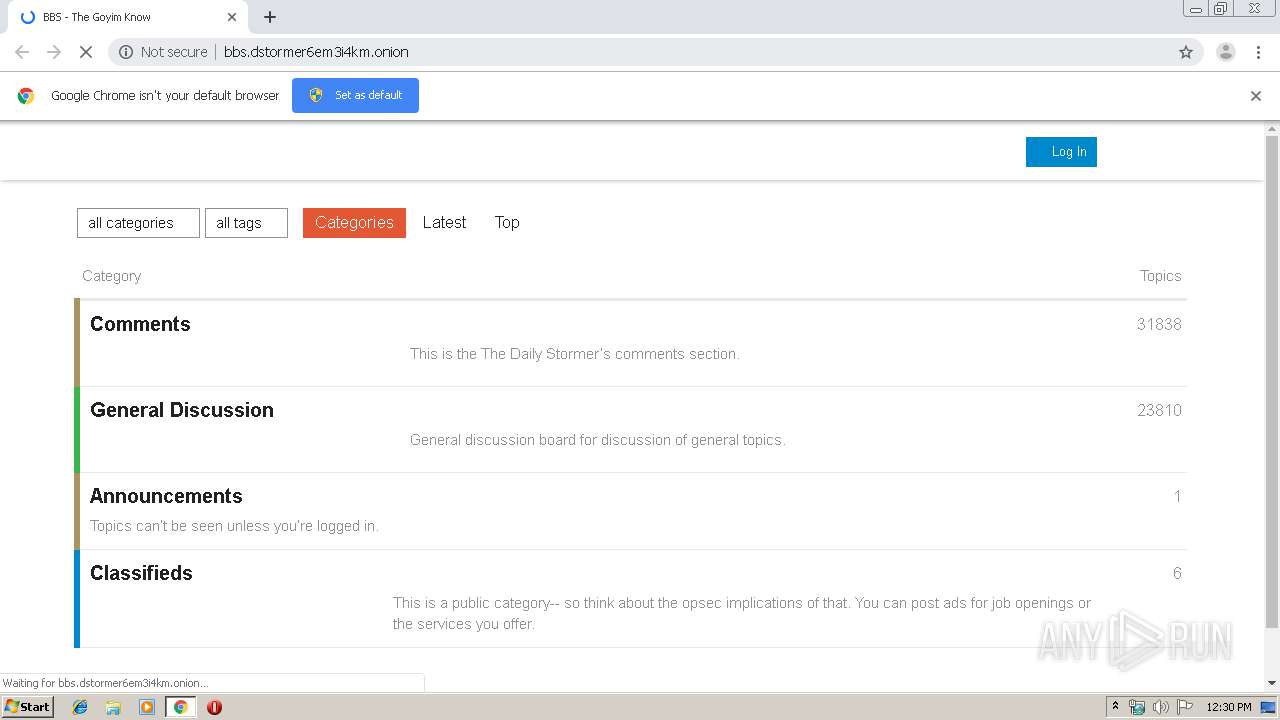
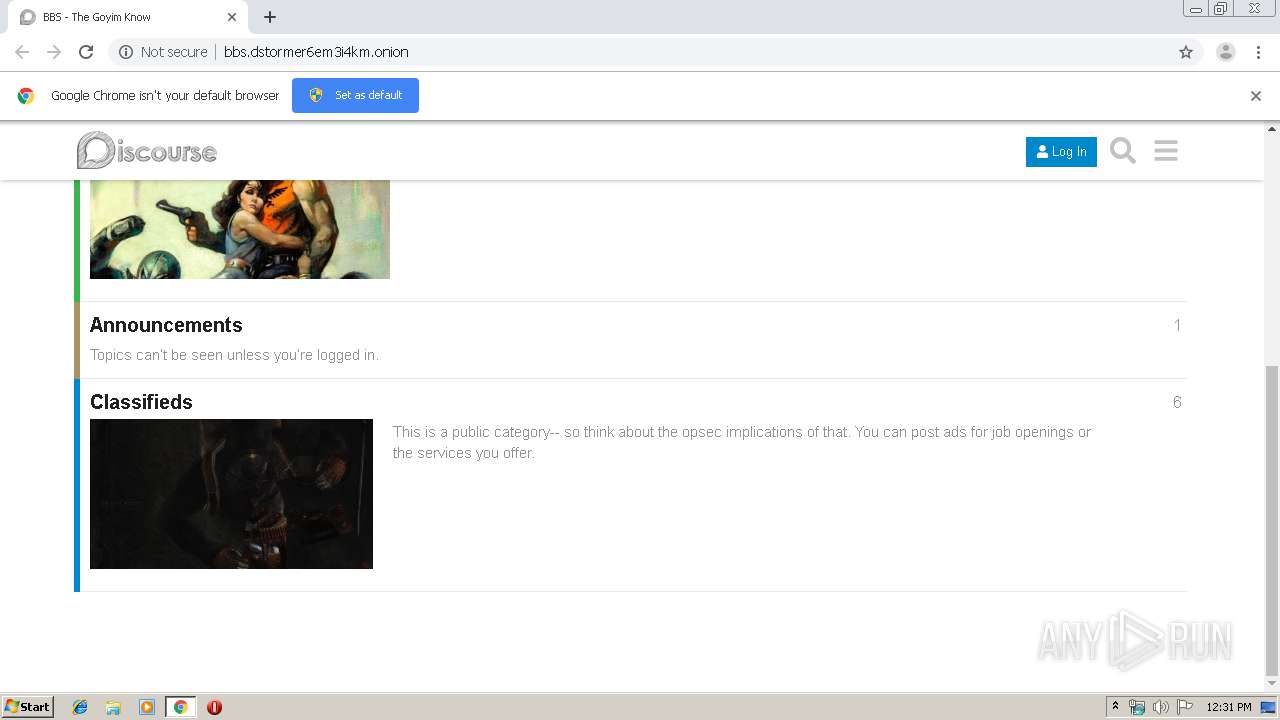
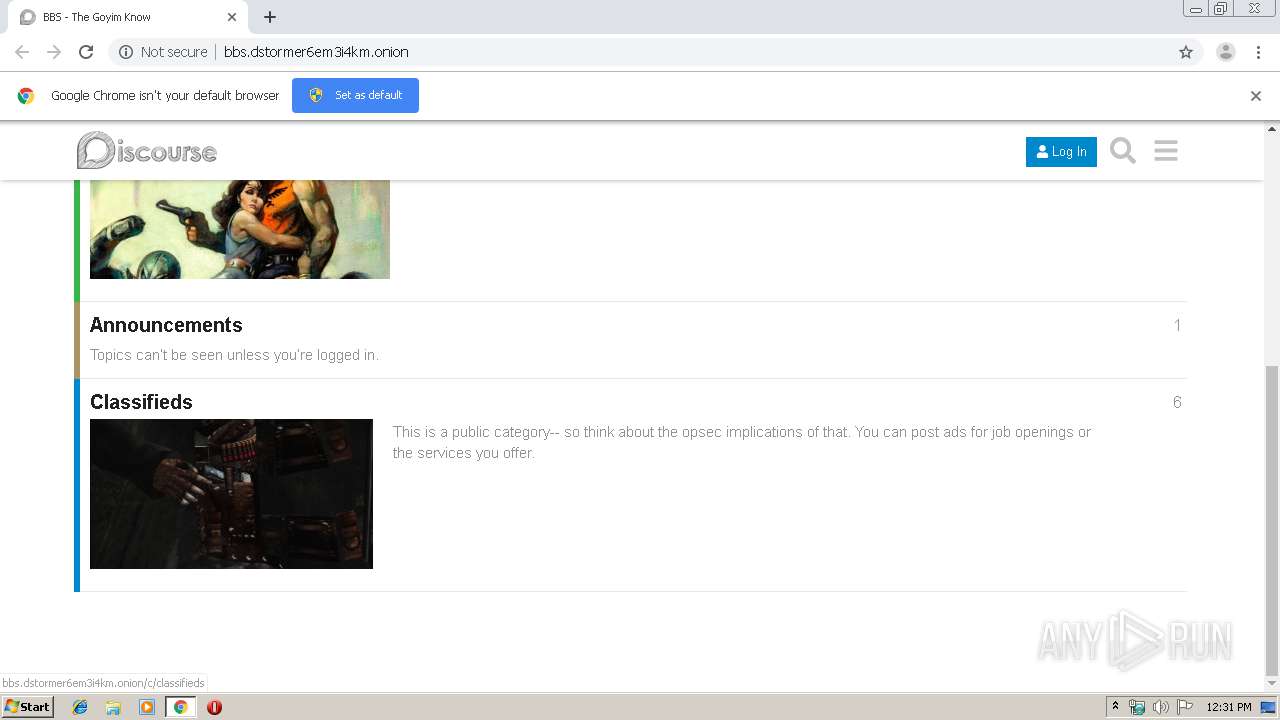
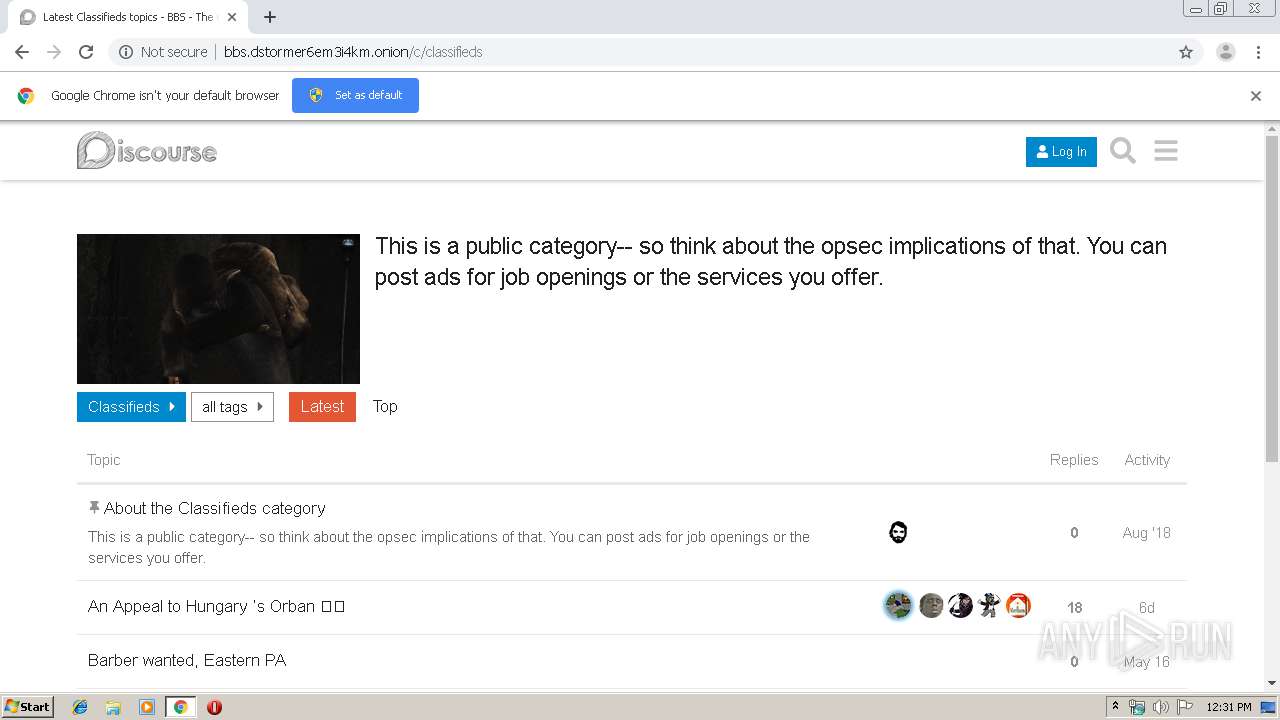
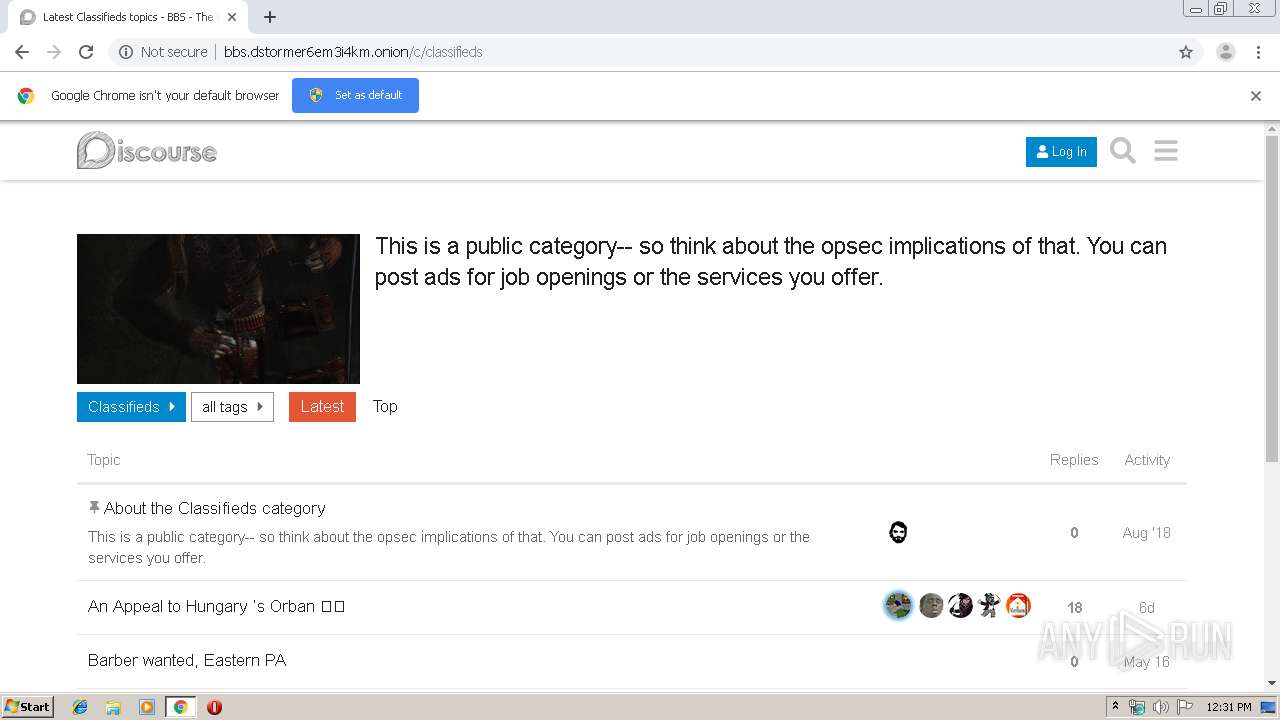
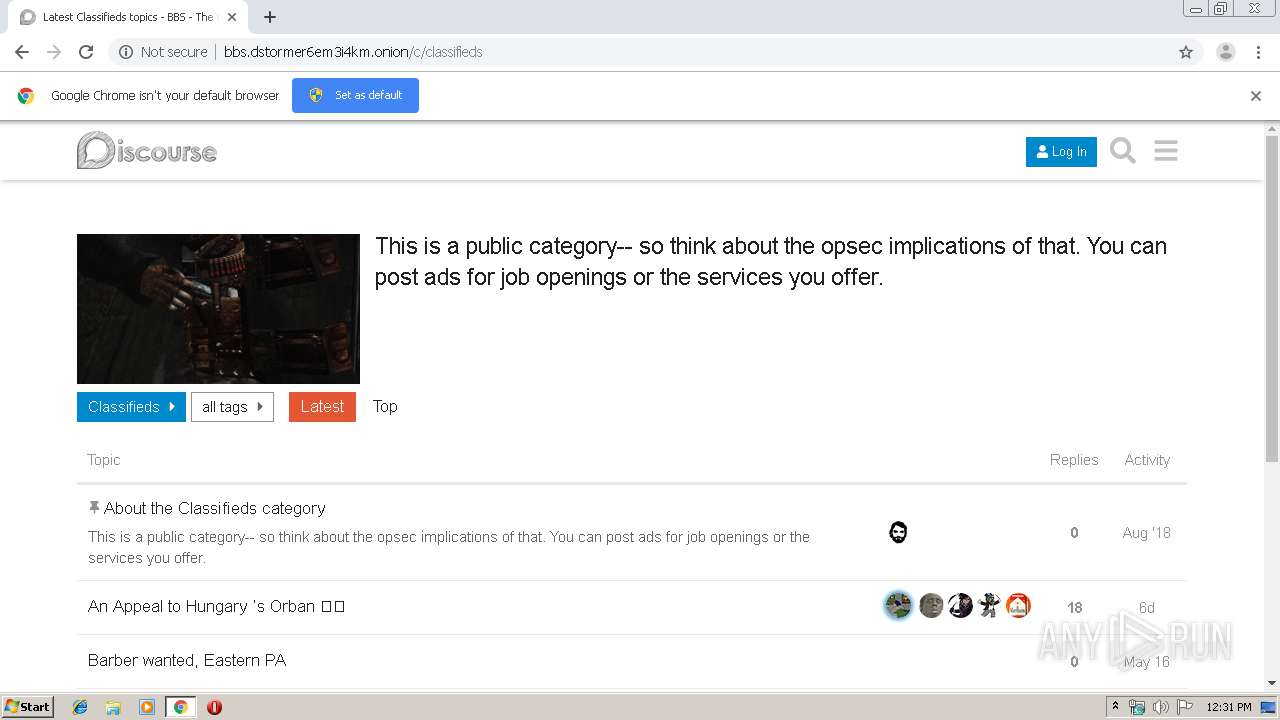
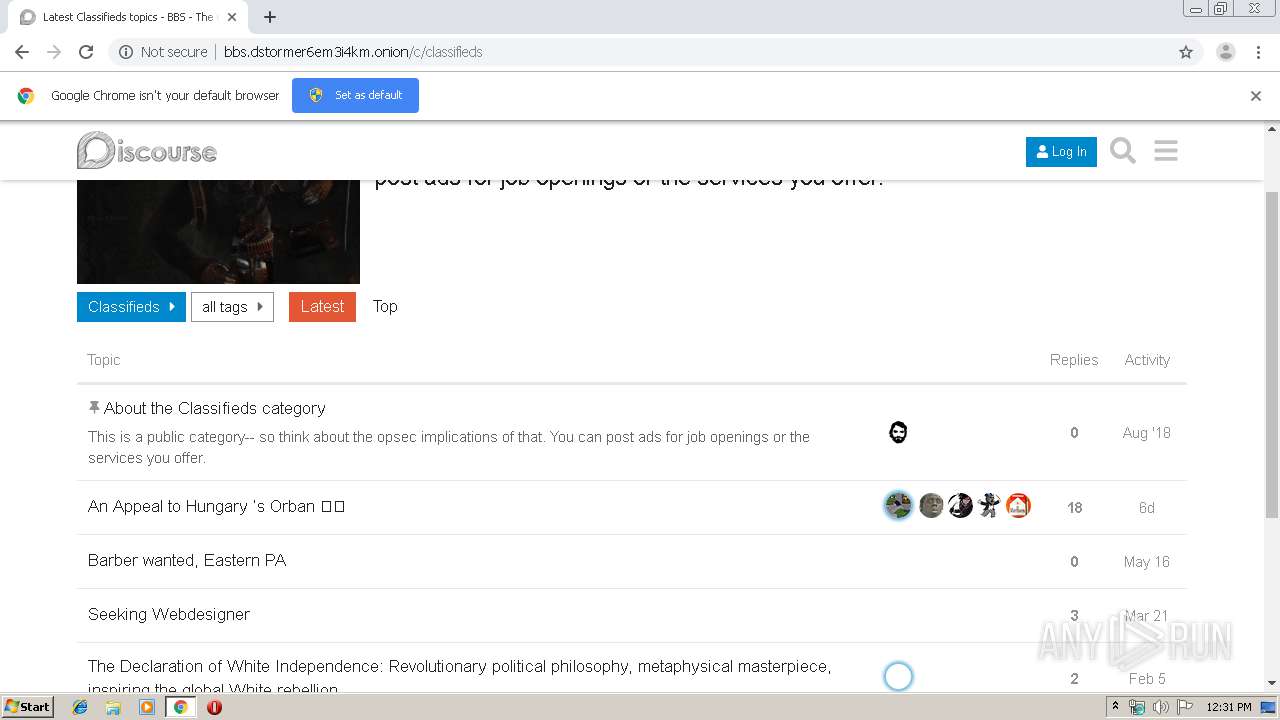
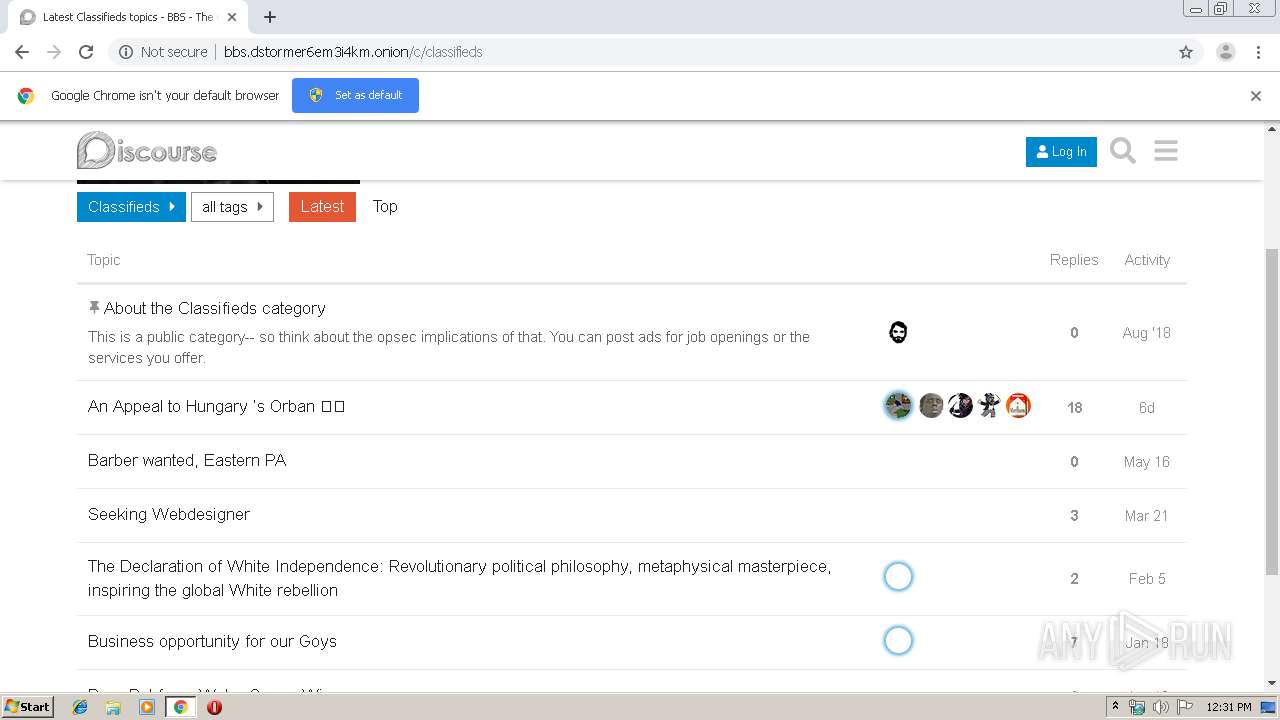
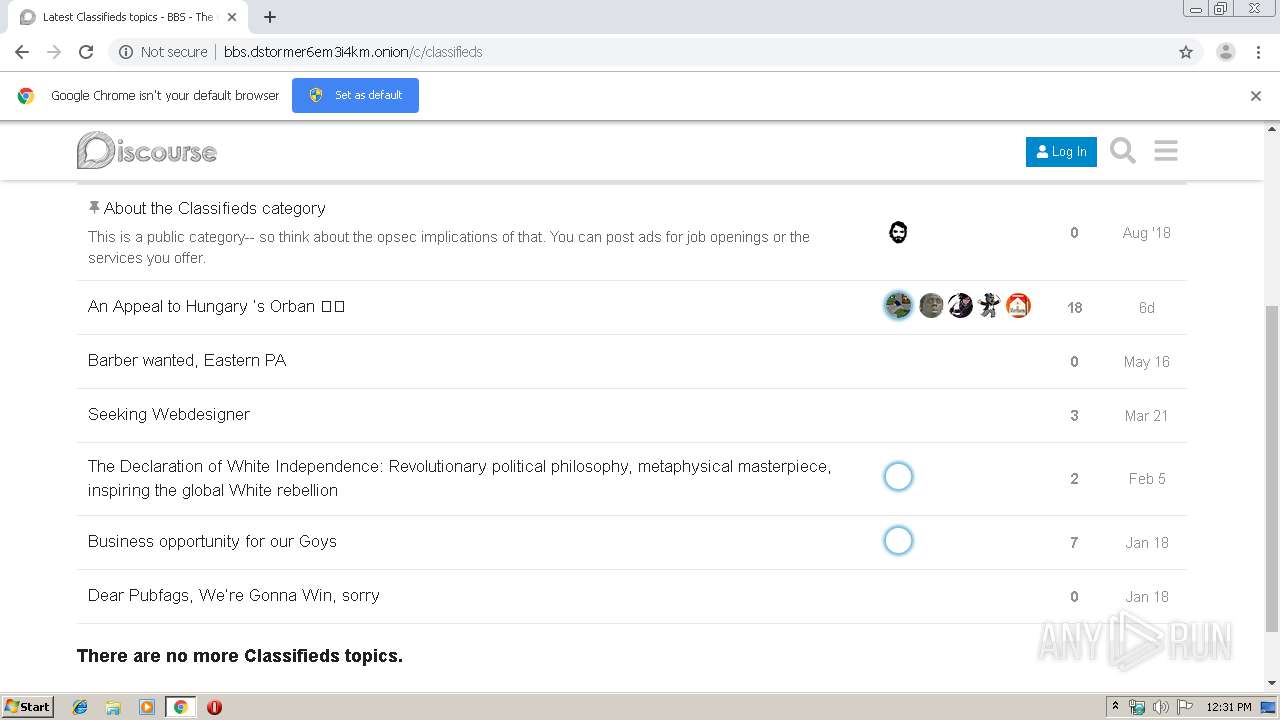
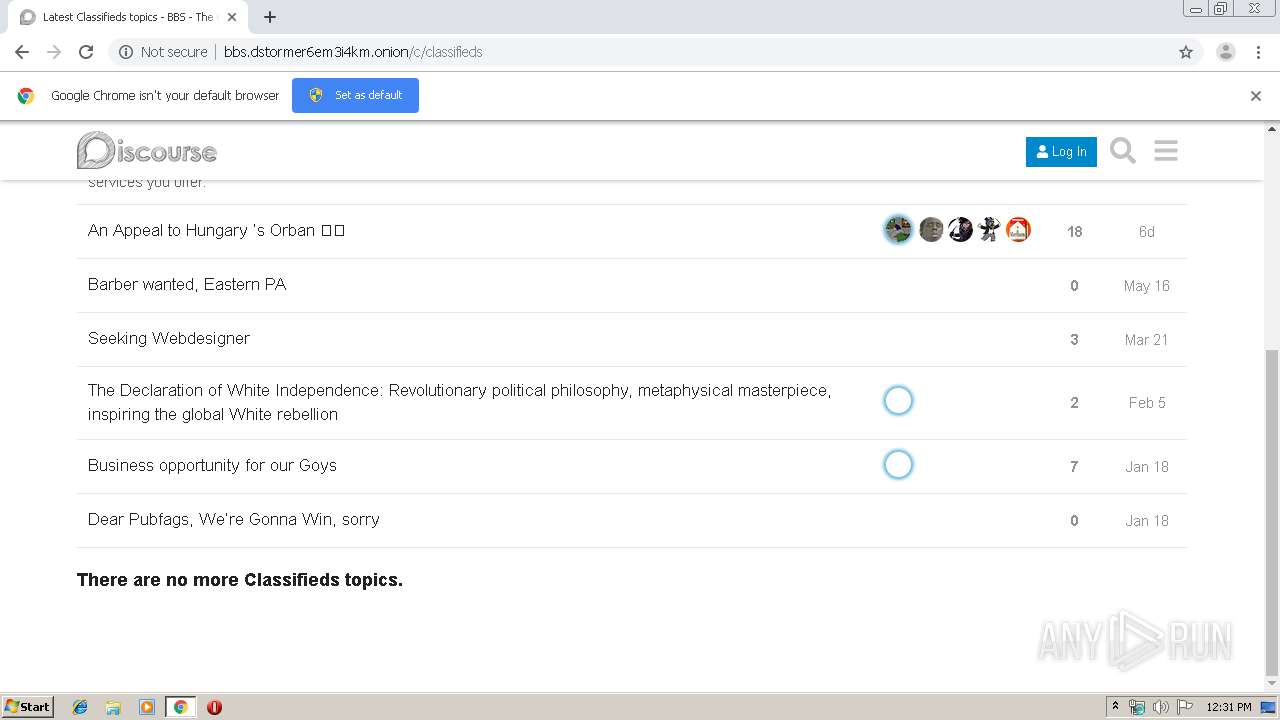
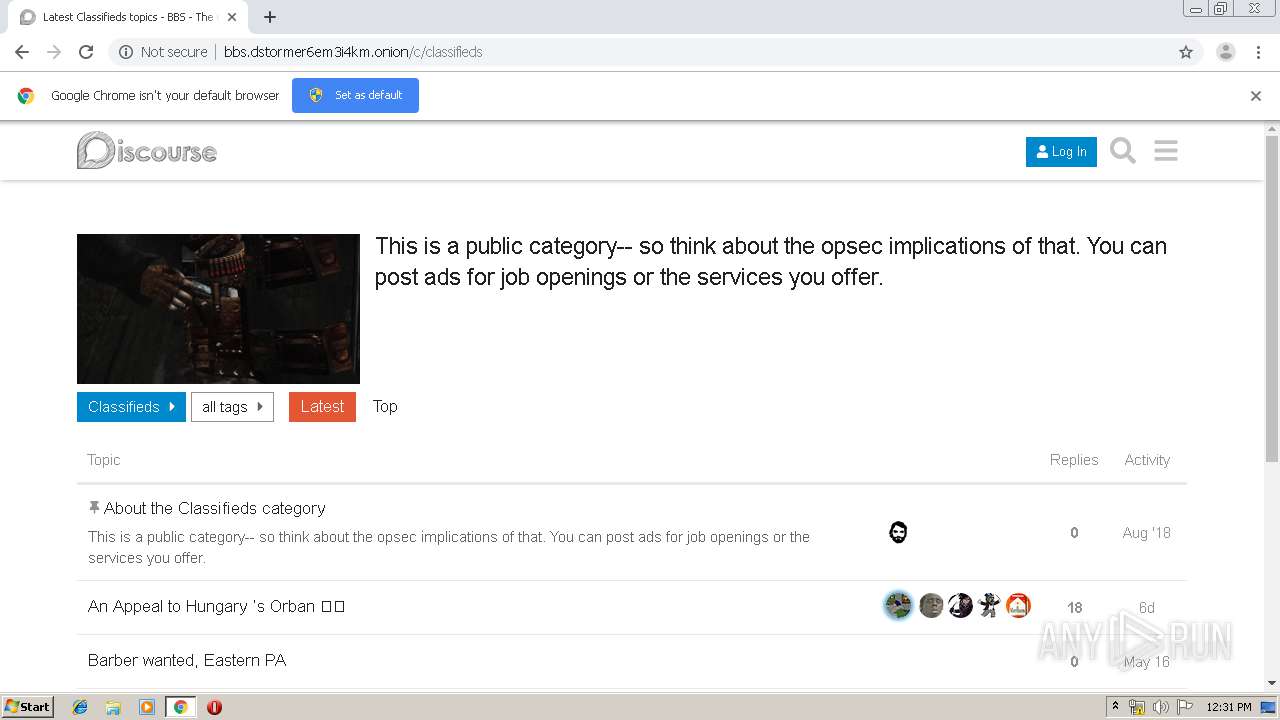
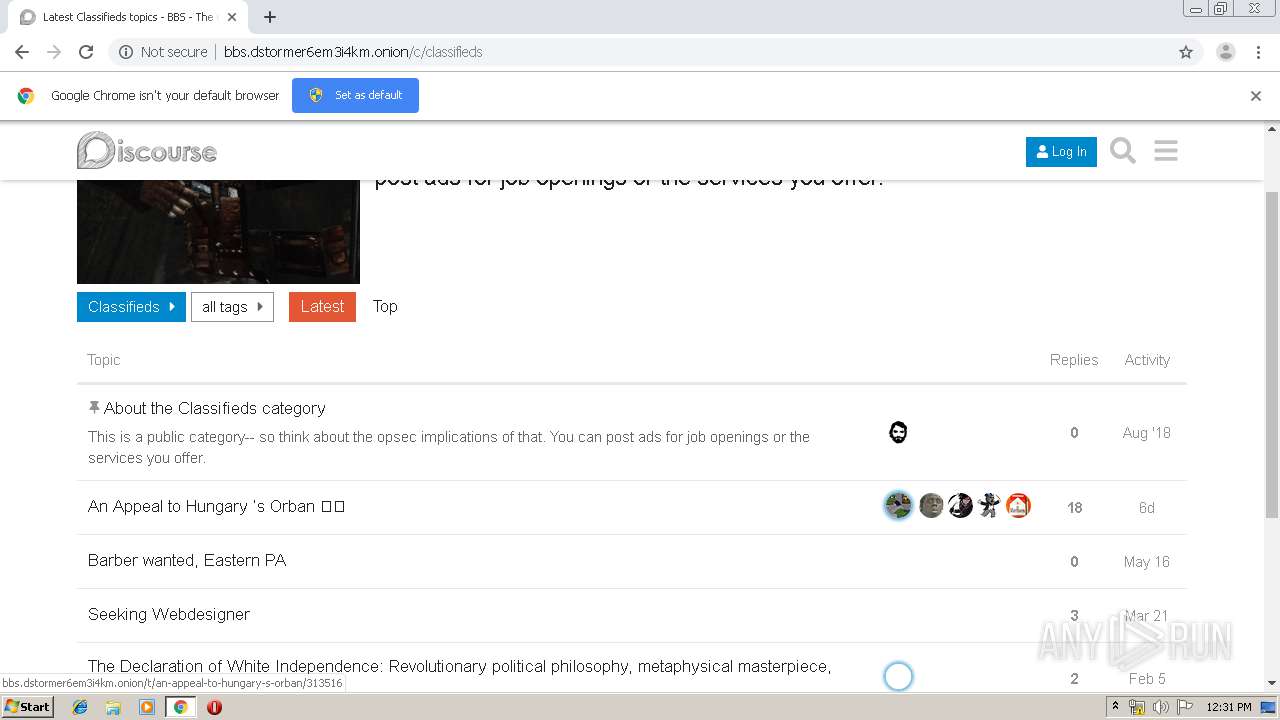
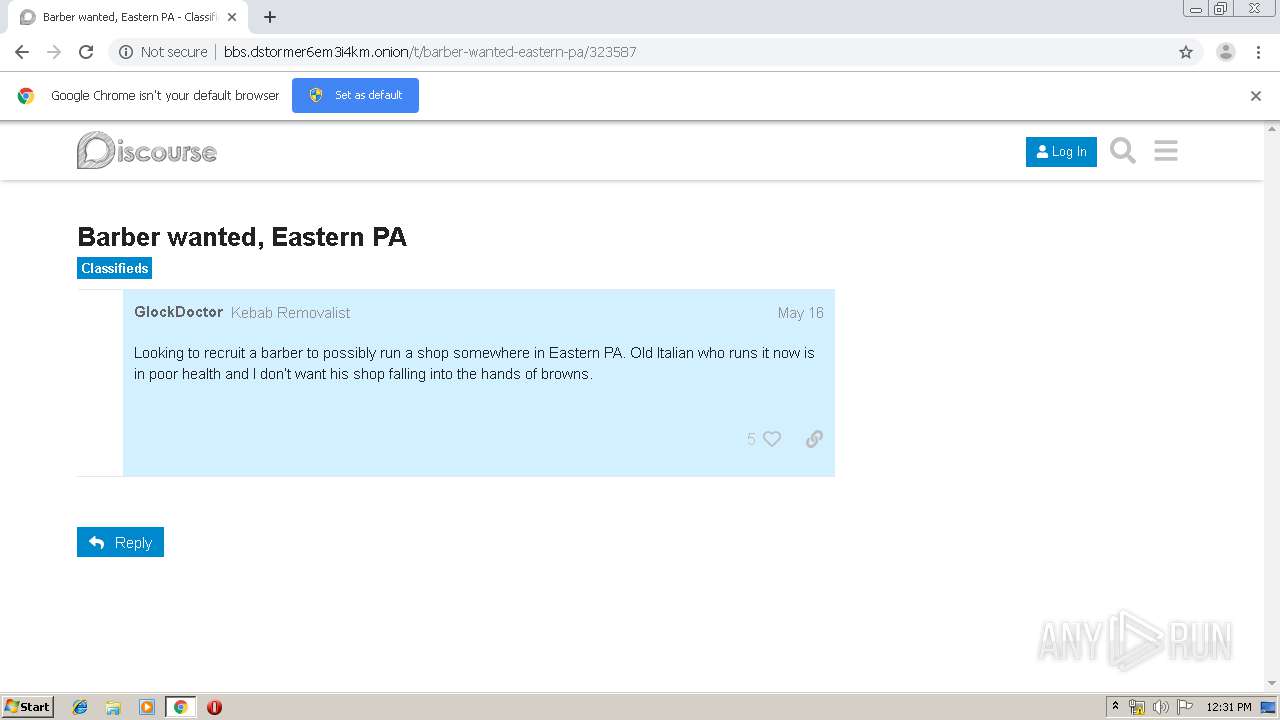
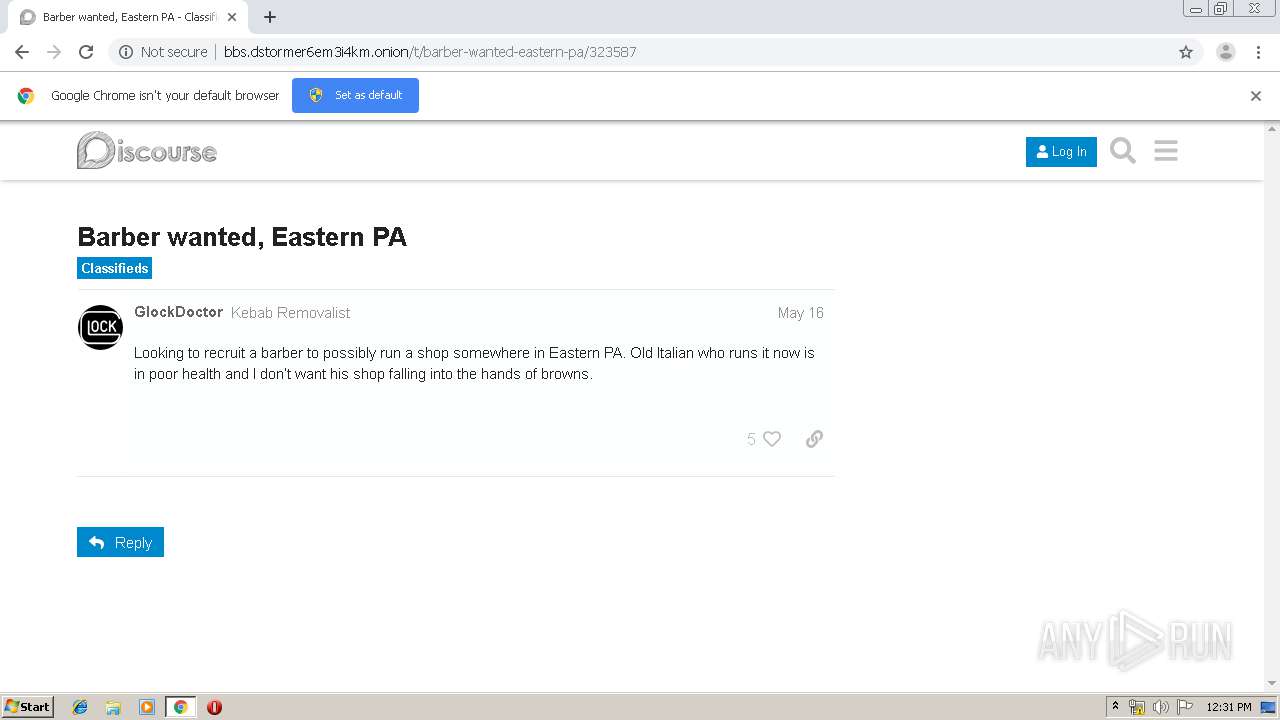
| URL: | http://bbs.dstormer6em3i4km.onion |
| Full analysis: | https://app.any.run/tasks/93556833-be9d-428d-86cd-fc618227aa66 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 11:30:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6B922AAF5A17B4B26F45C3D2AE9D6E56 |
| SHA1: | 8994EFB140FA875F2BE6C4A94CEC64CC5289C795 |
| SHA256: | 96CC8541952F386C7D5C223DE557EFA678A284FD9ACF37F4E57C40B20AC17B76 |
| SSDEEP: | 3:N1Kcsb1JLo5/n:Cc2JLoVn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2856)
INFO
Dropped object may contain TOR URL's
- chrome.exe (PID: 2856)
Application launched itself
- chrome.exe (PID: 2856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
21
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,11864090080286723051,11672762299058635630,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12938032712755219157 --mojo-platform-channel-handle=3304 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,11864090080286723051,11672762299058635630,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15248454424026077416 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,11864090080286723051,11672762299058635630,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3943579474317787402 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11864090080286723051,11672762299058635630,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3793631937982912845 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3688 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,11864090080286723051,11672762299058635630,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14377174906890432236 --mojo-platform-channel-handle=2884 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,11864090080286723051,11672762299058635630,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6314647598450925730 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://bbs.dstormer6em3i4km.onion" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2860 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,11864090080286723051,11672762299058635630,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15728756937719123873 --mojo-platform-channel-handle=3396 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,11864090080286723051,11672762299058635630,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9116414564814131301 --mojo-platform-channel-handle=3372 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
594
Read events
519
Write events
71
Delete events
4
Modification events
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2856-13207923039203625 |
Value: 259 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
42
Text files
196
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\442d4805-e144-4683-8a97-3d7ab9349ef7.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10eab0.TMP | text | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
72
DNS requests
43
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2388 | chrome.exe | GET | — | 10.205.211.235:80 | http://bbs.dstormer6em3i4km.onion/assets/preload-store-081120a9f8cb0871483b66a95e534ce8e81f97d19c8cef978aea6c696d1feb20.js | unknown | — | — | unknown |
2388 | chrome.exe | GET | 200 | 10.205.211.235:80 | http://bbs.dstormer6em3i4km.onion/assets/ember_jquery-0ae86c6a7527a99c2b9b8a11521273bd9cb4f7d41bc546df081b7ee94f26d9c3.js | unknown | text | 149 Kb | unknown |
2388 | chrome.exe | GET | 200 | 10.205.211.235:80 | http://bbs.dstormer6em3i4km.onion/ | unknown | html | 10.6 Kb | unknown |
2388 | chrome.exe | GET | 200 | 10.205.211.235:80 | http://bbs.dstormer6em3i4km.onion/assets/locales/en_US-7bd82a9d8e6e84ec459ac7afae5856e043eb89f9b927e278622c7525c7667fa1.js | unknown | text | 60.3 Kb | unknown |
2388 | chrome.exe | GET | 200 | 10.205.211.235:80 | http://bbs.dstormer6em3i4km.onion/stylesheets/desktop_d5a2932b5eff182416a00d45d3d2cac1927632bd.css?__ws=bbs.dstormer6em3i4km.onion | unknown | text | 54.8 Kb | unknown |
2388 | chrome.exe | GET | 200 | 10.205.211.235:80 | http://bbs.dstormer6em3i4km.onion/assets/plugin-6dbd11f40628de330f2a88c4aad9e5827e915247a6858367f22353d8bd71ac34.js | unknown | text | 18.5 Kb | unknown |
2388 | chrome.exe | GET | 200 | 10.205.211.235:80 | http://bbs.dstormer6em3i4km.onion/stylesheets/desktop_theme_2_76956dd1d1f593f5f3bac7104d4928fec2b05ec8.css?__ws=bbs.dstormer6em3i4km.onion | unknown | text | 206 b | unknown |
2388 | chrome.exe | GET | 200 | 10.205.211.235:80 | http://bbs.dstormer6em3i4km.onion/svg-sprite/bbs.dstormer6em3i4km.onion/svg-2-92ee02d991196f9960ce65f5820debd458555cfc.js | unknown | text | 33.8 Kb | unknown |
2388 | chrome.exe | GET | 200 | 10.205.211.235:80 | http://bbs.dstormer6em3i4km.onion/assets/application-75c776cb542a86606ec9adeebc244f0862ed62fb724c5a7262197b90990815bc.js | unknown | text | 399 Kb | unknown |
2388 | chrome.exe | GET | 200 | 10.205.211.235:80 | http://bbs.dstormer6em3i4km.onion/assets/vendor-25f91d66eba869fbd399d751711e74544b6d60bf034a5350b61c6c12caad0e2a.js | unknown | text | 52.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2388 | chrome.exe | 172.217.19.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 172.217.168.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 172.217.168.228:443 | www.google.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 172.217.168.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 172.217.19.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 172.217.168.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 74.125.100.167:80 | r1---sn-5hnedn7s.gvt1.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 216.58.211.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 216.58.208.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 172.217.17.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
bbs.dstormer6em3i4km.onion |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| malicious |
www.google-analytics.com |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1044 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1044 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1044 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
1044 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |