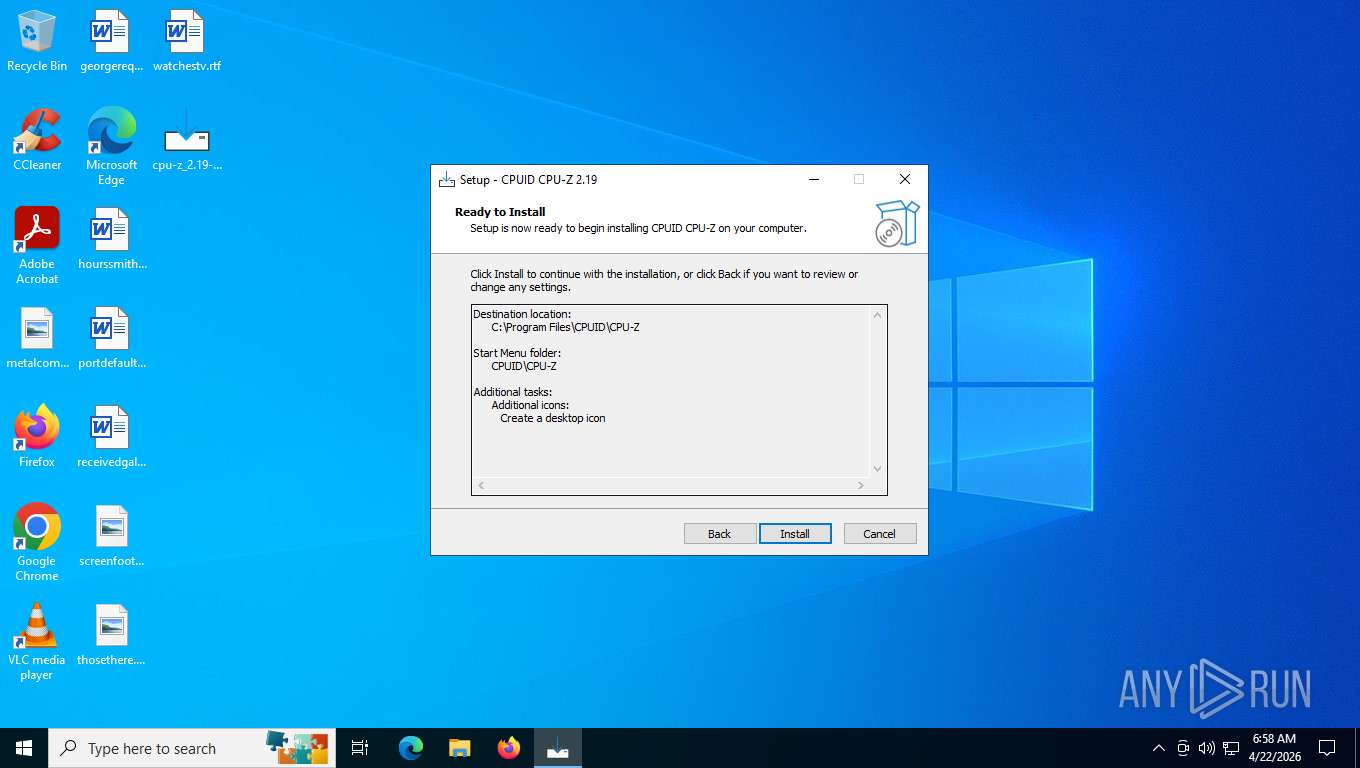
| File name: | cpu-z_2.19-en.malware |
| Full analysis: | https://app.any.run/tasks/fc0285a3-33ed-4c1a-9120-eabdf9bf2afd |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | April 22, 2026, 10:57:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 10 sections |
| MD5: | 291956D1AB3F5FEBF65D0BCCCA19B7FF |
| SHA1: | 179BE7CB7F97A3B52A934FD60904FED1D6B8630B |
| SHA256: | 96AC7864F87A133864293E92F6A3AB4484685470E5BDE82CC8EAF1F974741775 |
| SSDEEP: | 98304:0rq3BdwSTno07ryFY+7/lD3rDZjZ9Ez+H9m5fywZQzevEeSxJEYBMG5w/WHNFH4b:p+ZvyeHaPpHV |
MALICIOUS
GENERIC has been found (auto)
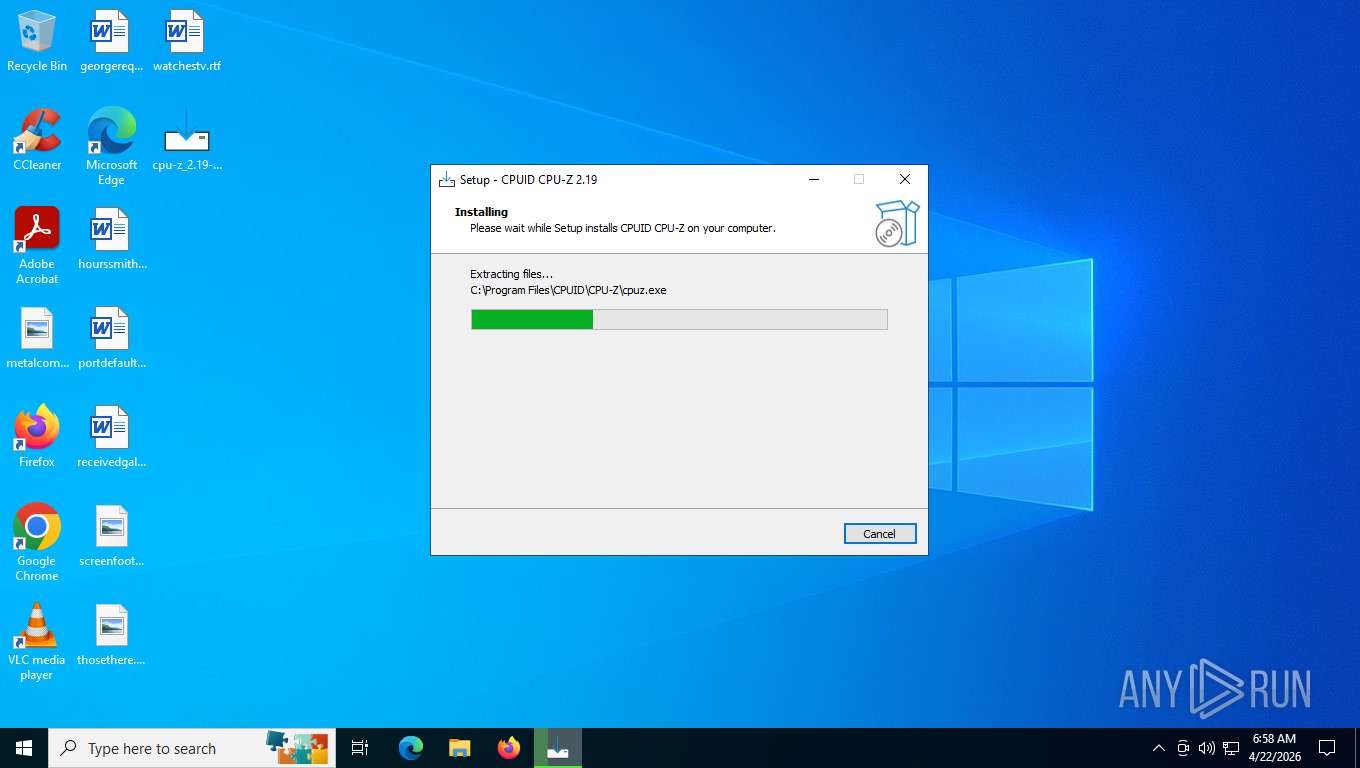
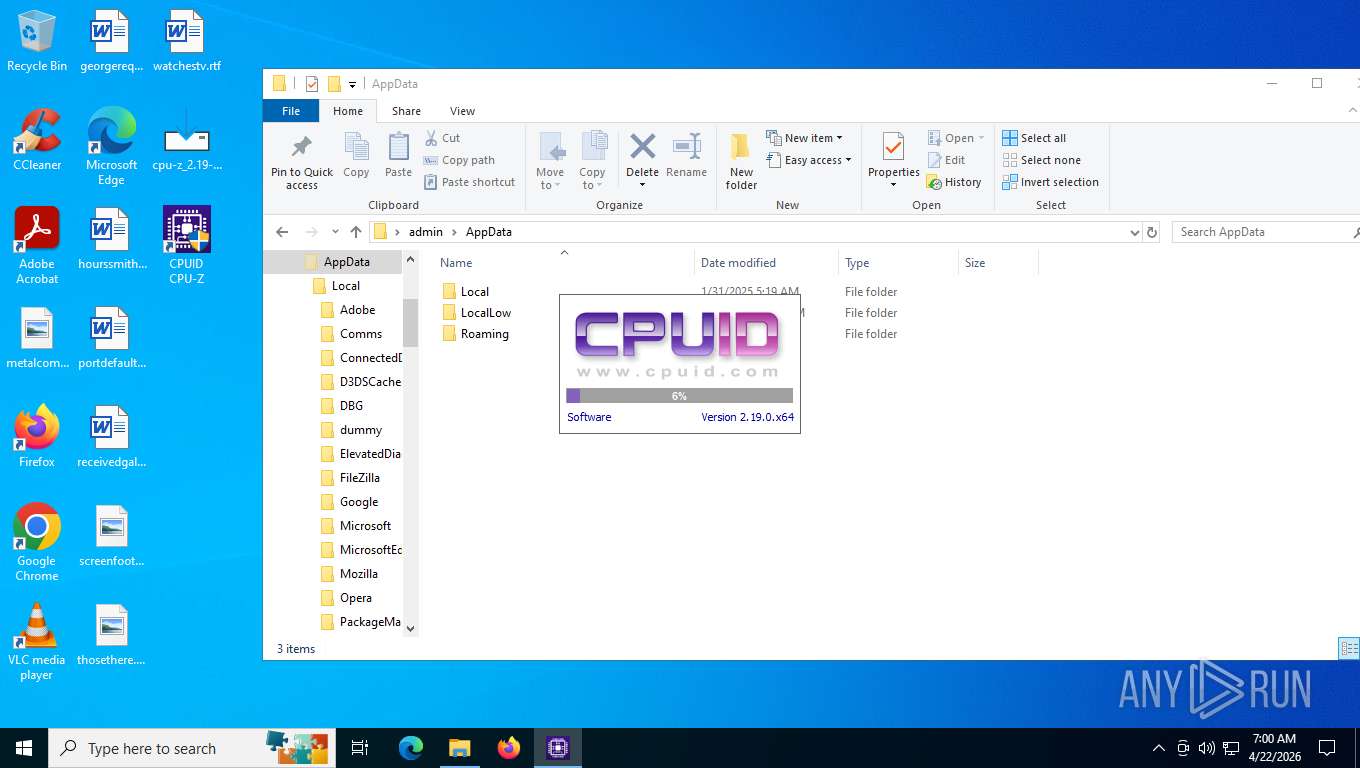
- cpu-z_2.19-en.malware.exe (PID: 6816)
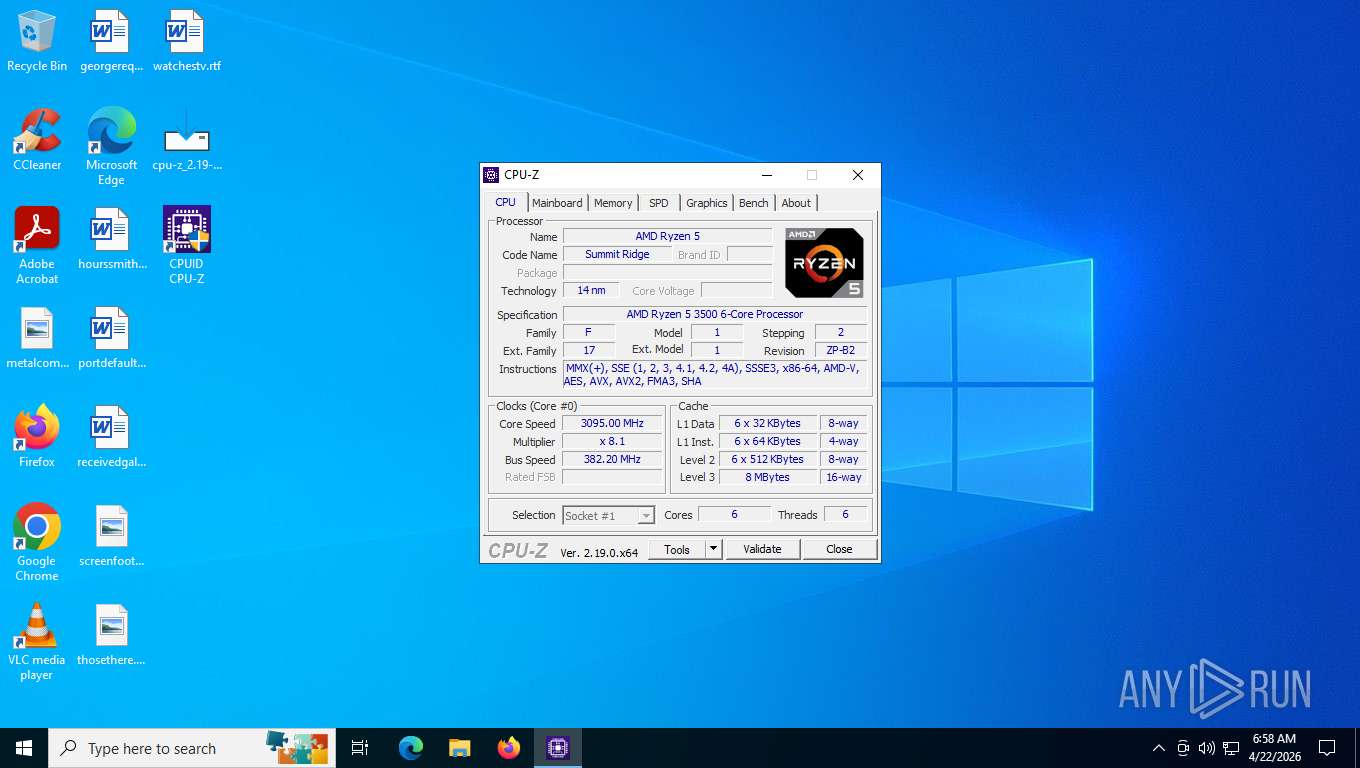
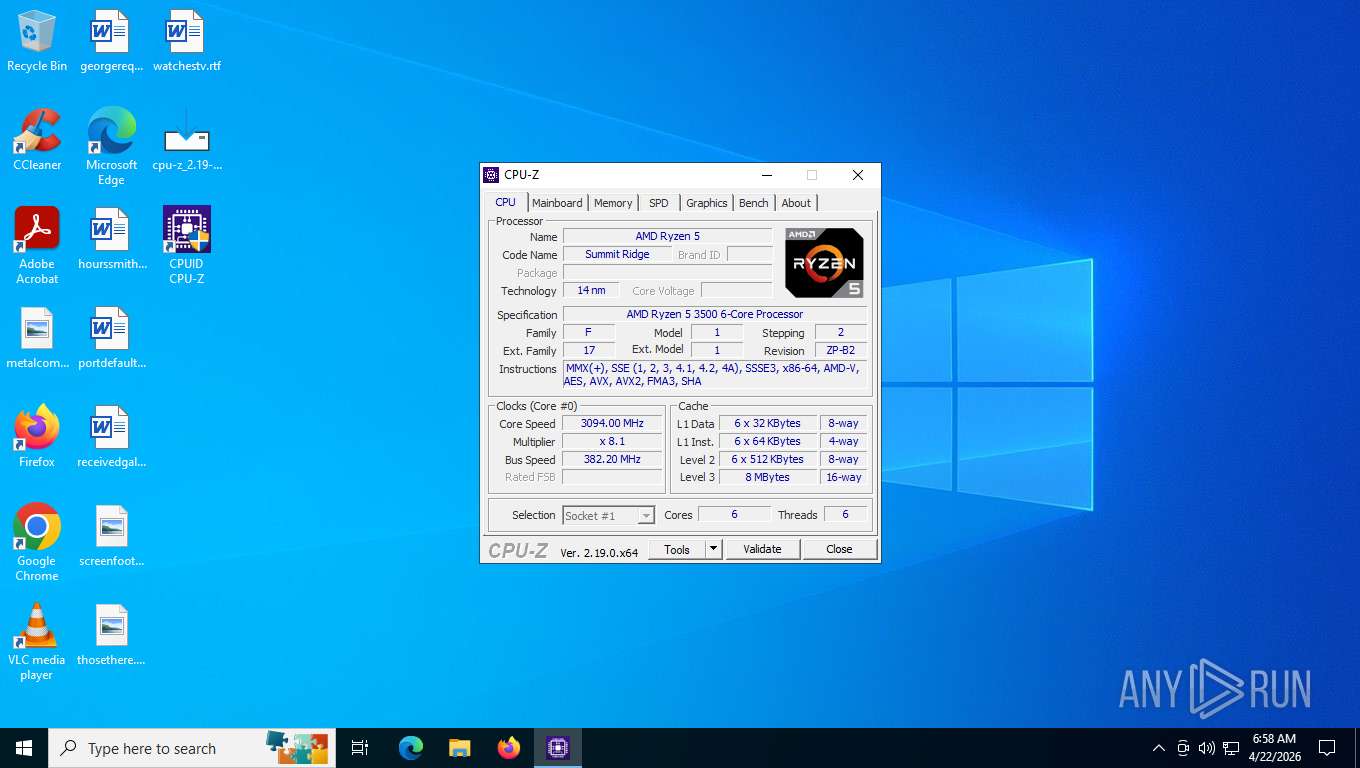
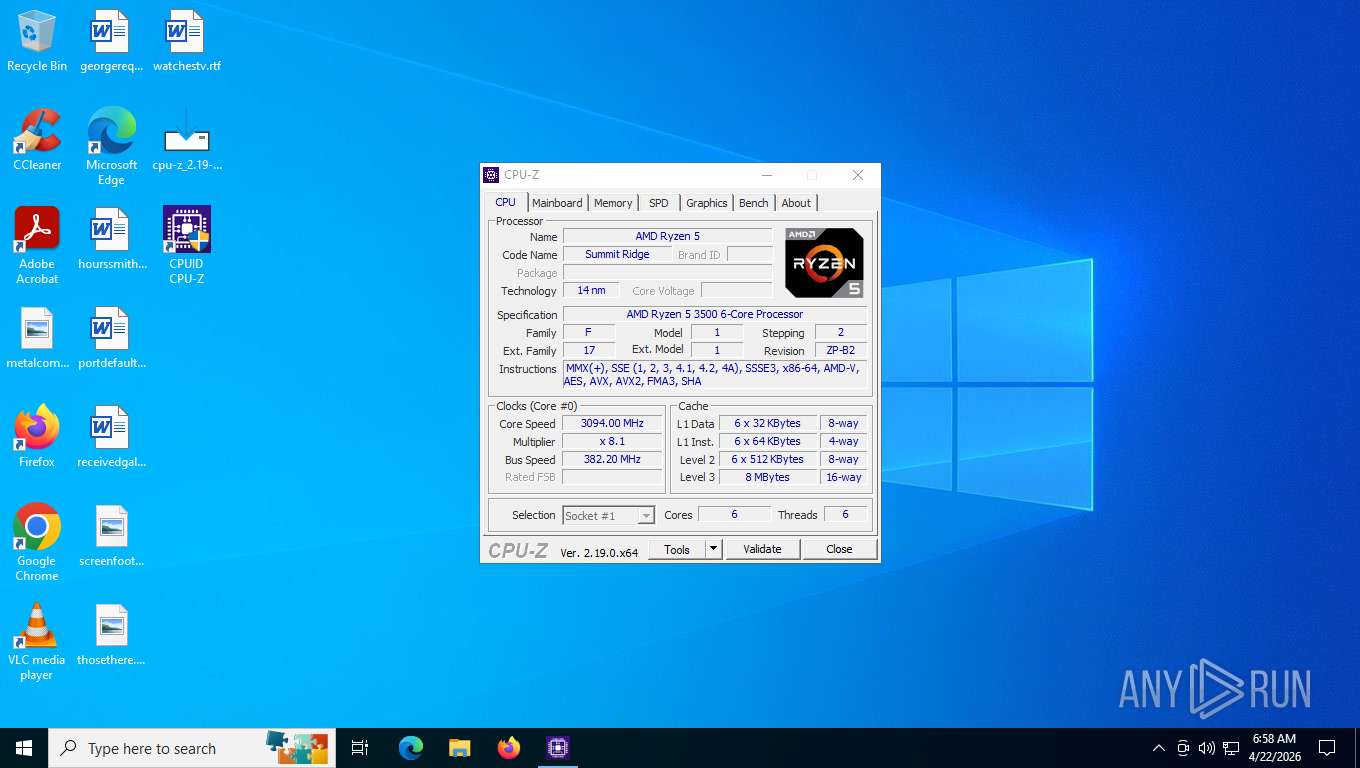
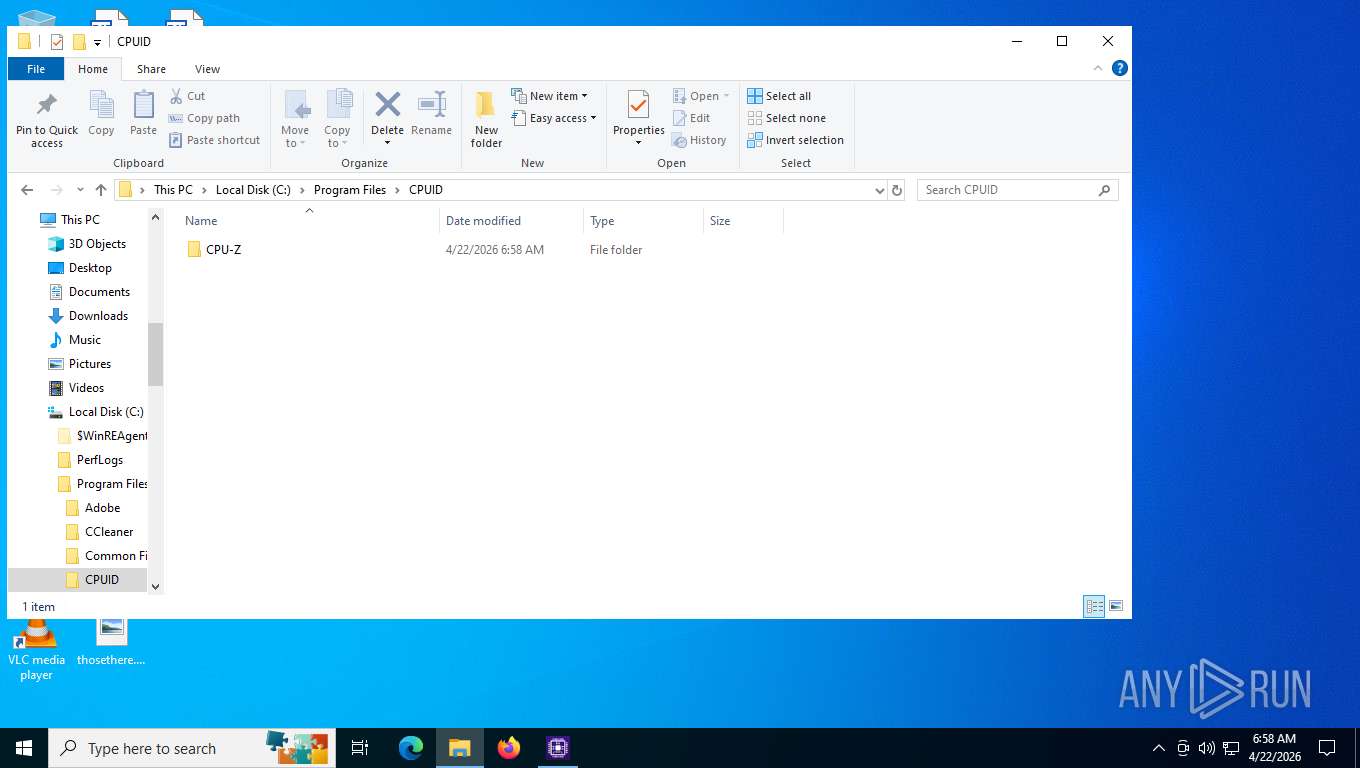
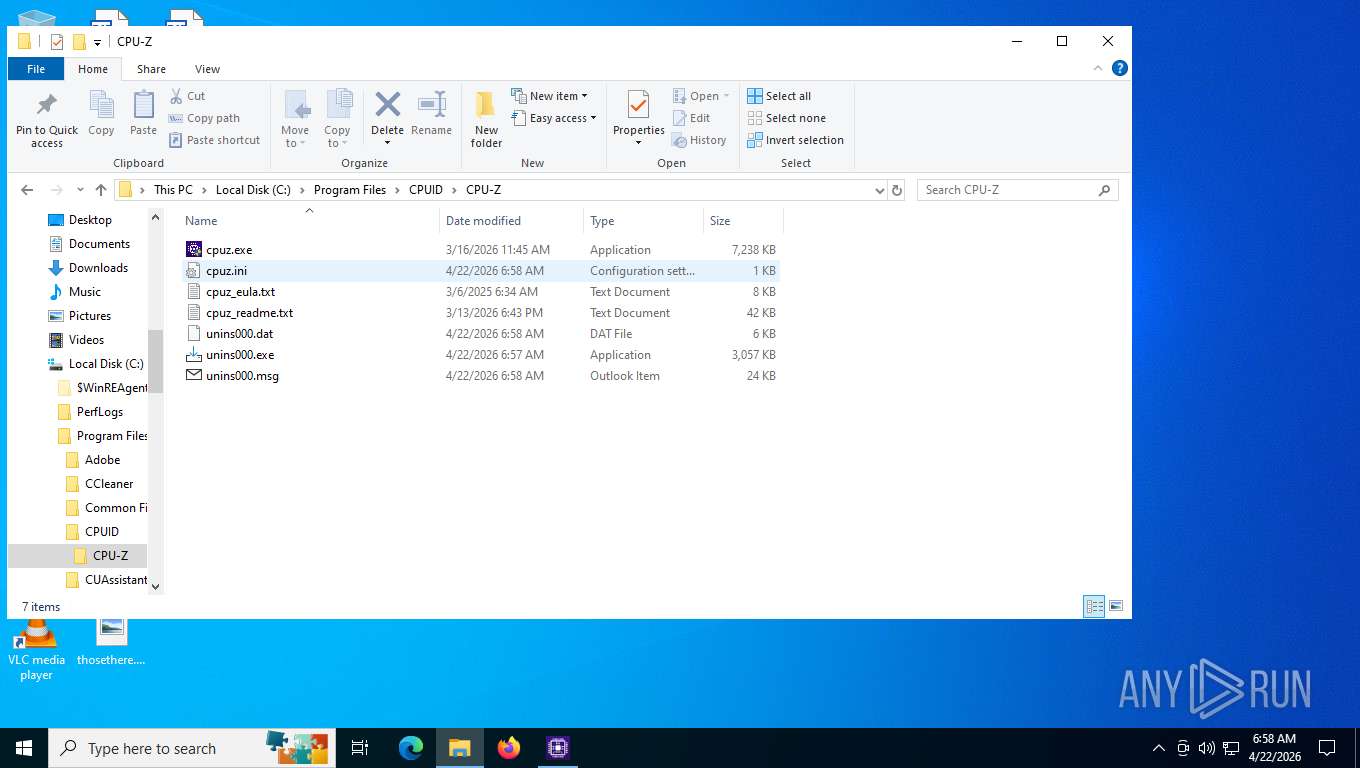
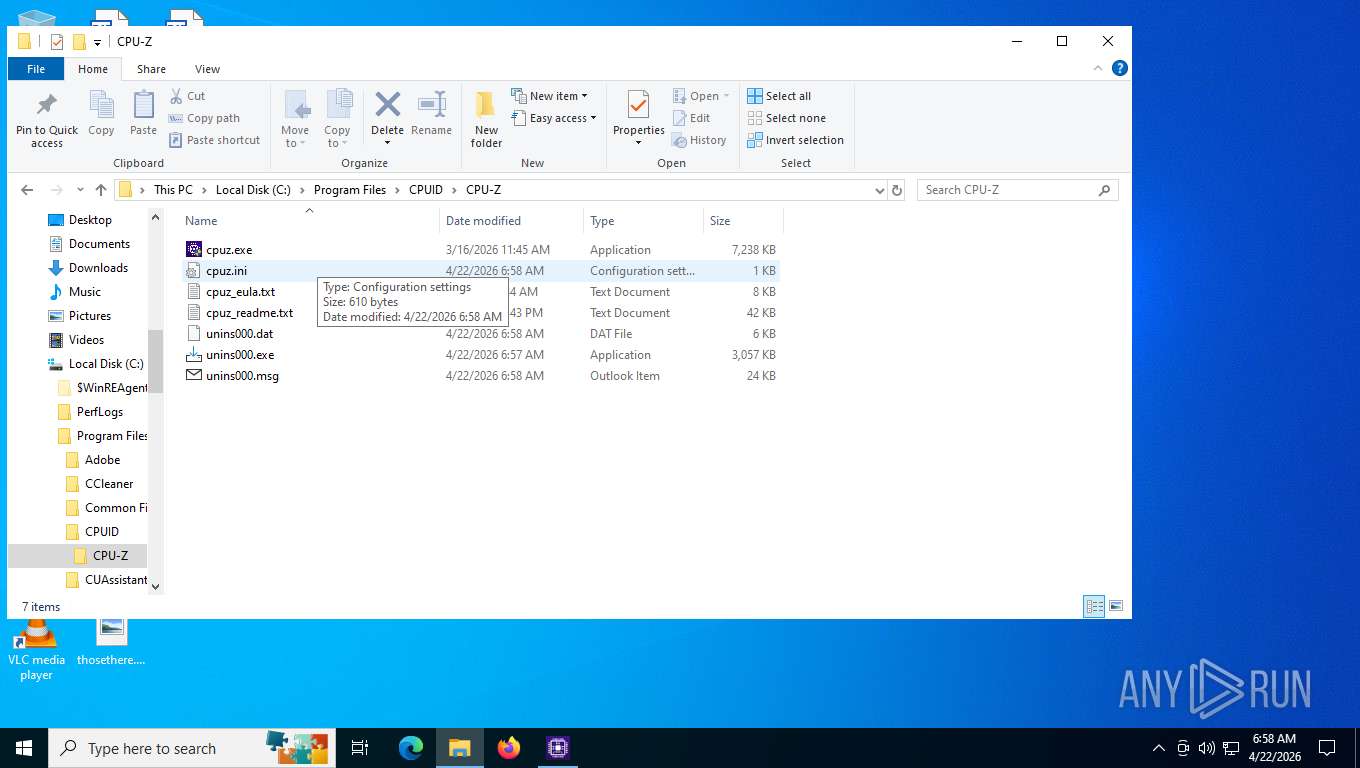
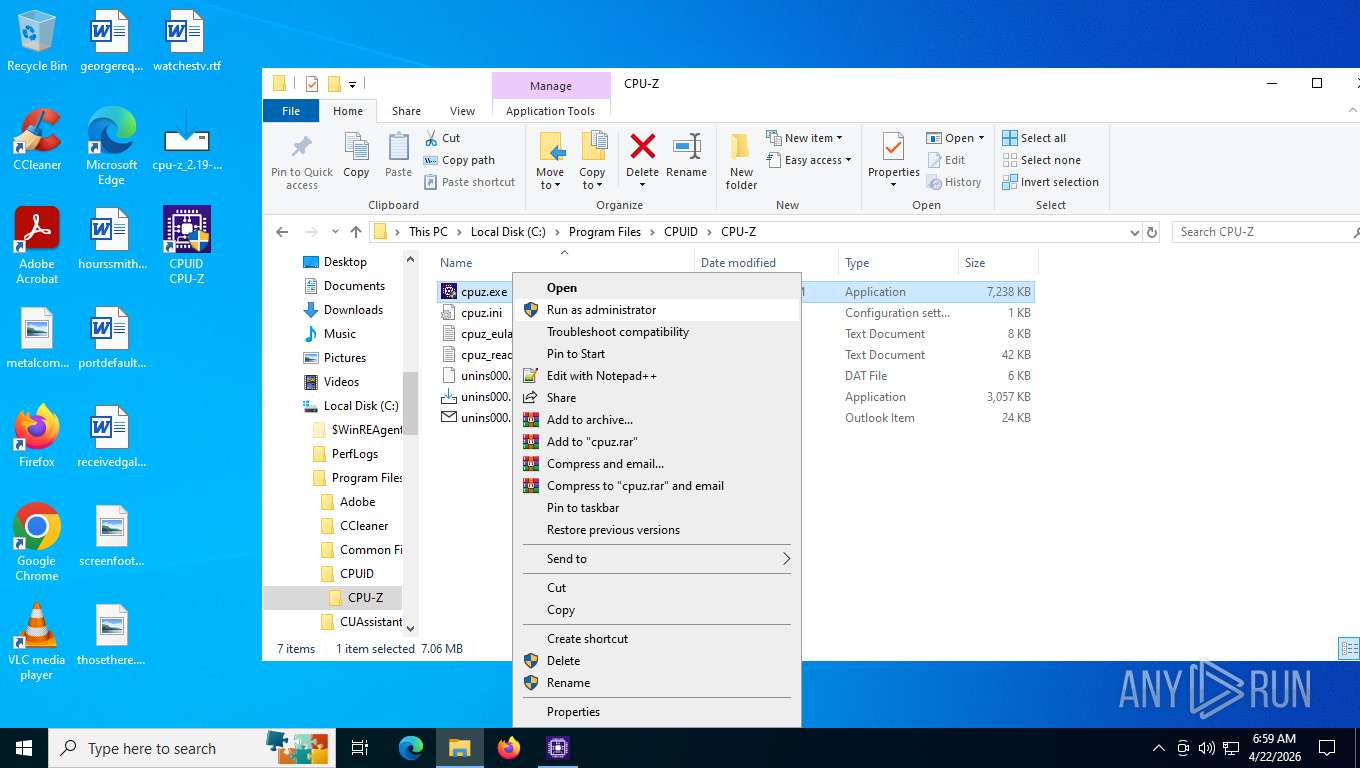
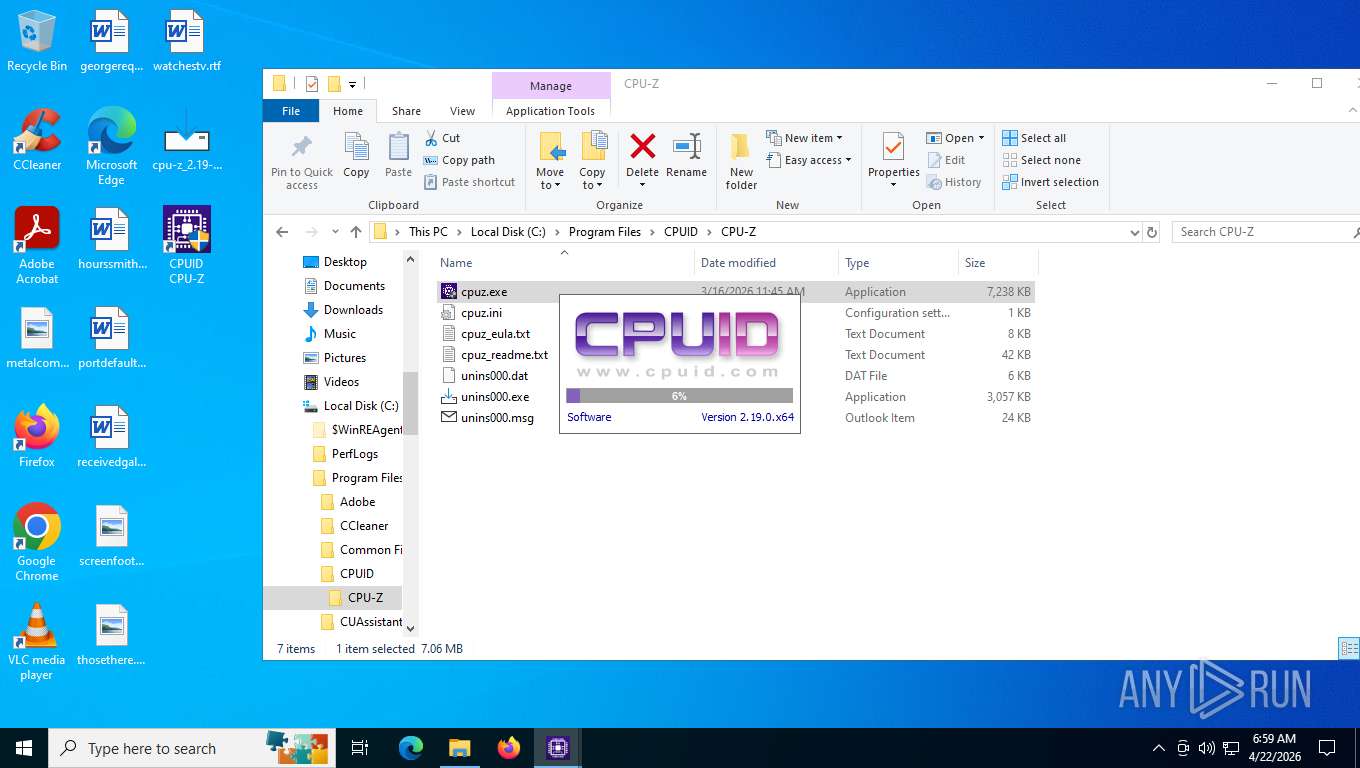
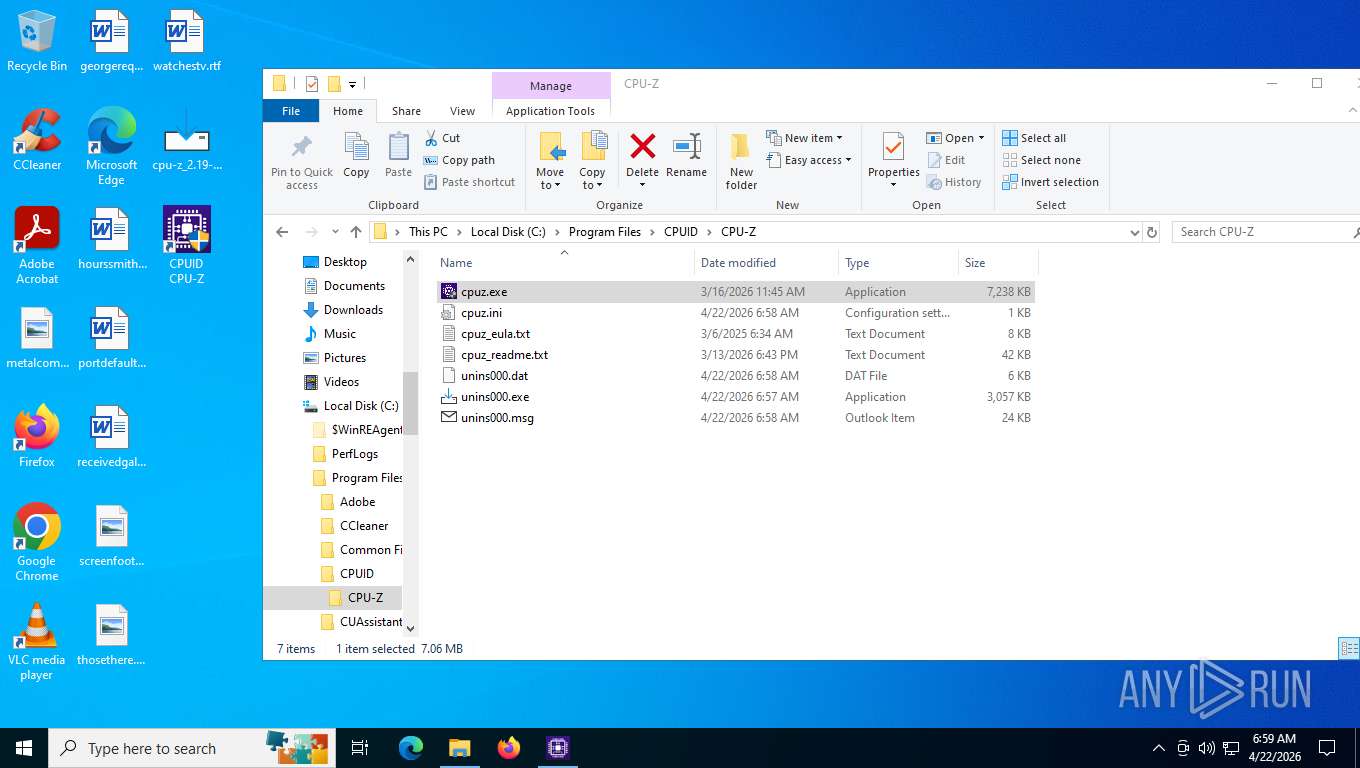
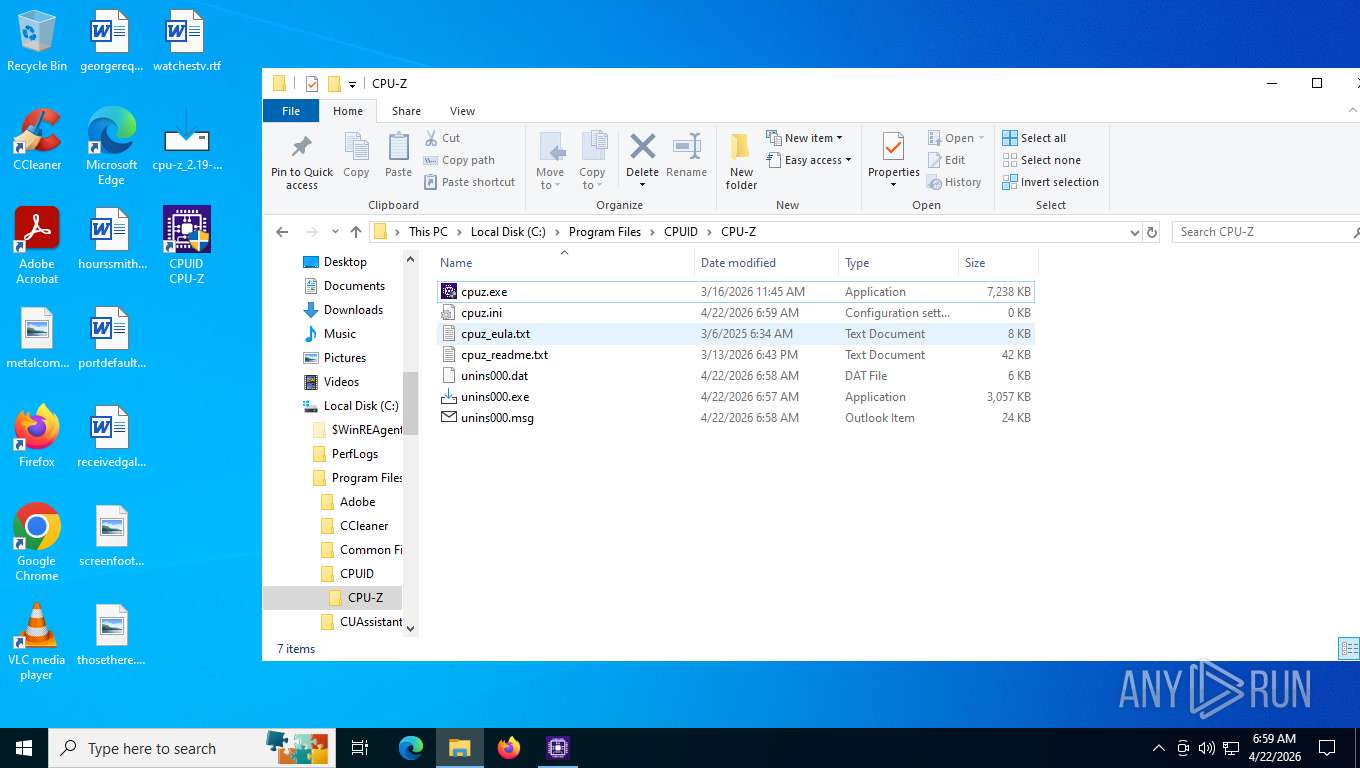
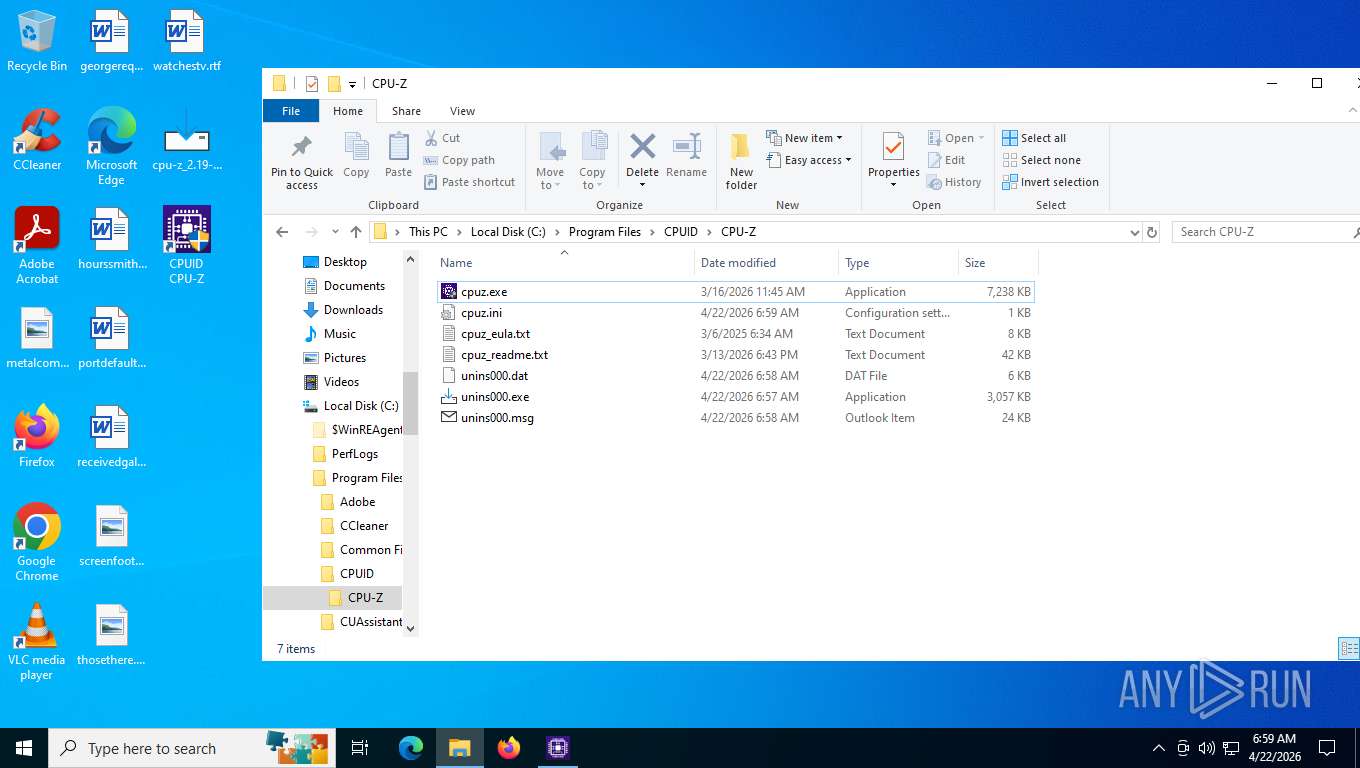
Trojanized CPUID files has been detected
- cpuz.exe (PID: 7420)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 2452)
- cpuz.exe (PID: 7152)
- cpuz.exe (PID: 8088)
SUSPICIOUS
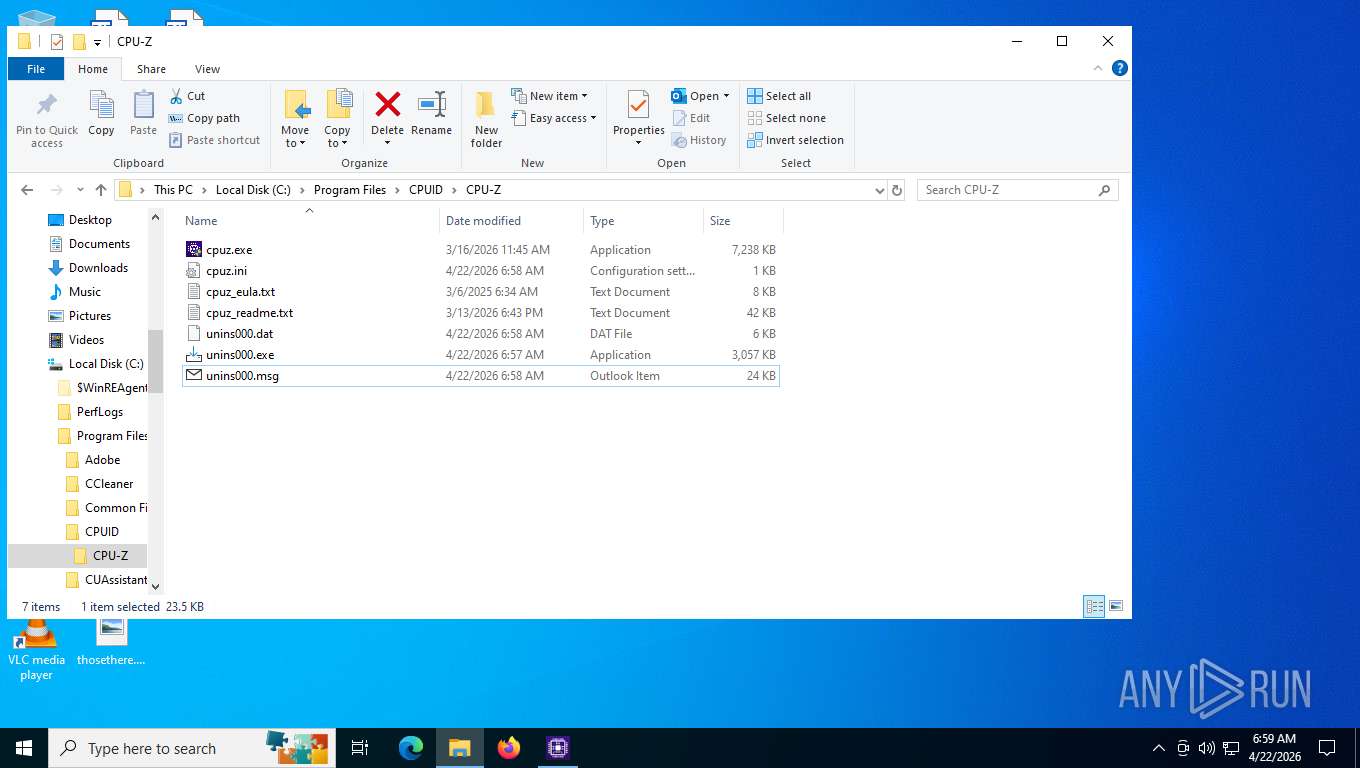
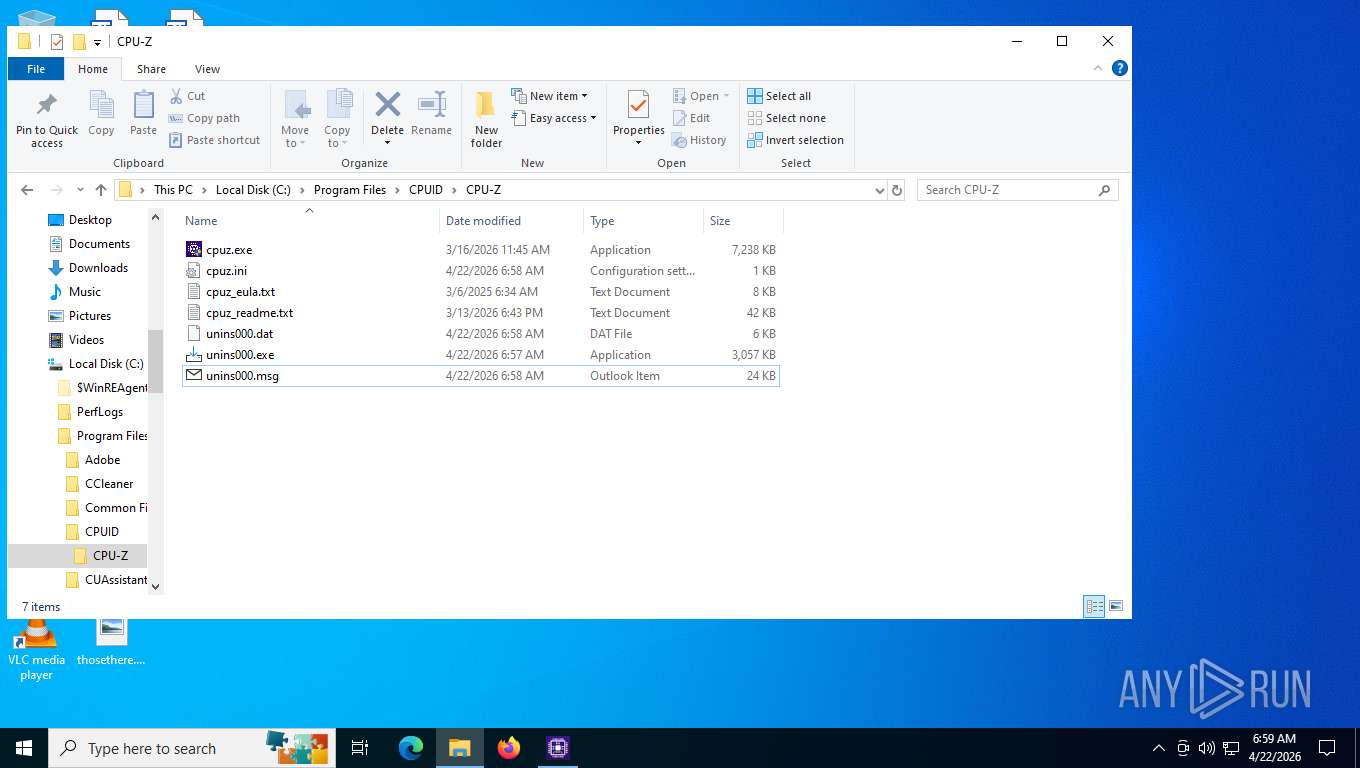
Executable content was dropped or overwritten
- cpu-z_2.19-en.malware.exe (PID: 6816)
- cpu-z_2.19-en.malware.exe (PID: 2452)
- cpu-z_2.19-en.malware.tmp (PID: 3380)
- cpuz.exe (PID: 7420)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 8088)
Reads the Windows owner or organization settings
- cpu-z_2.19-en.malware.tmp (PID: 3380)
Reads the date of Windows installation
- cpuz.exe (PID: 7420)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 2452)
- cpuz.exe (PID: 7152)
- cpuz.exe (PID: 8088)
There is functionality for VM detection VirtualBox (YARA)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 7152)
INFO
Checks supported languages
- cpu-z_2.19-en.malware.exe (PID: 6816)
- cpu-z_2.19-en.malware.tmp (PID: 5384)
- cpu-z_2.19-en.malware.exe (PID: 2452)
- cpu-z_2.19-en.malware.tmp (PID: 3380)
- _setup64.tmp (PID: 996)
- cpuz.exe (PID: 7420)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 2452)
- cpuz.exe (PID: 7152)
- cpuz.exe (PID: 8088)
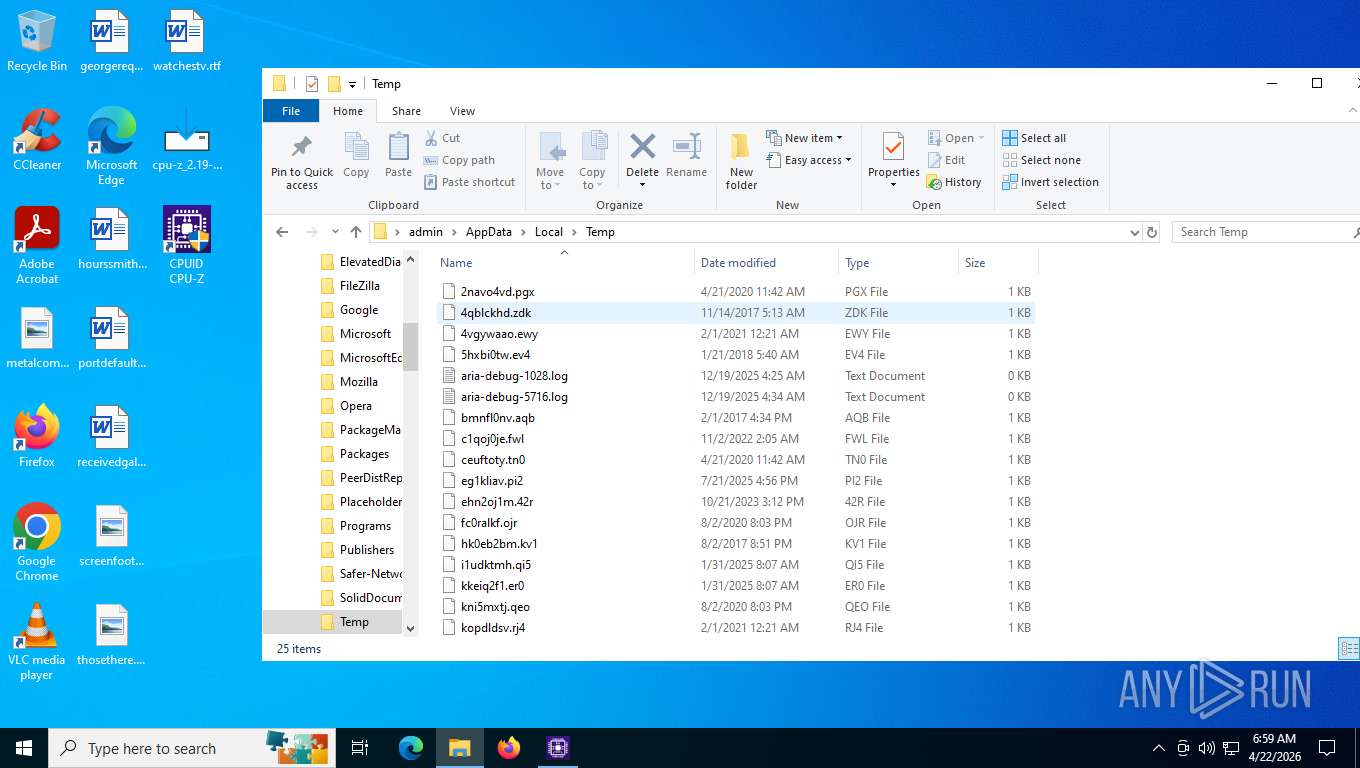
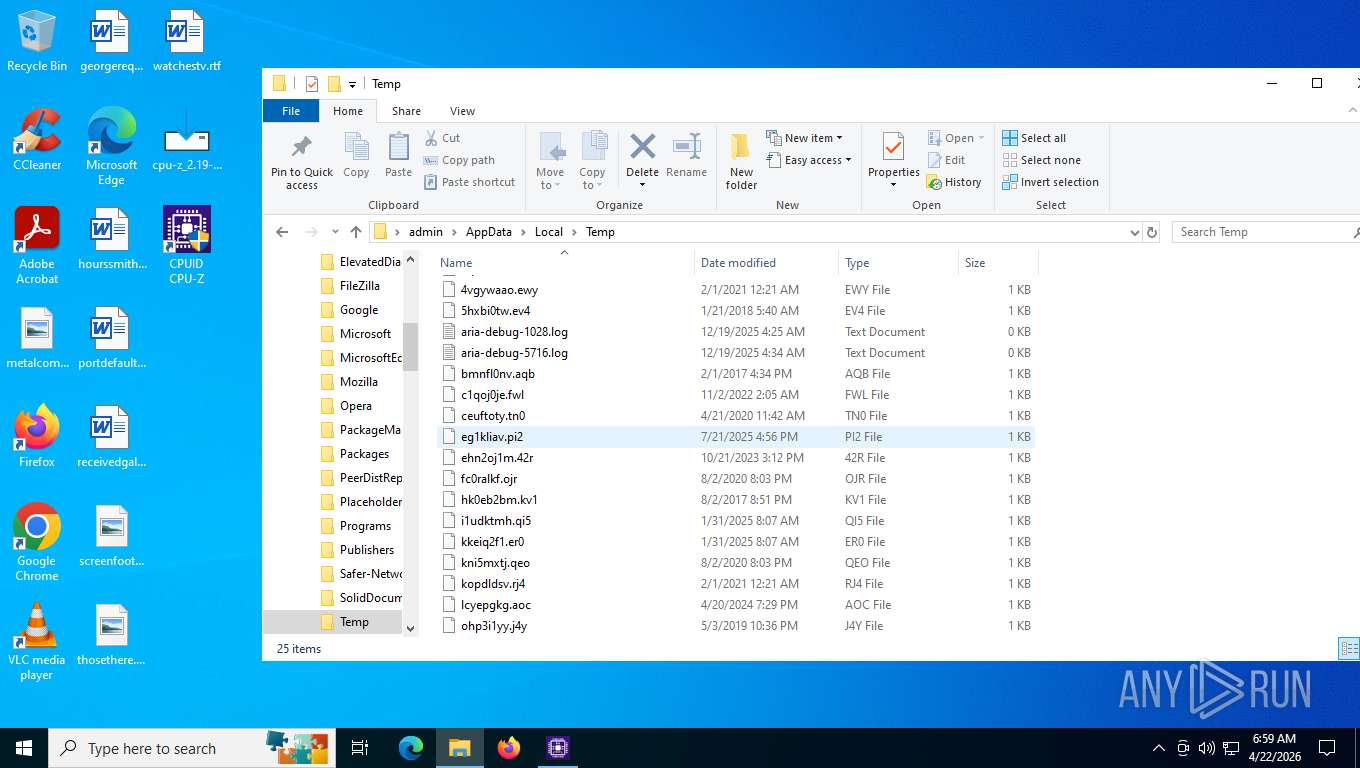
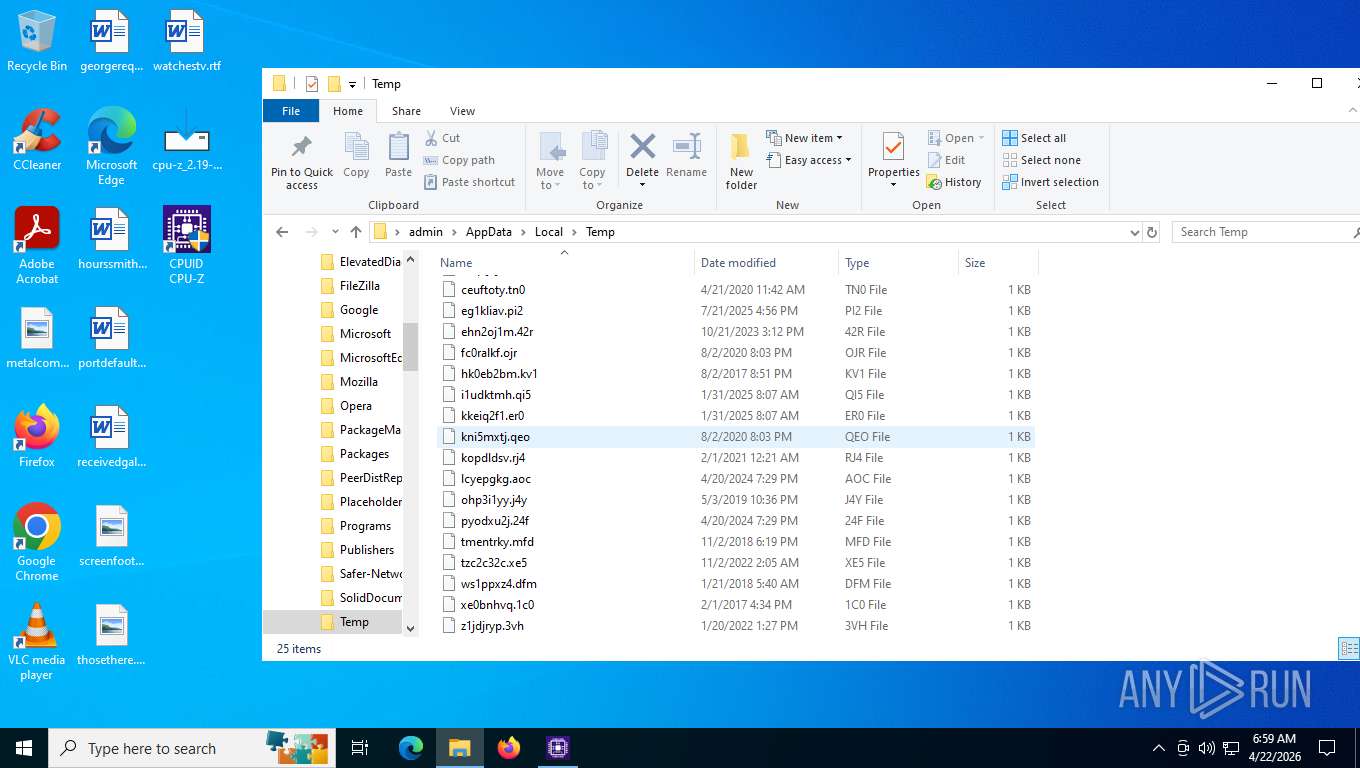
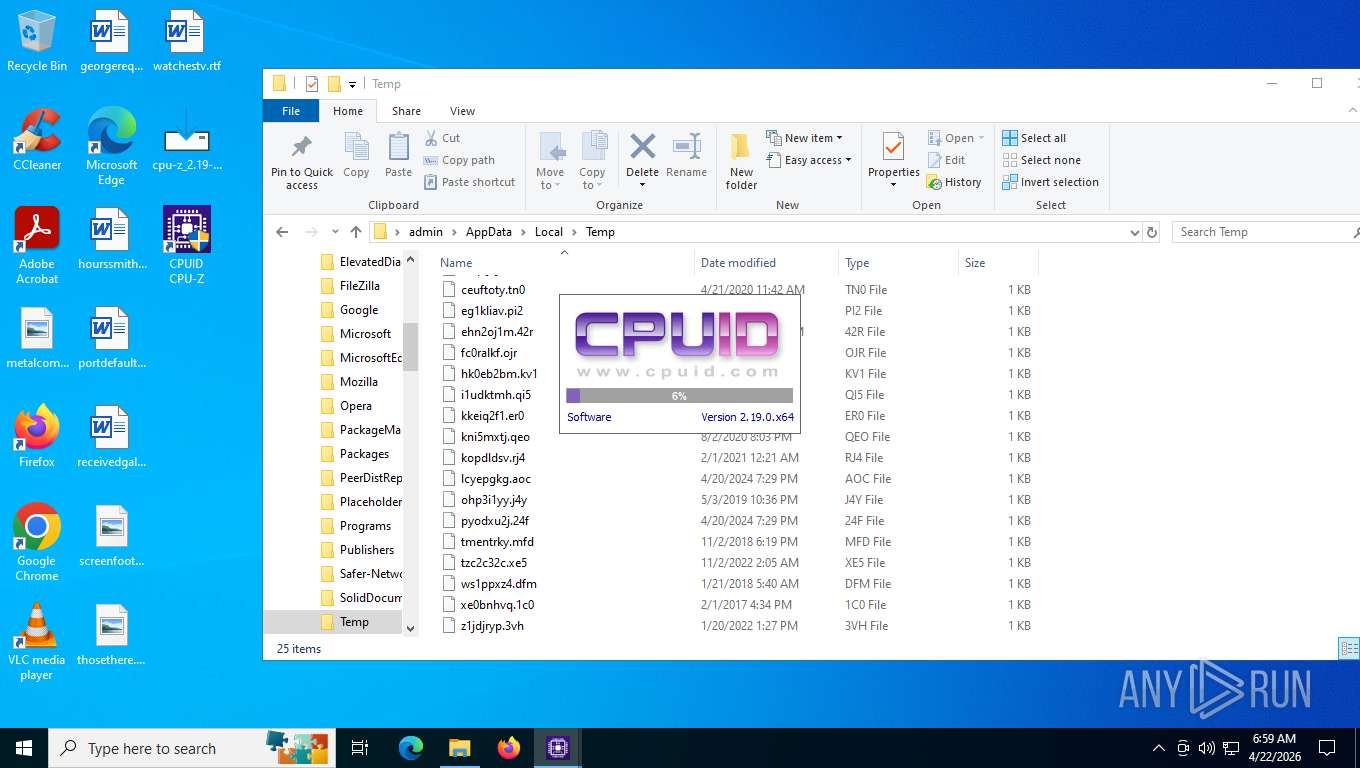
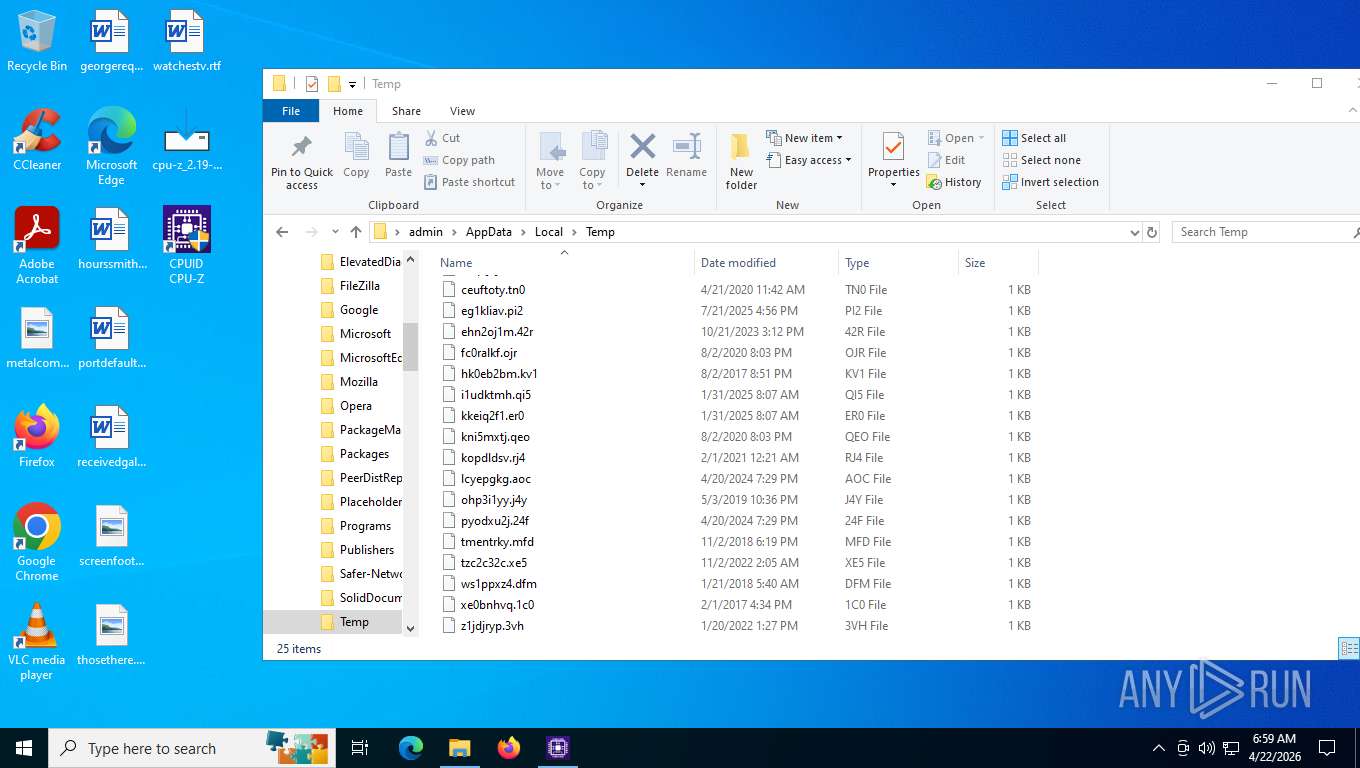
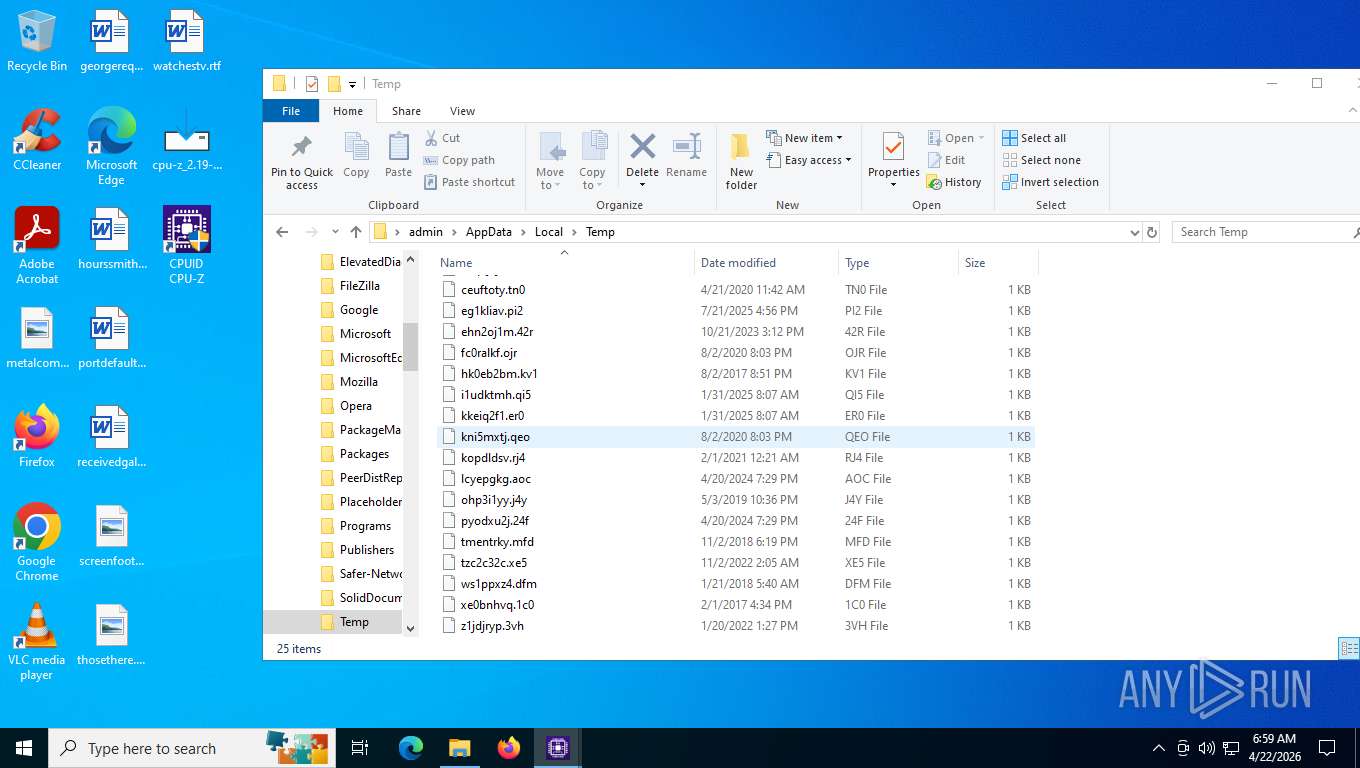
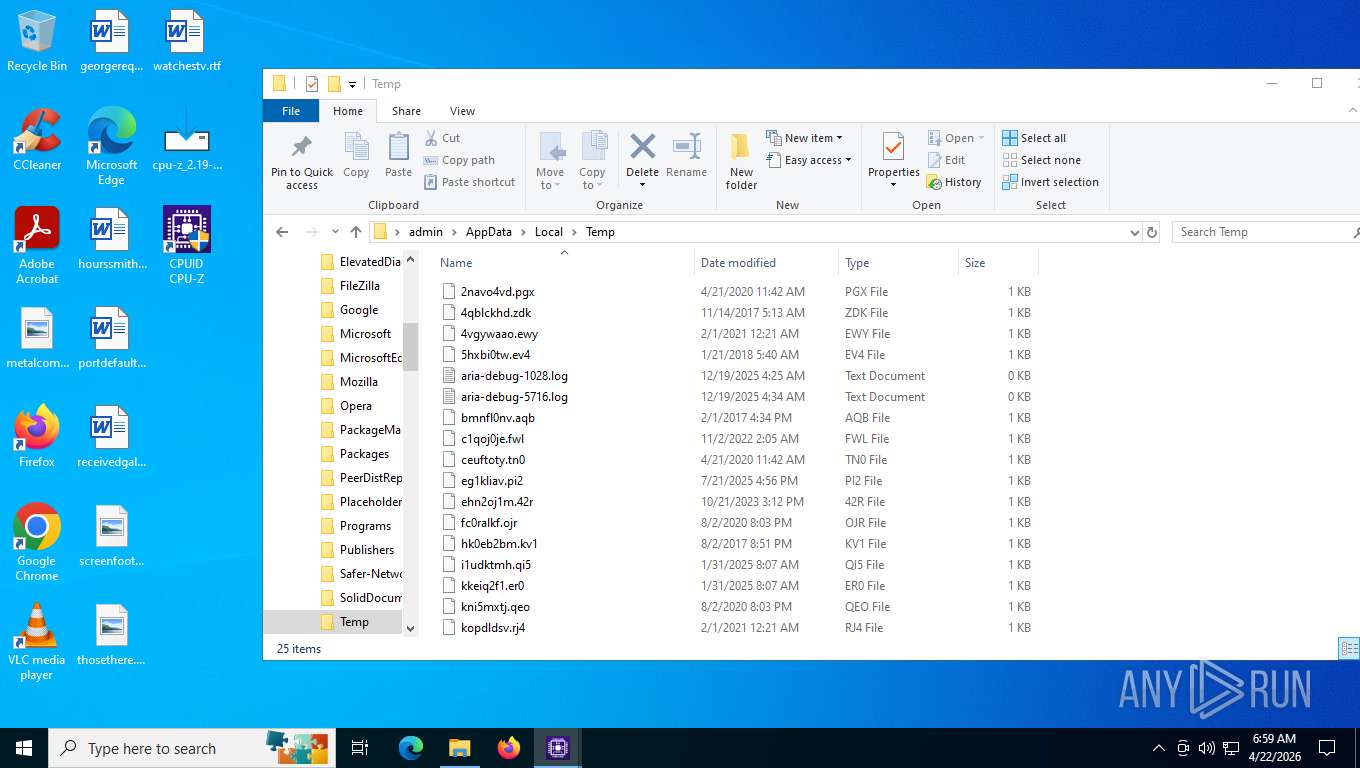
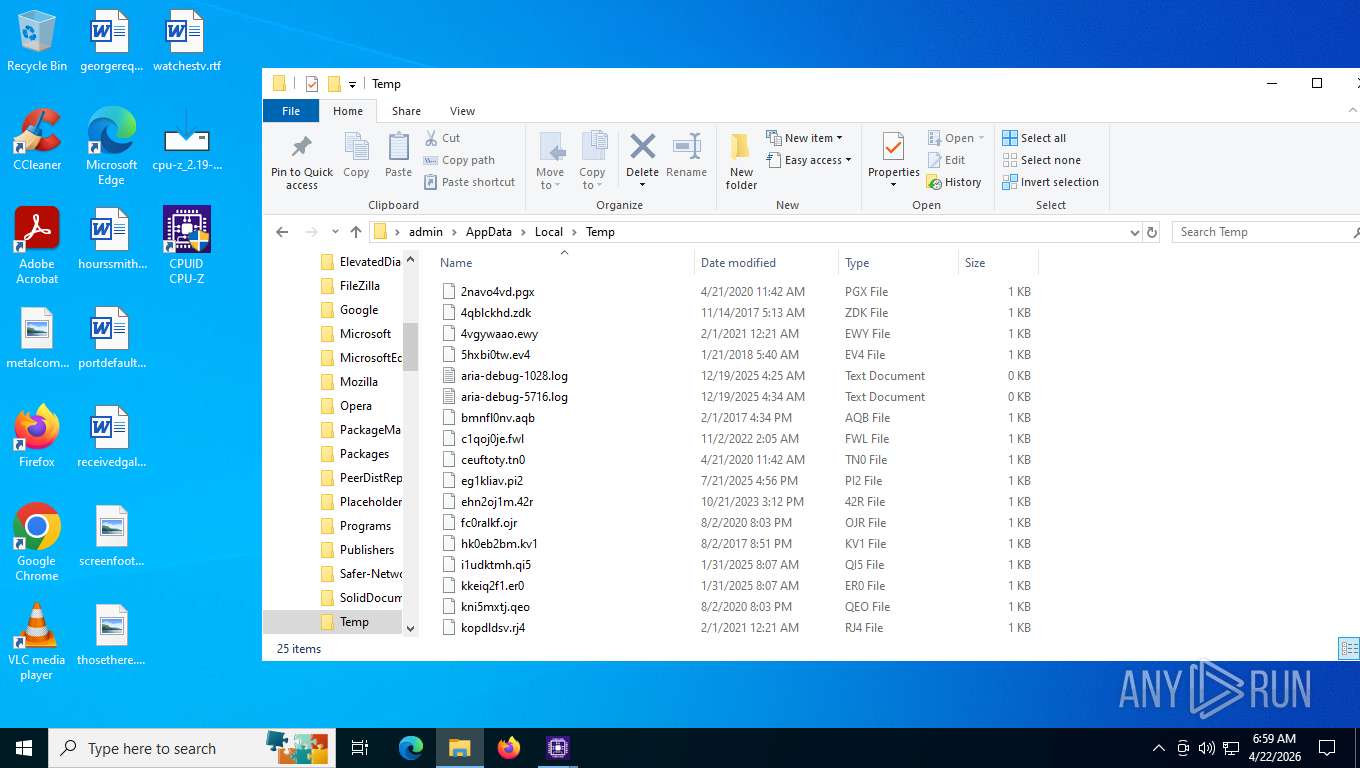
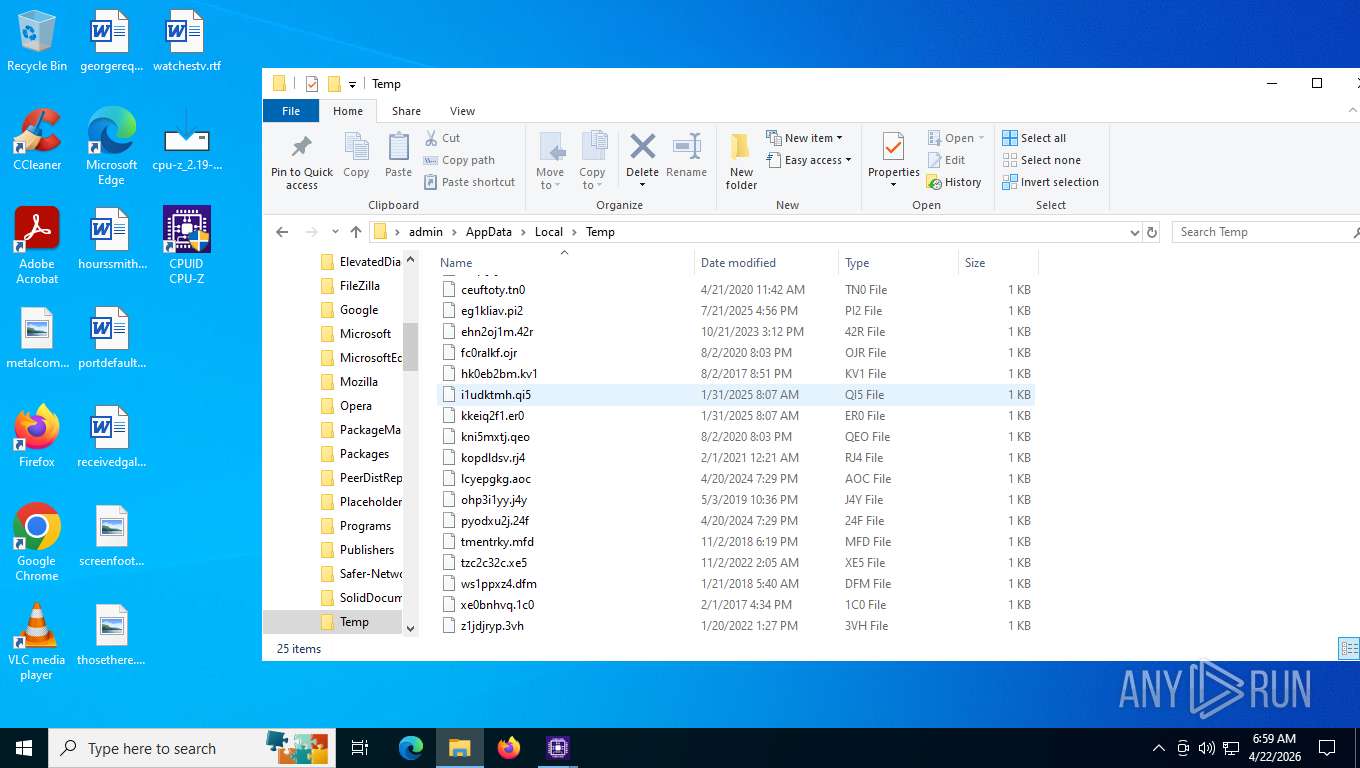
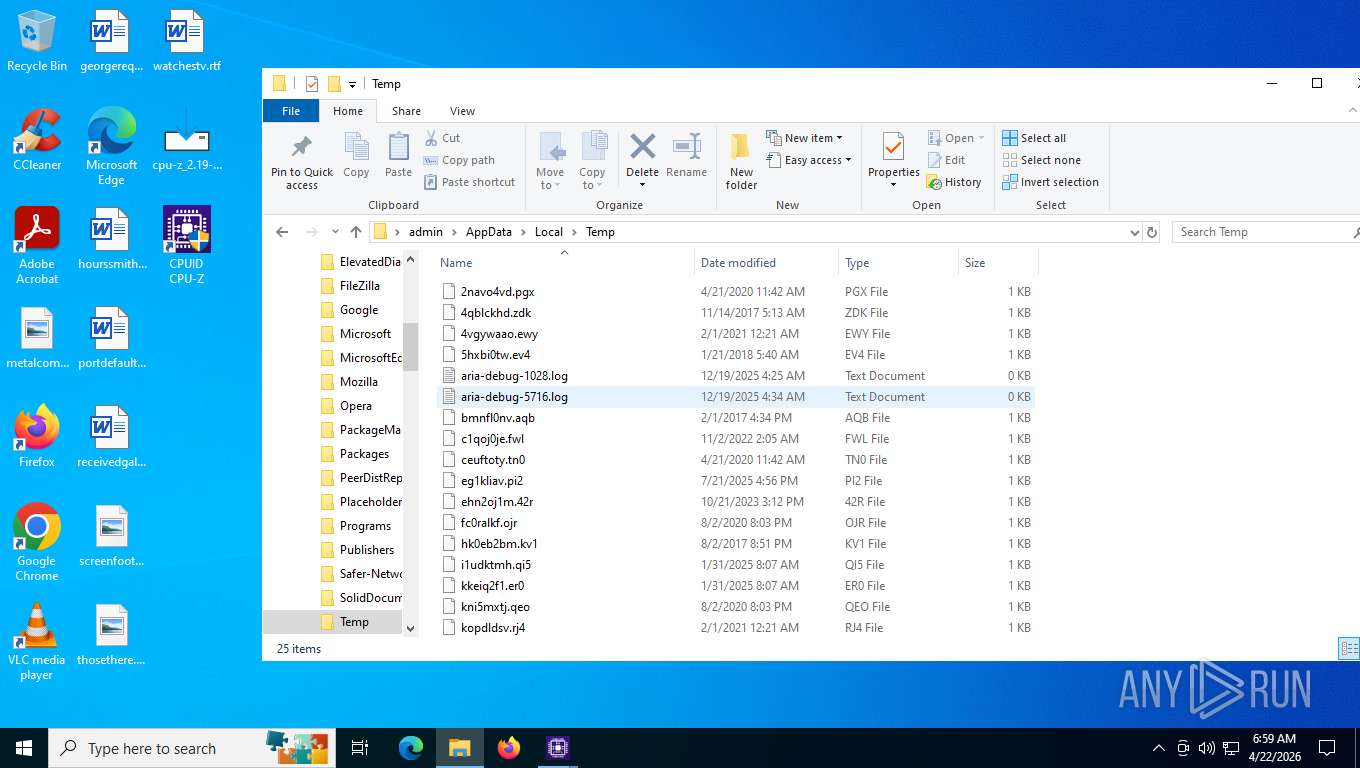
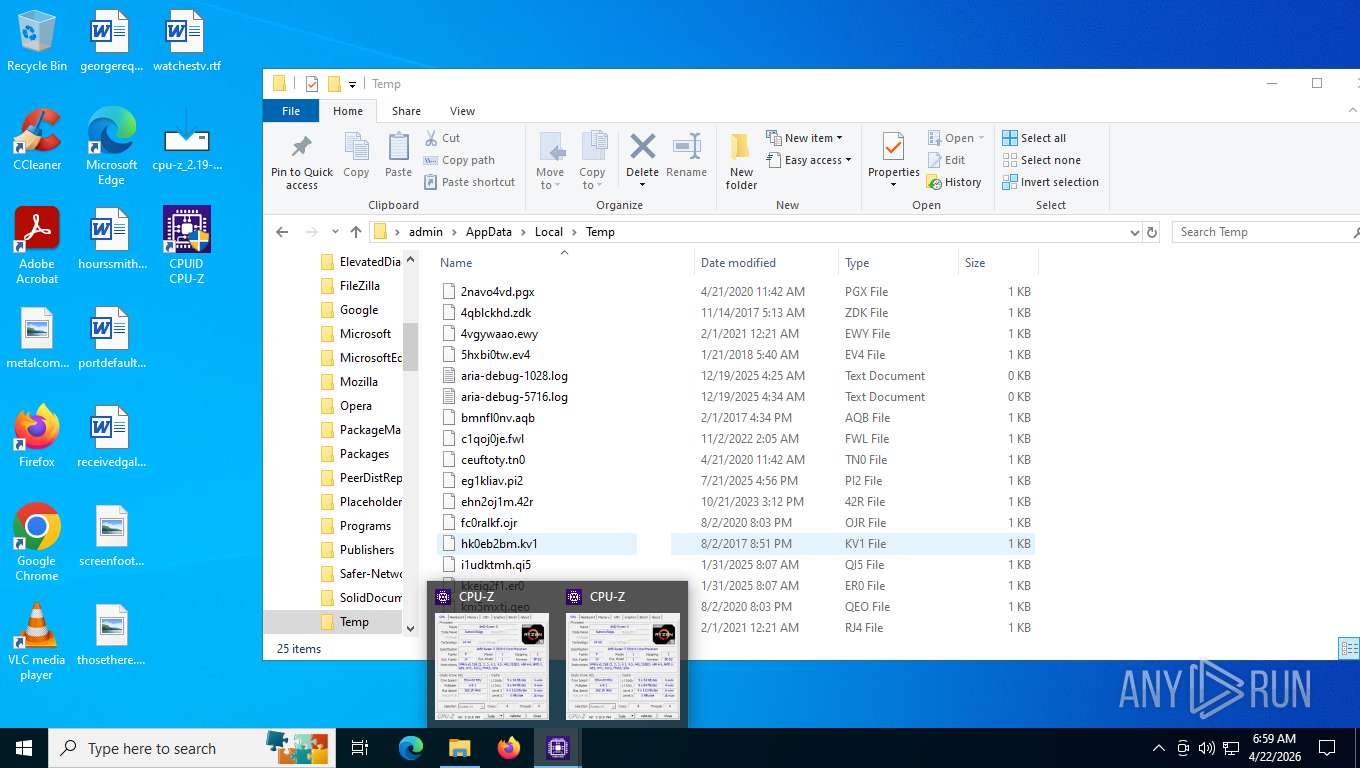
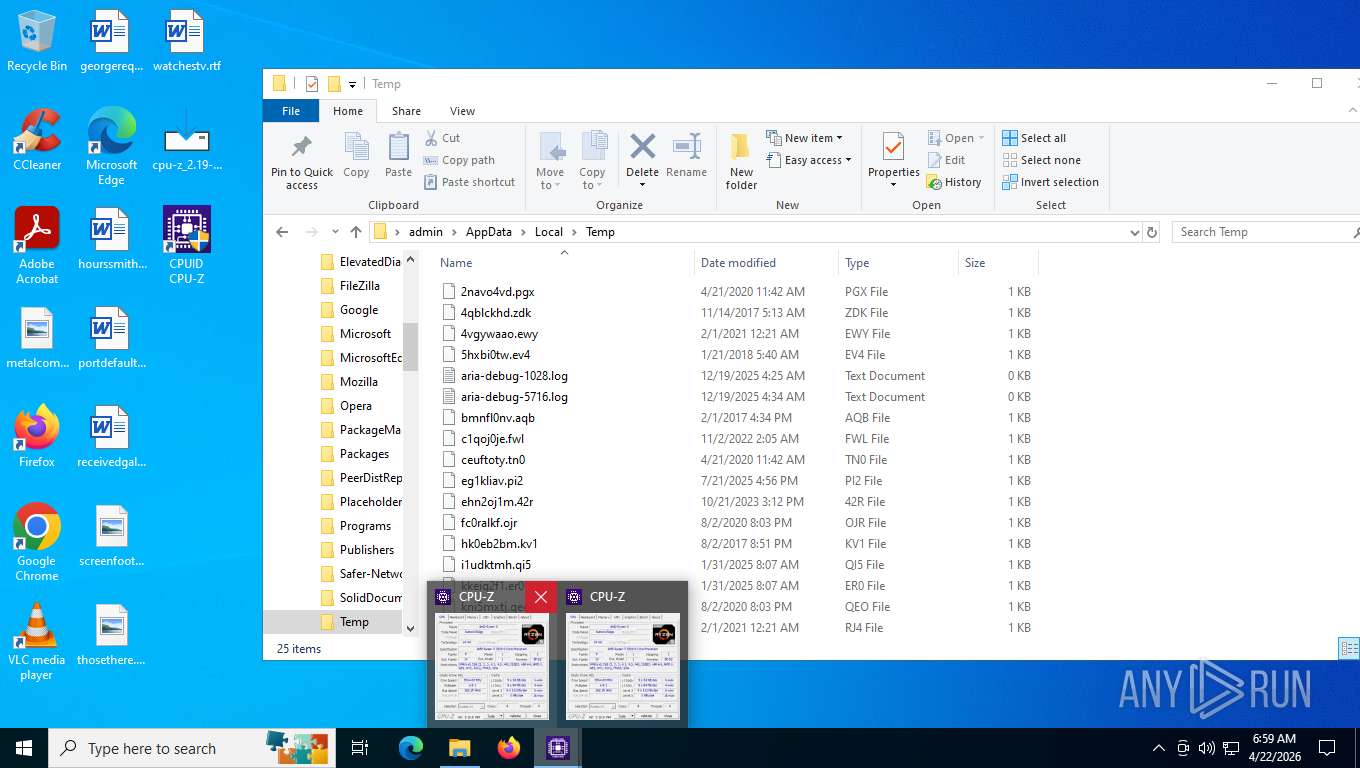
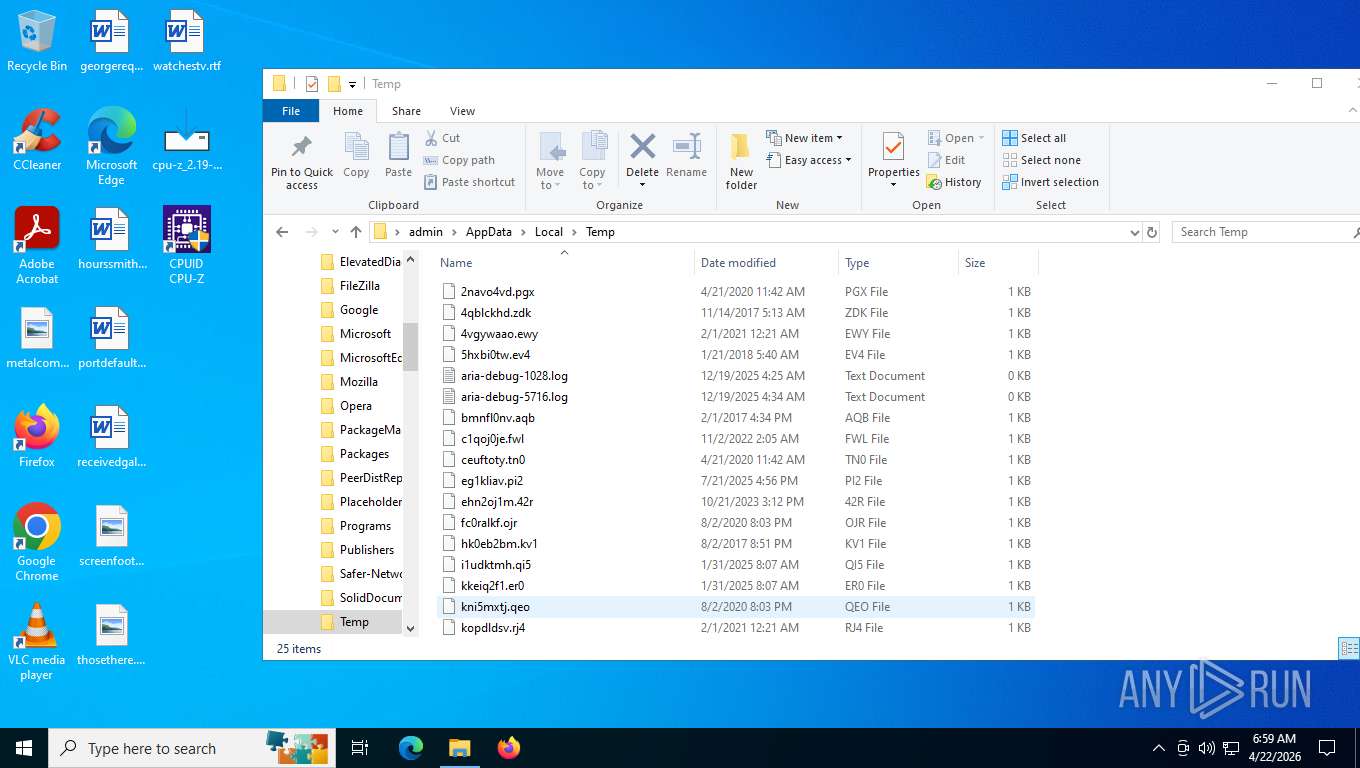
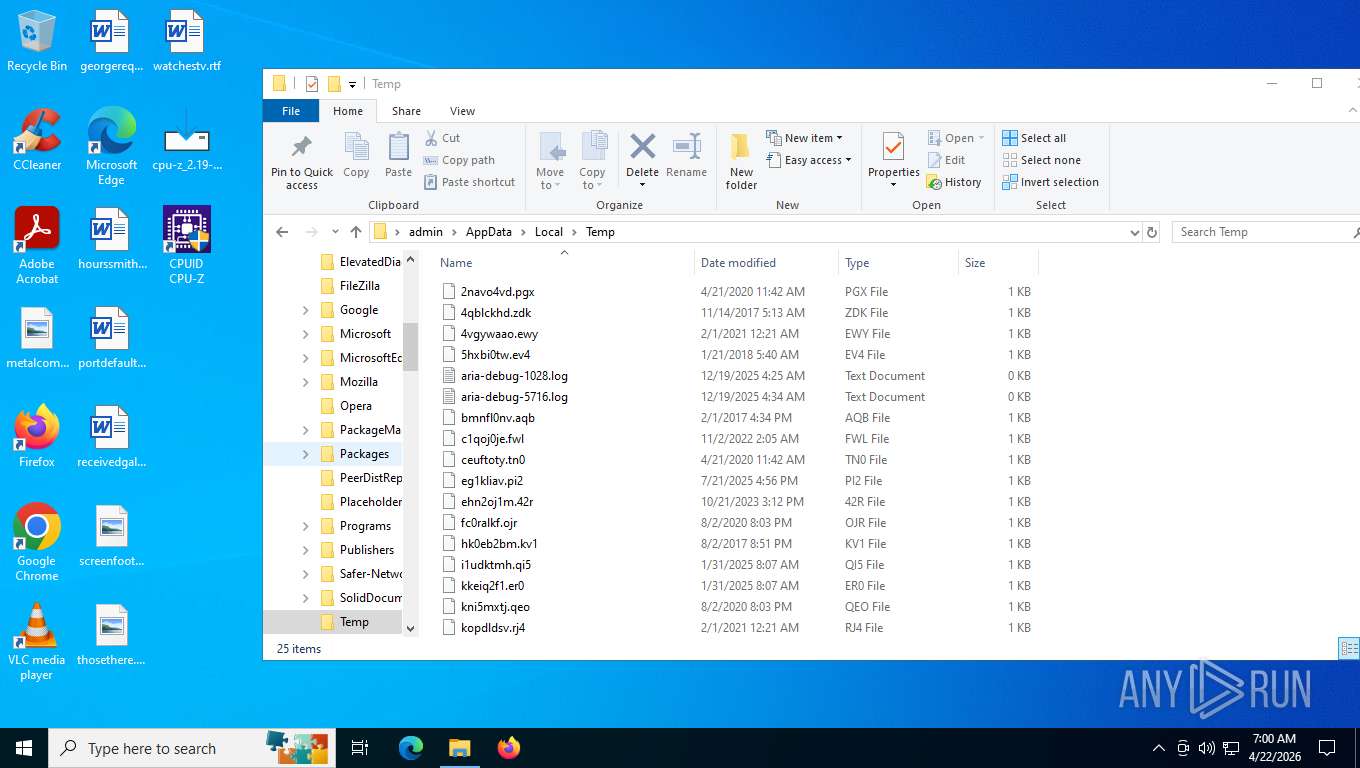
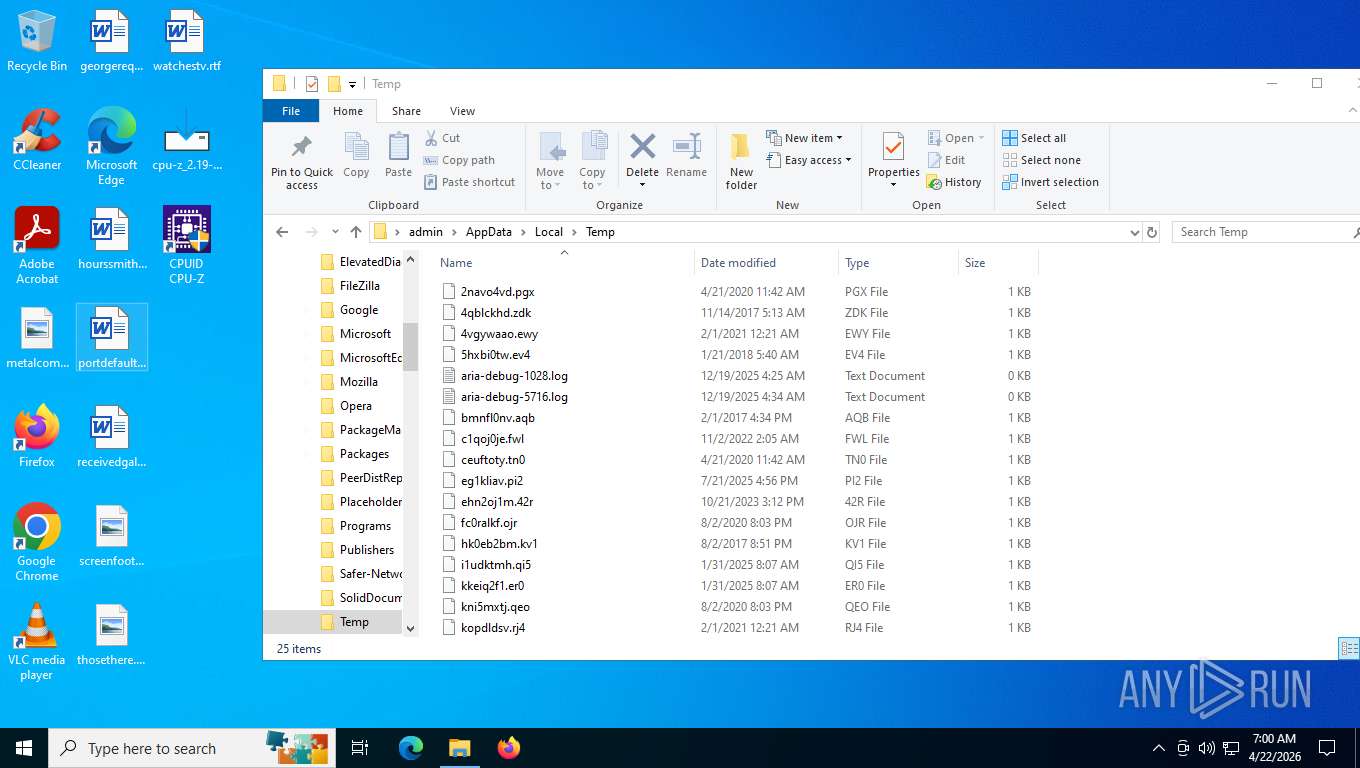
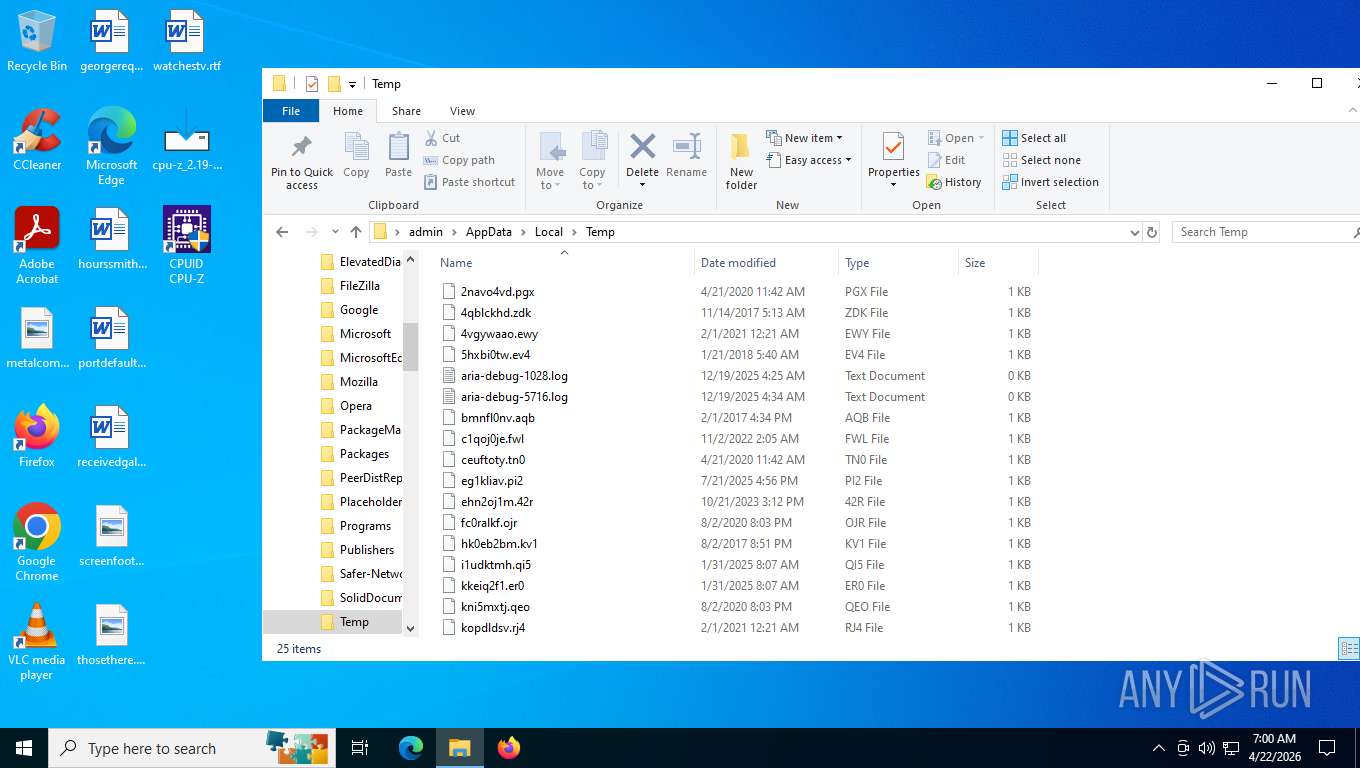
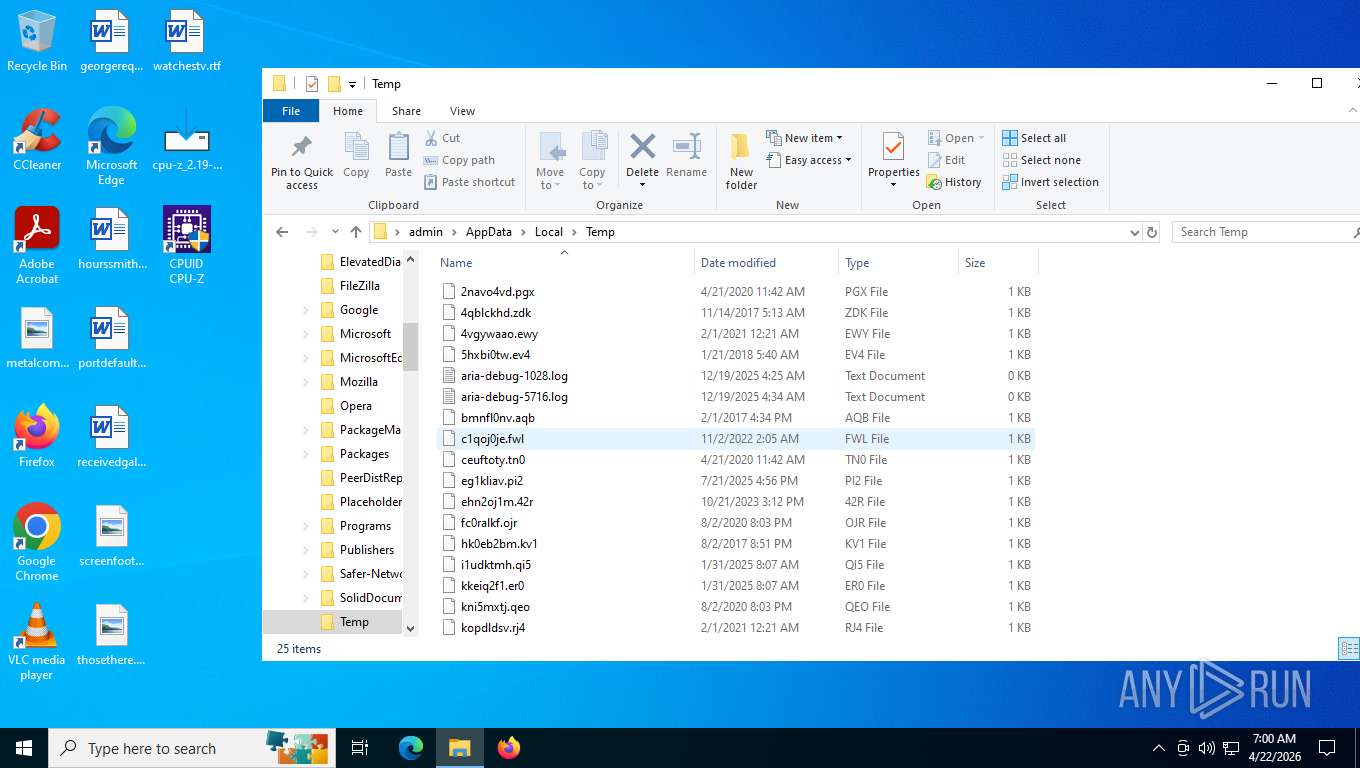
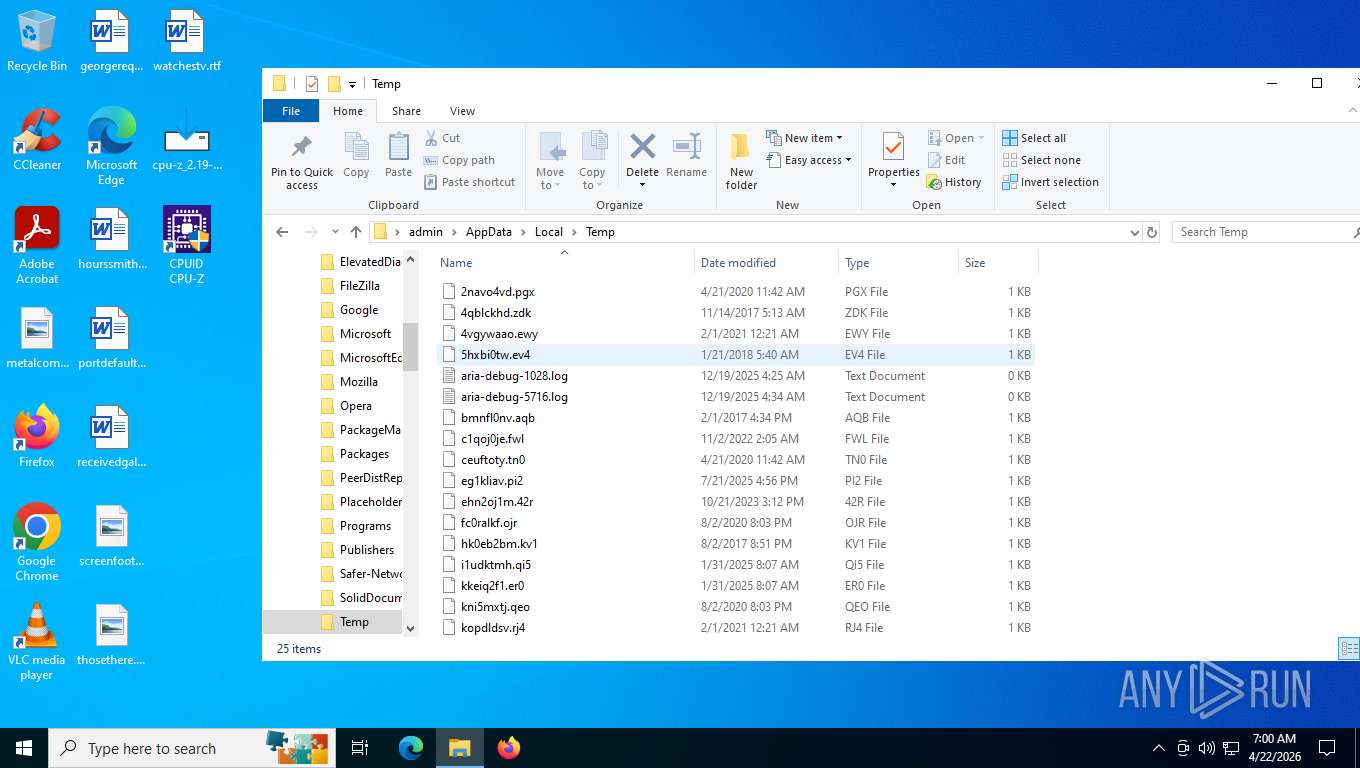
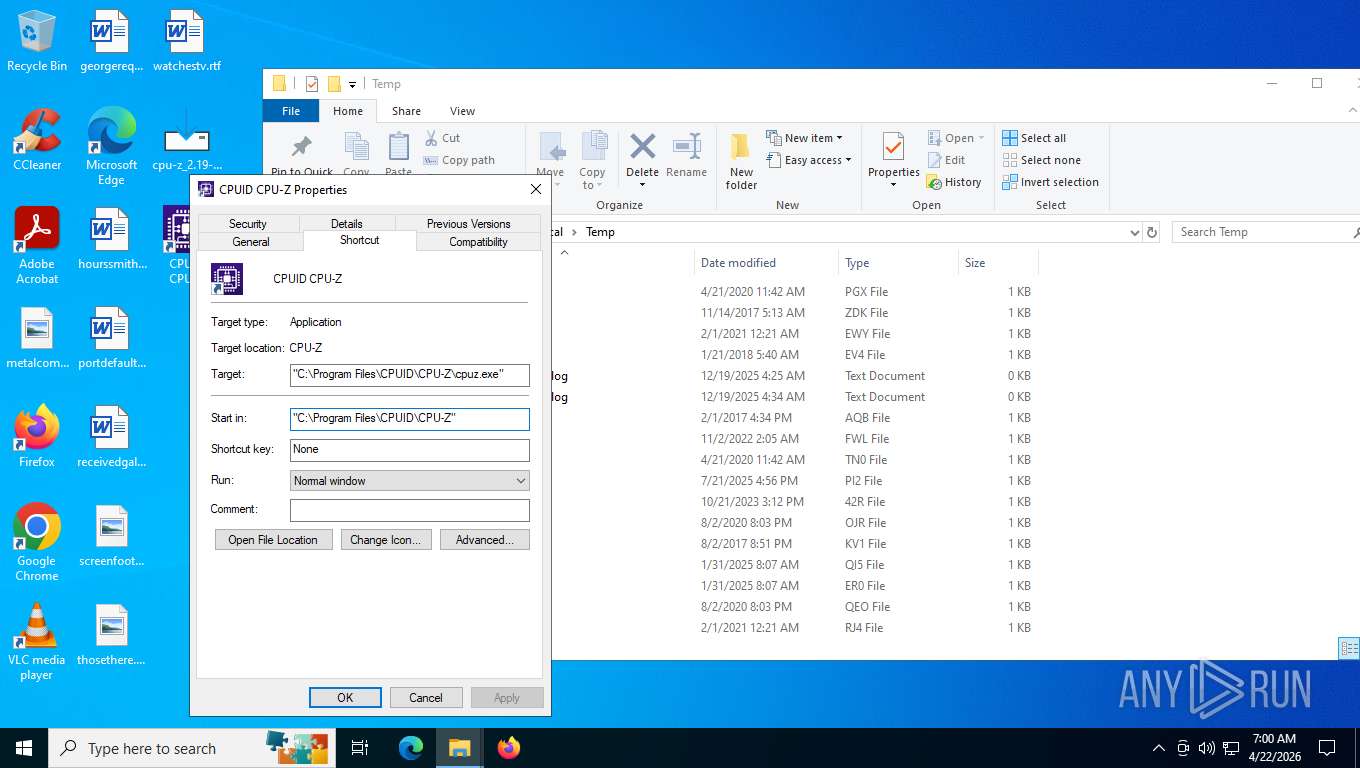
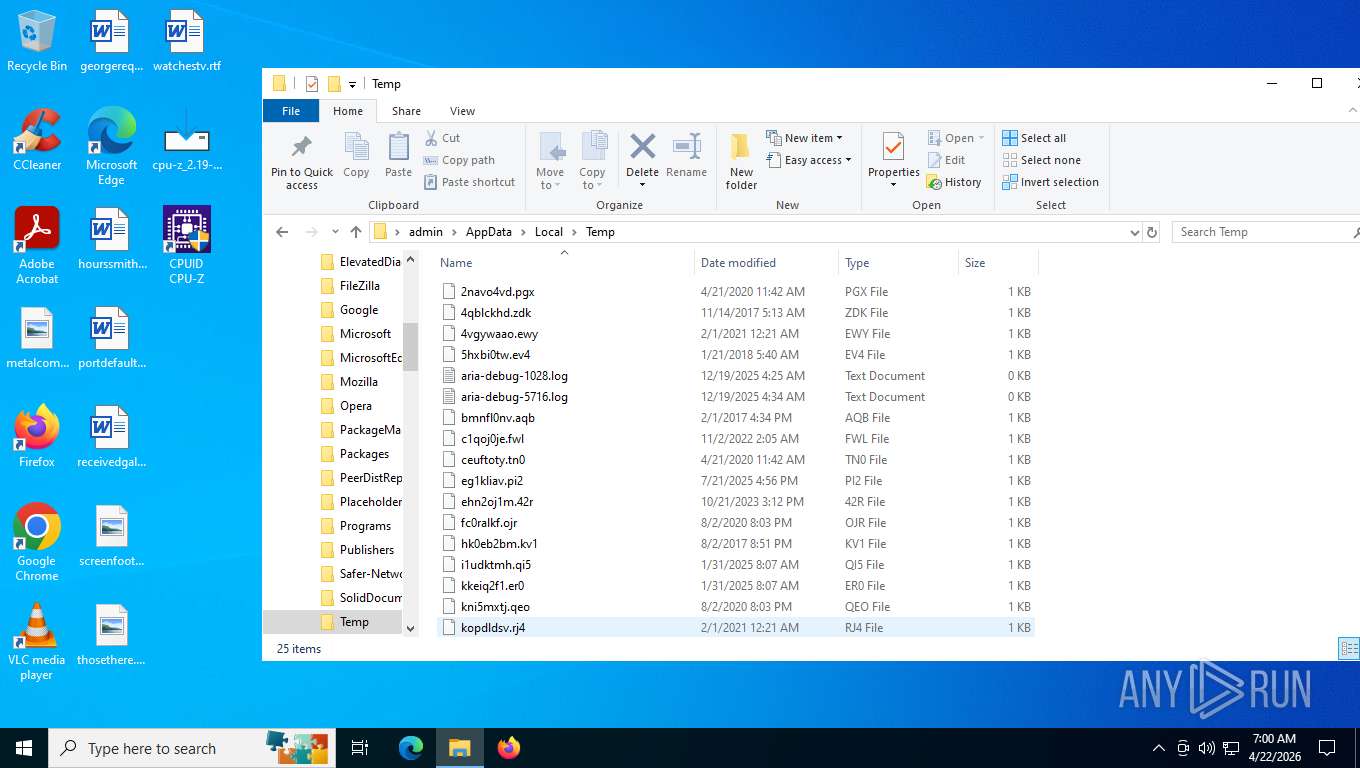
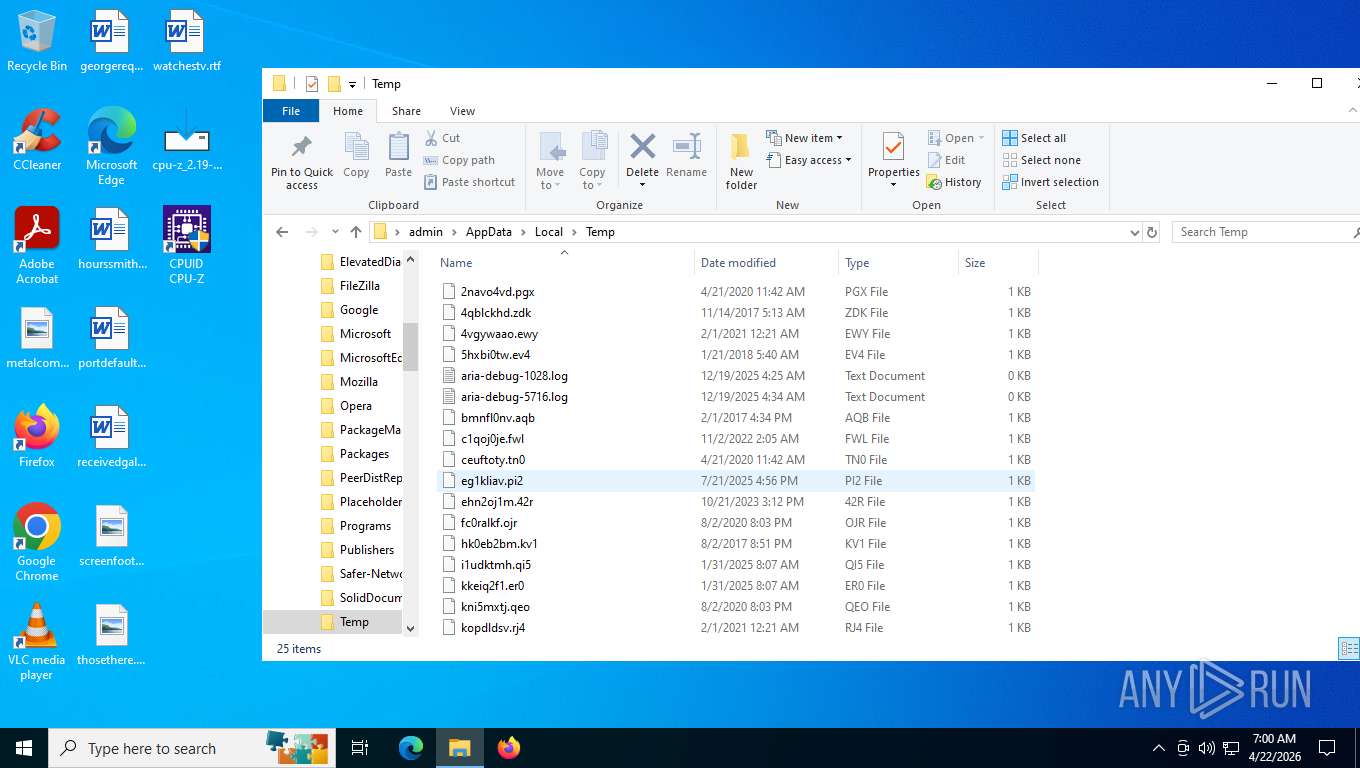
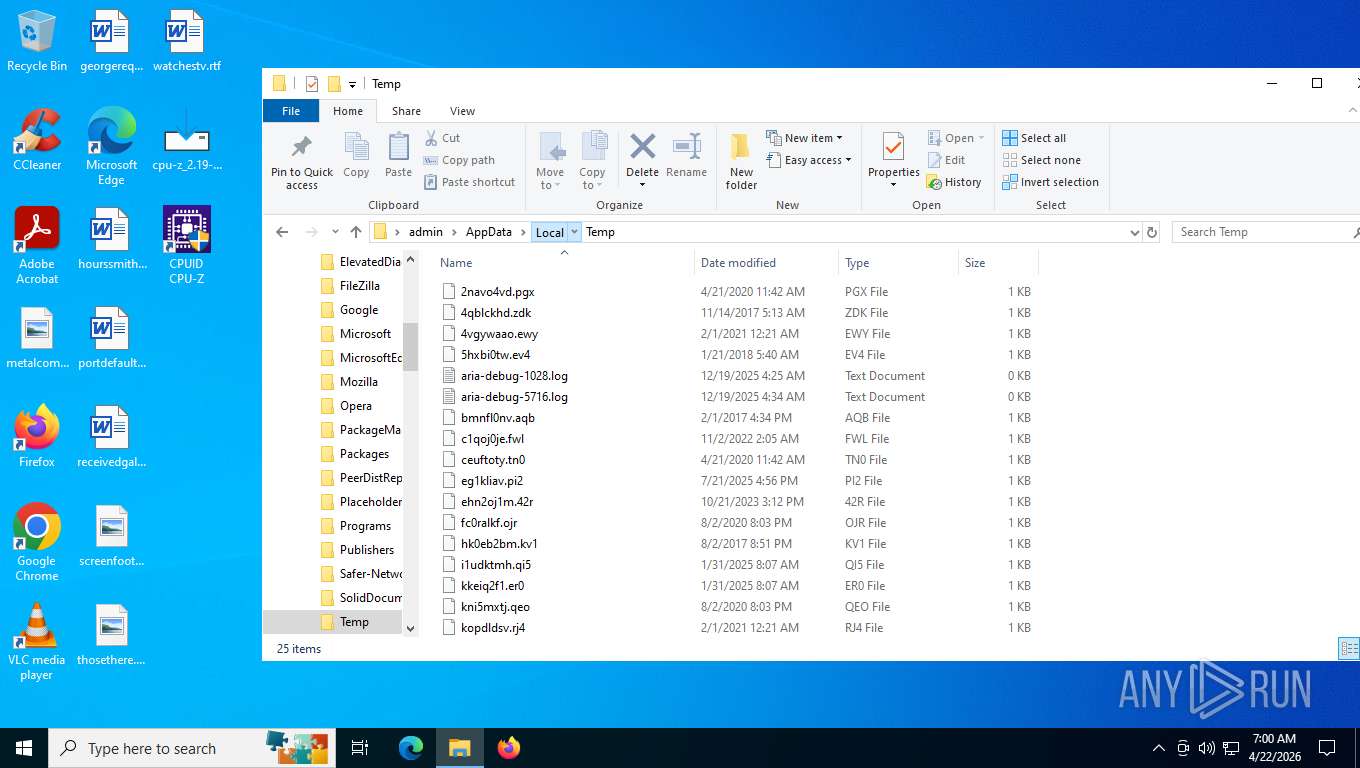
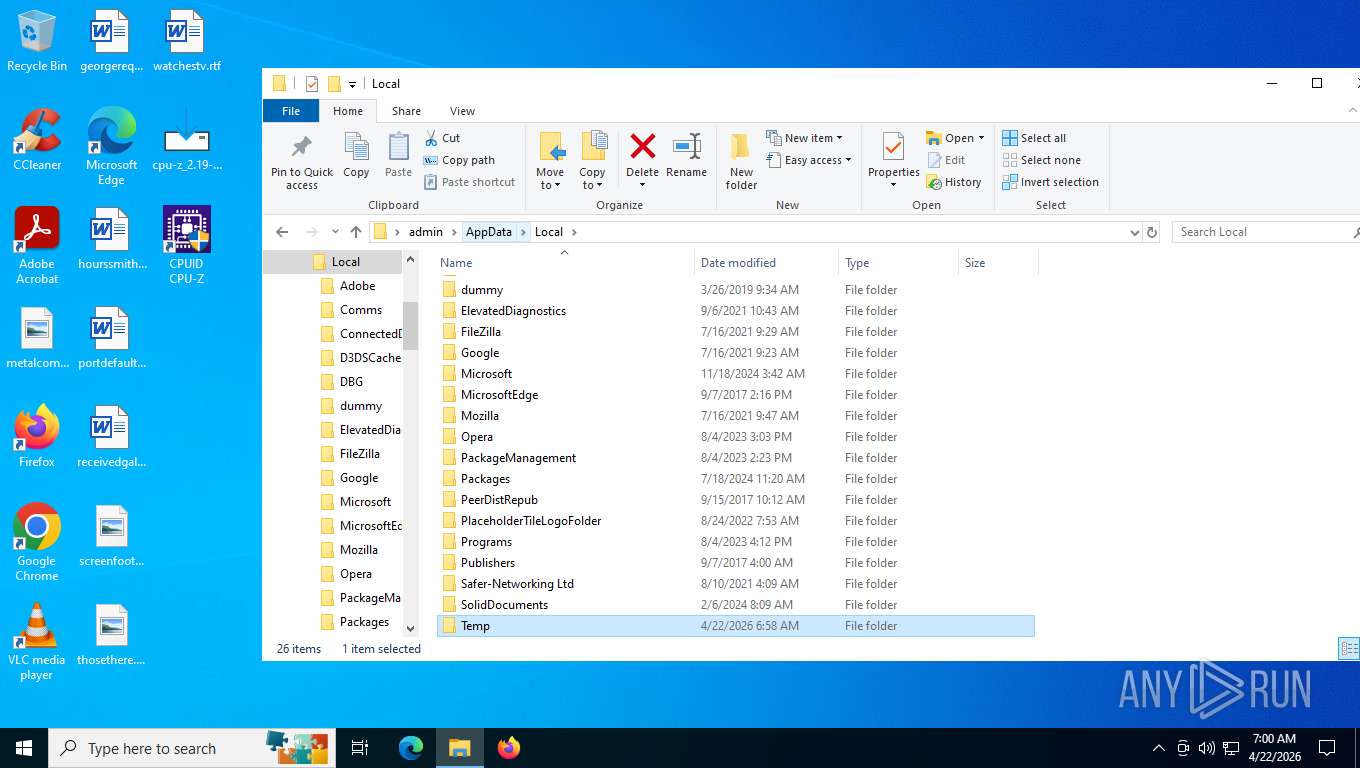
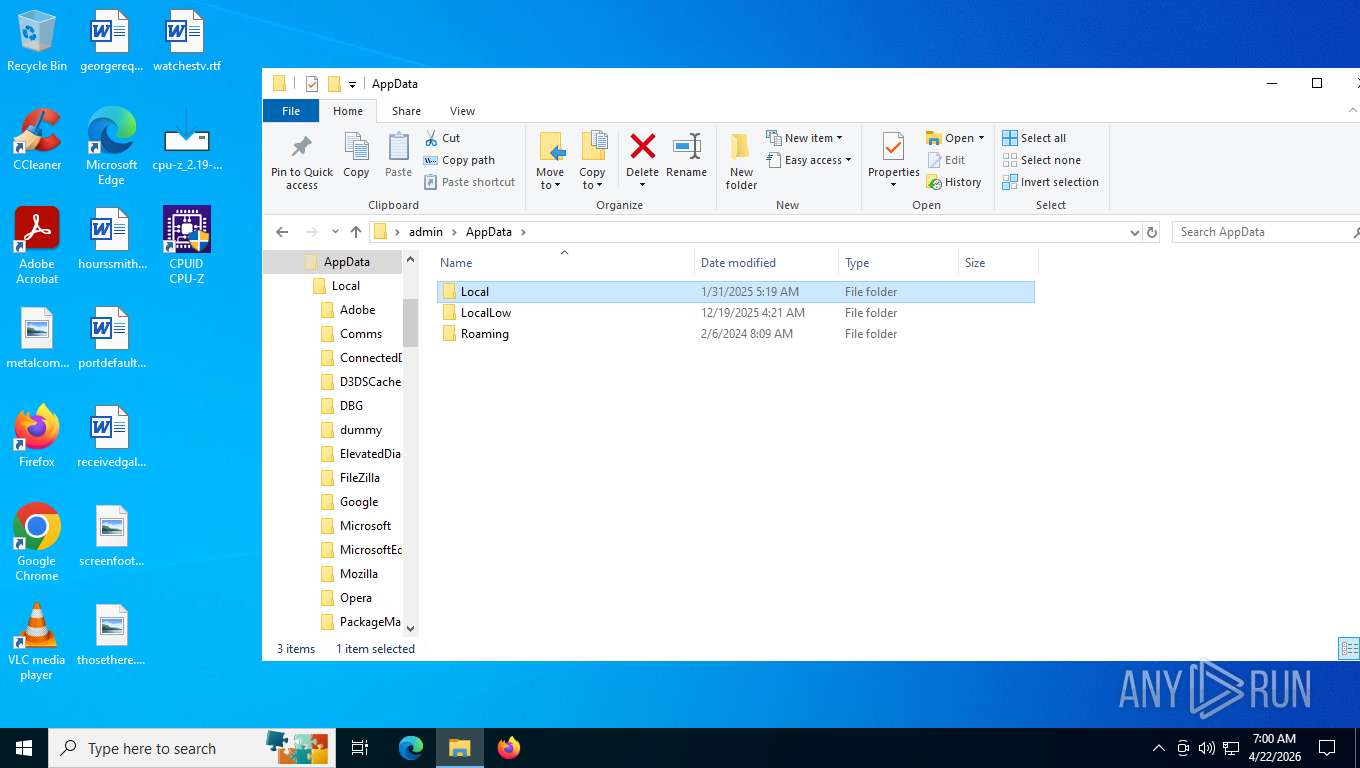
Create files in a temporary directory
- cpu-z_2.19-en.malware.exe (PID: 6816)
- cpu-z_2.19-en.malware.exe (PID: 2452)
- cpu-z_2.19-en.malware.tmp (PID: 3380)
Reads security settings of Internet Explorer
- cpu-z_2.19-en.malware.tmp (PID: 5384)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 2452)
- cpuz.exe (PID: 7152)
- cpuz.exe (PID: 8088)
- cpuz.exe (PID: 7420)
Reads the computer name
- cpu-z_2.19-en.malware.tmp (PID: 5384)
- cpu-z_2.19-en.malware.exe (PID: 2452)
- cpu-z_2.19-en.malware.tmp (PID: 3380)
- cpuz.exe (PID: 7420)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 2452)
- cpuz.exe (PID: 7152)
- cpuz.exe (PID: 8088)
Process checks computer location settings
- cpu-z_2.19-en.malware.tmp (PID: 5384)
Detects InnoSetup installer (YARA)
- cpu-z_2.19-en.malware.exe (PID: 6816)
- cpu-z_2.19-en.malware.tmp (PID: 5384)
- cpu-z_2.19-en.malware.exe (PID: 2452)
- cpu-z_2.19-en.malware.tmp (PID: 3380)
Compiled with Borland Delphi (YARA)
- cpu-z_2.19-en.malware.exe (PID: 6816)
- cpu-z_2.19-en.malware.tmp (PID: 5384)
- cpu-z_2.19-en.malware.exe (PID: 2452)
- cpu-z_2.19-en.malware.tmp (PID: 3380)
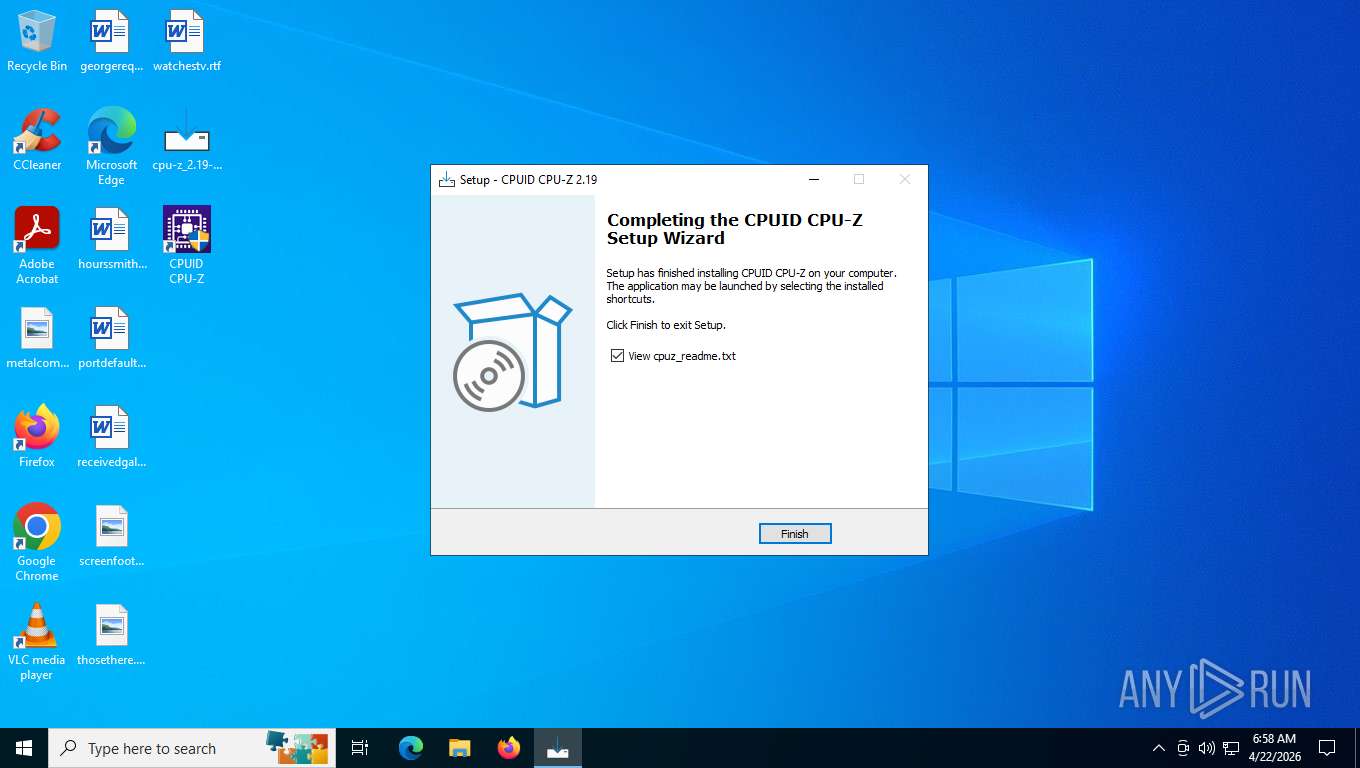
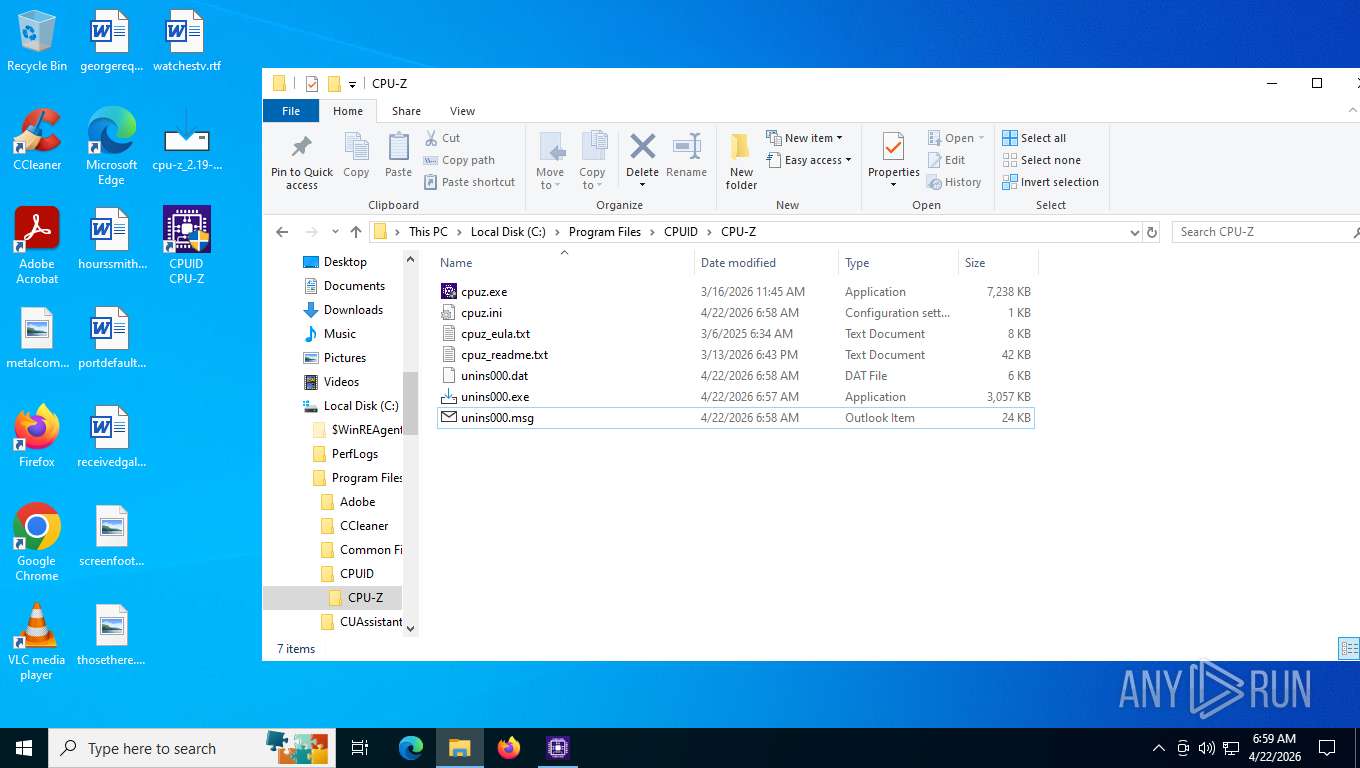
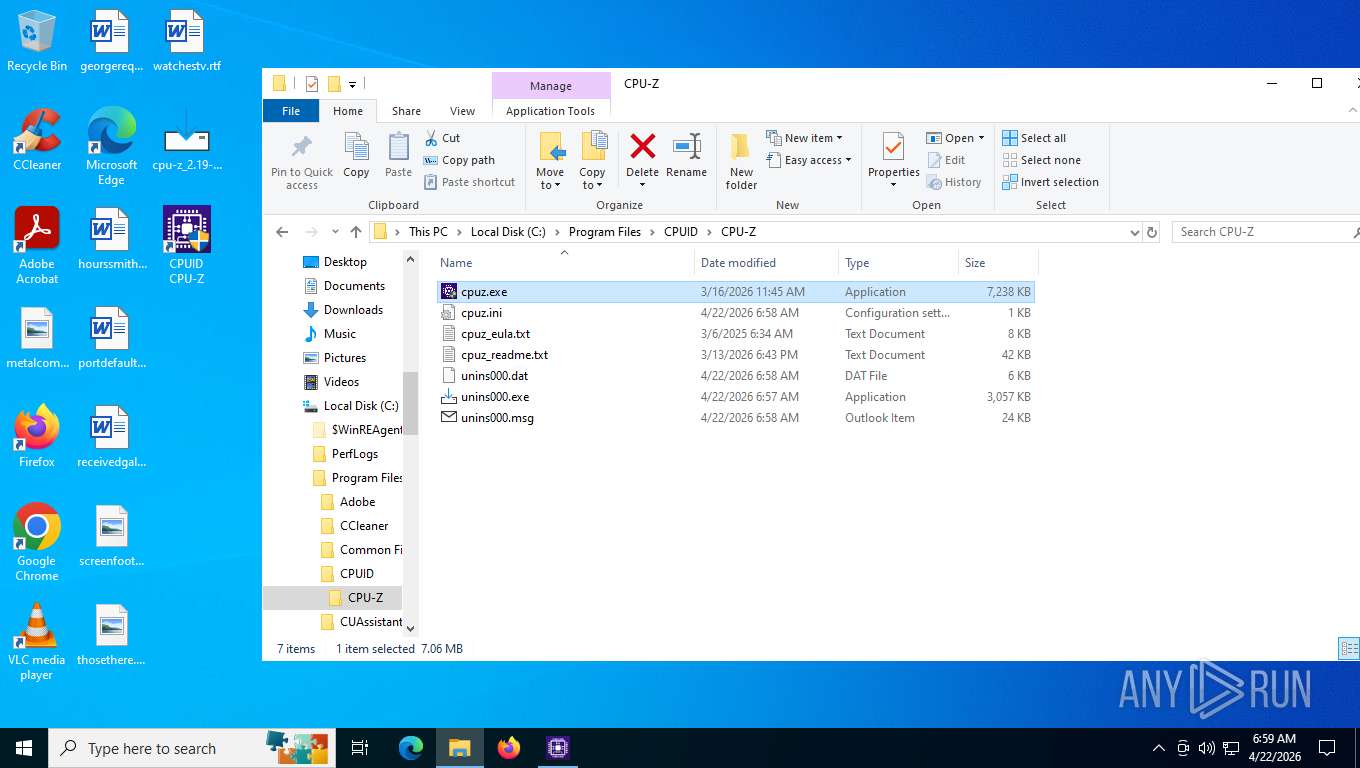
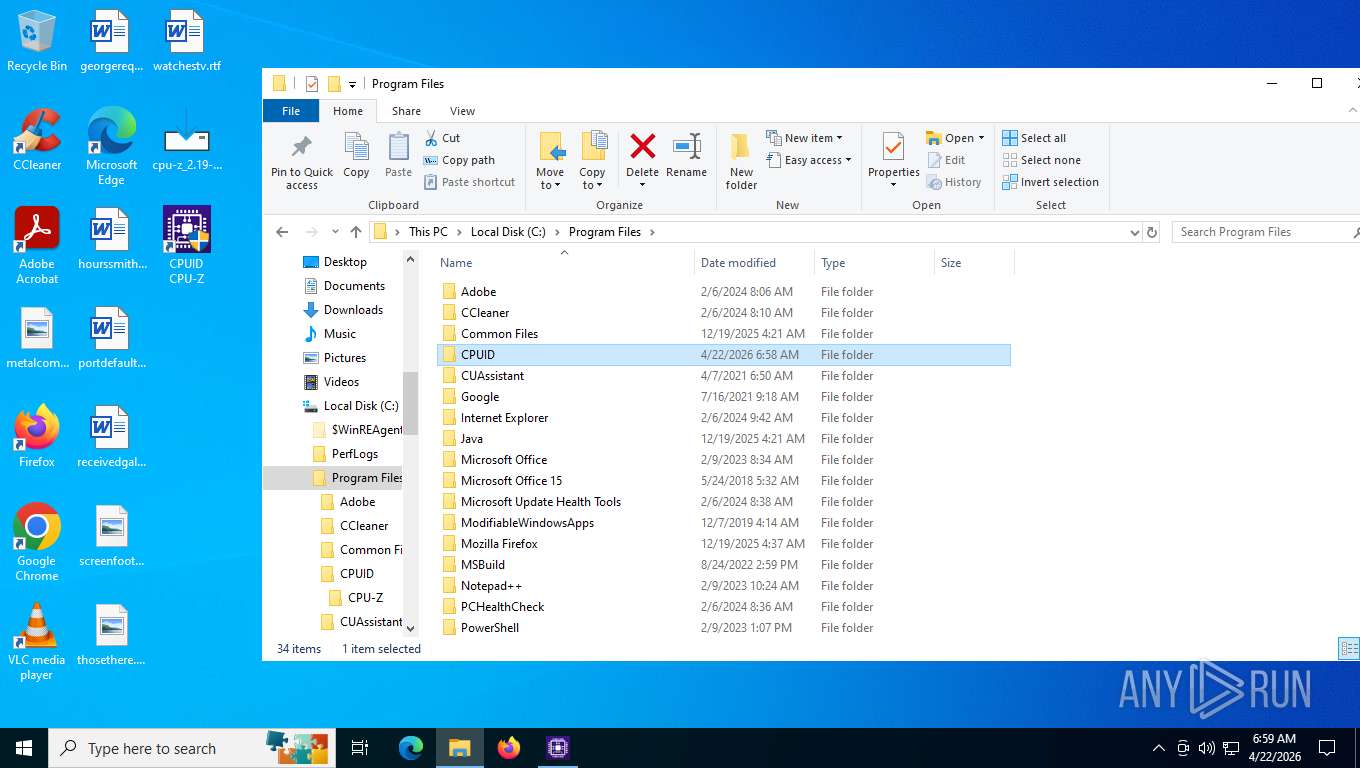
Creates a software uninstall entry
- cpu-z_2.19-en.malware.tmp (PID: 3380)
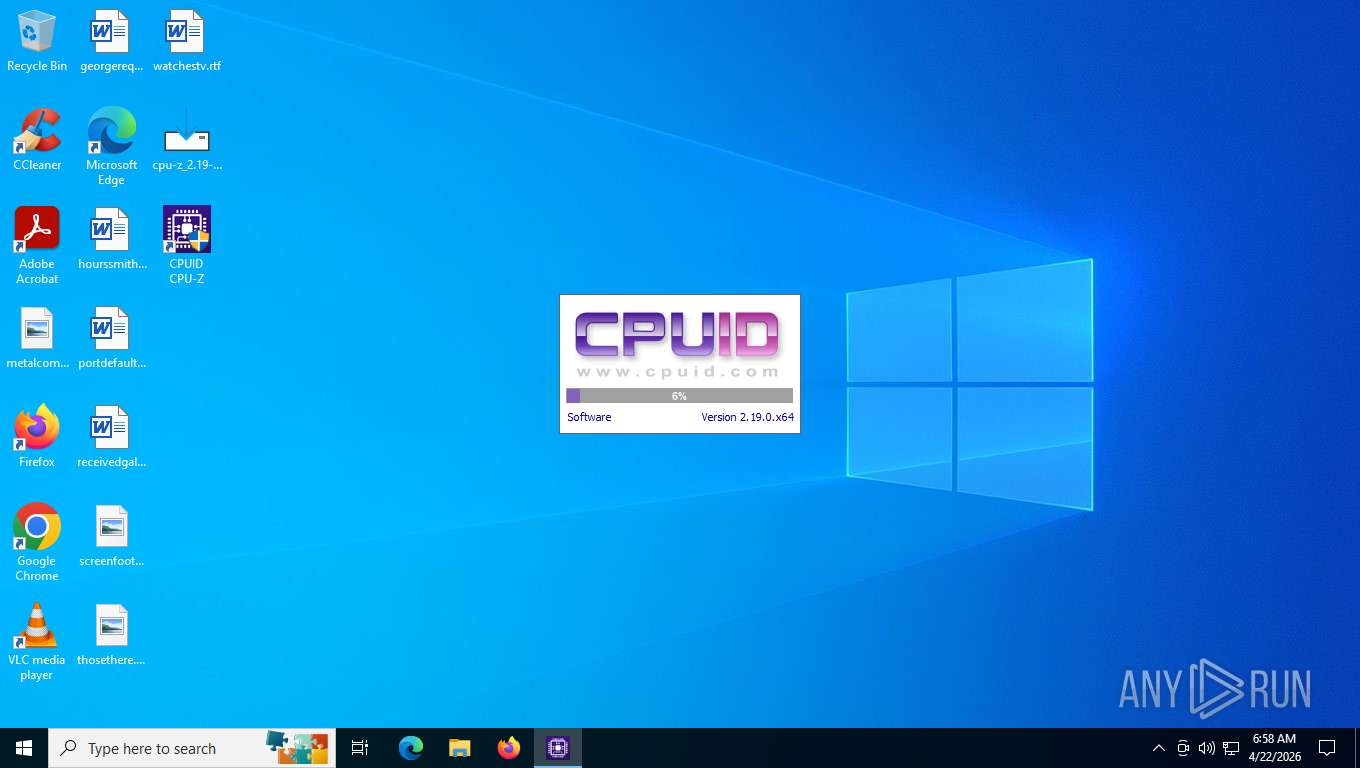
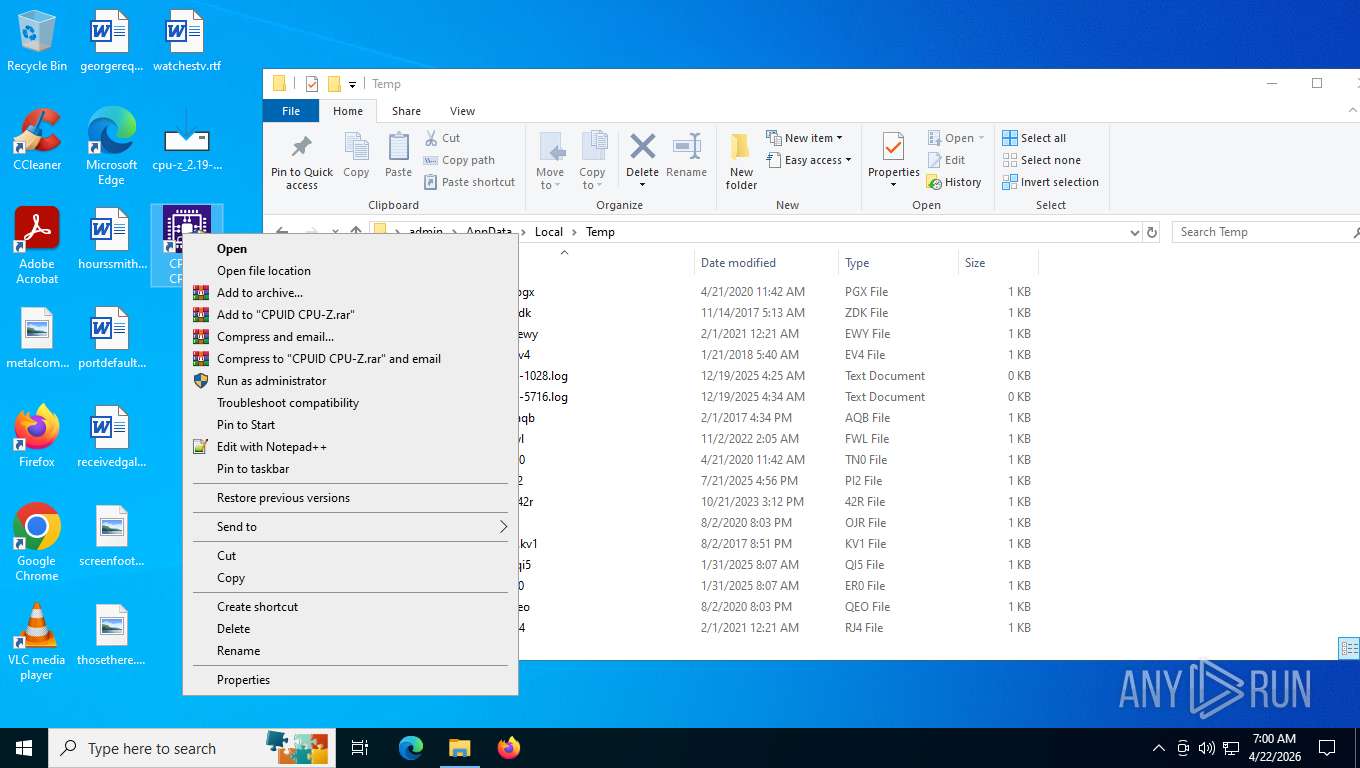
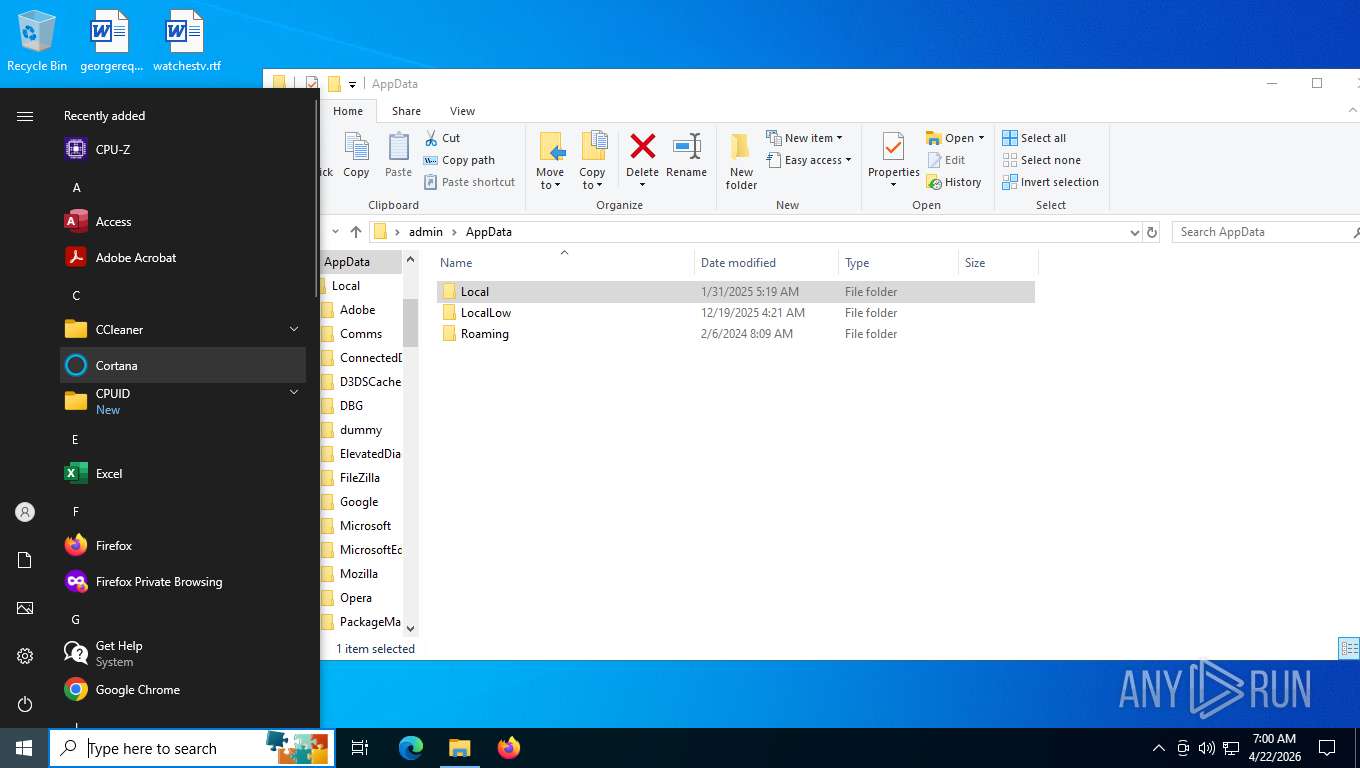
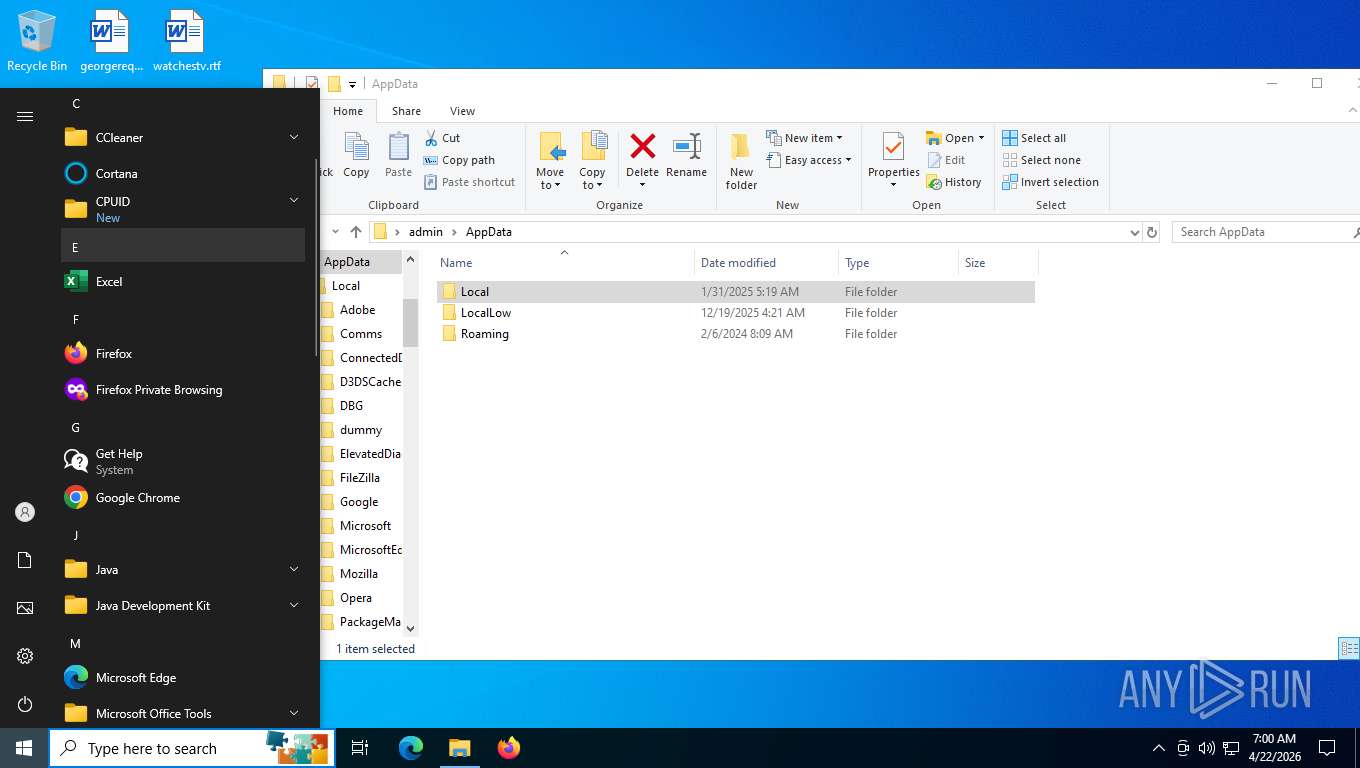
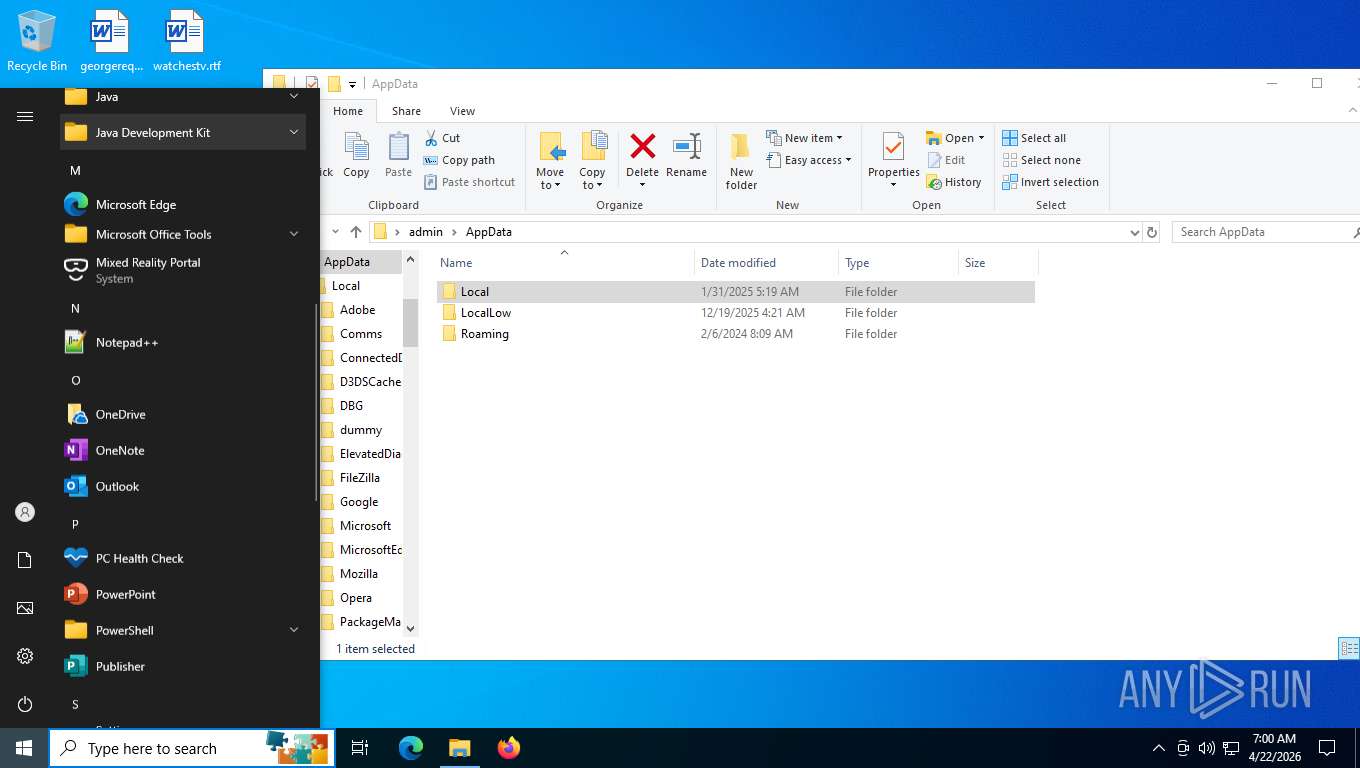
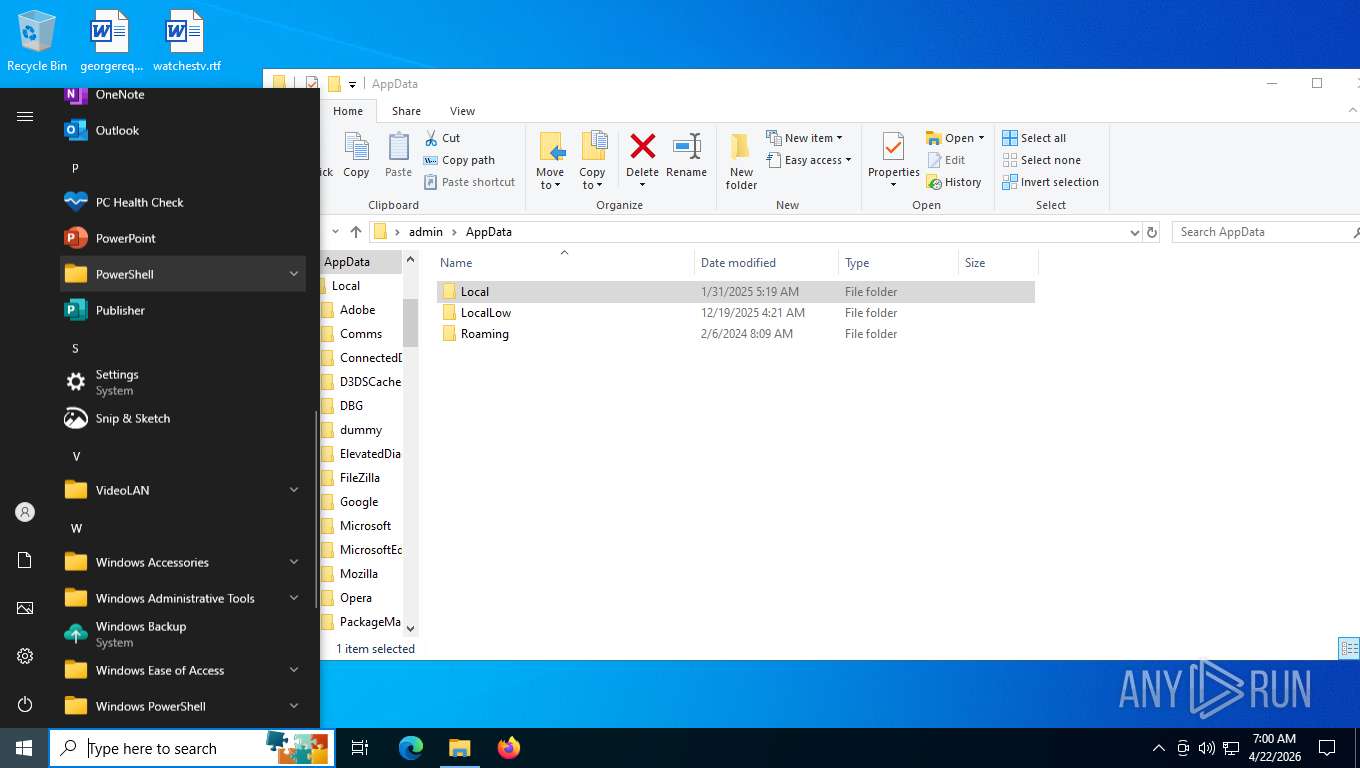
Manual execution by a user
- cpuz.exe (PID: 7556)
- cpuz.exe (PID: 7420)
- cpuz.exe (PID: 2216)
- cpuz.exe (PID: 7920)
- notepad++.exe (PID: 3420)
- cpuz.exe (PID: 2452)
- cpuz.exe (PID: 7984)
- cpuz.exe (PID: 7152)
- cpuz.exe (PID: 8088)
- mspaint.exe (PID: 7380)
- cpuz.exe (PID: 2000)
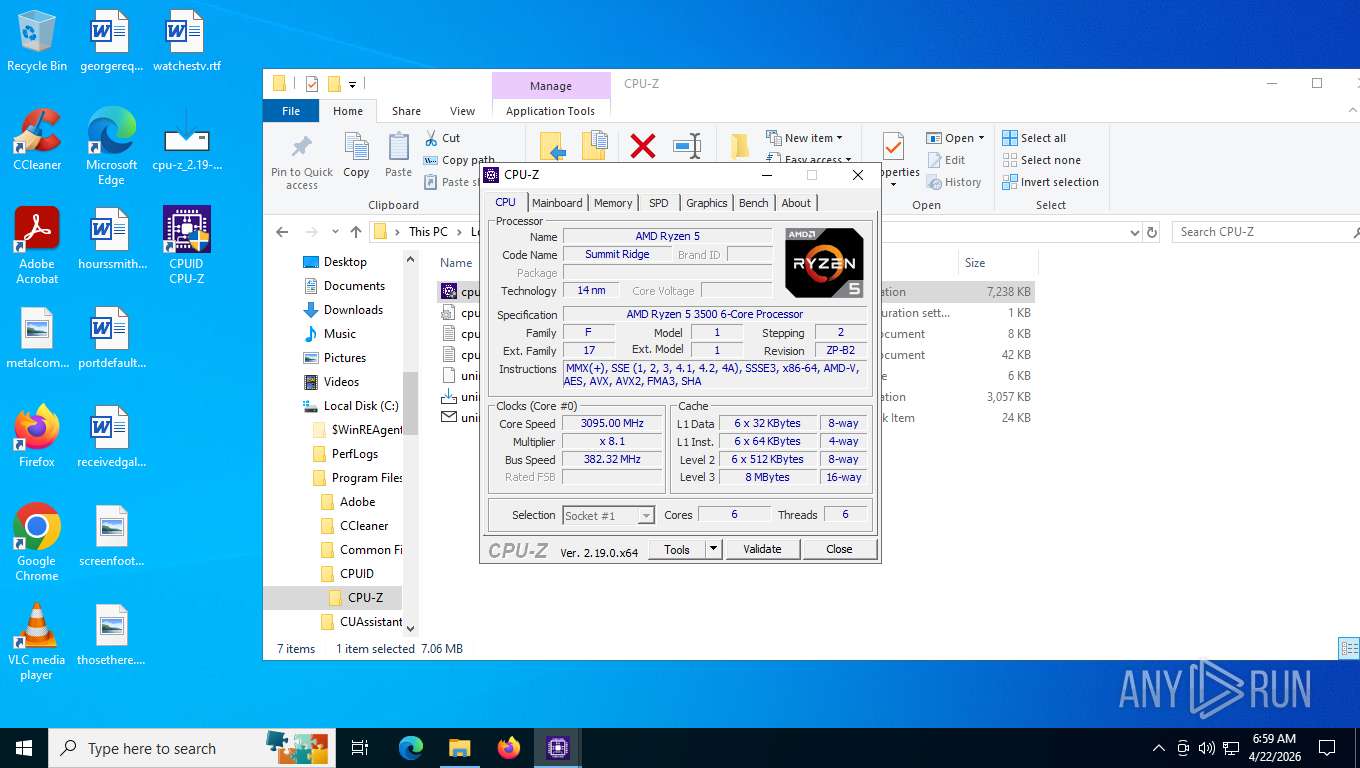
CPUZ mutex has been found
- cpuz.exe (PID: 7420)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 2452)
- cpuz.exe (PID: 7152)
- cpuz.exe (PID: 8088)
The sample compiled with english language support
- cpuz.exe (PID: 7420)
- cpu-z_2.19-en.malware.tmp (PID: 3380)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 8088)
Reads Environment values
- cpuz.exe (PID: 7420)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 2452)
- cpuz.exe (PID: 7152)
- cpuz.exe (PID: 8088)
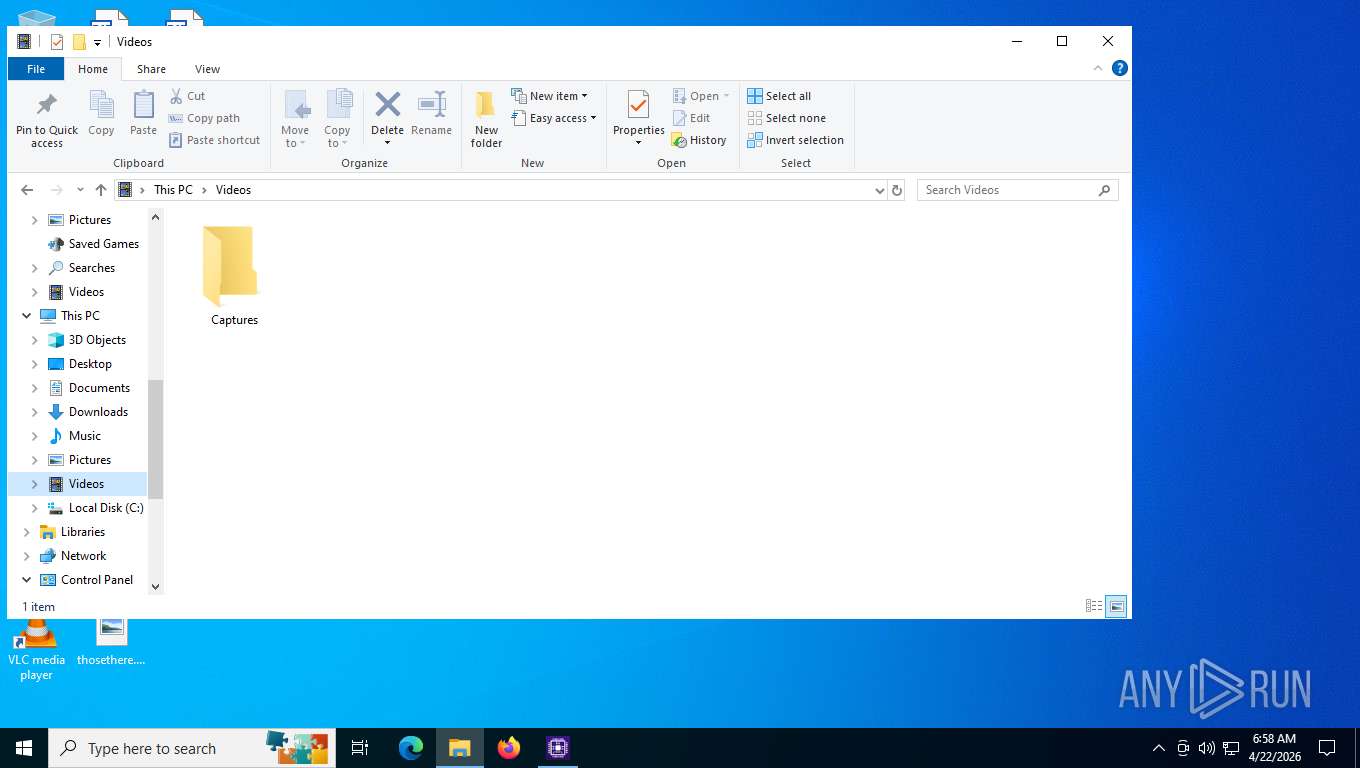
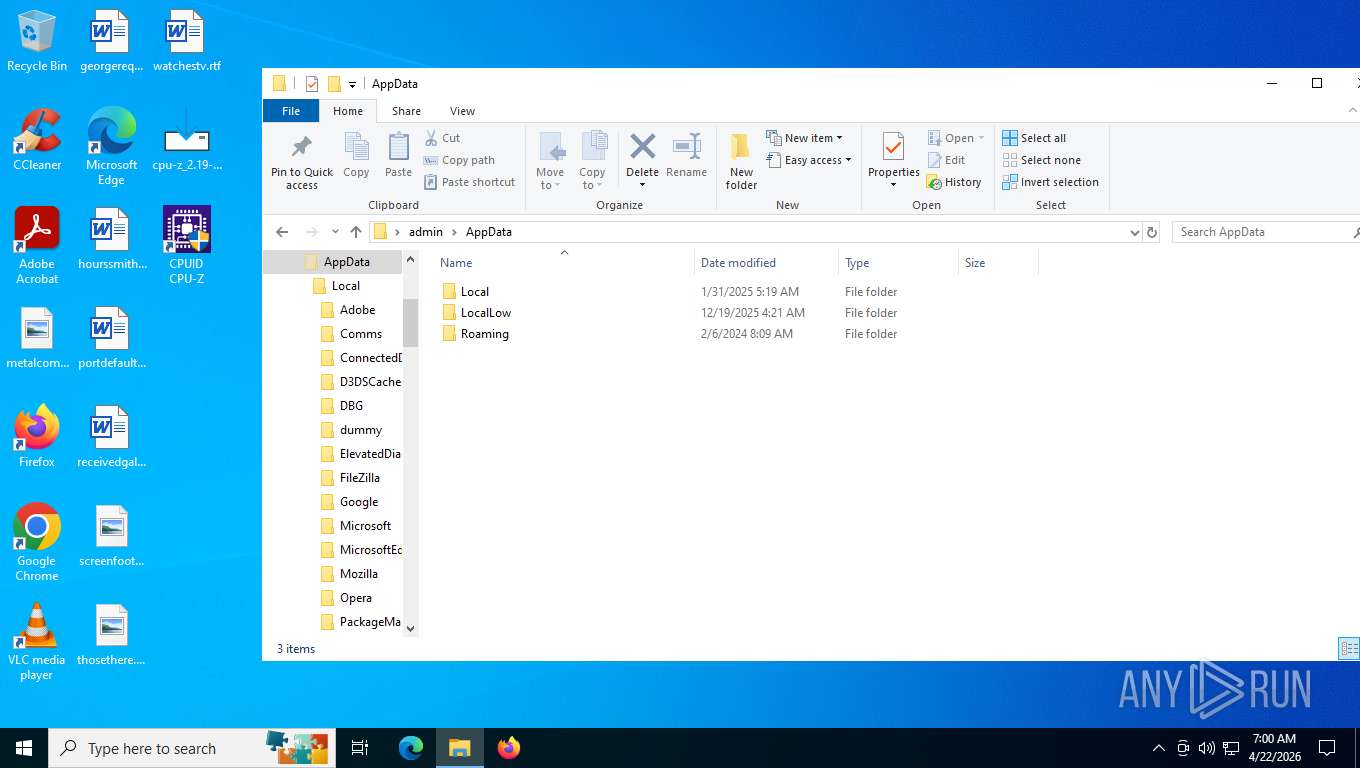
Creates files or folders in the user directory
- cpuz.exe (PID: 7420)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 2452)
- cpuz.exe (PID: 7152)
- cpuz.exe (PID: 8088)
Reads the machine GUID from the registry
- cpuz.exe (PID: 7420)
- cpuz.exe (PID: 7920)
- cpuz.exe (PID: 2452)
- cpuz.exe (PID: 7152)
- cpuz.exe (PID: 8088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:06:28 08:29:25+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 685056 |
| InitializedDataSize: | 90112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa83bc |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
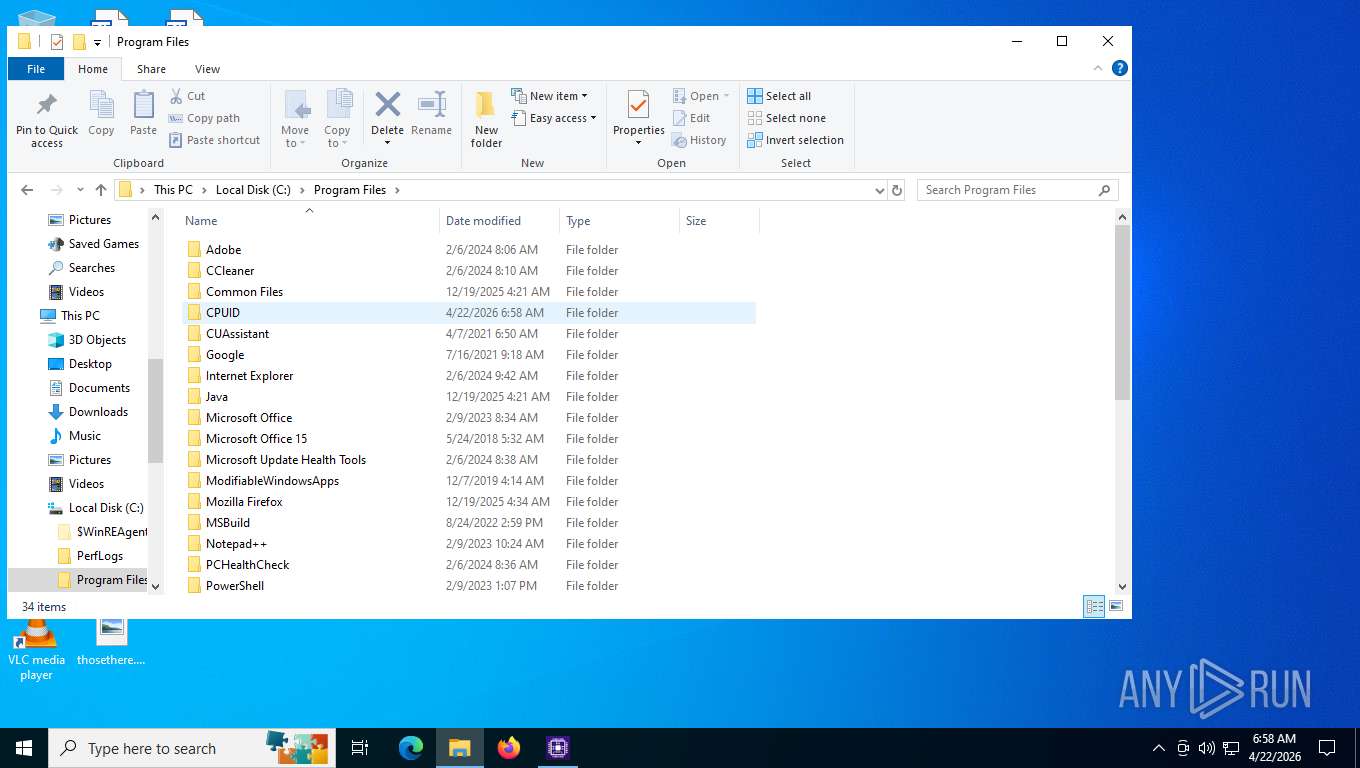
| CompanyName: | CPUID, Inc. |
| FileDescription: | CPUID CPU-Z Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | CPUID CPU-Z |
| ProductVersion: | 2.19 |
Total processes
163
Monitored processes
17
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 996 | helper 105 0x4CC | C:\Users\admin\AppData\Local\Temp\is-3LVG7.tmp\_isetup\_setup64.tmp | — | cpu-z_2.19-en.malware.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
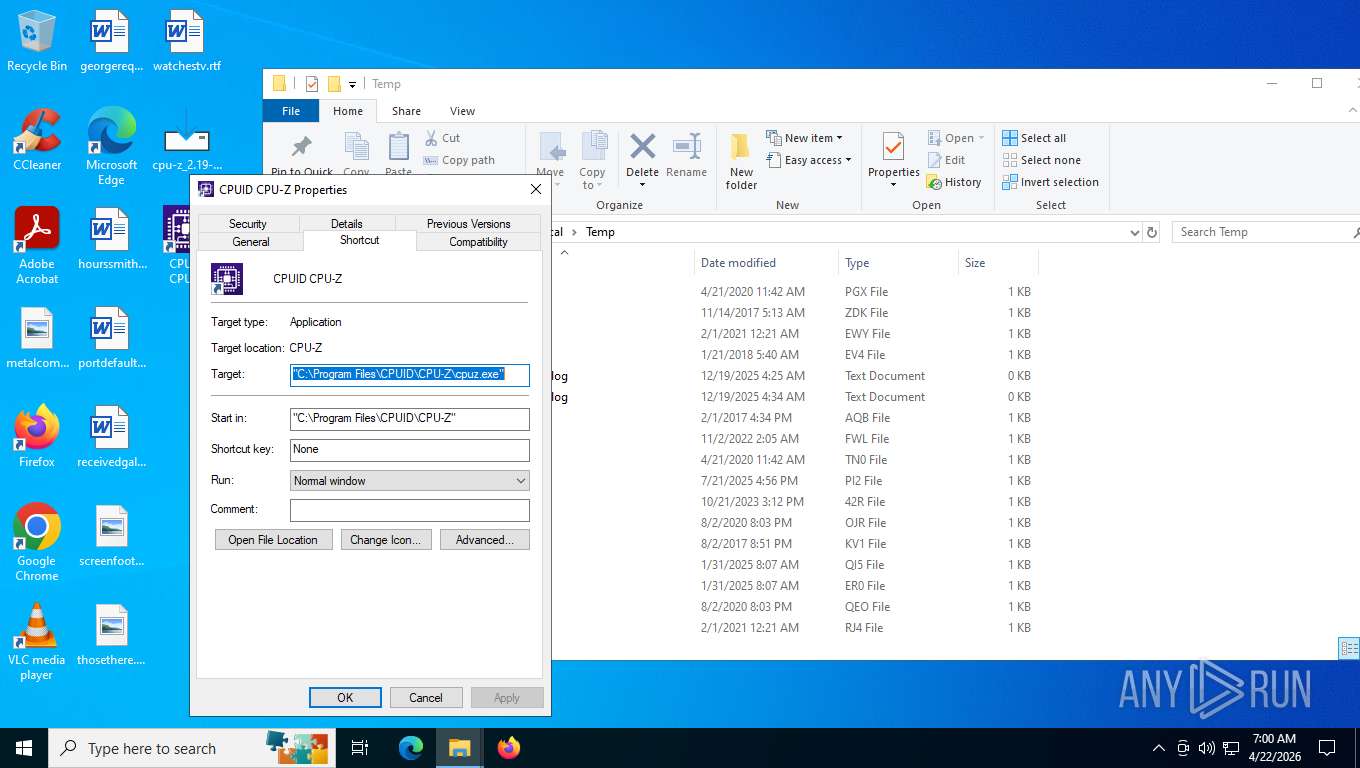
| 2000 | "C:\Program Files\CPUID\CPU-Z\cpuz.exe" | C:\Program Files\CPUID\CPU-Z\cpuz.exe | — | explorer.exe | |||||||||||
User: admin Company: CPUID Integrity Level: MEDIUM Description: CPU-Z Application Exit code: 3221226540 Version: 2, 1, 9, 0 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\CPUID\CPU-Z\cpuz.exe" | C:\Program Files\CPUID\CPU-Z\cpuz.exe | — | explorer.exe | |||||||||||
User: admin Company: CPUID Integrity Level: MEDIUM Description: CPU-Z Application Exit code: 3221226540 Version: 2, 1, 9, 0 Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\Desktop\cpu-z_2.19-en.malware.exe" /SPAWNWND=$7025E /NOTIFYWND=$90302 | C:\Users\admin\Desktop\cpu-z_2.19-en.malware.exe | cpu-z_2.19-en.malware.tmp | ||||||||||||
User: admin Company: CPUID, Inc. Integrity Level: HIGH Description: CPUID CPU-Z Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2452 | "C:\Program Files\CPUID\CPU-Z\cpuz.exe" | C:\Program Files\CPUID\CPU-Z\cpuz.exe | explorer.exe | ||||||||||||
User: admin Company: CPUID Integrity Level: HIGH Description: CPU-Z Application Exit code: 2 Version: 2, 1, 9, 0 Modules
| |||||||||||||||
| 3380 | "C:\Users\admin\AppData\Local\Temp\is-IT234.tmp\cpu-z_2.19-en.malware.tmp" /SL5="$17028C,3920132,776192,C:\Users\admin\Desktop\cpu-z_2.19-en.malware.exe" /SPAWNWND=$7025E /NOTIFYWND=$90302 | C:\Users\admin\AppData\Local\Temp\is-IT234.tmp\cpu-z_2.19-en.malware.tmp | cpu-z_2.19-en.malware.exe | ||||||||||||
User: admin Company: CPUID, Inc. Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
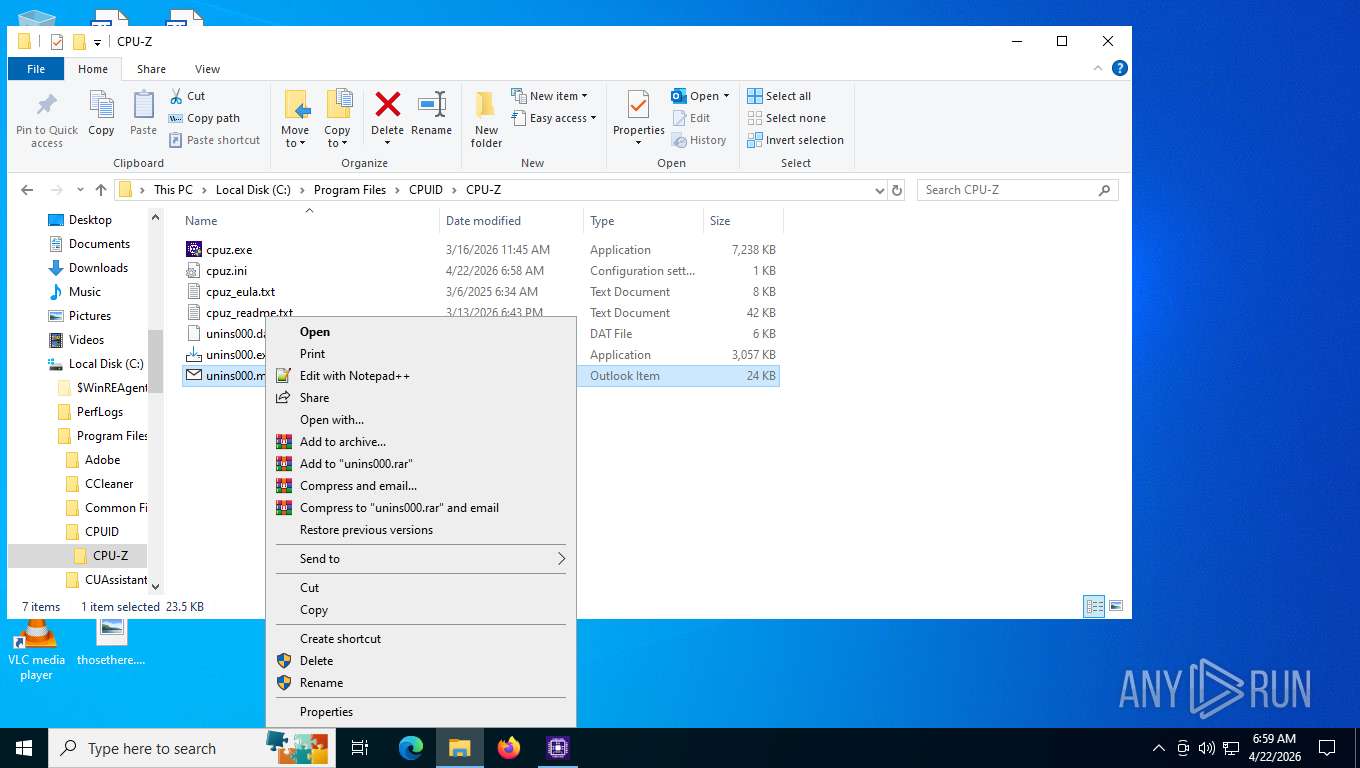
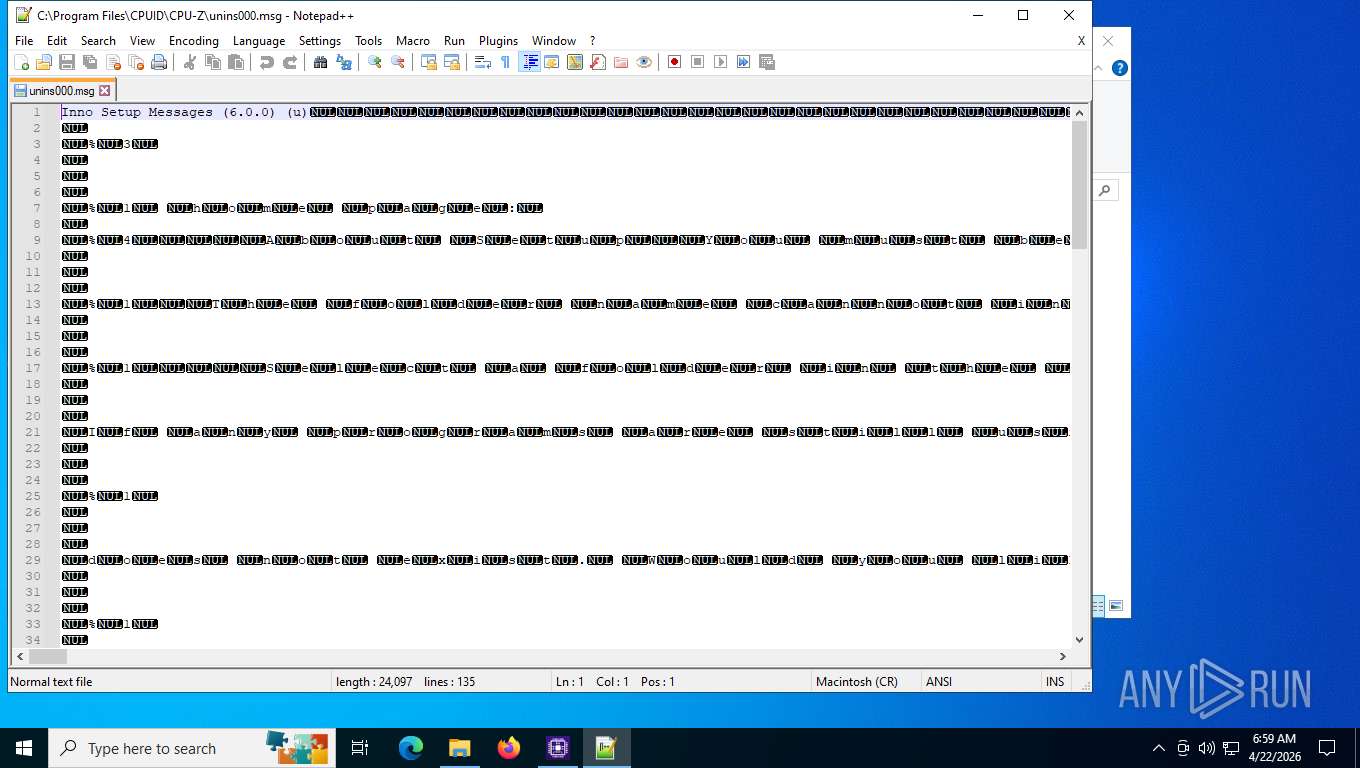
| 3420 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Program Files\CPUID\CPU-Z\unins000.msg" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 5384 | "C:\Users\admin\AppData\Local\Temp\is-V9BBS.tmp\cpu-z_2.19-en.malware.tmp" /SL5="$90302,3920132,776192,C:\Users\admin\Desktop\cpu-z_2.19-en.malware.exe" | C:\Users\admin\AppData\Local\Temp\is-V9BBS.tmp\cpu-z_2.19-en.malware.tmp | — | cpu-z_2.19-en.malware.exe | |||||||||||
User: admin Company: CPUID, Inc. Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 6472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | _setup64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6816 | "C:\Users\admin\Desktop\cpu-z_2.19-en.malware.exe" | C:\Users\admin\Desktop\cpu-z_2.19-en.malware.exe | explorer.exe | ||||||||||||
User: admin Company: CPUID, Inc. Integrity Level: MEDIUM Description: CPUID CPU-Z Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
4 661
Read events
4 592
Write events
68
Delete events
1
Modification events
| (PID) Process: | (3380) cpu-z_2.19-en.malware.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\CPUID\CPU-Z |
| Operation: | write | Name: | PATH |
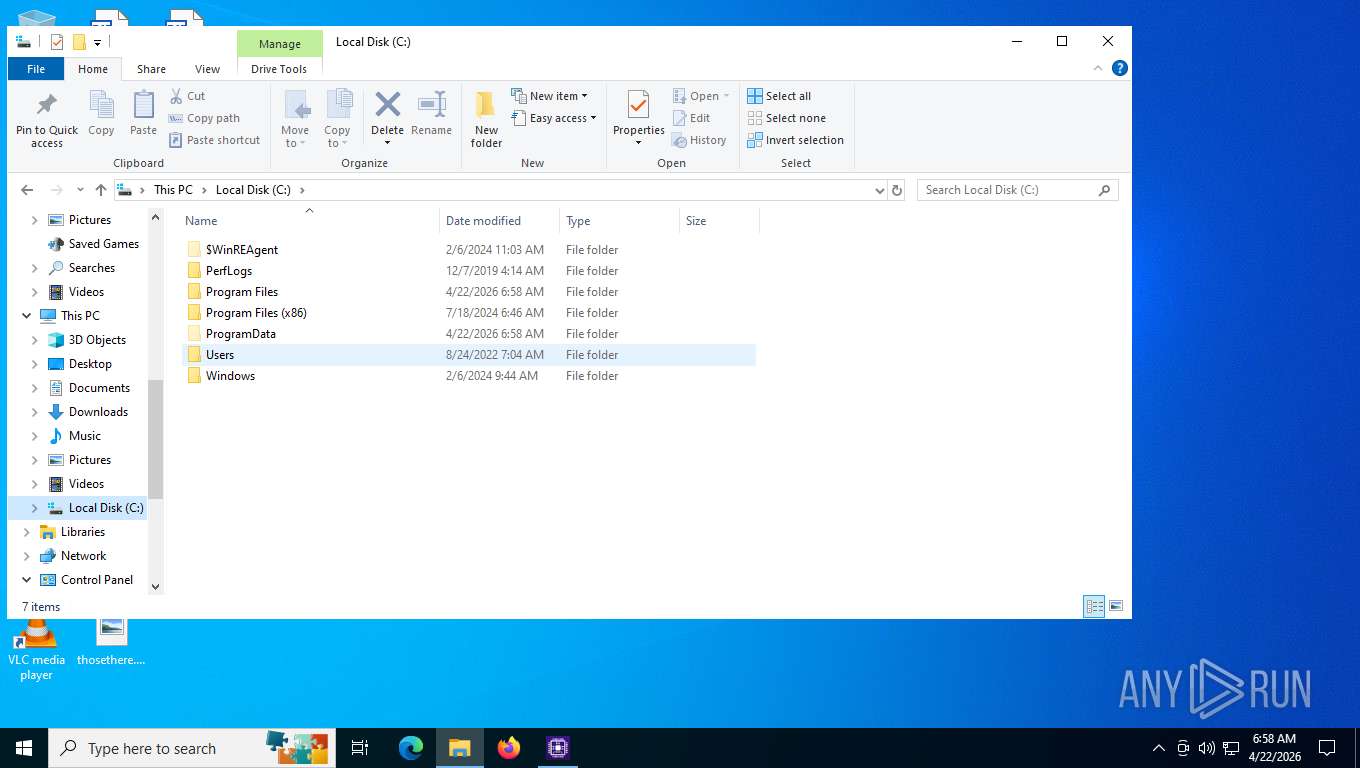
Value: C:\Program Files\CPUID\CPU-Z | |||
| (PID) Process: | (3380) cpu-z_2.19-en.malware.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\CPUID\CPU-Z |
| Operation: | write | Name: | PRODUCT_NAME |
Value: CPUID CPU-Z | |||
| (PID) Process: | (3380) cpu-z_2.19-en.malware.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\CPUID\CPU-Z |
| Operation: | write | Name: | VERSION |
Value: 2.19 | |||
| (PID) Process: | (3380) cpu-z_2.19-en.malware.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CPUID CPU-Z_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.3.2 | |||
| (PID) Process: | (3380) cpu-z_2.19-en.malware.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CPUID CPU-Z_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\CPUID\CPU-Z | |||
| (PID) Process: | (3380) cpu-z_2.19-en.malware.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CPUID CPU-Z_is1 |
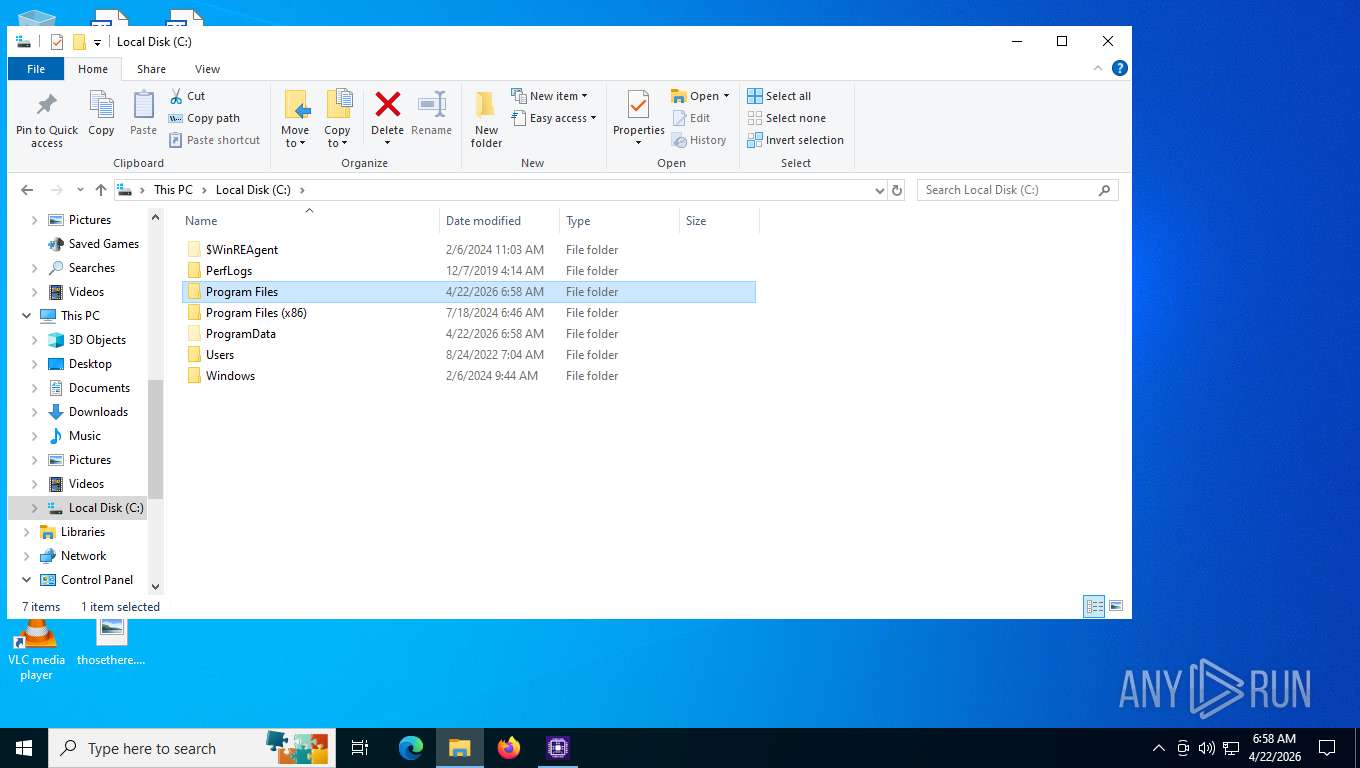
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\CPUID\CPU-Z\ | |||
| (PID) Process: | (3380) cpu-z_2.19-en.malware.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CPUID CPU-Z_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: CPUID\CPU-Z | |||
| (PID) Process: | (3380) cpu-z_2.19-en.malware.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CPUID CPU-Z_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (3380) cpu-z_2.19-en.malware.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CPUID CPU-Z_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (3380) cpu-z_2.19-en.malware.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CPUID CPU-Z_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
Executable files
10
Suspicious files
9
Text files
17
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3380 | cpu-z_2.19-en.malware.tmp | C:\Users\admin\AppData\Local\Temp\is-3LVG7.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 3380 | cpu-z_2.19-en.malware.tmp | C:\Program Files\CPUID\CPU-Z\is-AOIMD.tmp | executable | |
MD5:C4F7F0CE6B6CEAB637DA82892D2DBDC6 | SHA256:8E0077A742183FBCBB4F6CF2FE945EA2CED13A058CCF79F5B81157EDEDC47E16 | |||
| 3380 | cpu-z_2.19-en.malware.tmp | C:\Program Files\CPUID\CPU-Z\is-FDUJH.tmp | executable | |
MD5:7C96F37A4424CC7318FD5E6B4D67F8DF | SHA256:AA0CCBF7B1258D8F32A83FDCED7886B22C3AADD93999E17CC52621F0AC9BF819 | |||
| 2452 | cpu-z_2.19-en.malware.exe | C:\Users\admin\AppData\Local\Temp\is-IT234.tmp\cpu-z_2.19-en.malware.tmp | executable | |
MD5:7C96F37A4424CC7318FD5E6B4D67F8DF | SHA256:AA0CCBF7B1258D8F32A83FDCED7886B22C3AADD93999E17CC52621F0AC9BF819 | |||
| 3380 | cpu-z_2.19-en.malware.tmp | C:\Program Files\CPUID\CPU-Z\is-K3KO1.tmp | text | |
MD5:2A18A67ED5EB25E067C91B719F388426 | SHA256:D33F8C08A5DB0771D197DB4BFB6BA68D559E0A3B8855B7D58B845317EDF725D1 | |||
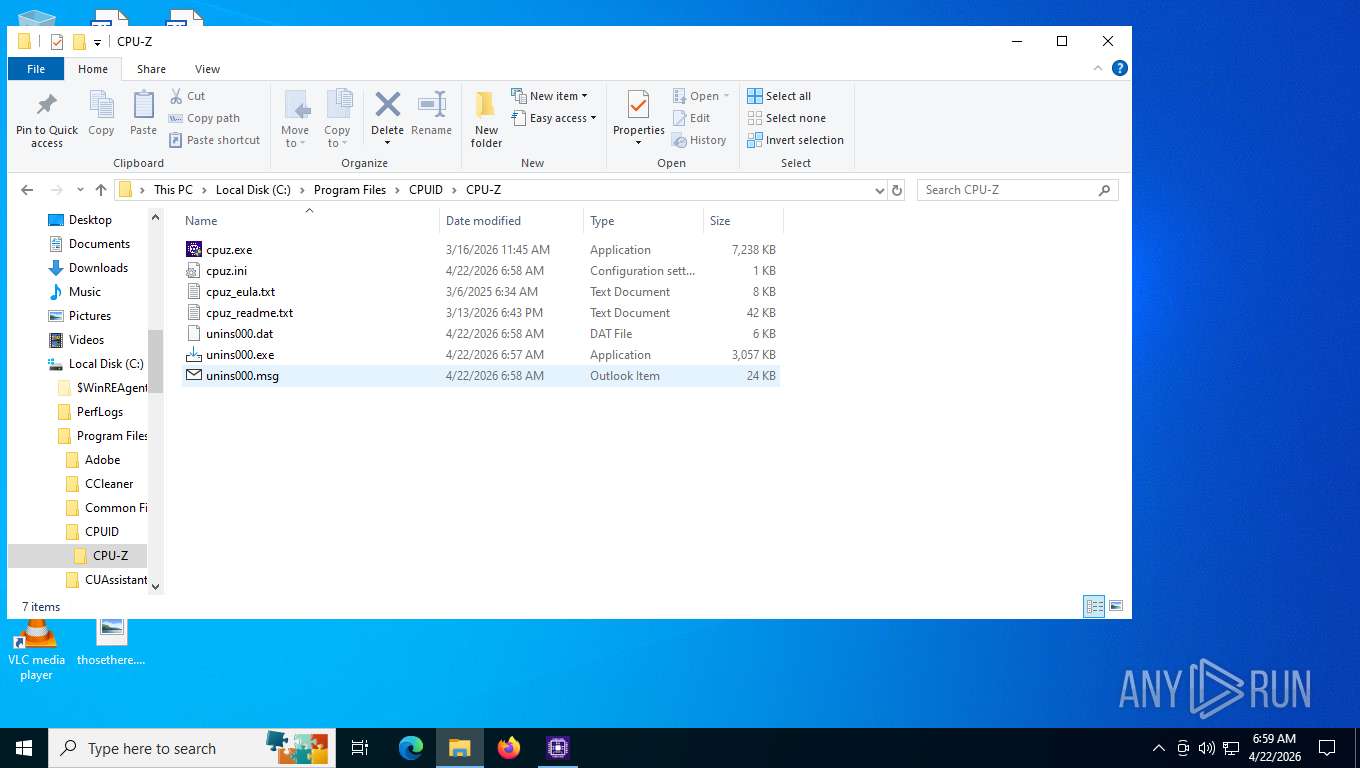
| 3380 | cpu-z_2.19-en.malware.tmp | C:\Program Files\CPUID\CPU-Z\cpuz.exe | executable | |
MD5:C4F7F0CE6B6CEAB637DA82892D2DBDC6 | SHA256:8E0077A742183FBCBB4F6CF2FE945EA2CED13A058CCF79F5B81157EDEDC47E16 | |||
| 3380 | cpu-z_2.19-en.malware.tmp | C:\Program Files\CPUID\CPU-Z\cpuz_readme.txt | text | |
MD5:15F2B115A7E5E828C368261841A7718B | SHA256:7EB3223B9759E6553FDB23F93B384F451AF342982A21343735D4349827E5D1A5 | |||
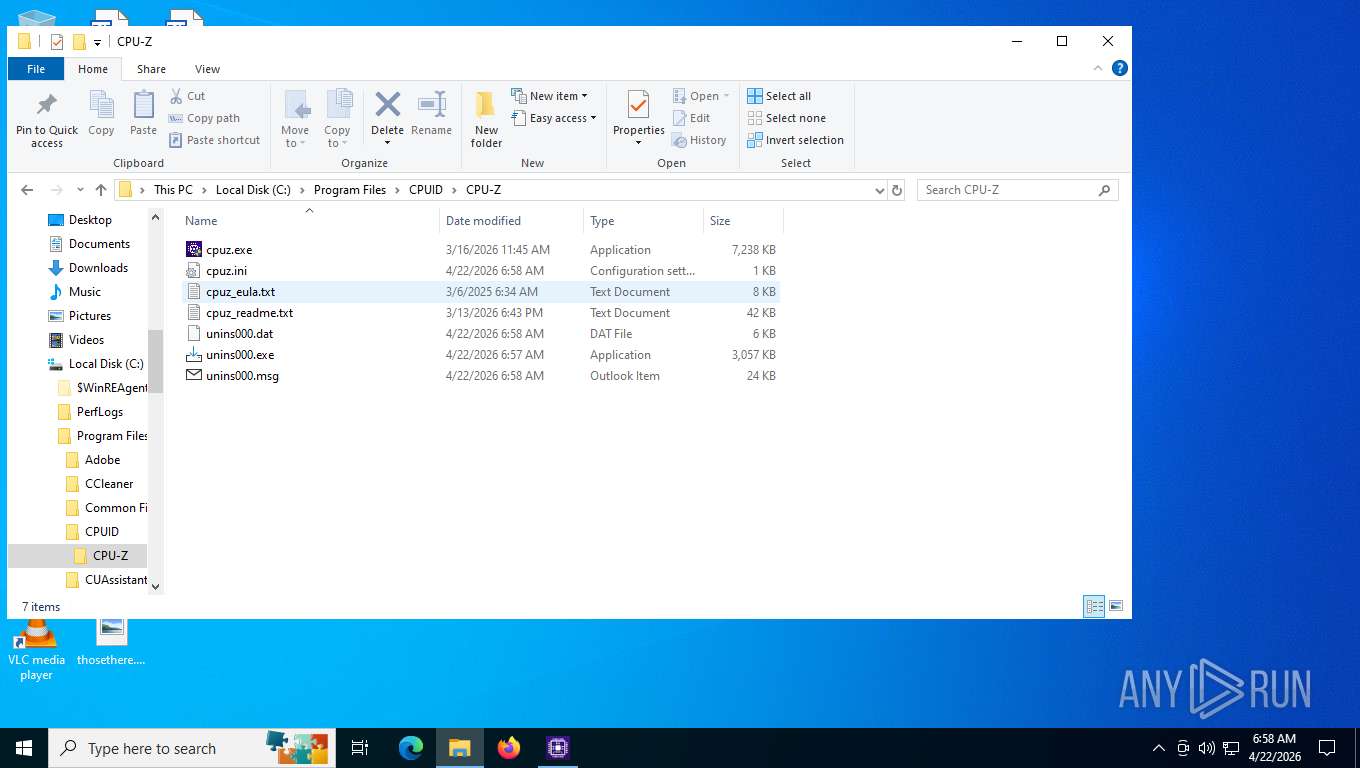
| 3380 | cpu-z_2.19-en.malware.tmp | C:\Program Files\CPUID\CPU-Z\cpuz_eula.txt | text | |
MD5:2A18A67ED5EB25E067C91B719F388426 | SHA256:D33F8C08A5DB0771D197DB4BFB6BA68D559E0A3B8855B7D58B845317EDF725D1 | |||
| 3380 | cpu-z_2.19-en.malware.tmp | C:\Program Files\CPUID\CPU-Z\unins000.exe | executable | |
MD5:7C96F37A4424CC7318FD5E6B4D67F8DF | SHA256:AA0CCBF7B1258D8F32A83FDCED7886B22C3AADD93999E17CC52621F0AC9BF819 | |||
| 6816 | cpu-z_2.19-en.malware.exe | C:\Users\admin\AppData\Local\Temp\is-V9BBS.tmp\cpu-z_2.19-en.malware.tmp | executable | |
MD5:7C96F37A4424CC7318FD5E6B4D67F8DF | SHA256:AA0CCBF7B1258D8F32A83FDCED7886B22C3AADD93999E17CC52621F0AC9BF819 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
35
DNS requests
25
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
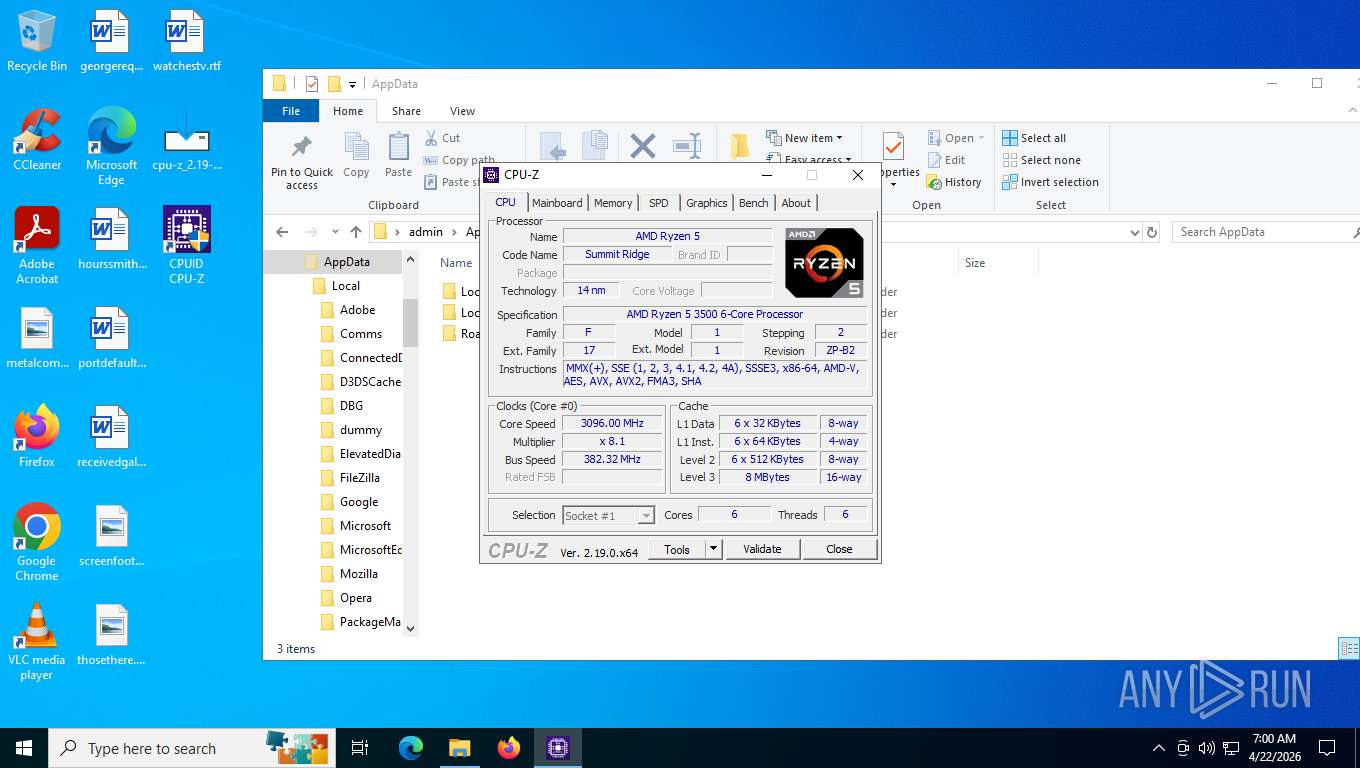
5276 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
5532 | SearchApp.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 312 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.130:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
5316 | svchost.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
3448 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
3448 | SIHClient.exe | GET | 200 | 74.178.76.54:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
3448 | SIHClient.exe | GET | 200 | 74.178.240.61:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
3448 | SIHClient.exe | GET | 304 | 74.178.240.61:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5532 | SearchApp.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 958 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.130:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6076 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6076 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6076 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6076 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3428 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6076 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|