| File name: | MDAC_TYP.EXE |
| Full analysis: | https://app.any.run/tasks/44b15be5-ecae-4f0d-8a03-0cc279bcdcfe |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2025, 20:20:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, MS CAB-Installer self-extracting archive, 3 sections |
| MD5: | DB045F71B17E39DCF3855AE37EF97353 |
| SHA1: | 8BE723A88DA18BDED00538A2AC85285DB8B4A4C1 |
| SHA256: | 9688ED4B64DAAB5D99DDF782B41858B0F951A2AF3C54E159B6DDB56DF26C6628 |
| SSDEEP: | 98304:COiRpXAeys23t2D1OmlnEqyfh0kR7QB2I4zrgqAKZDL8IJ97SLi/0ggk17hixvTT:i8Bb/CmeDr7 |
MALICIOUS
Executing a file with an untrusted certificate
- MDAC_TYP.EXE.exe (PID: 5164)
SUSPICIOUS
Process drops legitimate windows executable
- RUXIMICS.exe (PID: 5164)
Starts a Microsoft application from unusual location
- MDAC_TYP.EXE.exe (PID: 5164)
INFO
Creates files in the program directory
- RUXIMICS.exe (PID: 7148)
Checks supported languages
- MDAC_TYP.EXE.exe (PID: 5164)
- RUXIMICS.exe (PID: 7148)
Reads the computer name
- MDAC_TYP.EXE.exe (PID: 5164)
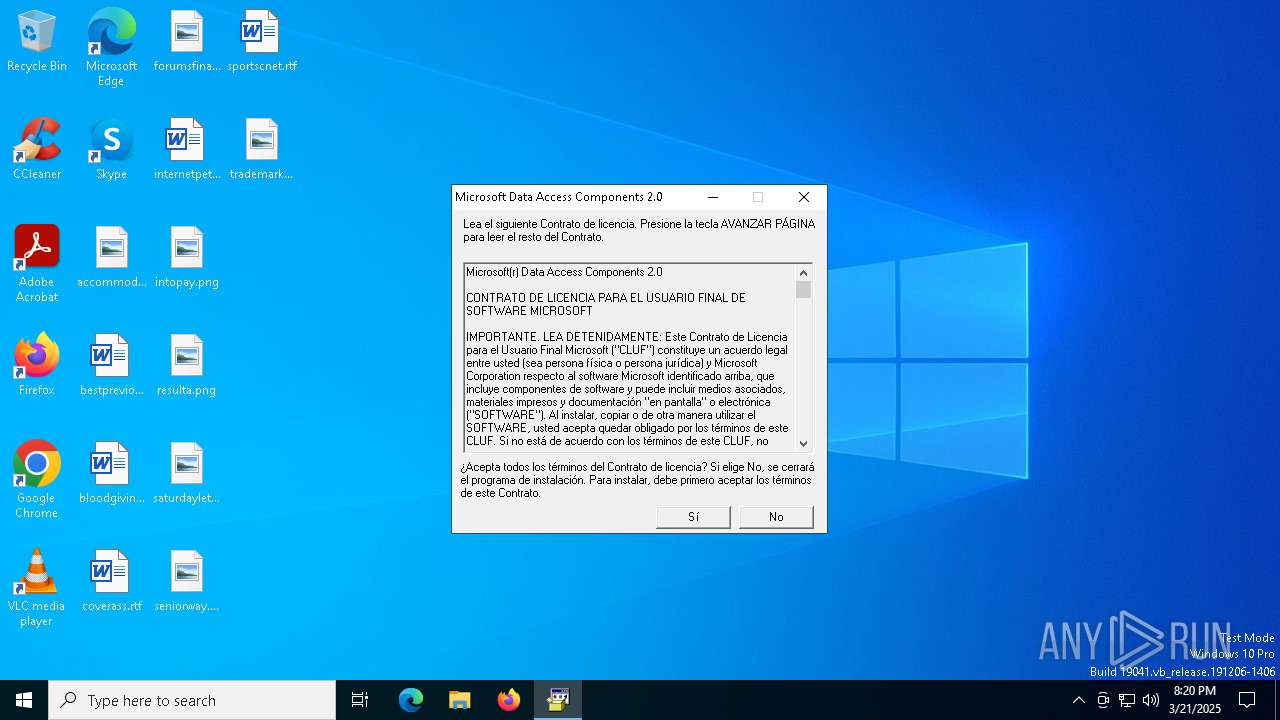
The sample compiled with spanish language support
- RUXIMICS.exe (PID: 5164)
Manual execution by a user
- RUXIMICS.exe (PID: 7148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (44.9) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (39.7) |
| .exe | | | Win32 Executable (generic) (6.4) |
| .exe | | | Win16/32 Executable Delphi generic (2.9) |
| .exe | | | Generic Win/DOS Executable (2.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1998:03:11 01:39:29+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 36864 |
| InitializedDataSize: | 6429184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2749 |
| OSVersion: | 5 |
| ImageVersion: | 5 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.72.3110.0 |
| ProductVersionNumber: | 4.72.3110.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Spanish (Modern) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 4.72.3110.0 |
| InternalName: | Wextract |
| LegalCopyright: | (C) Microsoft Corporation 1981-1997 |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Sistema operativo Microsoft(R) Windows NT(R) |
| ProductVersion: | 4.72.3110.0 |
Total processes
138
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5164 | %ProgramFiles%\RUXIM\RUXIMICS.EXE /onlyloadcampaigns | C:\Program Files\RUXIM\RUXIMICS.exe | PLUGScheduler.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Reusable UX Interaction Manager Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5164 | "C:\Users\admin\AppData\Local\Temp\MDAC_TYP.EXE.exe" | C:\Users\admin\AppData\Local\Temp\MDAC_TYP.EXE.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Version: 4.72.3110.0 Modules
| |||||||||||||||
| 7148 | %ProgramFiles%\RUXIM\RUXIMICS.EXE /nonetwork | C:\Program Files\RUXIM\RUXIMICS.exe | — | PLUGScheduler.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Reusable UX Interaction Manager Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7272 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7308 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
170
Read events
168
Write events
2
Delete events
0
Modification events
| (PID) Process: | (5164) RUXIMICS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate\PLUG\OneSettingsSync |
| Operation: | write | Name: | x-ms-onesetinterval |
Value: 1440 | |||
| (PID) Process: | (5164) RUXIMICS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdate\PLUG\OneSettingsSync |
| Operation: | write | Name: | RefreshAfter |
Value: A8066AD2679BDB01 | |||
Executable files
0
Suspicious files
43
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7148 | RUXIMICS.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.048.etl | binary | |
MD5:5EA68411BF8E9EAF4621BAF73F61449E | SHA256:9D4CA5A1D871F819C139A498BB910A63576C2FE6367853544F8D172D8B6EBFF7 | |||
| 7148 | RUXIMICS.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.045.etl | binary | |
MD5:A7A21FBC9D00F33F186B34A50E170C13 | SHA256:64CAC91E46D4FC832958232A658431CBF9D8D9F265653ACA2BEB32428D4688EC | |||
| 7148 | RUXIMICS.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.035.etl | binary | |
MD5:A477FE56C25FCDB850EA1AAB8D01B5C2 | SHA256:5C85DC2B41C2D076D6B2653C0BA5F5681ADABFEBDA8883C704E625EB9338F505 | |||
| 7148 | RUXIMICS.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.037.etl | binary | |
MD5:F9485F2BA891697F8B6CF8FB1E7F42C0 | SHA256:69146D4AAEFB8609745B6CA780B48ABC66054AA3CDB8061248CF7B32F3B32617 | |||
| 7148 | RUXIMICS.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.040.etl | binary | |
MD5:09359EE89B0634478ADFF73CDA7BFB12 | SHA256:4D800AC7C55960B107C9D3E40F63130407835E69DF4F5C558C500FC0BD20D8ED | |||
| 7148 | RUXIMICS.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.036.etl | binary | |
MD5:B787593A02A4E0A601164A65952D0CB9 | SHA256:3594AD496D8E1771BCC3E8B6F68B4C2B4190A9A331FB43F068A7DF4E1894E2CF | |||
| 7148 | RUXIMICS.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.033.etl | binary | |
MD5:DCB94F822B793FF178C7332174A89DFB | SHA256:4AB418FA76DFA333D37F7401B40B0B0F0E806876C79AB2F36CD3FD7CCAD8665B | |||
| 7148 | RUXIMICS.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.034.etl | binary | |
MD5:2FC3641AD4F7A4A3C83C9F3014B0F0A5 | SHA256:92C3D62BC45E1DDFC77DA511ACE5E47D021D69BA625D2766AF91E376102F11AC | |||
| 7148 | RUXIMICS.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.028.etl | binary | |
MD5:F9D8BBFBB3073C1ACA1D6D611F3937CC | SHA256:BC040E242B9963E9ACDEA9ED8DD6FEDC97EFBE93816250C1801A822539E8602B | |||
| 7148 | RUXIMICS.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.031.etl | binary | |
MD5:434842C62F806B8D2D51441B22C4F337 | SHA256:4570165C6BC2B881A423DABFC9F2361C8472DDD7178C352F3C7A68B6A1AB1D81 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4380 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8012 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8012 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.190:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5164 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 20.198.162.76:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4380 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4380 | backgroundTaskHost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
8012 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |