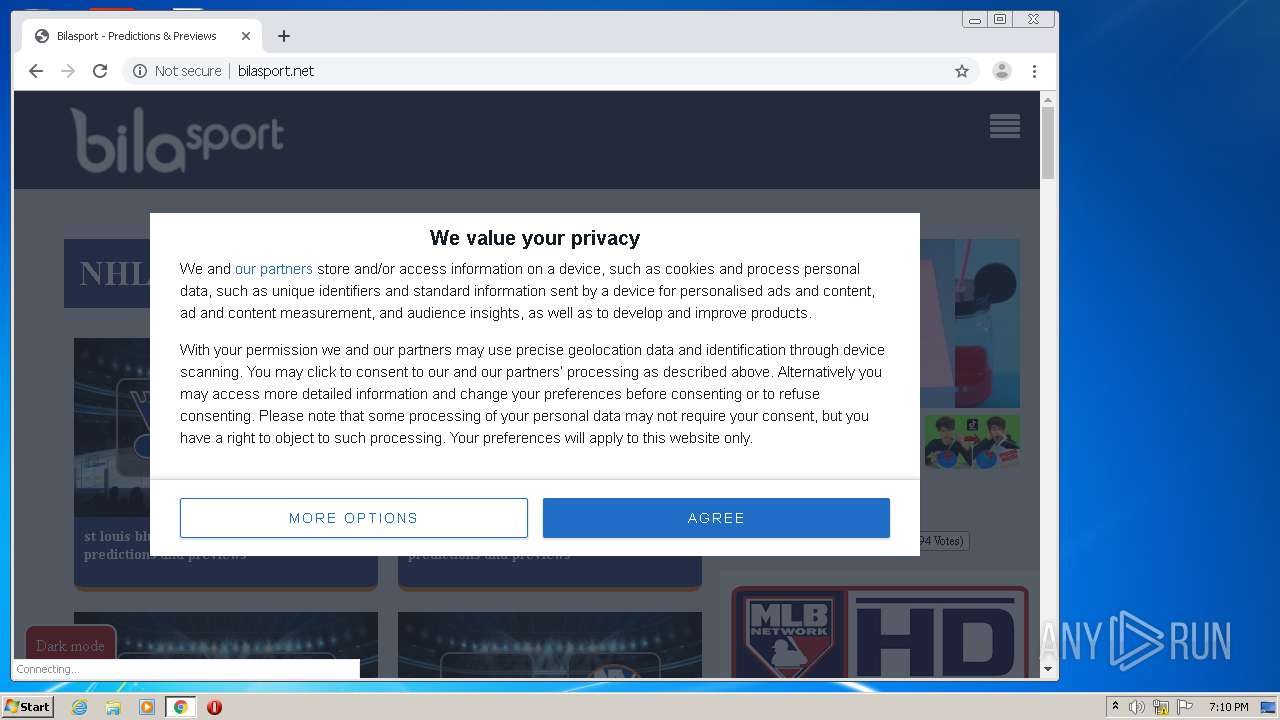
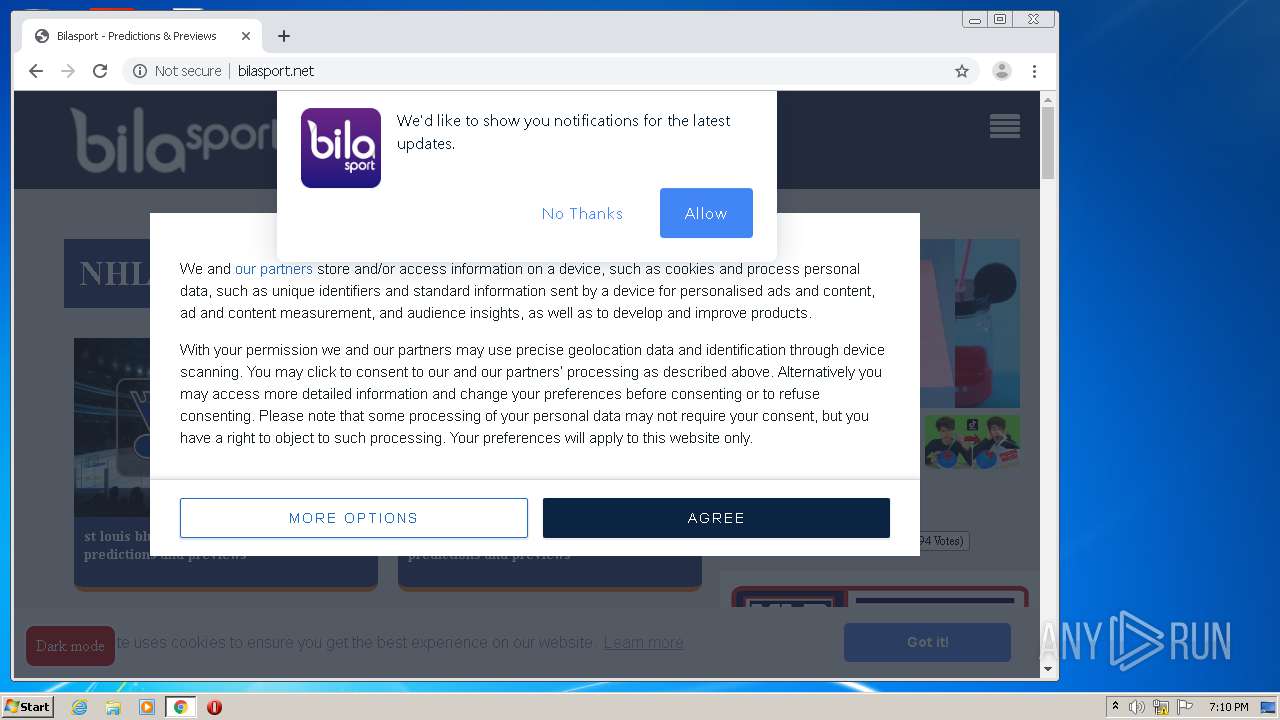
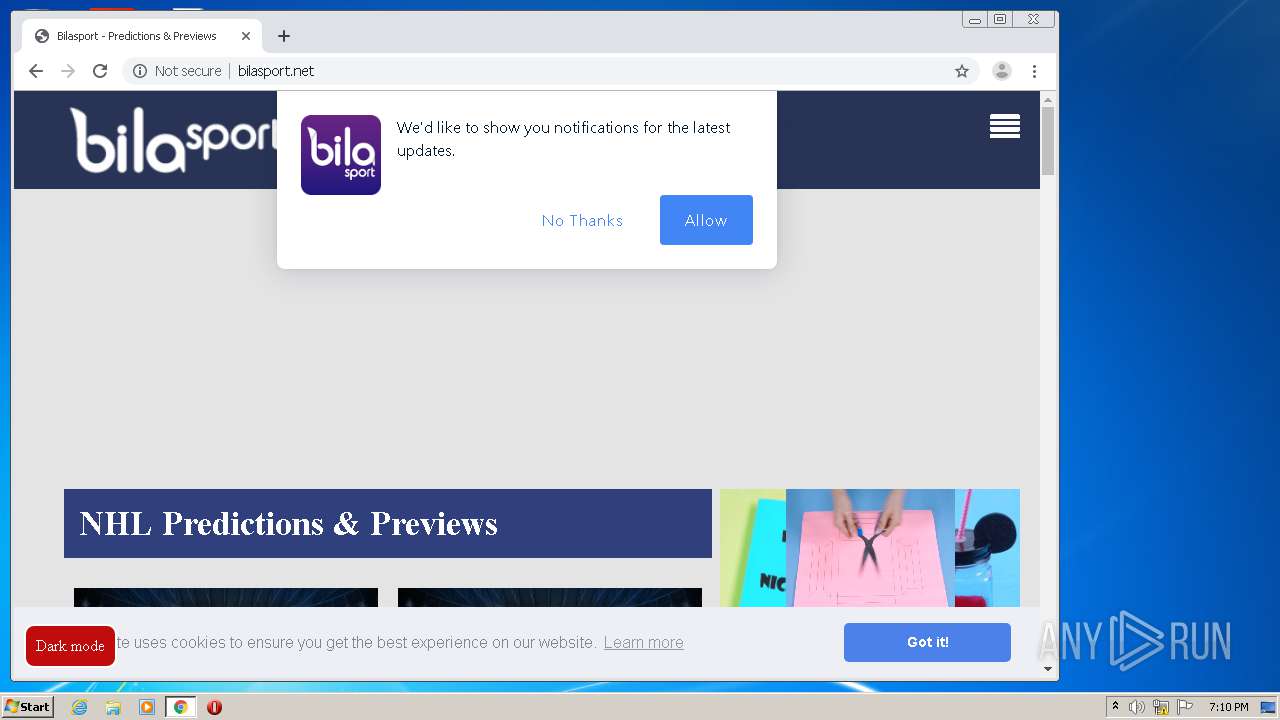
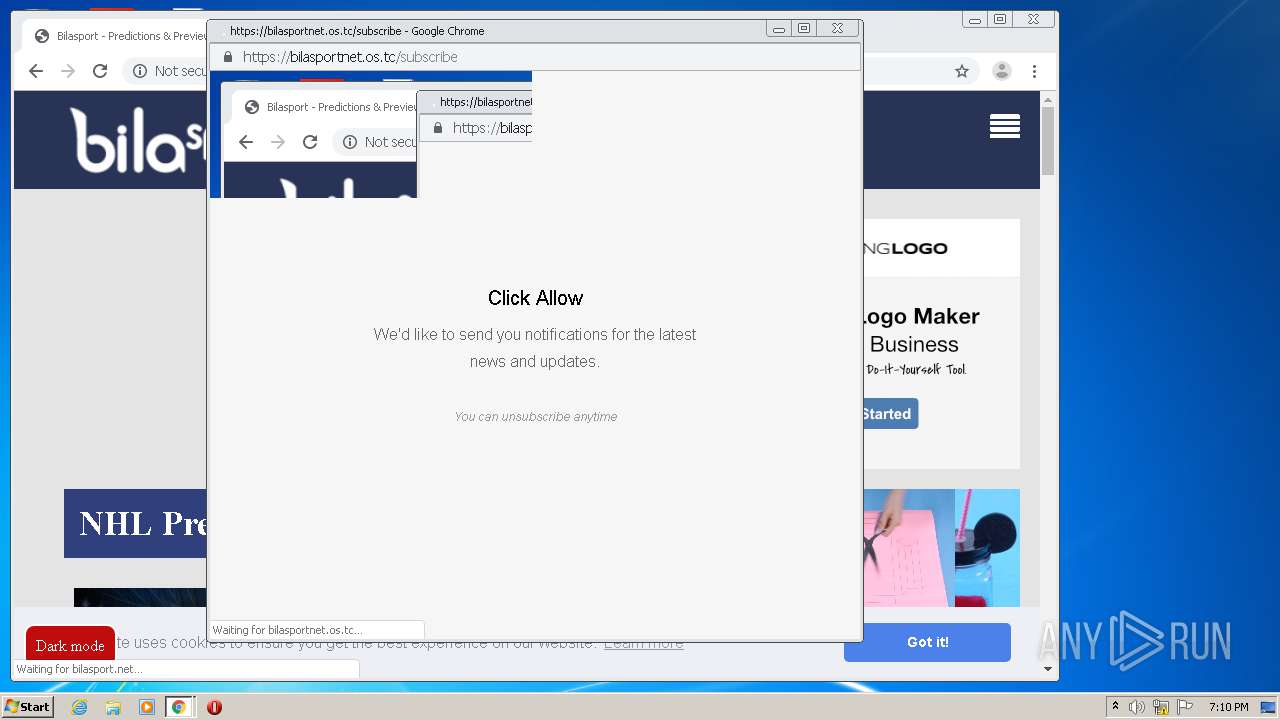
| URL: | https://bilasport.net |
| Full analysis: | https://app.any.run/tasks/1f8fbc88-9192-46ce-8a59-e95db731c59d |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2020, 18:10:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 297560842D65FFD525B34252E9A0B71F |
| SHA1: | 157FDBF8F25FCBE86F891B8C5963ECABC0AFDD0E |
| SHA256: | 969E0CB6B214FDADD7007114ED648D141CE2DEBB4CAC3E019E1BF52CD67CC8B1 |
| SSDEEP: | 3:N8RB/0:2RBs |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2872)
- iexplore.exe (PID: 2180)
Application launched itself
- iexplore.exe (PID: 2872)
- chrome.exe (PID: 4060)
Changes internet zones settings
- iexplore.exe (PID: 2872)
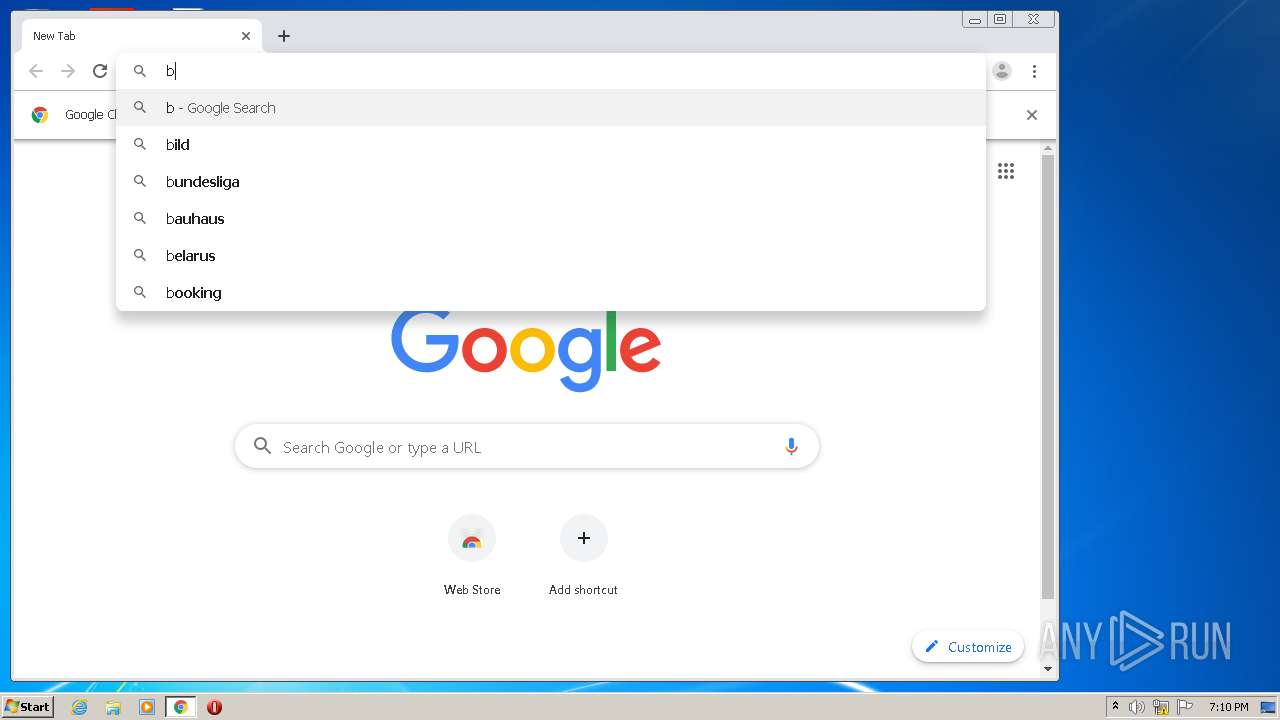
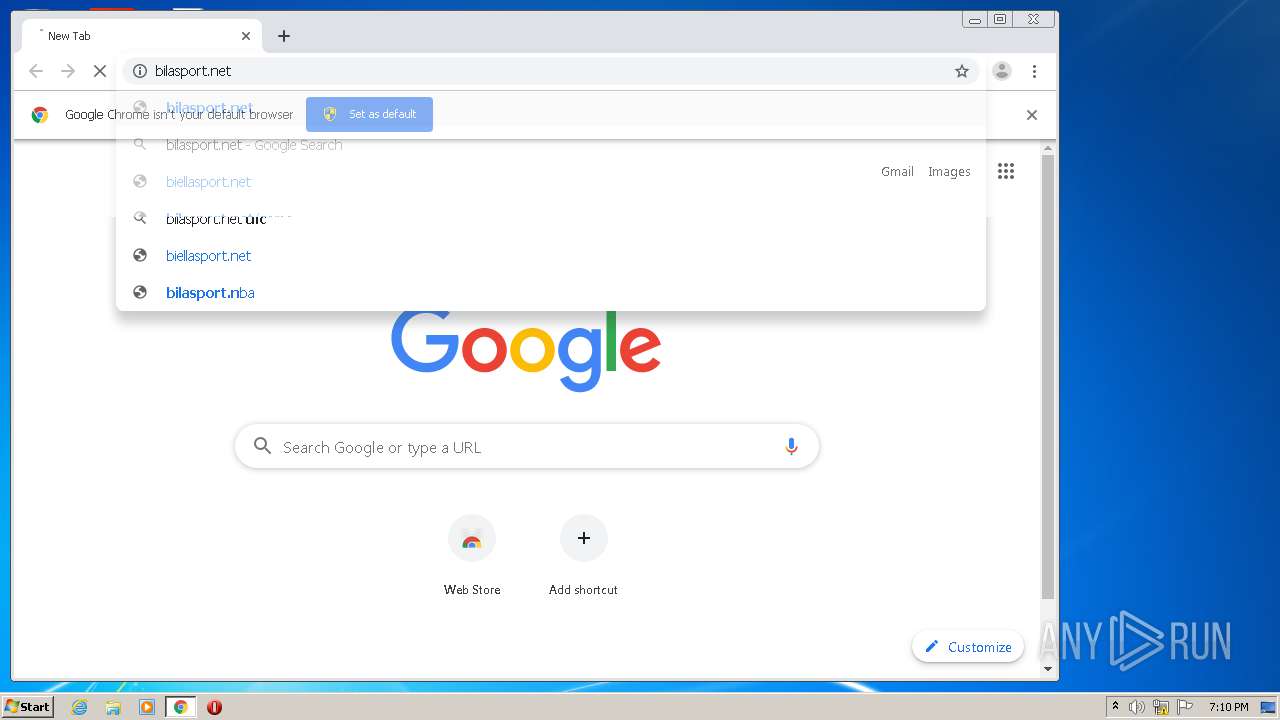
Manual execution by user
- chrome.exe (PID: 4060)
Reads the hosts file
- chrome.exe (PID: 4060)
- chrome.exe (PID: 2432)
Reads settings of System Certificates
- chrome.exe (PID: 2432)
Changes settings of System certificates
- chrome.exe (PID: 2432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
97
Monitored processes
59
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,7740178136881855999,15136693964254631618,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7227386252912929605 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4048 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,7740178136881855999,15136693964254631618,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5929461069914012164 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,7740178136881855999,15136693964254631618,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13047993684951024694 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,7740178136881855999,15136693964254631618,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10375947916310578550 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,7740178136881855999,15136693964254631618,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=966646883990056865 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,7740178136881855999,15136693964254631618,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9116951979634500730 --mojo-platform-channel-handle=3580 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,7740178136881855999,15136693964254631618,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17623499043505637769 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,7740178136881855999,15136693964254631618,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2290100002493111631 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,7740178136881855999,15136693964254631618,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16994745757326188181 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
921
Read events
712
Write events
200
Delete events
9
Modification events
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3865118812 | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30830803 | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
113
Text files
99
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3724550B87FCC755.TMP | — | |
MD5:— | SHA256:— | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFF065B85B3209EAF.TMP | — | |
MD5:— | SHA256:— | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB00C5DDF6C167E0C.TMP | — | |
MD5:— | SHA256:— | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{121DA31D-DCC7-11EA-99F8-12A9866C77DE}.dat | — | |
MD5:— | SHA256:— | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF074EF688C7E37052.TMP | — | |
MD5:— | SHA256:— | |||
| 2872 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{121DA31B-DCC7-11EA-99F8-12A9866C77DE}.dat | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF19258f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
109
TCP/UDP connections
221
DNS requests
162
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
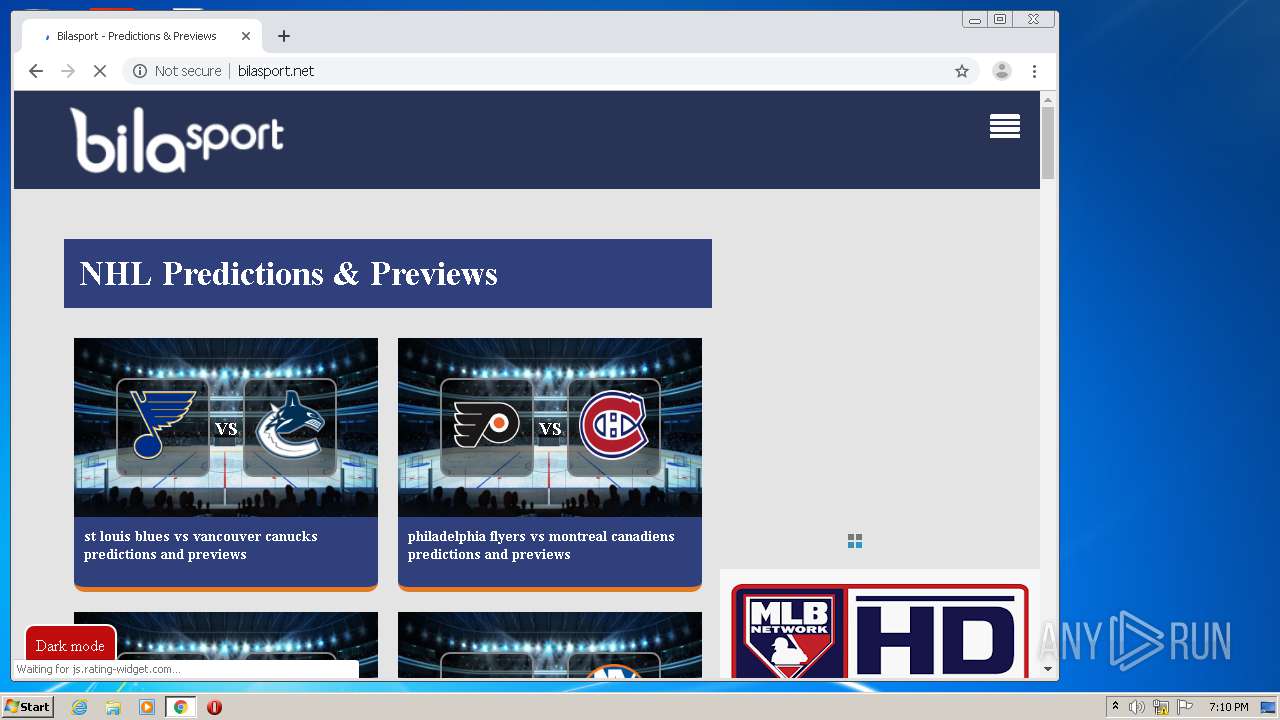
2432 | chrome.exe | GET | 200 | 192.124.249.4:80 | http://bilasport.net/css/font-awesome.min.css | US | text | 5.32 Kb | malicious |
2432 | chrome.exe | GET | 200 | 192.124.249.4:80 | http://bilasport.net/css/fa-snapchat.css | US | text | 191 b | malicious |
2432 | chrome.exe | GET | 200 | 104.17.78.107:80 | http://cdnjs.cloudflare.com/ajax/libs/cookieconsent2/3.1.0/cookieconsent.min.js | US | text | 6.71 Kb | whitelisted |
2432 | chrome.exe | GET | 200 | 192.124.249.4:80 | http://bilasport.net/ | US | html | 6.68 Kb | malicious |
2432 | chrome.exe | GET | 200 | 104.17.78.107:80 | http://cdnjs.cloudflare.com/ajax/libs/cookieconsent2/3.1.0/cookieconsent.min.css | US | text | 1.19 Kb | whitelisted |
2432 | chrome.exe | GET | 200 | 192.124.249.4:80 | http://bilasport.net/css/pagination.css | US | text | 569 b | malicious |
2432 | chrome.exe | GET | 200 | 192.124.249.4:80 | http://bilasport.net/css/sitev1.css | US | text | 4.75 Kb | malicious |
2432 | chrome.exe | GET | 200 | 192.124.249.4:80 | http://bilasport.net/css/espsv.css | US | text | 963 b | malicious |
2432 | chrome.exe | GET | 200 | 192.124.249.4:80 | http://bilasport.net/js/mmt.js | US | text | 27.0 Kb | malicious |
2432 | chrome.exe | GET | 200 | 192.124.249.4:80 | http://bilasport.net/js/sitev3.js | US | text | 672 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2180 | iexplore.exe | 192.124.249.4:443 | bilasport.net | Sucuri | US | malicious |
2432 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2432 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2432 | chrome.exe | 216.58.210.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2432 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2432 | chrome.exe | 216.58.212.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2432 | chrome.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2432 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2432 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2432 | chrome.exe | 216.58.210.14:443 | ogs.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bilasport.net |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |