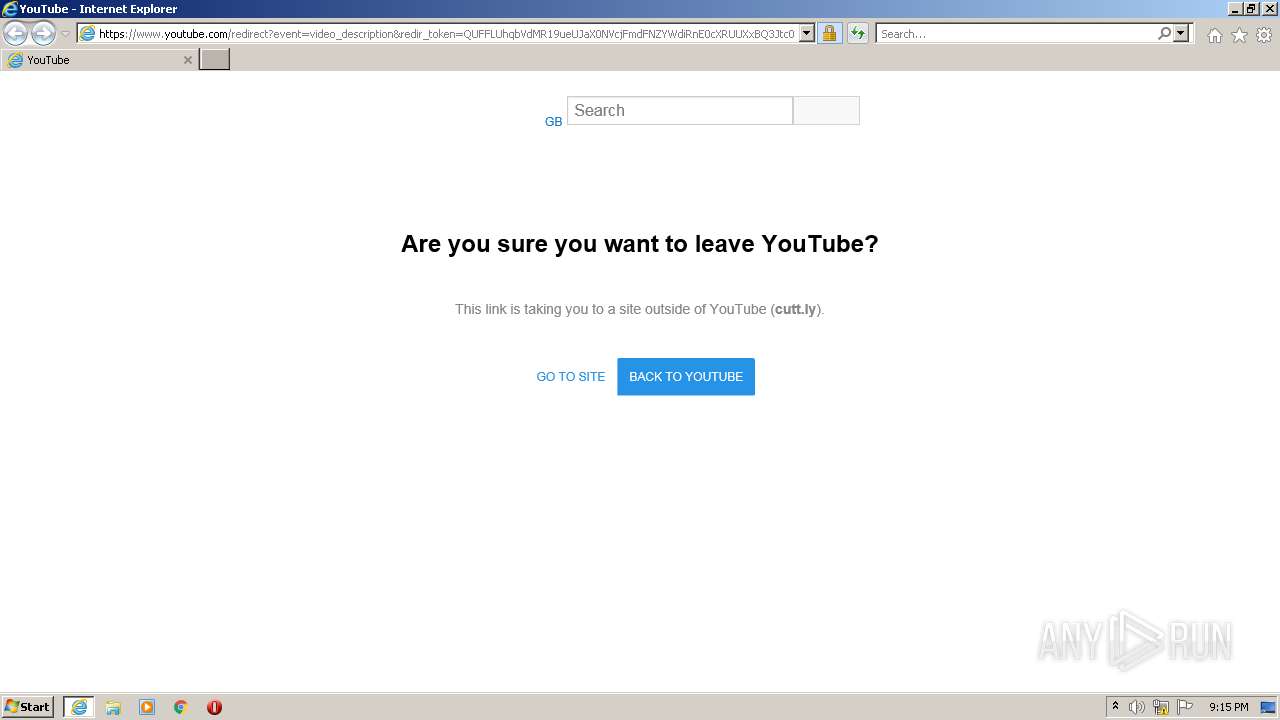
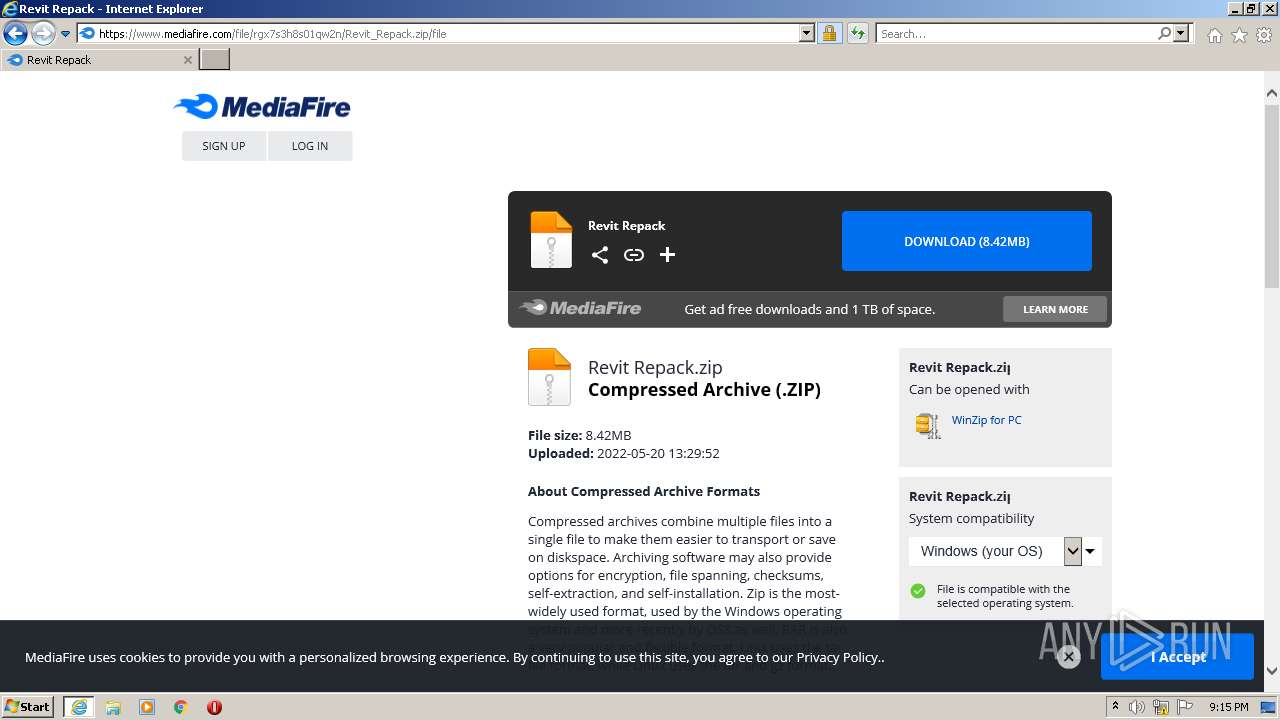
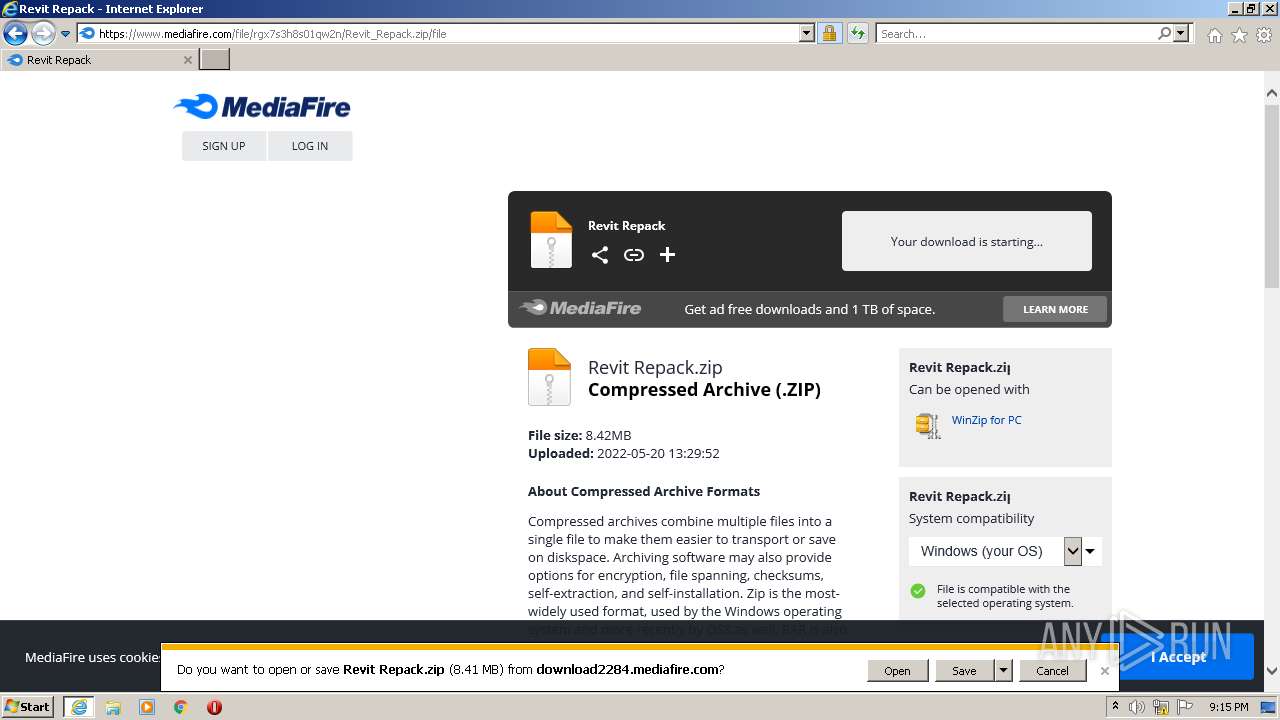
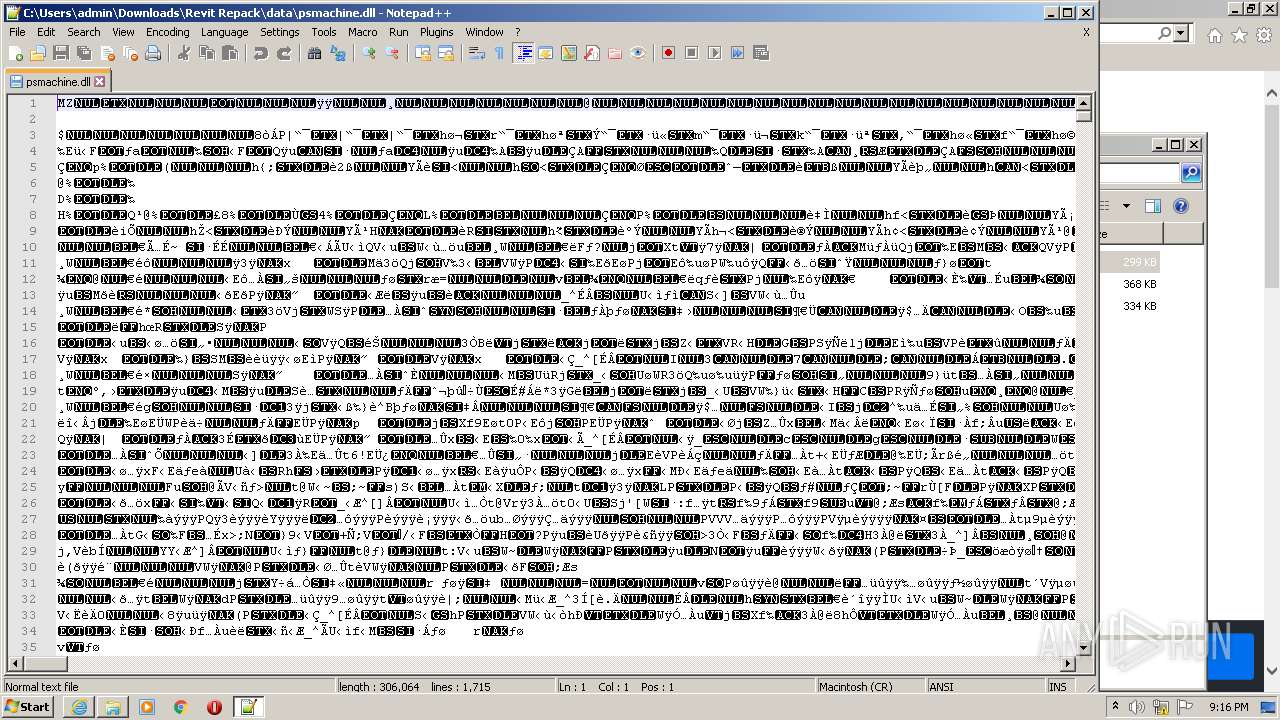
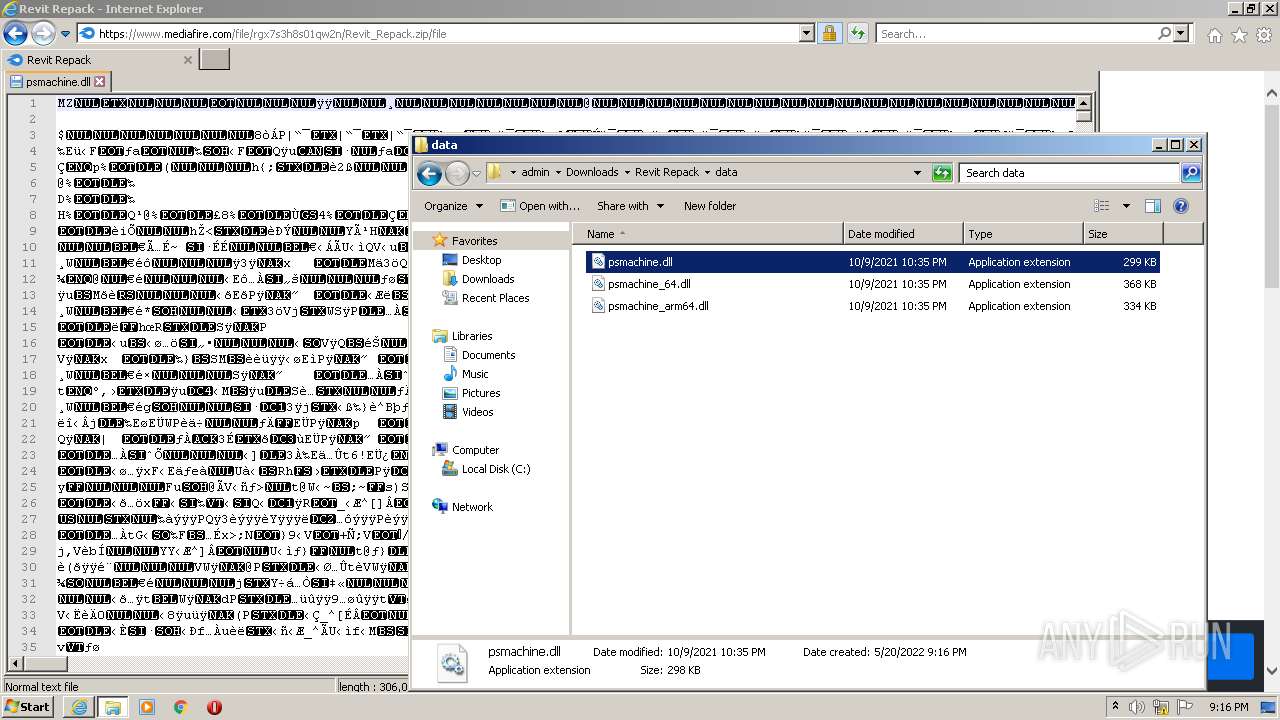
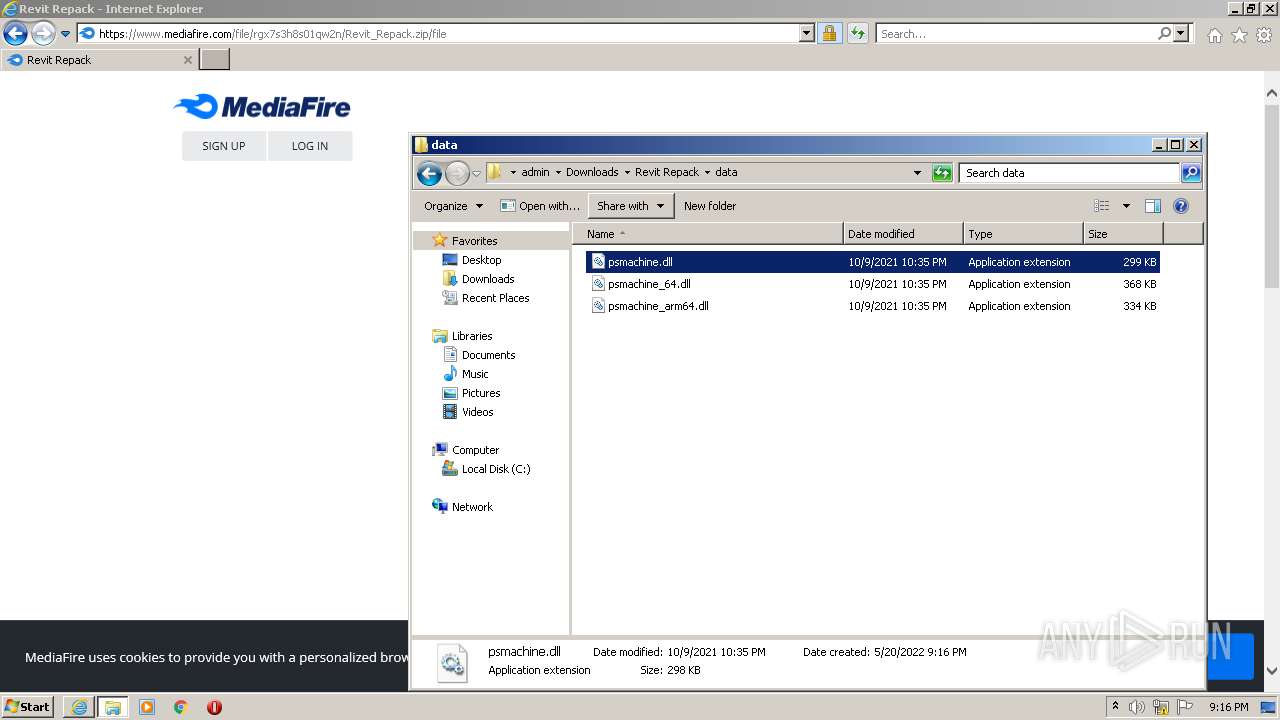
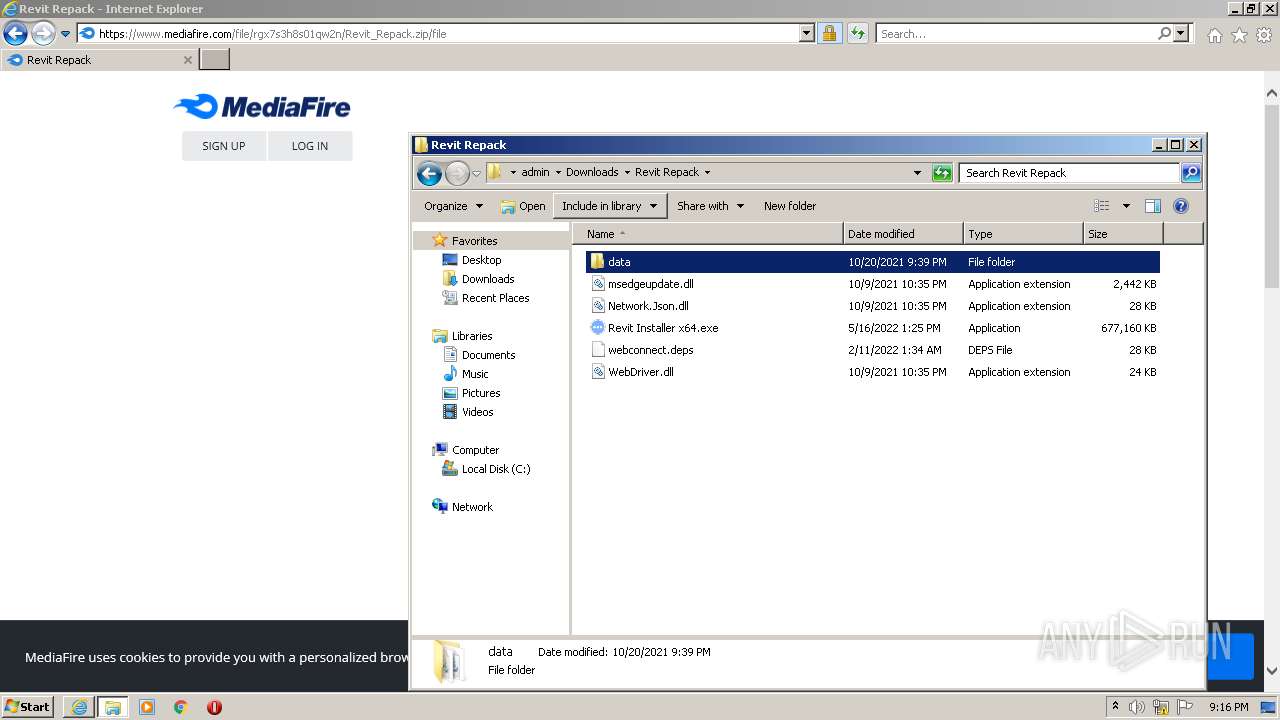
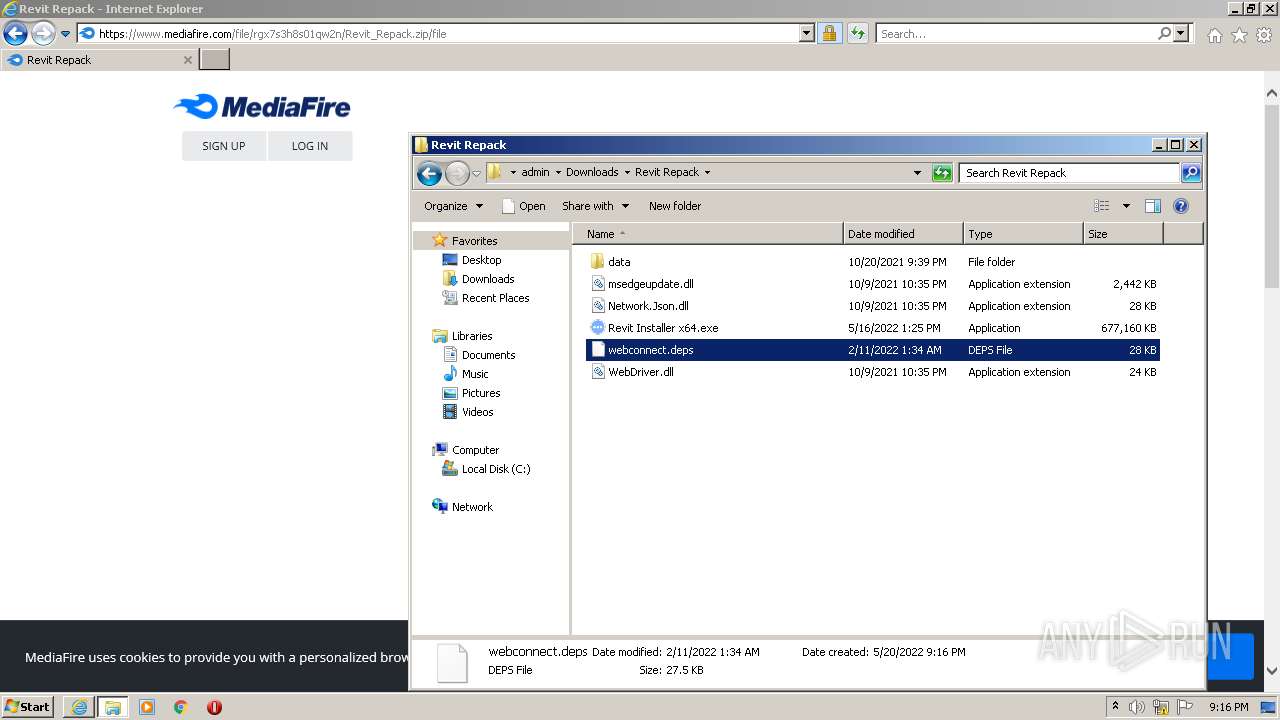
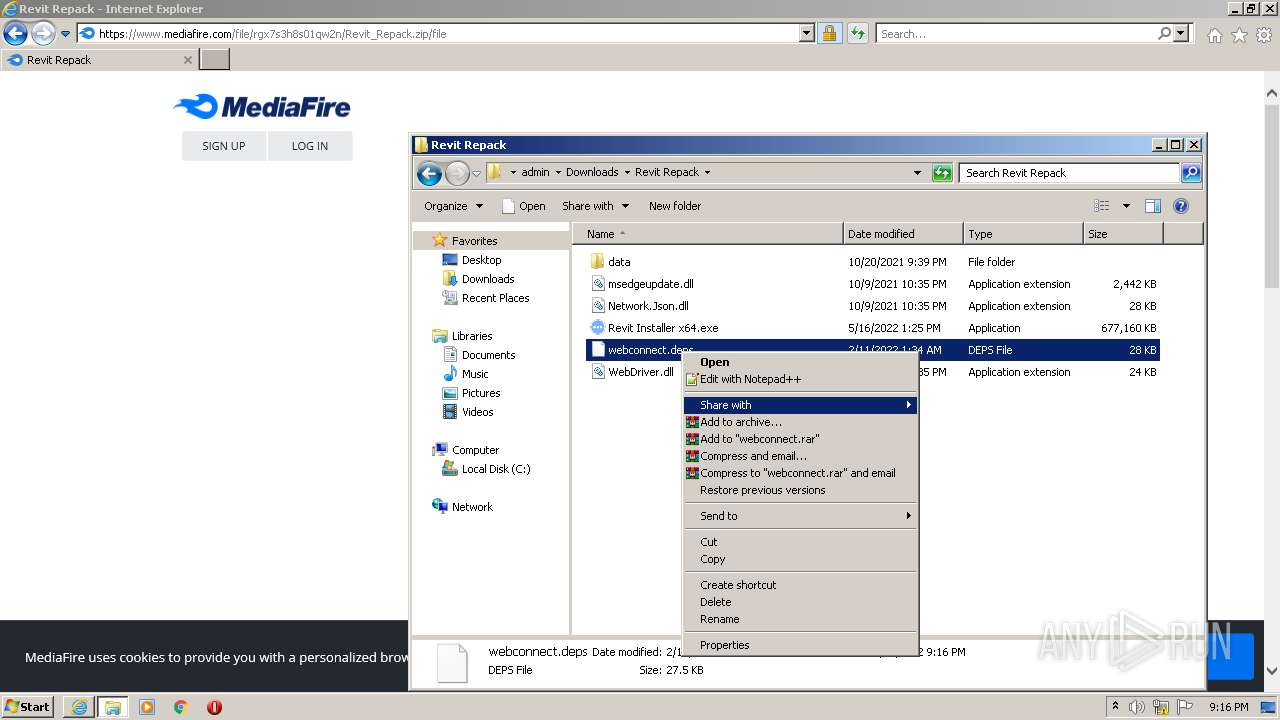
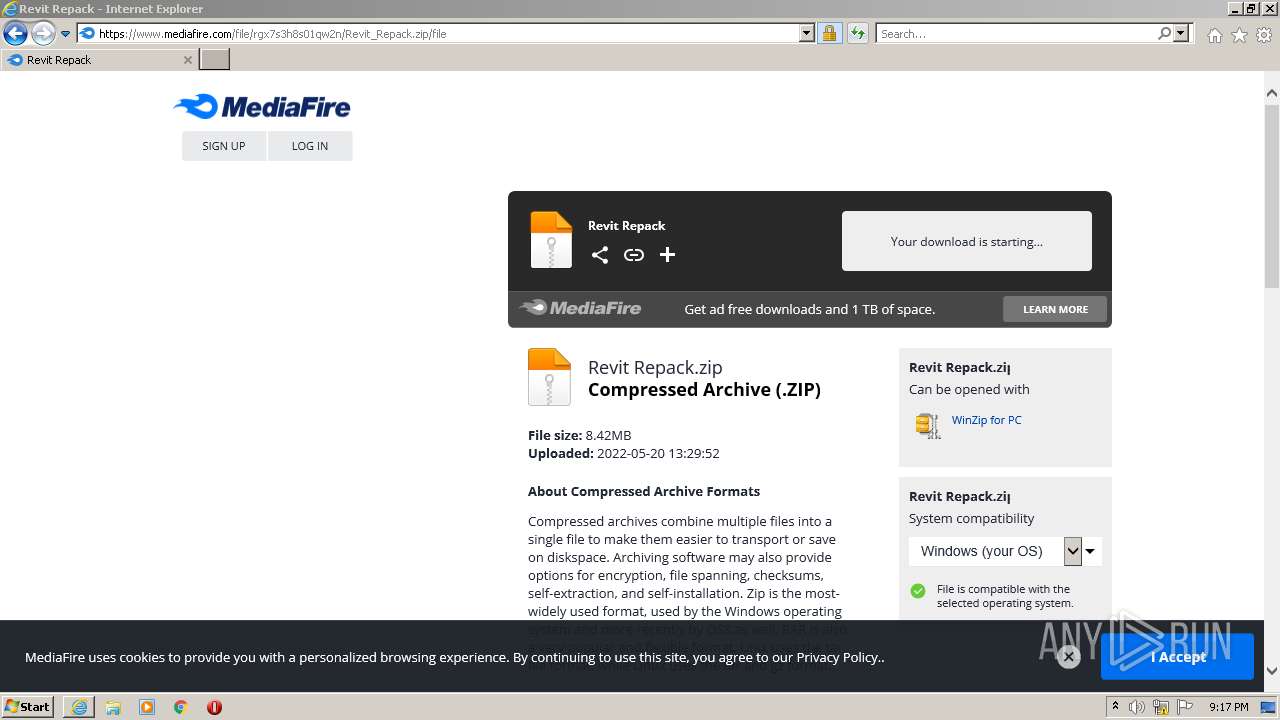
| URL: | https://www.youtube.com/redirect?event=video_description&redir_token=QUFFLUhqbVdMR19ueUJaX0NVcjFmdFNZYWdiRnE0cXRUUXxBQ3Jtc0ttY2F1d1dvUnFFY0lVUFF4Zi1ZSjc0TUViU3YzRTBJaldZd09lSzdwa2szejFnNHZaYW9rQWJBbFVoNWhUNl9xbk1SLW8zVGNIOEpzMFpvZkJTWWRwM2c5V0EwUUl6b0g3Vi1hT0N6bmkyeWhGT29Fbw&q=https%3A%2F%2Fcutt.ly%2FLHSPgSp&v=5ym6xiyTbaQ |
| Full analysis: | https://app.any.run/tasks/ca4e4061-a9aa-4a44-b99c-1942da8b4223 |
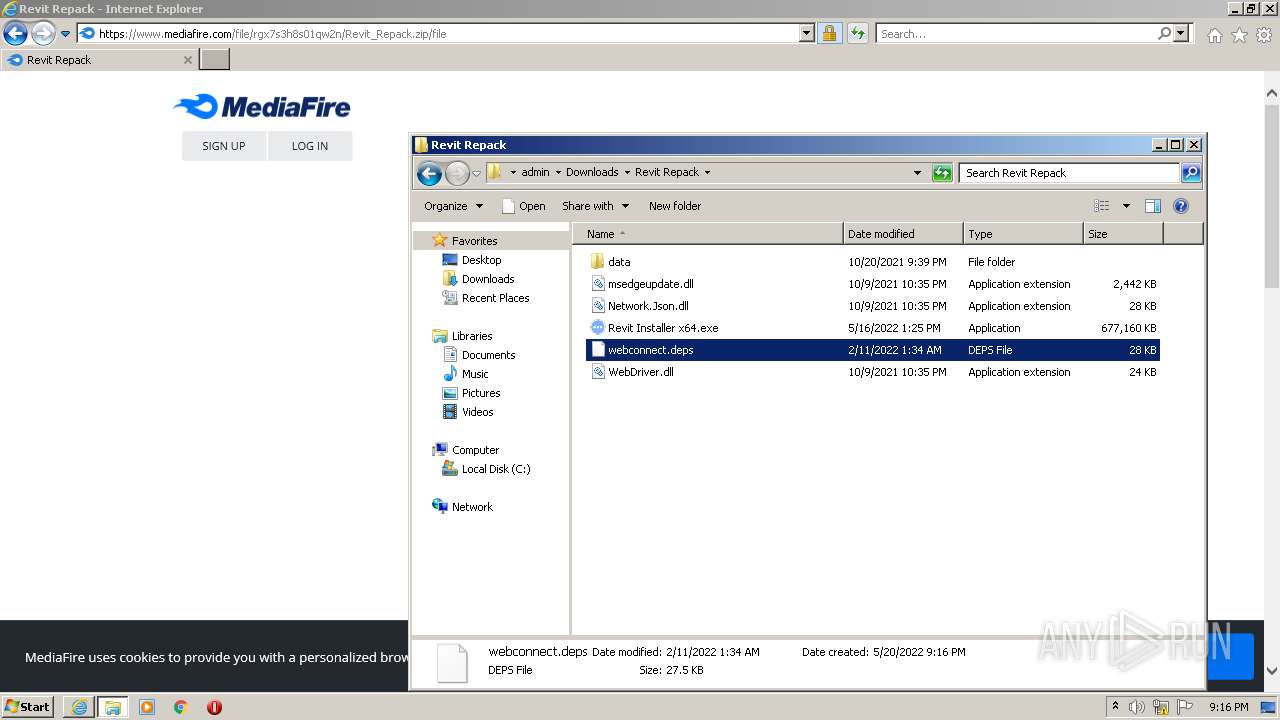
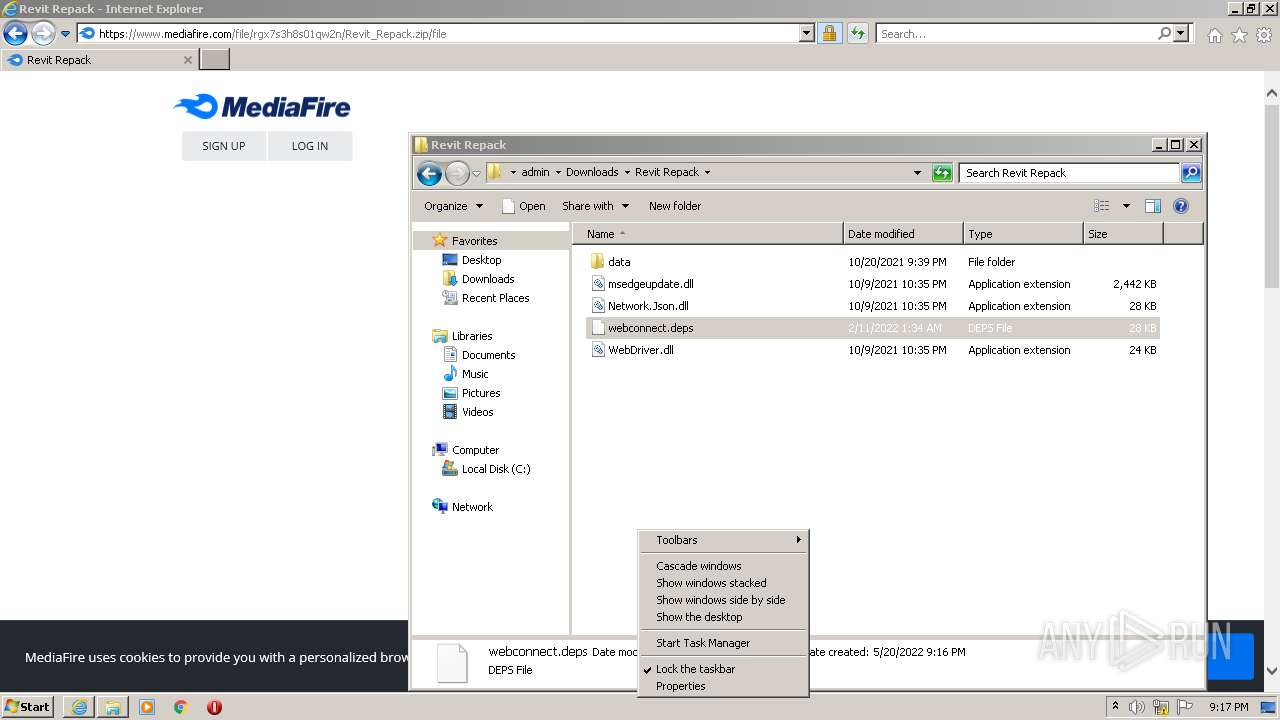
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 20:15:31 |
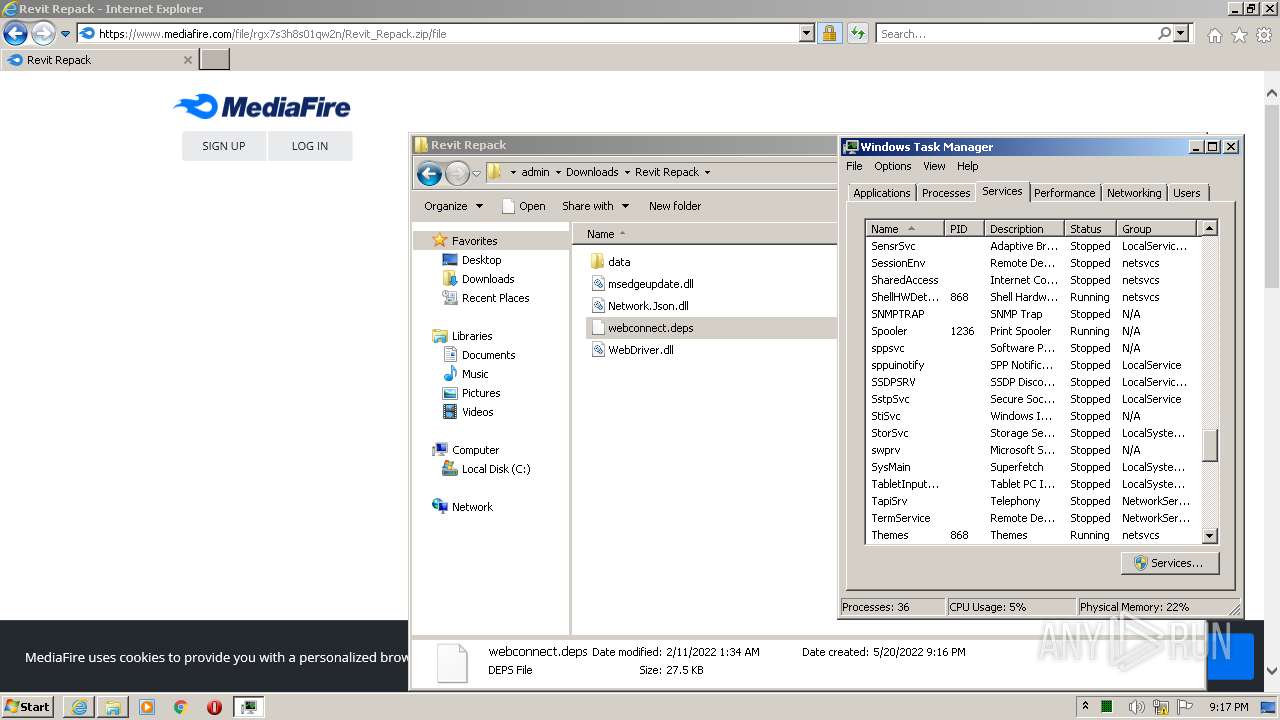
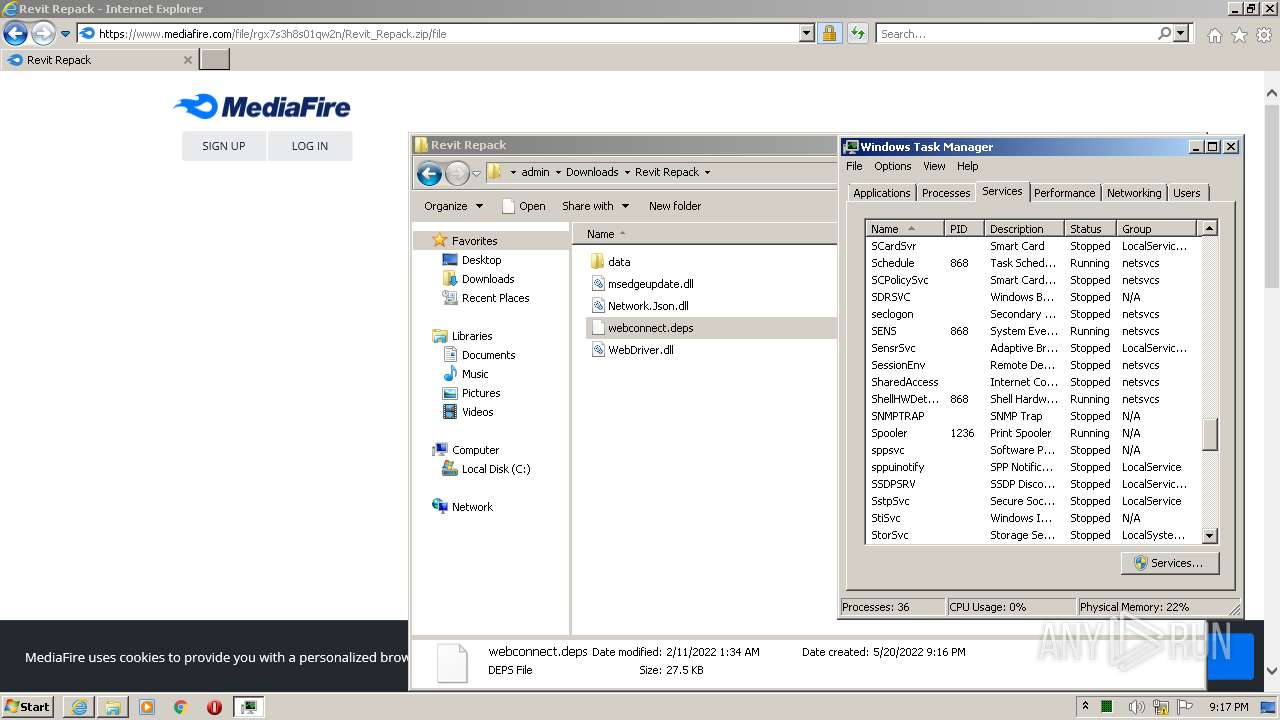
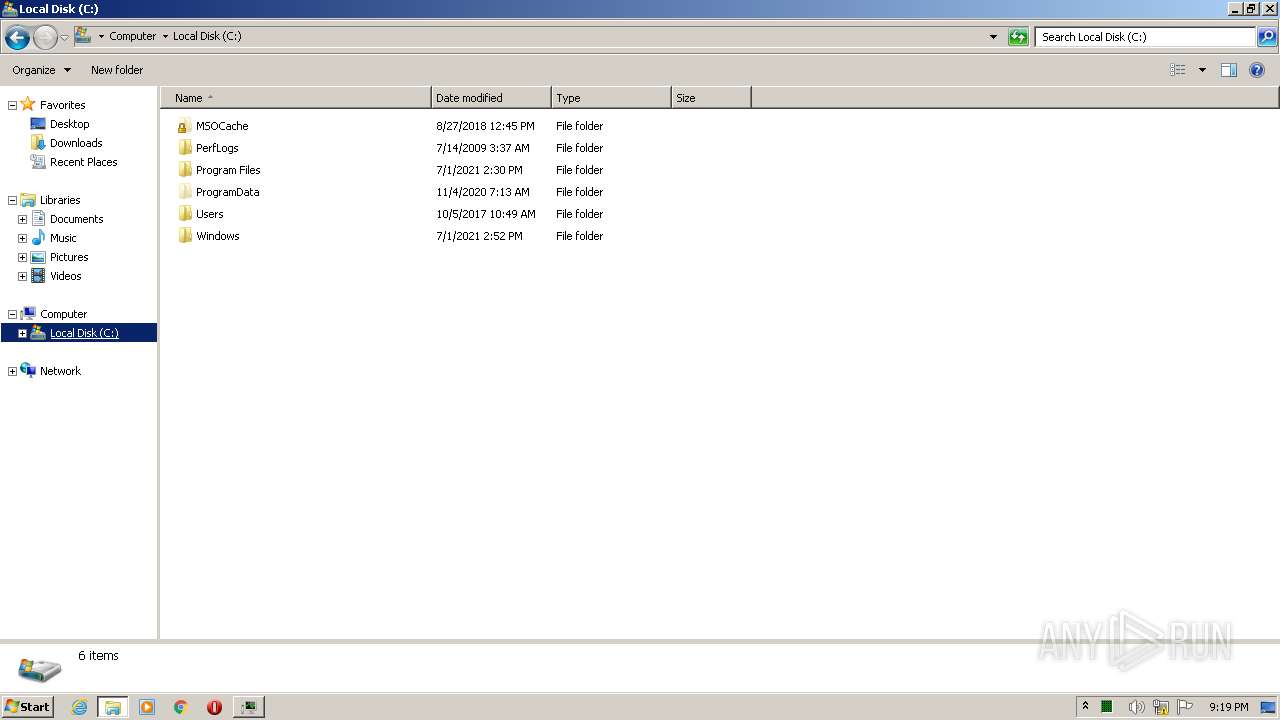
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0EBEF50F4EB2CC92786D4A54AB36FC4C |
| SHA1: | 5A16C3BAE2DA4769E6AF972E89391BFA05BB5398 |
| SHA256: | 96C459C4784767BDCECC432FD852D9E08E07DB98204C94262170E325818330BA |
| SSDEEP: | 6:2OLUxGKmKLqZ6kcNhGv3z/fBRgkECeE7zphf4lxN3zXdz2lBdn:2jGRfGNhGrDH/eCzpOr5Rz2Vn |
MALICIOUS
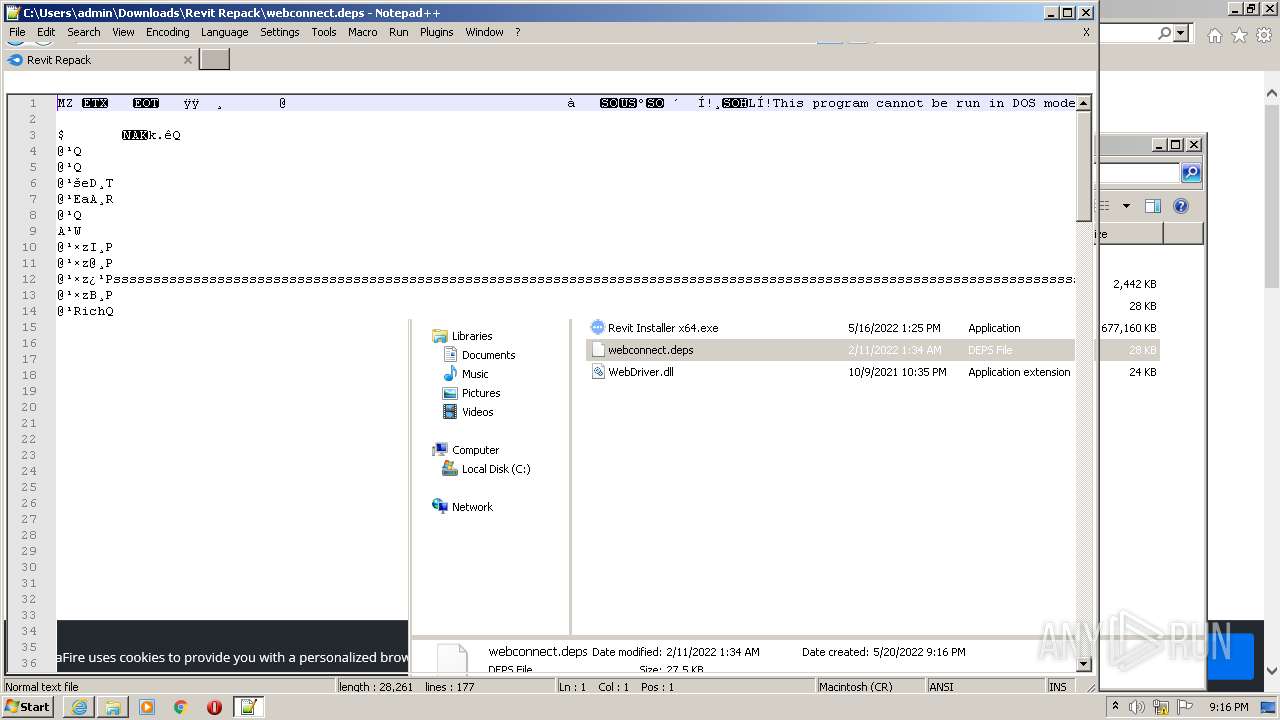
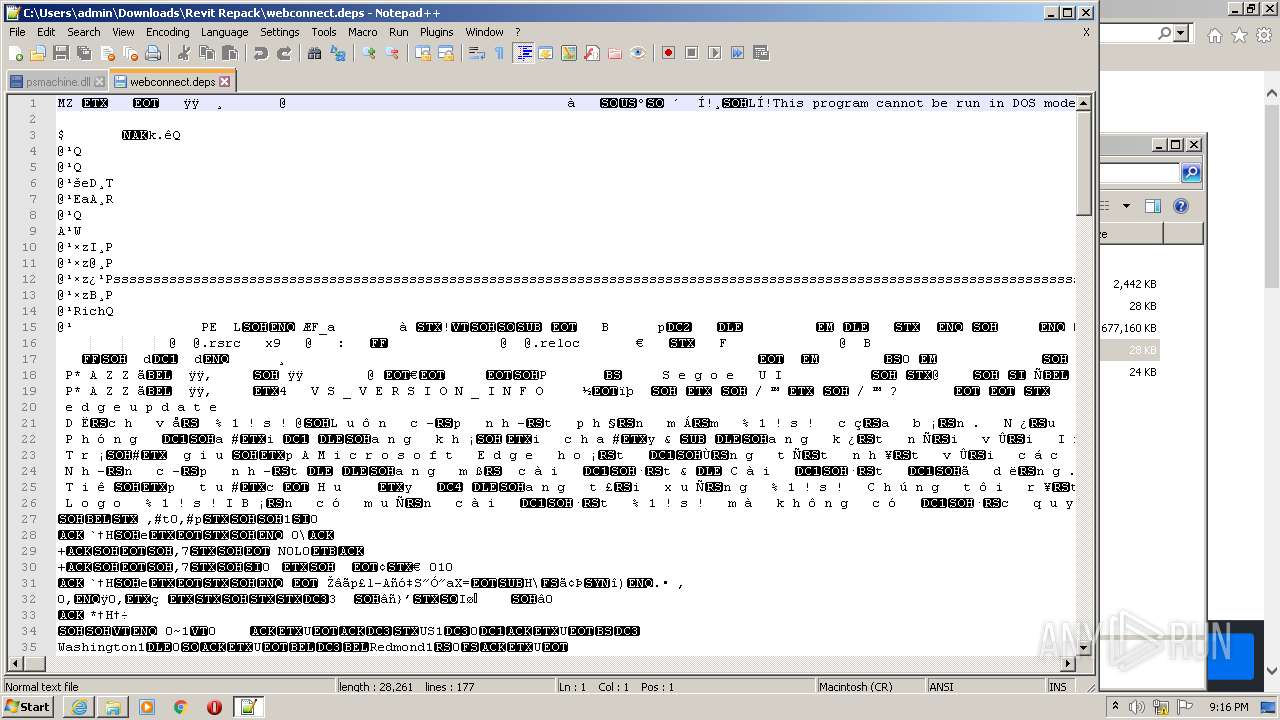
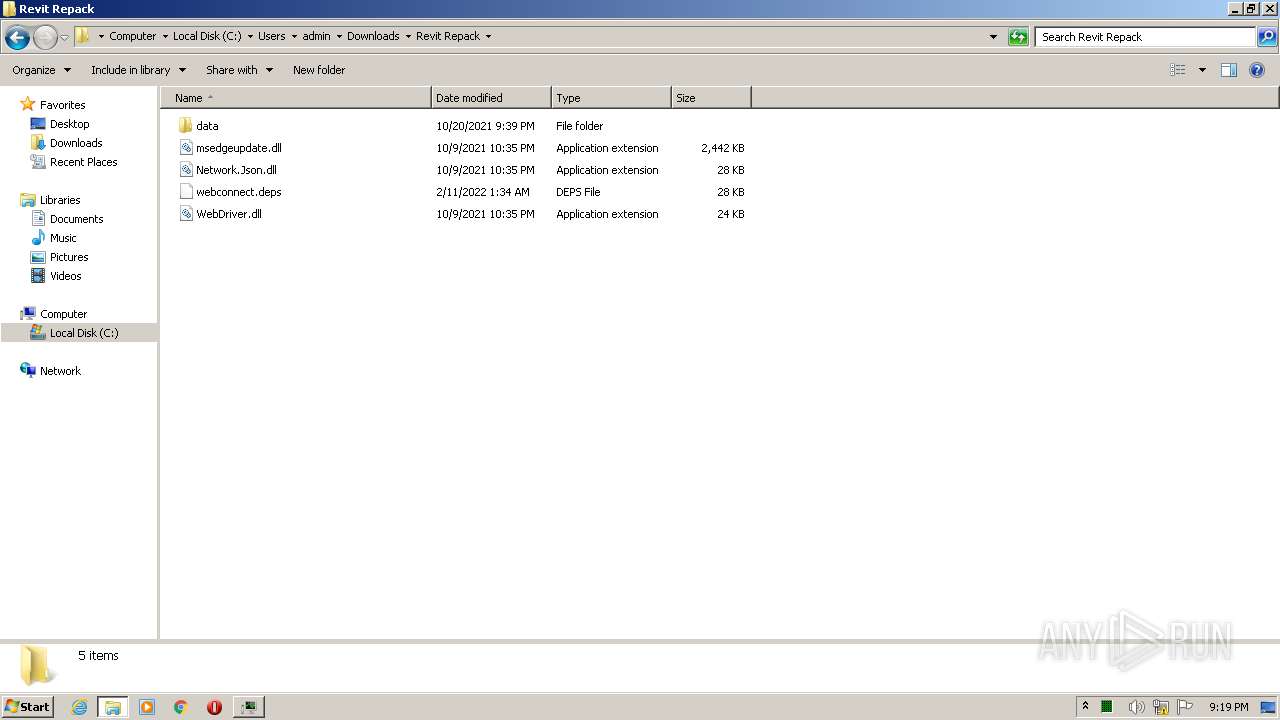
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2932)
- Explorer.EXE (PID: 1172)
Drops executable file immediately after starts
- WinRAR.exe (PID: 1176)
SUSPICIOUS
Starts Internet Explorer
- Explorer.EXE (PID: 1172)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3000)
Reads the computer name
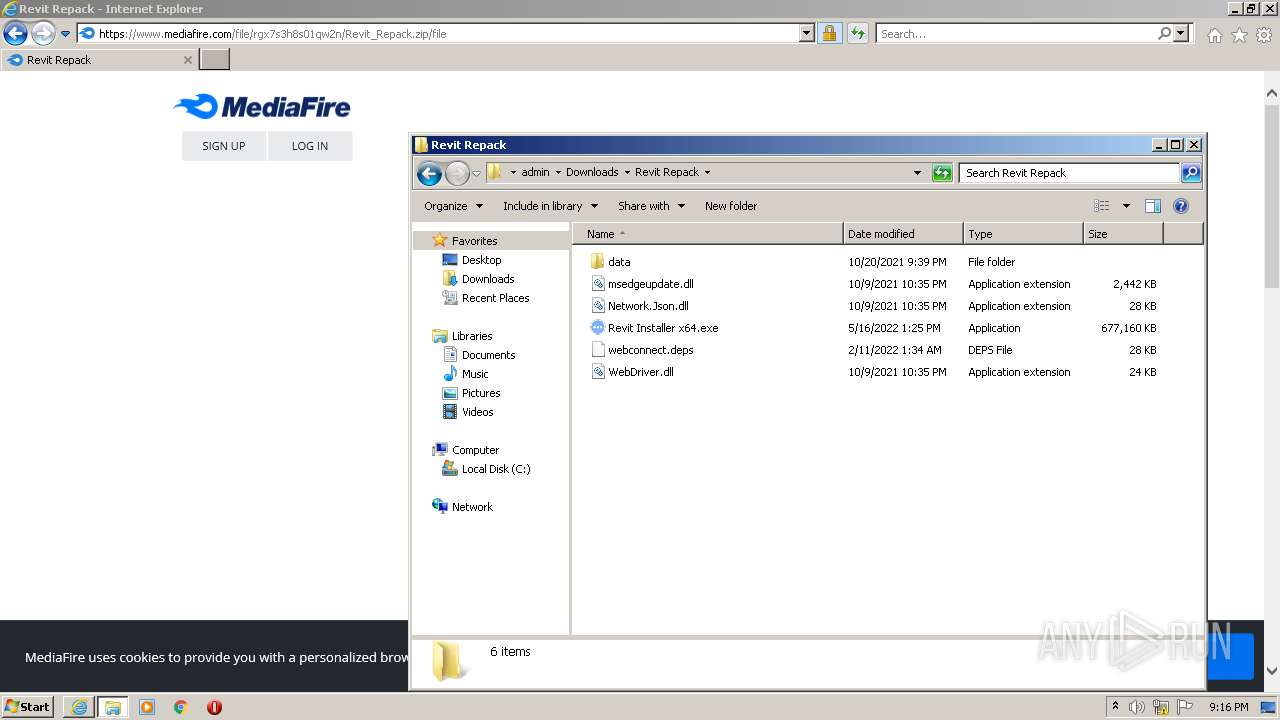
- WinRAR.exe (PID: 1176)
- Revit Installer x64.exe (PID: 2040)
- powershell.exe (PID: 584)
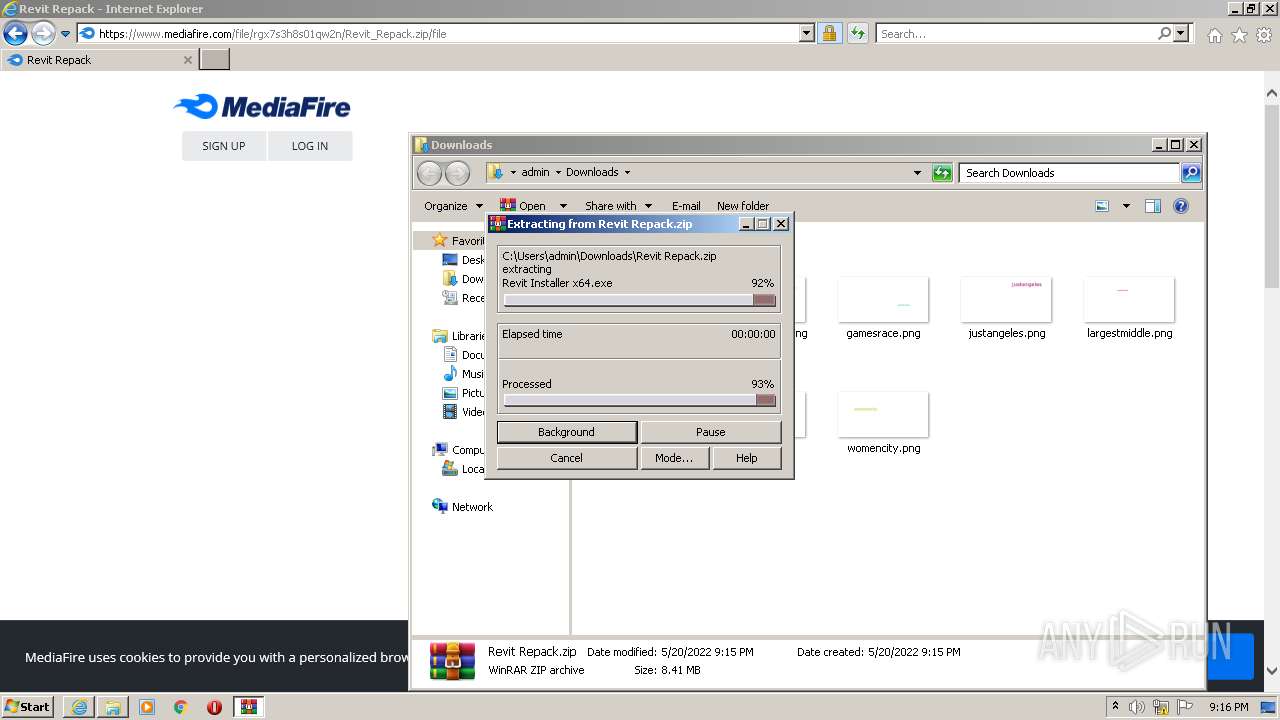
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1176)
Checks supported languages
- WinRAR.exe (PID: 1176)
- Revit Installer x64.exe (PID: 2040)
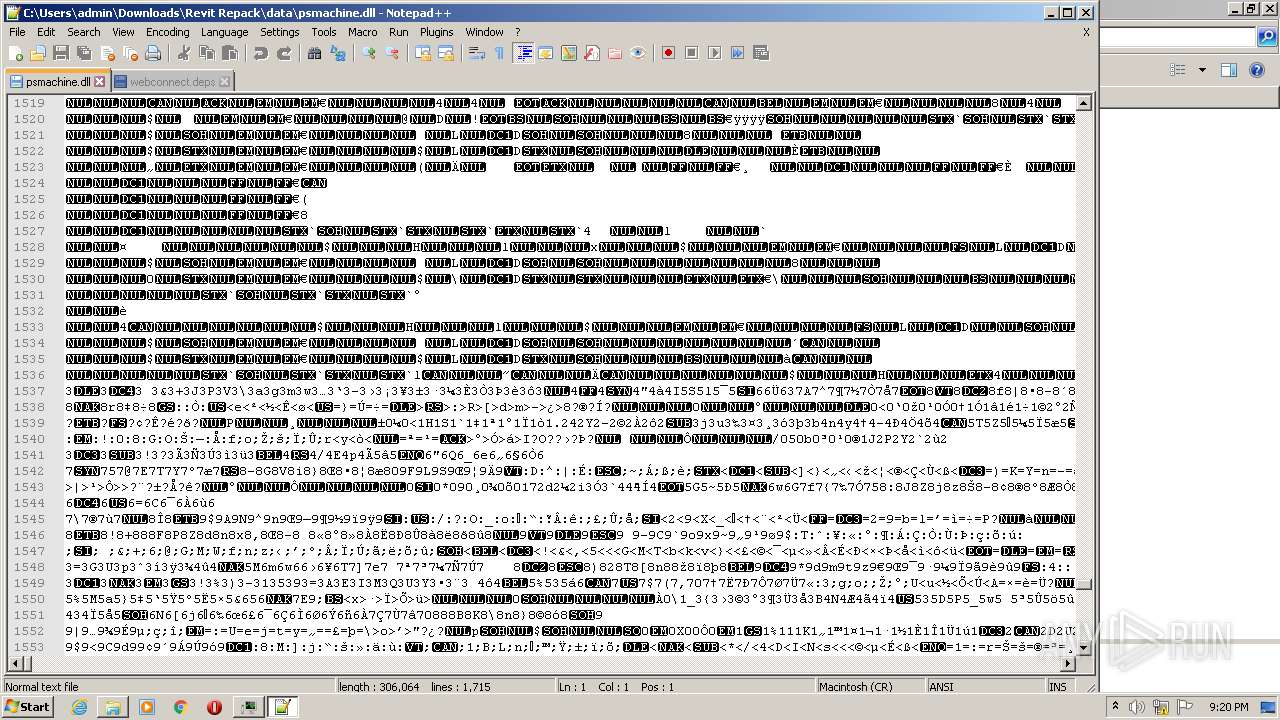
- notepad++.exe (PID: 1864)
- cmd.exe (PID: 1800)
- powershell.exe (PID: 584)
- notepad++.exe (PID: 3180)
- notepad++.exe (PID: 3956)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1176)
Reads default file associations for system extensions
- Explorer.EXE (PID: 1172)
Reads Environment values
- Revit Installer x64.exe (PID: 2040)
Starts CMD.EXE for commands execution
- Revit Installer x64.exe (PID: 2040)
Executes PowerShell scripts
- Revit Installer x64.exe (PID: 2040)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3280)
Application launched itself
- Explorer.EXE (PID: 1172)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2220)
Checks supported languages
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 2220)
- timeout.exe (PID: 2308)
- taskmgr.exe (PID: 1164)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 2308)
- chrome.exe (PID: 1368)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 1928)
- chrome.exe (PID: 856)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 2596)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 1032)
- Explorer.EXE (PID: 1172)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 1972)
- taskmgr.exe (PID: 472)
- explorer.exe (PID: 120)
Reads the computer name
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 2220)
- chrome.exe (PID: 3280)
- taskmgr.exe (PID: 1164)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 1032)
- chrome.exe (PID: 2596)
- chrome.exe (PID: 2624)
- taskmgr.exe (PID: 472)
- chrome.exe (PID: 4024)
- explorer.exe (PID: 120)
Reads internet explorer settings
- iexplore.exe (PID: 3000)
Checks Windows Trust Settings
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 2220)
- powershell.exe (PID: 584)
Reads settings of System Certificates
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 2220)
- Revit Installer x64.exe (PID: 2040)
- chrome.exe (PID: 3776)
Changes settings of System certificates
- iexplore.exe (PID: 2220)
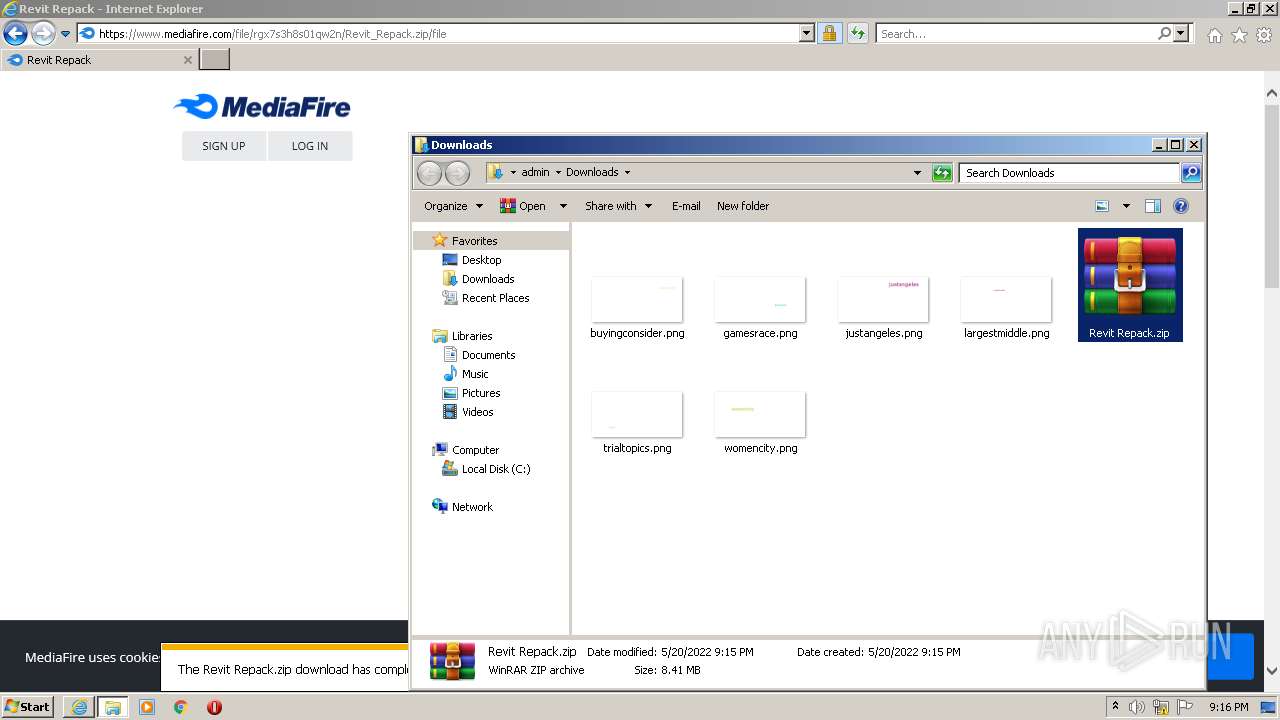
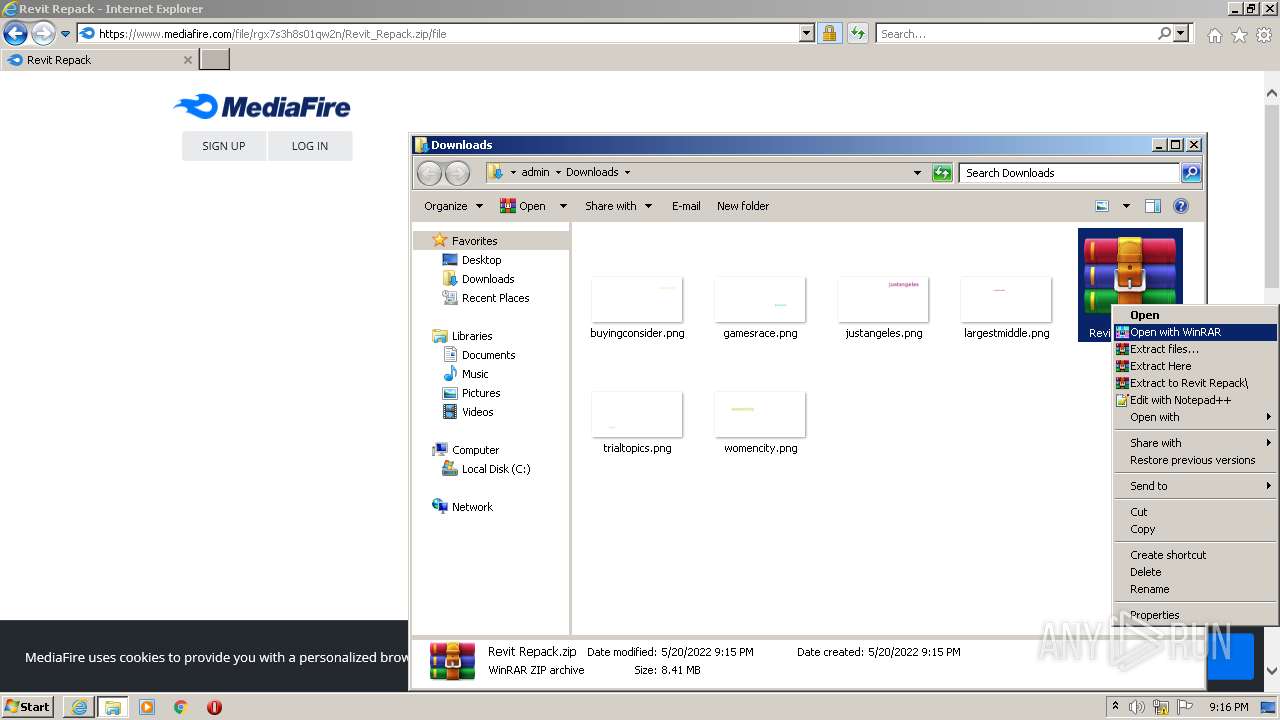
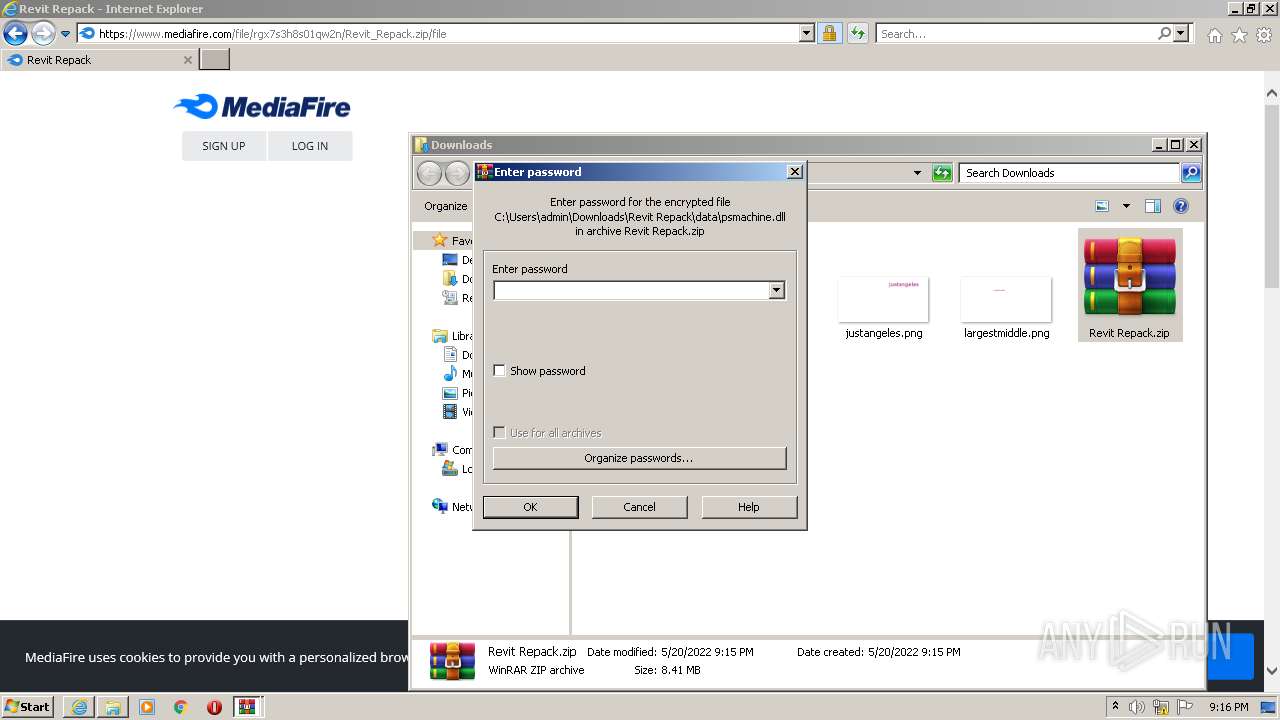
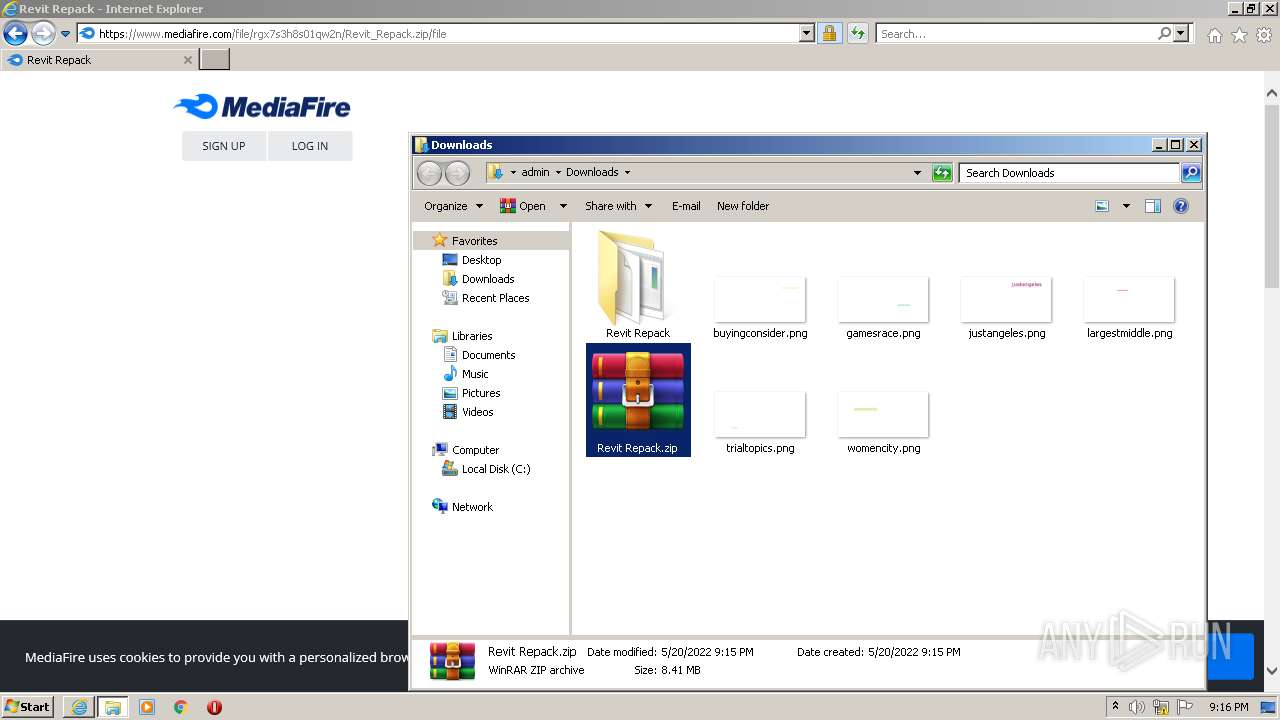
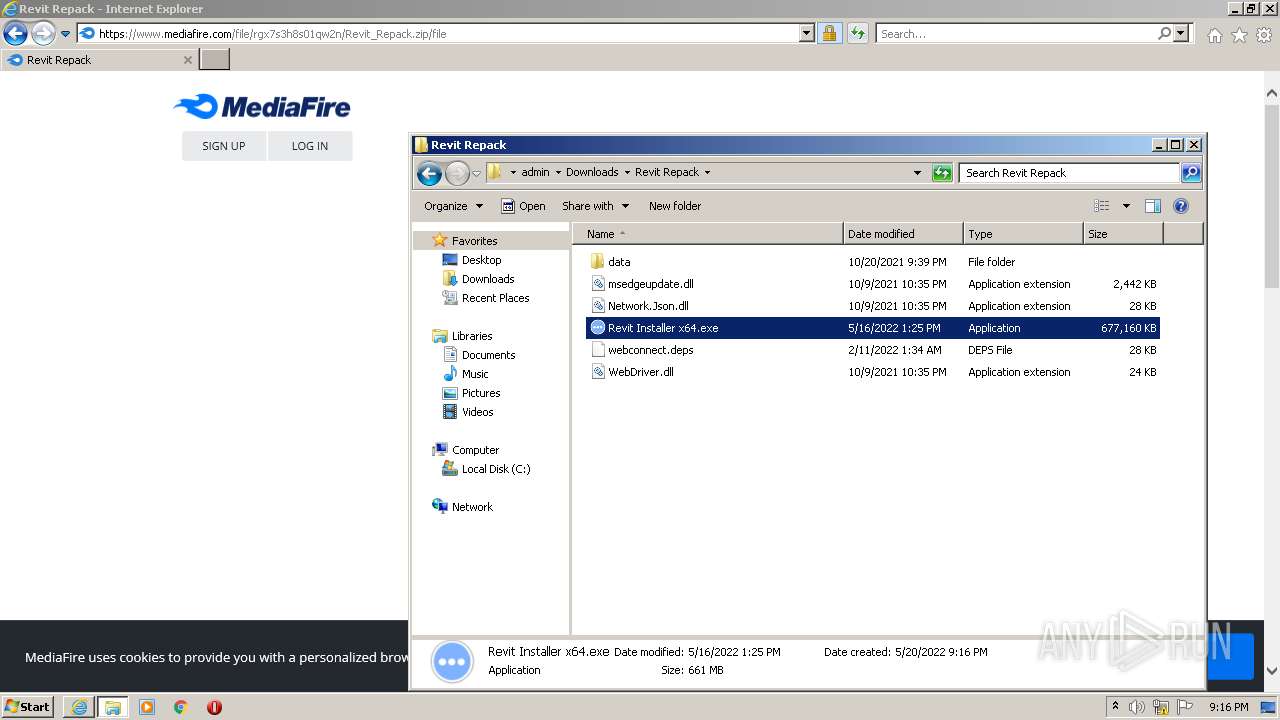
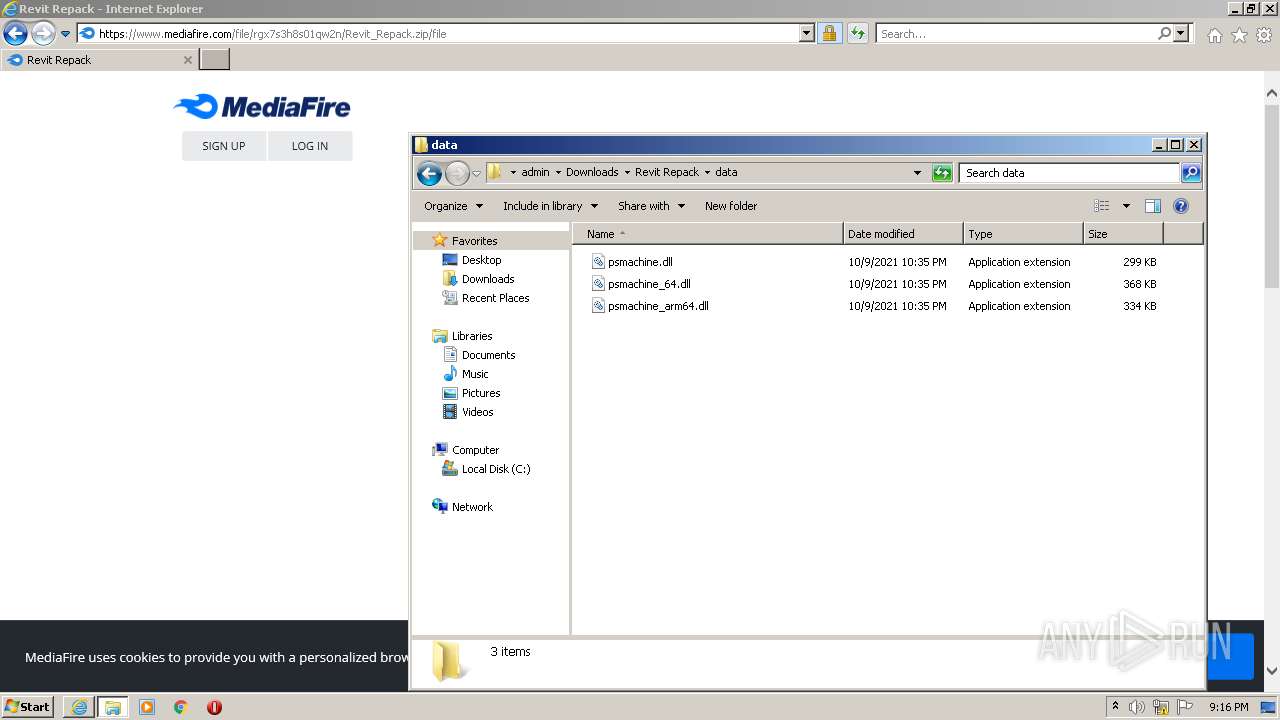
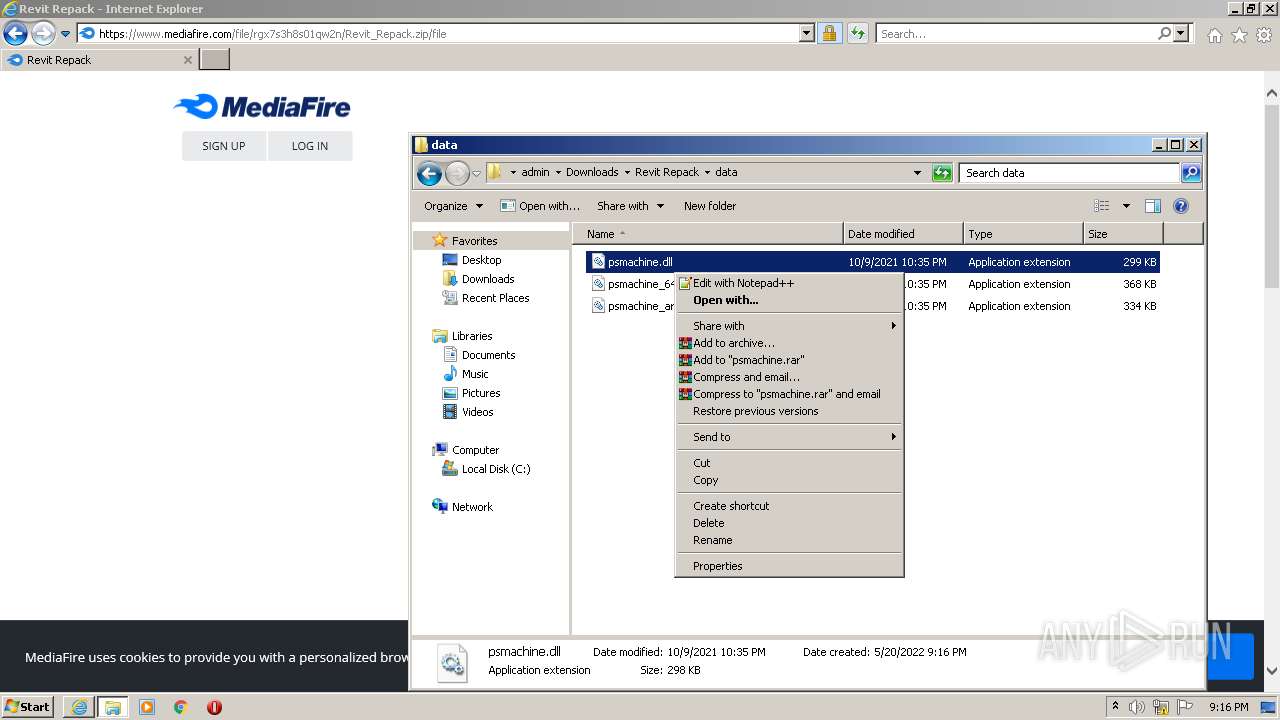
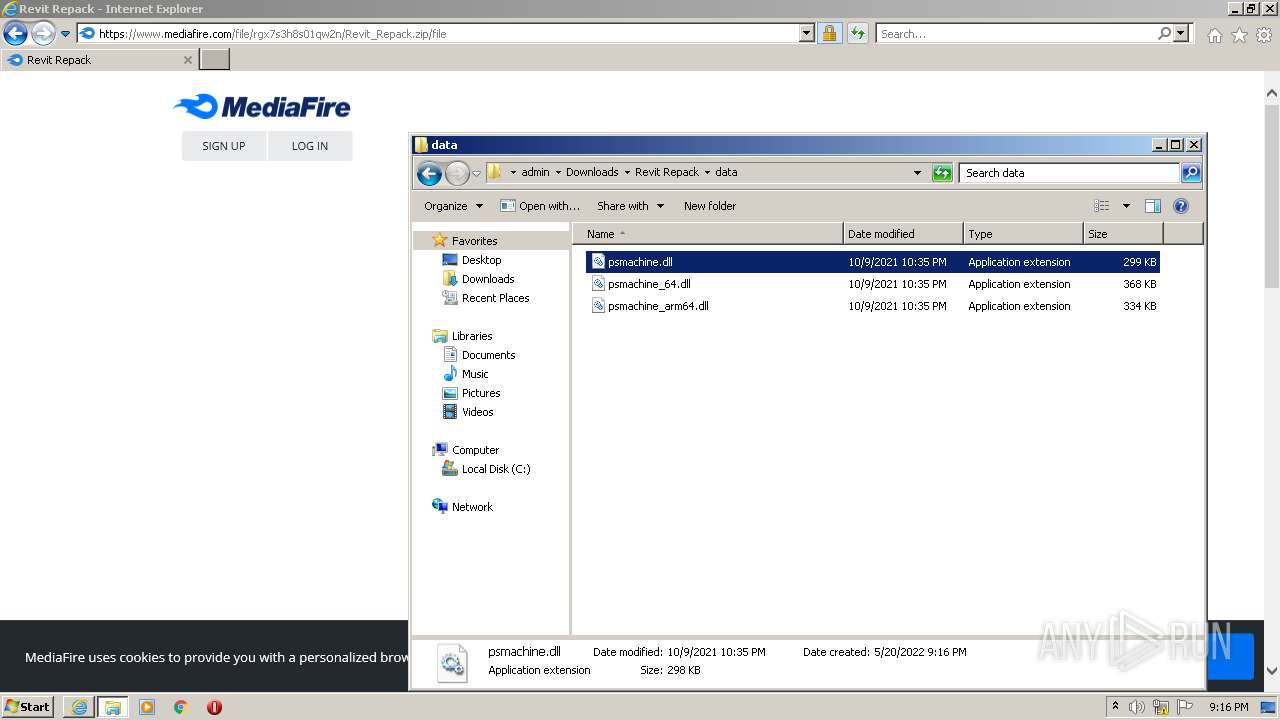
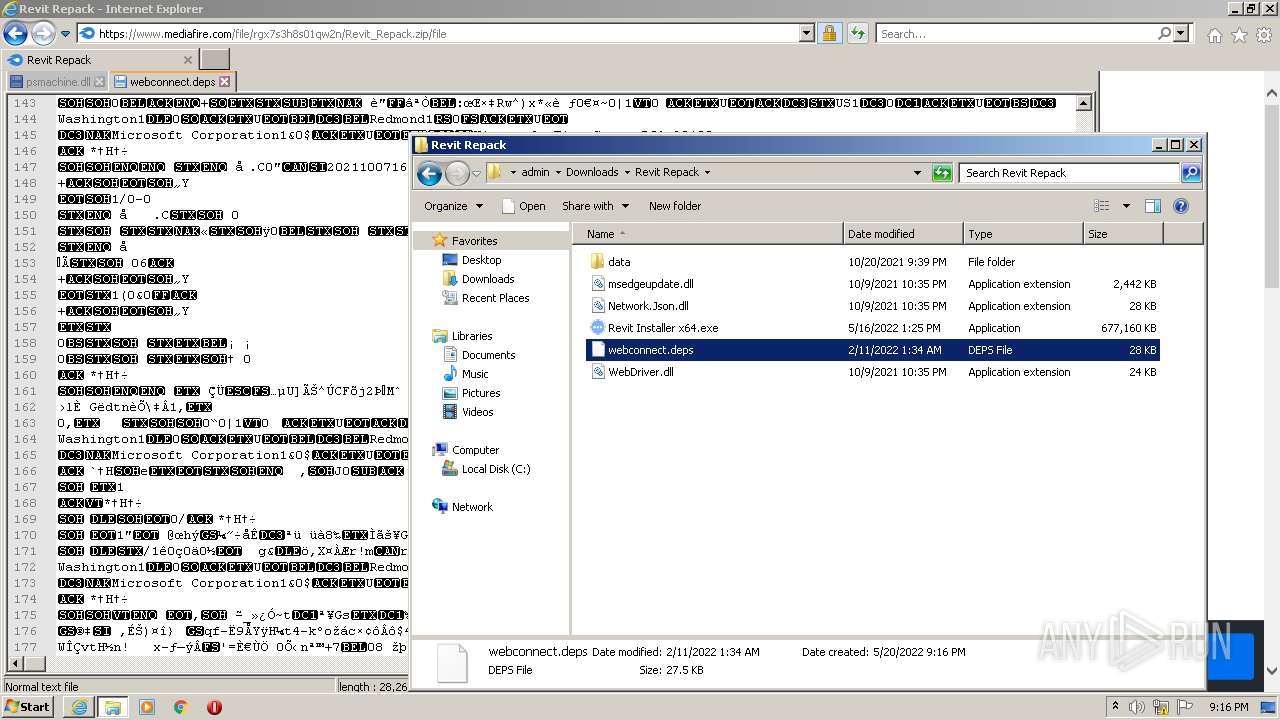
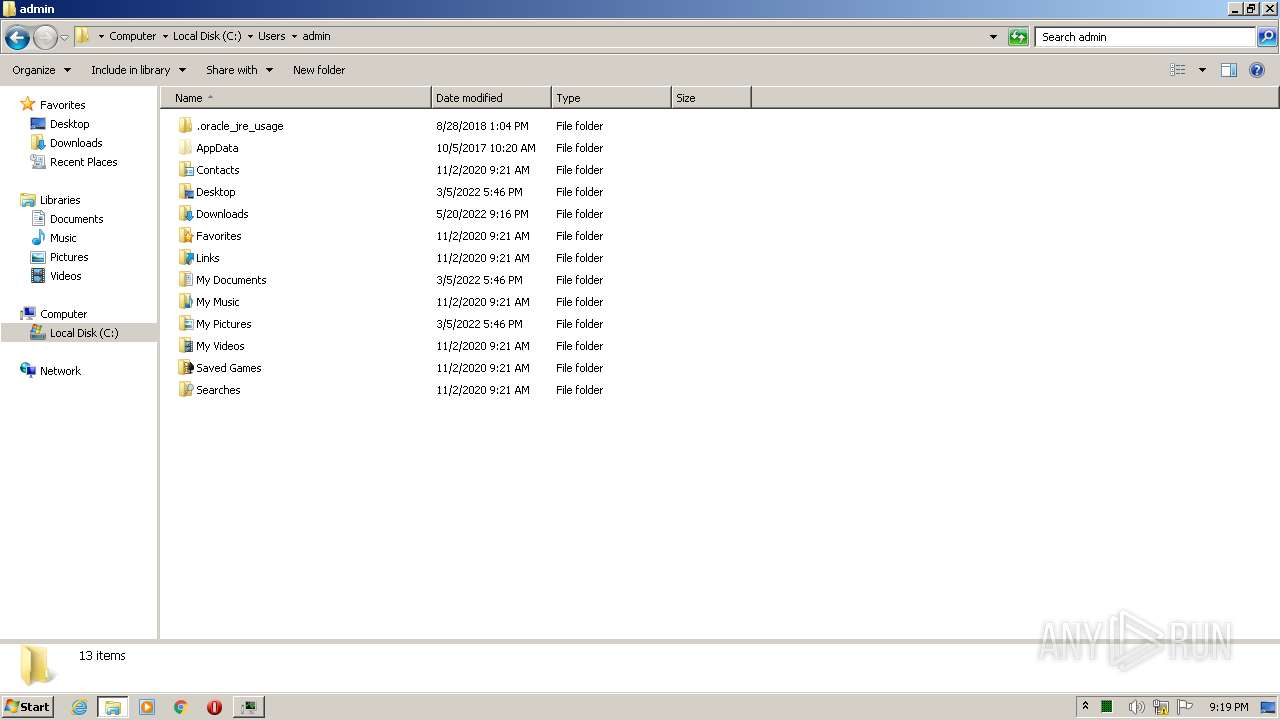
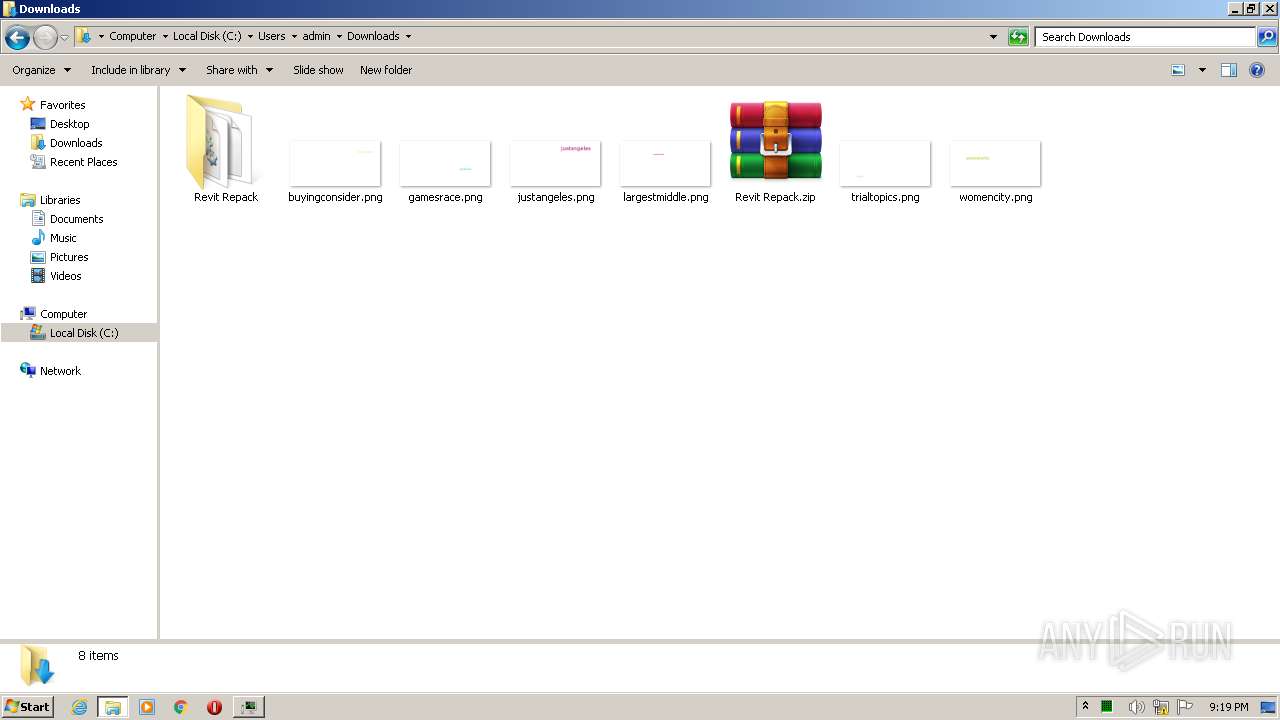
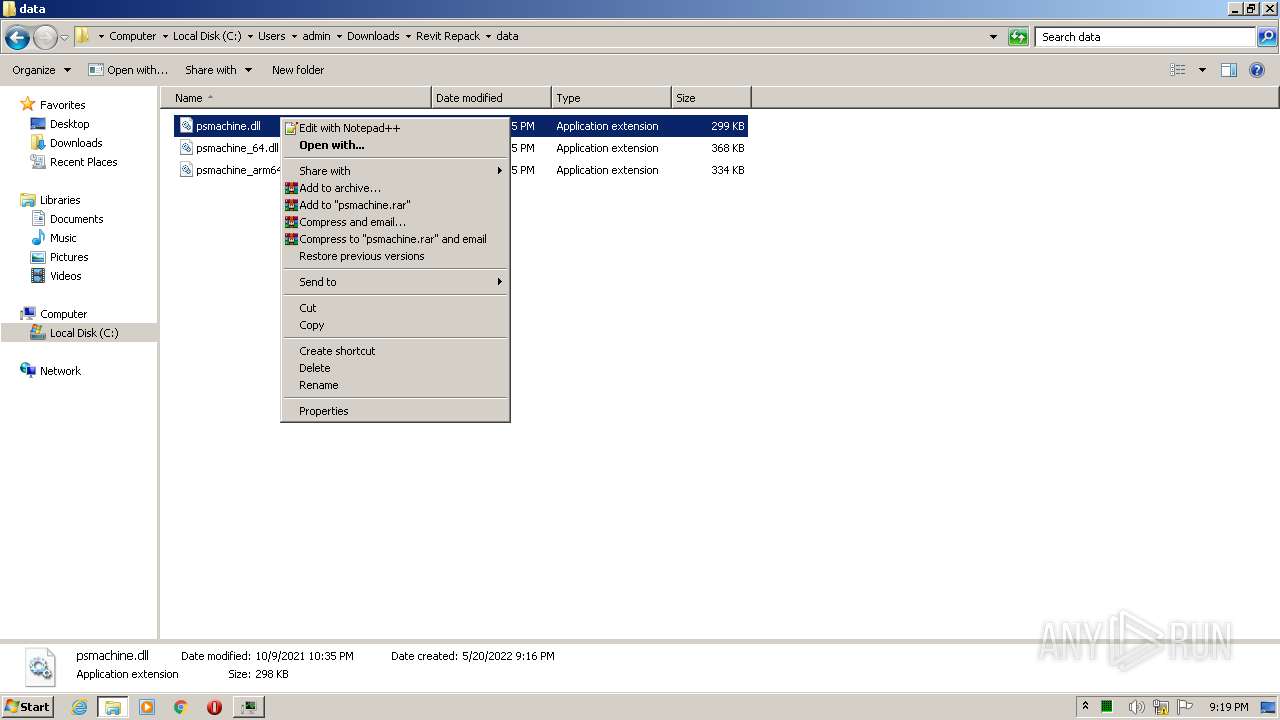
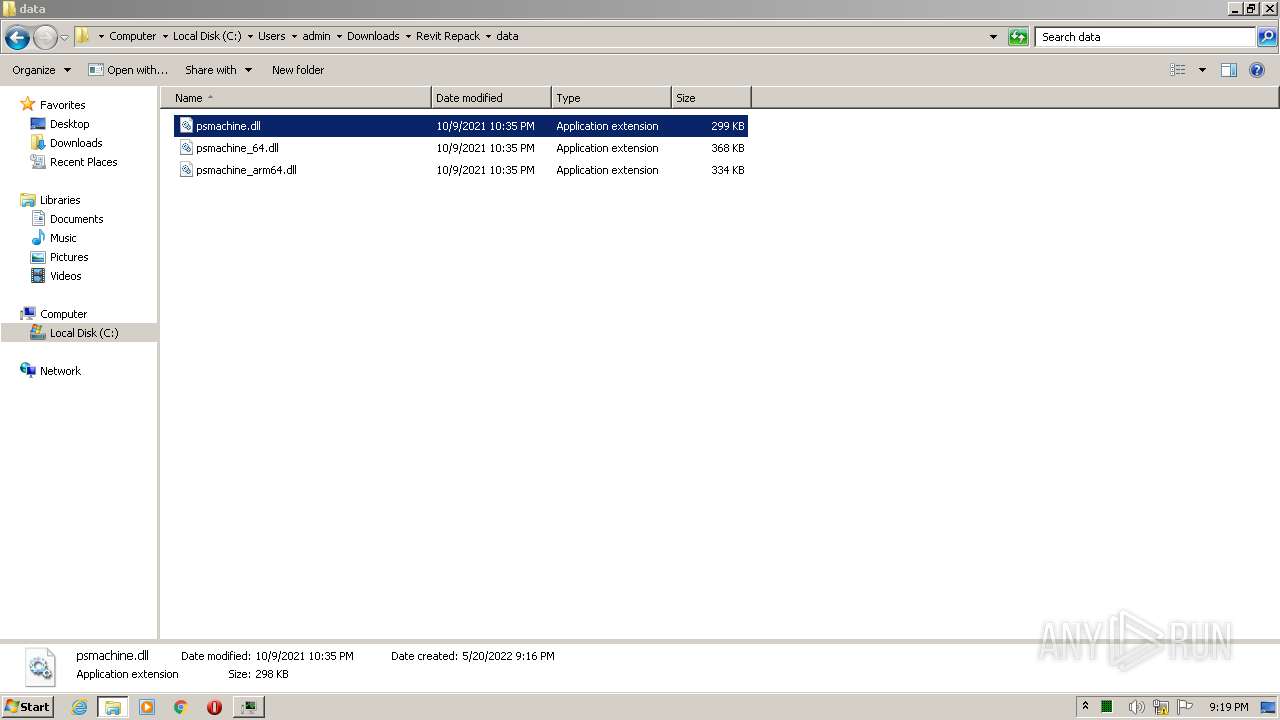
Manual execution by user
- WinRAR.exe (PID: 1176)
- Revit Installer x64.exe (PID: 2040)
Application launched itself
- iexplore.exe (PID: 2220)
- chrome.exe (PID: 3280)
Creates files in the user directory
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 2220)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2220)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2220)
Reads the hosts file
- chrome.exe (PID: 3280)
- chrome.exe (PID: 3776)
Reads the date of Windows installation
- iexplore.exe (PID: 2220)
- chrome.exe (PID: 1032)
Reads Microsoft Office registry keys
- Explorer.EXE (PID: 1172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
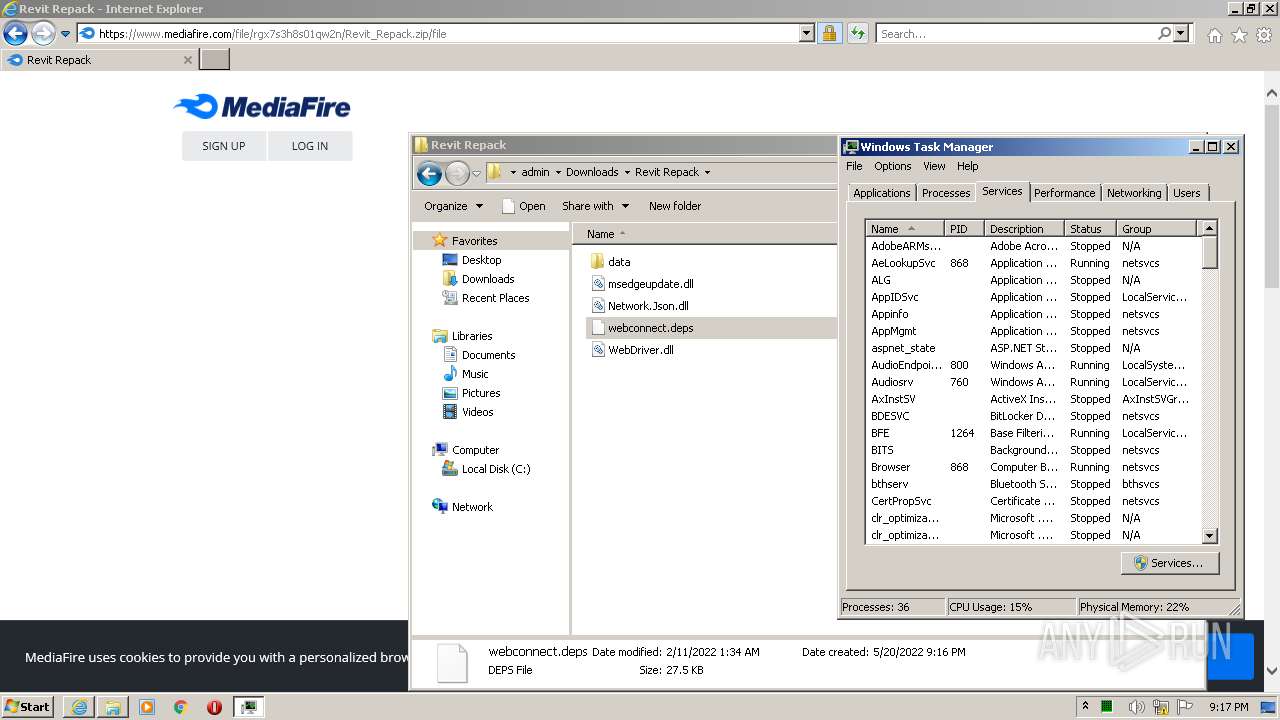
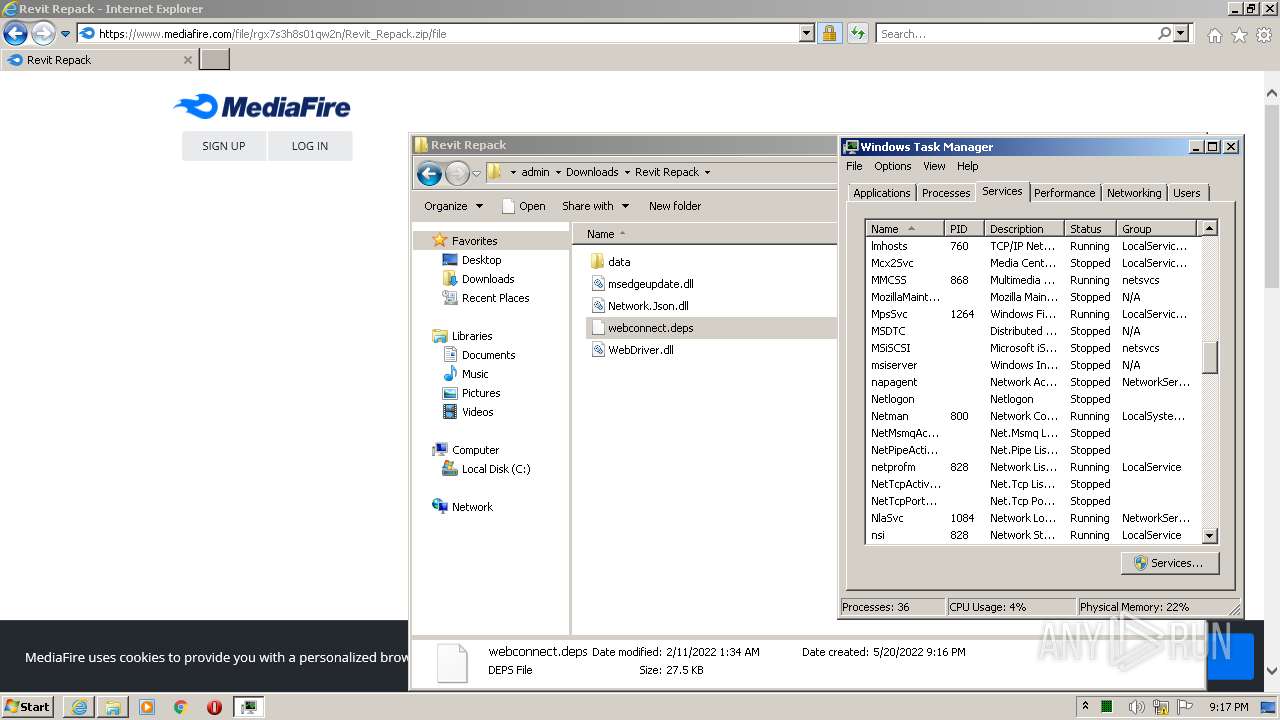
Total processes
75
Monitored processes
30
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
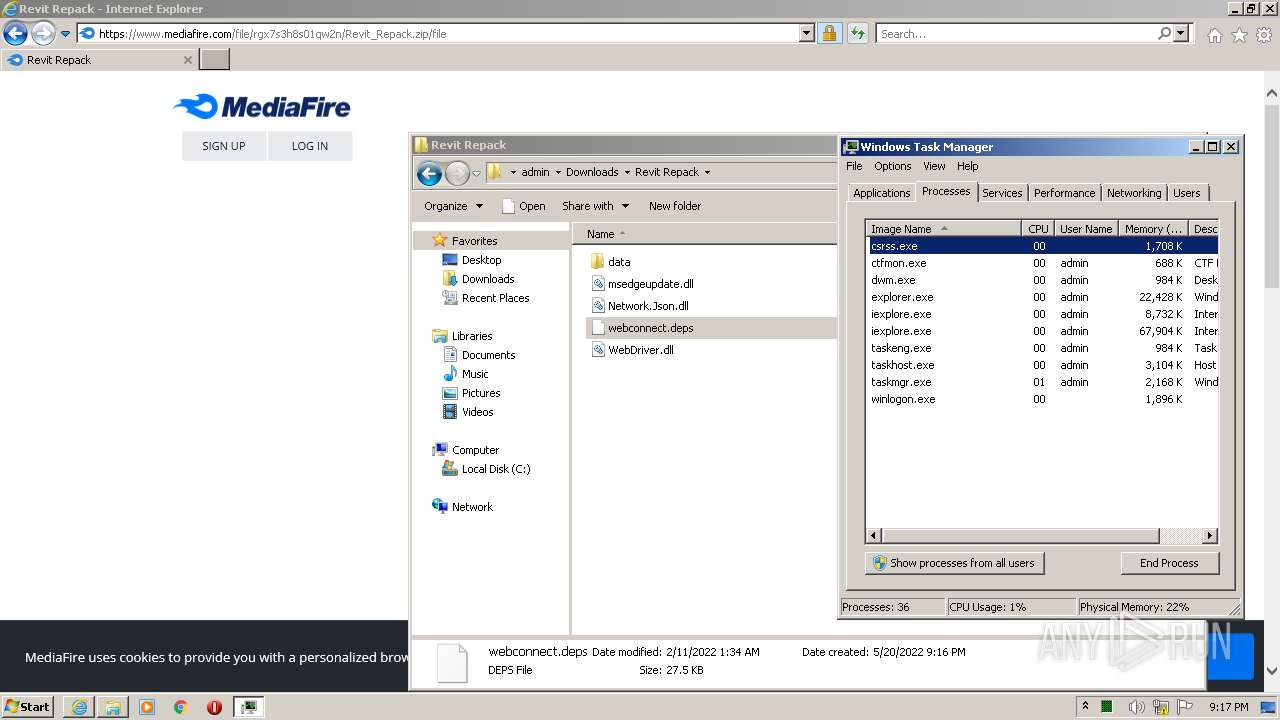
| 120 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 472 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -enc UwB0AGEAcgB0AC0AUwBsAGUAZQBwACAALQBzACAAMQAwADsAIABSAGUAbQBvAHYAZQAtAEkAdABlAG0AIAAtAFAAYQB0AGgAIAAiAEMAOgBcAFUAcwBlAHIAcwBcAGEAZABtAGkAbgBcAEQAbwB3AG4AbABvAGEAZABzAFwAUgBlAHYAaQB0ACAAUgBlAHAAYQBjAGsAXABSAGUAdgBpAHQAIABJAG4AcwB0AGEAbABsAGUAcgAgAHgANgA0AC4AZQB4AGUAIgAgAC0ARgBvAHIAYwBlAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Revit Installer x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,8351256612660202848,9362334404203590831,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,8351256612660202848,9362334404203590831,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1164 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1172 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
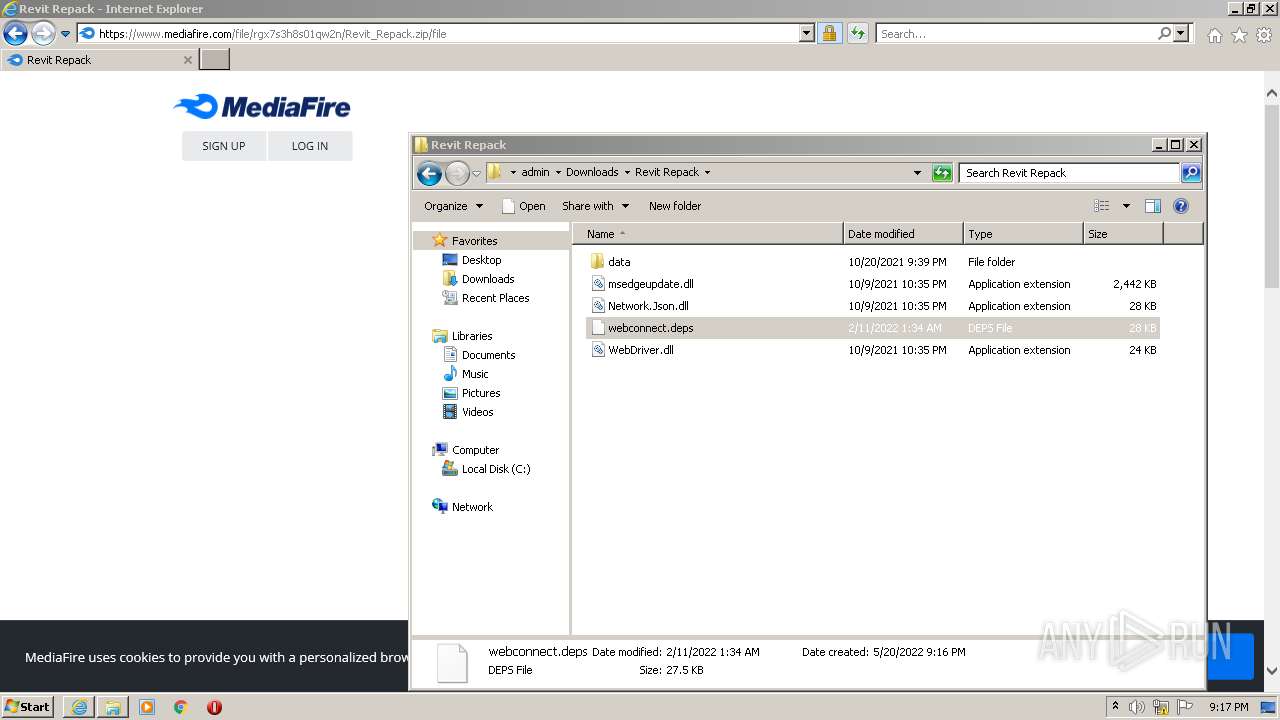
| 1176 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Revit Repack.zip" "C:\Users\admin\Downloads\Revit Repack\" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e8dd988,0x6e8dd998,0x6e8dd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1800 | "C:\Windows\System32\cmd.exe" /c timeout 11 | C:\Windows\System32\cmd.exe | — | Revit Installer x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
51 219
Read events
48 673
Write events
2 537
Delete events
9
Modification events
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960774 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960774 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
7
Suspicious files
86
Text files
161
Unknown types
47
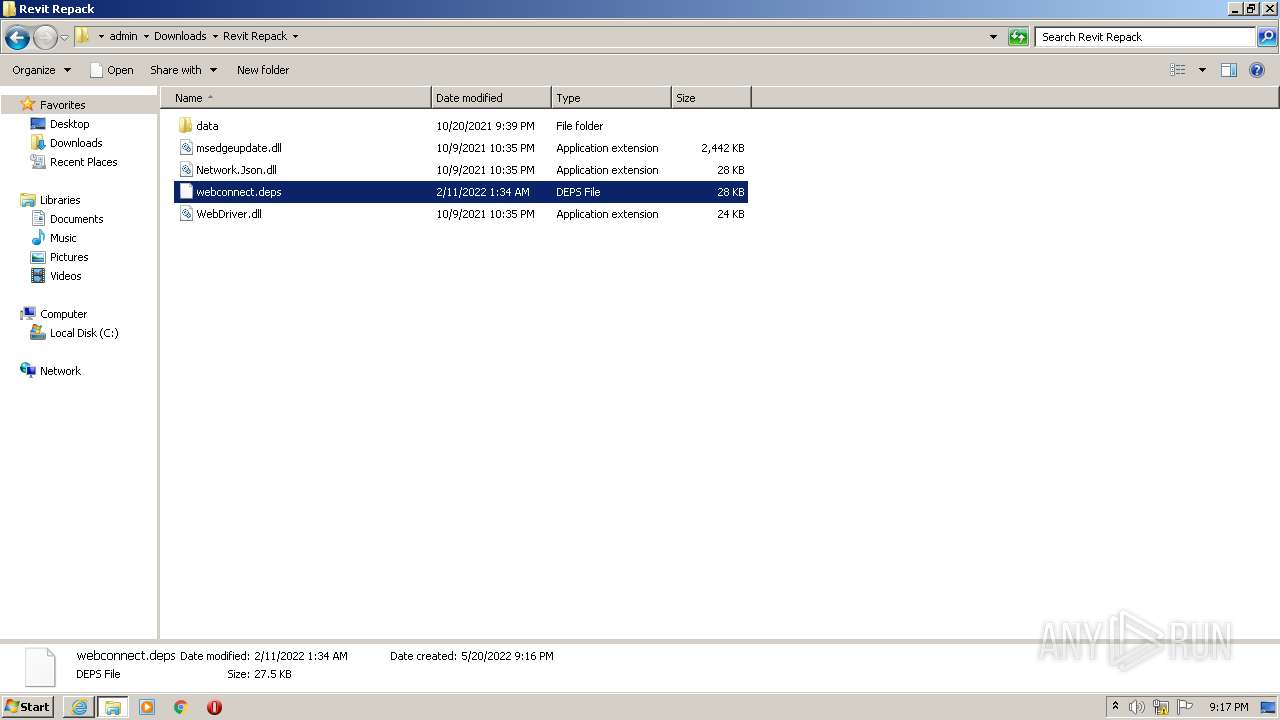
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_7172467AE25B54F1B9D87A9343356E9B | der | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F07644E38ED7C9F37D11EEC6D4335E02_7172467AE25B54F1B9D87A9343356E9B | binary | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\redirect[1].htm | html | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_C86B7000B5CEB7F9146D51D7AB048AFE | der | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\KEJEE6K0.txt | text | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_C86B7000B5CEB7F9146D51D7AB048AFE | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
124
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3000 | iexplore.exe | GET | — | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDwQ9JNOs3IcArkp%2FBu7NbU | US | — | — | whitelisted |
3000 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3000 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDExSUZ712qmxLhqE9UUaDV | US | der | 472 b | whitelisted |
3000 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3000 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAwIlmU1uUKpc1Jl5Pl1QLw%3D | US | der | 471 b | whitelisted |
2220 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3000 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 727 b | whitelisted |
3000 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3000 | iexplore.exe | GET | 200 | 18.161.94.229:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3000 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | iexplore.exe | 142.250.184.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
3000 | iexplore.exe | 23.216.77.69:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
3000 | iexplore.exe | 23.216.77.80:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
3000 | iexplore.exe | 142.250.186.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2220 | iexplore.exe | 142.250.184.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
3000 | iexplore.exe | 142.250.181.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2220 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3000 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2220 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3000 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
cutt.ly |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
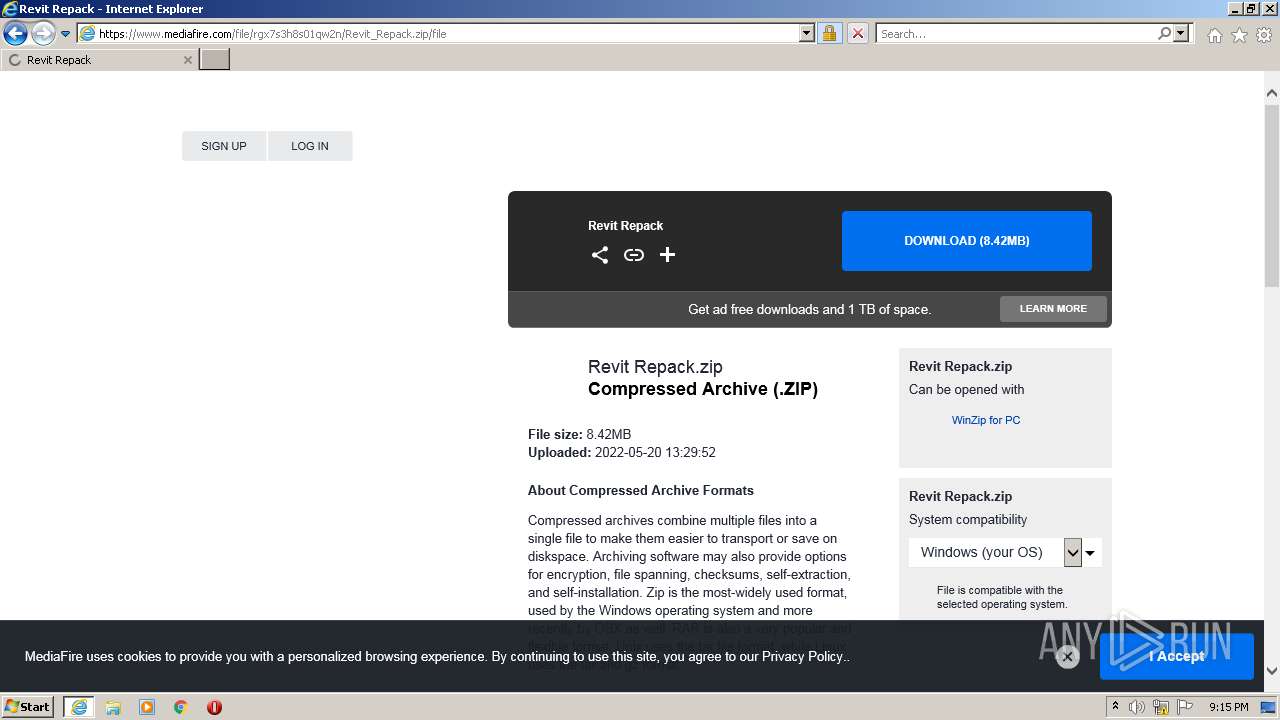
www.mediafire.com |
| shared |
ocsp.comodoca.com |
| whitelisted |
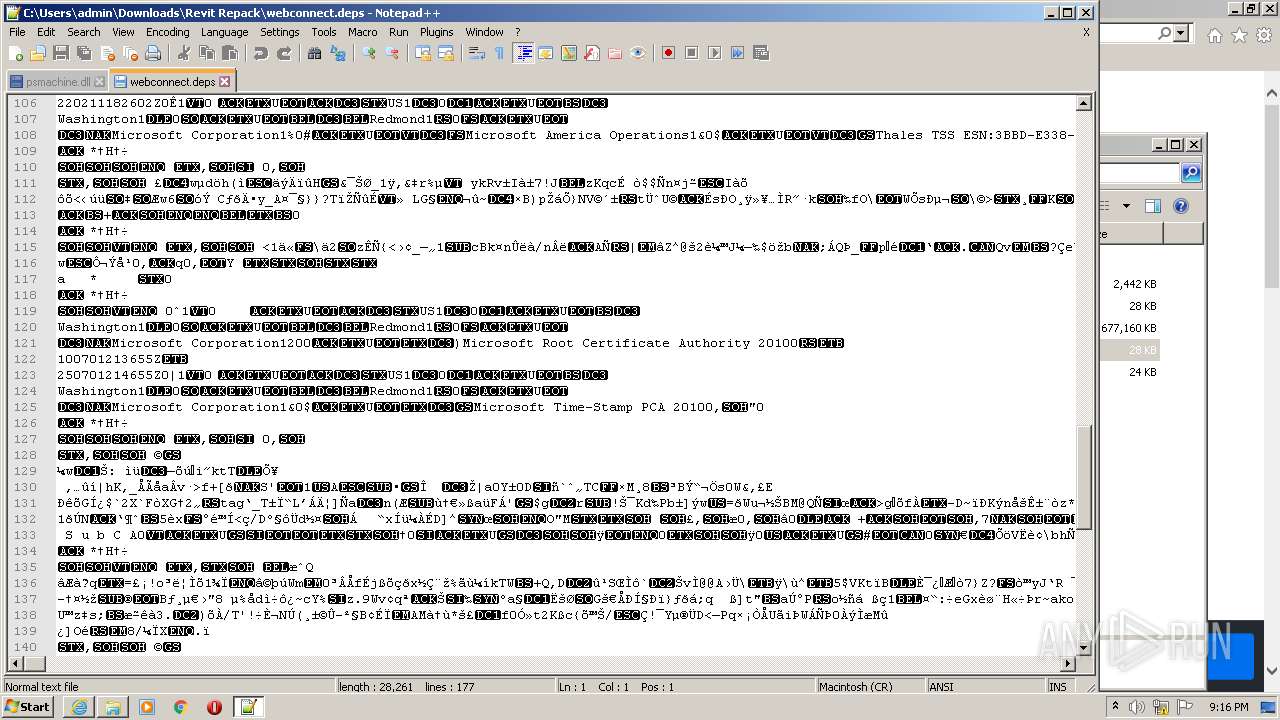
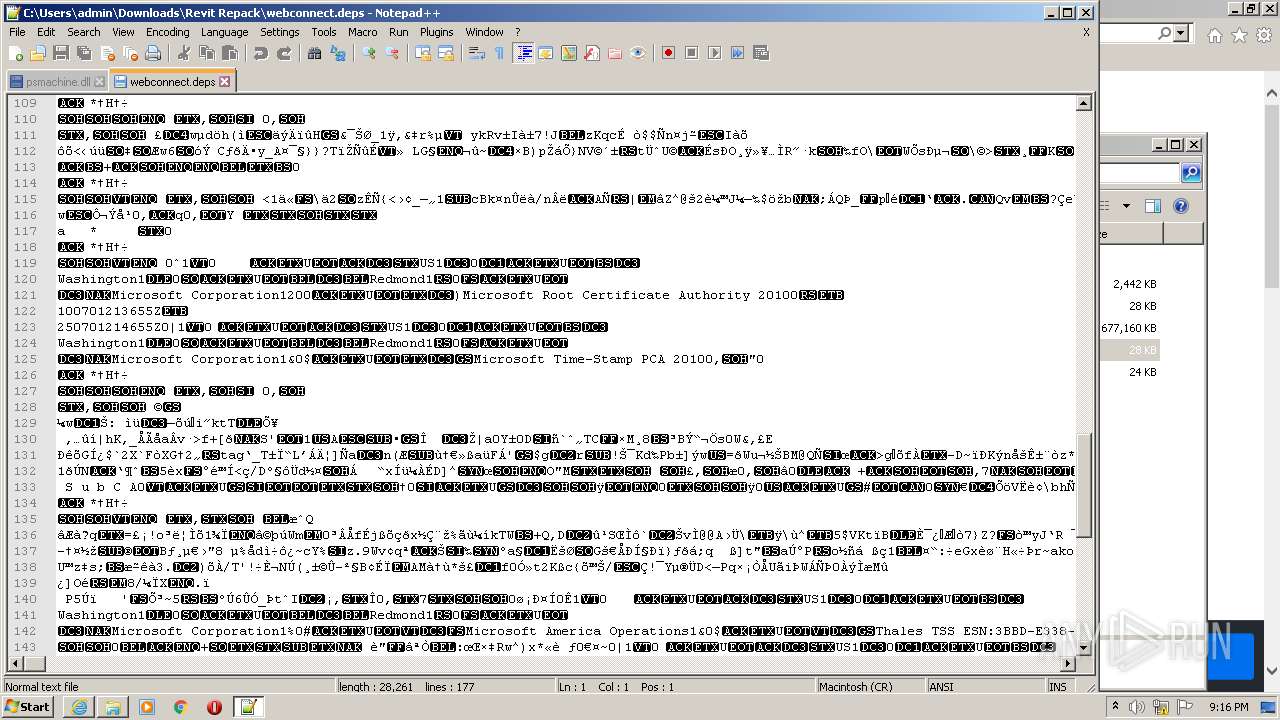
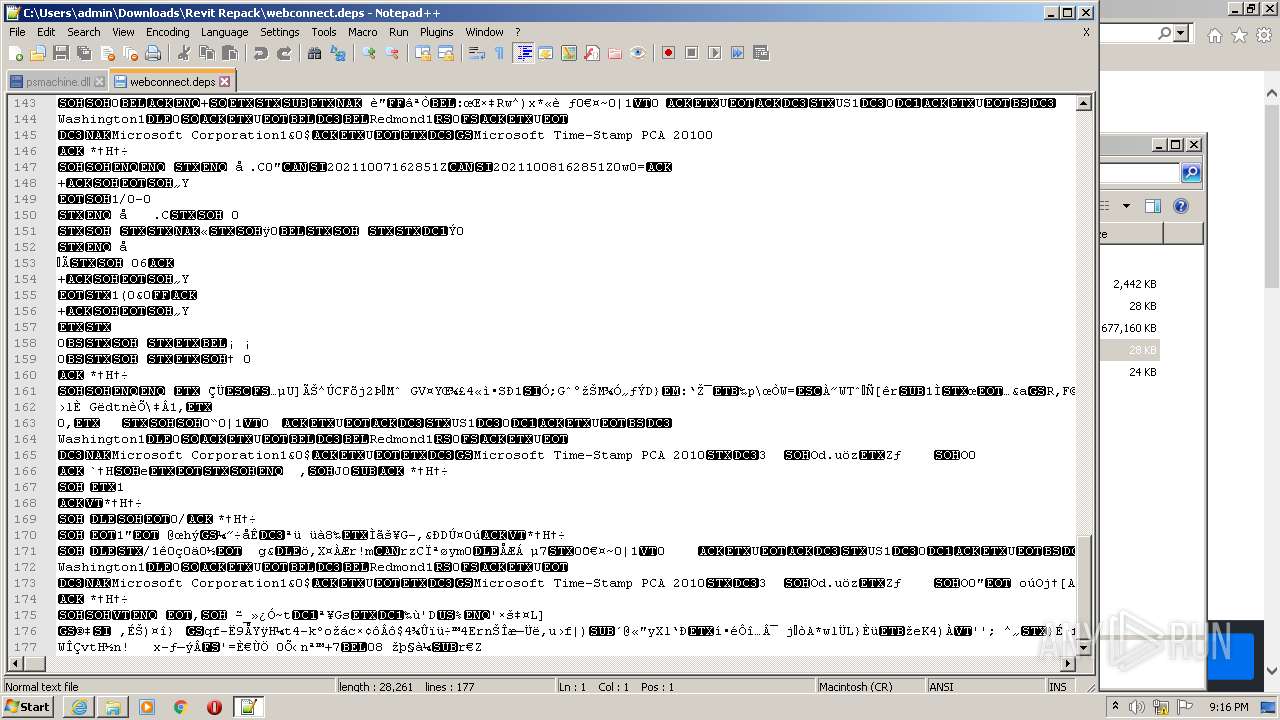
Threats
Process | Message |
|---|---|
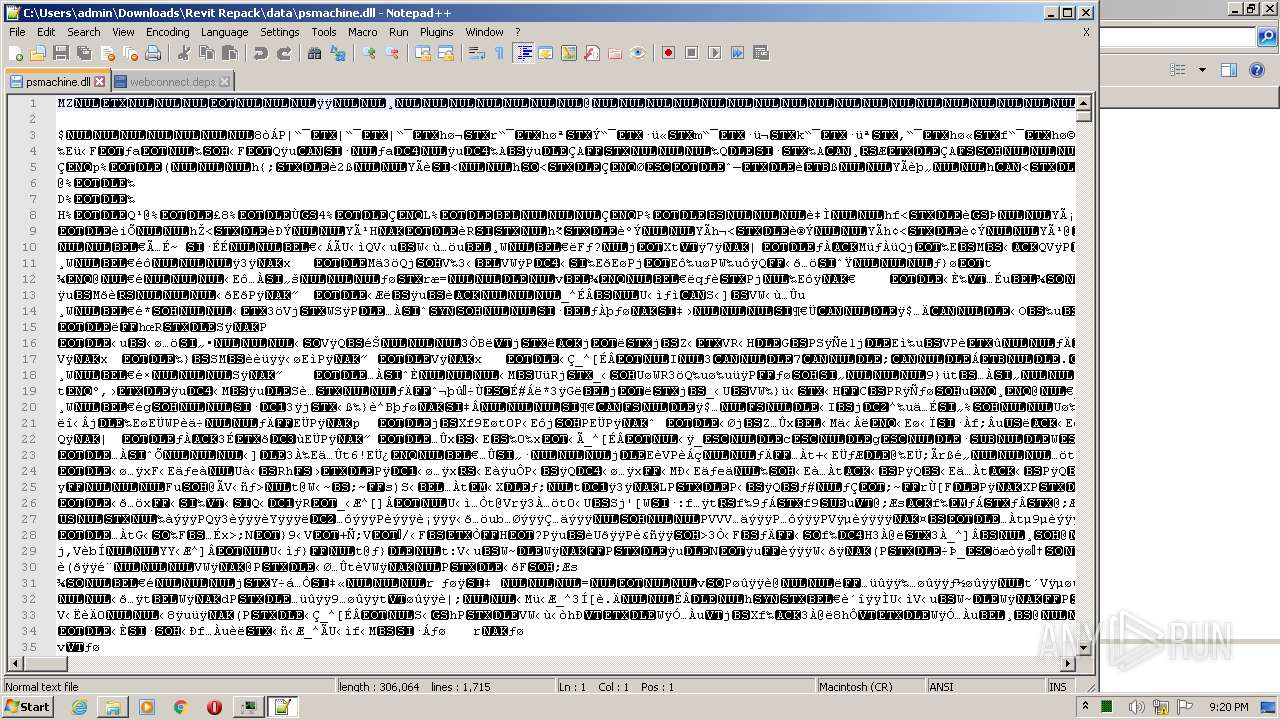
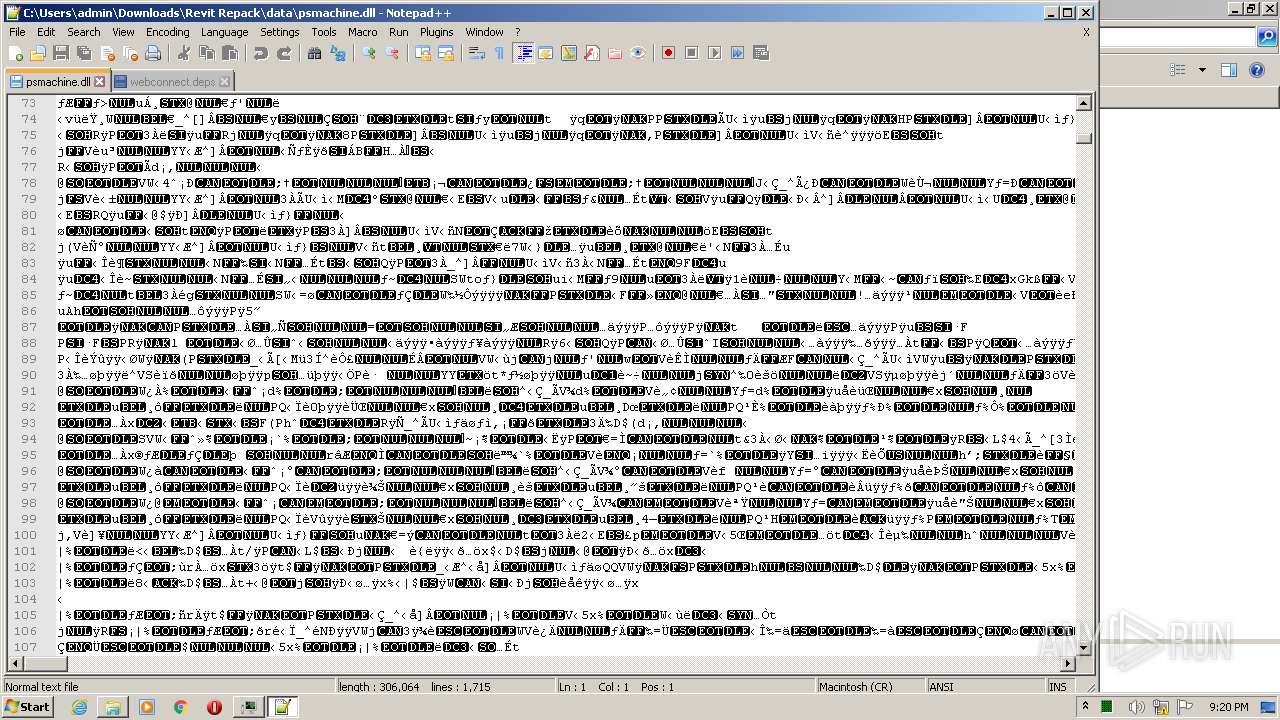
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|