| File name: | IDM_6.4x_Crack_v19.9.exe |
| Full analysis: | https://app.any.run/tasks/169eba62-5818-4e6b-8865-aa973d8d064e |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2025, 16:14:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | DB0F9DFFAF952032A48466A6CBC6240D |
| SHA1: | 4DBAFBEA04DFE037E9CFB162B909F18EB6F18206 |
| SHA256: | 96919764CE323D8B38D0DB440BB3B2219270BCB0975E7081943BFC58DAF6E793 |
| SSDEEP: | 1536:Se+j44XbBIwrYQeXww4lgH8N3CWWgFVa02MEA9:Se+04XDMxpMgHS3Wua02hA9 |
MALICIOUS
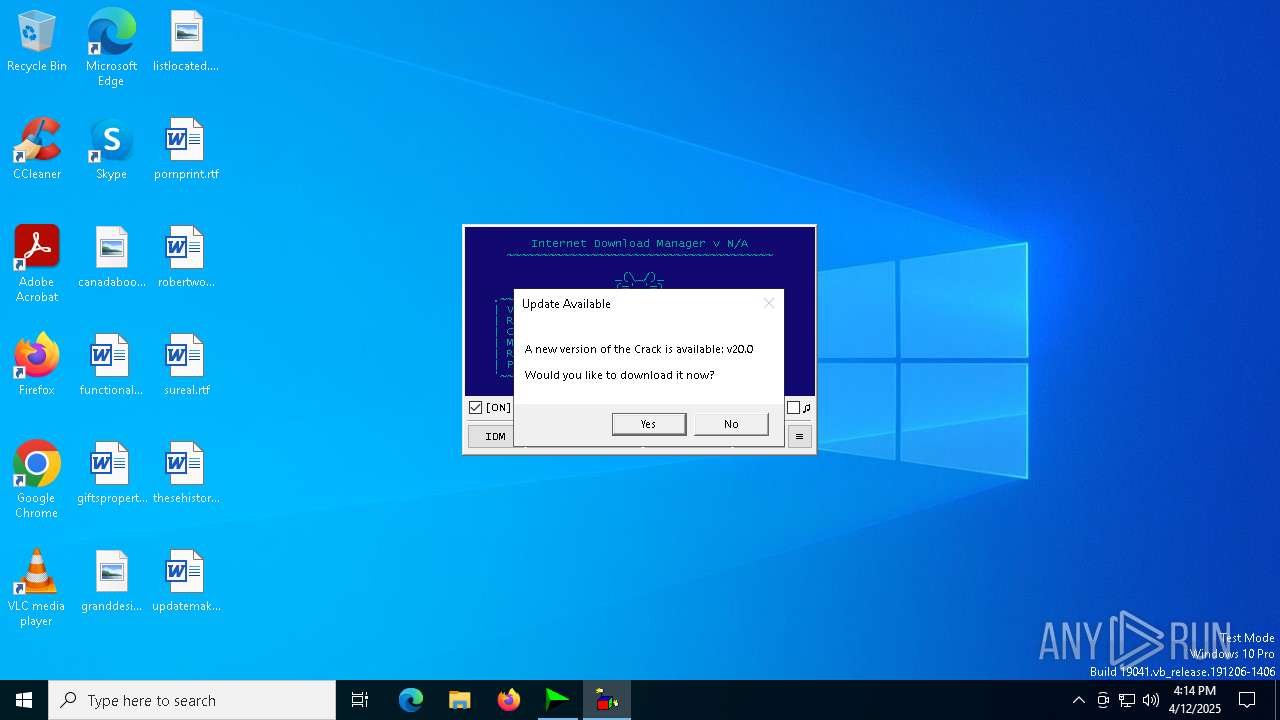
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3096)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3096)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 3096)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3096)
Deletes a file (SCRIPT)
- wscript.exe (PID: 3096)
SUSPICIOUS
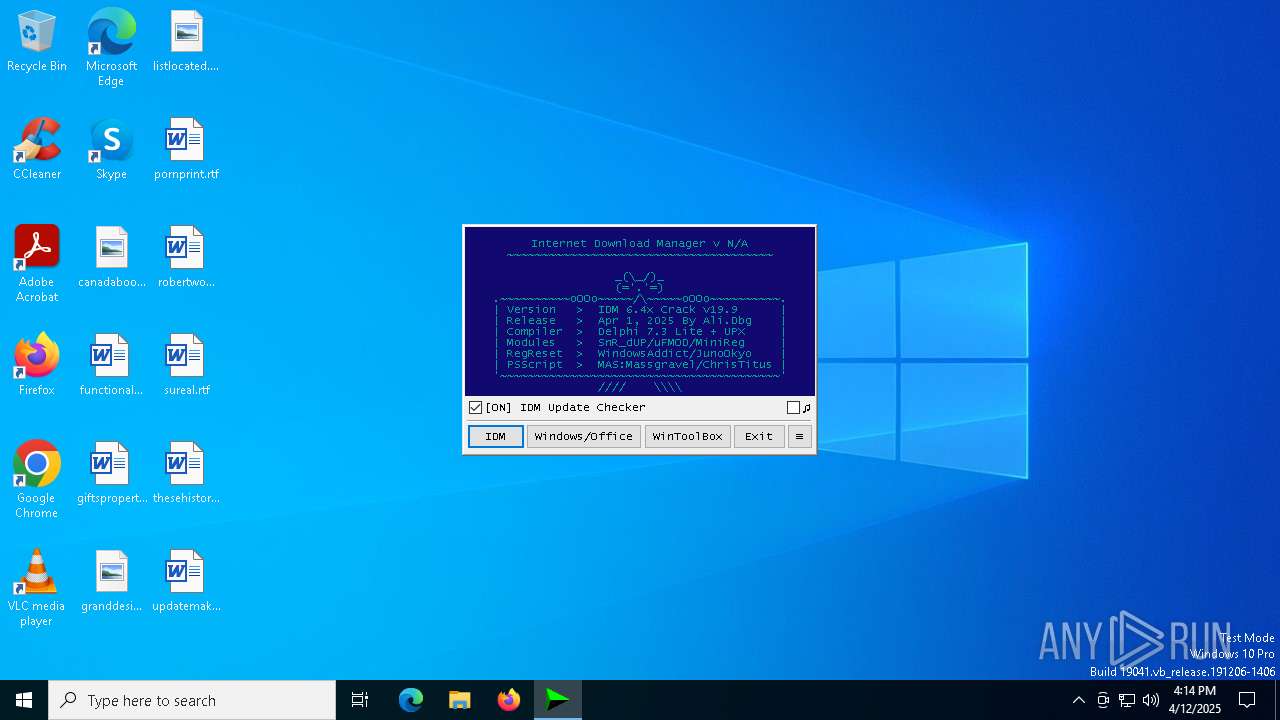
The process executes VB scripts
- IDM_6.4x_Crack_v19.9.exe (PID: 496)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3096)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v19.9.exe (PID: 496)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 1056)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v19.9.exe (PID: 496)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 1164)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 3096)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v19.9.exe (PID: 496)
- cmd.exe (PID: 1164)
Application launched itself
- cmd.exe (PID: 1164)
- cmd.exe (PID: 1056)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1164)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1164)
- cmd.exe (PID: 6808)
- cmd.exe (PID: 7852)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 1164)
Hides command output
- cmd.exe (PID: 5984)
- cmd.exe (PID: 7852)
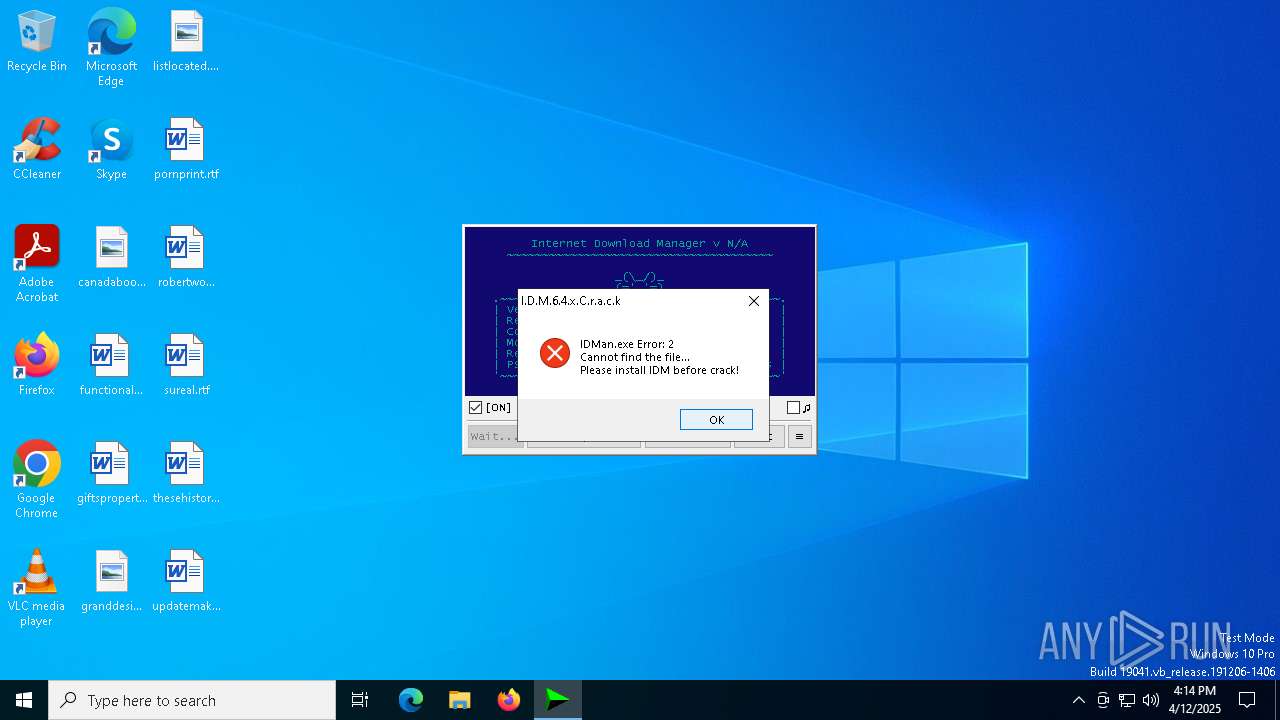
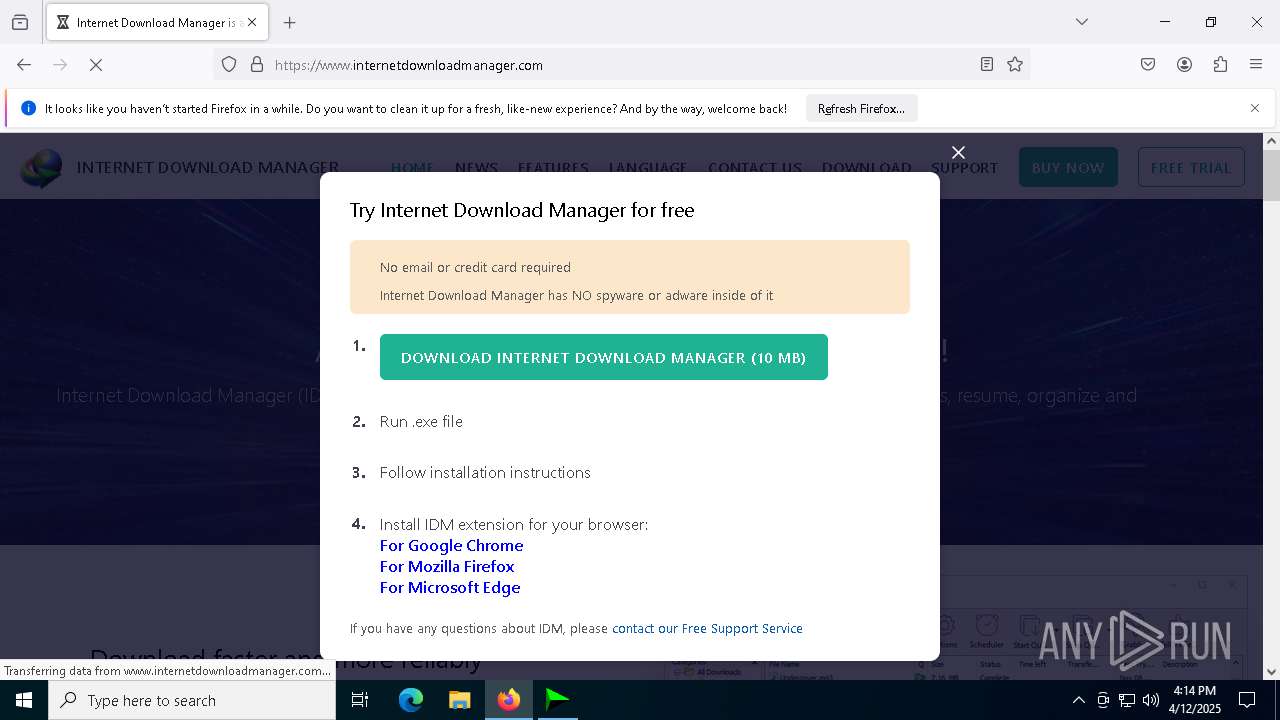
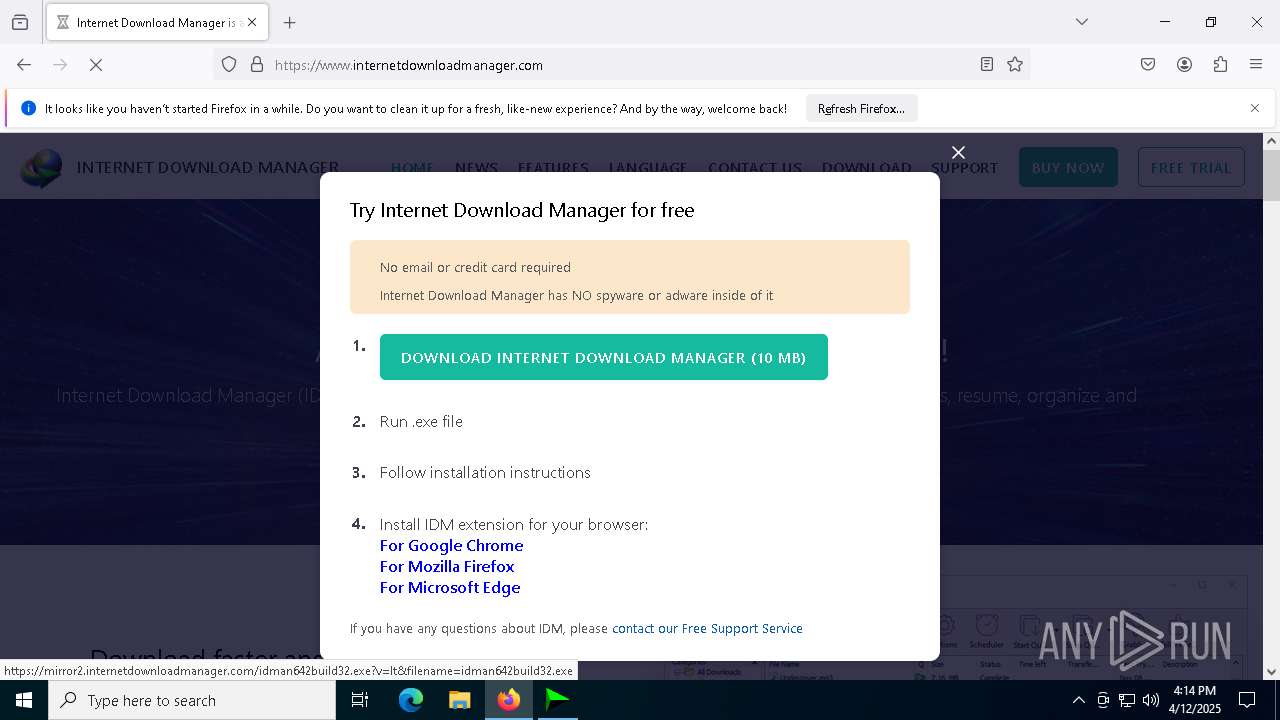
Starts application with an unusual extension
- idman642build32.exe (PID: 2192)
- cmd.exe (PID: 1164)
INFO
Reads the computer name
- IDM_6.4x_Crack_v19.9.exe (PID: 496)
- idman642build32.exe (PID: 2192)
Checks supported languages
- IDM_6.4x_Crack_v19.9.exe (PID: 496)
- chcp.com (PID: 7424)
- idman642build32.exe (PID: 2192)
Create files in a temporary directory
- IDM_6.4x_Crack_v19.9.exe (PID: 496)
- idman642build32.exe (PID: 2192)
- reg.exe (PID: 7440)
Checks operating system version
- cmd.exe (PID: 1164)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 7780)
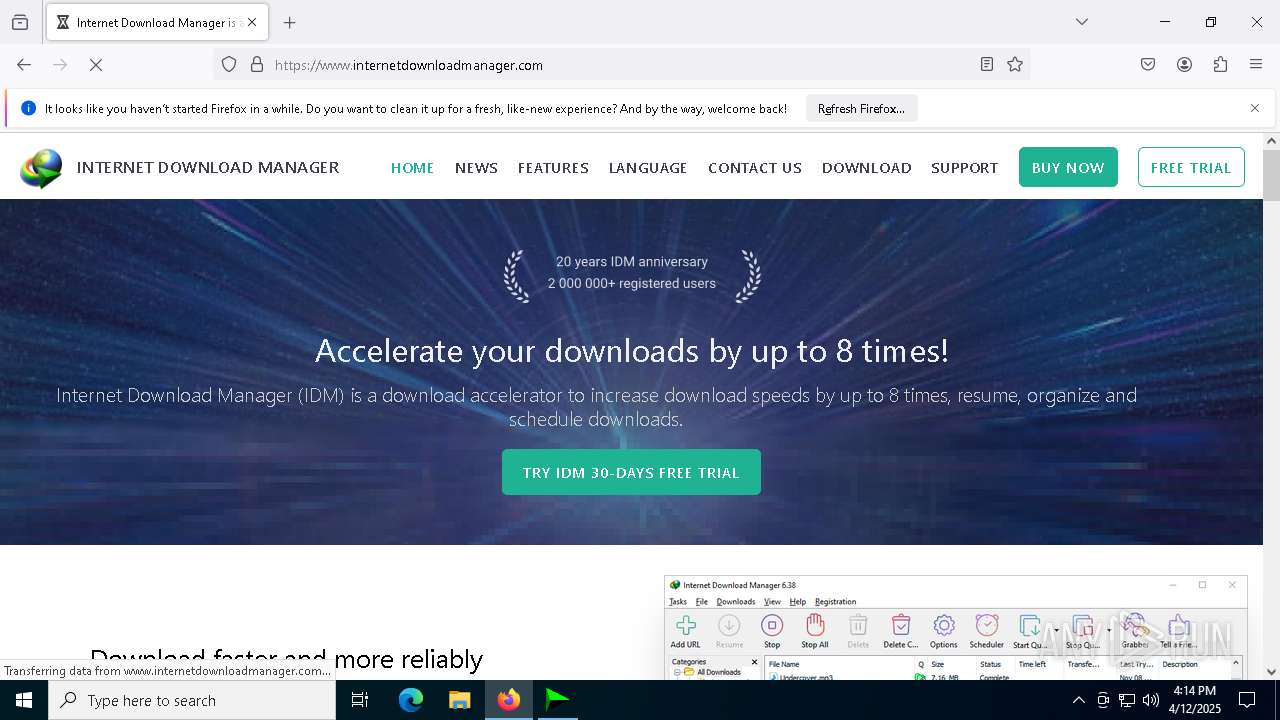
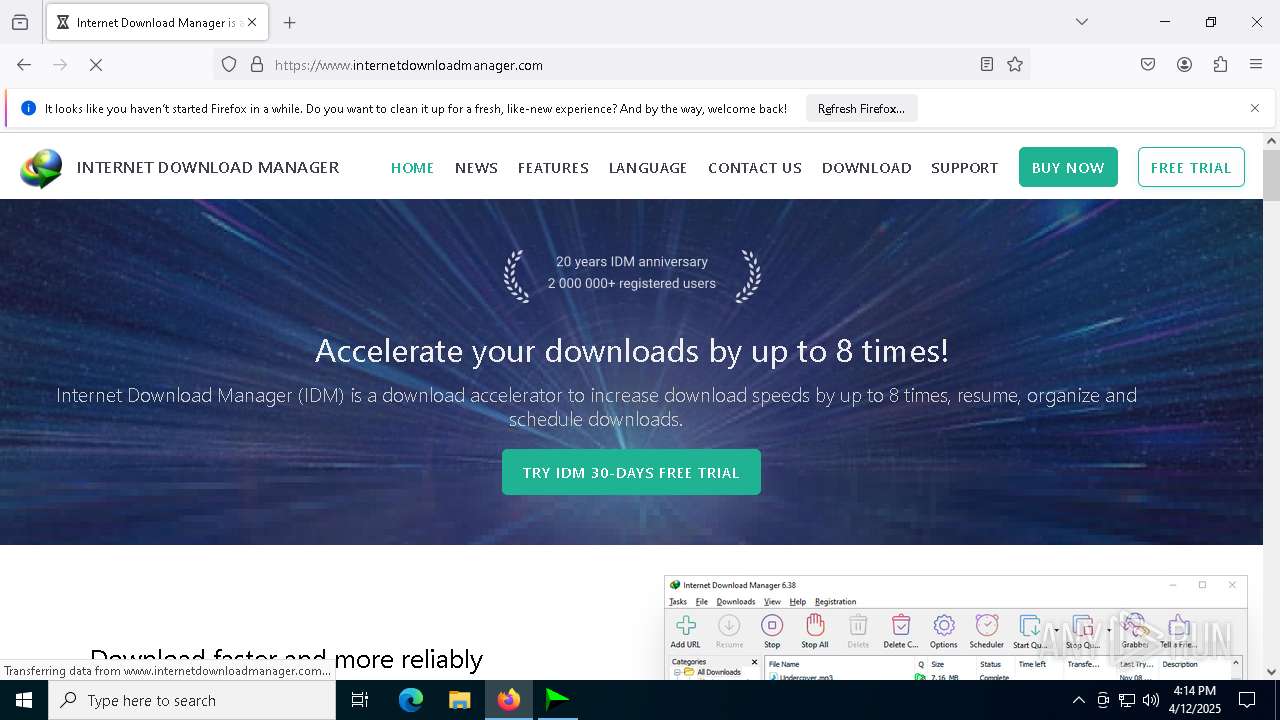
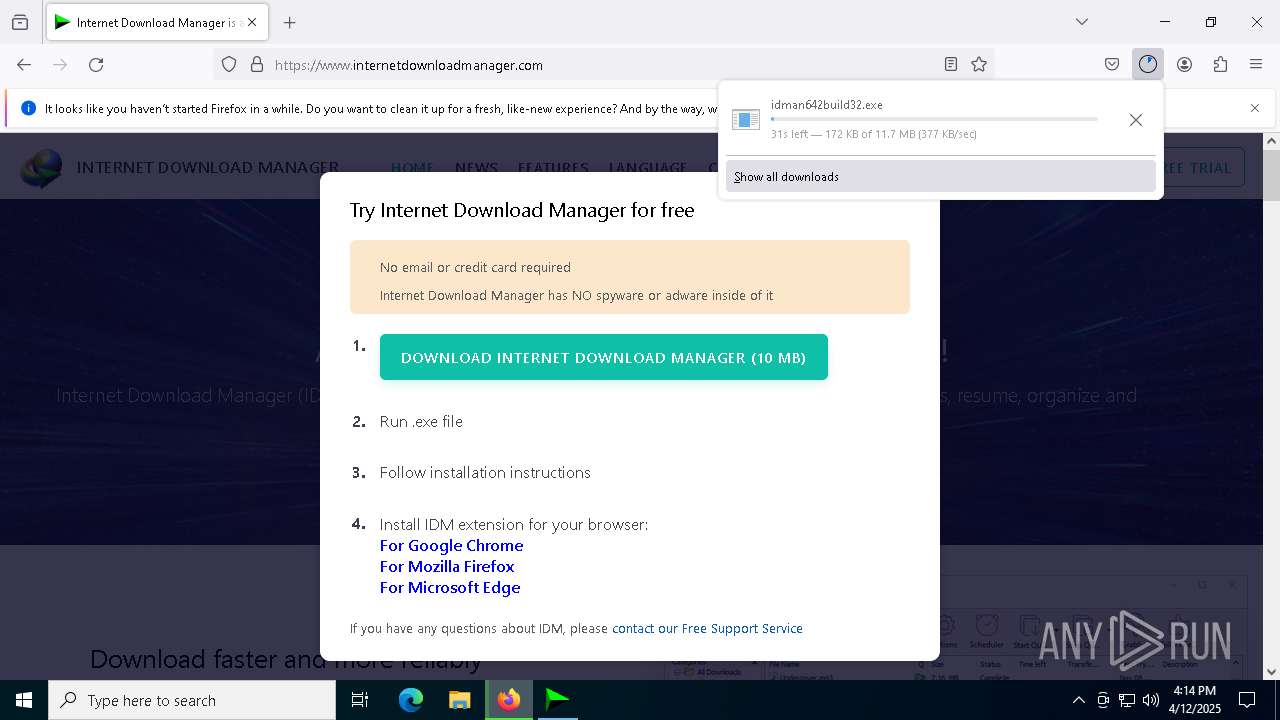
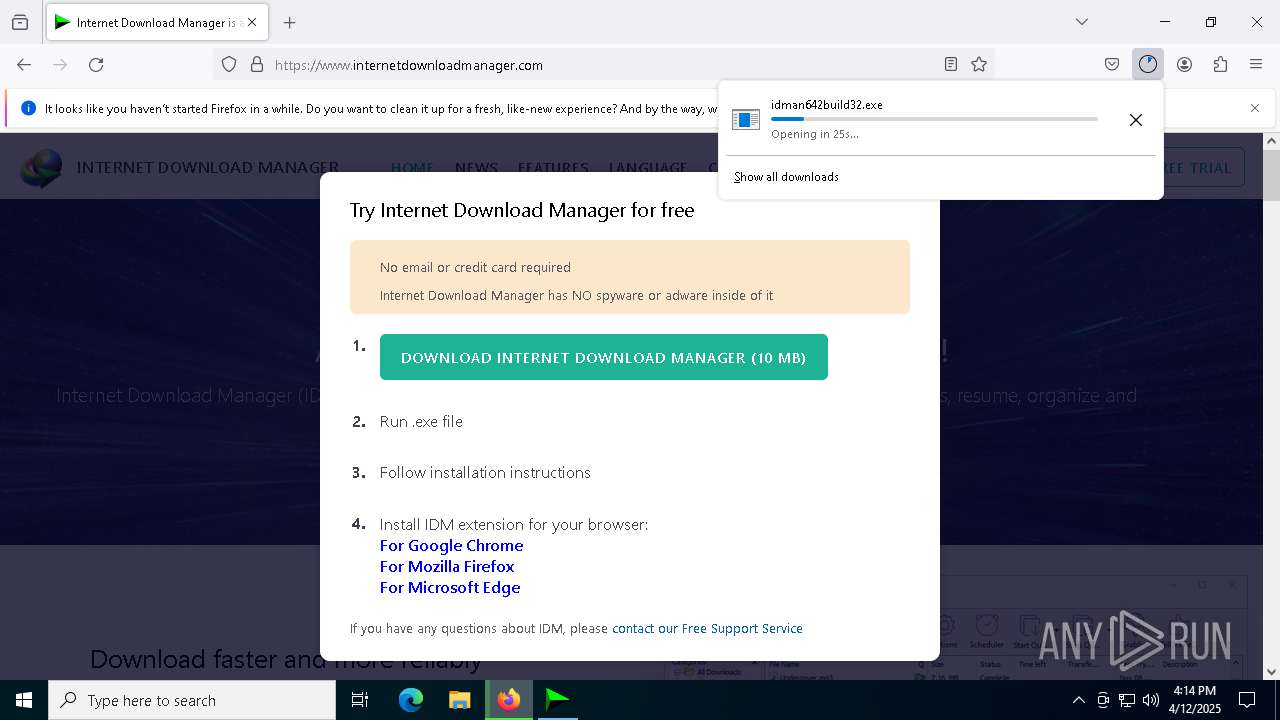
Manual execution by a user
- firefox.exe (PID: 632)
Application launched itself
- firefox.exe (PID: 632)
- firefox.exe (PID: 2772)
Executable content was dropped or overwritten
- firefox.exe (PID: 2772)
Autorun file from Downloads
- firefox.exe (PID: 2772)
The sample compiled with english language support
- firefox.exe (PID: 2772)
Changes the display of characters in the console
- cmd.exe (PID: 1164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 57344 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 188416 |
| EntryPoint: | 0x3cbf0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
202
Monitored processes
73
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v19.9.exe" | C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v19.9.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 632 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 728 | REG ADD "HKLM\Software\WOW6432Node\Internet Download Manager" /v "AdvIntDriverEnabled2" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | reg query "HKCU\Console" /v ForceV2 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | reg.exe import C:\Users\admin\AppData\Local\Temp\IDMRegClean.reg | C:\Windows\SysWOW64\reg.exe | — | IDM_6.4x_Crack_v19.9.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | REG ADD "HKCU\Software\DownloadManager" /v "LName" /t REG_SZ /d " " /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1920 -parentBuildID 20240213221259 -prefsHandle 1836 -prefMapHandle 1824 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {38307a71-9098-4835-abde-91194a075887} 2772 "\\.\pipe\gecko-crash-server-pipe.2772" 280781ef710 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1056 | C:\WINDOWS\system32\cmd.exe /c echo prompt $E | cmd | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | cmd.exe /c call "C:\Users\admin\AppData\Local\Temp\BATCLEN.bat" | C:\Windows\SysWOW64\cmd.exe | — | IDM_6.4x_Crack_v19.9.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | reg delete HKCU\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
38 971
Read events
38 930
Write events
26
Delete events
15
Modification events
| (PID) Process: | (496) IDM_6.4x_Crack_v19.9.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (496) IDM_6.4x_Crack_v19.9.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wow6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (496) IDM_6.4x_Crack_v19.9.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (496) IDM_6.4x_Crack_v19.9.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (496) IDM_6.4x_Crack_v19.9.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableCMD |
Value: 0 | |||
| (PID) Process: | (496) IDM_6.4x_Crack_v19.9.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 0 | |||
| (PID) Process: | (496) IDM_6.4x_Crack_v19.9.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 0 | |||
| (PID) Process: | (496) IDM_6.4x_Crack_v19.9.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | DisallowRun |
Value: 0 | |||
| (PID) Process: | (496) IDM_6.4x_Crack_v19.9.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\PowerShell |
| Operation: | write | Name: | EnableScripts |
Value: 1 | |||
| (PID) Process: | (496) IDM_6.4x_Crack_v19.9.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\PowerShell\1\ShellIds\ScriptedDiagnostics |
| Operation: | write | Name: | ExecutionPolicy |
Value: Bypass | |||
Executable files
2
Suspicious files
155
Text files
34
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2772 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 496 | IDM_6.4x_Crack_v19.9.exe | C:\Users\admin\AppData\Local\Temp\UPDT2.vbs | text | |
MD5:3450240915BFBD243415F24E20CF2381 | SHA256:AE07A018DB9F178882CD9389A2ACAF98F96E6775E2B455587D7C4B6FFB76A363 | |||
| 496 | IDM_6.4x_Crack_v19.9.exe | C:\Users\admin\AppData\Local\Temp\IDMRegClean.reg | text | |
MD5:73C023B1480CC88BE4D7761EF11A7703 | SHA256:9C7F6CE7CE6FA4093A20CFA3C1A6D2CDD7D5307AFF7405830C898A21F154ED68 | |||
| 5548 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3lox2hmx.a05.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 496 | IDM_6.4x_Crack_v19.9.exe | C:\Users\admin\AppData\Local\Temp\BATCLEN.bat | text | |
MD5:9FE22C4AD624881F8F0977CC7614346F | SHA256:12B47C1949CC555C2F68F9FD4677ED5266F25C4DA4630BEC36E303629B133225 | |||
| 5548 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5fhesood.rzk.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2772 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 2772 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2772 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2772 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:F1CEBF5260EEB4C851AF827E3970EC44 | SHA256:DFC7CA4E63EBBFB63C41BAB5D28ACEEA91DB6681B19FA4B409D6209073F0D150 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
122
DNS requests
152
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2772 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
2772 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
2772 | firefox.exe | POST | 200 | 172.217.18.99:80 | http://o.pki.goog/we2 | US | binary | 280 b | whitelisted |
2772 | firefox.exe | POST | 200 | 172.217.18.99:80 | http://o.pki.goog/we2 | US | binary | 280 b | whitelisted |
2772 | firefox.exe | POST | 200 | 172.217.18.99:80 | http://o.pki.goog/we2 | US | binary | 279 b | whitelisted |
2772 | firefox.exe | POST | 200 | 172.217.18.99:80 | http://o.pki.goog/we2 | US | binary | 279 b | whitelisted |
2772 | firefox.exe | POST | 200 | 172.217.18.99:80 | http://o.pki.goog/s/wr3/cgo | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3096 | wscript.exe | 188.114.97.3:443 | idm.0dy.ir | CLOUDFLARENET | NL | unknown |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
idm.0dy.ir |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |