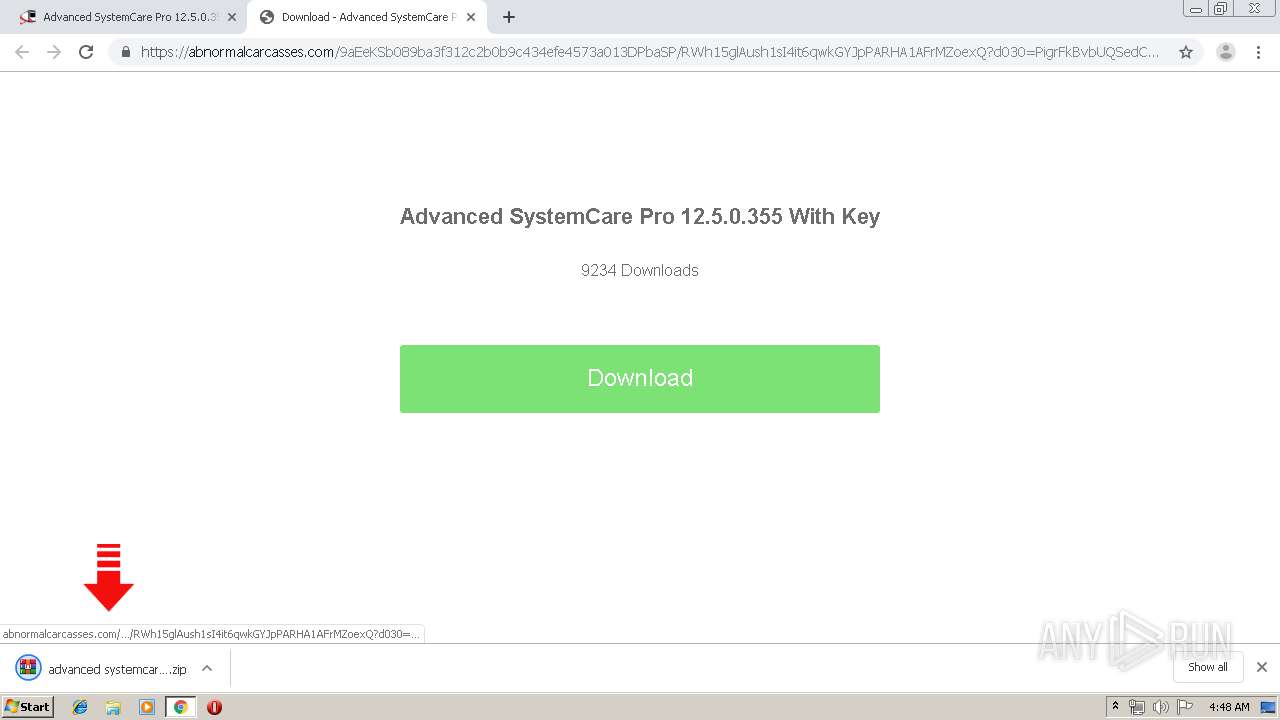
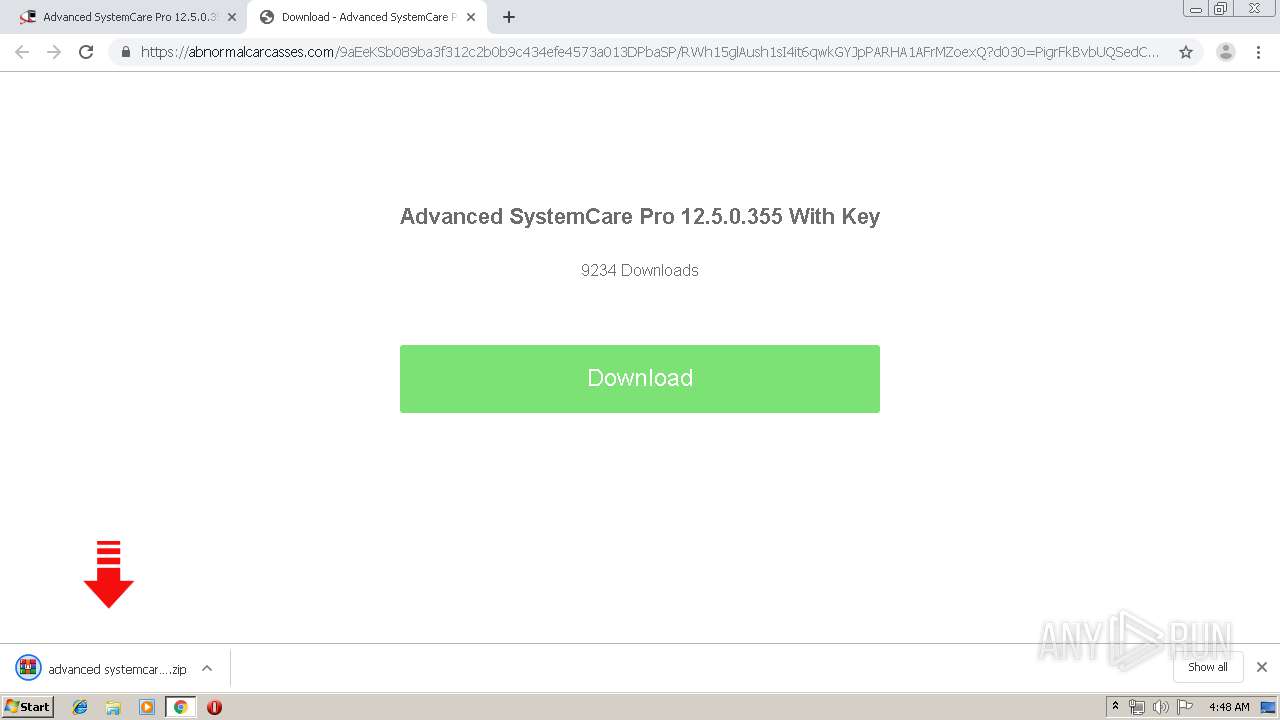
3624 | chrome.exe | GET | 200 | 89.248.168.177:80 | http://mega-download.info/file/style.css | SC | text | 1.35 Kb | suspicious |
3624 | chrome.exe | GET | 200 | 89.248.168.177:80 | http://mega-download.info/file/?Advanced%20SystemCare%20Pro%2012.5.0.355%20With%20Key | SC | html | 764 b | suspicious |
3624 | chrome.exe | GET | 301 | 89.248.168.177:80 | http://mega-download.info/file?Advanced%20SystemCare%20Pro%2012.5.0.355%20With%20Key | SC | html | 293 b | suspicious |
3624 | chrome.exe | GET | 500 | 89.248.168.177:80 | http://mega-download.info/images/loading.gif | SC | html | 680 b | suspicious |
3624 | chrome.exe | GET | 200 | 89.248.168.177:80 | http://mega-download.info/file/javascript.js | SC | text | 539 b | suspicious |
3624 | chrome.exe | GET | 200 | 89.248.168.177:80 | http://mega-download.info/file/images/sprites-steps.png | SC | image | 13.7 Kb | suspicious |
3624 | chrome.exe | GET | 200 | 89.248.168.177:80 | http://mega-download.info/file/images/gaussian-blur.jpg | SC | image | 93.7 Kb | suspicious |
3624 | chrome.exe | GET | 200 | 78.140.165.14:80 | http://wsopicmov.pw/rtb/s/AAnWVF1qWQAAUw8CAFBMGQASAFwql_gA | NL | html | 9.11 Kb | malicious |
3624 | chrome.exe | GET | 200 | 173.194.150.139:80 | http://r5---sn-f5f7ln7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.217.54&mm=28&mn=sn-f5f7ln7s&ms=nvh&mt=1565840583&mv=u&mvi=4&pl=21&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3624 | chrome.exe | 173.194.150.139:80 | r5---sn-f5f7ln7s.gvt1.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 89.248.168.177:443 | piratepc.net | Quasi Networks LTD. | SC | suspicious |
3624 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 172.217.16.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 172.217.22.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 192.0.77.32:443 | s0.wp.com | Automattic, Inc | US | suspicious |
3624 | chrome.exe | 192.0.73.2:443 | secure.gravatar.com | Automattic, Inc | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
piratepc.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
s0.wp.com |
| whitelisted |
secure.gravatar.com |
| whitelisted |
stats.wp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
3624 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |