| URL: | zapto.org |
| Full analysis: | https://app.any.run/tasks/7c382e0a-a1d5-4ee2-a177-05ef91ee8cf5 |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2023, 23:05:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 13377DAC5A9D87C76E88880AE46BEFE9 |
| SHA1: | B17842AEA21326F3BEC60785ACBBF58C6FDC4E6B |
| SHA256: | 96ED7EB2F75840734D8C82C0CDA310F4ECA122E60C5DE0DA2F37CAD4B4758CF0 |
| SSDEEP: | 3:oK:v |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3428)
Checks supported languages
- wmpnscfg.exe (PID: 3632)
Manual execution by a user
- wmpnscfg.exe (PID: 3632)
Reads the computer name
- wmpnscfg.exe (PID: 3632)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3216 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3428 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3428 | "C:\Program Files\Internet Explorer\iexplore.exe" "zapto.org" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3632 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
19 197
Read events
19 084
Write events
110
Delete events
3
Modification events
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
46
Text files
44
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3216 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\FI9LB3KU.txt | text | |
MD5:2F0026B759031DCCF04C4873C4F7E658 | SHA256:B4F22764A9E0B16FAEE6EB6A6970910EFA5CD7E781DDF2F77D2B2890792B88BD | |||
| 3428 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\logo-grey[1].png | image | |
MD5:9B0EE274D3E0546FE2D5515C182E874F | SHA256:BEACEB10412E96FB56E91B8451872257F3D3D741C66FF7ED59B5180BA6A25ECF | |||
| 3428 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:B76DDB1D643B8A1FBA0A5D38A4872AF7 | SHA256:9BEF20F86C9CD51A7D0CCB823F1A583FF90654C6AA1D7EF6763D341BF0112C22 | |||
| 3428 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | binary | |
MD5:264EC1C52C79ADF28F4CAE58DA29B77D | SHA256:55D51093175862EB6E66E112F661304D22CEAEEC4051C8EDE932369513A6C167 | |||
| 3428 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | binary | |
MD5:7D536FCB9FD9797C34E408FC410EBFE2 | SHA256:F6C44B4D754640E4AE96FDD36597A8E5BD0F206CC18B4157F322FA201404FE93 | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\shortstar[1].css | text | |
MD5:1E52D4E0657BE67C16FE32134C6F42DA | SHA256:49C0C251A5FA8B7A34159A1C32D8FE410068C7878AE45F4C992173D04D9D7147 | |||
| 3428 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3428 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\6xKydSBYKcSV-LCoeQqfX1RYOo3ik4zwlxdo[1].woff | binary | |
MD5:3BCC787B94E90E45DCE32670AD2F3845 | SHA256:D40268EACF4E3F34EC8272B42364310EEF19D0B5067AA7F6D8B3C11A23A25243 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
73
DNS requests
33
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
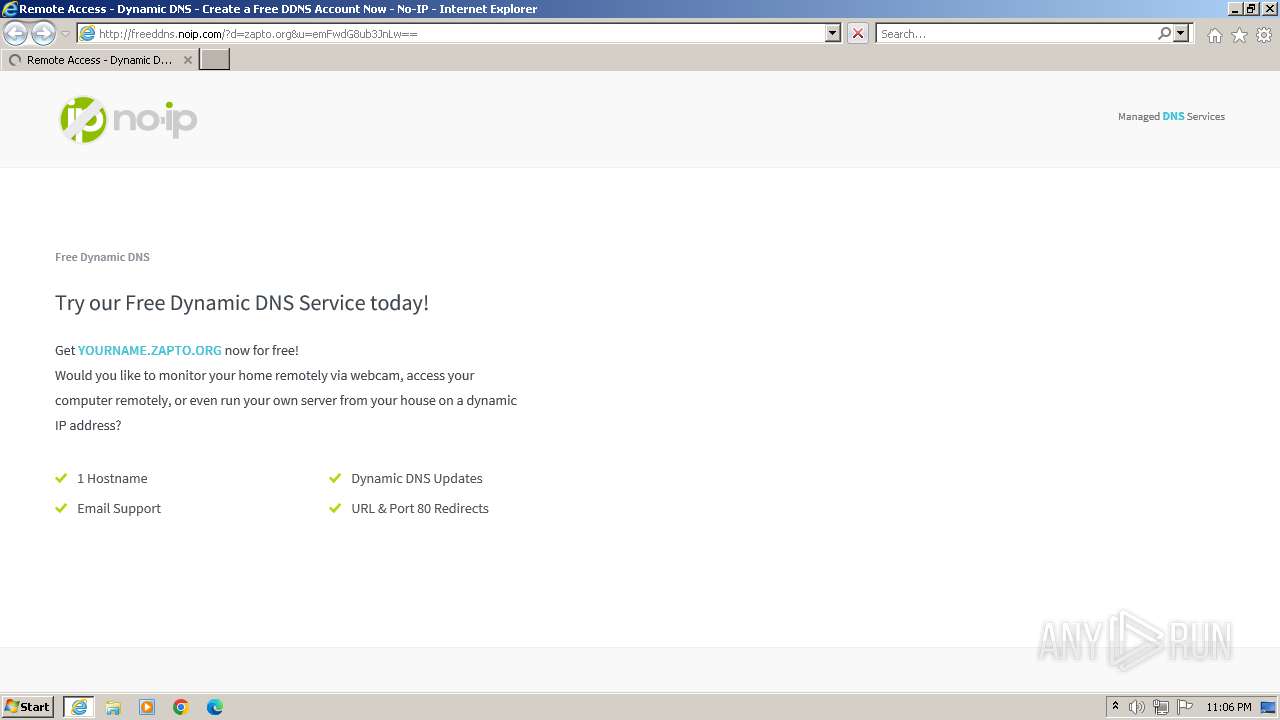
3216 | iexplore.exe | GET | 200 | 158.247.7.206:80 | http://freeddns.noip.com/?d=zapto.org&u=emFwdG8ub3JnLw== | unknown | html | 11.3 Kb | unknown |
3216 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://fonts.gstatic.com/s/opensans/v36/memSYaGs126MiZpBA-UvWbX2vVnXBbObj2OVZyOOSr4dVJWUgsg-1x4gaVQ.woff | unknown | binary | 21.8 Kb | unknown |
3216 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://fonts.gstatic.com/s/opensans/v36/memSYaGs126MiZpBA-UvWbX2vVnXBbObj2OVZyOOSr4dVJWUgsjZ0B4gaVQ.woff | unknown | binary | 22.3 Kb | unknown |
3216 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://fonts.gstatic.com/s/opensans/v36/memSYaGs126MiZpBA-UvWbX2vVnXBbObj2OVZyOOSr4dVJWUgsgH1x4gaVQ.woff | unknown | binary | 22.3 Kb | unknown |
3216 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://fonts.gstatic.com/s/robotoslab/v34/BngbUXZYTXPIvIBgJJSb6s3BzlRRfKOFbvjojISmb2Rl.woff | unknown | binary | 17.1 Kb | unknown |
3216 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3216 | iexplore.exe | GET | 301 | 158.247.7.206:80 | http://zapto.org/ | unknown | — | — | unknown |
3216 | iexplore.exe | GET | 200 | 143.204.205.79:80 | http://d2qr50rz2oof04.cloudfront.net/assets/build/css/shortstar.css?id=1e52d4e0657be67c16fe | unknown | text | 133 Kb | unknown |
3216 | iexplore.exe | GET | 200 | 143.204.205.79:80 | http://d2qr50rz2oof04.cloudfront.net/assets/img/logo/logo-grey.png | unknown | image | 1.52 Kb | unknown |
3216 | iexplore.exe | GET | 200 | 142.250.186.106:80 | http://fonts.googleapis.com/css?family=Source+Sans+Pro:300,400,600,700|Open+Sans:400,300,600,700|Dosis:300,400|Roboto+Slab:400 | unknown | text | 457 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | iexplore.exe | 158.247.7.206:80 | zapto.org | NOIP-VITAL | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3216 | iexplore.exe | 143.204.205.79:80 | d2qr50rz2oof04.cloudfront.net | AMAZON-02 | US | unknown |
3216 | iexplore.exe | 142.250.186.106:80 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3428 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3428 | iexplore.exe | 184.24.77.194:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3428 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zapto.org |
| unknown |
freeddns.noip.com |
| malicious |
d2qr50rz2oof04.cloudfront.net |
| unknown |
fonts.googleapis.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report