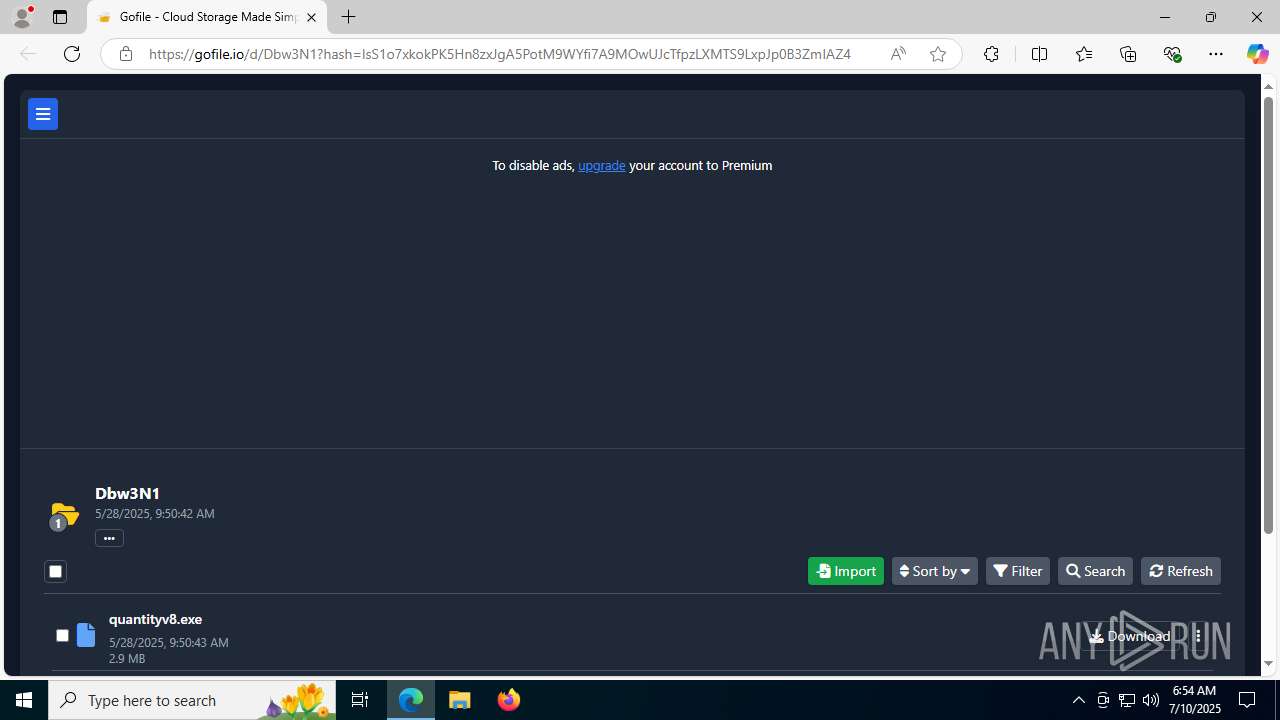
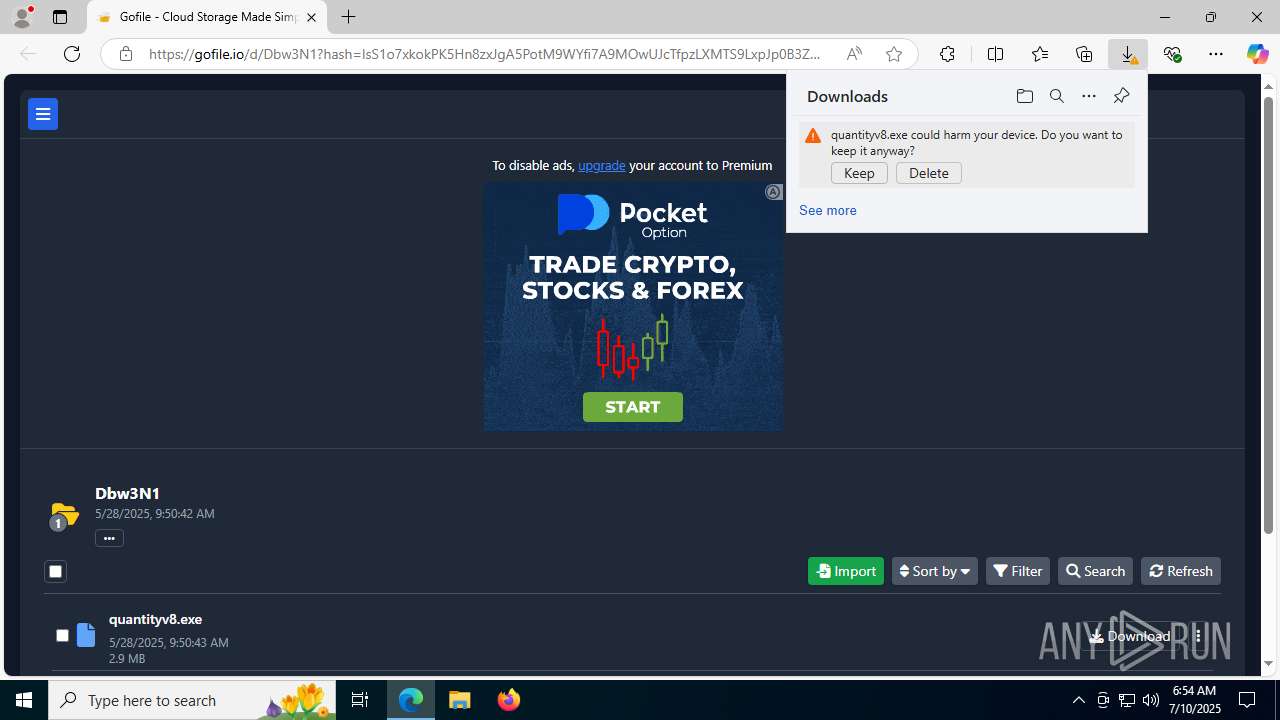
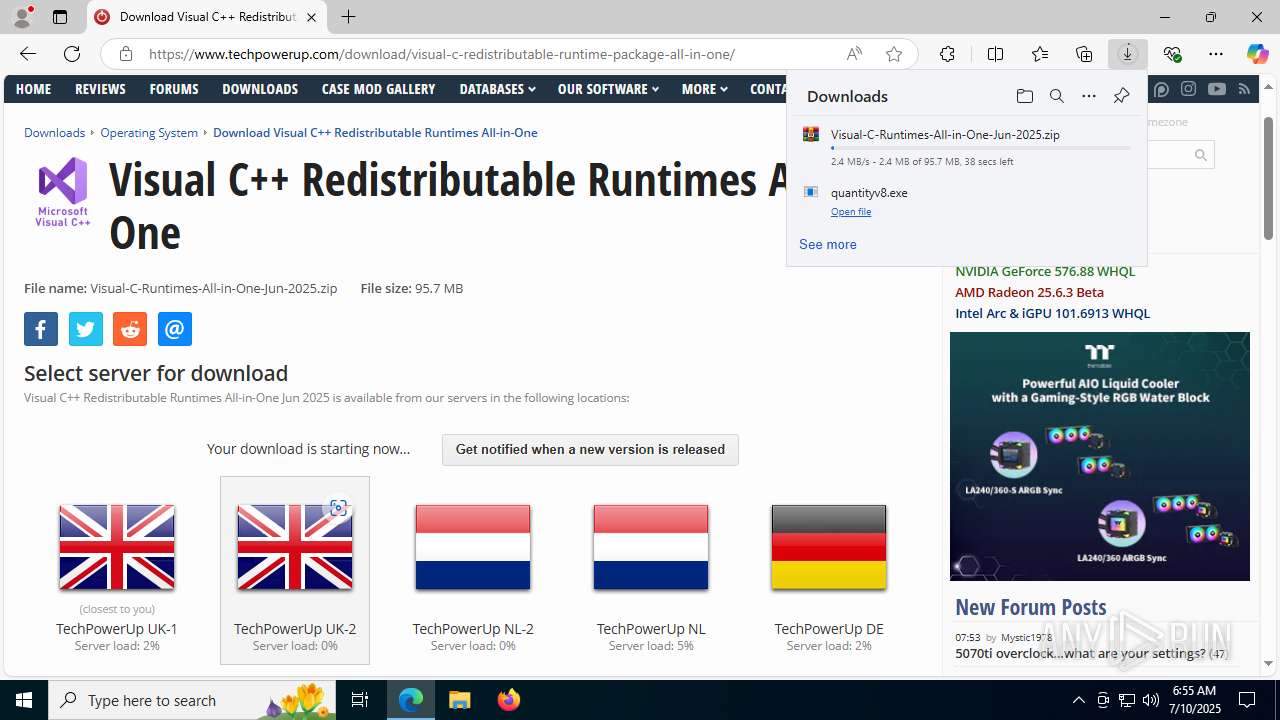
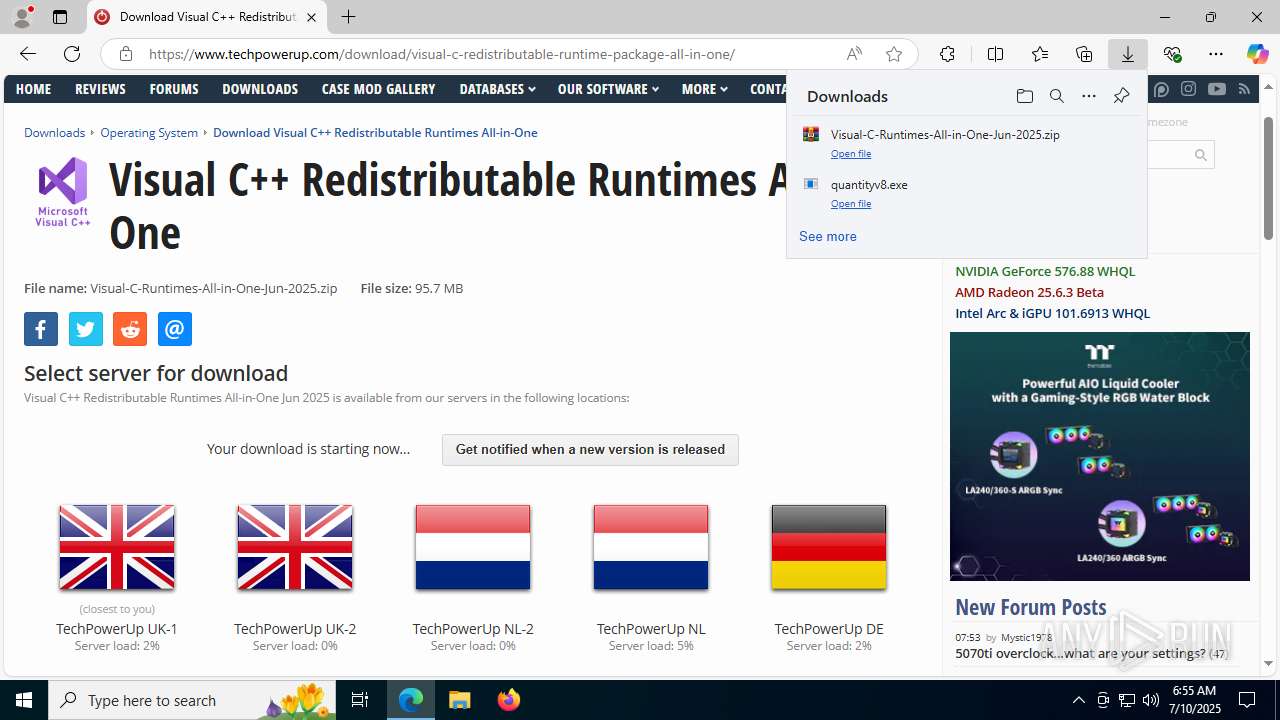
| URL: | https://gofile.io/d/Dbw3N1?hash=IsS1o7xkokPK5Hn8zxJgA5PotM9WYfi7A9MOwUJcTfpzLXMTS9LxpJp0B3ZmIAZ4 |
| Full analysis: | https://app.any.run/tasks/2e4335ed-a293-4bda-9b8c-0e54955c533e |
| Verdict: | Malicious activity |
| Analysis date: | July 10, 2025, 06:54:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 603234702DB8671536CCB8A2648D1F52 |
| SHA1: | FAF4C81EA82CCDAC058CB270B8E30195F084126D |
| SHA256: | 96E810B1182E164F1D18543425F76ED3BC8A08D8277663F792D9829326213F63 |
| SSDEEP: | 3:N8rxL1v//YKa0EE3DMutXHnW2n:2Z1FQutX22n |
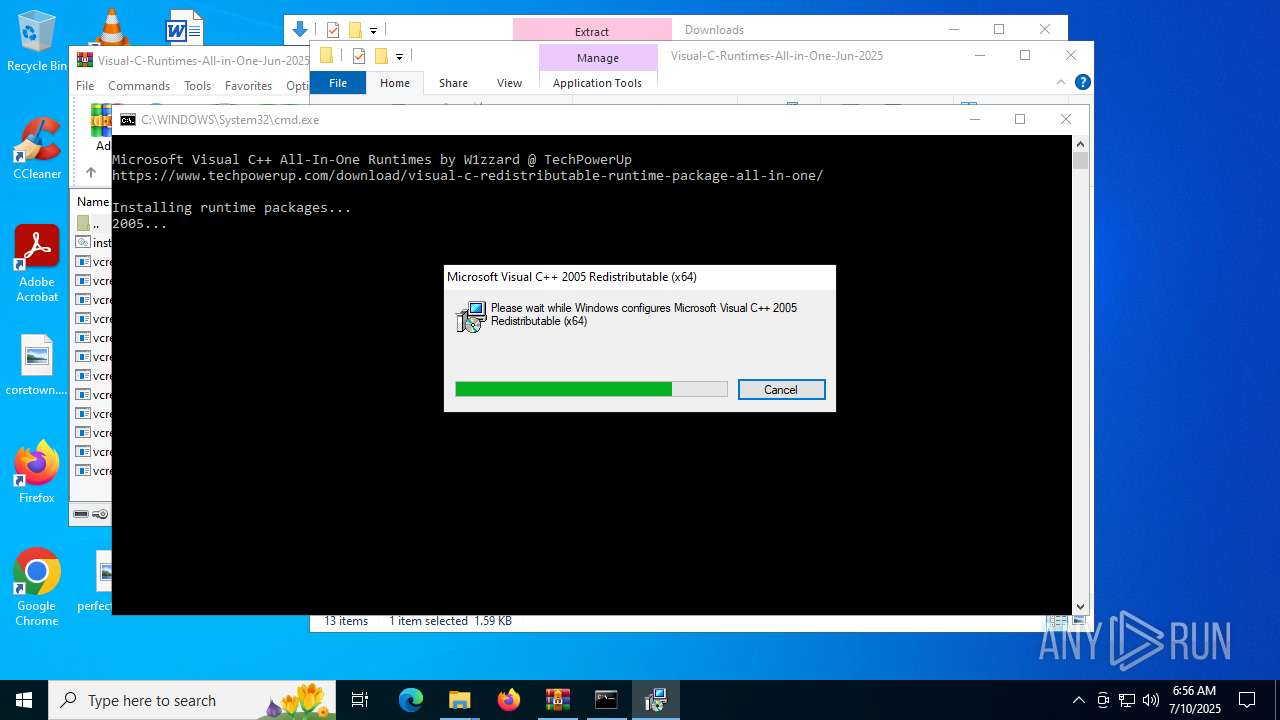
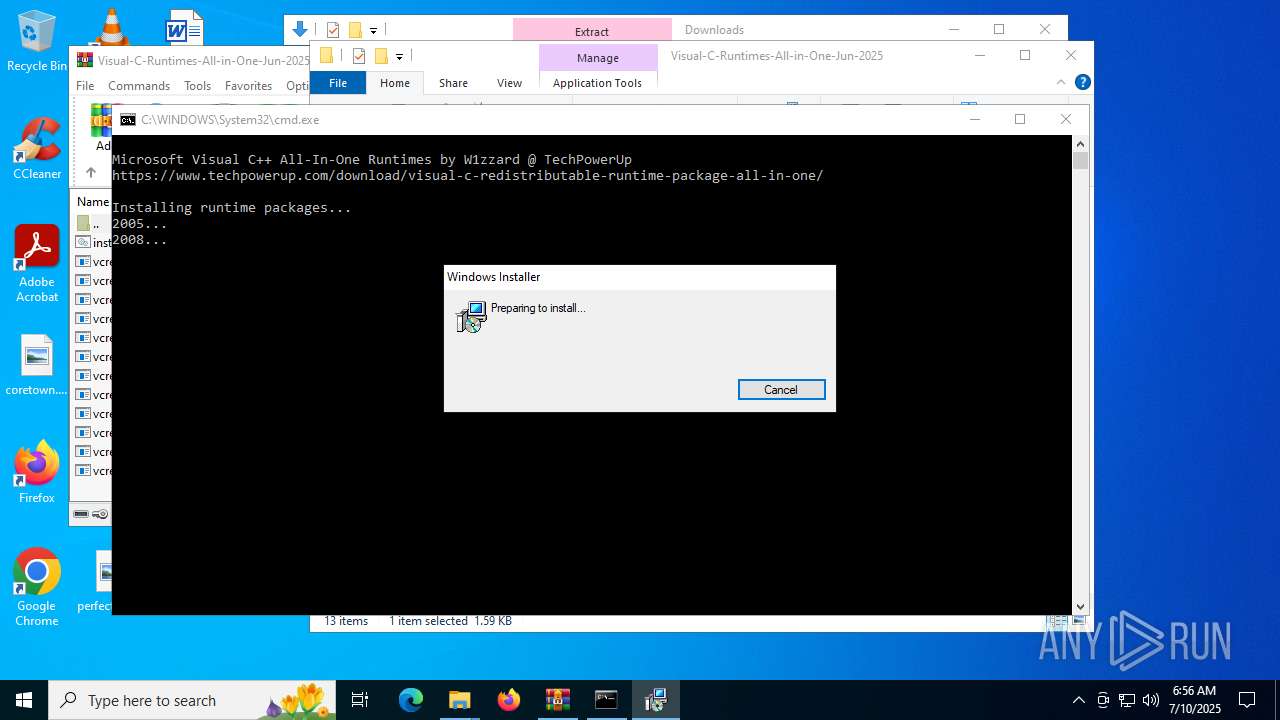
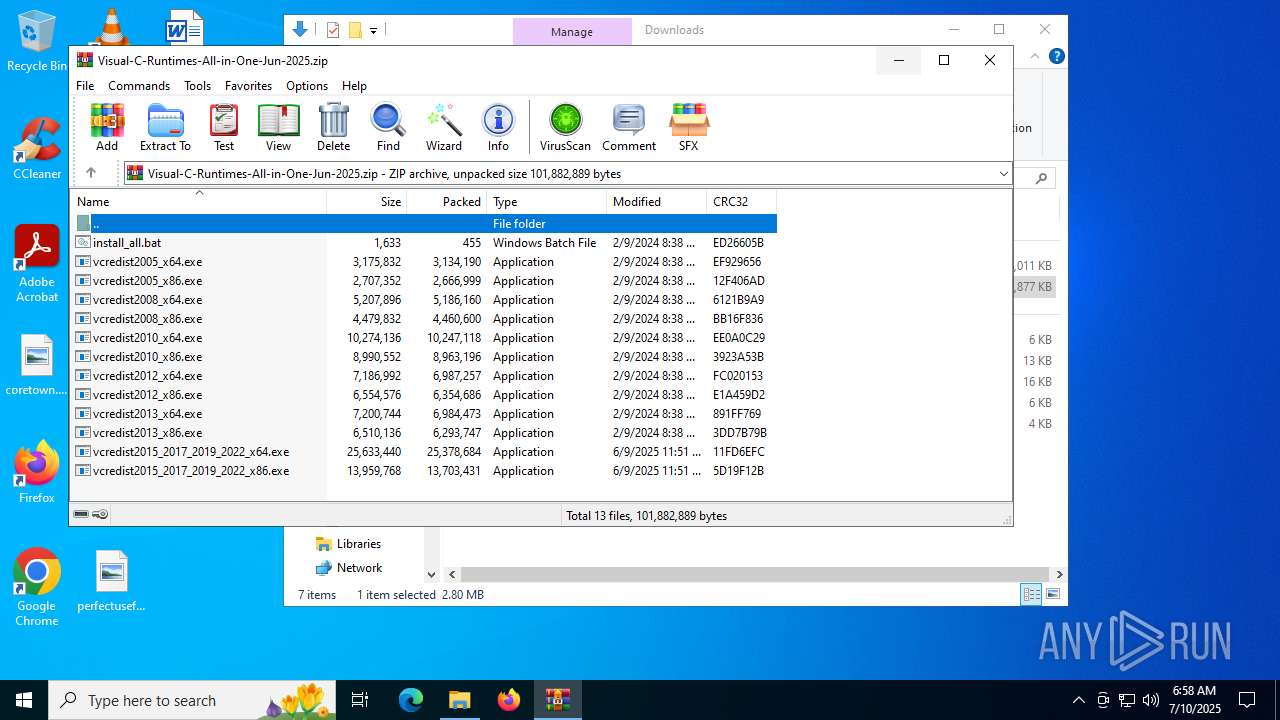
MALICIOUS
Changes the autorun value in the registry
- vcredist2005_x86.exe (PID: 7956)
- vcredist2005_x64.exe (PID: 4372)
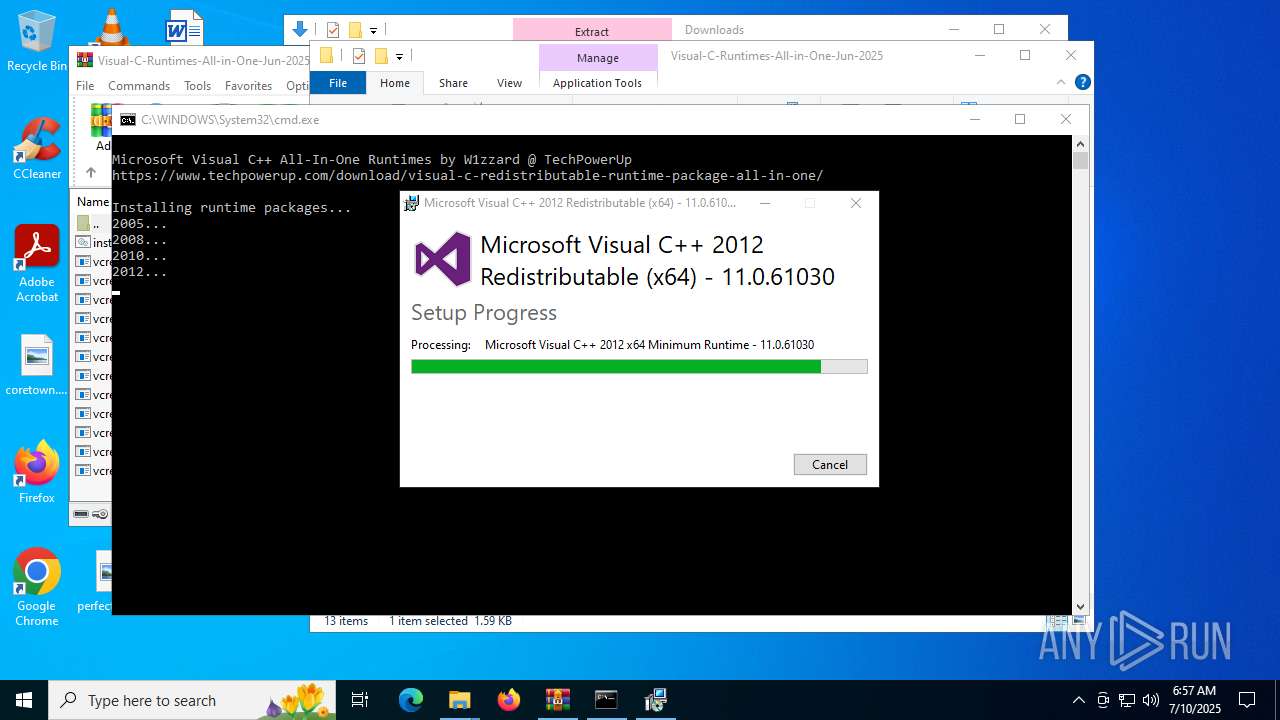
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x64.exe (PID: 4864)
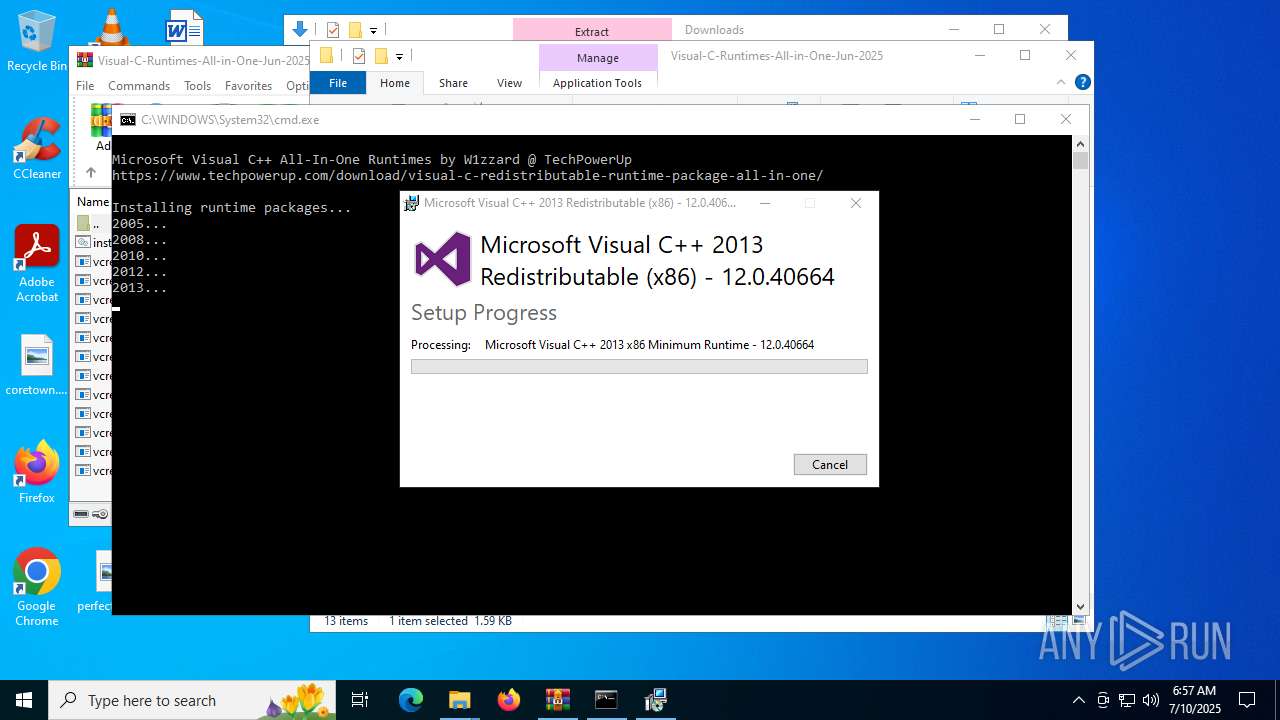
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 6036)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x64.exe (PID: 6124)
Executing a file with an untrusted certificate
- vcredist2005_x86.exe (PID: 7956)
- vcredist2005_x64.exe (PID: 4372)
- vcredist2008_x86.exe (PID: 4312)
- install.exe (PID: 7584)
- vcredist2008_x64.exe (PID: 2228)
- install.exe (PID: 8028)
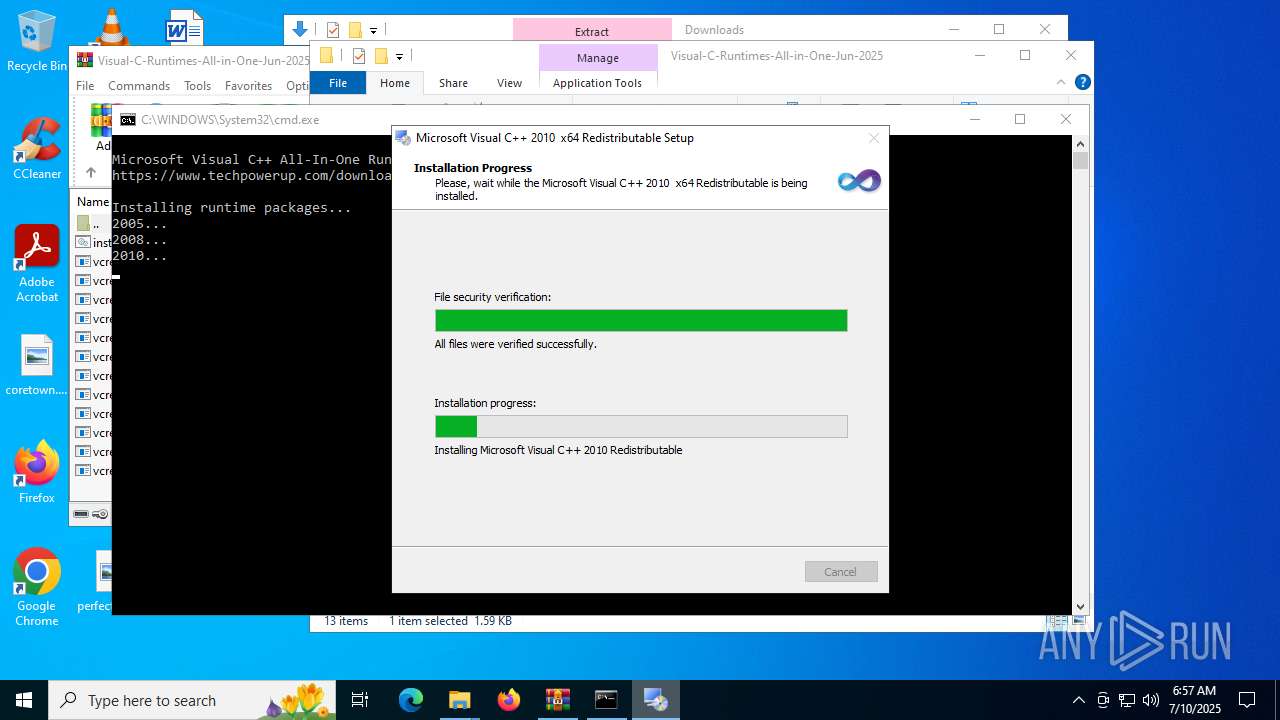
- vcredist2010_x86.exe (PID: 7216)
- Setup.exe (PID: 5616)
- vcredist2010_x64.exe (PID: 3900)
- Setup.exe (PID: 480)
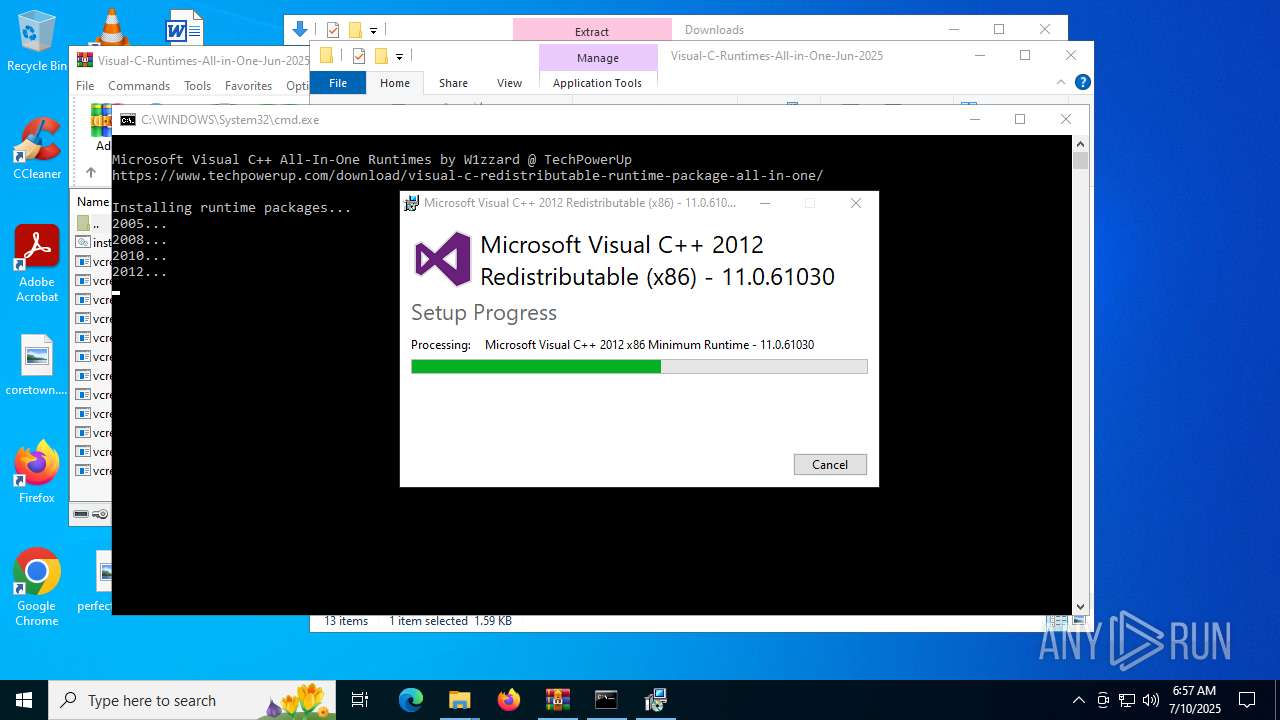
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x86.exe (PID: 6224)
- vcredist2012_x64.exe (PID: 6140)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x86.exe (PID: 4948)
- vcredist2013_x64.exe (PID: 6036)
- vcredist2013_x64.exe (PID: 2800)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3964)
- WinRAR.exe (PID: 2792)
- Setup.exe (PID: 5616)
- Setup.exe (PID: 480)
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 6036)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4644)
- VC_redist.x86.exe (PID: 7208)
- vcredist2015_2017_2019_2022_x64.exe (PID: 6212)
- VC_redist.x64.exe (PID: 2716)
Process drops legitimate windows executable
- WinRAR.exe (PID: 3964)
- WinRAR.exe (PID: 2792)
- msiexec.exe (PID: 1508)
- TiWorker.exe (PID: 3632)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- msiexec.exe (PID: 6360)
- vcredist2012_x86.exe (PID: 6224)
- vcredist2012_x86.exe (PID: 7836)
- msiexec.exe (PID: 3476)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2012_x64.exe (PID: 6140)
- vcredist2013_x86.exe (PID: 4948)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 2800)
- vcredist2013_x64.exe (PID: 6036)
- vcredist2015_2017_2019_2022_x86.exe (PID: 7156)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4644)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x86.exe (PID: 1028)
- vcredist2015_2017_2019_2022_x64.exe (PID: 6212)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5644)
- VC_redist.x64.exe (PID: 6124)
- VC_redist.x64.exe (PID: 1760)
Starts a Microsoft application from unusual location
- vcredist2005_x86.exe (PID: 7956)
- vcredist2005_x64.exe (PID: 4372)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x86.exe (PID: 6224)
- vcredist2012_x64.exe (PID: 6140)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x86.exe (PID: 4948)
- vcredist2013_x64.exe (PID: 6036)
- vcredist2013_x64.exe (PID: 2800)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4644)
- vcredist2015_2017_2019_2022_x86.exe (PID: 7156)
- VC_redist.x86.exe (PID: 1356)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5644)
- vcredist2015_2017_2019_2022_x64.exe (PID: 6212)
- VC_redist.x64.exe (PID: 6124)
Executable content was dropped or overwritten
- vcredist2005_x86.exe (PID: 7956)
- TiWorker.exe (PID: 3632)
- vcredist2005_x64.exe (PID: 4372)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- vcredist2012_x86.exe (PID: 6224)
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x64.exe (PID: 6140)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 4948)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 2800)
- vcredist2013_x64.exe (PID: 6036)
- vcredist2015_2017_2019_2022_x86.exe (PID: 7156)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4644)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x86.exe (PID: 1028)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5644)
- VC_redist.x86.exe (PID: 7208)
- vcredist2015_2017_2019_2022_x64.exe (PID: 6212)
- VC_redist.x64.exe (PID: 6124)
- VC_redist.x64.exe (PID: 2716)
- VC_redist.x64.exe (PID: 1760)
Executes as Windows Service
- VSSVC.exe (PID: 5708)
The process drops C-runtime libraries
- msiexec.exe (PID: 1508)
- TiWorker.exe (PID: 3632)
- vcredist2010_x86.exe (PID: 7216)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1508)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
Creates file in the systems drive root
- vcredist2008_x86.exe (PID: 4312)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
Application launched itself
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 6036)
- VC_redist.x86.exe (PID: 3956)
- VC_redist.x86.exe (PID: 7208)
- VC_redist.x64.exe (PID: 5480)
- VC_redist.x64.exe (PID: 2716)
Searches for installed software
- vcredist2012_x86.exe (PID: 6224)
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2012_x64.exe (PID: 6140)
- vcredist2013_x86.exe (PID: 4948)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 2800)
- vcredist2013_x64.exe (PID: 6036)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4644)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x86.exe (PID: 1028)
- vcredist2015_2017_2019_2022_x64.exe (PID: 6212)
- VC_redist.x86.exe (PID: 7208)
- VC_redist.x64.exe (PID: 6124)
- VC_redist.x64.exe (PID: 1760)
- VC_redist.x64.exe (PID: 2716)
Creates a software uninstall entry
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 6036)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x64.exe (PID: 6124)
Starts itself from another location
- vcredist2015_2017_2019_2022_x86.exe (PID: 4644)
- vcredist2015_2017_2019_2022_x64.exe (PID: 6212)
The process checks if it is being run in the virtual environment
- msiexec.exe (PID: 3476)
INFO
Reads Environment values
- identity_helper.exe (PID: 7776)
- identity_helper.exe (PID: 7184)
Checks supported languages
- identity_helper.exe (PID: 7776)
- identity_helper.exe (PID: 7184)
- msiexec.exe (PID: 1508)
- vcredist2005_x86.exe (PID: 7956)
- msiexec.exe (PID: 2492)
- vcredist2005_x64.exe (PID: 4372)
- msiexec.exe (PID: 3400)
- vcredist2008_x86.exe (PID: 4312)
- install.exe (PID: 7584)
- vcredist2008_x64.exe (PID: 2228)
- install.exe (PID: 8028)
- vcredist2010_x86.exe (PID: 7216)
- Setup.exe (PID: 5616)
- vcredist2010_x64.exe (PID: 3900)
- Setup.exe (PID: 480)
- msiexec.exe (PID: 6360)
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x86.exe (PID: 6224)
- msiexec.exe (PID: 3476)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2012_x64.exe (PID: 6140)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x86.exe (PID: 4948)
- vcredist2013_x64.exe (PID: 6036)
- vcredist2013_x64.exe (PID: 2800)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4644)
- vcredist2015_2017_2019_2022_x86.exe (PID: 7156)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x86.exe (PID: 3956)
- VC_redist.x86.exe (PID: 7208)
- VC_redist.x86.exe (PID: 1028)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5644)
- vcredist2015_2017_2019_2022_x64.exe (PID: 6212)
- VC_redist.x64.exe (PID: 6124)
- VC_redist.x64.exe (PID: 2716)
- VC_redist.x64.exe (PID: 5480)
- VC_redist.x64.exe (PID: 1760)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6528)
Application launched itself
- msedge.exe (PID: 6528)
- msedge.exe (PID: 4444)
Executable content was dropped or overwritten
- msedge.exe (PID: 6528)
- msedge.exe (PID: 6748)
- WinRAR.exe (PID: 3964)
- WinRAR.exe (PID: 2792)
- msiexec.exe (PID: 1508)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
Reads the computer name
- identity_helper.exe (PID: 7776)
- identity_helper.exe (PID: 7184)
- vcredist2005_x86.exe (PID: 7956)
- msiexec.exe (PID: 1508)
- msiexec.exe (PID: 2492)
- vcredist2005_x64.exe (PID: 4372)
- vcredist2008_x86.exe (PID: 4312)
- msiexec.exe (PID: 3400)
- install.exe (PID: 7584)
- vcredist2008_x64.exe (PID: 2228)
- install.exe (PID: 8028)
- vcredist2010_x86.exe (PID: 7216)
- Setup.exe (PID: 5616)
- vcredist2010_x64.exe (PID: 3900)
- Setup.exe (PID: 480)
- msiexec.exe (PID: 6360)
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x86.exe (PID: 6224)
- msiexec.exe (PID: 3476)
- vcredist2012_x64.exe (PID: 6140)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 4948)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 2800)
- vcredist2013_x64.exe (PID: 6036)
- vcredist2015_2017_2019_2022_x86.exe (PID: 7156)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4644)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x86.exe (PID: 1028)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5644)
- VC_redist.x86.exe (PID: 7208)
- VC_redist.x64.exe (PID: 6124)
- vcredist2015_2017_2019_2022_x64.exe (PID: 6212)
- VC_redist.x64.exe (PID: 2716)
- VC_redist.x64.exe (PID: 1760)
The sample compiled with english language support
- WinRAR.exe (PID: 3964)
- WinRAR.exe (PID: 2792)
- msiexec.exe (PID: 1508)
- TiWorker.exe (PID: 3632)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- msiexec.exe (PID: 6360)
- vcredist2012_x86.exe (PID: 6224)
- vcredist2012_x86.exe (PID: 7836)
- msiexec.exe (PID: 3476)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2012_x64.exe (PID: 6140)
- vcredist2013_x86.exe (PID: 4948)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 2800)
- vcredist2013_x64.exe (PID: 6036)
- vcredist2015_2017_2019_2022_x86.exe (PID: 7156)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4644)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x86.exe (PID: 1028)
- VC_redist.x86.exe (PID: 7208)
- vcredist2015_2017_2019_2022_x64.exe (PID: 6212)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5644)
- VC_redist.x64.exe (PID: 6124)
- VC_redist.x64.exe (PID: 2716)
- VC_redist.x64.exe (PID: 1760)
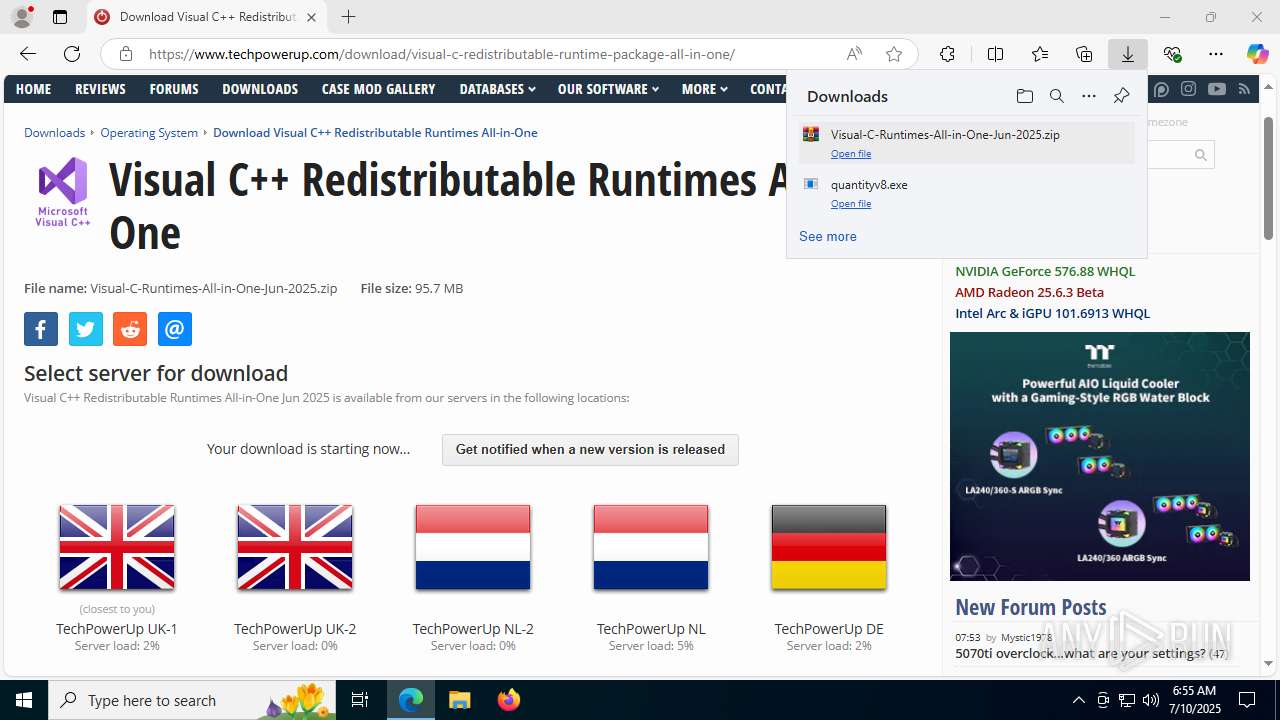
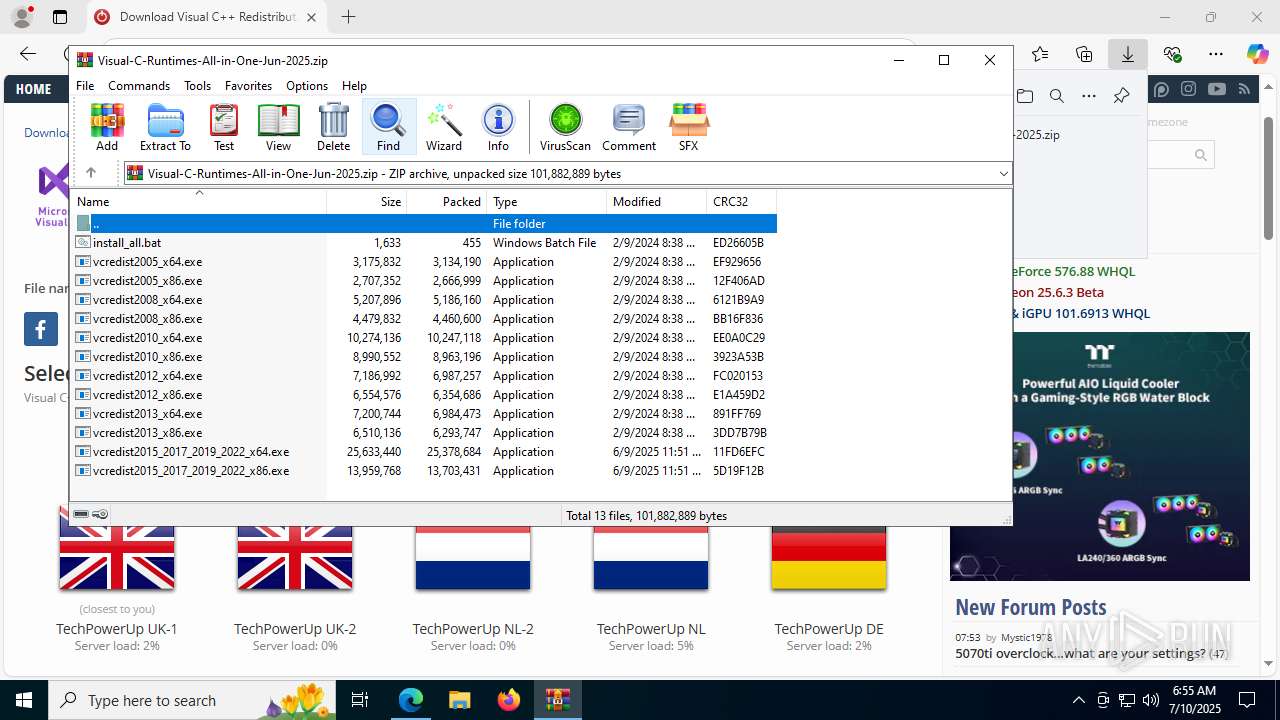
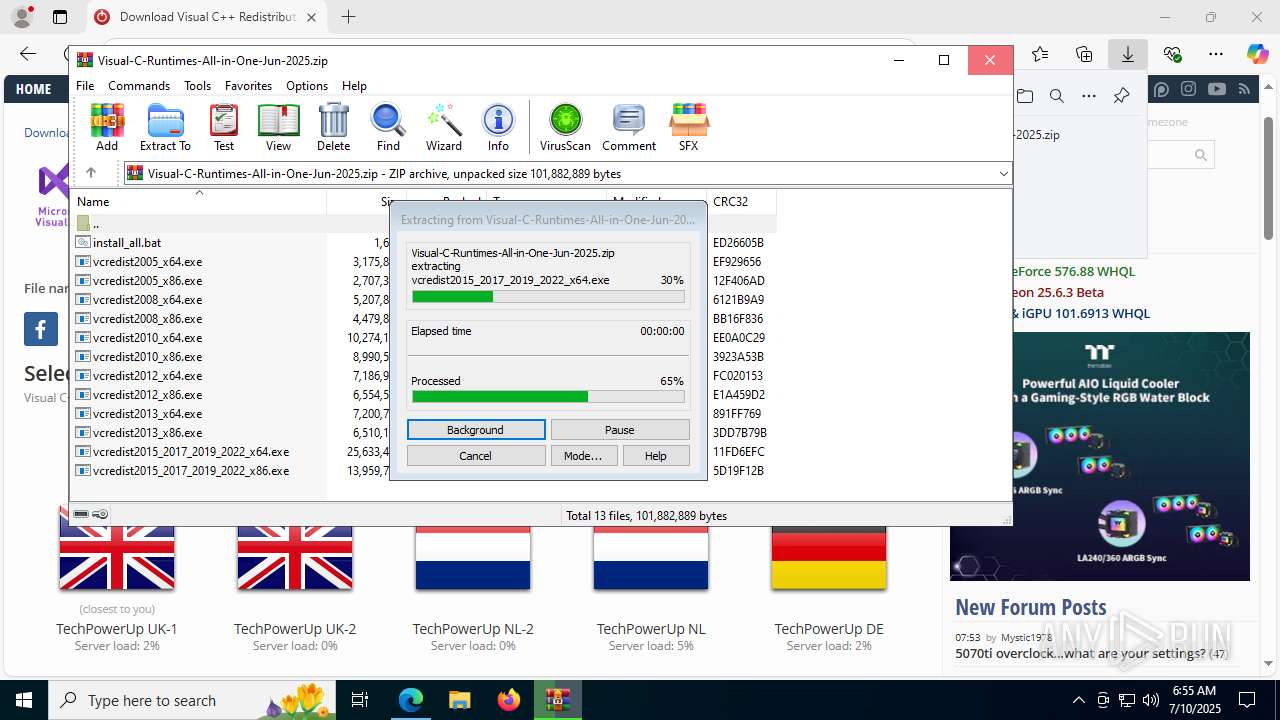
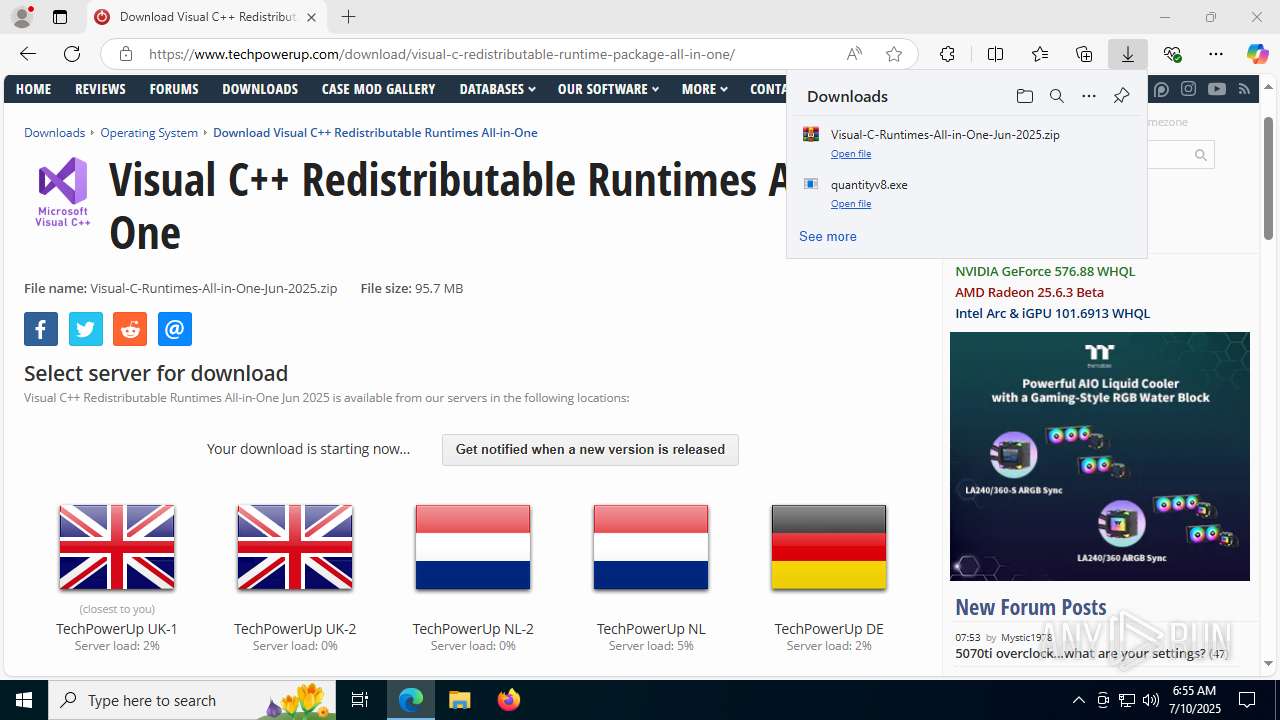
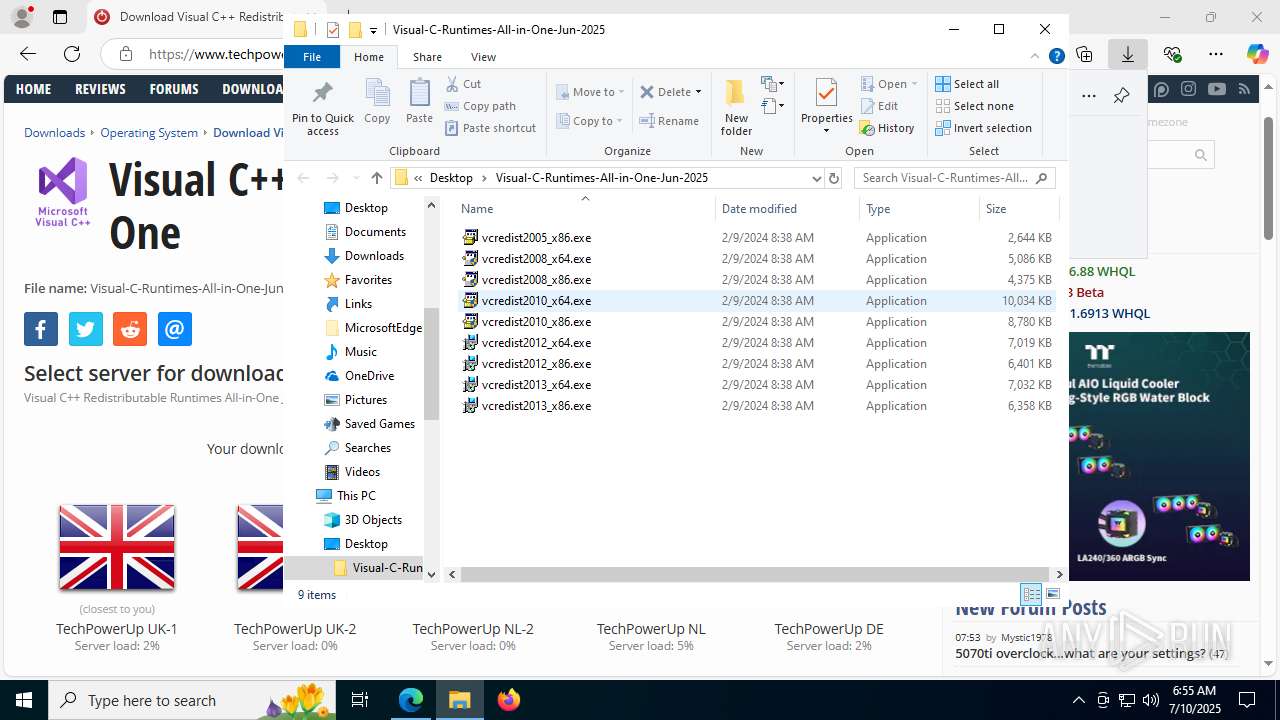
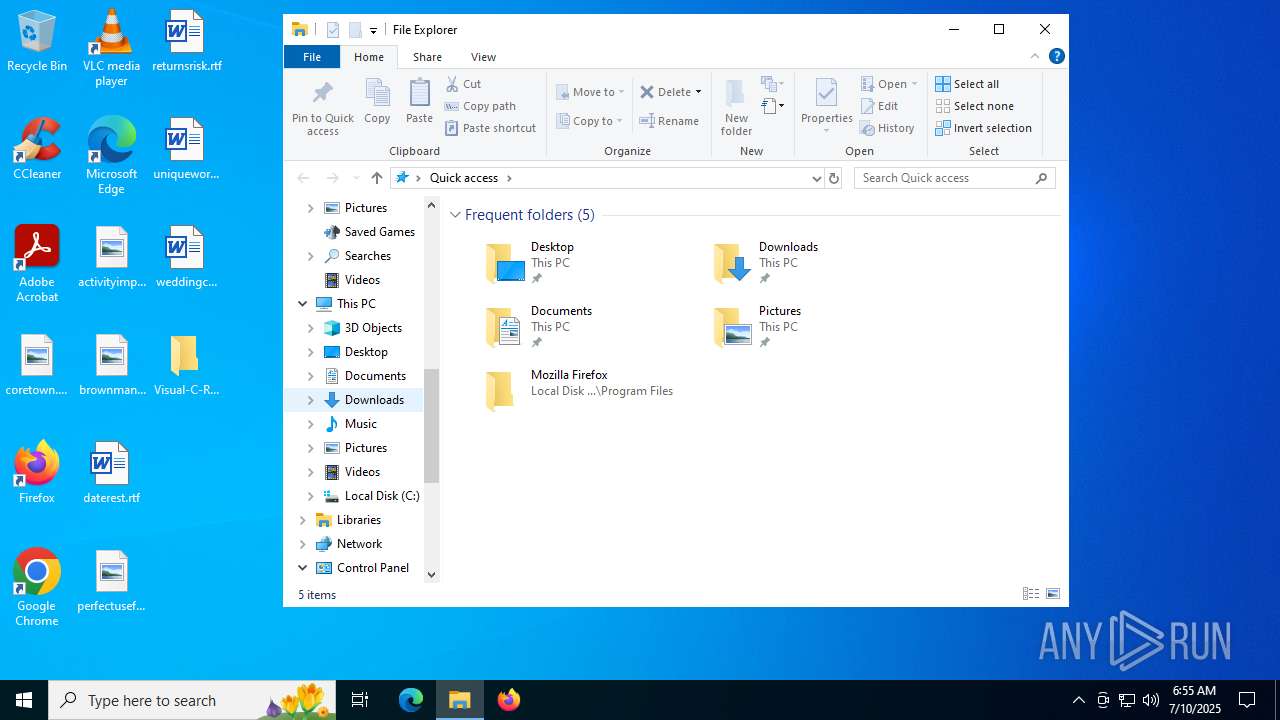
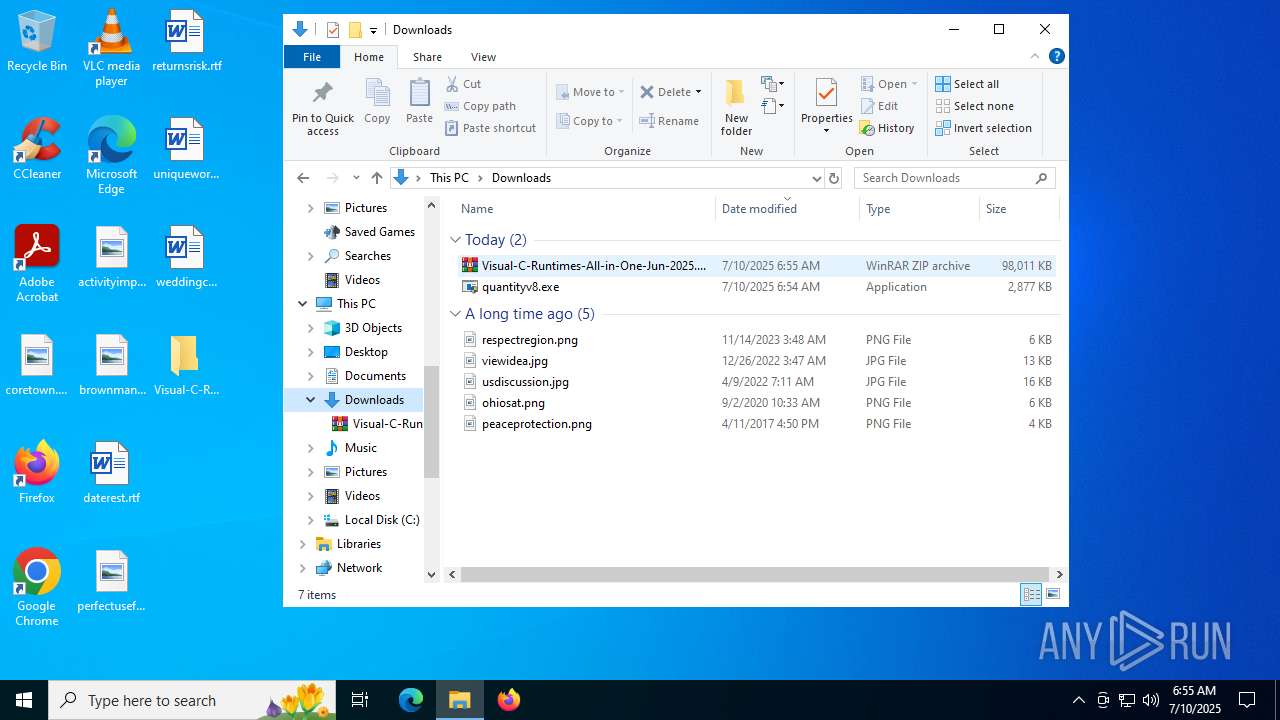
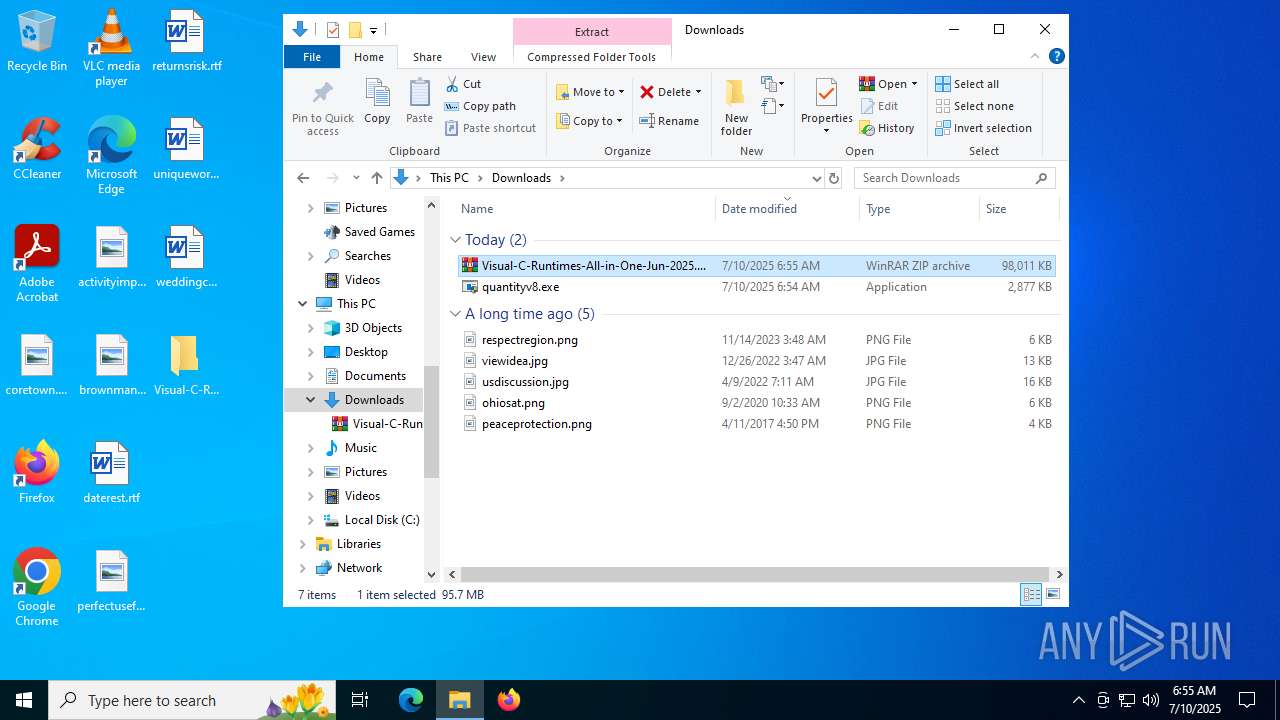
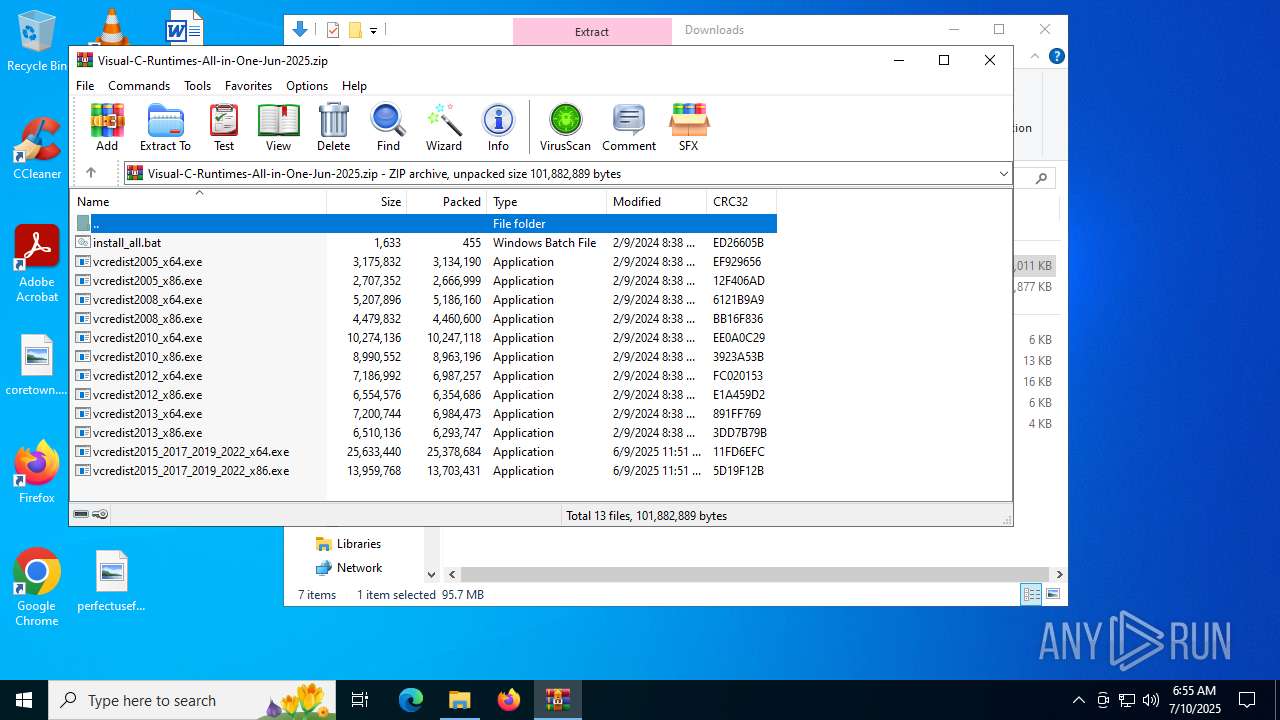
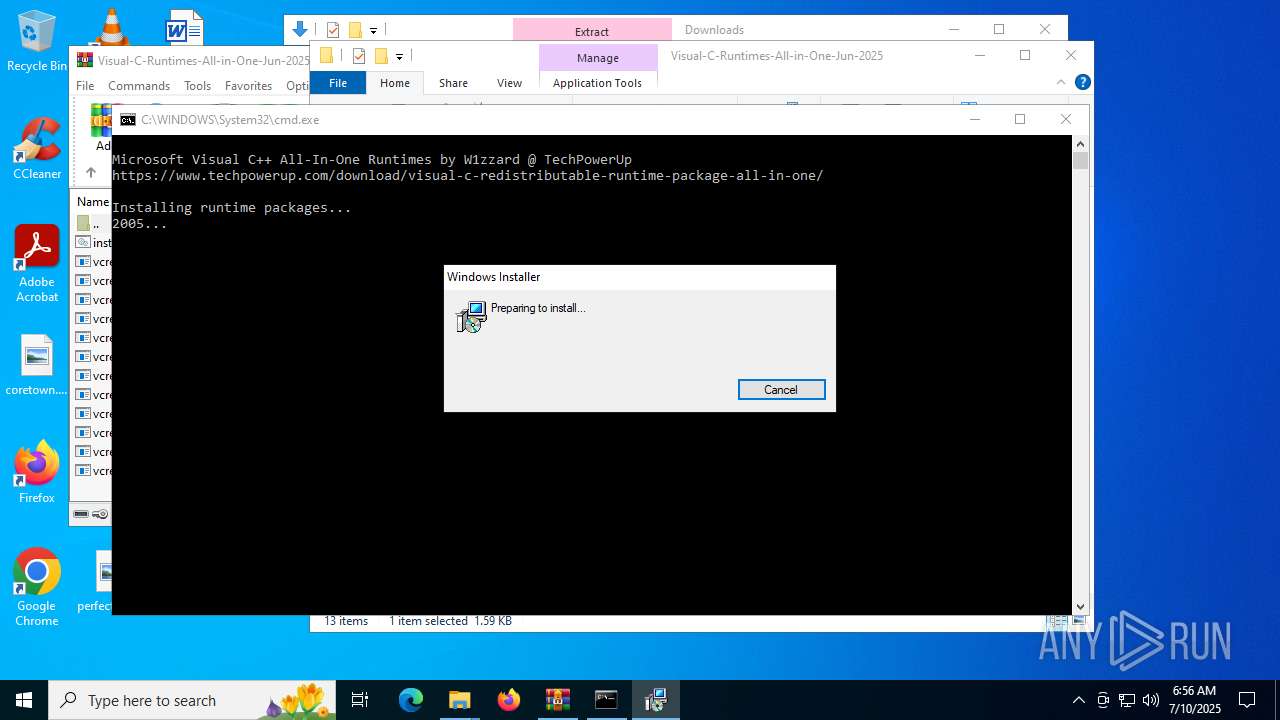
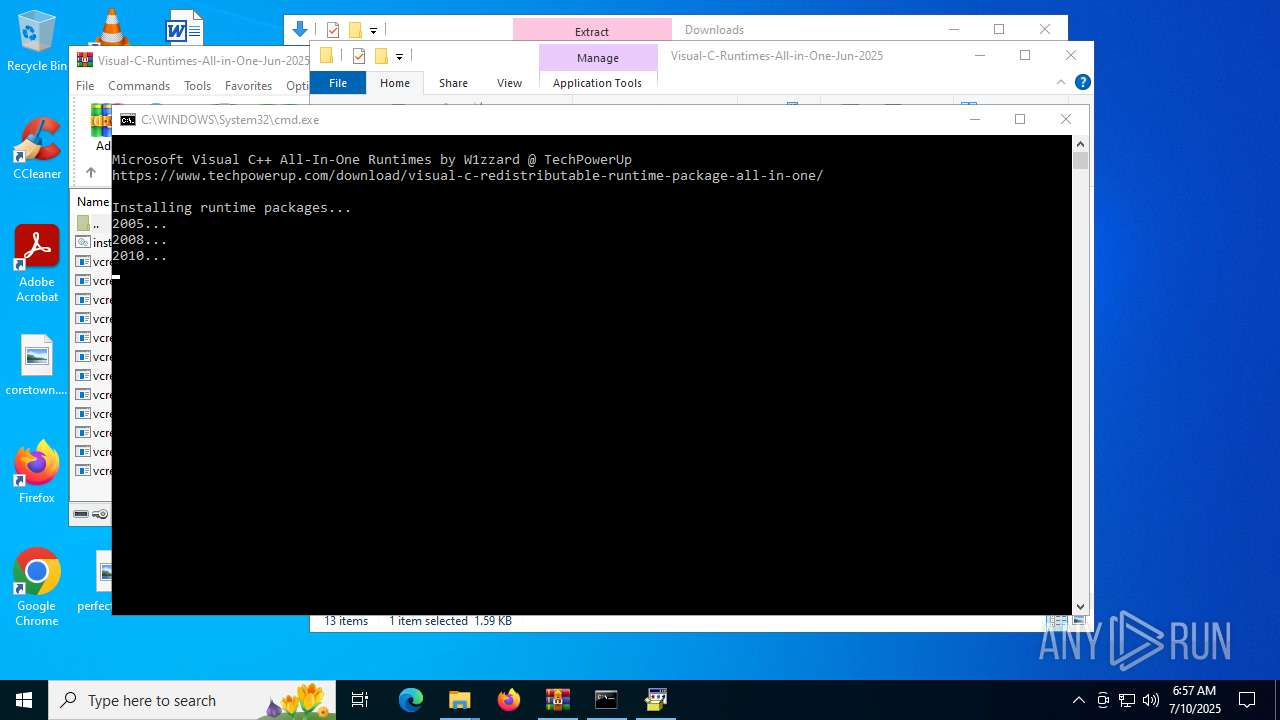
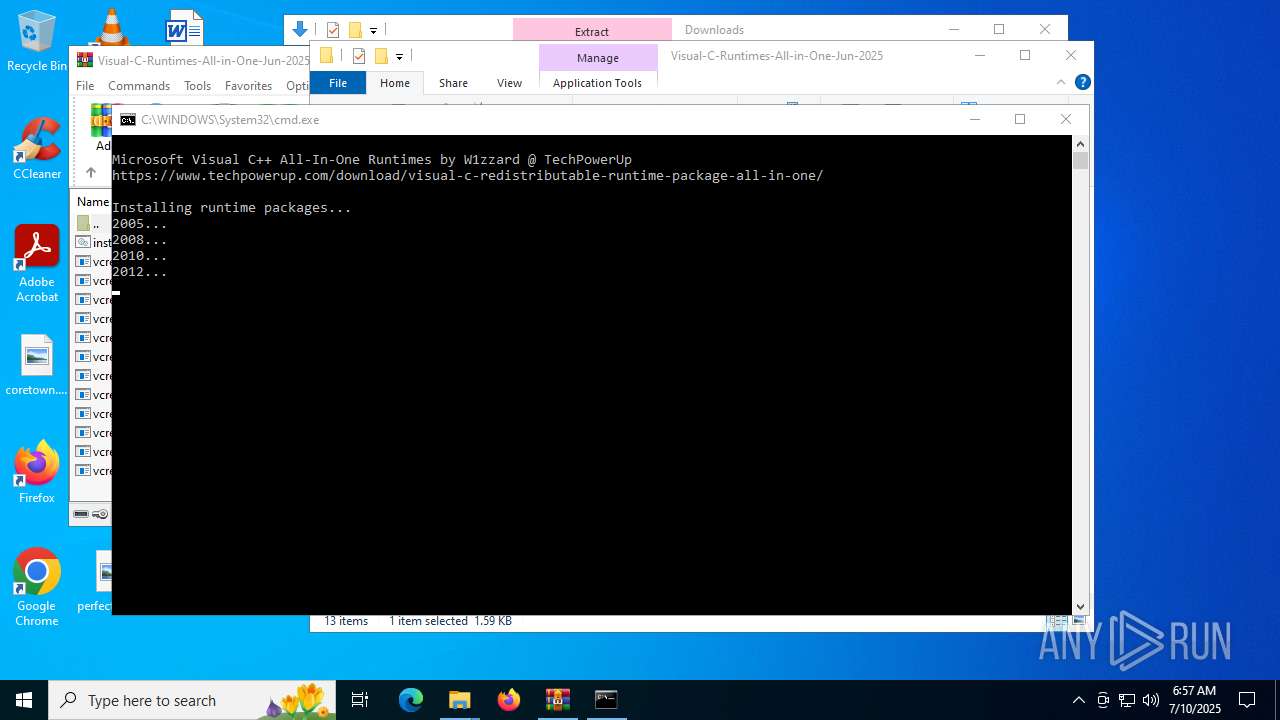
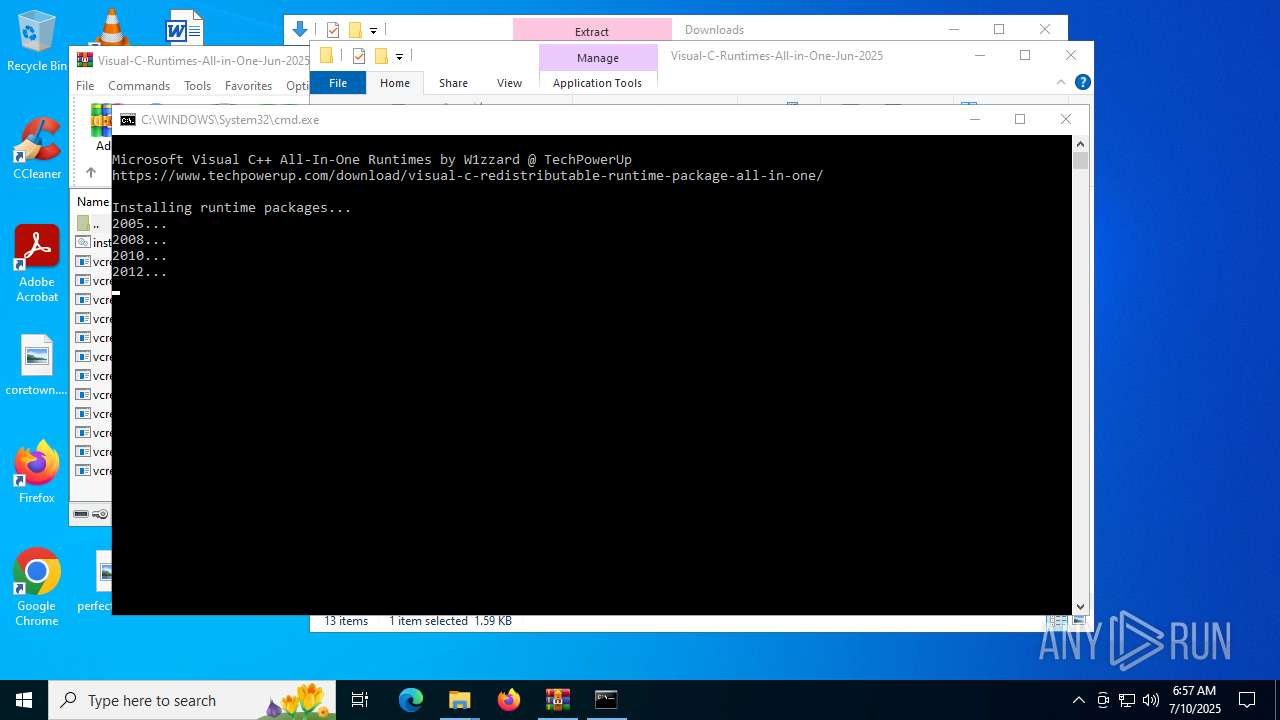
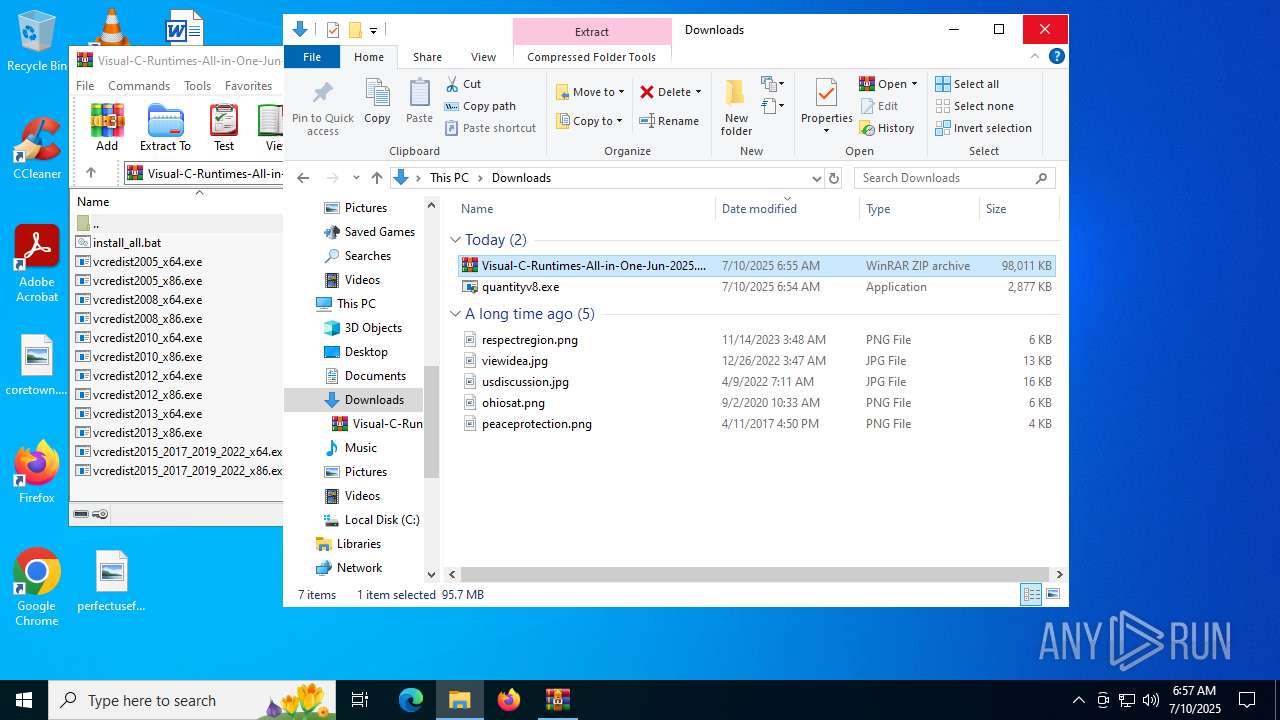
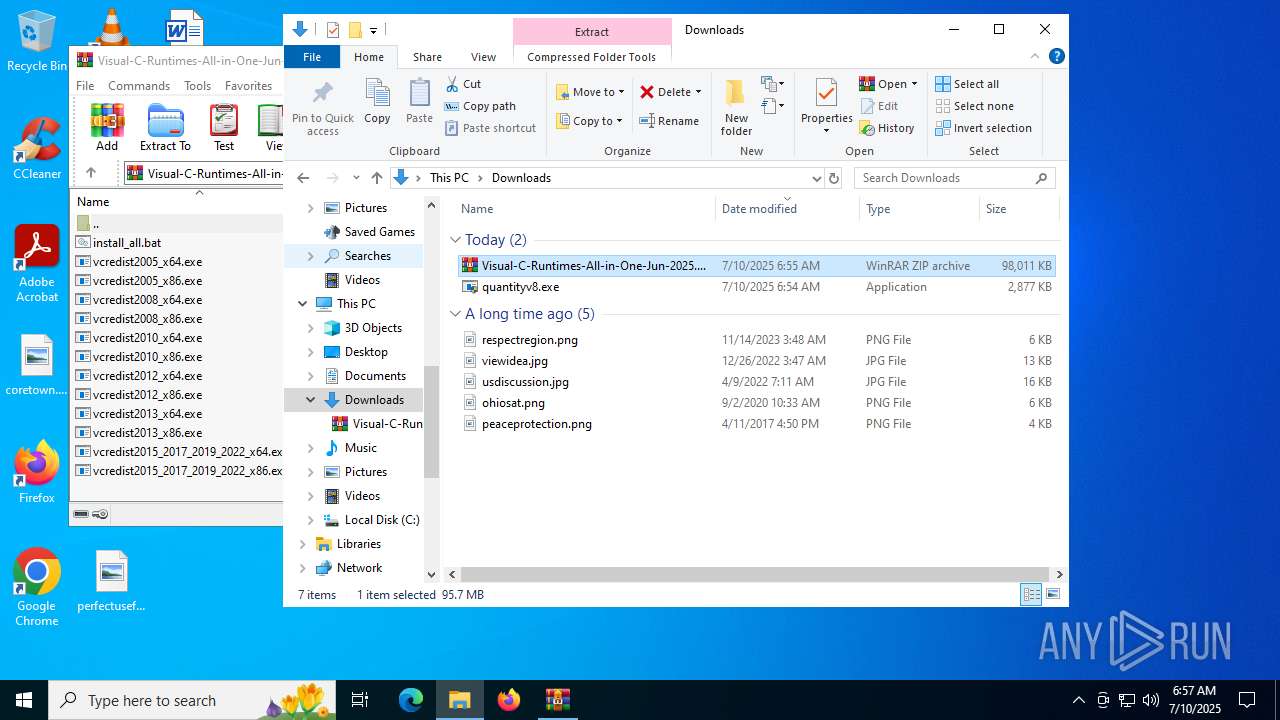
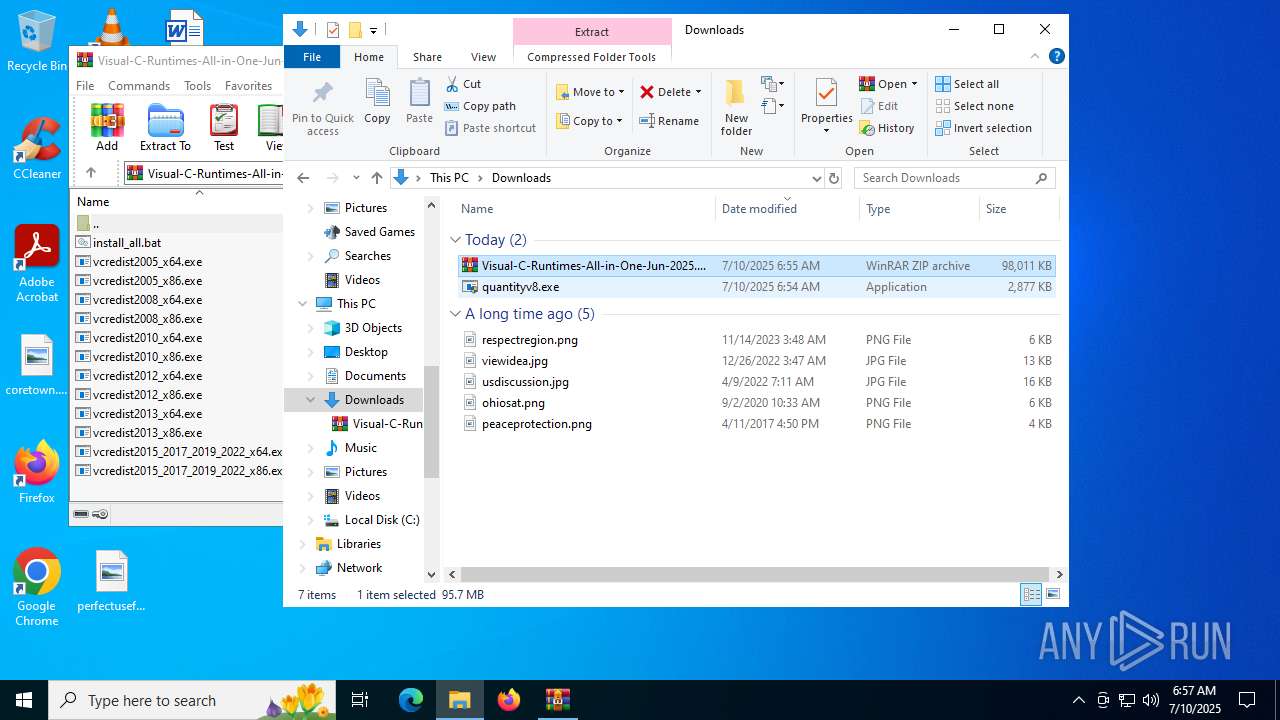
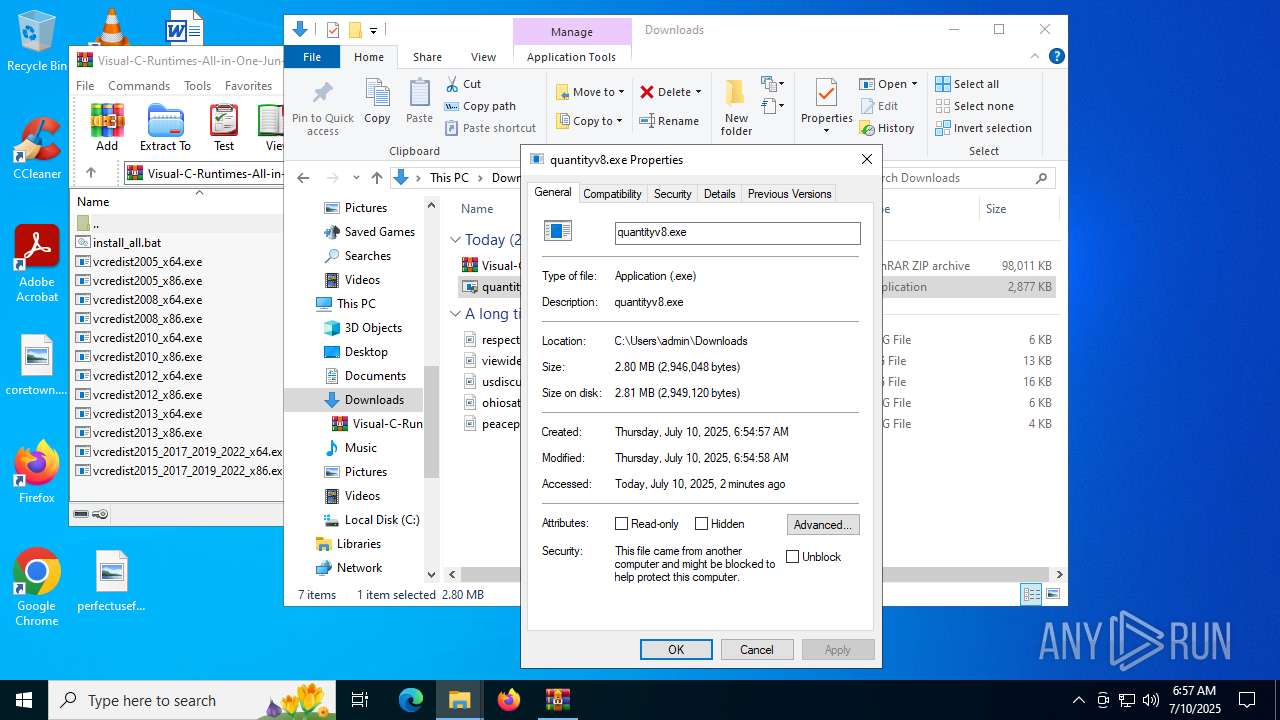
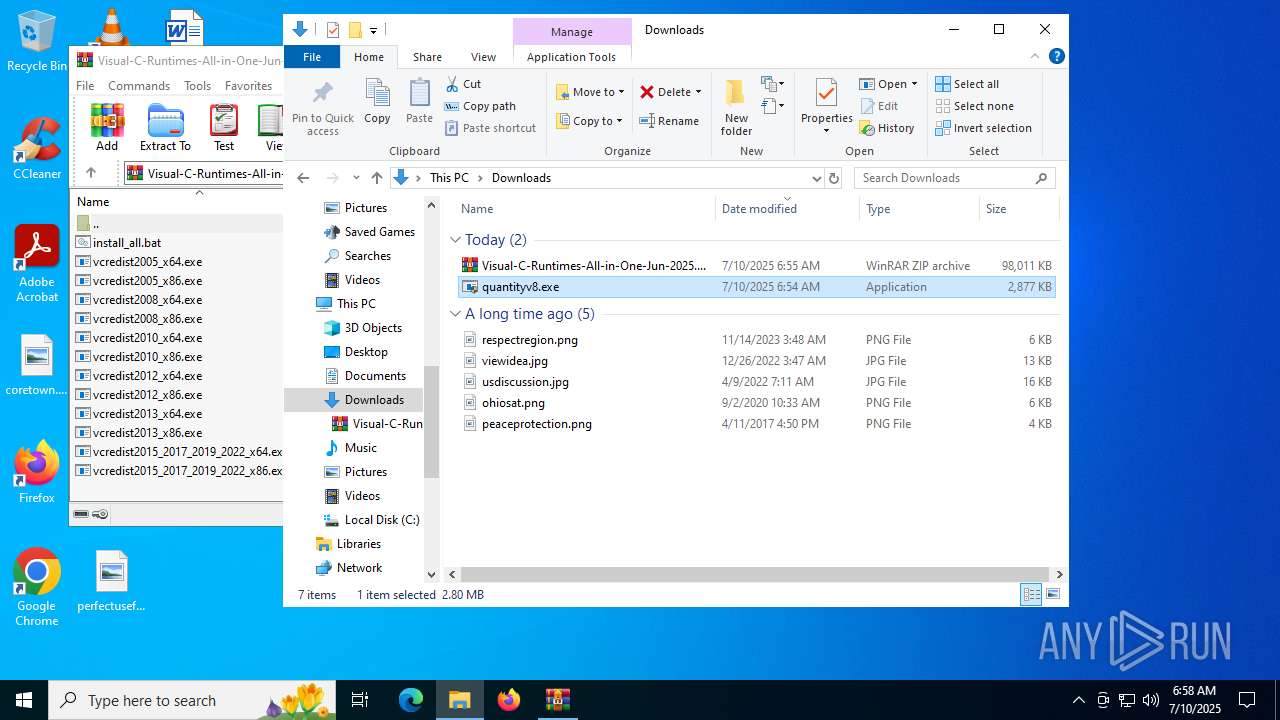
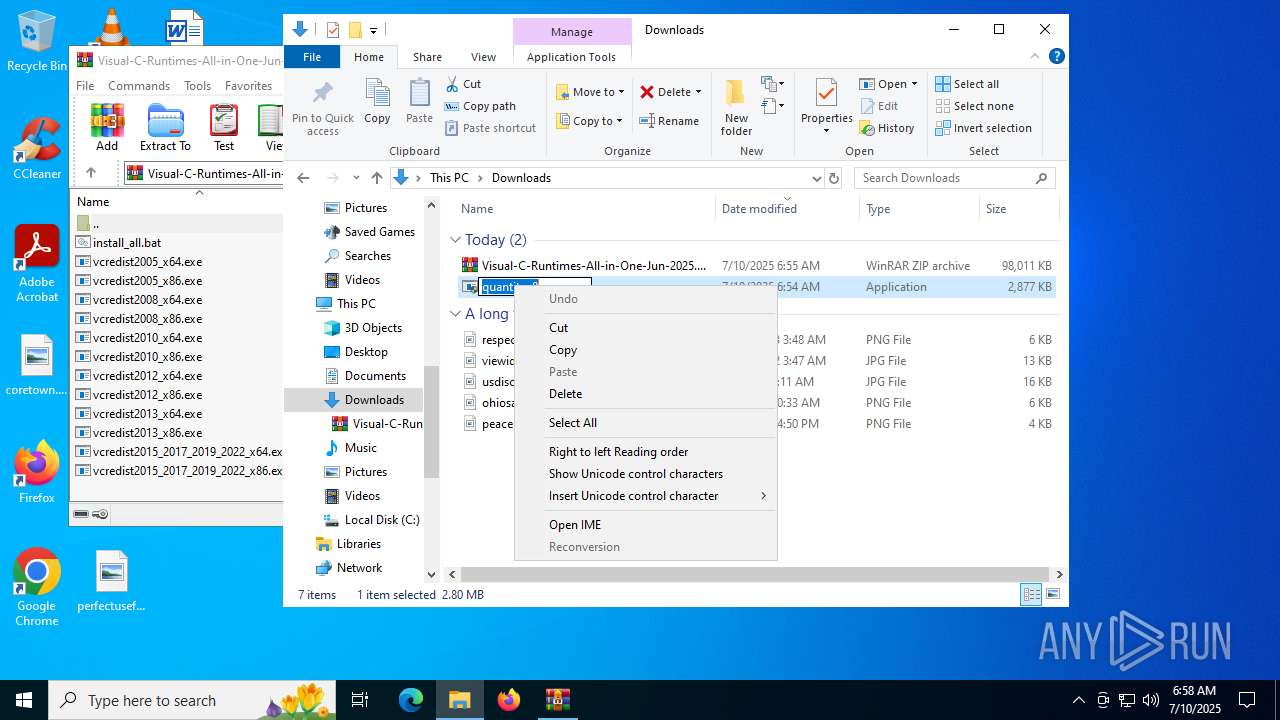
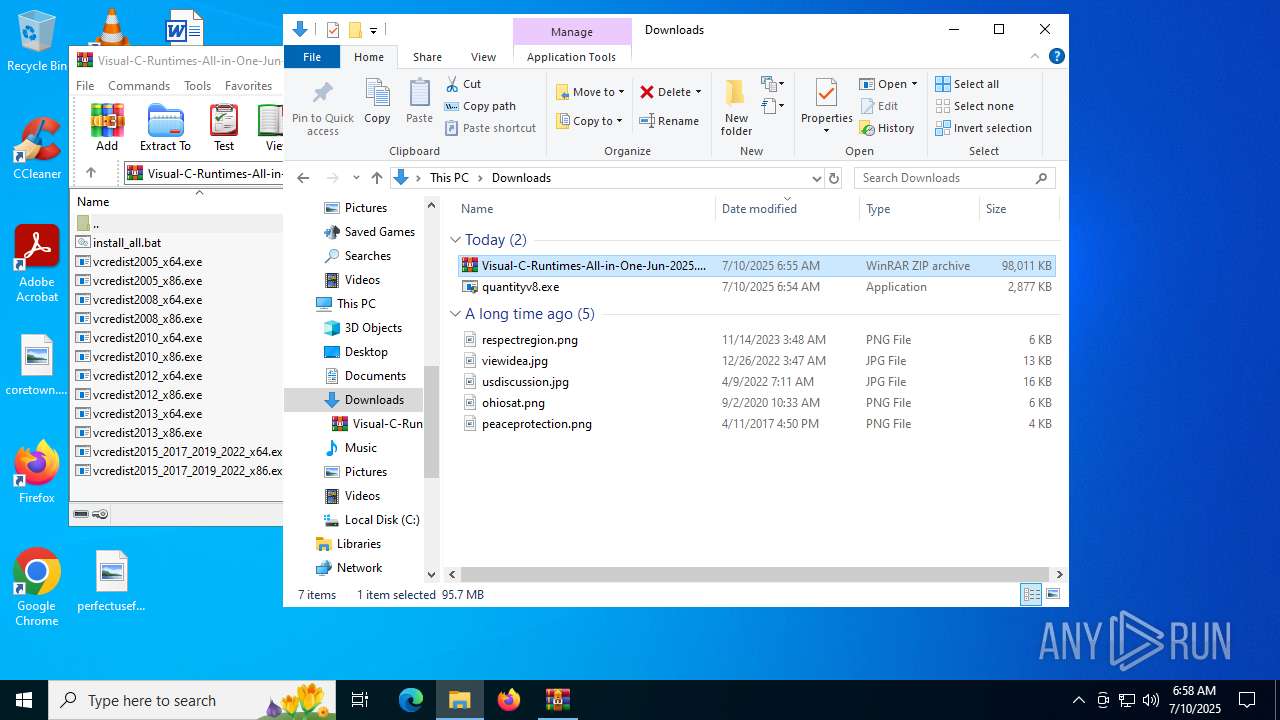
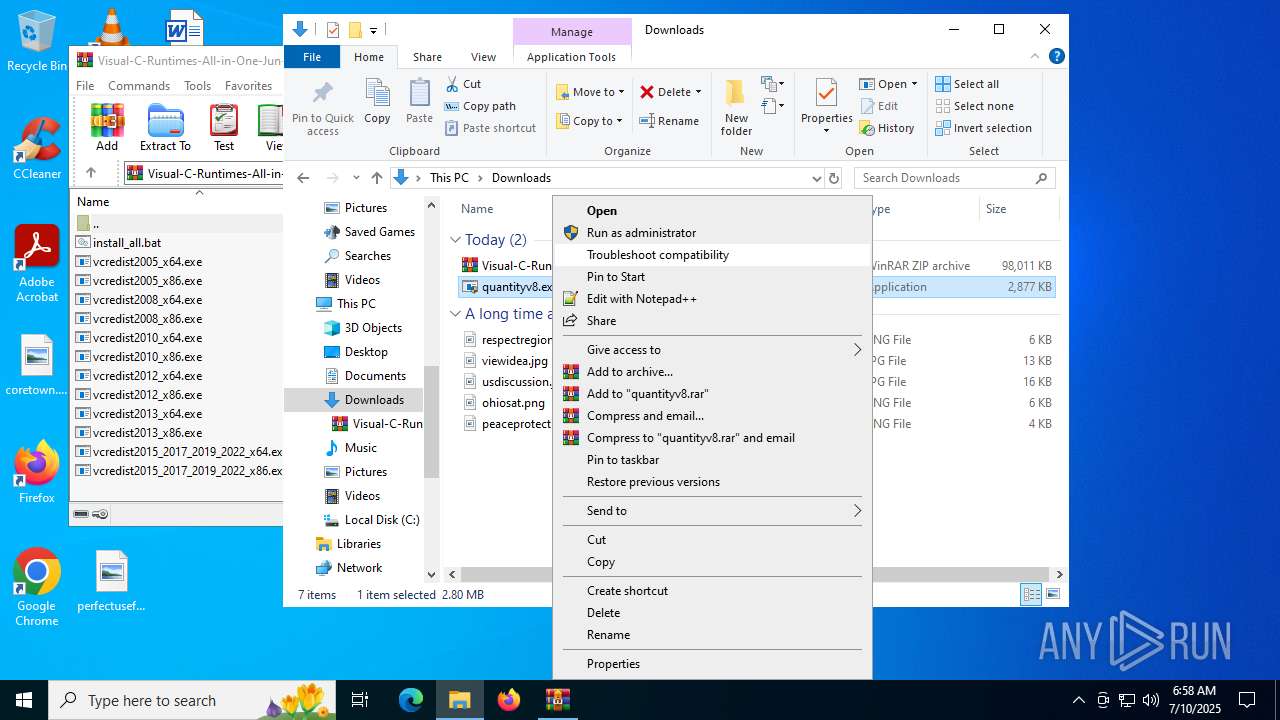
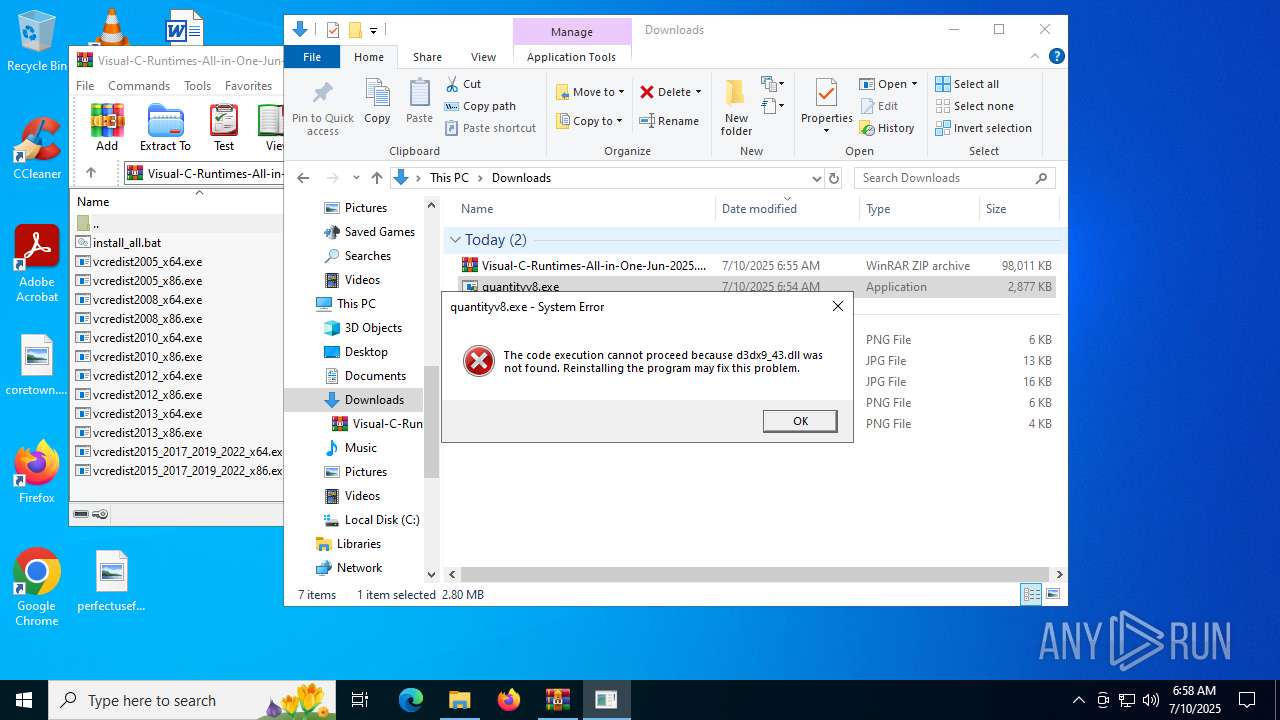
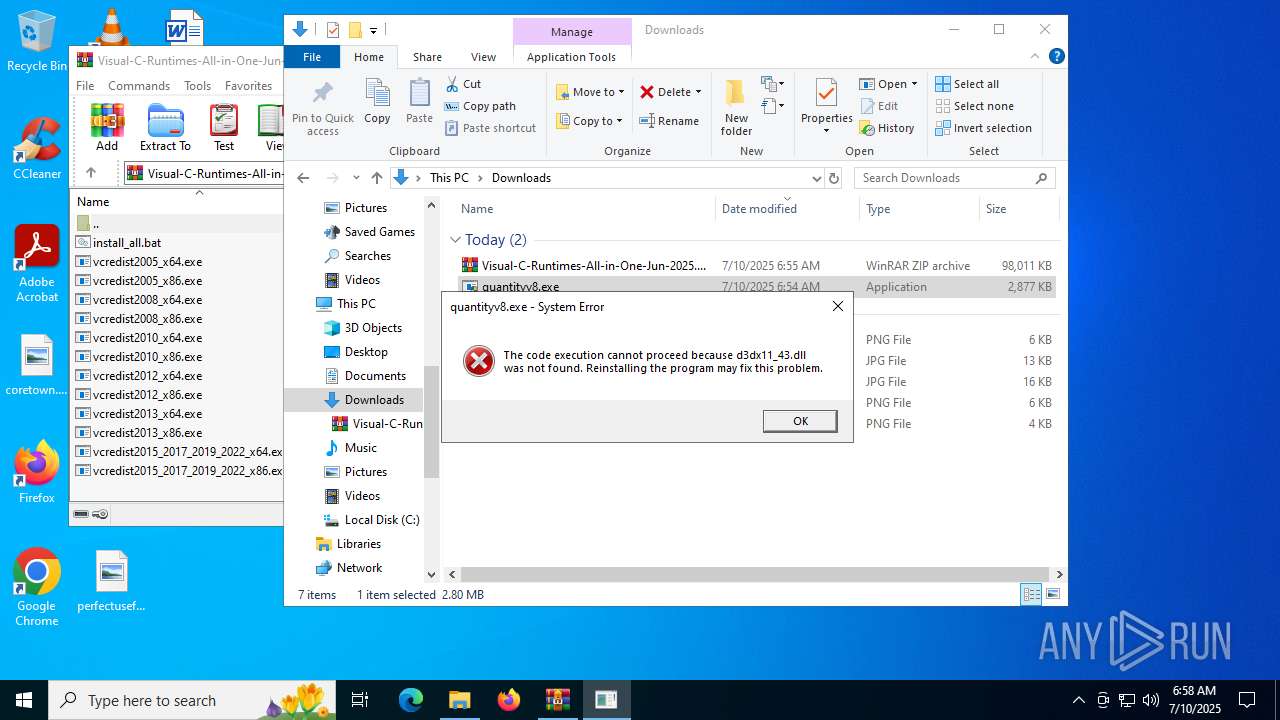
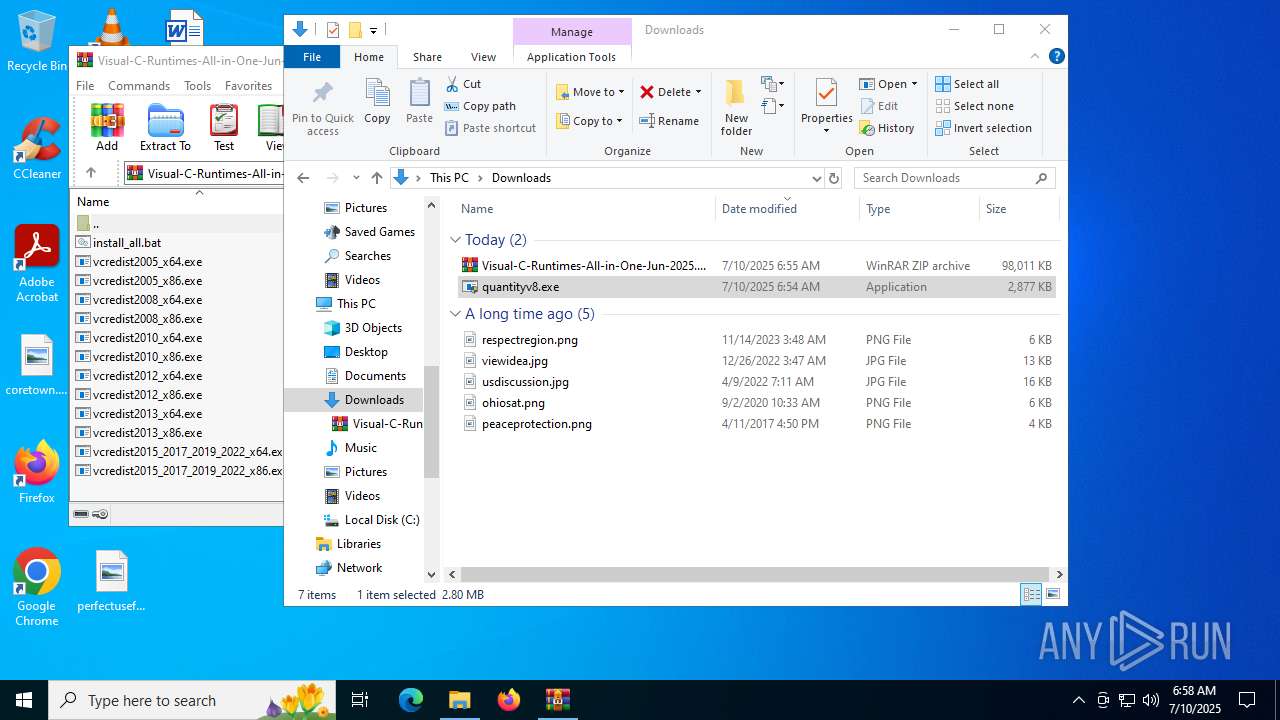
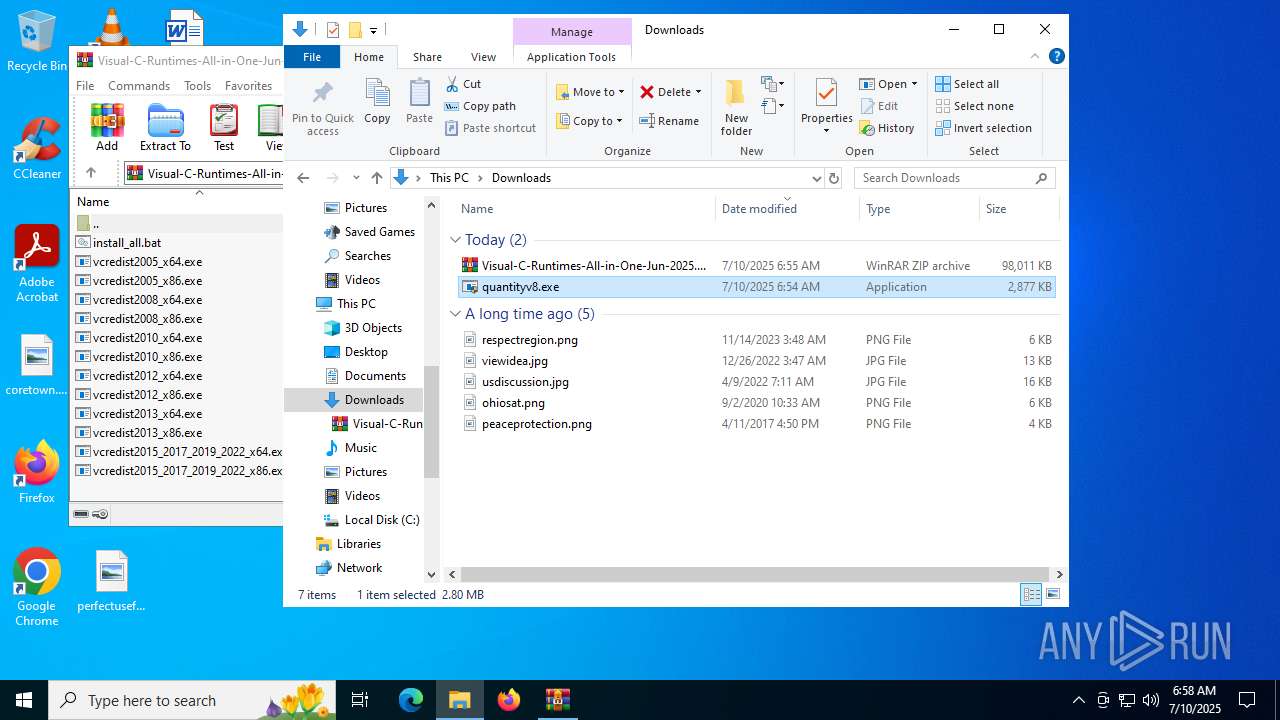
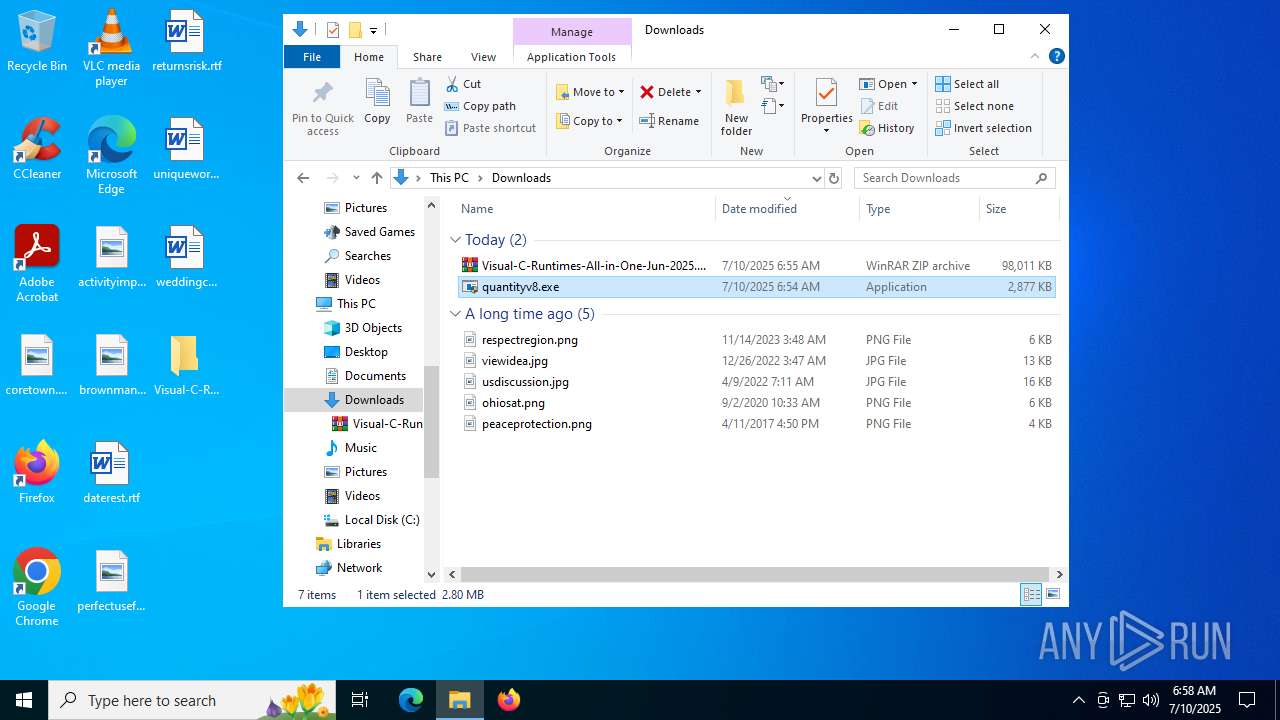
Manual execution by a user
- WinRAR.exe (PID: 2792)
- cmd.exe (PID: 7872)
- quantityv8.exe (PID: 6776)
Creates files or folders in the user directory
- msiexec.exe (PID: 7736)
- vcredist2012_x86.exe (PID: 7836)
Launching a file from a Registry key
- vcredist2005_x86.exe (PID: 7956)
- vcredist2005_x64.exe (PID: 4372)
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 6036)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x64.exe (PID: 6124)
Reads the software policy settings
- msiexec.exe (PID: 7736)
- msiexec.exe (PID: 1508)
- slui.exe (PID: 8176)
- msiexec.exe (PID: 6652)
- Setup.exe (PID: 5616)
- msiexec.exe (PID: 6360)
- Setup.exe (PID: 480)
- vcredist2012_x86.exe (PID: 7836)
- msiexec.exe (PID: 3476)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 6036)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7736)
- msiexec.exe (PID: 6652)
Checks proxy server information
- msiexec.exe (PID: 7736)
- slui.exe (PID: 8176)
- vcredist2012_x86.exe (PID: 7836)
- vcredist2013_x86.exe (PID: 1660)
Manages system restore points
- SrTasks.exe (PID: 4864)
- SrTasks.exe (PID: 6720)
- SrTasks.exe (PID: 7720)
- SrTasks.exe (PID: 7504)
Create files in a temporary directory
- vcredist2005_x86.exe (PID: 7956)
- vcredist2005_x64.exe (PID: 4372)
- install.exe (PID: 7584)
- install.exe (PID: 8028)
- Setup.exe (PID: 5616)
- Setup.exe (PID: 480)
- vcredist2012_x86.exe (PID: 6224)
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x64.exe (PID: 6140)
- vcredist2013_x86.exe (PID: 4948)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 2800)
- vcredist2013_x64.exe (PID: 6036)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4644)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x86.exe (PID: 7208)
- vcredist2015_2017_2019_2022_x64.exe (PID: 6212)
- VC_redist.x64.exe (PID: 6124)
- VC_redist.x64.exe (PID: 2716)
The sample compiled with spanish language support
- msiexec.exe (PID: 1508)
- TiWorker.exe (PID: 3632)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
The sample compiled with japanese language support
- msiexec.exe (PID: 1508)
- TiWorker.exe (PID: 3632)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
The sample compiled with chinese language support
- msiexec.exe (PID: 1508)
- TiWorker.exe (PID: 3632)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
The sample compiled with Italian language support
- msiexec.exe (PID: 1508)
- TiWorker.exe (PID: 3632)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
The sample compiled with german language support
- msiexec.exe (PID: 1508)
- TiWorker.exe (PID: 3632)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
The sample compiled with korean language support
- msiexec.exe (PID: 1508)
- TiWorker.exe (PID: 3632)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
Reads the machine GUID from the registry
- msiexec.exe (PID: 1508)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- Setup.exe (PID: 5616)
- vcredist2010_x64.exe (PID: 3900)
- msiexec.exe (PID: 6360)
- Setup.exe (PID: 480)
- vcredist2012_x86.exe (PID: 7836)
- msiexec.exe (PID: 3476)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 6036)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x64.exe (PID: 6124)
The sample compiled with french language support
- msiexec.exe (PID: 1508)
- TiWorker.exe (PID: 3632)
- vcredist2008_x86.exe (PID: 4312)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
Creates a software uninstall entry
- msiexec.exe (PID: 1508)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
The sample compiled with russian language support
- vcredist2008_x86.exe (PID: 4312)
- TiWorker.exe (PID: 3632)
- msiexec.exe (PID: 1508)
- vcredist2008_x64.exe (PID: 2228)
- vcredist2010_x86.exe (PID: 7216)
- vcredist2010_x64.exe (PID: 3900)
- msiexec.exe (PID: 6360)
- msiexec.exe (PID: 3476)
Reads CPU info
- Setup.exe (PID: 5616)
- Setup.exe (PID: 480)
Creates files in the program directory
- vcredist2012_x86.exe (PID: 7836)
- vcredist2012_x64.exe (PID: 4864)
- vcredist2013_x86.exe (PID: 1660)
- vcredist2013_x64.exe (PID: 6036)
- VC_redist.x86.exe (PID: 1356)
- VC_redist.x64.exe (PID: 6124)
Process checks computer location settings
- vcredist2015_2017_2019_2022_x86.exe (PID: 4644)
- VC_redist.x86.exe (PID: 7208)
- vcredist2015_2017_2019_2022_x64.exe (PID: 6212)
- VC_redist.x64.exe (PID: 2716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
265
Monitored processes
111
Malicious processes
32
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | c:\53979e70226ca918ba2b2adc\Setup.exe /passive /norestart | C:\53979e70226ca918ba2b2adc\Setup.exe | vcredist2010_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 10.0.40219.325 built by: SP1LDR Modules
| |||||||||||||||
| 1028 | "C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{9CD515A2-79BA-4DF0-B79A-8999ACFFDB4B} {13EC8509-B35A-4CE3-880D-7CFF3FB8D114} 7208 | C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe | — | VC_redist.x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 1136 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7192,i,8639135556003639854,15897683521427871999,262144 --variations-seed-version --mojo-platform-channel-handle=7368 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --always-read-main-dll --field-trial-handle=7464,i,8639135556003639854,15897683521427871999,262144 --variations-seed-version --mojo-platform-channel-handle=8060 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
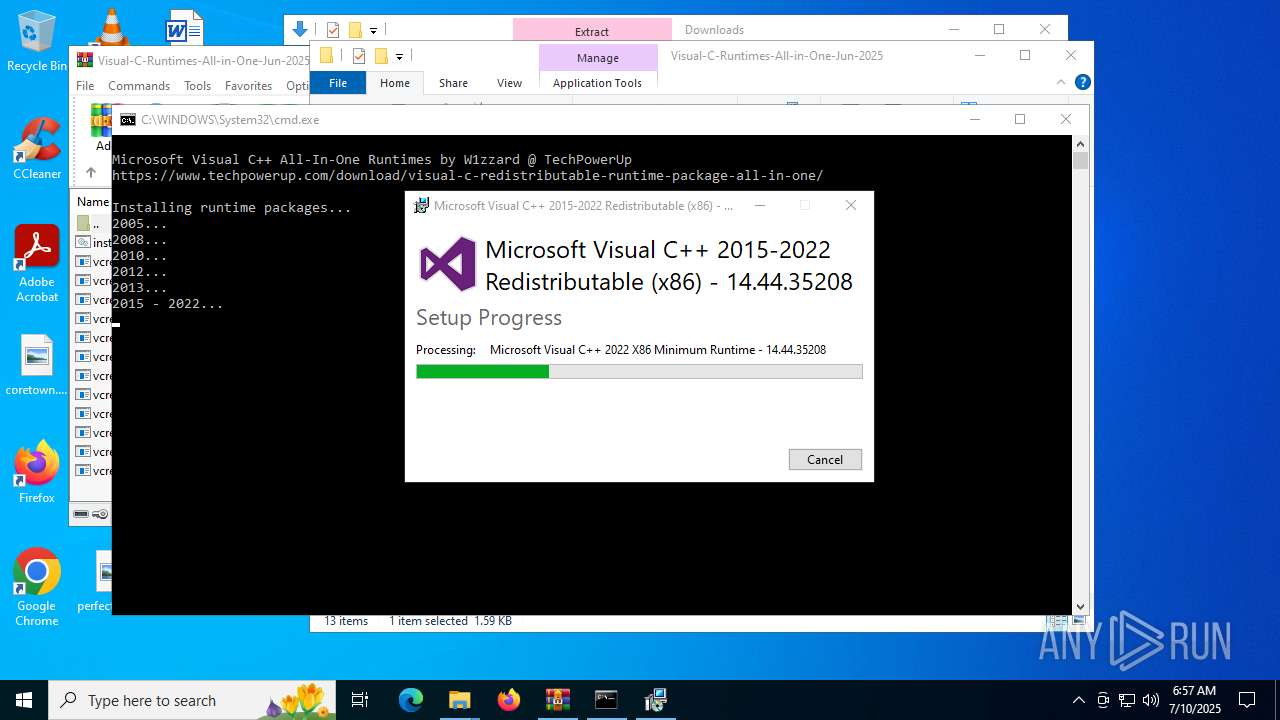
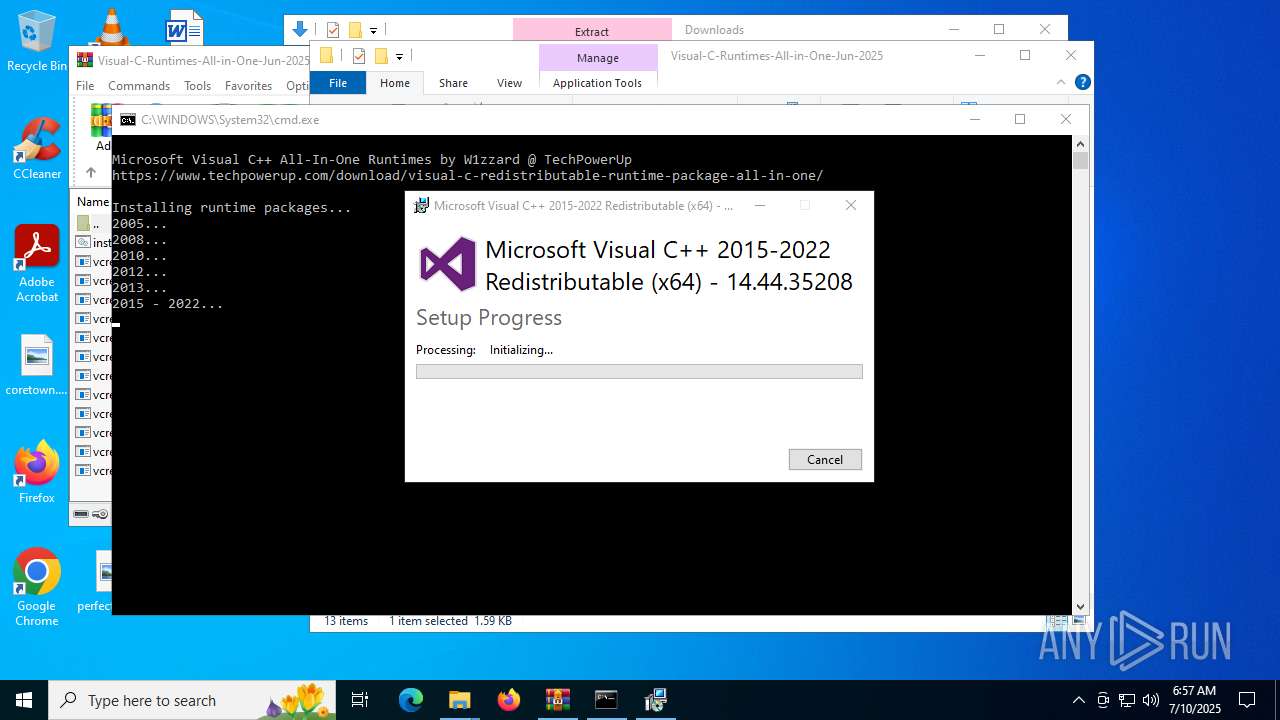
| 1356 | "C:\WINDOWS\Temp\{76BF4189-8F14-4F97-89CB-9770BEEE4169}\.be\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{704A66DA-1E86-4424-B066-5C4CA341C81F} {B92CE784-4E14-4409-9D93-F1F31EF88DE4} 4644 | C:\Windows\Temp\{76BF4189-8F14-4F97-89CB-9770BEEE4169}\.be\VC_redist.x86.exe | — | vcredist2015_2017_2019_2022_x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.44.35208 Exit code: 0 Version: 14.44.35208.0 Modules
| |||||||||||||||
| 1508 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1636 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3660,i,8639135556003639854,15897683521427871999,262144 --variations-seed-version --mojo-platform-channel-handle=3560 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
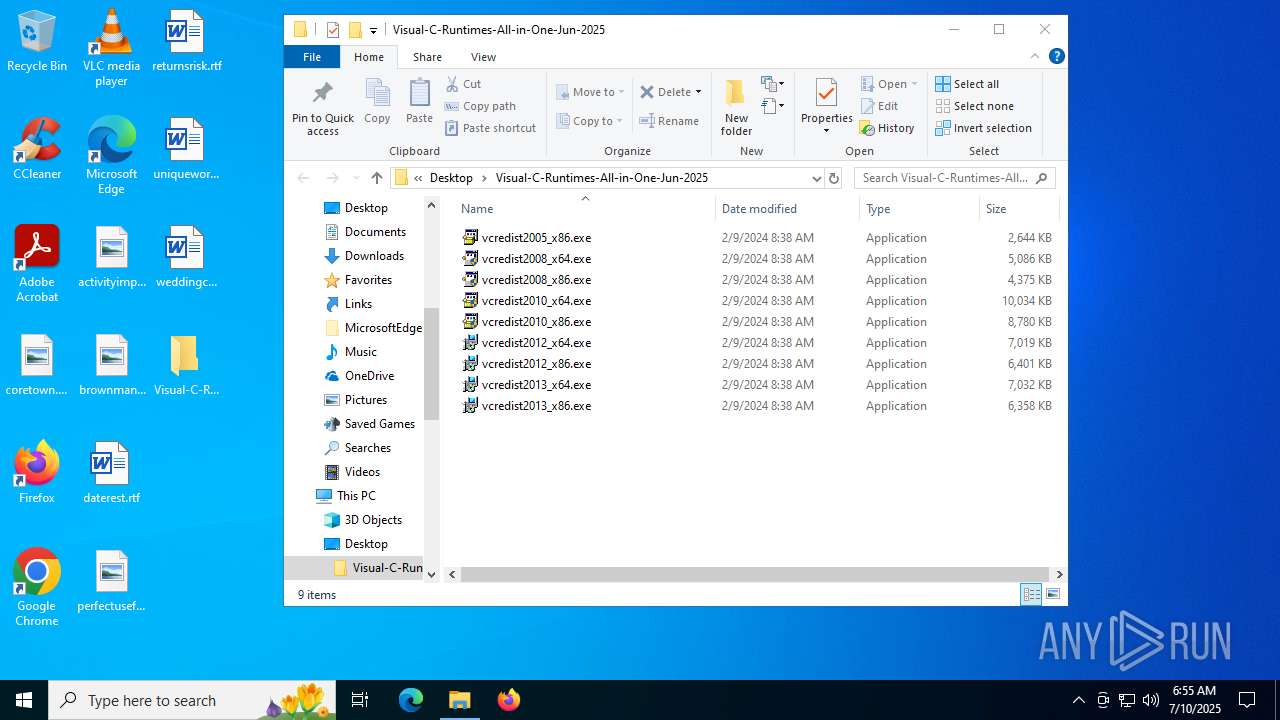
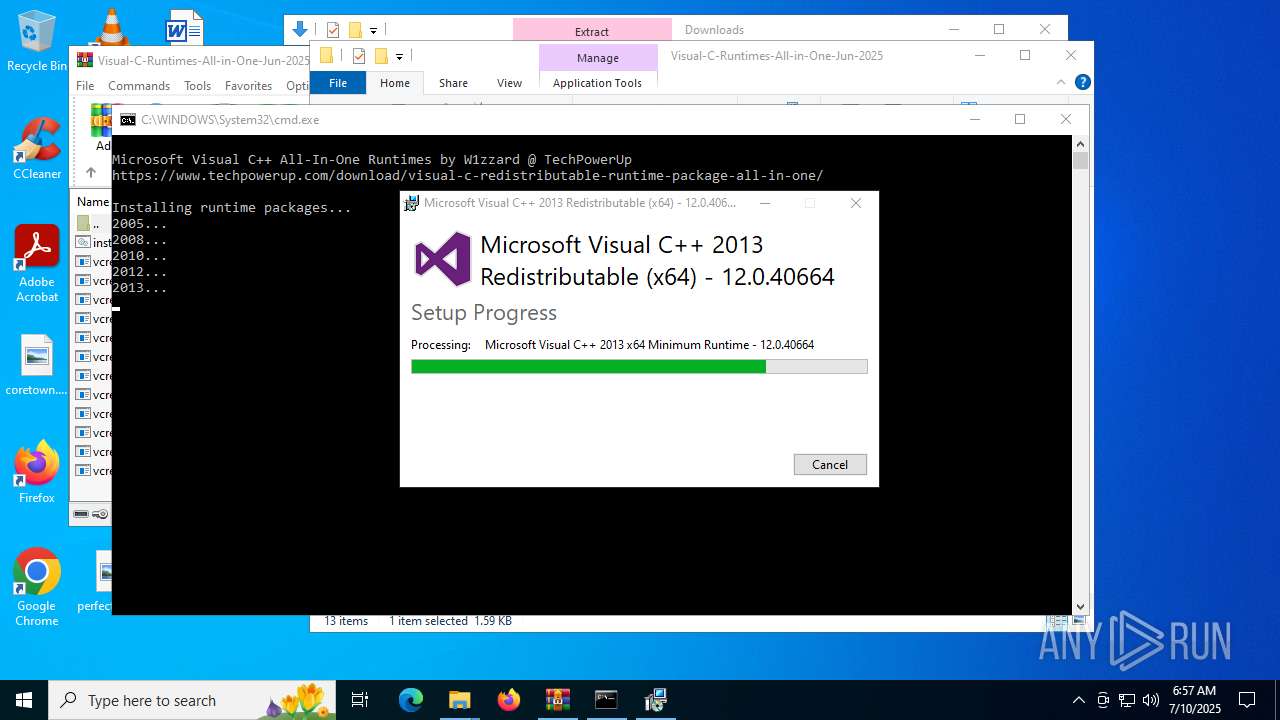
| 1660 | vcredist2013_x86.exe /passive /norestart | C:\Users\admin\Desktop\Visual-C-Runtimes-All-in-One-Jun-2025\vcredist2013_x86.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.40664 Exit code: 0 Version: 12.0.40664.0 Modules
| |||||||||||||||
| 1760 | "C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe" -q -burn.elevated BurnPipe.{D2003D09-0658-4CDA-91D2-1D779EBD3C12} {F47C0DAC-7457-43E1-86C9-005938994F3F} 2716 | C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe | — | VC_redist.x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 2228 | vcredist2008_x64.exe /qb | C:\Users\admin\Desktop\Visual-C-Runtimes-All-in-One-Jun-2025\vcredist2008_x64.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2008 Redistributable Setup Exit code: 0 Version: 9.0.30729.5677 Modules
| |||||||||||||||
Total events
100 672
Read events
92 530
Write events
6 813
Delete events
1 329
Modification events
| (PID) Process: | (6528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6528) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D5A42DF423982F00 | |||
| (PID) Process: | (6528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\787138 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F3EC5ABC-02FE-4974-952D-33B03A3761E0} | |||
| (PID) Process: | (6528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\787138 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A135B7DD-8150-4CAA-BA7F-BEFE4B57401B} | |||
| (PID) Process: | (6528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\787138 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {74325123-4156-4981-83C2-8A2E2A0D1782} | |||
| (PID) Process: | (6528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\787138 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {280C484C-0E59-4CAB-A3A9-B71838C9A1E9} | |||
| (PID) Process: | (6528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
699
Suspicious files
1 067
Text files
783
Unknown types
295
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176254.TMP | — | |
MD5:— | SHA256:— | |||
| 6528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176263.TMP | — | |
MD5:— | SHA256:— | |||
| 6528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176263.TMP | — | |
MD5:— | SHA256:— | |||
| 6528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176273.TMP | — | |
MD5:— | SHA256:— | |||
| 6528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176273.TMP | — | |
MD5:— | SHA256:— | |||
| 6528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176292.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
151
DNS requests
153
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6748 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:pBa8R7BQG0_UO0dDHxh_OsA1db6-45EKuqjrw02Mixw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
420 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8092 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8092 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8188 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752577395&P2=404&P3=2&P4=Twldpiq0ZD12MABNfxOqCH5gxN4d4MDEn8pqNQRE2k2UKhWpJWJLQFeSHV1xsJ%2f2qVQDRnqYdwrg%2bWmhG%2ft%2bIA%3d%3d | unknown | — | — | whitelisted |
7736 | msiexec.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/CSPCA.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
8188 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752577395&P2=404&P3=2&P4=Twldpiq0ZD12MABNfxOqCH5gxN4d4MDEn8pqNQRE2k2UKhWpJWJLQFeSHV1xsJ%2f2qVQDRnqYdwrg%2bWmhG%2ft%2bIA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4816 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6748 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6748 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6748 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6748 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
6748 | msedge.exe | 45.112.123.126:443 | gofile.io | AMAZON-02 | SG | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
gofile.io |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.gofile.io |
| whitelisted |
s.gofile.io |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6748 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
6748 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
6748 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
6748 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
6748 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
6748 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
6748 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
6748 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
6748 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
6748 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
Process | Message |
|---|---|
Setup.exe | The operation completed successfully.
|
Setup.exe | The operation completed successfully.
|
msiexec.exe | Failed to release Service
|