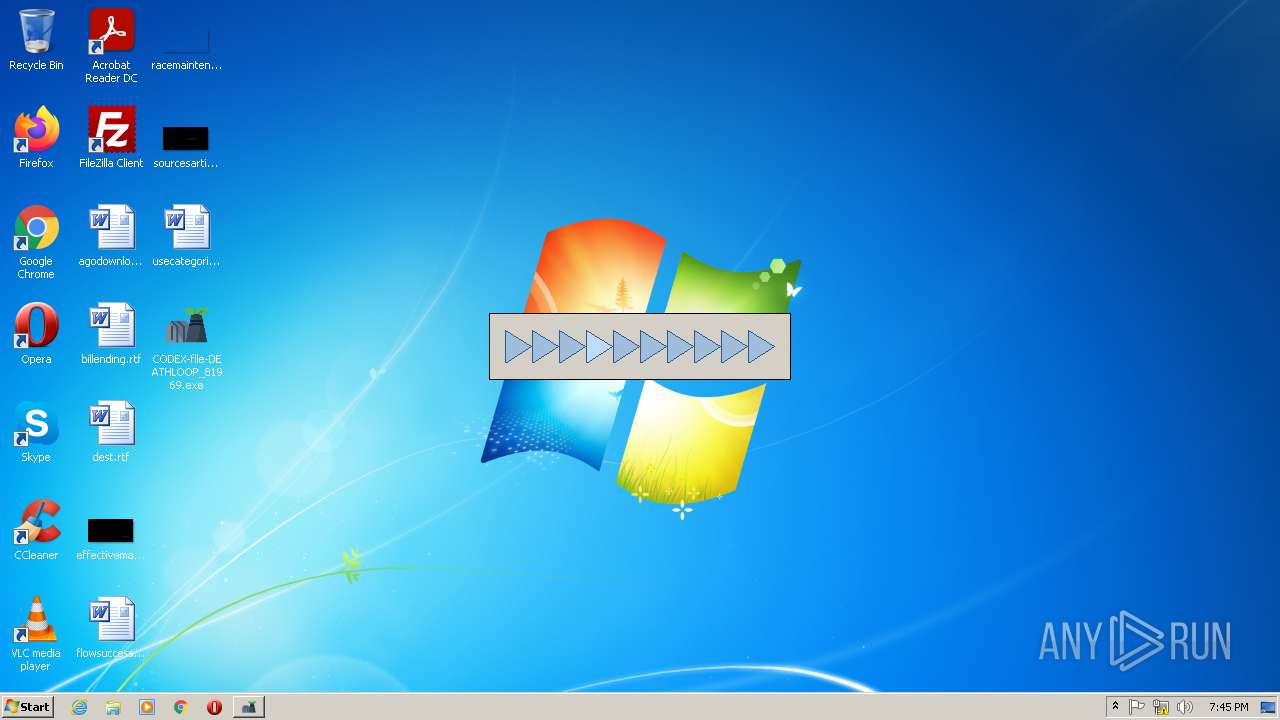
| File name: | CODEX-file-DEATHLOOP_81969.exe |
| Full analysis: | https://app.any.run/tasks/dfd7a716-9800-4b1e-b187-5c8ca838835a |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2021, 18:43:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7D28EACD05A447E90FFC35A9322510DB |
| SHA1: | 970DA1823462ED7B24E82B3DD02932B5D8FC22B4 |
| SHA256: | 969E884229E832335128DB18F02A0D015DCA7F4D0DA5553713D5252E7F6DCD31 |
| SSDEEP: | 98304:tUxAwN2LOlY0lMCTn1oz4UN6ecF+Ikq1YM6ECFV7sQsYCwxHKnP1M:tUxA5LT0lMXIkq1mHHKnP+ |
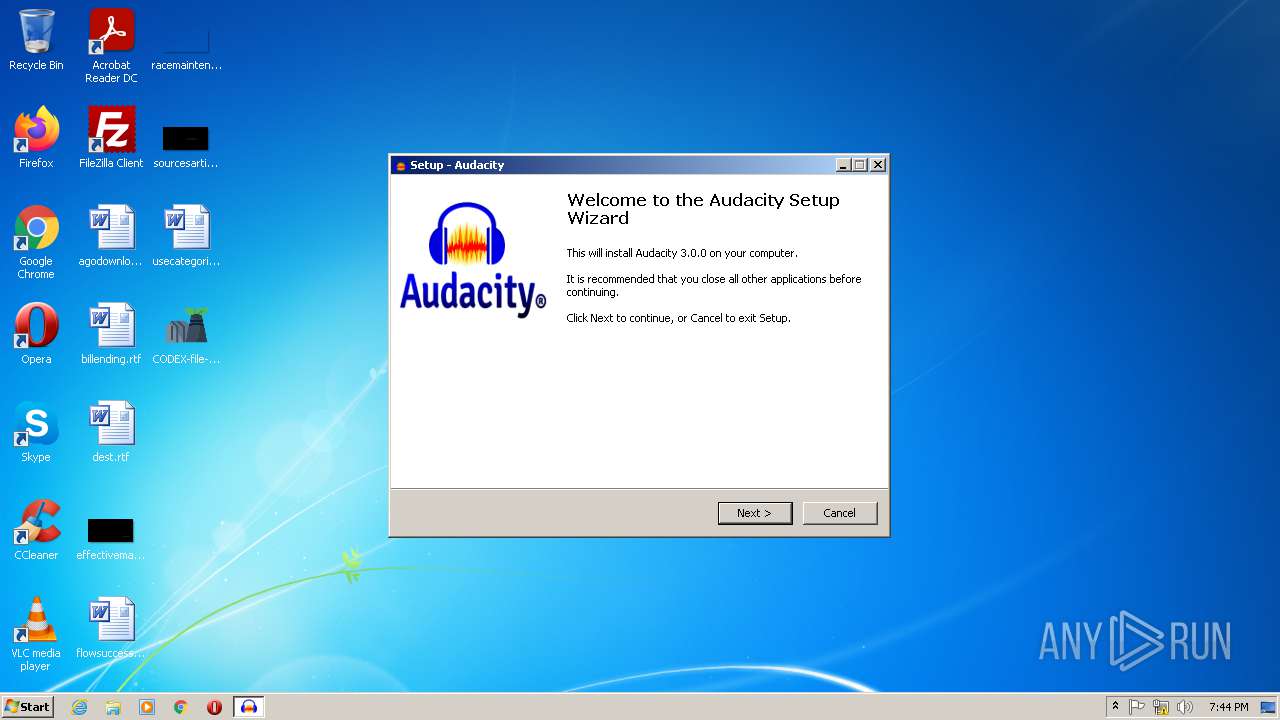
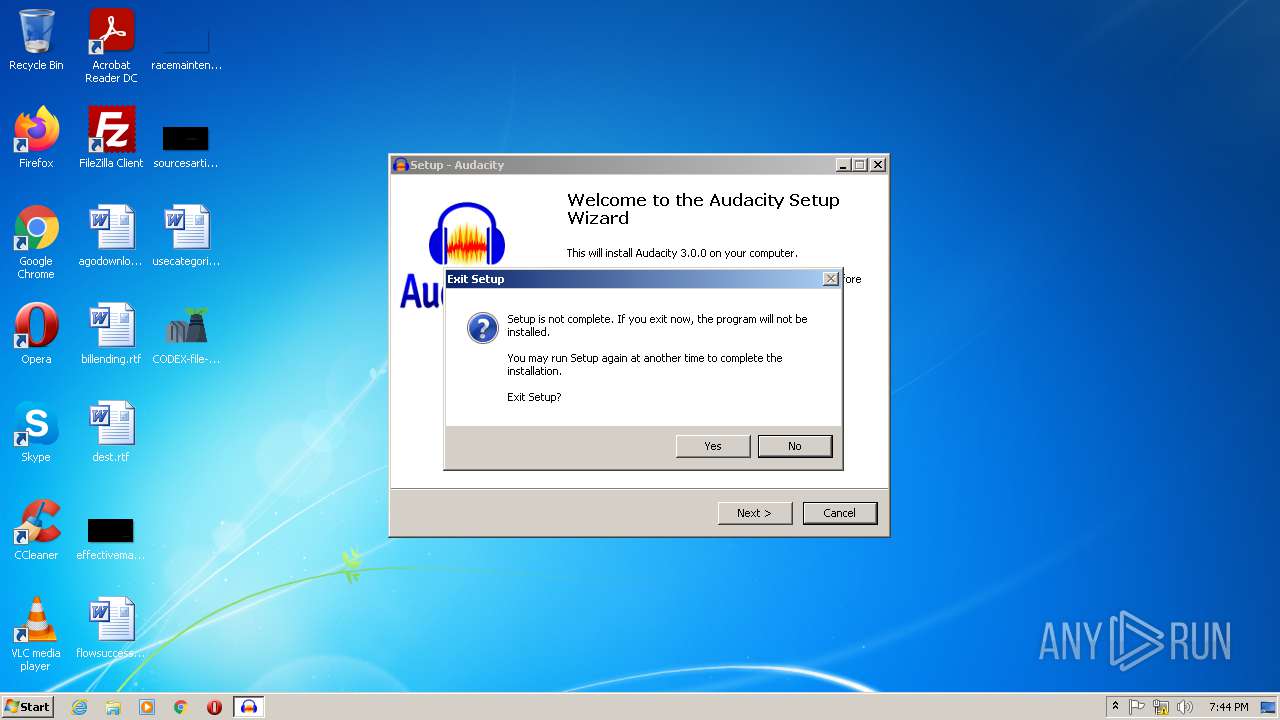
MALICIOUS
Changes settings of System certificates
- CODEX-file-DEATHLOOP_81969.exe (PID: 3356)
Drops executable file immediately after starts
- NuclearhSafety.exe (PID: 4036)
- NuclearySafety.exe (PID: 2116)
- chrome.exe (PID: 1692)
Application was dropped or rewritten from another process
- NuclearhSafety.exe (PID: 4036)
- NuclearySafety.exe (PID: 2116)
SUSPICIOUS
Checks supported languages
- CODEX-file-DEATHLOOP_81969.exe (PID: 116)
- CODEX-file-DEATHLOOP_81969.exe (PID: 3356)
- cmd.exe (PID: 3856)
- cmd.exe (PID: 268)
- NuclearhSafety.exe (PID: 4036)
- NuclearhSafety.tmp (PID: 3404)
- CODEX-file-DEATHLOOP_81969.exe (PID: 1940)
- cmd.exe (PID: 756)
- NuclearySafety.exe (PID: 2116)
- CODEX-file-DEATHLOOP_81969.exe (PID: 3896)
- cmd.exe (PID: 1808)
- NuclearySafety.tmp (PID: 3300)
Starts CMD.EXE for commands execution
- CODEX-file-DEATHLOOP_81969.exe (PID: 3356)
- CODEX-file-DEATHLOOP_81969.exe (PID: 3896)
Application launched itself
- CODEX-file-DEATHLOOP_81969.exe (PID: 116)
- CODEX-file-DEATHLOOP_81969.exe (PID: 1940)
Starts SC.EXE for service management
- cmd.exe (PID: 268)
- cmd.exe (PID: 3856)
- cmd.exe (PID: 1808)
- cmd.exe (PID: 756)
Reads the computer name
- CODEX-file-DEATHLOOP_81969.exe (PID: 116)
- CODEX-file-DEATHLOOP_81969.exe (PID: 3356)
- NuclearhSafety.tmp (PID: 3404)
- CODEX-file-DEATHLOOP_81969.exe (PID: 1940)
- CODEX-file-DEATHLOOP_81969.exe (PID: 3896)
- NuclearySafety.tmp (PID: 3300)
Adds / modifies Windows certificates
- CODEX-file-DEATHLOOP_81969.exe (PID: 3356)
Creates a directory in Program Files
- CODEX-file-DEATHLOOP_81969.exe (PID: 3356)
- CODEX-file-DEATHLOOP_81969.exe (PID: 3896)
- NuclearySafety.tmp (PID: 3300)
Creates files in the program directory
- CODEX-file-DEATHLOOP_81969.exe (PID: 3356)
- CODEX-file-DEATHLOOP_81969.exe (PID: 3896)
Executable content was dropped or overwritten
- CODEX-file-DEATHLOOP_81969.exe (PID: 3356)
- NuclearhSafety.exe (PID: 4036)
- CODEX-file-DEATHLOOP_81969.exe (PID: 3896)
- NuclearySafety.exe (PID: 2116)
- NuclearySafety.tmp (PID: 3300)
- chrome.exe (PID: 1692)
Reads the Windows organization settings
- NuclearhSafety.tmp (PID: 3404)
- NuclearySafety.tmp (PID: 3300)
Reads Windows owner or organization settings
- NuclearhSafety.tmp (PID: 3404)
- NuclearySafety.tmp (PID: 3300)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2856)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 1692)
- NuclearySafety.tmp (PID: 3300)
INFO
Checks supported languages
- sc.exe (PID: 3064)
- find.exe (PID: 2076)
- find.exe (PID: 564)
- sc.exe (PID: 2344)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 1952)
- chrome.exe (PID: 1244)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 2416)
- chrome.exe (PID: 1180)
- chrome.exe (PID: 596)
- chrome.exe (PID: 2804)
- sc.exe (PID: 1900)
- find.exe (PID: 3300)
- sc.exe (PID: 3520)
- find.exe (PID: 3528)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 3168)
- chrome.exe (PID: 1224)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 3868)
- chrome.exe (PID: 240)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 1460)
- chrome.exe (PID: 1240)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 1244)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 3400)
- chrome.exe (PID: 2080)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 1692)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 1944)
- chrome.exe (PID: 1620)
Reads the computer name
- sc.exe (PID: 2344)
- sc.exe (PID: 3064)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 596)
- chrome.exe (PID: 2804)
- sc.exe (PID: 3520)
- sc.exe (PID: 1900)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 1224)
- chrome.exe (PID: 2080)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 1244)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 2868)
Checks Windows Trust Settings
- CODEX-file-DEATHLOOP_81969.exe (PID: 3356)
- CODEX-file-DEATHLOOP_81969.exe (PID: 3896)
Reads settings of System Certificates
- CODEX-file-DEATHLOOP_81969.exe (PID: 3356)
- chrome.exe (PID: 3224)
- CODEX-file-DEATHLOOP_81969.exe (PID: 3896)
- chrome.exe (PID: 2856)
Application launched itself
- chrome.exe (PID: 2960)
- chrome.exe (PID: 2856)
Reads the hosts file
- chrome.exe (PID: 2960)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 1588)
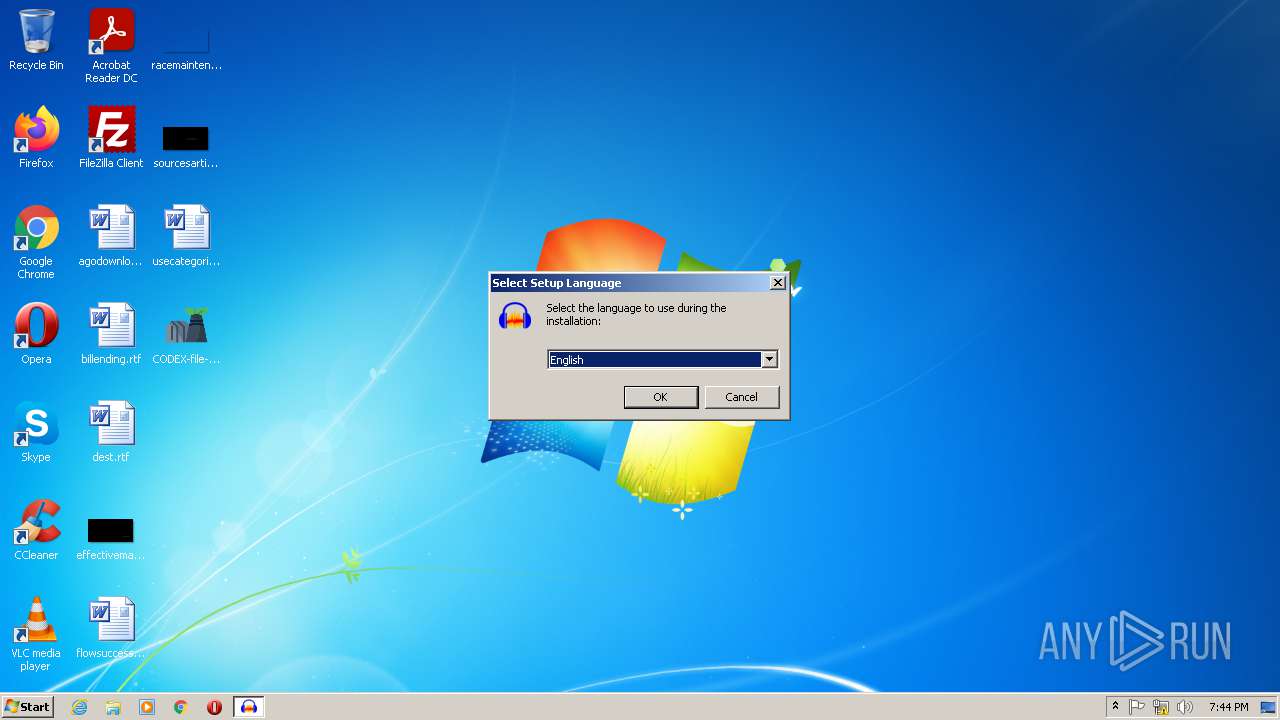
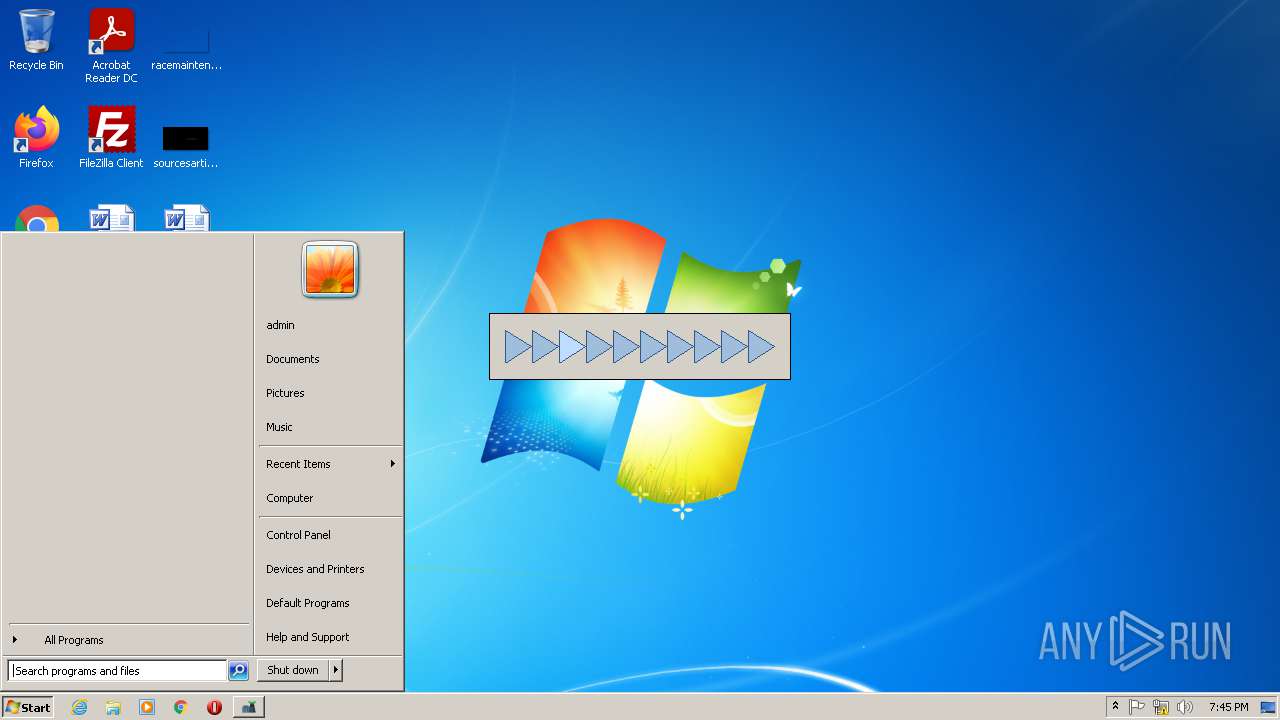
Manual execution by user
- chrome.exe (PID: 2960)
- CODEX-file-DEATHLOOP_81969.exe (PID: 1940)
- chrome.exe (PID: 2856)
Application was dropped or rewritten from another process
- NuclearhSafety.tmp (PID: 3404)
- NuclearySafety.tmp (PID: 3300)
Creates files in the program directory
- NuclearySafety.tmp (PID: 3300)
Reads the date of Windows installation
- chrome.exe (PID: 3904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (83.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (8.7) |
| .exe | | | Generic Win/DOS Executable (3.8) |
| .exe | | | DOS Executable Generic (3.8) |
EXIF
EXE
| ProductVersion: | 1.0.0.0 |
|---|---|
| ProductName: | Nuclear Install |
| OriginalFileName: | NuclearInstall.exe |
| LegalCopyright: | Nuclear Safety Install (c) 2021. All rights reserved. |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Nuclear Install |
| CompanyName: | Nuclear Safety Install |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x227611 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1679872 |
| CodeSize: | 2559488 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2021:09:03 15:29:27+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Sep-2021 13:29:27 |
| Detected languages: |
|
| CompanyName: | Nuclear Safety Install |
| FileDescription: | Nuclear Install |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | Nuclear Safety Install (c) 2021. All rights reserved. |
| OriginalFilename: | NuclearInstall.exe |
| ProductName: | Nuclear Install |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 03-Sep-2021 13:29:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00270D0D | 0x00270E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47045 |
.rdata | 0x00272000 | 0x0005A8D2 | 0x0005AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.26457 |
.data | 0x002CD000 | 0x0000CEA0 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.81269 |
.gfids | 0x002DA000 | 0x0001AAEC | 0x0001AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.23435 |
.giats | 0x002F5000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.155178 |
.tls | 0x002F6000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x002F7000 | 0x000F4DC8 | 0x000F4E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.33379 |
.reloc | 0x003EC000 | 0x00022878 | 0x00022A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.5243 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13553 | 1773 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.02695 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3 | 2.74274 | 180 | UNKNOWN | English - United States | RT_CURSOR |
4 | 2.34038 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.34004 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.51649 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.45401 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 2.34864 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 2.34505 | 308 | UNKNOWN | English - United States | RT_CURSOR |
10 | 2.34864 | 308 | UNKNOWN | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
105
Monitored processes
57
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\Desktop\CODEX-file-DEATHLOOP_81969.exe" | C:\Users\admin\Desktop\CODEX-file-DEATHLOOP_81969.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Nuclear Safety Install Integrity Level: MEDIUM Description: Nuclear Install Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,2420752700408524362,3469937184738142039,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 268 | C:\Windows\system32\cmd.exe /c sc query npcap | FIND /C "RUNNING" | C:\Windows\system32\cmd.exe | — | CODEX-file-DEATHLOOP_81969.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 564 | FIND /C "RUNNING" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,7043175666385685504,12669929704300669662,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 756 | C:\Windows\system32\cmd.exe /c sc query NPF | FIND /C "RUNNING" | C:\Windows\system32\cmd.exe | — | CODEX-file-DEATHLOOP_81969.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,7043175666385685504,12669929704300669662,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,2420752700408524362,3469937184738142039,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,2420752700408524362,3469937184738142039,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,7043175666385685504,12669929704300669662,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2800 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
32 341
Read events
32 085
Write events
244
Delete events
12
Modification events
| (PID) Process: | (116) CODEX-file-DEATHLOOP_81969.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (116) CODEX-file-DEATHLOOP_81969.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (116) CODEX-file-DEATHLOOP_81969.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (116) CODEX-file-DEATHLOOP_81969.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3356) CODEX-file-DEATHLOOP_81969.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3356) CODEX-file-DEATHLOOP_81969.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3356) CODEX-file-DEATHLOOP_81969.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3356) CODEX-file-DEATHLOOP_81969.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3356) CODEX-file-DEATHLOOP_81969.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000042010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3356) CODEX-file-DEATHLOOP_81969.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
29
Suspicious files
82
Text files
3 089
Unknown types
153
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61423EFA-B90.pma | — | |
MD5:— | SHA256:— | |||
| 3356 | CODEX-file-DEATHLOOP_81969.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\644B8874112055B5E195ECB0E8F243A4 | der | |
MD5:— | SHA256:— | |||
| 3356 | CODEX-file-DEATHLOOP_81969.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\644B8874112055B5E195ECB0E8F243A4 | binary | |
MD5:— | SHA256:— | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | binary | |
MD5:— | SHA256:— | |||
| 3356 | CODEX-file-DEATHLOOP_81969.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3356 | CODEX-file-DEATHLOOP_81969.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3356 | CODEX-file-DEATHLOOP_81969.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:54E9306F95F32E50CCD58AF19753D929 | SHA256:45F94DCEB18A8F738A26DA09CE4558995A4FE02B971882E8116FC9B59813BB72 | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | vxd | |
MD5:41876349CB12D6DB992F1309F22DF3F0 | SHA256:E09F42C398D688DCE168570291F1F92D079987DEDA3099A34ADB9E8C0522B30C | |||
| 3696 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
41
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | — | — | whitelisted |
— | — | HEAD | 200 | 173.194.160.71:80 | http://r2---sn-1gi7znes.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3?cms_redirect=yes&mh=DH&mip=85.203.45.40&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1631731219&mv=m&mvi=2&pl=24&rmhost=r1---sn-1gi7znes.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
— | — | GET | 206 | 173.194.160.71:80 | http://r2---sn-1gi7znes.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3?cms_redirect=yes&mh=DH&mip=85.203.45.40&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1631731219&mv=m&mvi=2&pl=24&rmhost=r1---sn-1gi7znes.gvt1.com&shardbypass=yes | US | binary | 10.3 Kb | whitelisted |
— | — | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | html | 574 b | whitelisted |
— | — | GET | 206 | 173.194.160.71:80 | http://r2---sn-1gi7znes.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3?cms_redirect=yes&mh=DH&mip=85.203.45.40&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1631731219&mv=m&mvi=2&pl=24&rmhost=r1---sn-1gi7znes.gvt1.com&shardbypass=yes | US | binary | 10.1 Kb | whitelisted |
— | — | GET | 206 | 173.194.160.71:80 | http://r2---sn-1gi7znes.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3?cms_redirect=yes&mh=DH&mip=85.203.45.40&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1631731459&mv=m&mvi=2&pl=24&rmhost=r1---sn-1gi7znes.gvt1.com&shardbypass=yes | US | binary | 10.1 Kb | whitelisted |
— | — | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | html | 574 b | whitelisted |
— | — | GET | 206 | 173.194.160.71:80 | http://r2---sn-1gi7znes.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3?cms_redirect=yes&mh=DH&mip=85.203.45.40&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1631731219&mv=m&mvi=2&pl=24&rmhost=r1---sn-1gi7znes.gvt1.com&shardbypass=yes | US | binary | 5.64 Kb | whitelisted |
— | — | GET | 206 | 173.194.160.71:80 | http://r2---sn-1gi7znes.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3?cms_redirect=yes&mh=DH&mip=85.203.45.40&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1631731219&mv=m&mvi=2&pl=24&rmhost=r1---sn-1gi7znes.gvt1.com&shardbypass=yes | US | binary | 21.7 Kb | whitelisted |
1588 | chrome.exe | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 592 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3356 | CODEX-file-DEATHLOOP_81969.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3224 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3224 | chrome.exe | 142.250.180.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3224 | chrome.exe | 142.250.184.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3224 | chrome.exe | 142.250.186.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3224 | chrome.exe | 172.217.19.110:443 | apis.google.com | Google Inc. | US | whitelisted |
1588 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
1588 | chrome.exe | 142.250.185.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 142.250.185.99:443 | update.googleapis.com | Google Inc. | US | whitelisted |
1588 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
universalappshop.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
crl.identrust.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |