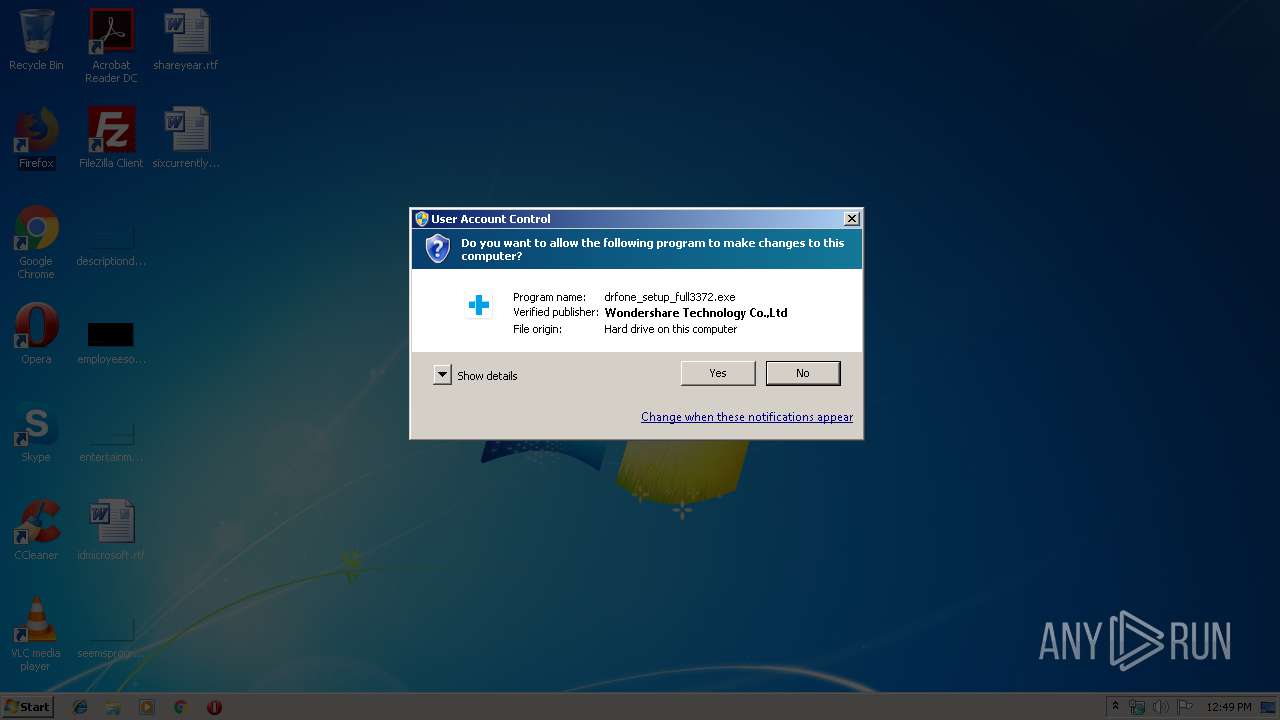
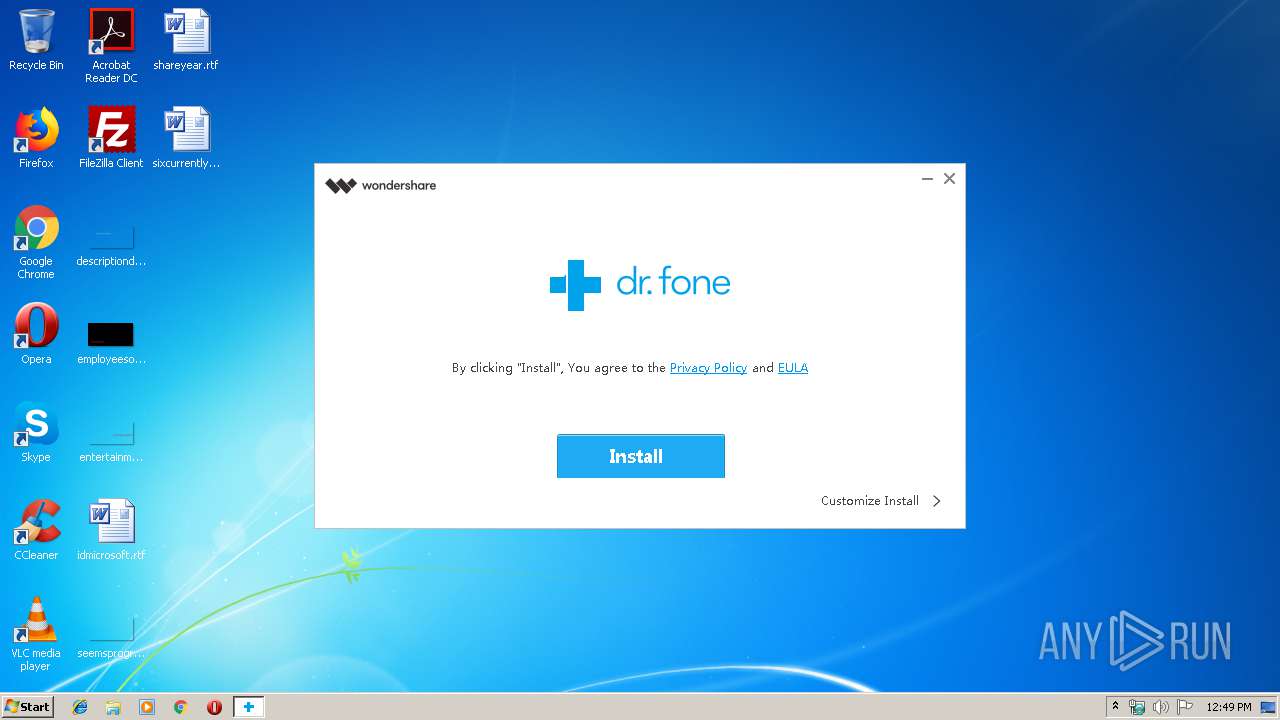
| File name: | drfone_unlock_setup_full3372.exe |
| Full analysis: | https://app.any.run/tasks/2f12c1f5-03d3-4ee6-bd2e-545108ac3810 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 11:49:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1F81B7B803327DC172690C5C5DA1E5FC |
| SHA1: | EB7C8DF1819538646EDA7D33507F4ED61A5C165D |
| SHA256: | 96EDD981C62CCFEFE17CB47DFF8B73058DD3BD34F5A525E13F1AD6172425645A |
| SSDEEP: | 12288:SMRfauvtHMxljmQ5rX+XbKNDkS8mWlWYwU0fClaLMkUtfvHB1+j1:lEmQ5ubKNDkS8m9Yw0WVUFvv+p |
MALICIOUS
Application was dropped or rewritten from another process
- NFWCHK.exe (PID: 2144)
- devcon_x86.exe (PID: 2320)
- devcon_x86.exe (PID: 1420)
- devcon_x86.exe (PID: 2156)
- devcon_x86.exe (PID: 2688)
- WAFSetup.exe (PID: 3444)
- WsAppService.exe (PID: 2404)
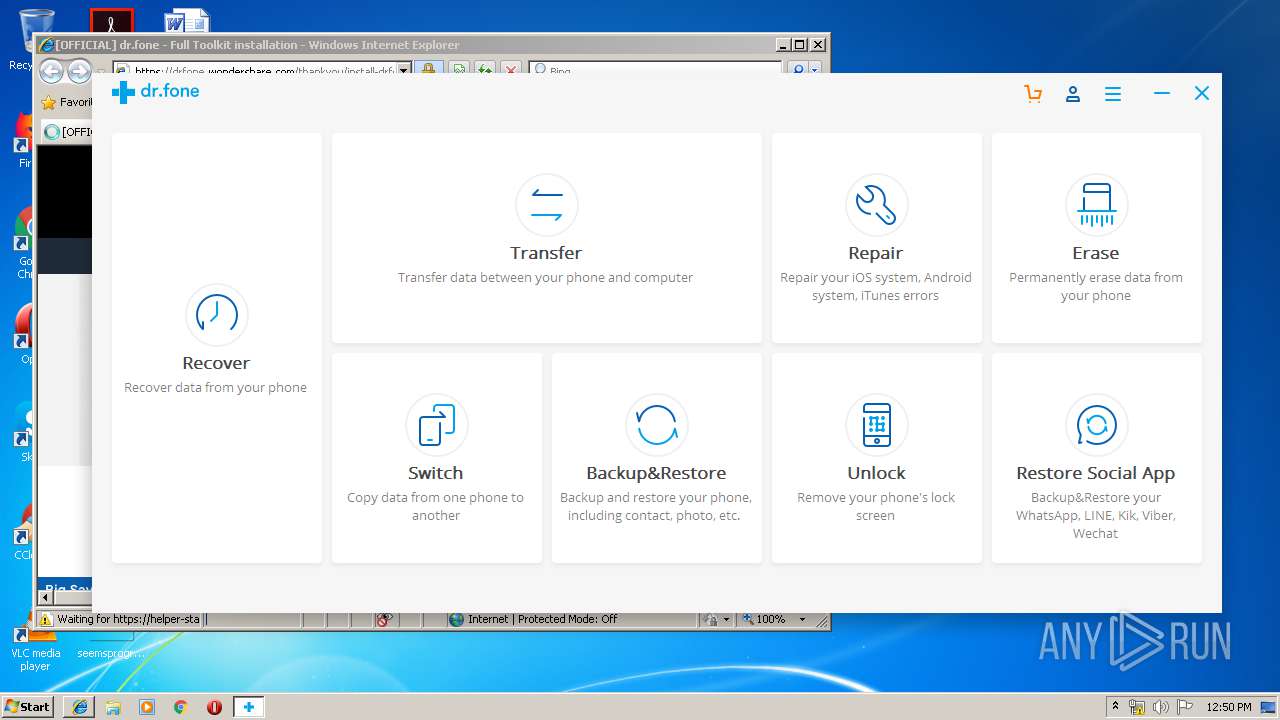
- DrFoneToolKit.exe (PID: 3404)
- WsAppClient.exe (PID: 2424)
- CrashService.exe (PID: 2864)
- DrFoneUnlock.exe (PID: 3936)
Changes settings of System certificates
- NFWCHk.exe (PID: 2368)
- CertUtil.exe (PID: 2272)
- CertUtil.exe (PID: 3744)
- DrFoneUnlock.exe (PID: 3936)
Loads dropped or rewritten executable
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 3484)
- WsAppService.exe (PID: 2404)
- RegAsm.exe (PID: 2240)
- RegAsm.exe (PID: 2608)
- RegAsm.exe (PID: 932)
- RegAsm.exe (PID: 3668)
- DrFoneToolKit.exe (PID: 3404)
- WsAppClient.exe (PID: 2424)
- CrashService.exe (PID: 2864)
- DrFoneUnlock.exe (PID: 3936)
SUSPICIOUS
Low-level read access rights to disk partition
- drfone_unlock_setup_full3372.exe (PID: 3864)
Reads internet explorer settings
- drfone_unlock_setup_full3372.exe (PID: 3864)
- WsAppClient.exe (PID: 2424)
Executable content was dropped or overwritten
- drfone_unlock_setup_full3372.exe (PID: 3864)
- drfone_unlock_full3372.exe (PID: 1944)
- NetFxLite.exe (PID: 3144)
- NetFxLite.tmp (PID: 3332)
- drfone_unlock_full3372.tmp (PID: 2572)
- WAFSetup.tmp (PID: 2620)
- WAFSetup.exe (PID: 3444)
- devcon_x86.exe (PID: 2320)
- DrFoneToolKit.exe (PID: 2244)
- DrFoneToolKit.tmp (PID: 1084)
- WsAppService.exe (PID: 2404)
- DrFoneUnlock.exe (PID: 3412)
- DrFoneUnlock.tmp (PID: 1904)
- devcon_x86.exe (PID: 2156)
- devcon_x86.exe (PID: 2688)
- DrvInst.exe (PID: 4052)
Reads Windows owner or organization settings
- drfone_unlock_full3372.tmp (PID: 2572)
- NetFxLite.tmp (PID: 3332)
- WAFSetup.tmp (PID: 2620)
- DrFoneToolKit.tmp (PID: 1084)
- DrFoneUnlock.tmp (PID: 1904)
Reads the Windows organization settings
- drfone_unlock_full3372.tmp (PID: 2572)
- NetFxLite.tmp (PID: 3332)
- WAFSetup.tmp (PID: 2620)
- DrFoneToolKit.tmp (PID: 1084)
- DrFoneUnlock.tmp (PID: 1904)
Reads Internet Cache Settings
- drfone_unlock_setup_full3372.exe (PID: 3864)
- RegAsm.exe (PID: 2240)
Creates files in the Windows directory
- drfone_unlock_full3372.tmp (PID: 2572)
- NetFxLite.tmp (PID: 3332)
- WAFSetup.tmp (PID: 2620)
- DrvInst.exe (PID: 3116)
- devcon_x86.exe (PID: 2320)
- DrvInst.exe (PID: 2912)
- InstallUtil.exe (PID: 1332)
- CertUtil.exe (PID: 2272)
- CertUtil.exe (PID: 3744)
- DrvInst.exe (PID: 4052)
- DrvInst.exe (PID: 3020)
Adds / modifies Windows certificates
- NFWCHk.exe (PID: 2368)
- DrFoneUnlock.exe (PID: 3936)
Creates COM task schedule object
- RegAsm.exe (PID: 2240)
- RegAsm.exe (PID: 932)
- RegAsm.exe (PID: 2324)
Reads Environment values
- RegAsm.exe (PID: 2240)
- WsAppService.exe (PID: 2404)
- DrFoneToolKit.exe (PID: 3404)
- WsAppClient.exe (PID: 2424)
- DrFoneUnlock.exe (PID: 3936)
Creates files in the program directory
- RegAsm.exe (PID: 932)
- RegAsm.exe (PID: 2240)
- RegAsm.exe (PID: 3484)
- WsAppService.exe (PID: 2404)
- RegAsm.exe (PID: 2324)
- InstallUtil.exe (PID: 1332)
- DrFoneToolKit.exe (PID: 3404)
- WsAppClient.exe (PID: 2424)
- DrFoneUnlock.exe (PID: 3936)
Modifies the open verb of a shell class
- RegAsm.exe (PID: 932)
Creates or modifies windows services
- WAFSetup.tmp (PID: 2620)
Removes files from Windows directory
- DrvInst.exe (PID: 2912)
- DrvInst.exe (PID: 3116)
- CertUtil.exe (PID: 2272)
- CertUtil.exe (PID: 3744)
- DrvInst.exe (PID: 4052)
- DrvInst.exe (PID: 3020)
Creates files in the driver directory
- DrvInst.exe (PID: 2912)
- DrvInst.exe (PID: 3116)
- DrvInst.exe (PID: 4052)
- DrvInst.exe (PID: 3020)
Searches for installed software
- DrFoneToolKit.tmp (PID: 1084)
- RegAsm.exe (PID: 2240)
- DrFoneUnlock.tmp (PID: 1904)
- WsAppService.exe (PID: 2404)
Creates files in the user directory
- DrFoneUnlock.tmp (PID: 1904)
- drfone_unlock_full3372.tmp (PID: 2572)
Starts Internet Explorer
- drfone_unlock_setup_full3372.exe (PID: 3864)
INFO
Application was dropped or rewritten from another process
- drfone_unlock_full3372.tmp (PID: 2572)
- NFWCHk.exe (PID: 2368)
- DrFoneToolKit.tmp (PID: 1084)
- DrFoneUnlock.exe (PID: 3412)
- DrFoneUnlock.tmp (PID: 1904)
- NetFxLite.tmp (PID: 3332)
- NetFxLite.exe (PID: 3144)
- DrFoneToolKit.exe (PID: 2244)
- WAFSetup.tmp (PID: 2620)
Loads dropped or rewritten executable
- drfone_unlock_full3372.tmp (PID: 2572)
- WAFSetup.tmp (PID: 2620)
Creates a software uninstall entry
- drfone_unlock_full3372.tmp (PID: 2572)
Dropped object may contain Bitcoin addresses
- drfone_unlock_full3372.tmp (PID: 2572)
Creates files in the program directory
- WAFSetup.tmp (PID: 2620)
- drfone_unlock_full3372.tmp (PID: 2572)
- DrFoneToolKit.tmp (PID: 1084)
- DrFoneUnlock.tmp (PID: 1904)
Changes settings of System certificates
- DrvInst.exe (PID: 4052)
- iexplore.exe (PID: 2632)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 4052)
- iexplore.exe (PID: 2632)
Application launched itself
- iexplore.exe (PID: 2220)
Changes internet zones settings
- iexplore.exe (PID: 2220)
Creates files in the user directory
- iexplore.exe (PID: 2632)
Reads internet explorer settings
- iexplore.exe (PID: 2632)
Reads Internet Cache Settings
- iexplore.exe (PID: 2632)
Reads settings of System Certificates
- iexplore.exe (PID: 2632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (16.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (14.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.4) |
| .exe | | | Win32 Executable (generic) (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:07:05 11:49:09+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 451072 |
| InitializedDataSize: | 534528 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x51205 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.10.2 |
| ProductVersionNumber: | 2.0.10.2 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | drfone_setup_full3372.exe |
| FileVersion: | 2.0.10.2 |
| LegalCopyright: | Copyright©2017 Wondershare. All rights reserved. |
| ProductName: | drfone |
| ProductVersion: | 9.6.3 |
Total processes
92
Monitored processes
39
Malicious processes
21
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 932 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" "C:\Program Files\Wondershare\WAF\2.4.3.237\WsAppClient.exe" /codebase /tlb:"C:\Program Files\Wondershare\WAF\WsAppClient.tlb" /nologo | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | WAFSetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1084 | "C:\Users\admin\AppData\Local\Temp\is-LK696.tmp\DrFoneToolKit.tmp" /SL5="$50174,726173,121344,C:\Users\admin\AppData\Local\Temp\is-LJEBN.tmp\DrFoneToolKit.exe" /SP- /silent /VERYSILENT /NoCustomize /LANG=ENG /Dir="C:\Program Files\Wondershare\drfone" /CreateDesktopIcon /CreateQuickLaunchIcon | C:\Users\admin\AppData\Local\Temp\is-LK696.tmp\DrFoneToolKit.tmp | DrFoneToolKit.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1332 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" "C:\Program Files\Wondershare\drfone\Library\DriverInstaller\DriverInstall.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | — | DrFoneToolKit.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Framework installation utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Wondershare\drfone\Library\RootRecovery\1.0.0\tools\devcon_x86.exe" dp_add "C:\Program Files\Wondershare\drfone\Library\RootRecovery\1.0.0\tools\driver\ssudbus.inf" | C:\Program Files\Wondershare\drfone\Library\RootRecovery\1.0.0\tools\devcon_x86.exe | — | drfone_unlock_full3372.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 (win7_wdk.100208-1538) Modules
| |||||||||||||||
| 1904 | "C:\Users\admin\AppData\Local\Temp\is-DUFFT.tmp\DrFoneUnlock.tmp" /SL5="$60174,18008873,121344,C:\Users\admin\AppData\Local\Temp\is-LJEBN.tmp\DrFoneUnlock.exe" /SP- /silent /VERYSILENT /LANG=ENG /Dir="C:\Program Files\Wondershare\drfone" | C:\Users\admin\AppData\Local\Temp\is-DUFFT.tmp\DrFoneUnlock.tmp | DrFoneUnlock.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1944 | "C:\Users\Public\Documents\Wondershare\drfone_unlock_full3372.exe" /VERYSILENT /NOPAGE /LANG=ENG /LOG="C:\Users\admin\AppData\Local\Temp\WAE-drfone.log" /installpath: "C:\Program Files\Wondershare\drfone\" /DIR="C:\Program Files\Wondershare\drfone\" | C:\Users\Public\Documents\Wondershare\drfone_unlock_full3372.exe | drfone_unlock_setup_full3372.exe | ||||||||||||
User: admin Company: Wondershare Integrity Level: HIGH Description: dr.fone Exit code: 0 Version: 9.9.8.41 Modules
| |||||||||||||||
| 2144 | C:\Users\Public\Documents\Wondershare\NFWCHK.exe | C:\Users\Public\Documents\Wondershare\NFWCHK.exe | — | drfone_unlock_setup_full3372.exe | |||||||||||
User: admin Company: Wondershare Integrity Level: HIGH Description: .NET Framework Checker Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Wondershare\drfone\Addins\Unlock\devcon_x86.exe" dp_add "C:\Program Files\Wondershare\drfone\Addins\Unlock\Driver\lganddiag.inf" | C:\Program Files\Wondershare\drfone\Addins\Unlock\devcon_x86.exe | DrFoneUnlock.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 (win7_wdk.100208-1538) Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | drfone_unlock_setup_full3372.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2240 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" "C:\Program Files\Wondershare\WAF\2.4.3.237\WsAppService.exe" /codebase /tlb:"C:\Program Files\Wondershare\WAF\WsAppService.tlb" /nologo | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | WAFSetup.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
Total events
3 593
Read events
1 922
Write events
1 619
Delete events
52
Modification events
| (PID) Process: | (3864) drfone_unlock_setup_full3372.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WafCX |
| Operation: | write | Name: | |
Value: sku-ween | |||
| (PID) Process: | (3864) drfone_unlock_setup_full3372.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WafCX |
| Operation: | write | Name: | 3372 |
Value: sku-ween | |||
| (PID) Process: | (3864) drfone_unlock_setup_full3372.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wondershare\Wondershare Helper Compact |
| Operation: | write | Name: | ClientSign |
Value: {C4BA3647-0000-0QM0-0001-5254004A04AF} | |||
| (PID) Process: | (3864) drfone_unlock_setup_full3372.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wondershare\WAF |
| Operation: | write | Name: | ClientSign |
Value: {C4BA3647-0000-0QM0-0001-5254004A04AF} | |||
| (PID) Process: | (3864) drfone_unlock_setup_full3372.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3864) drfone_unlock_setup_full3372.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3864) drfone_unlock_setup_full3372.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\drfone_unlock_setup_full3372_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3864) drfone_unlock_setup_full3372.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\drfone_unlock_setup_full3372_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3864) drfone_unlock_setup_full3372.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\drfone_unlock_setup_full3372_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3864) drfone_unlock_setup_full3372.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\drfone_unlock_setup_full3372_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
203
Suspicious files
56
Text files
823
Unknown types
71
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | drfone_unlock_setup_full3372.exe | C:\Users\Public\Documents\Wondershare\drfone_unlock_full3372.exe.~P2S | — | |
MD5:— | SHA256:— | |||
| 3864 | drfone_unlock_setup_full3372.exe | C:\Users\Public\Documents\Wondershare\drfone_unlock_full3372.exe | — | |
MD5:— | SHA256:— | |||
| 2572 | drfone_unlock_full3372.tmp | C:\Program Files\Wondershare\drfone\is-DH9LJ.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | drfone_unlock_full3372.tmp | C:\Program Files\Wondershare\drfone\is-P1TR4.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | drfone_unlock_full3372.tmp | C:\Program Files\Wondershare\drfone\Library\CBS\is-PQ4S0.tmp | — | |
MD5:— | SHA256:— | |||
| 3864 | drfone_unlock_setup_full3372.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\3372-20181030143622[1].htm | html | |
MD5:— | SHA256:— | |||
| 2572 | drfone_unlock_full3372.tmp | C:\ProgramData\Wondershare\dr.fone\NewCustomization.xml | xml | |
MD5:— | SHA256:— | |||
| 2572 | drfone_unlock_full3372.tmp | C:\Program Files\Wondershare\drfone\Library\ADB\is-SPQQN.tmp | — | |
MD5:— | SHA256:— | |||
| 3864 | drfone_unlock_setup_full3372.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\3372-20181030143622[1].htm | html | |
MD5:— | SHA256:— | |||
| 2572 | drfone_unlock_full3372.tmp | C:\Program Files\Wondershare\drfone\Library\ADB\is-ORENH.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
70
TCP/UDP connections
98
DNS requests
36
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3864 | drfone_unlock_setup_full3372.exe | GET | — | 2.16.186.90:80 | http://download.wondershare.com/cbs_down/drfone_unlock_full3372.exe | unknown | — | — | whitelisted |
3864 | drfone_unlock_setup_full3372.exe | GET | — | 63.159.217.165:80 | http://dlinst.wondershare.com/player/style/orbit-1.3.0.css | US | — | — | suspicious |
3864 | drfone_unlock_setup_full3372.exe | GET | — | 2.16.186.90:80 | http://download.wondershare.com/cbs_down/drfone_unlock_full3372.exe | unknown | — | — | whitelisted |
3864 | drfone_unlock_setup_full3372.exe | GET | — | 2.16.186.90:80 | http://download.wondershare.com/cbs_down/drfone_unlock_full3372.exe | unknown | — | — | whitelisted |
3864 | drfone_unlock_setup_full3372.exe | HEAD | 200 | 2.16.186.90:80 | http://download.wondershare.com/cbs_down/drfone_unlock_full3372.exe | unknown | — | — | whitelisted |
3864 | drfone_unlock_setup_full3372.exe | GET | — | 2.16.186.90:80 | http://download.wondershare.com/cbs_down/drfone_unlock_full3372.exe | unknown | — | — | whitelisted |
3864 | drfone_unlock_setup_full3372.exe | GET | — | 2.16.186.90:80 | http://download.wondershare.com/cbs_down/drfone_unlock_full3372.exe | unknown | — | — | whitelisted |
3864 | drfone_unlock_setup_full3372.exe | GET | — | 2.16.186.90:80 | http://download.wondershare.com/cbs_down/drfone_unlock_full3372.exe | unknown | — | — | whitelisted |
3864 | drfone_unlock_setup_full3372.exe | GET | 200 | 47.91.67.36:80 | http://platform.wondershare.com/rest/v2/downloader/runtime/?client_sign={C4BA3647-0000-0QM0-0001-5254004A04AF}&product_id=3372 | US | xml | 1.54 Kb | suspicious |
3864 | drfone_unlock_setup_full3372.exe | GET | 200 | 63.159.217.165:80 | http://dlinst.wondershare.com/player/3372-20181030143622.html | US | html | 882 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3864 | drfone_unlock_setup_full3372.exe | 47.91.67.36:80 | platform.wondershare.com | Alibaba (China) Technology Co., Ltd. | US | suspicious |
3864 | drfone_unlock_setup_full3372.exe | 63.159.217.165:80 | dlinst.wondershare.com | QUANTIL, INC | US | unknown |
3864 | drfone_unlock_setup_full3372.exe | 2.16.186.83:80 | download.wondershare.com | Akamai International B.V. | — | whitelisted |
2240 | RegAsm.exe | 203.130.48.150:80 | was.wondershare.com | QUANTIL, INC | CN | unknown |
2404 | WsAppService.exe | 63.159.217.174:80 | was-stats.wondershare.com | QUANTIL, INC | US | suspicious |
2240 | RegAsm.exe | 63.159.217.174:80 | was-stats.wondershare.com | QUANTIL, INC | US | suspicious |
2404 | WsAppService.exe | 203.130.48.150:80 | was.wondershare.com | QUANTIL, INC | CN | unknown |
2404 | WsAppService.exe | 2.16.186.64:80 | download.wondershare.com | Akamai International B.V. | — | whitelisted |
2572 | drfone_unlock_full3372.tmp | 47.91.89.199:80 | cbs.wondershare.com | Alibaba (China) Technology Co., Ltd. | US | malicious |
2572 | drfone_unlock_full3372.tmp | 184.31.91.27:443 | drfone.wondershare.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
platform.wondershare.com |
| suspicious |
download.wondershare.com |
| whitelisted |
dlinst.wondershare.com |
| suspicious |
www.download.windowsupdate.com |
| whitelisted |
us.wondershare.com |
| unknown |
was.wondershare.com |
| unknown |
was-stats.wondershare.com |
| suspicious |
cbs.wondershare.com |
| whitelisted |
drfone.wondershare.com |
| suspicious |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3864 | drfone_unlock_setup_full3372.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3864 | drfone_unlock_setup_full3372.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3864 | drfone_unlock_setup_full3372.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3864 | drfone_unlock_setup_full3372.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3864 | drfone_unlock_setup_full3372.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|