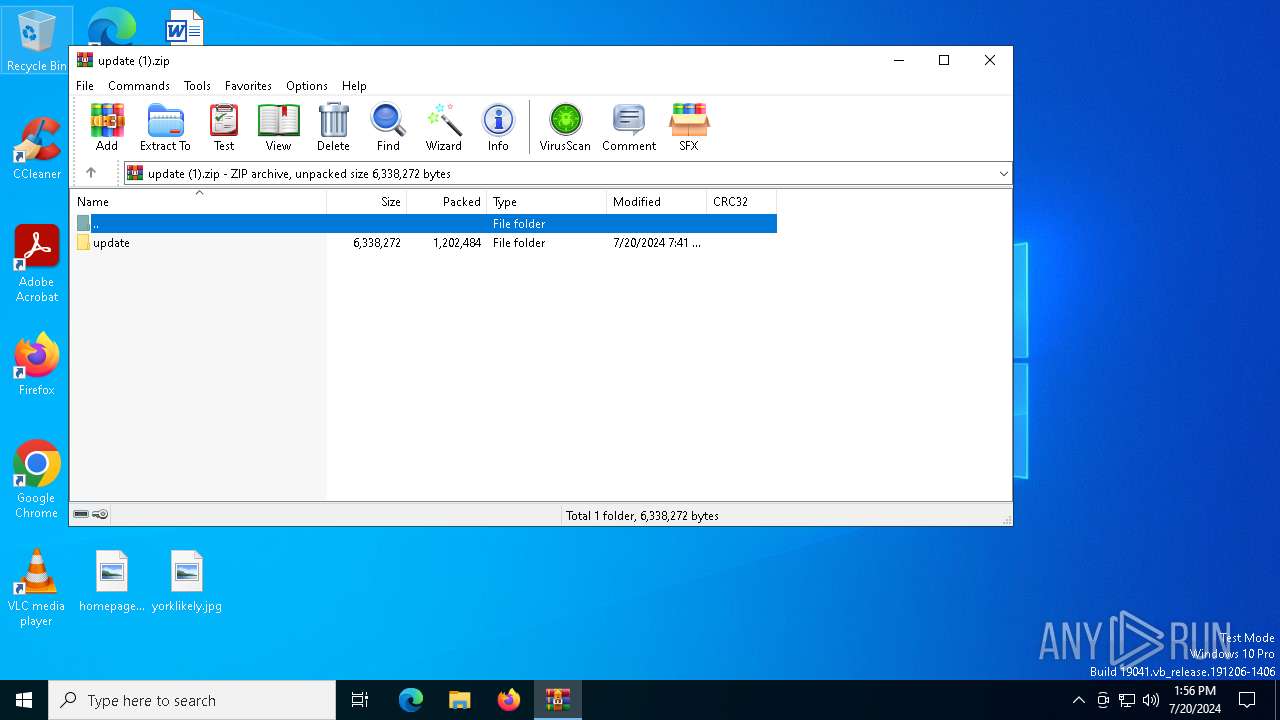
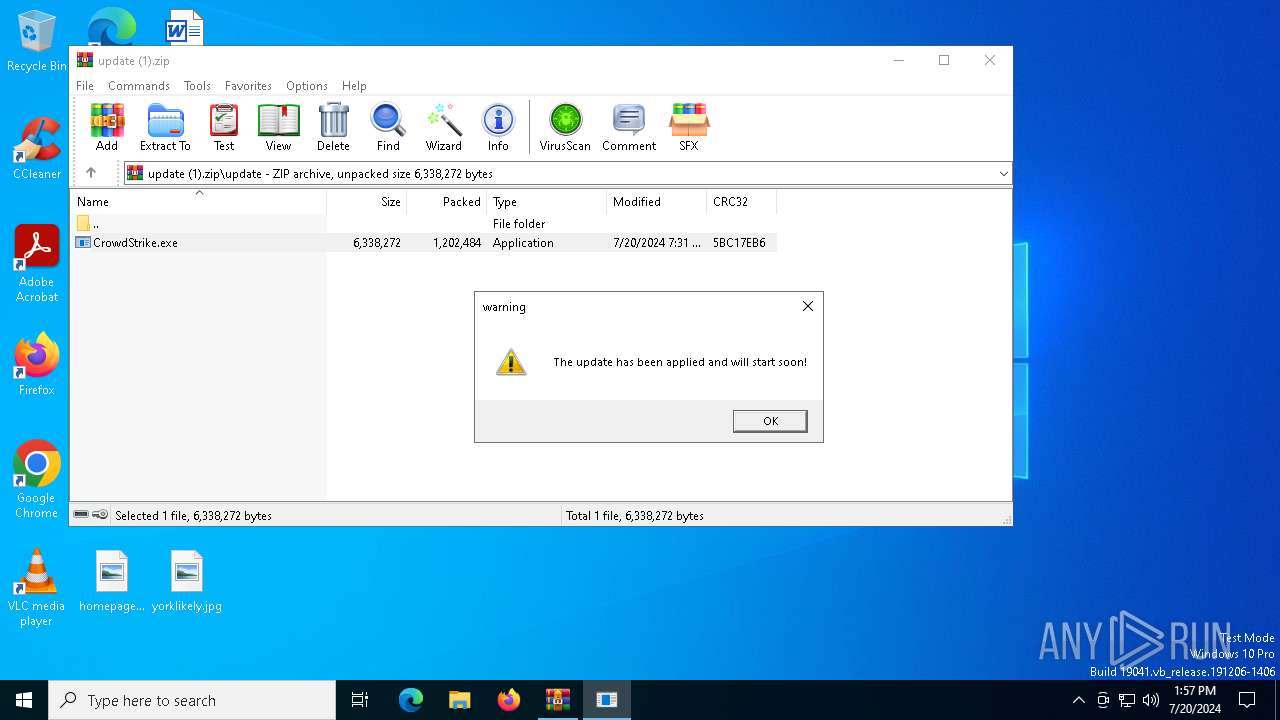
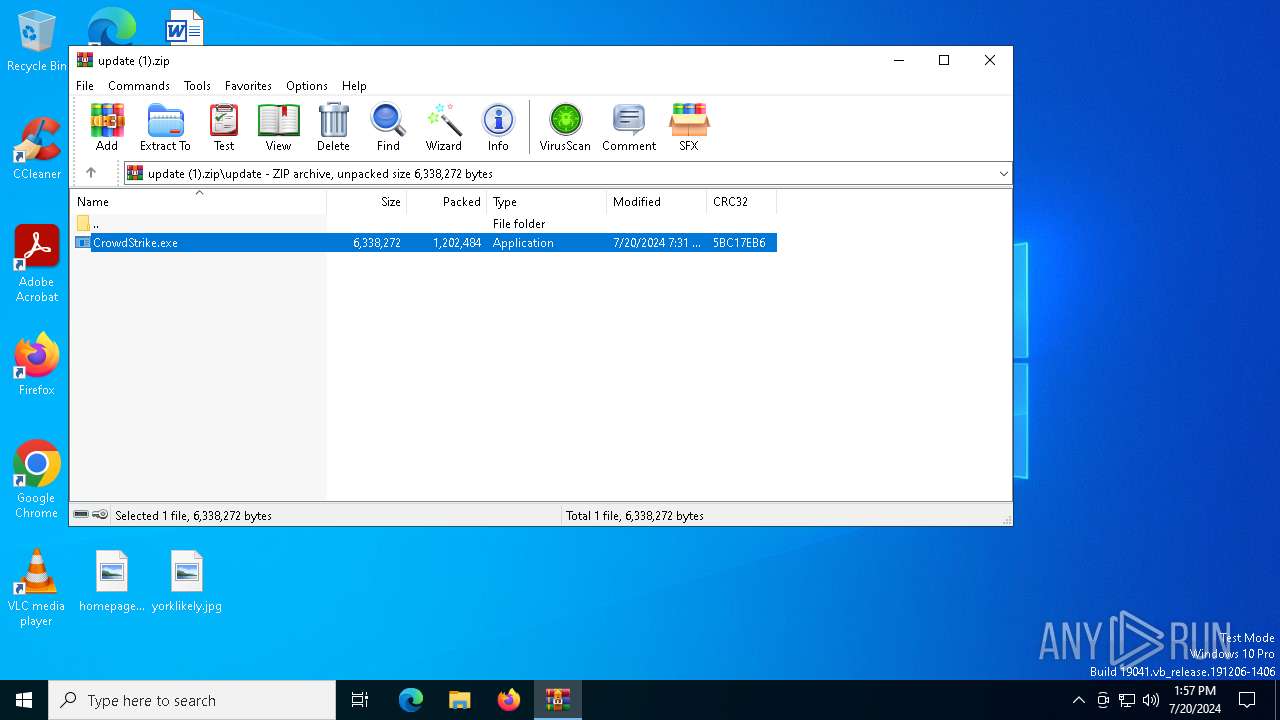
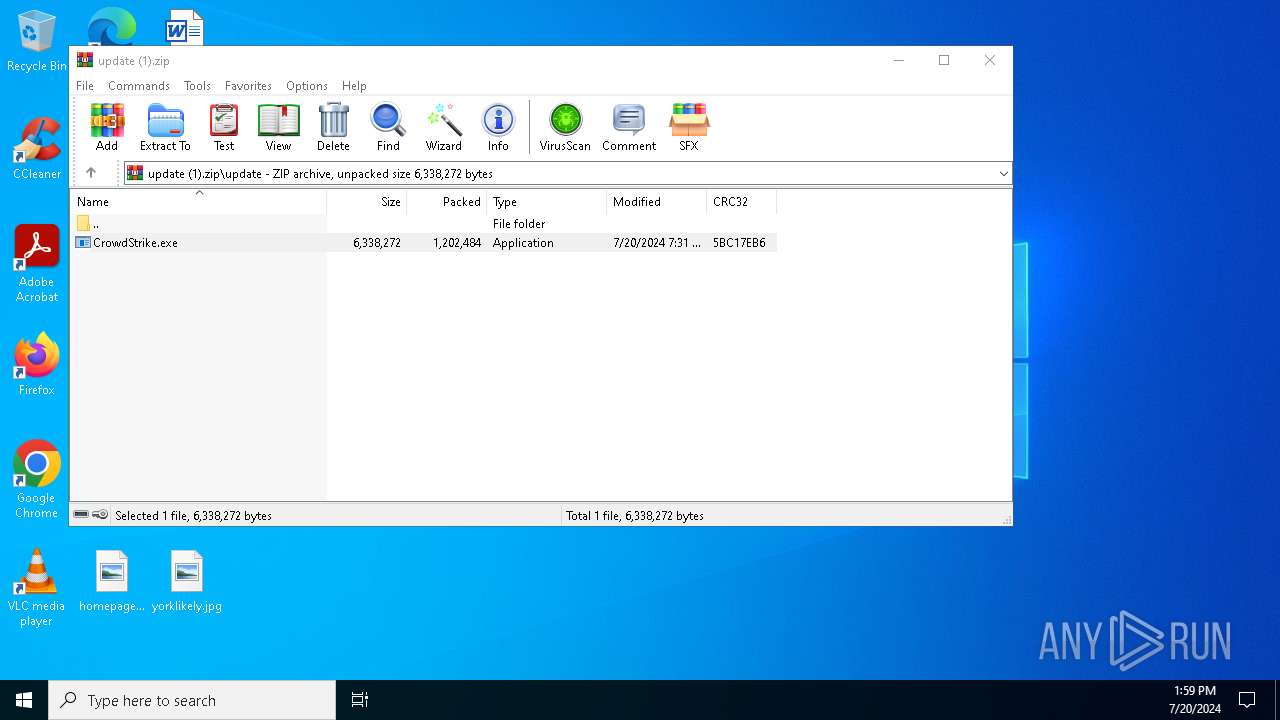
| File name: | update (1).zip |
| Full analysis: | https://app.any.run/tasks/b4d99af0-a433-45ab-8691-740dca9ae4ec |
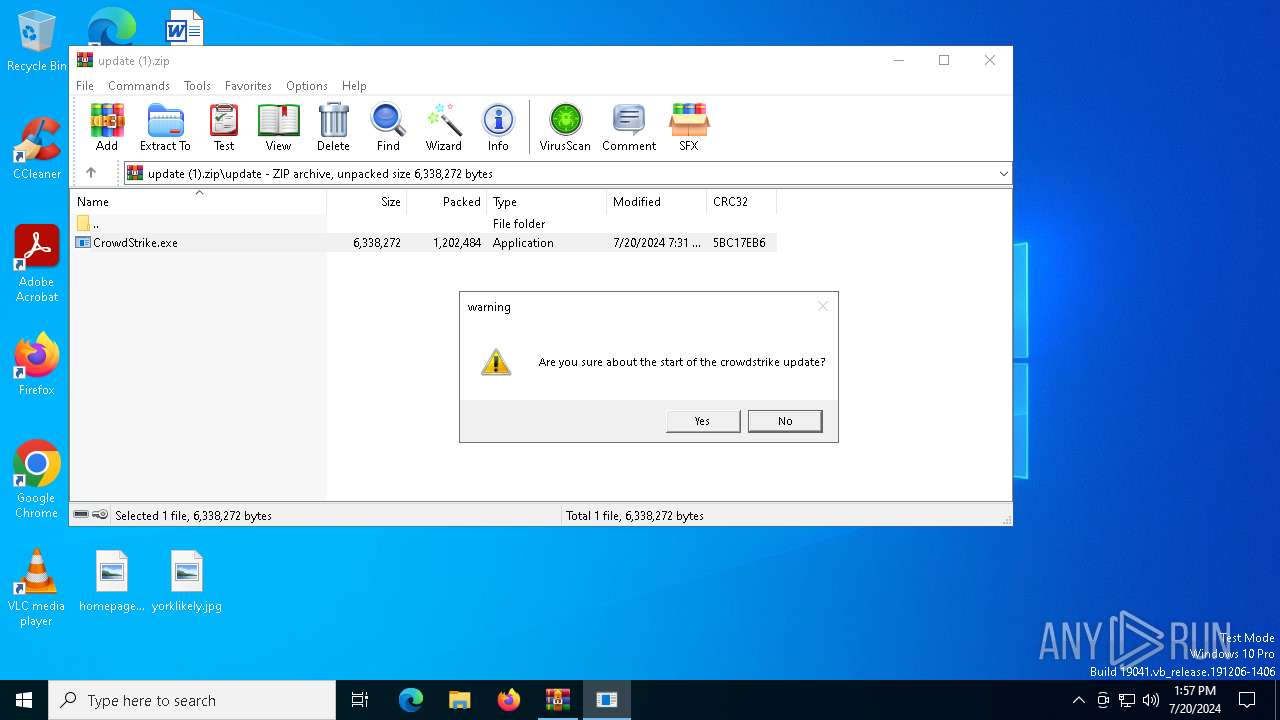
| Verdict: | Malicious activity |
| Analysis date: | July 20, 2024, 13:56:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | D32F89A8A3DD360DB3FA9B838163FFA0 |
| SHA1: | 66FBE2B33E545062A1399A4962B9AF4FBBD4B356 |
| SHA256: | 96DEC6E07229201A02F538310815C695CF6147C548FF1C6A0DEF2FE38F3DCBC8 |
| SSDEEP: | 49152:wFUG/KGKxVTQ8WqwjrFkiV4sKPGsECGu32l6PB6IVhvCT93emKGjBcAgAm/3Gbk5:wFUG/STQ8Wqw/FkiJKexu3igZv6jBcAY |
MALICIOUS
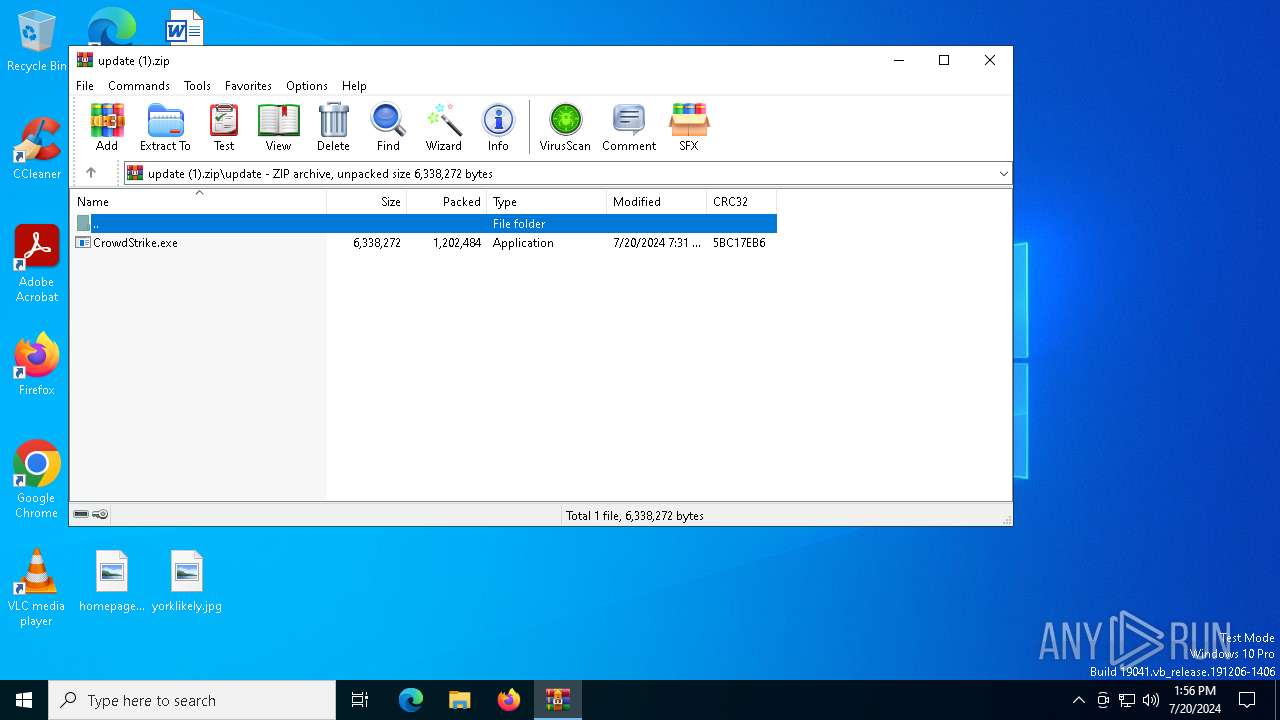
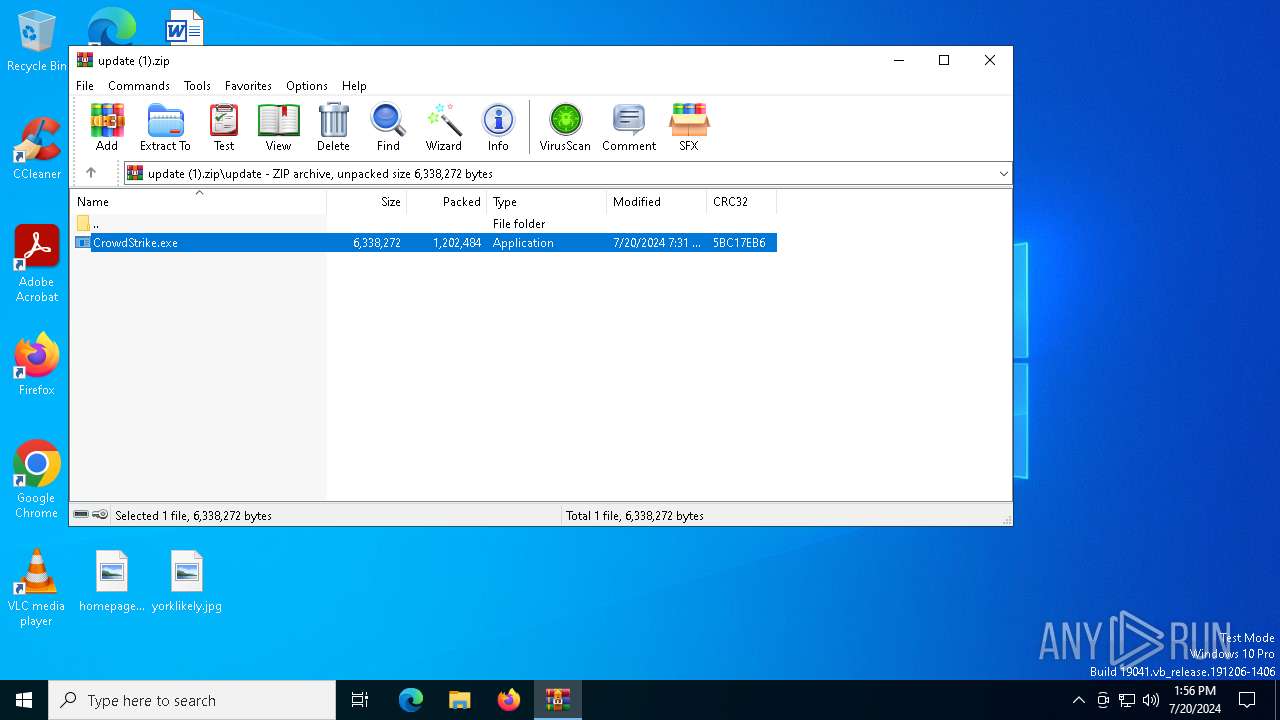
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3800)
- CrowdStrike.exe (PID: 7440)
- cmd.exe (PID: 5936)
- RegAsm.exe (PID: 7092)
- Champion.pif (PID: 6944)
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 3836)
- findstr.exe (PID: 7416)
- findstr.exe (PID: 5460)
- findstr.exe (PID: 7352)
Create files in the Startup directory
- RegAsm.exe (PID: 7092)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 7092)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3800)
- CrowdStrike.exe (PID: 7440)
- Champion.pif (PID: 7016)
- CrowdStrike.exe (PID: 4972)
- GameBar.exe (PID: 3360)
- StartMenuExperienceHost.exe (PID: 5720)
Reads the date of Windows installation
- CrowdStrike.exe (PID: 7440)
- Champion.pif (PID: 7016)
- CrowdStrike.exe (PID: 4972)
- StartMenuExperienceHost.exe (PID: 5720)
Executing commands from ".cmd" file
- CrowdStrike.exe (PID: 7440)
- CrowdStrike.exe (PID: 4972)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5936)
- cmd.exe (PID: 5856)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5936)
- CrowdStrike.exe (PID: 7440)
- Champion.pif (PID: 7016)
- CrowdStrike.exe (PID: 4972)
- cmd.exe (PID: 5856)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 5936)
Application launched itself
- cmd.exe (PID: 5936)
- cmd.exe (PID: 5856)
Executable content was dropped or overwritten
- cmd.exe (PID: 5936)
- RegAsm.exe (PID: 7092)
- Champion.pif (PID: 6944)
Get information on the list of running processes
- cmd.exe (PID: 5936)
- cmd.exe (PID: 5856)
Suspicious file concatenation
- cmd.exe (PID: 7236)
- cmd.exe (PID: 2928)
Starts application with an unusual extension
- cmd.exe (PID: 5936)
- cmd.exe (PID: 5856)
The executable file from the user directory is run by the CMD process
- Champion.pif (PID: 7016)
- CrowdStrike.exe (PID: 4972)
- Champion.pif (PID: 6944)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5936)
- cmd.exe (PID: 5856)
Process drops legitimate windows executable
- Champion.pif (PID: 6944)
Starts a Microsoft application from unusual location
- RegAsm.exe (PID: 6984)
- RegAsm.exe (PID: 7092)
Drops a system driver (possible attempt to evade defenses)
- RegAsm.exe (PID: 7092)
Checks for external IP
- RegAsm.exe (PID: 7092)
Creates file in the systems drive root
- RegAsm.exe (PID: 7092)
Write to the desktop.ini file (may be used to cloak folders)
- RegAsm.exe (PID: 7092)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- RegAsm.exe (PID: 7092)
The process creates files with name similar to system file names
- WerFault.exe (PID: 1764)
- Champion.pif (PID: 6944)
Executes application which crashes
- GameBar.exe (PID: 3360)
- RegAsm.exe (PID: 7092)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3800)
Checks supported languages
- CrowdStrike.exe (PID: 7440)
- Champion.pif (PID: 7016)
- CrowdStrike.exe (PID: 4972)
- Champion.pif (PID: 6944)
- RegAsm.exe (PID: 7092)
- GameBar.exe (PID: 3360)
- TextInputHost.exe (PID: 8000)
- StartMenuExperienceHost.exe (PID: 5720)
- SearchApp.exe (PID: 7020)
Create files in a temporary directory
- CrowdStrike.exe (PID: 7440)
- CrowdStrike.exe (PID: 4972)
- Champion.pif (PID: 6944)
- RegAsm.exe (PID: 7092)
Reads the computer name
- CrowdStrike.exe (PID: 7440)
- Champion.pif (PID: 7016)
- CrowdStrike.exe (PID: 4972)
- RegAsm.exe (PID: 7092)
- GameBar.exe (PID: 3360)
- TextInputHost.exe (PID: 8000)
- StartMenuExperienceHost.exe (PID: 5720)
- SearchApp.exe (PID: 7020)
- Champion.pif (PID: 6944)
Process checks computer location settings
- CrowdStrike.exe (PID: 7440)
- Champion.pif (PID: 7016)
- CrowdStrike.exe (PID: 4972)
- StartMenuExperienceHost.exe (PID: 5720)
- SearchApp.exe (PID: 7020)
Reads mouse settings
- Champion.pif (PID: 7016)
- Champion.pif (PID: 6944)
Disables trace logs
- RegAsm.exe (PID: 7092)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 7092)
- SearchApp.exe (PID: 7020)
Checks proxy server information
- RegAsm.exe (PID: 7092)
- SearchApp.exe (PID: 7020)
Reads Environment values
- RegAsm.exe (PID: 7092)
- SearchApp.exe (PID: 7020)
Reads the software policy settings
- RegAsm.exe (PID: 7092)
- SearchApp.exe (PID: 7020)
Attempting to use instant messaging service
- RegAsm.exe (PID: 7092)
Manual execution by a user
- WerFault.exe (PID: 1764)
Creates files or folders in the user directory
- WerFault.exe (PID: 1764)
- GameBar.exe (PID: 3360)
- WerFault.exe (PID: 7432)
Process checks Internet Explorer phishing filters
- SearchApp.exe (PID: 7020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:07:20 11:11:18 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | update/ |
Total processes
204
Monitored processes
40
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 852 | timeout 15 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | C:\WINDOWS\system32\WerFault.exe -u -p 4016 -s 3804 | C:\Windows\System32\WerFault.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2436 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2928 | cmd /c copy /b Treating + Viagra + Vision + Jul + Str 564784\L | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3360 | findstr /V "locatedflatrendsoperating" Ukraine | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3360 | "C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe" -ServerName:App.AppXbdkk0yrkwpcgeaem8zk81k8py1eaahny.mca | C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226107 Modules
| |||||||||||||||
| 3396 | timeout 15 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3544 | cmd /c md 564784 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3800 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\update (1).zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
37 134
Read events
37 030
Write events
102
Delete events
2
Modification events
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\update (1).zip | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3800) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
7
Suspicious files
1 093
Text files
140
Unknown types
69
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7440 | CrowdStrike.exe | C:\Users\admin\AppData\Local\Temp\Democracy | binary | |
MD5:DEE42E543988CD988E8AEB4B03F488EB | SHA256:8F444581168196C045FABDE65F1C0667154AFE2FE6302E7FF342AEFD3B6B829D | |||
| 7440 | CrowdStrike.exe | C:\Users\admin\AppData\Local\Temp\Halo | binary | |
MD5:E859420711C0FAFFEDF33DA17A2EB4B1 | SHA256:5010762DC34EB3679AFE29CDA9C2040309D8A784BEA758F64ED4977773C20465 | |||
| 7440 | CrowdStrike.exe | C:\Users\admin\AppData\Local\Temp\Develops | binary | |
MD5:6DB6B2AE5BAAE977FAE168E4A08641B4 | SHA256:88C137E5726172061F509246ADA7D2D3CB8E5DABCF35CADF1D49C49B073A80A4 | |||
| 3800 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3800.10302\update\CrowdStrike.exe | executable | |
MD5:755C0350038DAEFB29B888B6F8739E81 | SHA256:4491901EFF338AB52C85A77A3FBD3CE80FDA738046EE3B7DA7BE468DA5B331A3 | |||
| 7440 | CrowdStrike.exe | C:\Users\admin\AppData\Local\Temp\Wave | binary | |
MD5:E27F5F4215920D7C0DB01D3A07E32FAD | SHA256:C5A836D0021A235D4FC30764DFD4A2ABB33B23CA25F4DCA4A9BA7A8423F7753E | |||
| 7440 | CrowdStrike.exe | C:\Users\admin\AppData\Local\Temp\Ferry | binary | |
MD5:05607FDAAA89639249B09951F5624870 | SHA256:11BDE3AF35BD166FEA20604167525CC28A2EB2FD0BC66B054C190AF00447F50C | |||
| 7440 | CrowdStrike.exe | C:\Users\admin\AppData\Local\Temp\Recipes | binary | |
MD5:D0808D4907E66F73A821AB6E7FC942C1 | SHA256:221EEE5A84FDE75849816CDBB84F723E5C96A3E81922692DB21E7844B8537A04 | |||
| 7440 | CrowdStrike.exe | C:\Users\admin\AppData\Local\Temp\Handle | binary | |
MD5:4DD2539DAA375331505B81E8BAD6F6F3 | SHA256:2FA5DFE0785E6E2EE3CF30277E09BDB46D2B7FC096D40D6AAF78EC27F5B6B68B | |||
| 7440 | CrowdStrike.exe | C:\Users\admin\AppData\Local\Temp\Moreover | binary | |
MD5:F335E743D9A5D72A068210A9C9F605E3 | SHA256:E5DC3C6C185C46FB75C682327750A542D0A84F7C17CAA39469755EADEEF37BA7 | |||
| 7440 | CrowdStrike.exe | C:\Users\admin\AppData\Local\Temp\Consequences | pgc | |
MD5:19E98CBB75F1B8BD8EFDE5FE0ABD34B2 | SHA256:DF0CB092CD377DF6571BB86BB48E586E1A5012EDBE1C8A180DE8BE3FAE080356 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
46
DNS requests
18
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7092 | RegAsm.exe | GET | 200 | 104.16.185.241:80 | http://icanhazip.com/ | unknown | — | — | shared |
7092 | RegAsm.exe | GET | 200 | 104.16.184.241:80 | http://icanhazip.com/ | unknown | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7856 | svchost.exe | 4.209.32.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4716 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5620 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2760 | svchost.exe | 40.115.3.253:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5672 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4716 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6256 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
XLuvBdVPcngNKMPfoEAAuT.XLuvBdVPcngNKMPfoEAAuT |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7092 | RegAsm.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
2168 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
7092 | RegAsm.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
2168 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7092 | RegAsm.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
7092 | RegAsm.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
7092 | RegAsm.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
2168 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
7092 | RegAsm.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |