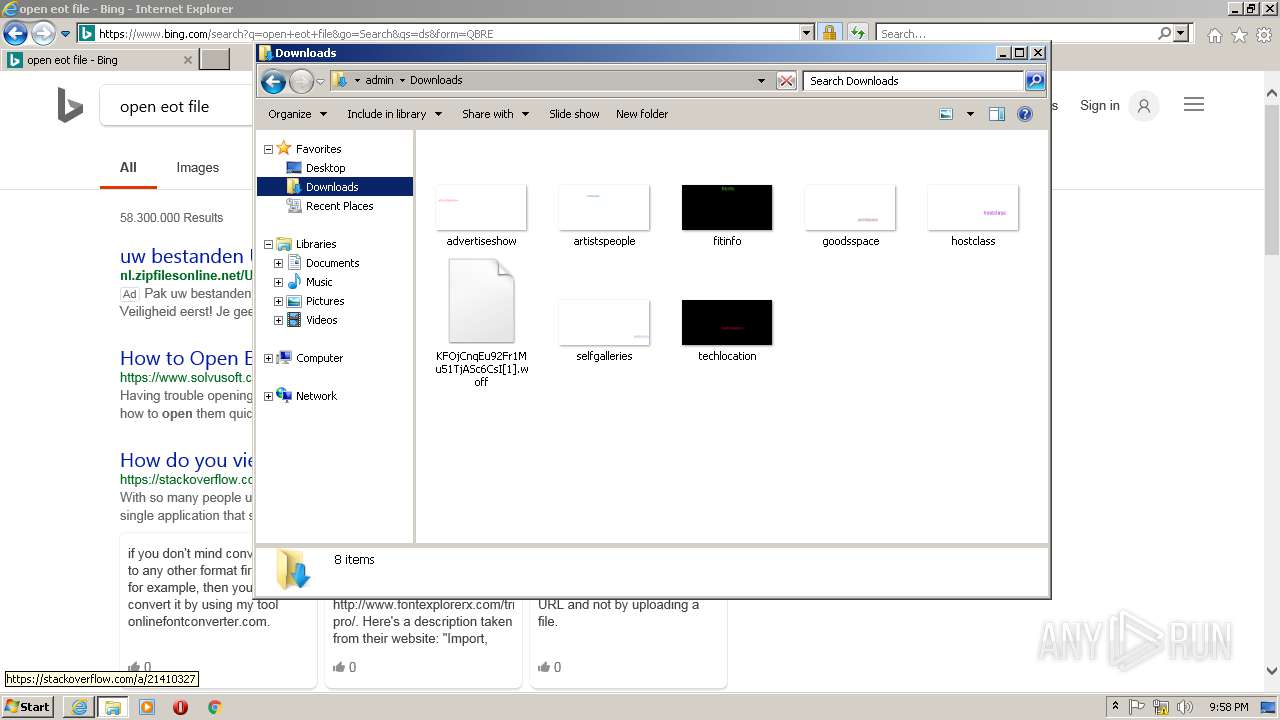
| File name: | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\XLWA6BPE\KFOjCnqEu92Fr1Mu51TjASc6CsI[1].woff |
| Full analysis: | https://app.any.run/tasks/293e6a48-92d6-45cc-9620-04a7294f8846 |
| Verdict: | No threats detected |
| Analysis date: | March 11, 2019, 21:56:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | Web Open Font Format, TrueType, length 21776, version 1.1 |
| MD5: | 210A7C781F5A354A0E4985656AB456D9 |
| SHA1: | E6240E79B795D952F4BE7E9F5338AF1EA62DDDDD |
| SHA256: | 96E0BF768FC3C6FDB04C5D11AA1A63080B27BD48754444AC10D449886720AF78 |
| SSDEEP: | 384:i7sNCb8EbeqhYyEz407taa6vNcZG0X3Wsl9aTeR4we/P/y0ktTArJH1KW8Y:2s4zbHOzMaeNcZjX3BzdR4we/XgTyH8q |
MALICIOUS
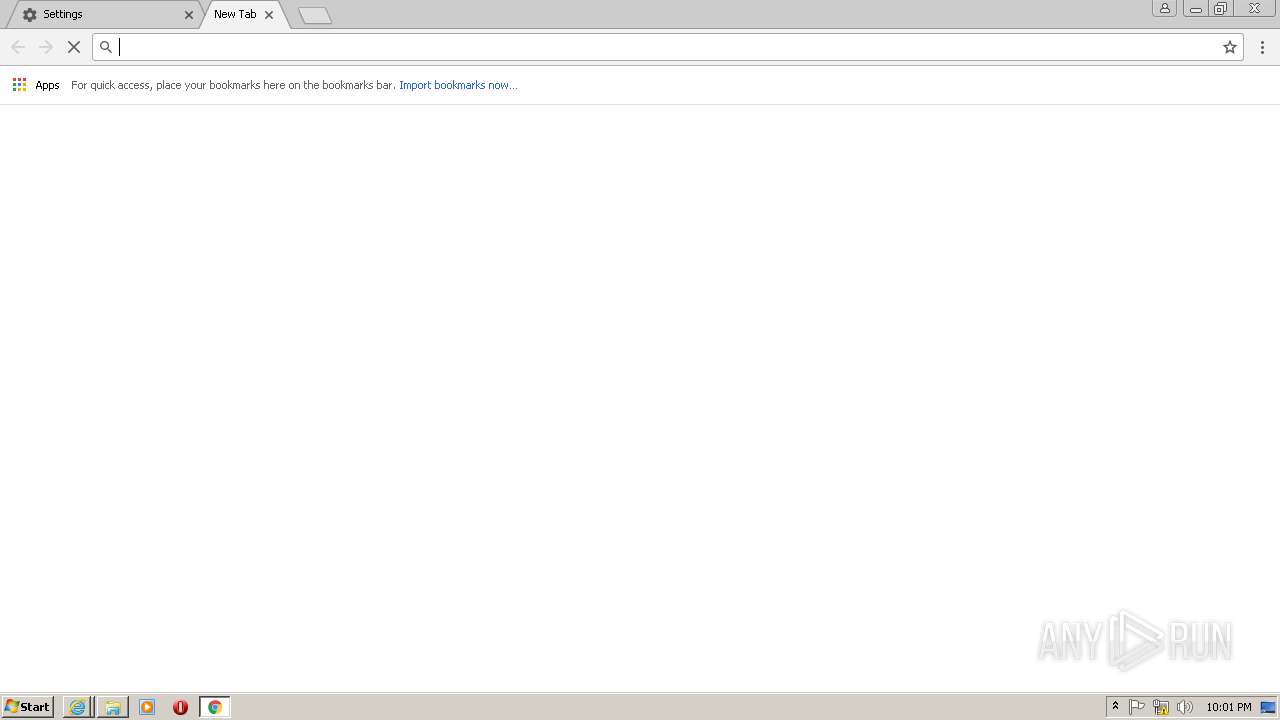
No malicious indicators.SUSPICIOUS
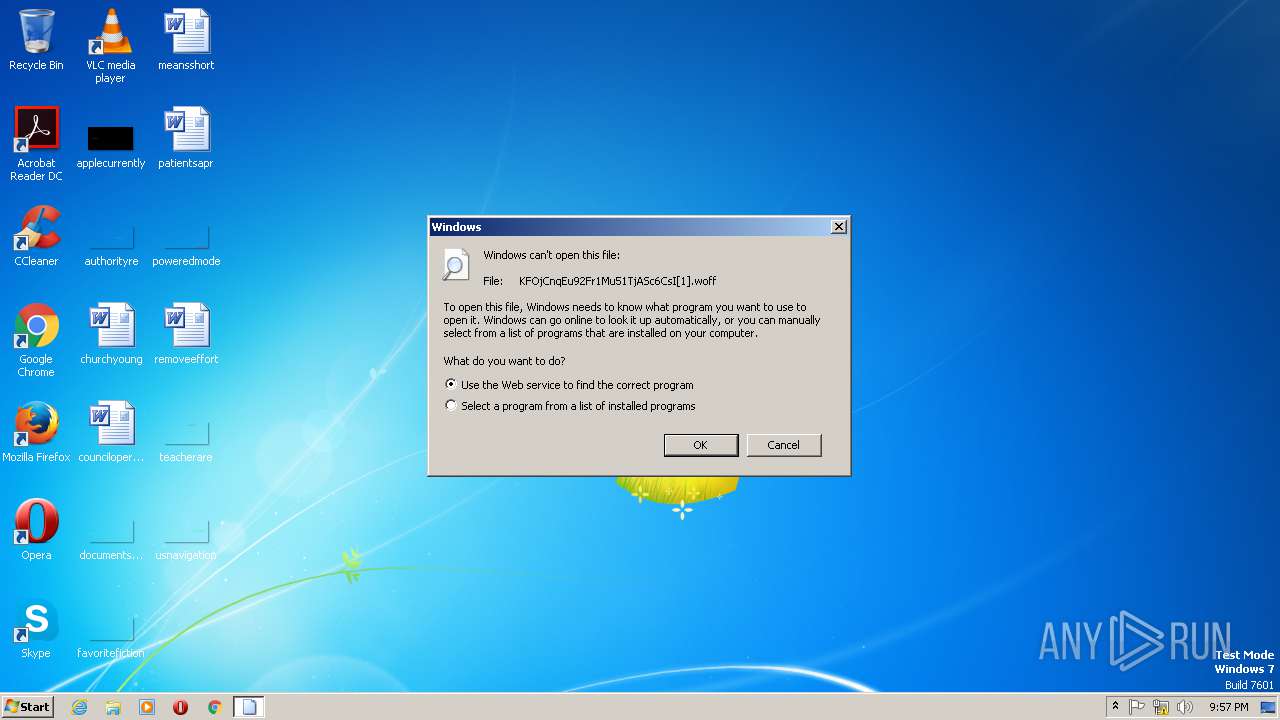
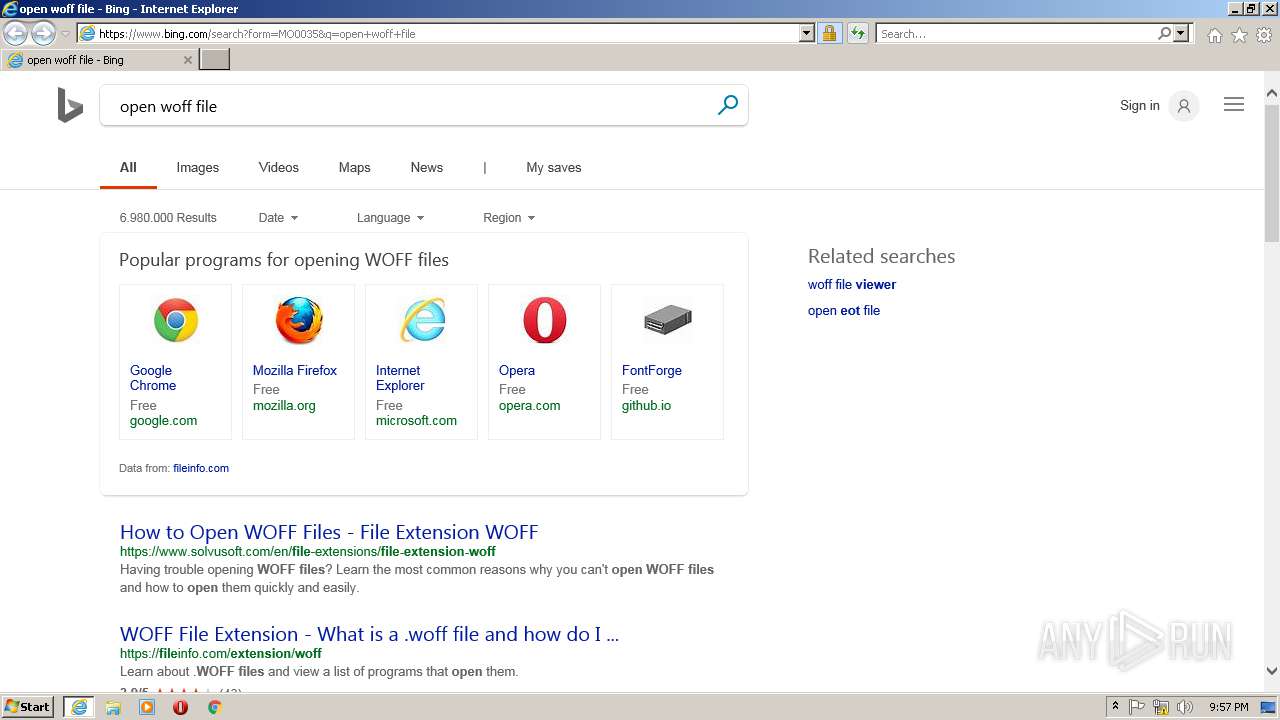
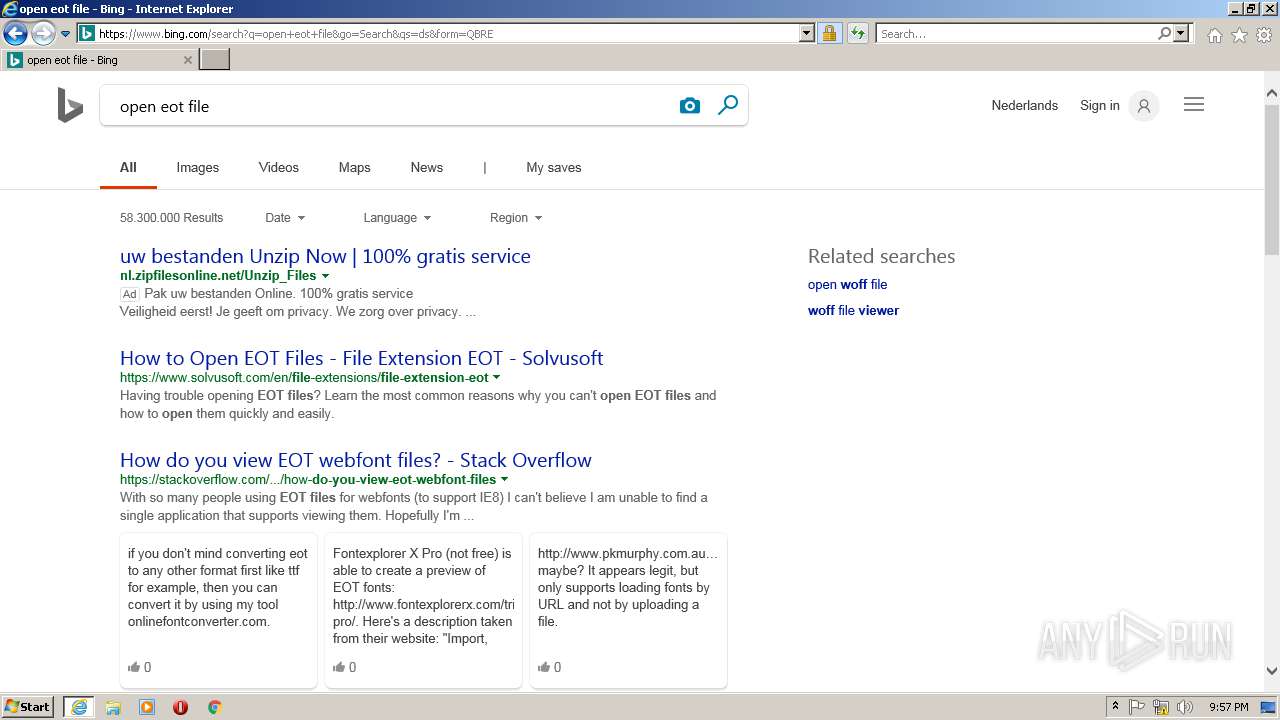
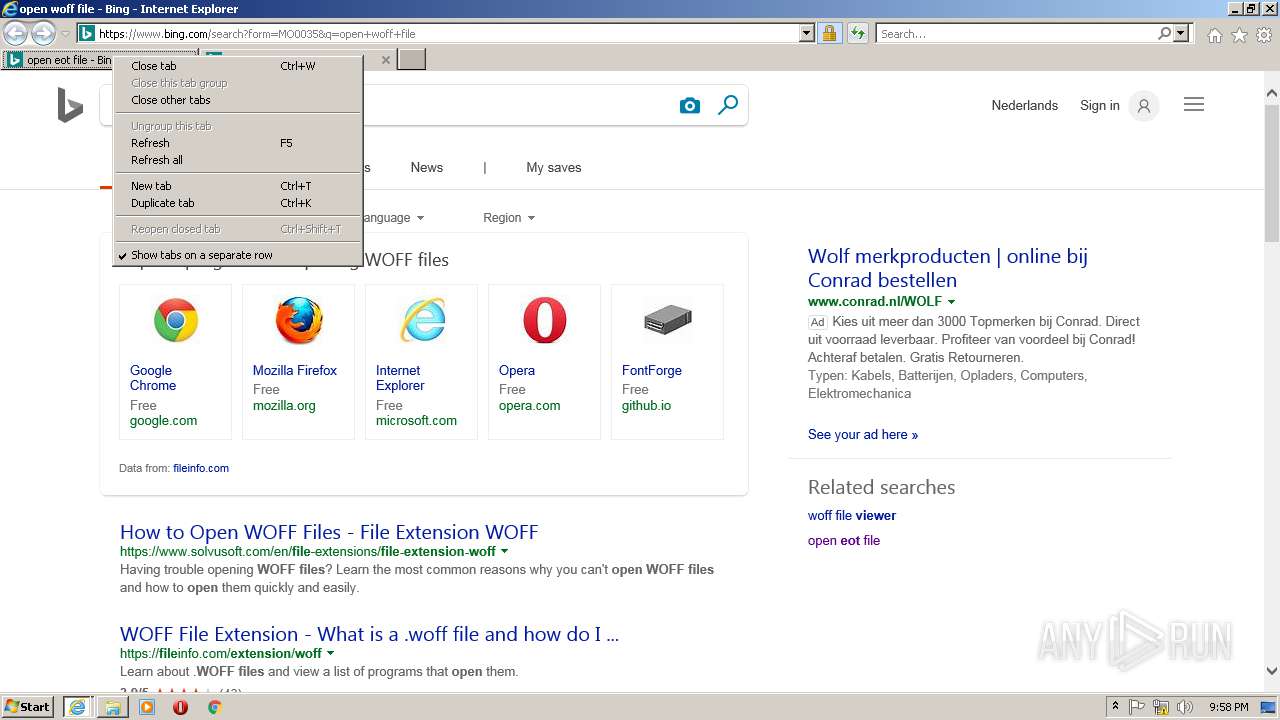
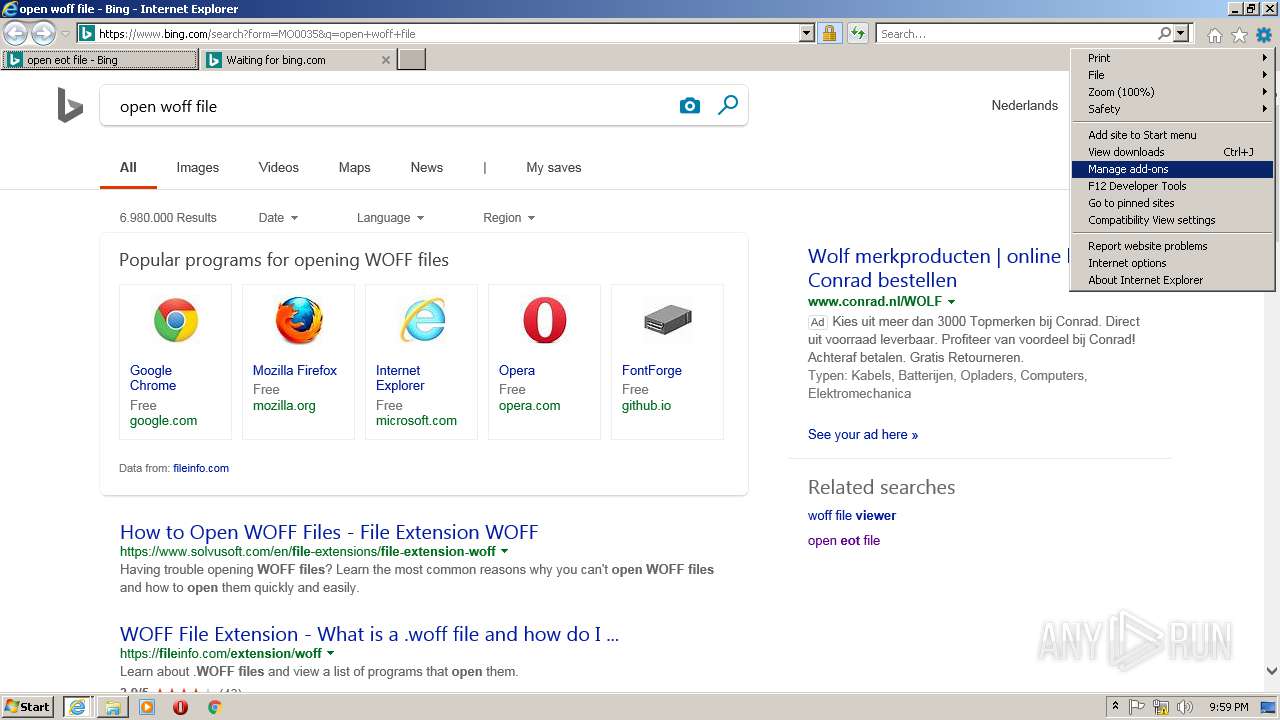
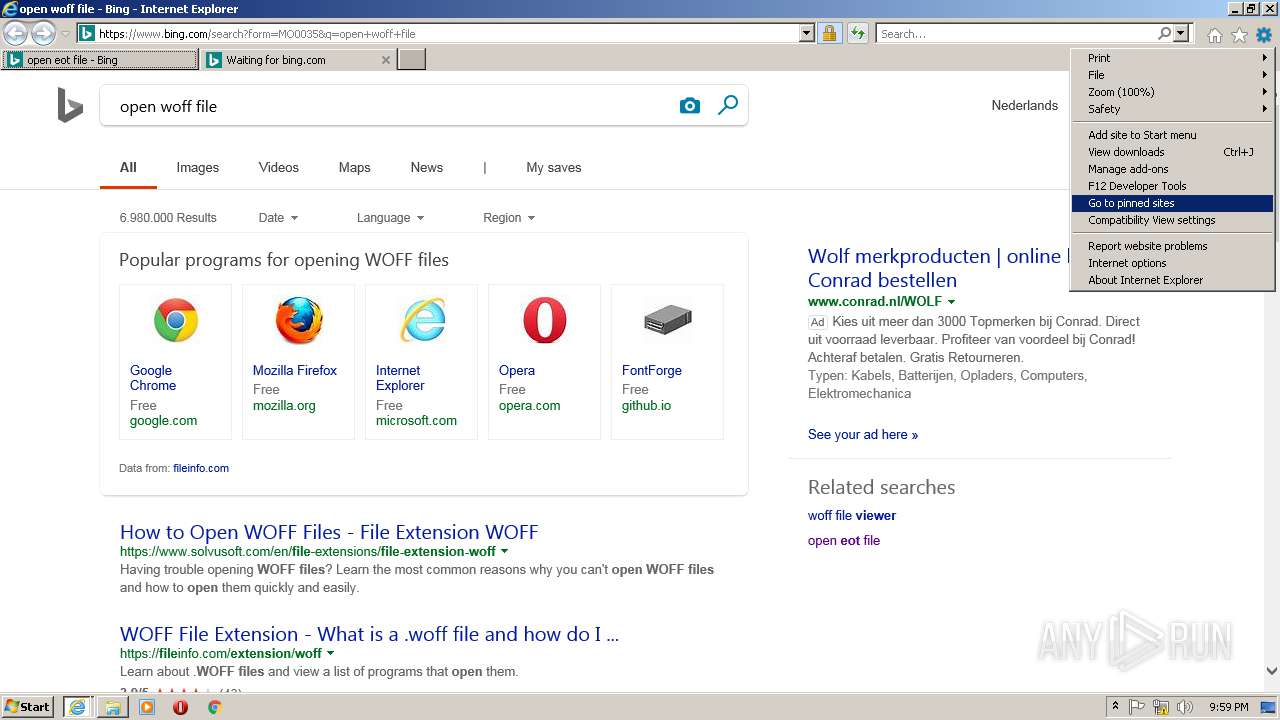
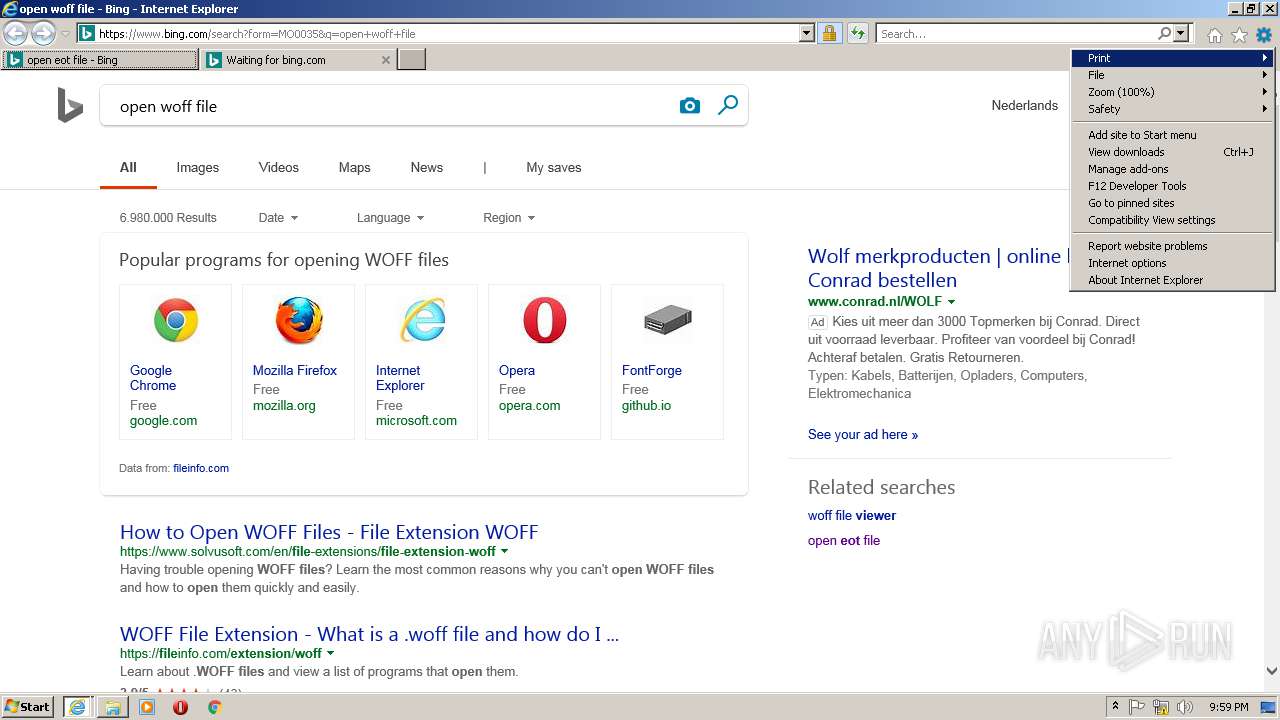
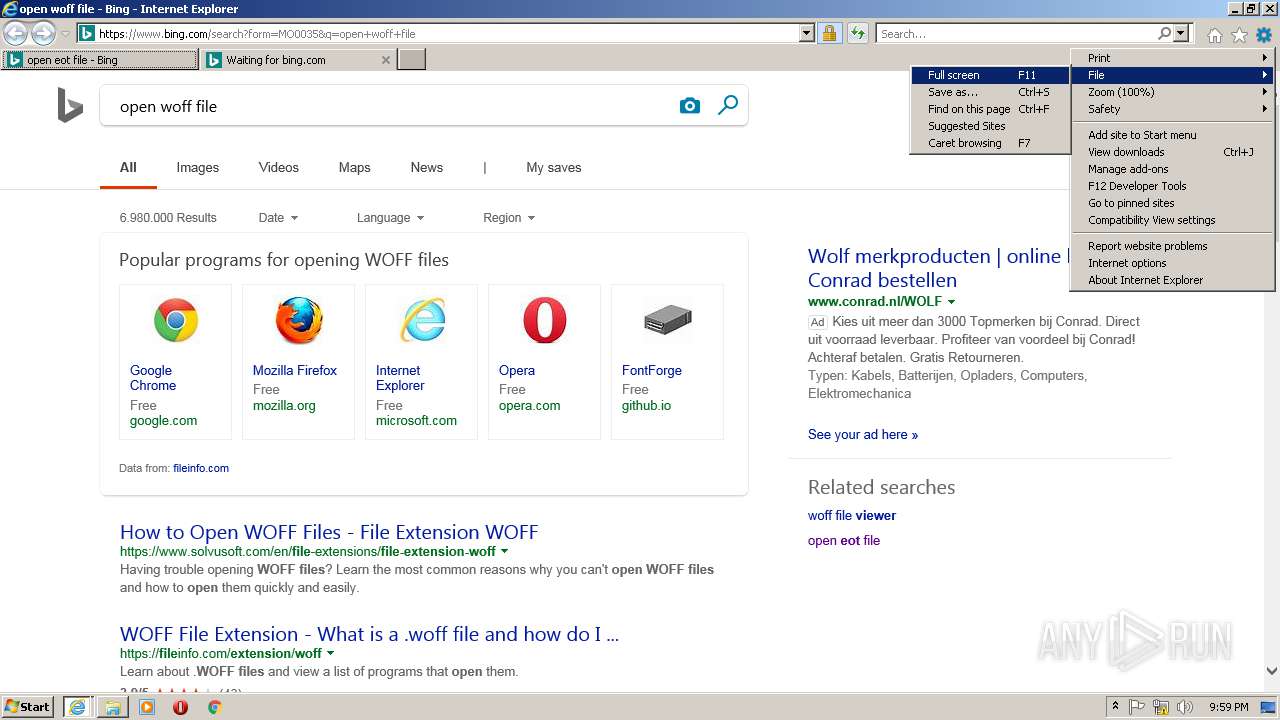
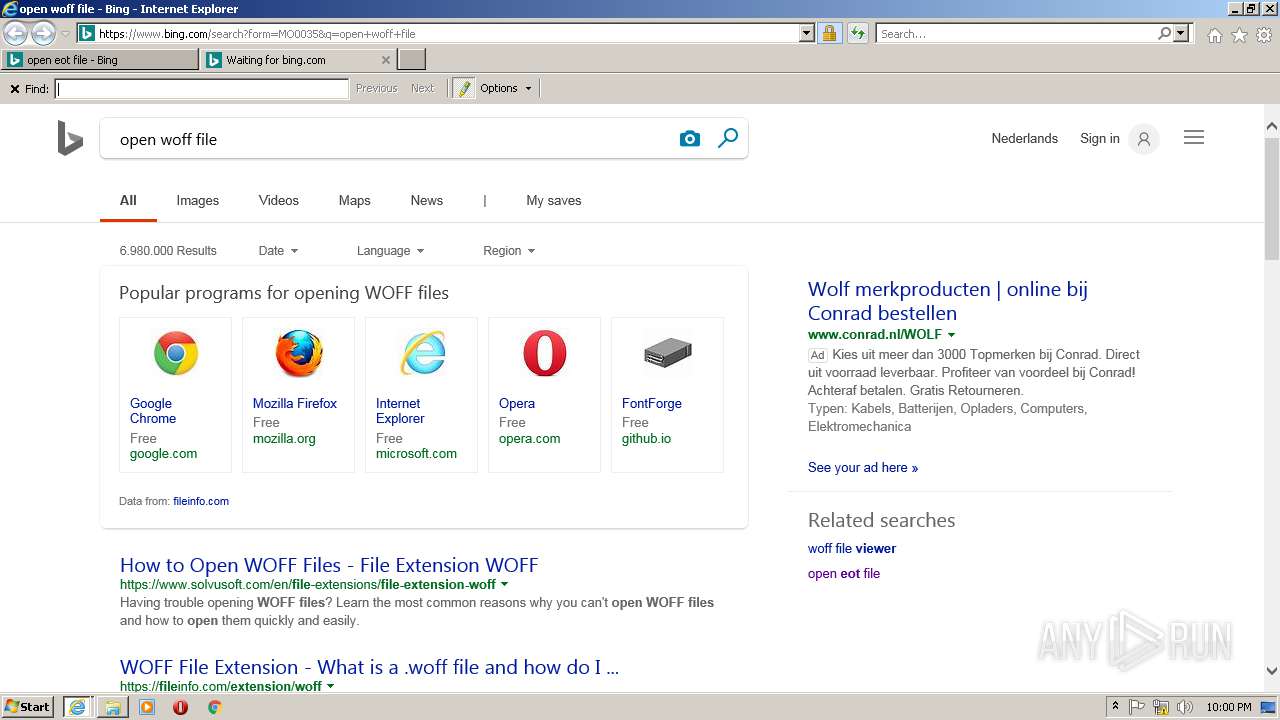
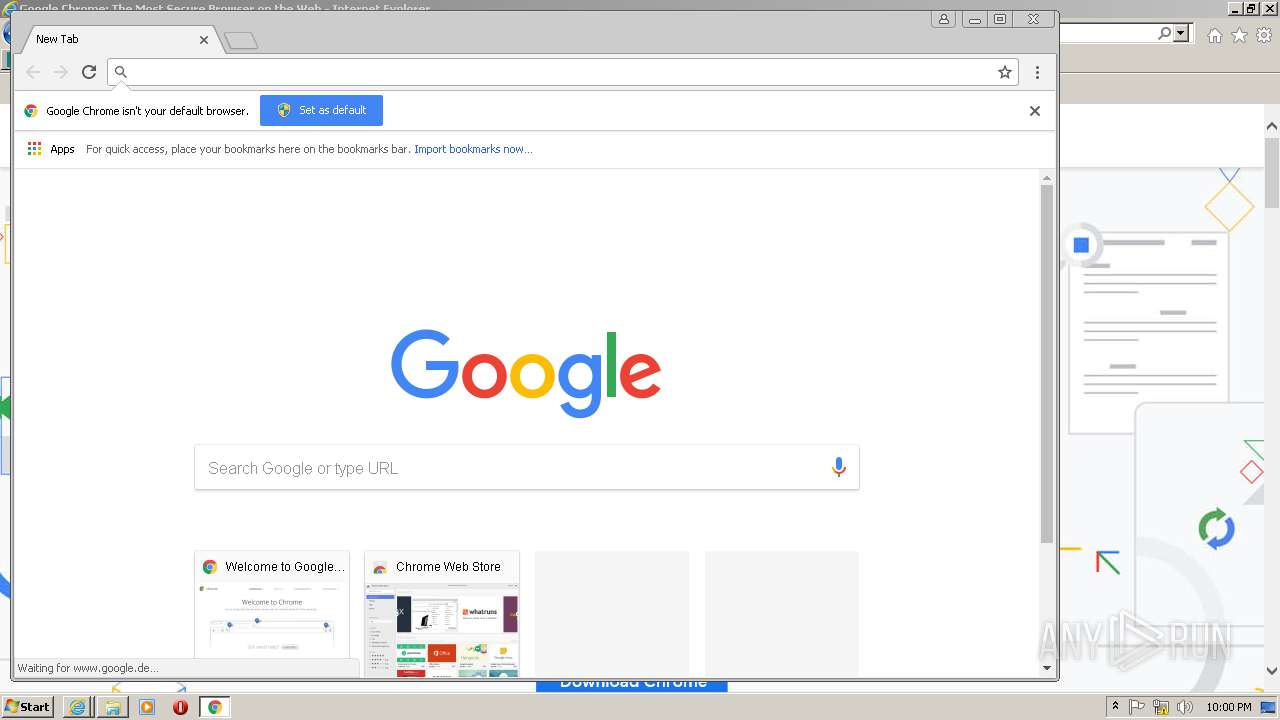
Starts Internet Explorer
- rundll32.exe (PID: 2076)
Reads the machine GUID from the registry
- explorer.exe (PID: 2884)
INFO
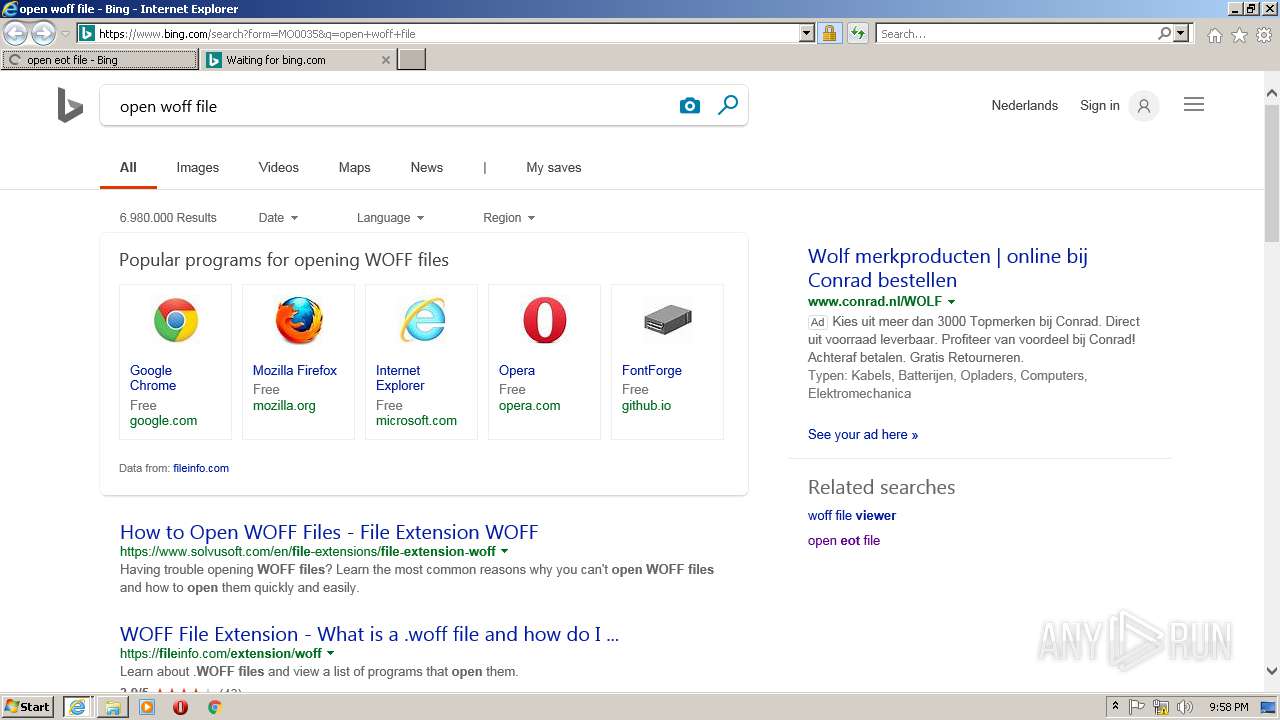
Changes internet zones settings
- iexplore.exe (PID: 2108)
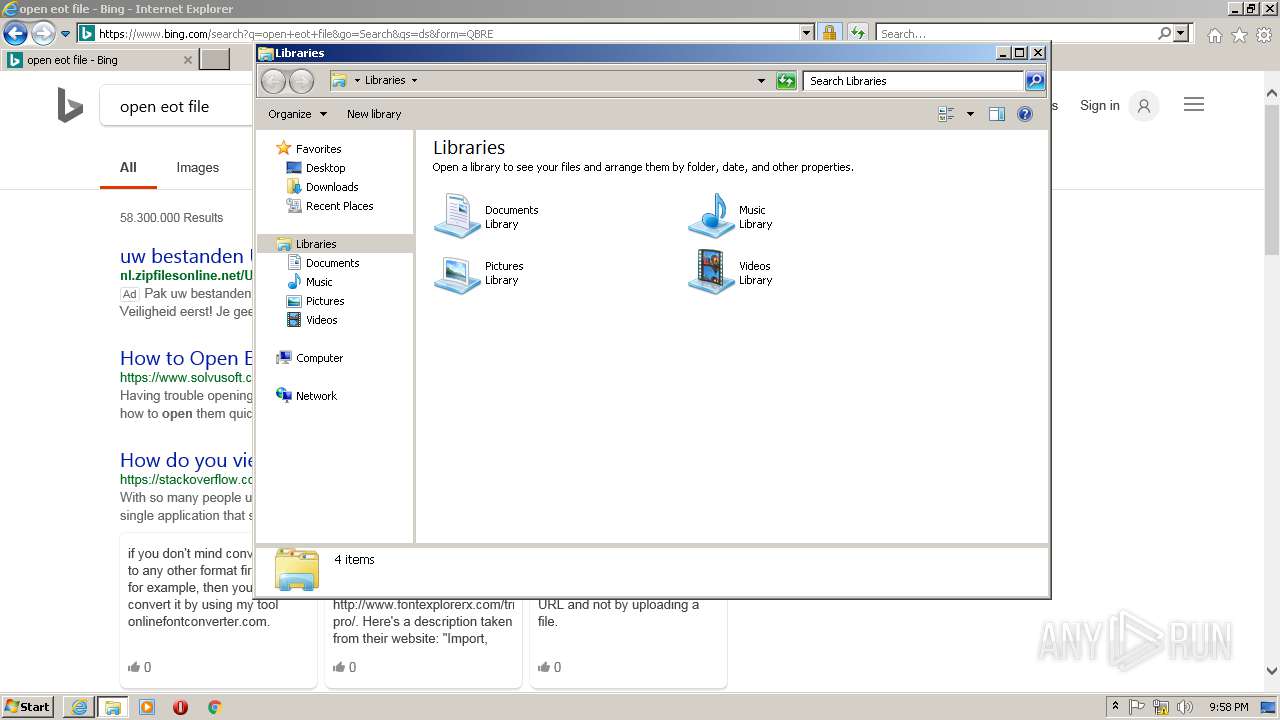
Creates files in the user directory
- IEXPLORE.EXE (PID: 1260)
- chrome.exe (PID: 2140)
- IEXPLORE.EXE (PID: 2136)
- iexplore.exe (PID: 2108)
Reads settings of System Certificates
- IEXPLORE.EXE (PID: 1260)
- chrome.exe (PID: 2140)
- IEXPLORE.EXE (PID: 2136)
- iexplore.exe (PID: 2108)
Reads the machine GUID from the registry
- iexplore.exe (PID: 2108)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 720)
Reads Internet Cache Settings
- iexplore.exe (PID: 2108)
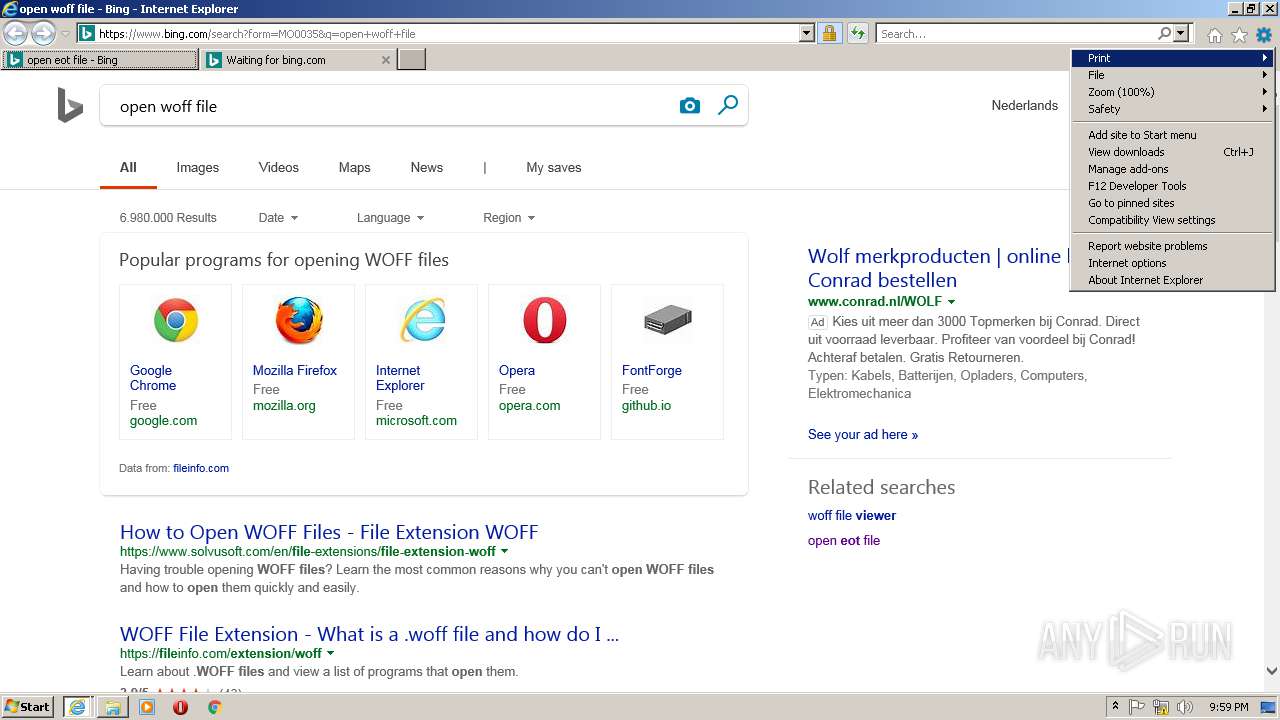
Reads internet explorer settings
- IEXPLORE.EXE (PID: 1260)
- IEXPLORE.EXE (PID: 2136)
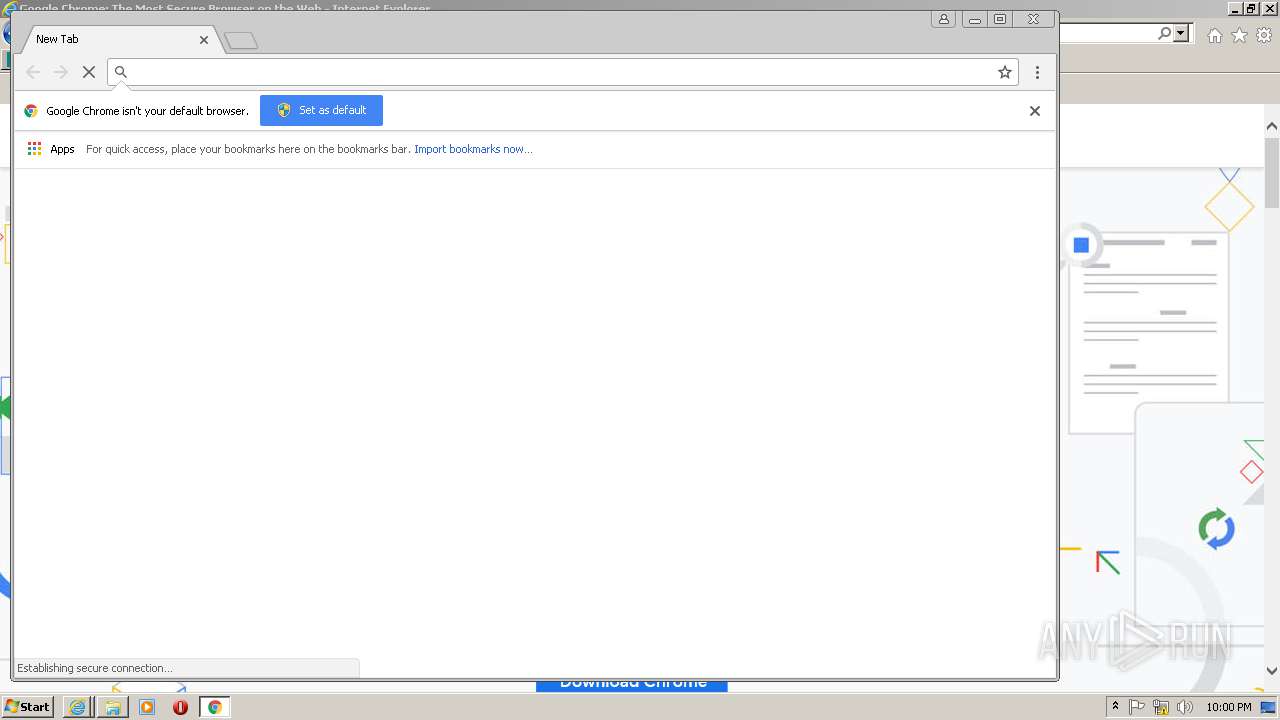
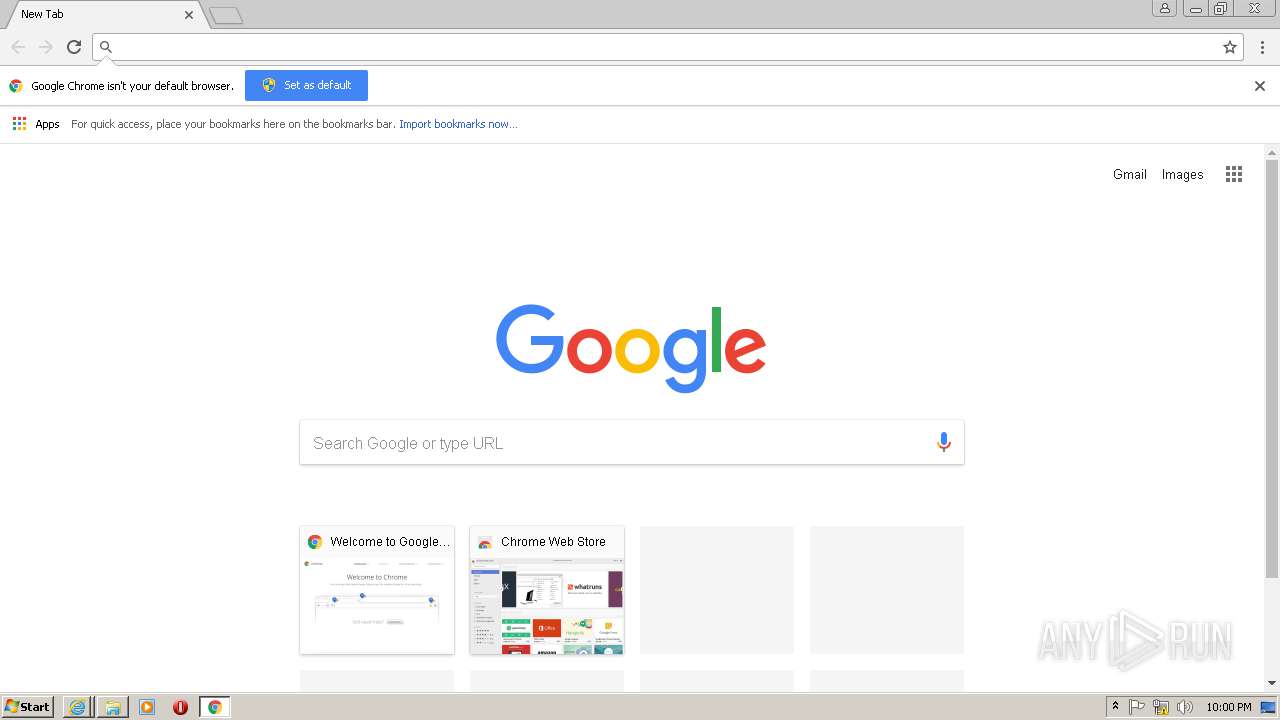
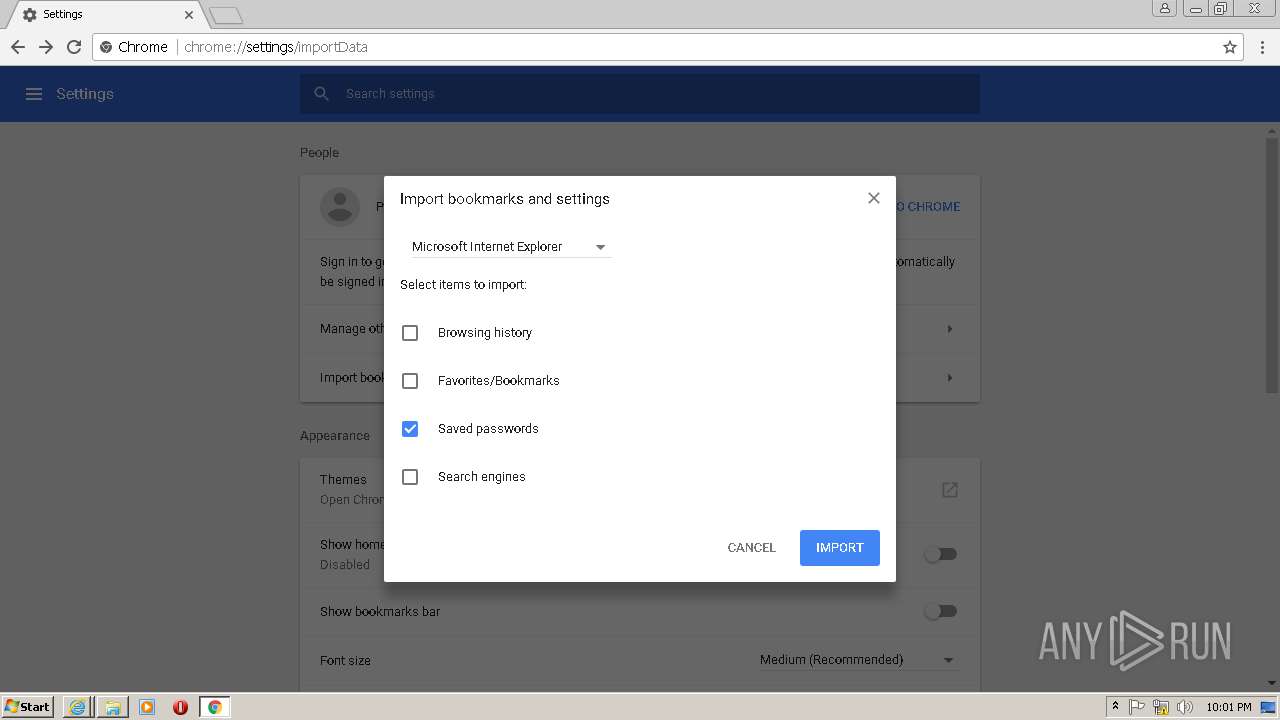
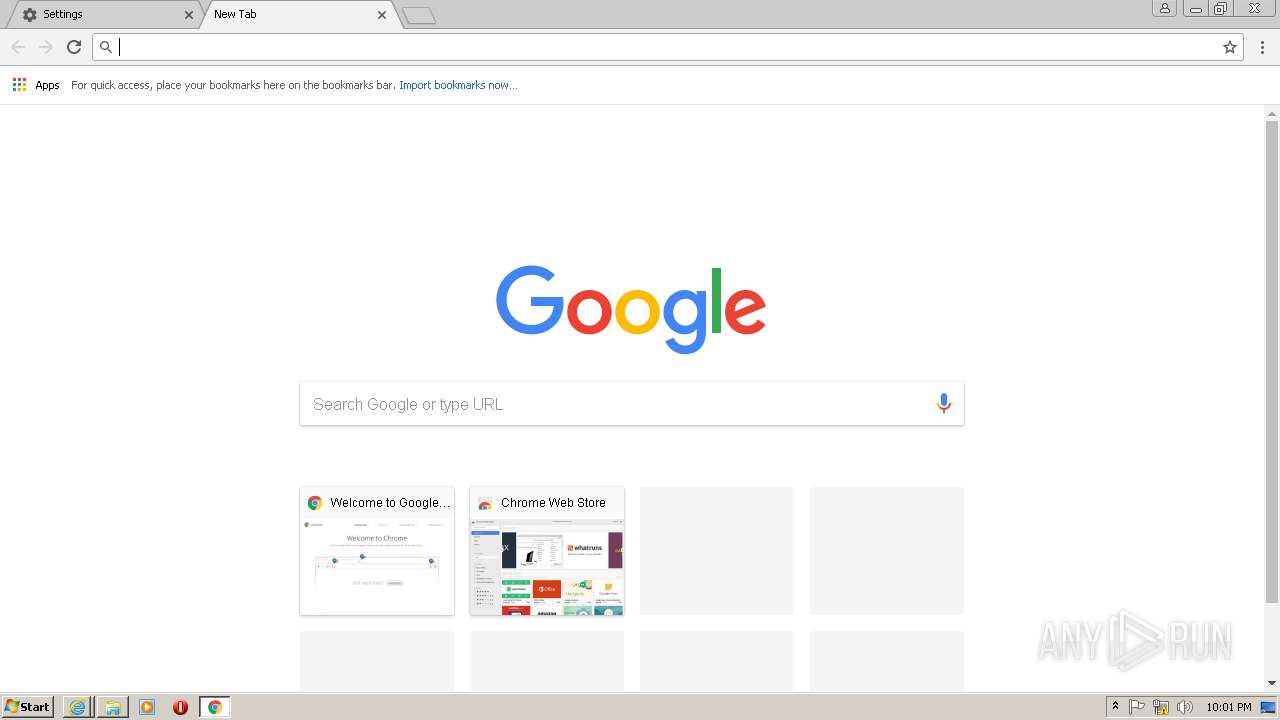
Application launched itself
- chrome.exe (PID: 2140)
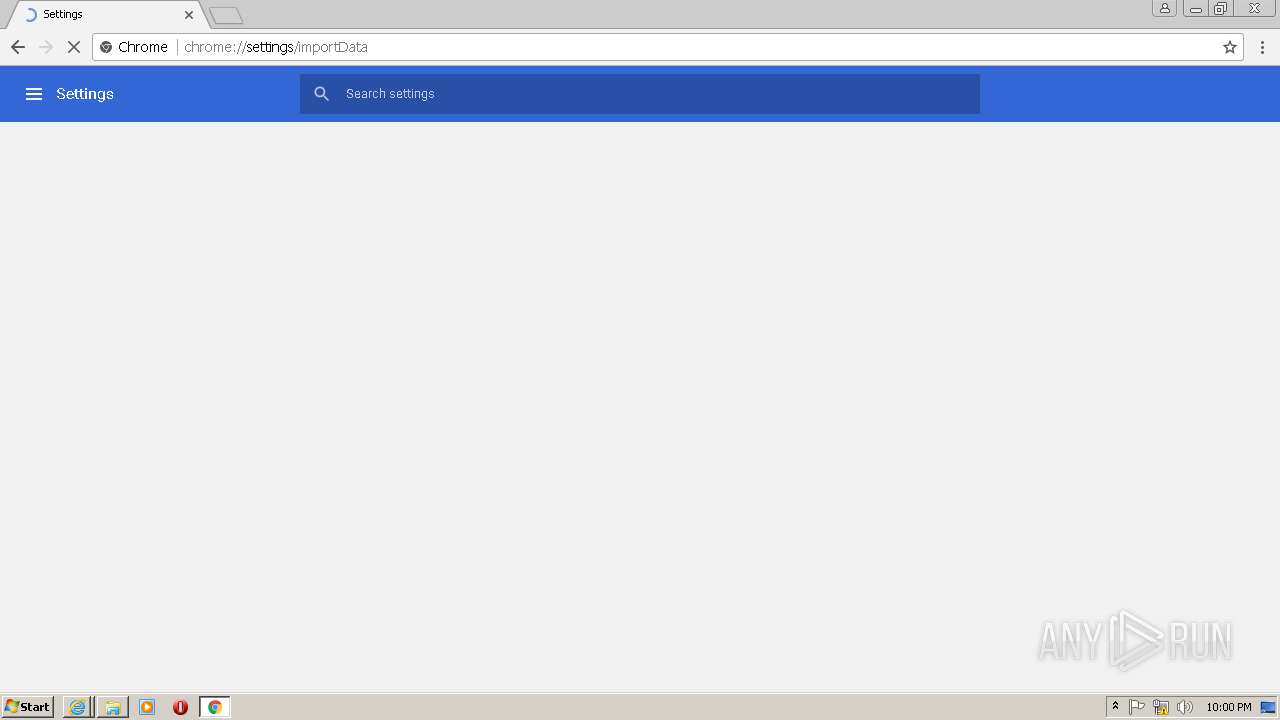
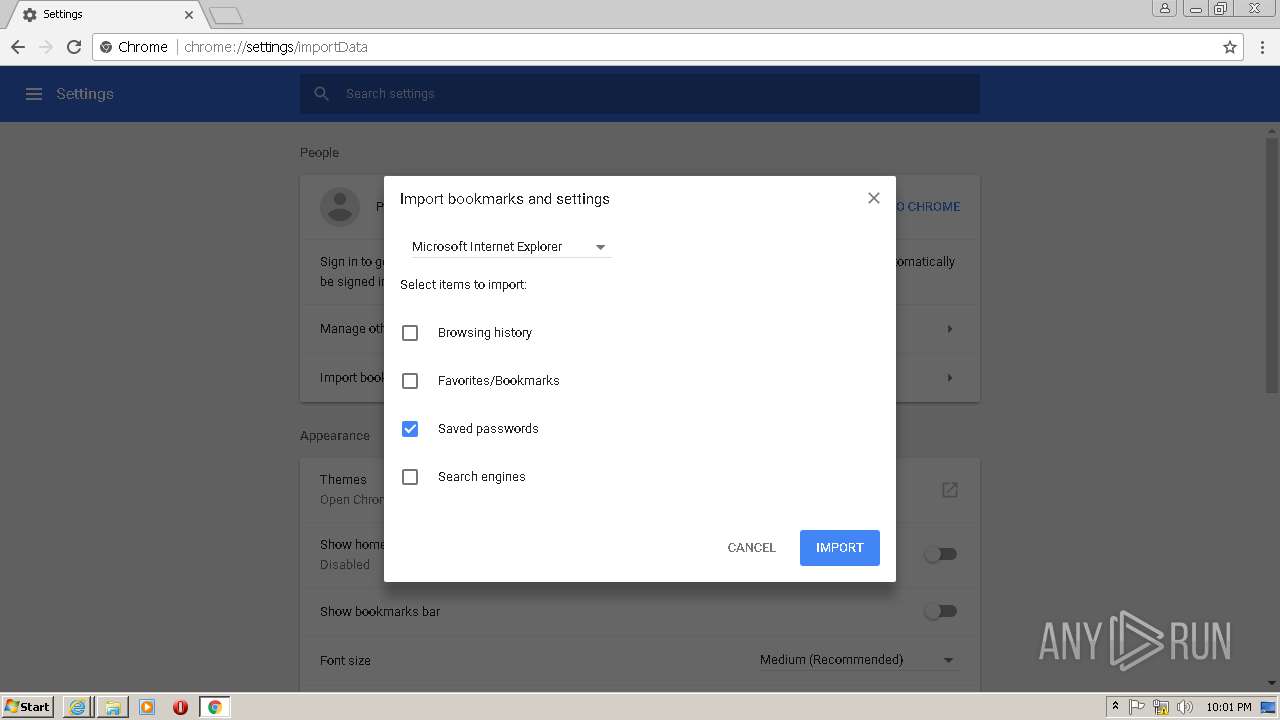
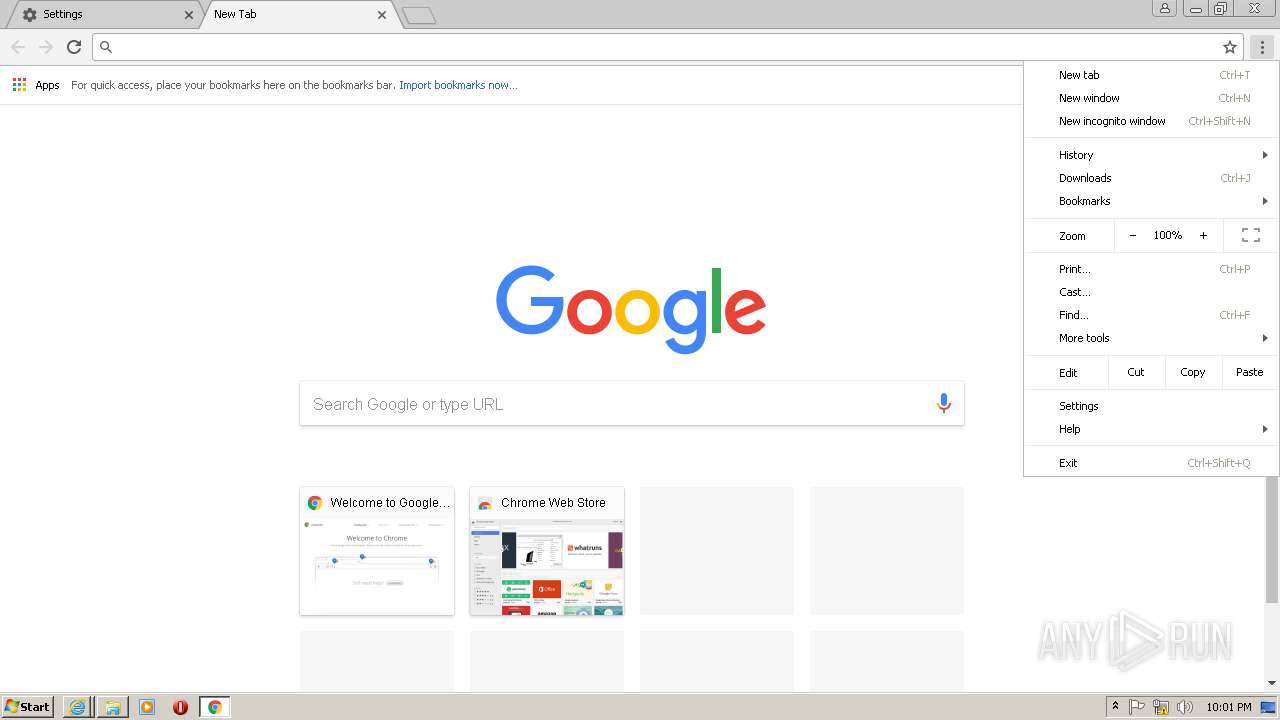
Modifies the open verb of a shell class
- chrome.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .woff | | | Web Open Font Format (100) |
|---|
Total processes
51
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1712,2578962380318099393,8108093972694209096,131072 --service-pipe-token=FCCBE2A275346CB6D3635CB877E85EDA --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=FCCBE2A275346CB6D3635CB877E85EDA --renderer-client-id=5 --mojo-platform-channel-handle=3336 /prefetch:1 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1712,2578962380318099393,8108093972694209096,131072 --lang=en-US --no-sandbox --service-request-channel-token=6DDAD9D35F79E1508FB5D1DC626D15F3 --mojo-platform-channel-handle=2324 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1712,2578962380318099393,8108093972694209096,131072 --service-pipe-token=643FA896519B453DFCCA7DDBE95AFDF4 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=643FA896519B453DFCCA7DDBE95AFDF4 --renderer-client-id=4 --mojo-platform-channel-handle=1724 /prefetch:1 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 1260 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2108 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
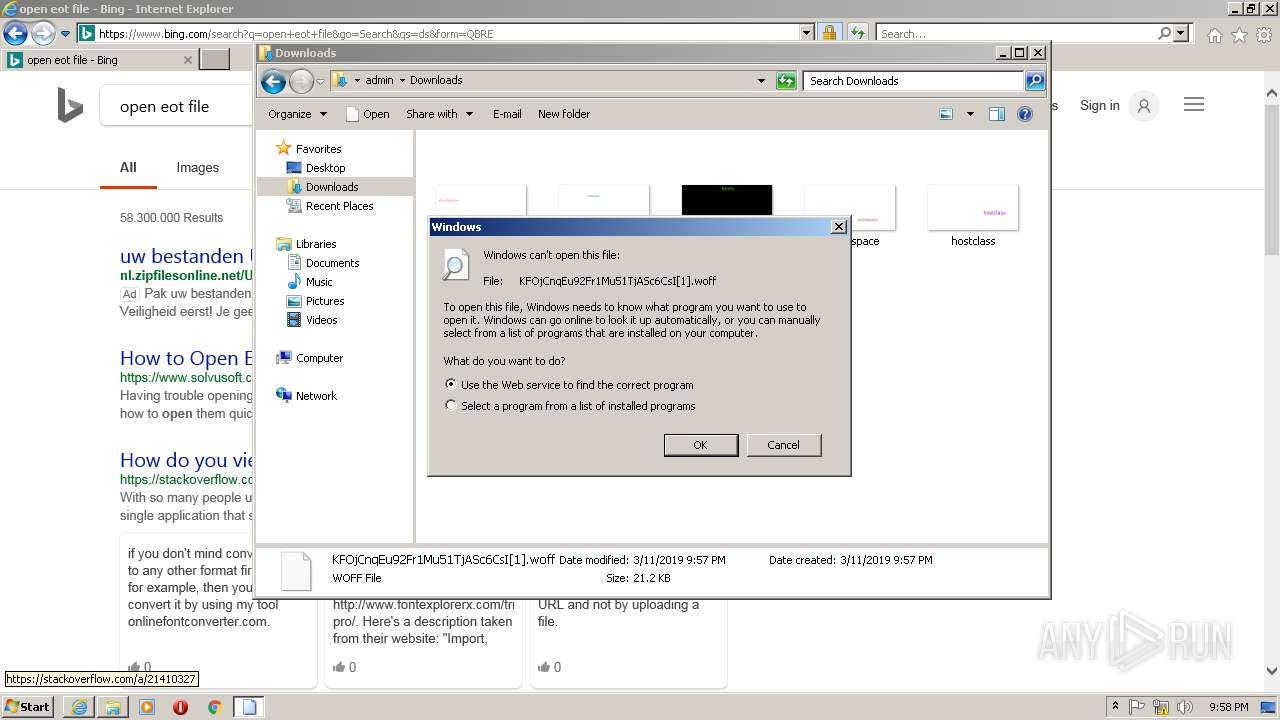
| 2076 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\KFOjCnqEu92Fr1Mu51TjASc6CsI[1].woff | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2088 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\KFOjCnqEu92Fr1Mu51TjASc6CsI[1].woff | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
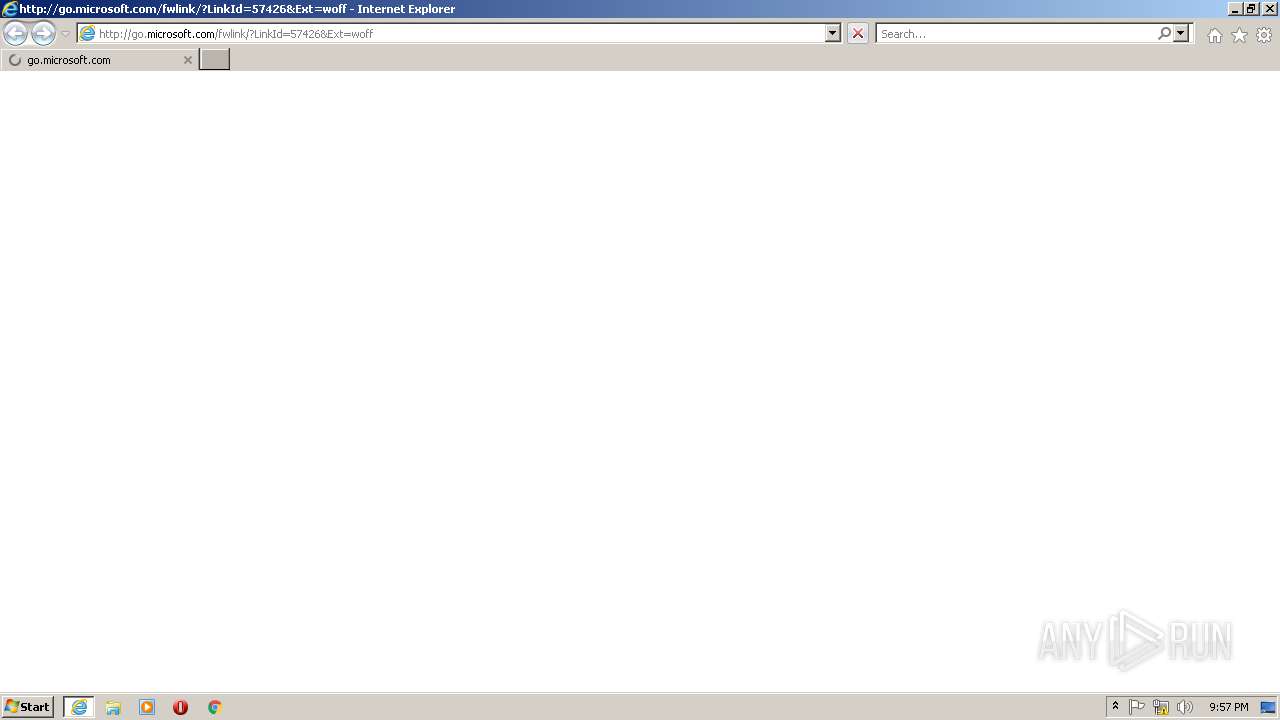
| 2108 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=woff | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2120 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=61.0.3163.91 --initial-client-data=0x80,0x84,0x88,0x7c,0x8c,0x7fef3891978,0x7fef3891938,0x7fef3891948 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2128 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1712,2578962380318099393,8108093972694209096,131072 --lang=en-US --service-request-channel-token=192870CF19B4D9D698E7F27D05CCD68F --mojo-platform-channel-handle=648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2136 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2108 CREDAT:2954562 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 085
Read events
1 830
Write events
241
Delete events
14
Modification events
| (PID) Process: | (2076) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 010000000000000014004A6655D8D401 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 2 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 1717523216 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30726229 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2017531966 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30726229 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
0
Suspicious files
56
Text files
165
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1260 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0CGJUTOP.txt | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\K78MRVB5\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1260 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\B2JBJJ0H.txt | text | |
MD5:— | SHA256:— | |||
| 1260 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YQPEPCE1\SharedSpriteDesktopRewards_022118[1].png | image | |
MD5:— | SHA256:— | |||
| 1260 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\XLWA6BPE\search[1].htm | html | |
MD5:— | SHA256:— | |||
| 1260 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UJFUX3OG\cc8437ad[1].js | text | |
MD5:— | SHA256:— | |||
| 1260 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YQPEPCE1\ee9f5ae1[1].js | text | |
MD5:— | SHA256:— | |||
| 1260 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\2ISUM8PH.txt | — | |
MD5:— | SHA256:— | |||
| 1260 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\XLWA6BPE\33036ea1[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
222
TCP/UDP connections
105
DNS requests
30
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
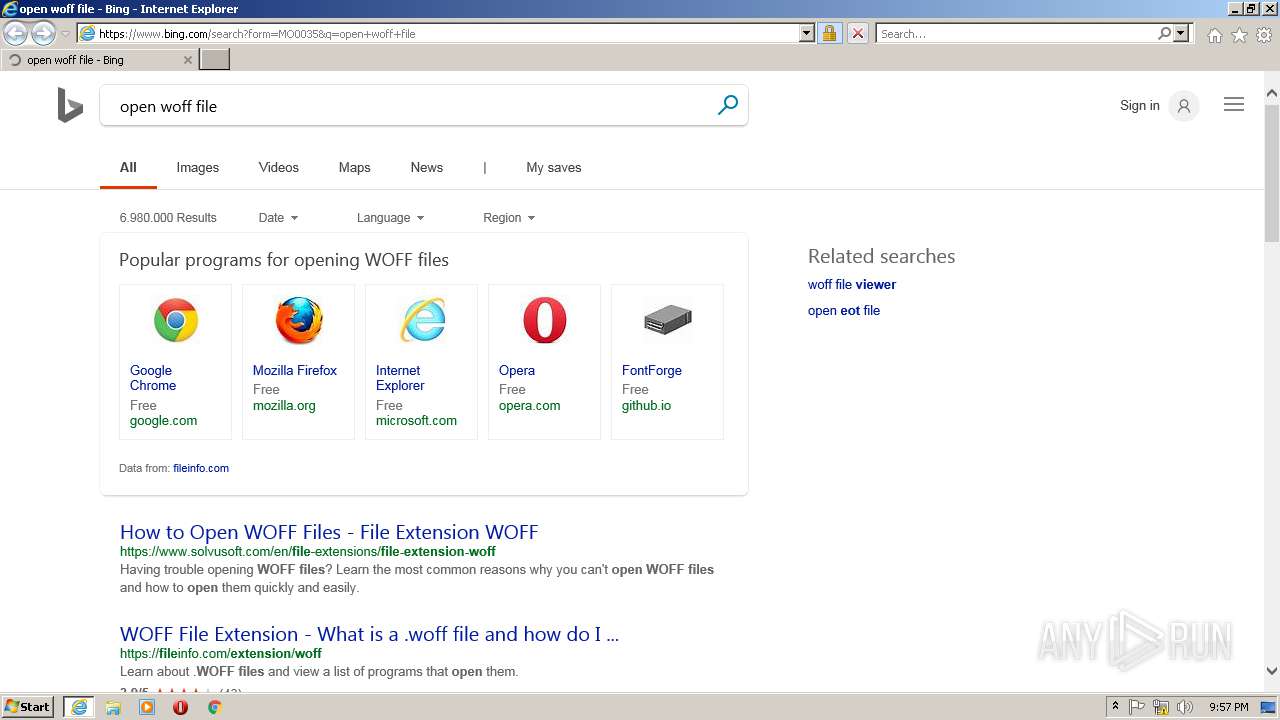
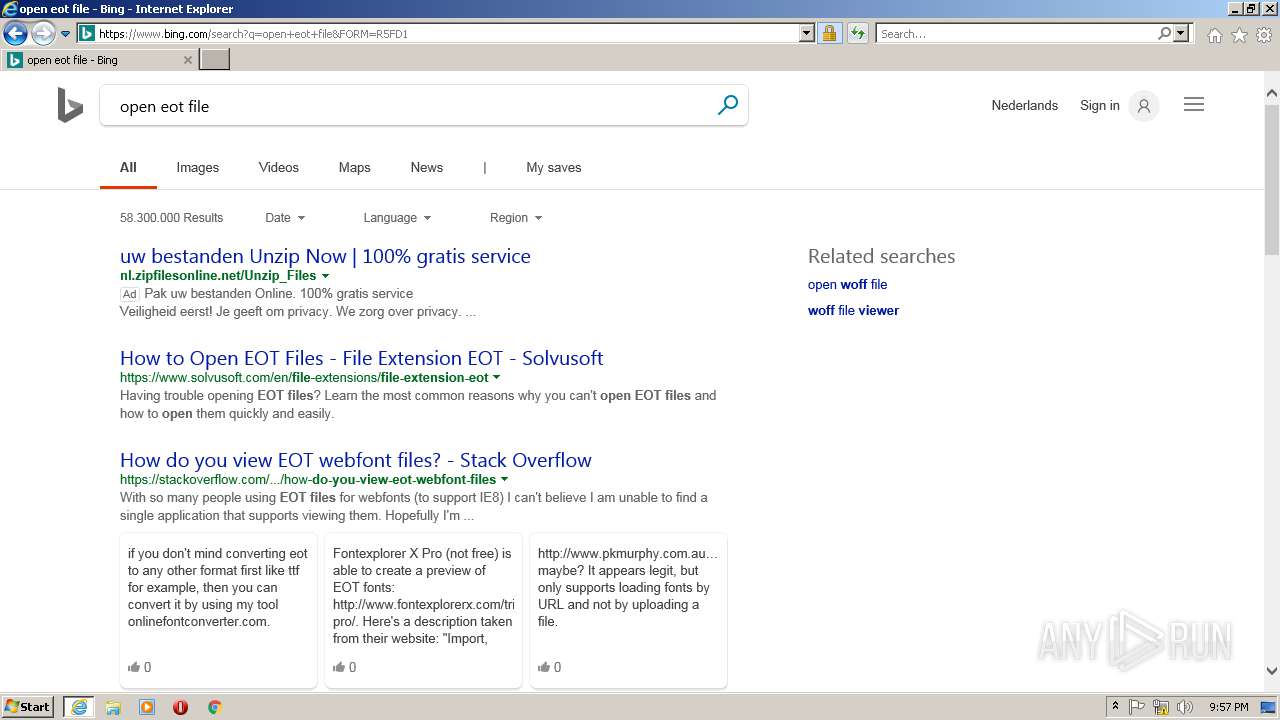
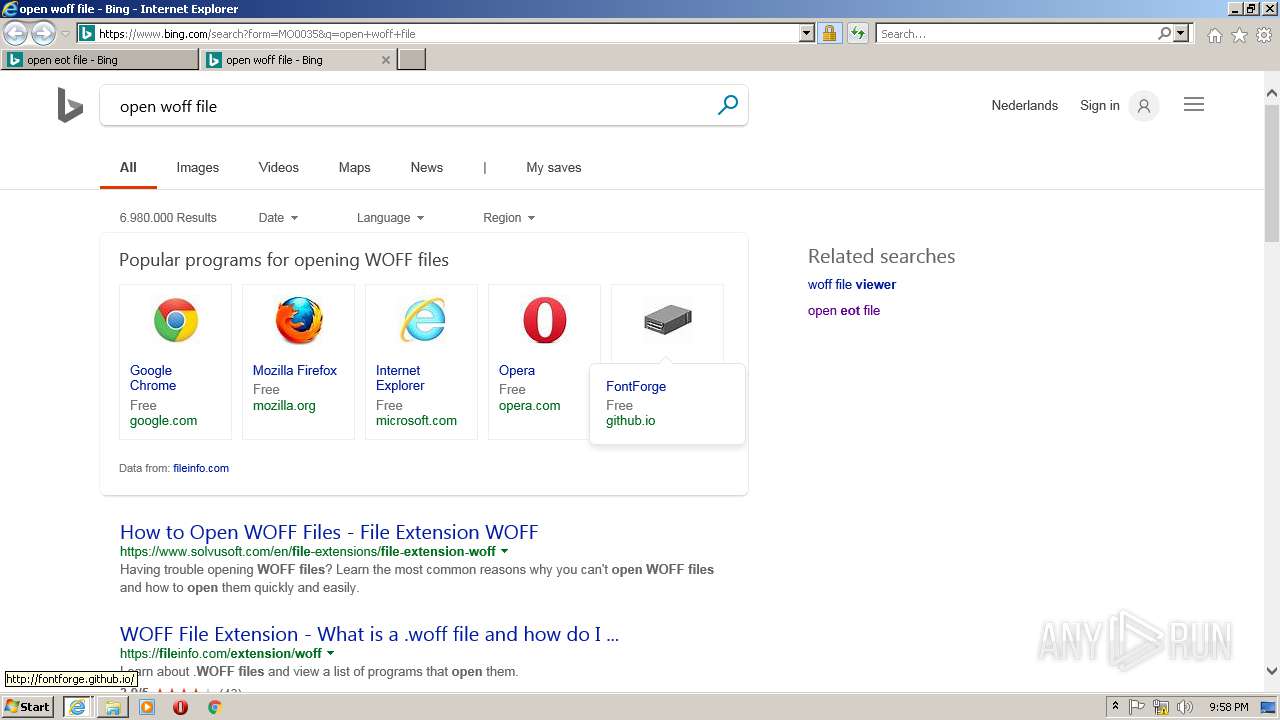
1260 | IEXPLORE.EXE | GET | 302 | 104.109.80.115:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=woff | NL | — | — | whitelisted |
1260 | IEXPLORE.EXE | GET | 301 | 2.18.213.33:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=woff | unknown | — | — | whitelisted |
1260 | IEXPLORE.EXE | GET | 200 | 204.79.197.200:443 | https://www.bing.com/fd/ls/l?IG=69526E9330A74D9DBAADD17DB6AF3381&CID=0311B58F1D976859311FB8931C5D695B&Type=Event.CPT&DATA={"pp":{"S":"L","FC":66,"BC":66,"SE":-1,"TC":-1,"H":89,"BP":1270,"CT":1287,"IL":13},"ad":[-1,-1,1264,621,1264,2424,0]}&P=SERP&DA=DUB02 | US | — | — | whitelisted |
1260 | IEXPLORE.EXE | GET | 200 | 204.79.197.200:443 | https://www.bing.com/sa/simg/SharedSpriteDesktopRewards_022118.png | US | image | 5.73 Kb | whitelisted |
1260 | IEXPLORE.EXE | GET | 200 | 204.79.197.200:443 | https://www.bing.com/rs/2Z/1X/cj,nj/4c7364c5/40e1b425.js | US | text | 1.53 Kb | whitelisted |
1260 | IEXPLORE.EXE | GET | 200 | 204.79.197.200:443 | https://www.bing.com/rb/15/cj,nj/1b7dfb88/cc8437ad.js?bu=DikuXGxwdGhgZKwBsAEuoAEu | US | text | 18.3 Kb | whitelisted |
1260 | IEXPLORE.EXE | GET | 200 | 204.79.197.200:443 | https://www.bing.com/rb/3R/ic/61505d92/25ddf288.png?bu=At4u4S4 | US | image | 190 b | whitelisted |
1260 | IEXPLORE.EXE | GET | 200 | 204.79.197.200:443 | https://www.bing.com/rs/6q/4T/cj,nj/347afee2/33036ea1.js | US | text | 3.93 Kb | whitelisted |
1260 | IEXPLORE.EXE | GET | 200 | 204.79.197.200:443 | https://www.bing.com/rs/5o/1af/cj,nj/a39998e4/6798a322.js | US | text | 544 b | whitelisted |
2108 | iexplore.exe | GET | 200 | 204.79.197.200:443 | https://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1260 | IEXPLORE.EXE | 104.109.80.115:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
1260 | IEXPLORE.EXE | 2.18.213.33:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
1260 | IEXPLORE.EXE | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2108 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2136 | IEXPLORE.EXE | 104.109.80.115:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
2136 | IEXPLORE.EXE | 2.18.213.33:80 | shell.windows.com | Akamai International B.V. | — | whitelisted |
2136 | IEXPLORE.EXE | 172.217.16.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2108 | iexplore.exe | 40.83.186.94:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
2136 | IEXPLORE.EXE | 216.58.214.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2136 | IEXPLORE.EXE | 172.217.18.66:443 | adservice.google.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
www2.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1260 | IEXPLORE.EXE | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
1260 | IEXPLORE.EXE | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2136 | IEXPLORE.EXE | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |