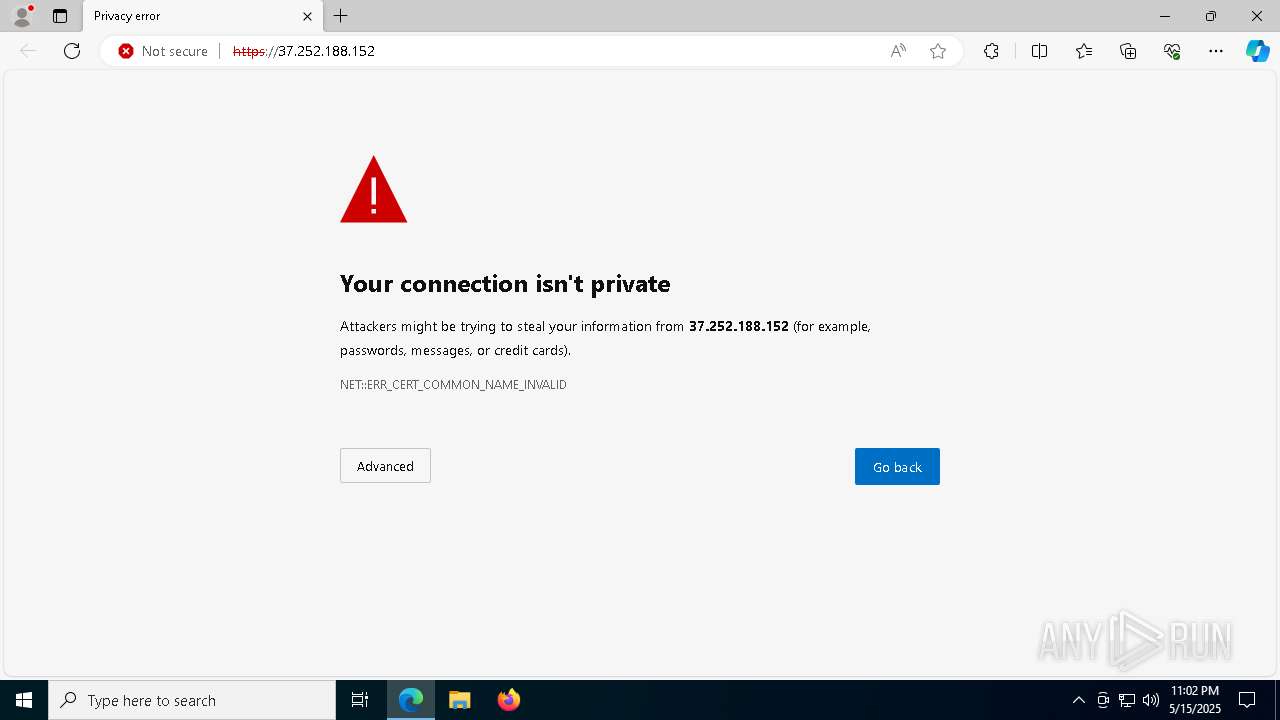
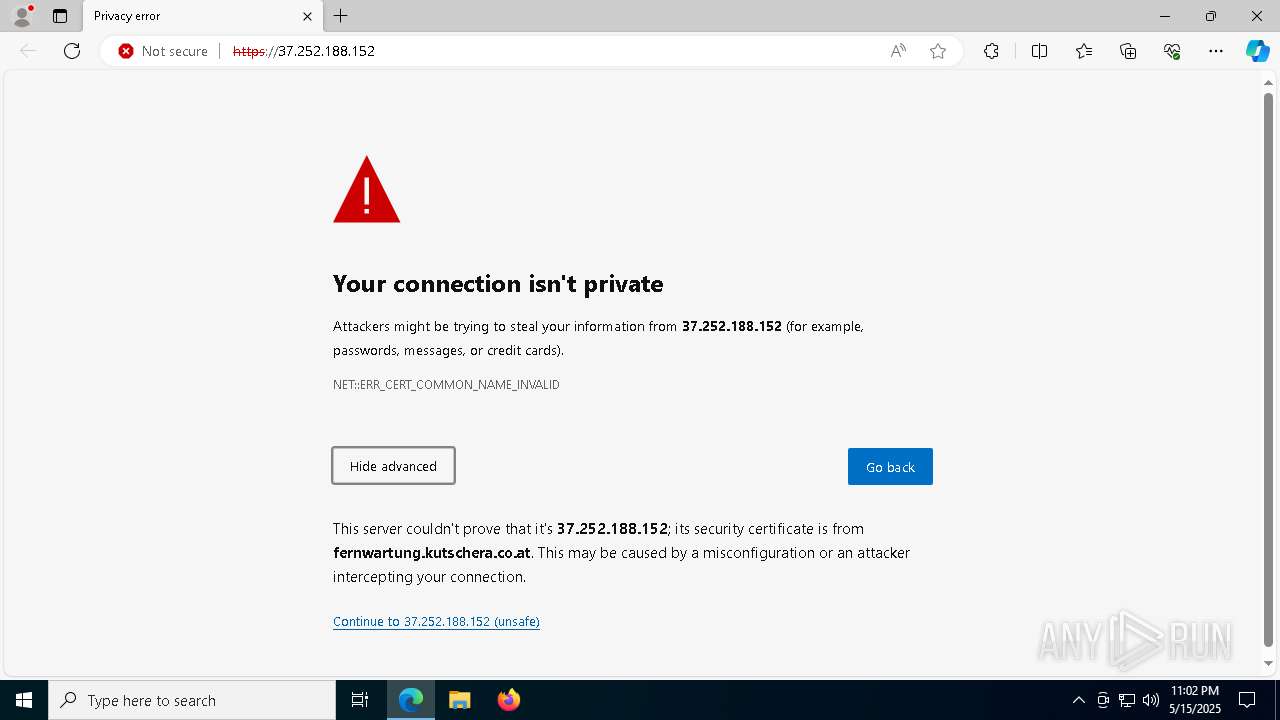
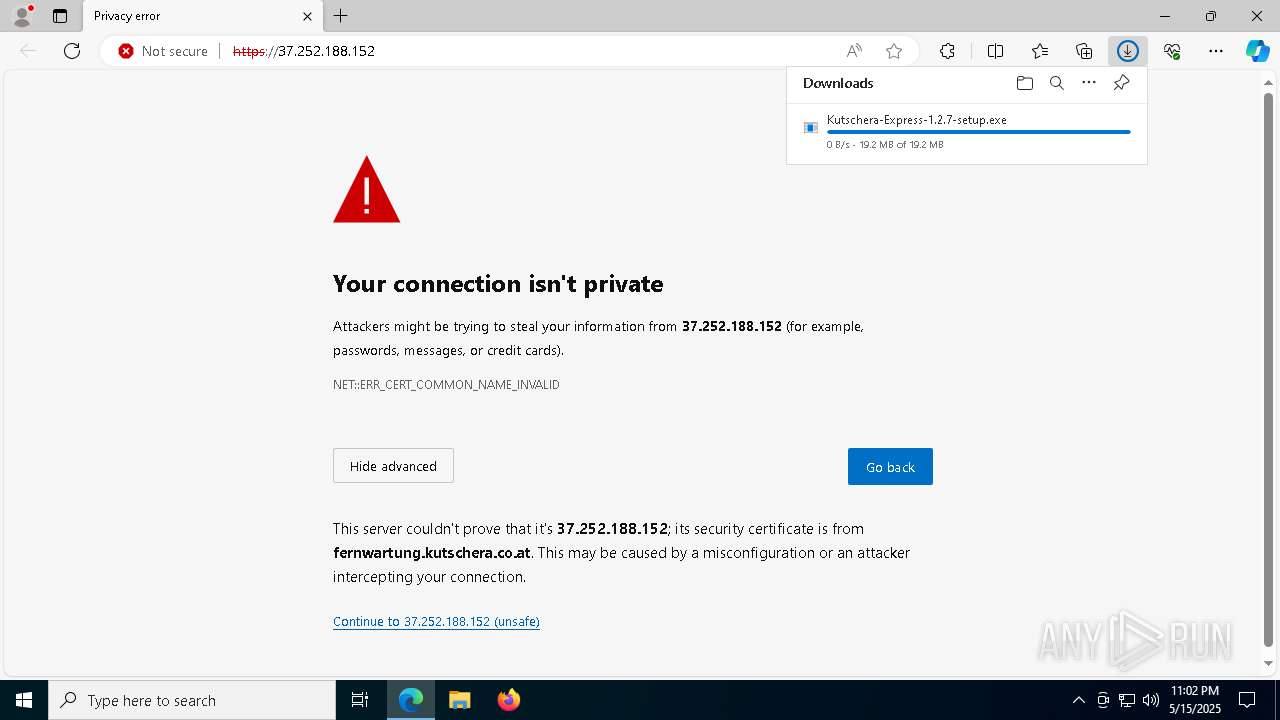
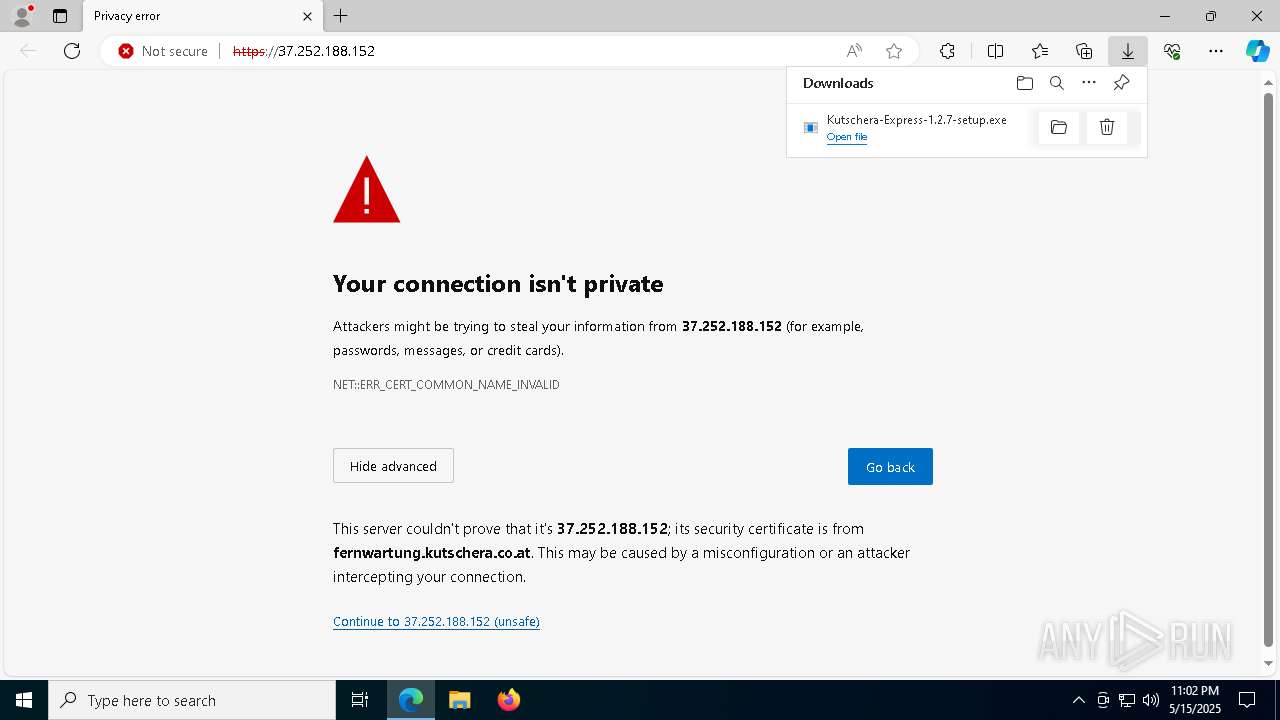
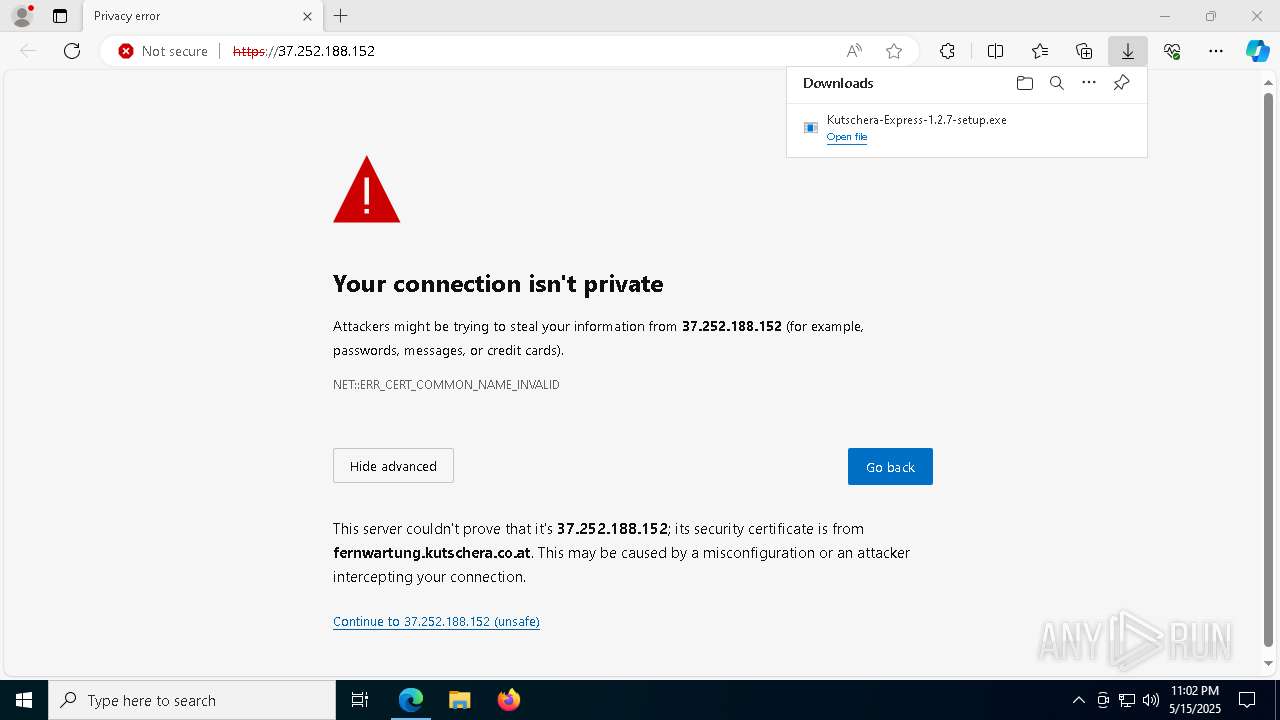
| URL: | https://37.252.188.152 |
| Full analysis: | https://app.any.run/tasks/ae428f6d-7f32-4e2f-bd7b-bbdf30ac9a77 |
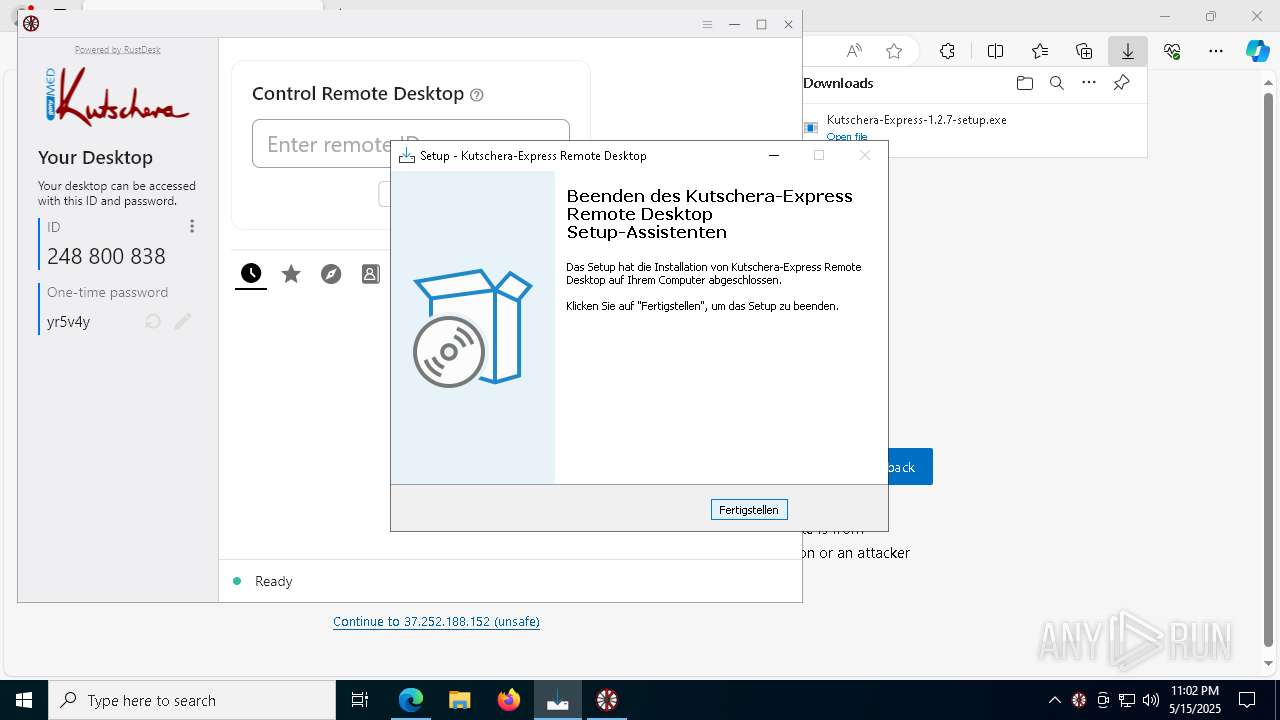
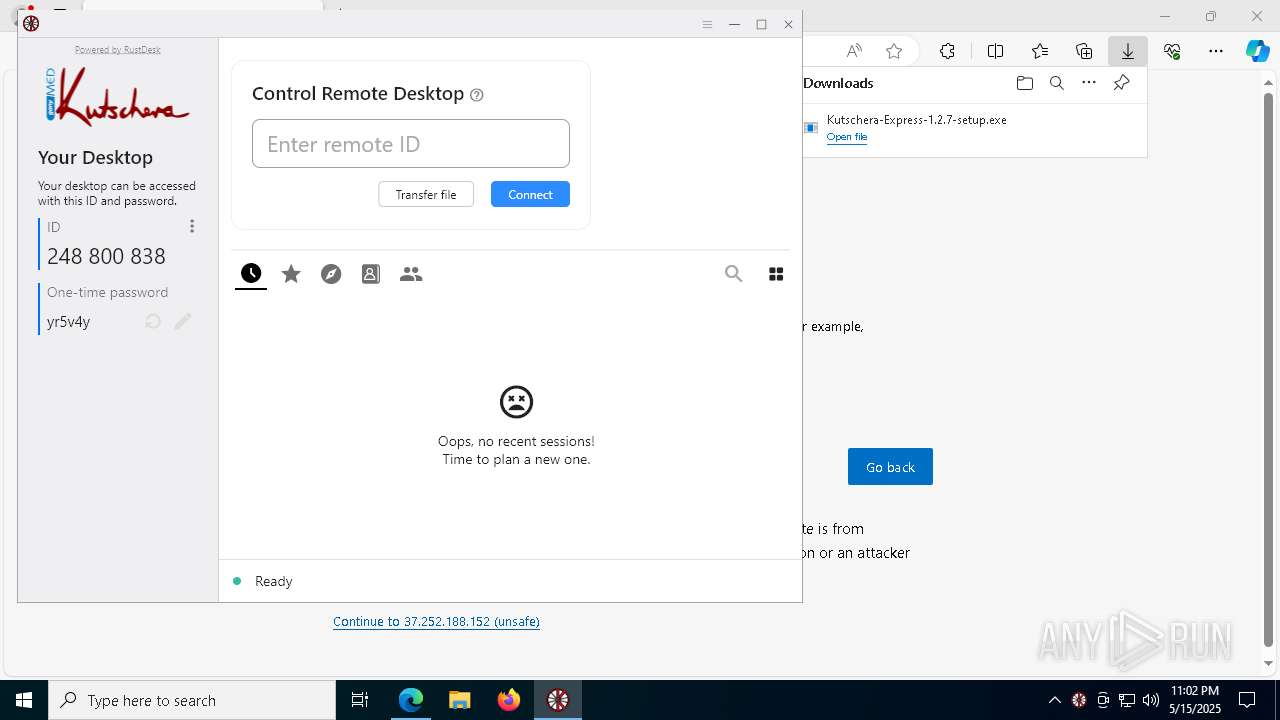
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 23:01:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FEF0BA9F7D4C1BC207D40B98A4E07BA6 |
| SHA1: | D7FF0E911CD477127663C01766D227C0CE3CBB7D |
| SHA256: | 96810582A681863AAB7C07DDA5064D2EC752BFFD4E80A17FDB1C02E987BA4C50 |
| SSDEEP: | 3:N8fL9JXn:2xJXn |
MALICIOUS
Create files in the Startup directory
- cmd.exe (PID: 5780)
SUSPICIOUS
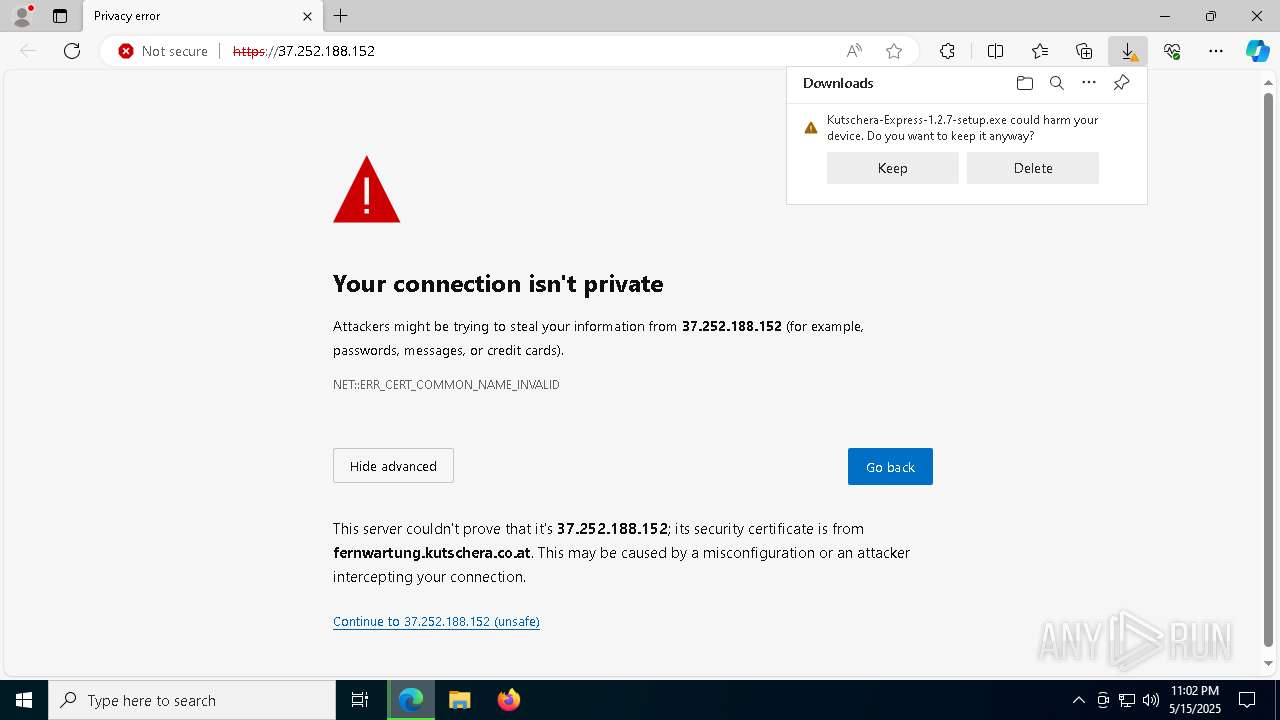
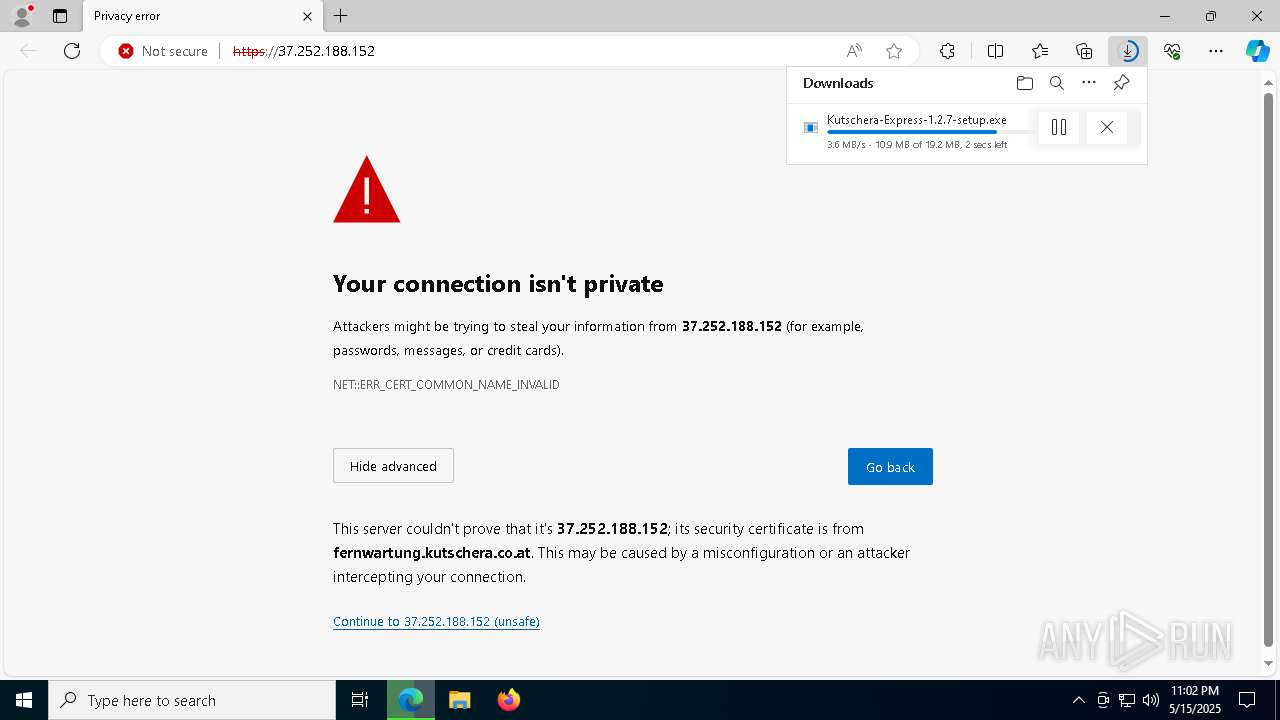
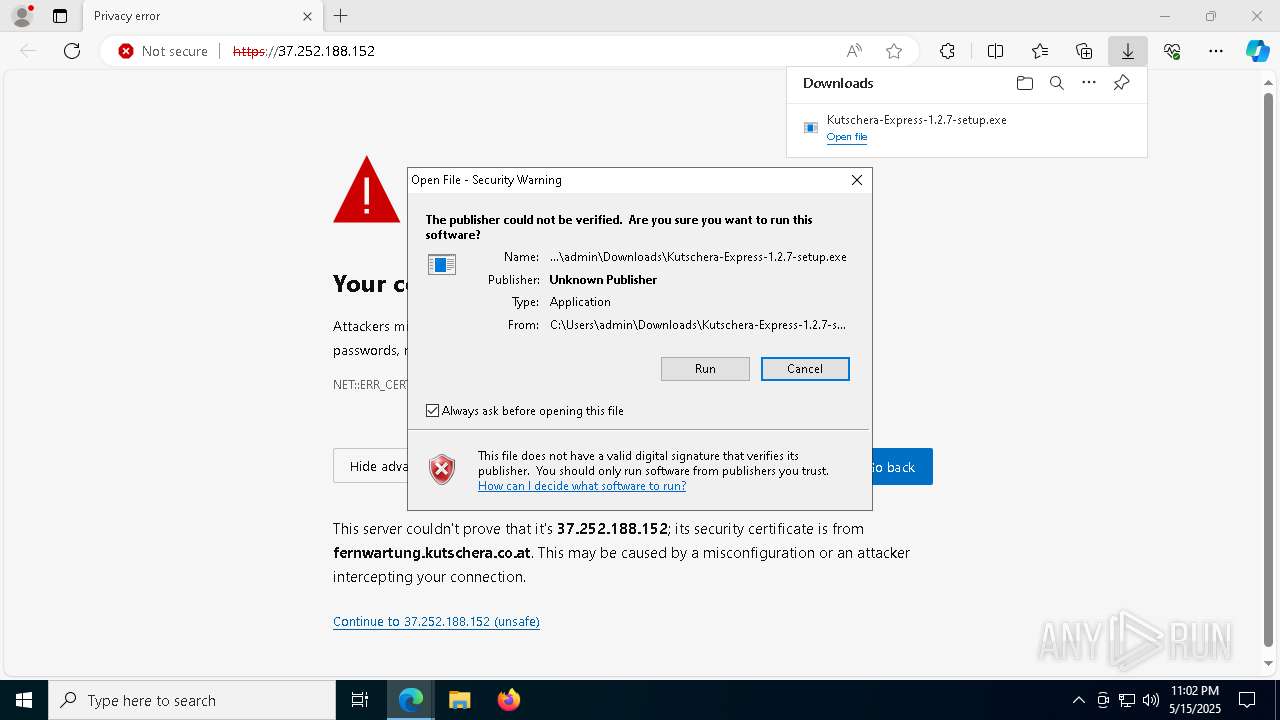
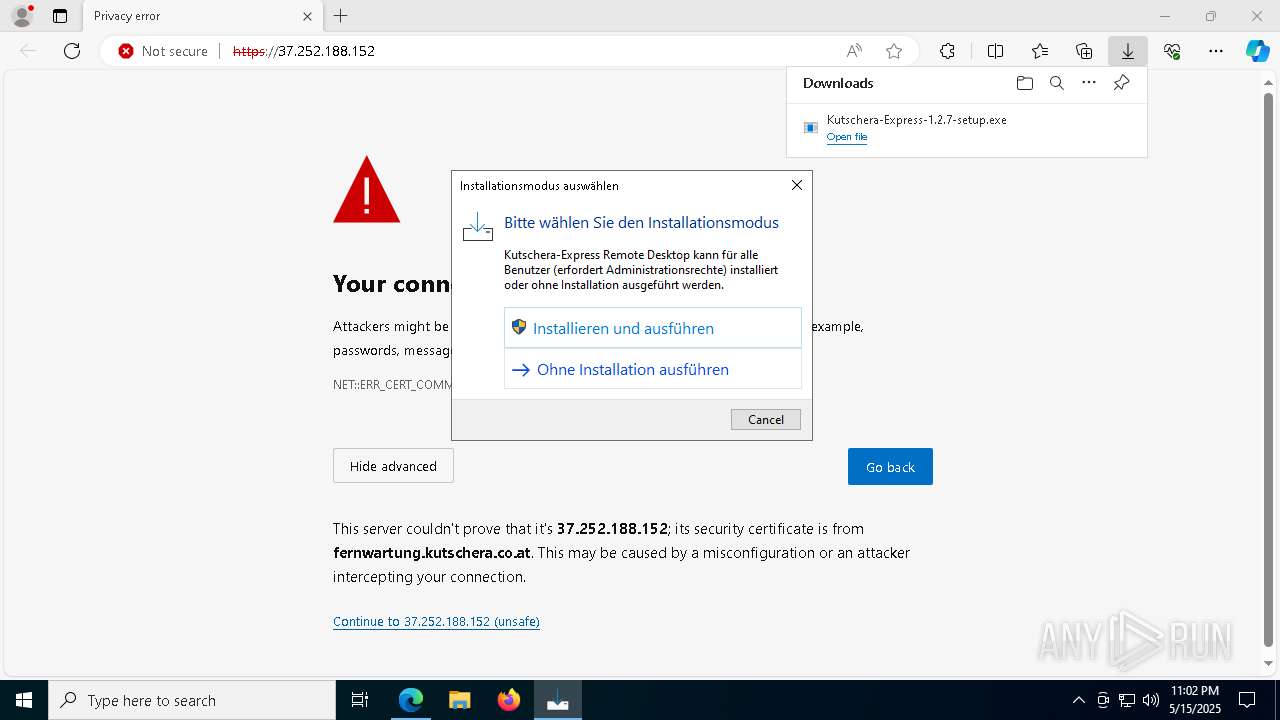
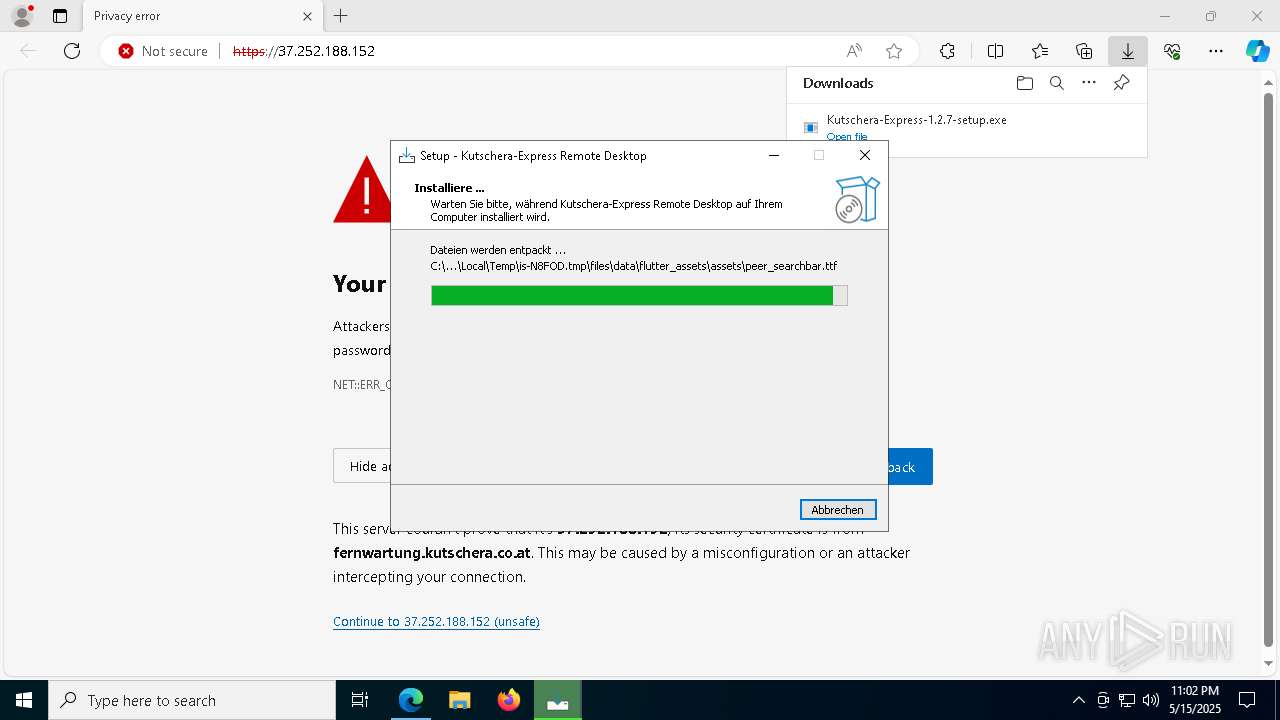
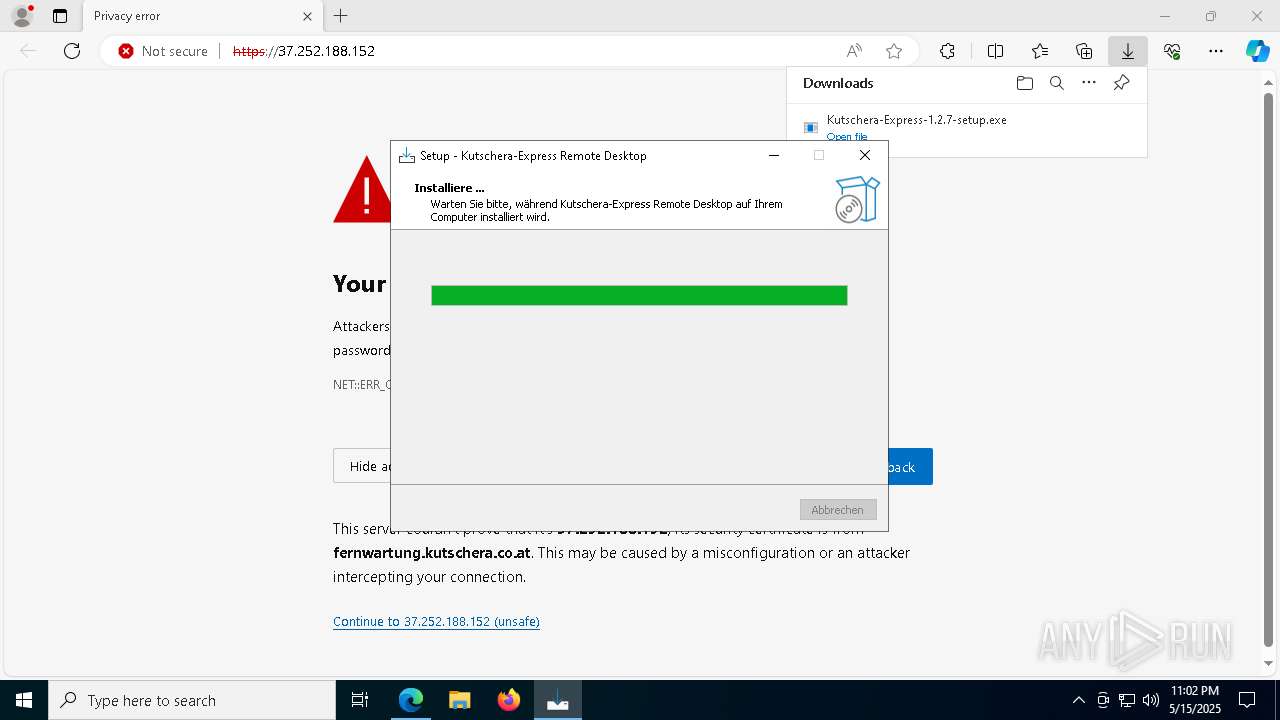
Executable content was dropped or overwritten
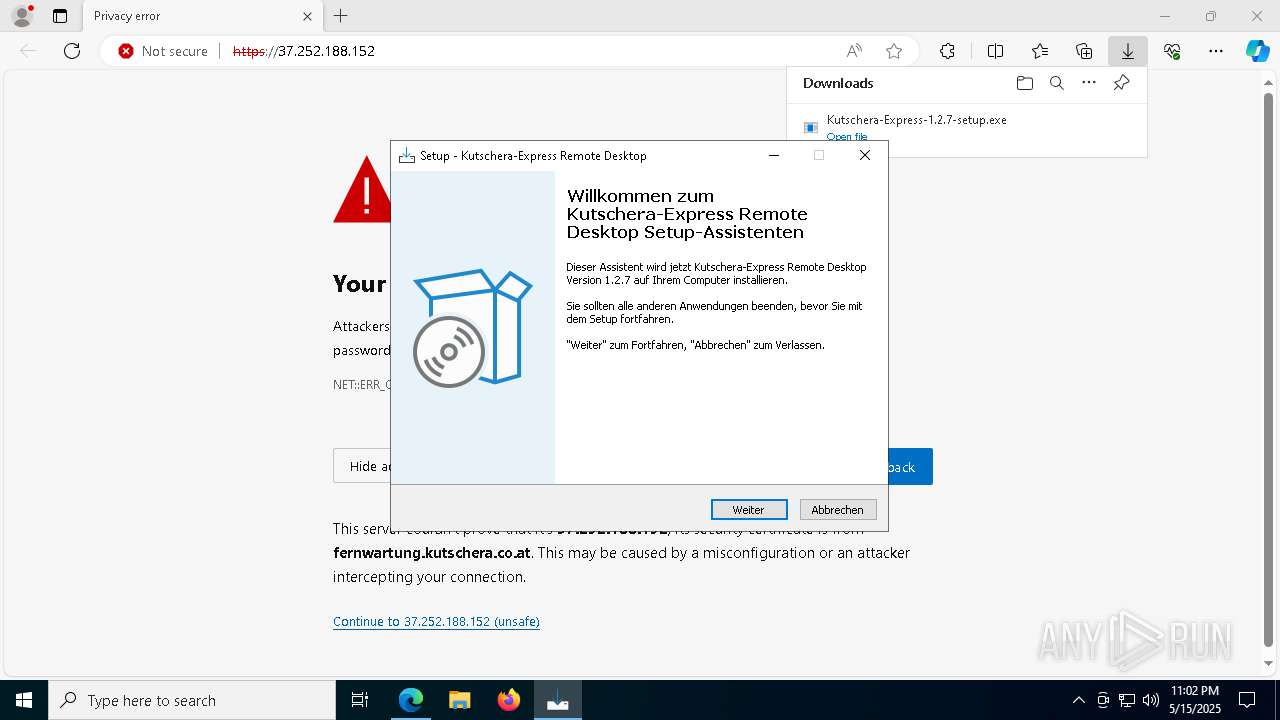
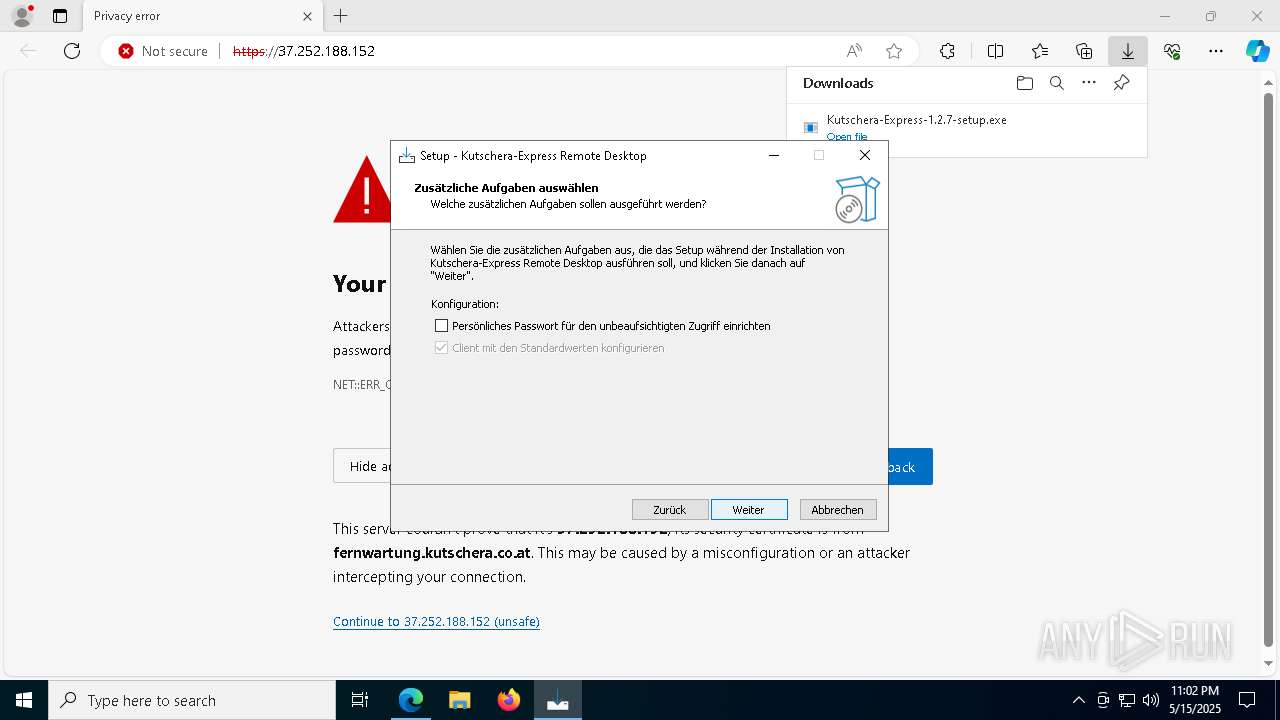
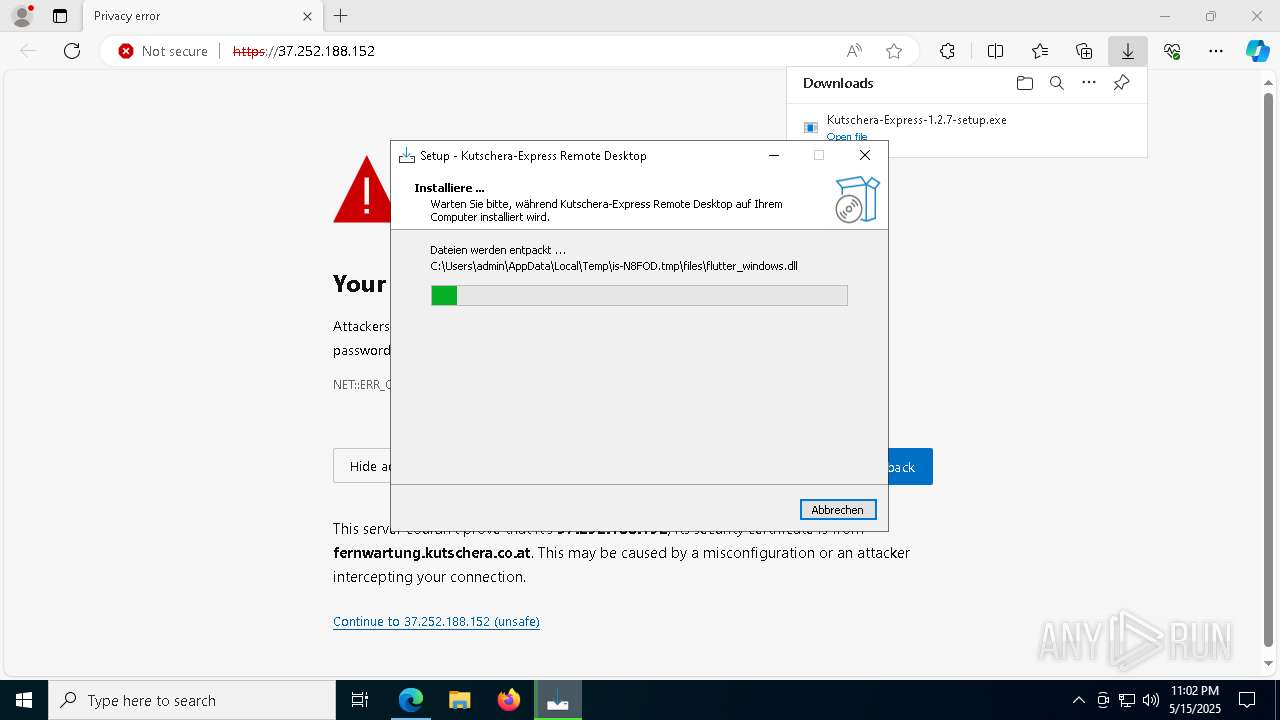
- Kutschera-Express-1.2.7-setup.exe (PID: 7400)
- Kutschera-Express-1.2.7-setup.exe (PID: 5552)
- Kutschera-Express-1.2.7-setup.tmp (PID: 3240)
- xcopy.exe (PID: 1132)
- cmd.exe (PID: 5780)
Reads security settings of Internet Explorer
- Kutschera-Express-1.2.7-setup.tmp (PID: 4996)
- Kutschera-Express.exe (PID: 5084)
- Kutschera-Express.exe (PID: 4736)
Reads the Windows owner or organization settings
- Kutschera-Express-1.2.7-setup.tmp (PID: 3240)
- Kutschera-Express.exe (PID: 8172)
Windows service management via SC.EXE
- sc.exe (PID: 1532)
- sc.exe (PID: 4200)
- sc.exe (PID: 7216)
- sc.exe (PID: 7184)
- sc.exe (PID: 7264)
- sc.exe (PID: 2552)
- sc.exe (PID: 8184)
- sc.exe (PID: 6268)
- sc.exe (PID: 3304)
- sc.exe (PID: 728)
- sc.exe (PID: 6228)
Stops a currently running service
- sc.exe (PID: 4008)
- sc.exe (PID: 5756)
- sc.exe (PID: 4756)
- sc.exe (PID: 8176)
- sc.exe (PID: 1096)
- sc.exe (PID: 5244)
- sc.exe (PID: 2656)
Starts CMD.EXE for commands execution
- Kutschera-Express.exe (PID: 5084)
- Kutschera-Express.exe (PID: 6048)
- Kutschera-Express.exe (PID: 4736)
- Kutschera-Express.exe (PID: 7396)
- Kutschera-Express-1.2.7-setup.tmp (PID: 3240)
Executing commands from a ".bat" file
- Kutschera-Express.exe (PID: 5084)
- Kutschera-Express.exe (PID: 4736)
Reads the date of Windows installation
- Kutschera-Express.exe (PID: 5084)
- Kutschera-Express.exe (PID: 4736)
- Kutschera-Express.exe (PID: 8172)
Starts application with an unusual extension
- cmd.exe (PID: 5780)
- cmd.exe (PID: 6572)
Starts SC.EXE for service management
- cmd.exe (PID: 5780)
- cmd.exe (PID: 6572)
The executable file from the user directory is run by the CMD process
- Kutschera-Express.exe (PID: 6476)
- Kutschera-Express.exe (PID: 5328)
- Kutschera-Express.exe (PID: 4696)
- Kutschera-Express.exe (PID: 7176)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5780)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 5780)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 5780)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 516)
Process drops legitimate windows executable
- cmd.exe (PID: 5780)
Searches for installed software
- reg.exe (PID: 1040)
- reg.exe (PID: 4464)
- reg.exe (PID: 2040)
- reg.exe (PID: 4188)
- reg.exe (PID: 5588)
- reg.exe (PID: 7928)
- reg.exe (PID: 2236)
- reg.exe (PID: 6228)
- reg.exe (PID: 1012)
- reg.exe (PID: 7528)
- reg.exe (PID: 4736)
- reg.exe (PID: 5576)
- reg.exe (PID: 7952)
- Kutschera-Express.exe (PID: 1056)
- Kutschera-Express.exe (PID: 6044)
- Kutschera-Express.exe (PID: 5084)
- Kutschera-Express.exe (PID: 6048)
- Kutschera-Express.exe (PID: 5756)
- Kutschera-Express.exe (PID: 8036)
- Kutschera-Express.exe (PID: 4736)
- Kutschera-Express.exe (PID: 7928)
- Kutschera-Express.exe (PID: 7396)
- Kutschera-Express.exe (PID: 5228)
- Kutschera-Express.exe (PID: 5352)
- Kutschera-Express.exe (PID: 5212)
- Kutschera-Express.exe (PID: 2552)
- Kutschera-Express.exe (PID: 5244)
- Kutschera-Express.exe (PID: 5592)
- Kutschera-Express.exe (PID: 4696)
- Kutschera-Express.exe (PID: 7176)
- Kutschera-Express.exe (PID: 208)
- Kutschera-Express-1.2.7-setup.tmp (PID: 3240)
- Kutschera-Express.exe (PID: 8172)
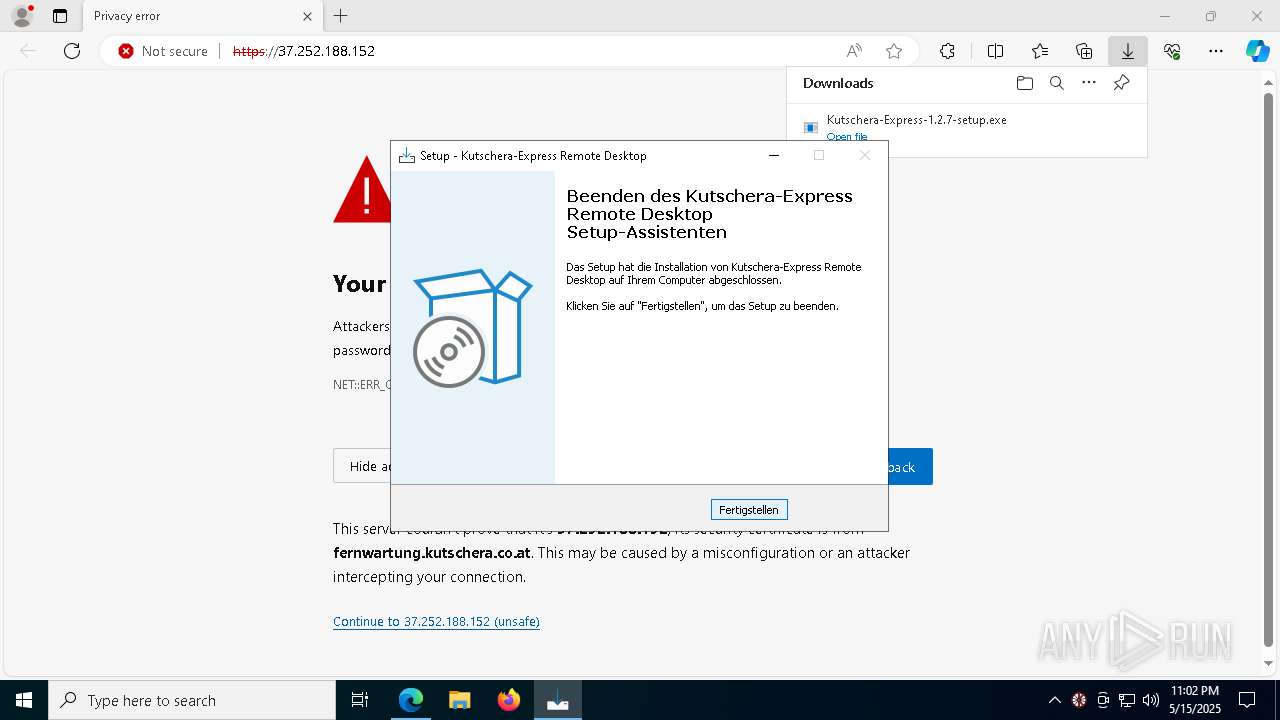
Creates a software uninstall entry
- reg.exe (PID: 1040)
- reg.exe (PID: 4464)
- reg.exe (PID: 2040)
- reg.exe (PID: 4188)
- reg.exe (PID: 5588)
- reg.exe (PID: 2236)
- reg.exe (PID: 6228)
- reg.exe (PID: 1012)
- reg.exe (PID: 7928)
- reg.exe (PID: 7528)
- reg.exe (PID: 7952)
- reg.exe (PID: 4736)
- reg.exe (PID: 5576)
Runs shell command (SCRIPT)
- cscript.exe (PID: 6252)
- cscript.exe (PID: 7180)
- cscript.exe (PID: 720)
- cscript.exe (PID: 7172)
The process executes VB scripts
- cmd.exe (PID: 5780)
- cmd.exe (PID: 6572)
Sets the service to start on system boot
- sc.exe (PID: 6048)
- sc.exe (PID: 1348)
Executes as Windows Service
- Kutschera-Express.exe (PID: 1056)
- Kutschera-Express.exe (PID: 8036)
- Kutschera-Express.exe (PID: 7928)
- Kutschera-Express.exe (PID: 5228)
Application launched itself
- Kutschera-Express.exe (PID: 6048)
- Kutschera-Express.exe (PID: 8036)
- Kutschera-Express.exe (PID: 5228)
- Kutschera-Express.exe (PID: 7396)
Creates a new Windows service
- sc.exe (PID: 5600)
- sc.exe (PID: 7428)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 5780)
Starts itself from another location
- Kutschera-Express.exe (PID: 5084)
- Kutschera-Express.exe (PID: 4736)
The process checks if it is being run in the virtual environment
- Kutschera-Express.exe (PID: 6048)
- Kutschera-Express.exe (PID: 7396)
- Kutschera-Express.exe (PID: 8172)
Connects to unusual port
- Kutschera-Express.exe (PID: 6048)
- Kutschera-Express.exe (PID: 7396)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6468)
INFO
Create files in a temporary directory
- Kutschera-Express-1.2.7-setup.exe (PID: 7400)
- Kutschera-Express-1.2.7-setup.exe (PID: 5552)
- Kutschera-Express-1.2.7-setup.tmp (PID: 3240)
- Kutschera-Express.exe (PID: 5084)
- cscript.exe (PID: 7180)
- cscript.exe (PID: 720)
- cscript.exe (PID: 6252)
- Kutschera-Express.exe (PID: 4736)
- cscript.exe (PID: 7172)
Checks supported languages
- Kutschera-Express-1.2.7-setup.exe (PID: 7400)
- identity_helper.exe (PID: 516)
- Kutschera-Express-1.2.7-setup.tmp (PID: 4996)
- Kutschera-Express-1.2.7-setup.exe (PID: 5552)
- Kutschera-Express-1.2.7-setup.tmp (PID: 3240)
- Kutschera-Express.exe (PID: 5084)
- Kutschera-Express.exe (PID: 6476)
- Kutschera-Express.exe (PID: 5328)
- chcp.com (PID: 2908)
- chcp.com (PID: 3884)
- Kutschera-Express.exe (PID: 1056)
- chcp.com (PID: 736)
- Kutschera-Express.exe (PID: 8036)
- Kutschera-Express.exe (PID: 6048)
- Kutschera-Express.exe (PID: 6044)
- Kutschera-Express.exe (PID: 5756)
- Kutschera-Express.exe (PID: 4736)
- chcp.com (PID: 7180)
- Kutschera-Express.exe (PID: 7928)
- Kutschera-Express.exe (PID: 5228)
- Kutschera-Express.exe (PID: 7396)
- Kutschera-Express.exe (PID: 5352)
- Kutschera-Express.exe (PID: 2552)
- Kutschera-Express.exe (PID: 5212)
- Kutschera-Express.exe (PID: 208)
- Kutschera-Express.exe (PID: 5244)
- Kutschera-Express.exe (PID: 4696)
- Kutschera-Express.exe (PID: 5592)
- Kutschera-Express.exe (PID: 8172)
- Kutschera-Express.exe (PID: 7176)
Application launched itself
- msedge.exe (PID: 7376)
Reads the computer name
- identity_helper.exe (PID: 516)
- Kutschera-Express-1.2.7-setup.tmp (PID: 4996)
- Kutschera-Express-1.2.7-setup.exe (PID: 5552)
- Kutschera-Express-1.2.7-setup.tmp (PID: 3240)
- Kutschera-Express.exe (PID: 5084)
- Kutschera-Express.exe (PID: 6476)
- Kutschera-Express.exe (PID: 5328)
- Kutschera-Express.exe (PID: 1056)
- Kutschera-Express.exe (PID: 8036)
- Kutschera-Express.exe (PID: 6048)
- Kutschera-Express.exe (PID: 5756)
- Kutschera-Express.exe (PID: 4736)
- Kutschera-Express.exe (PID: 6044)
- Kutschera-Express.exe (PID: 5228)
- Kutschera-Express.exe (PID: 7396)
- Kutschera-Express.exe (PID: 5352)
- Kutschera-Express.exe (PID: 7928)
- Kutschera-Express.exe (PID: 2552)
- Kutschera-Express.exe (PID: 5212)
- Kutschera-Express.exe (PID: 5244)
- Kutschera-Express.exe (PID: 208)
- Kutschera-Express.exe (PID: 5592)
- Kutschera-Express.exe (PID: 4696)
- Kutschera-Express.exe (PID: 8172)
- Kutschera-Express.exe (PID: 7176)
Reads Environment values
- identity_helper.exe (PID: 516)
- Kutschera-Express.exe (PID: 8172)
- Kutschera-Express.exe (PID: 7396)
Executable content was dropped or overwritten
- msedge.exe (PID: 7376)
Process checks computer location settings
- Kutschera-Express-1.2.7-setup.tmp (PID: 4996)
- Kutschera-Express.exe (PID: 5084)
- Kutschera-Express.exe (PID: 4736)
Detects InnoSetup installer (YARA)
- Kutschera-Express-1.2.7-setup.exe (PID: 7400)
Compiled with Borland Delphi (YARA)
- Kutschera-Express-1.2.7-setup.exe (PID: 7400)
Creates files or folders in the user directory
- Kutschera-Express.exe (PID: 5084)
- Kutschera-Express.exe (PID: 6476)
- Kutschera-Express.exe (PID: 5328)
- Kutschera-Express.exe (PID: 4736)
- Kutschera-Express.exe (PID: 6044)
- Kutschera-Express.exe (PID: 5352)
- Kutschera-Express.exe (PID: 5212)
- Kutschera-Express.exe (PID: 5244)
- Kutschera-Express.exe (PID: 5592)
- Kutschera-Express-1.2.7-setup.tmp (PID: 3240)
- Kutschera-Express.exe (PID: 4696)
- Kutschera-Express.exe (PID: 208)
- Kutschera-Express.exe (PID: 8172)
- Kutschera-Express.exe (PID: 7176)
Creates files in the program directory
- cmd.exe (PID: 5780)
- xcopy.exe (PID: 1132)
Changes the display of characters in the console
- cmd.exe (PID: 5780)
- cmd.exe (PID: 6572)
The sample compiled with english language support
- cmd.exe (PID: 5780)
Reads security settings of Internet Explorer
- cscript.exe (PID: 7180)
- cscript.exe (PID: 720)
- cscript.exe (PID: 6252)
- cscript.exe (PID: 7172)
Reads the machine GUID from the registry
- Kutschera-Express.exe (PID: 6048)
- Kutschera-Express.exe (PID: 7396)
- Kutschera-Express.exe (PID: 4696)
- Kutschera-Express.exe (PID: 8172)
Reads Windows Product ID
- Kutschera-Express.exe (PID: 8172)
Checks proxy server information
- Kutschera-Express.exe (PID: 8172)
Reads product name
- Kutschera-Express.exe (PID: 8172)
- Kutschera-Express.exe (PID: 7396)
Reads the software policy settings
- Kutschera-Express.exe (PID: 8172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
272
Monitored processes
143
Malicious processes
13
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | reg add HKEY_CLASSES_ROOT\.kutschera-express /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | "C:\Users\admin\AppData\Local\Temp\is-N8FOD.tmp\files\Kutschera-Express.exe" --option verification-method use-both-passwords | C:\Users\admin\AppData\Local\Temp\is-N8FOD.tmp\files\Kutschera-Express.exe | — | Kutschera-Express-1.2.7-setup.tmp | |||||||||||
User: admin Company: Kutschera Datentechnik GmbH Integrity Level: HIGH Description: Kutschera-Express Remote Desktop Exit code: 0 Version: 1.2.7+46 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5776 --field-trial-handle=2372,i,831742956706278187,16152116285265995595,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | "cmd" /c "taskkill /F /IM RuntimeBroker_rustdesk.exe" | C:\Windows\System32\cmd.exe | — | Kutschera-Express.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6596 --field-trial-handle=2372,i,831742956706278187,16152116285265995595,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3864 --field-trial-handle=2372,i,831742956706278187,16152116285265995595,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | cscript "C:\Users\admin\AppData\Local\Temp\Kutschera-Express_uninstall_shortcut.vbs" | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5204 --field-trial-handle=2372,i,831742956706278187,16152116285265995595,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | reg add HKEY_CLASSES_ROOT\.kutschera-express\shell\open /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 538
Read events
12 512
Write events
26
Delete events
0
Modification events
| (PID) Process: | (7376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7376) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D4B8F9EFCA932F00 | |||
| (PID) Process: | (7376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (7376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (7376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328396 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B8193BF1-0322-4AE2-9F80-F9B5C38BC928} | |||
| (PID) Process: | (7376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (7376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328396 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0C1E60B5-EC78-4F83-B109-641F54DEF9A9} | |||
Executable files
60
Suspicious files
93
Text files
284
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b596.TMP | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b596.TMP | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b5a6.TMP | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b5b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b5b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
49
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 204 | 150.171.73.11:80 | http://edge-http.microsoft.com/captiveportal/generate_204 | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7048 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7048 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 37.252.188.152:443 | fernwartung.kutschera.co.at | IPAX OG | AT | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
edge-http.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |