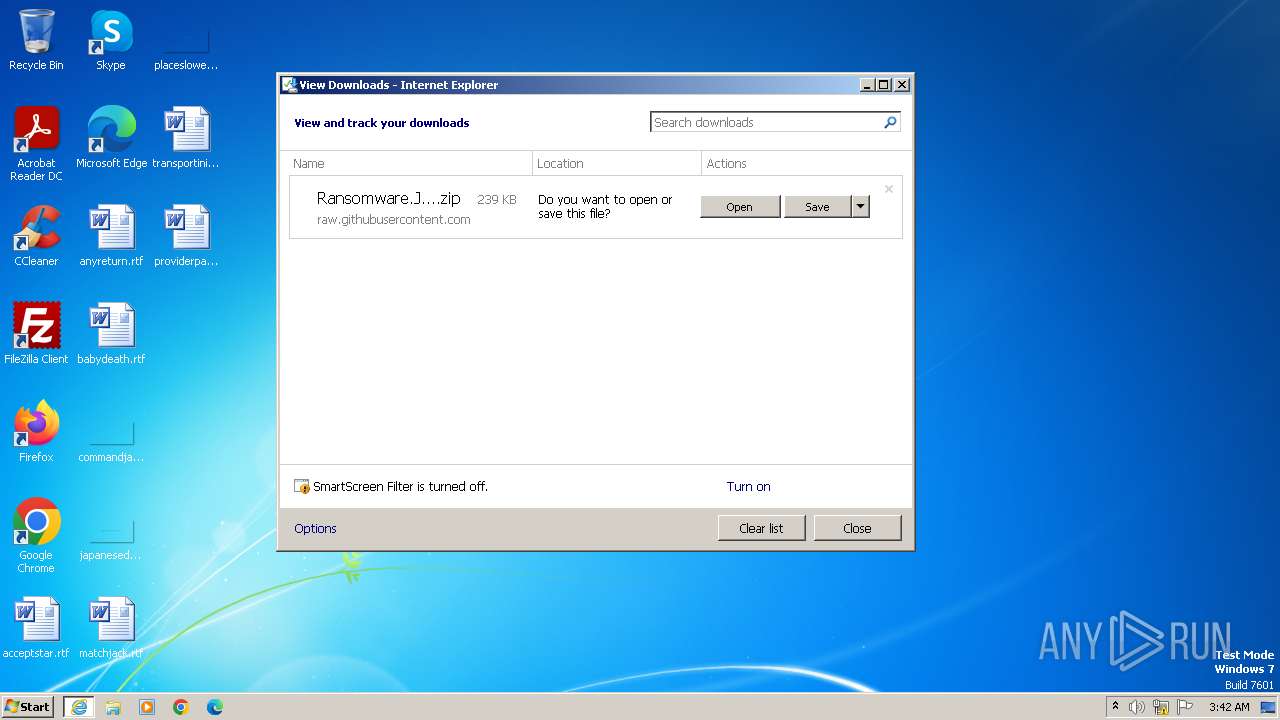
| URL: | https://github.com/kh4sh3i/Ransomware-Samples/raw/main/Jigsaw/Ransomware.Jigsaw.zip |
| Full analysis: | https://app.any.run/tasks/355a2b5c-3af1-4801-9b1b-1258876a7ca3 |
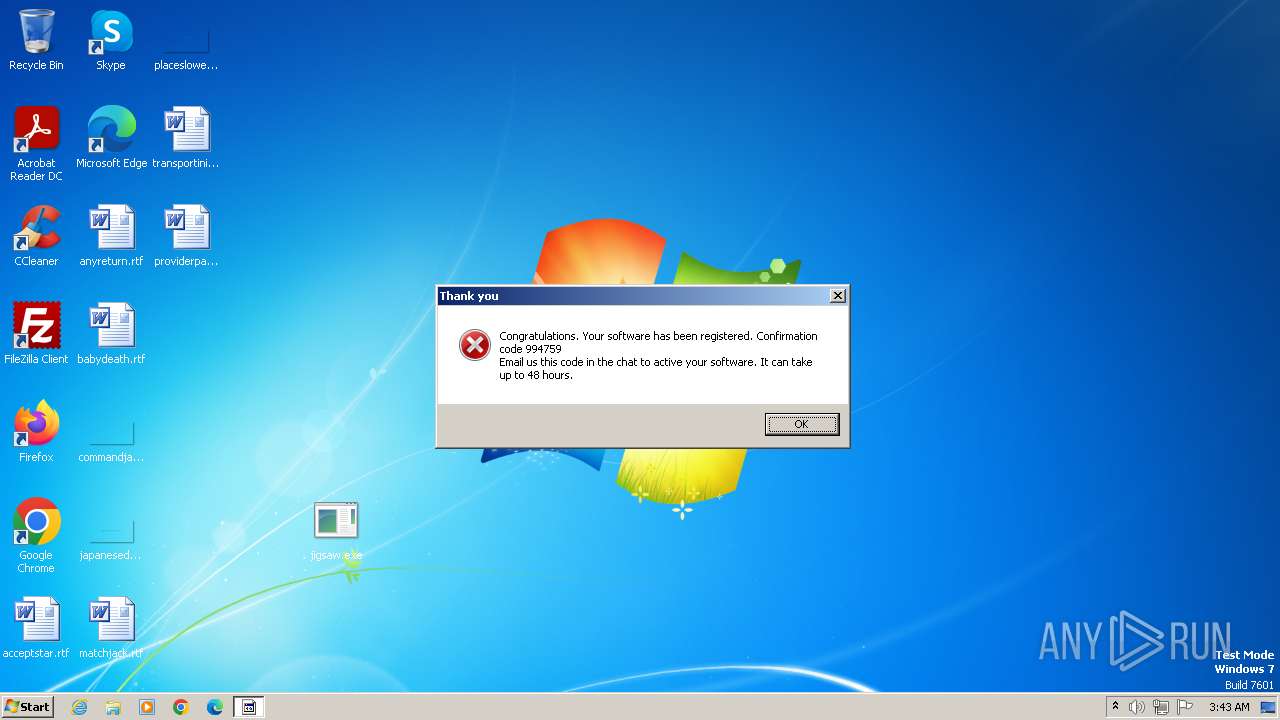
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2023, 03:42:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | AB1FFB5B75A0F12AFF0742CDA474C23A9D9B8A2F |
| SHA256: | 967DF4A2BB6B1C091FEDA140A1A51F984B1E7AC5CC47FDB398F7C26EB6733348 |
| SSDEEP: | 3:N8tEd+NbttIHH5R/c:2uoNh6Hf/c |
MALICIOUS
Drops the executable file immediately after the start
- jigsaw.exe (PID: 3956)
- drpbx.exe (PID: 4036)
Steals credentials from Web Browsers
- drpbx.exe (PID: 4036)
Actions looks like stealing of personal data
- drpbx.exe (PID: 4036)
SUSPICIOUS
Reads the Internet Settings
- jigsaw.exe (PID: 3956)
Starts itself from another location
- jigsaw.exe (PID: 3956)
INFO
Application launched itself
- iexplore.exe (PID: 3196)
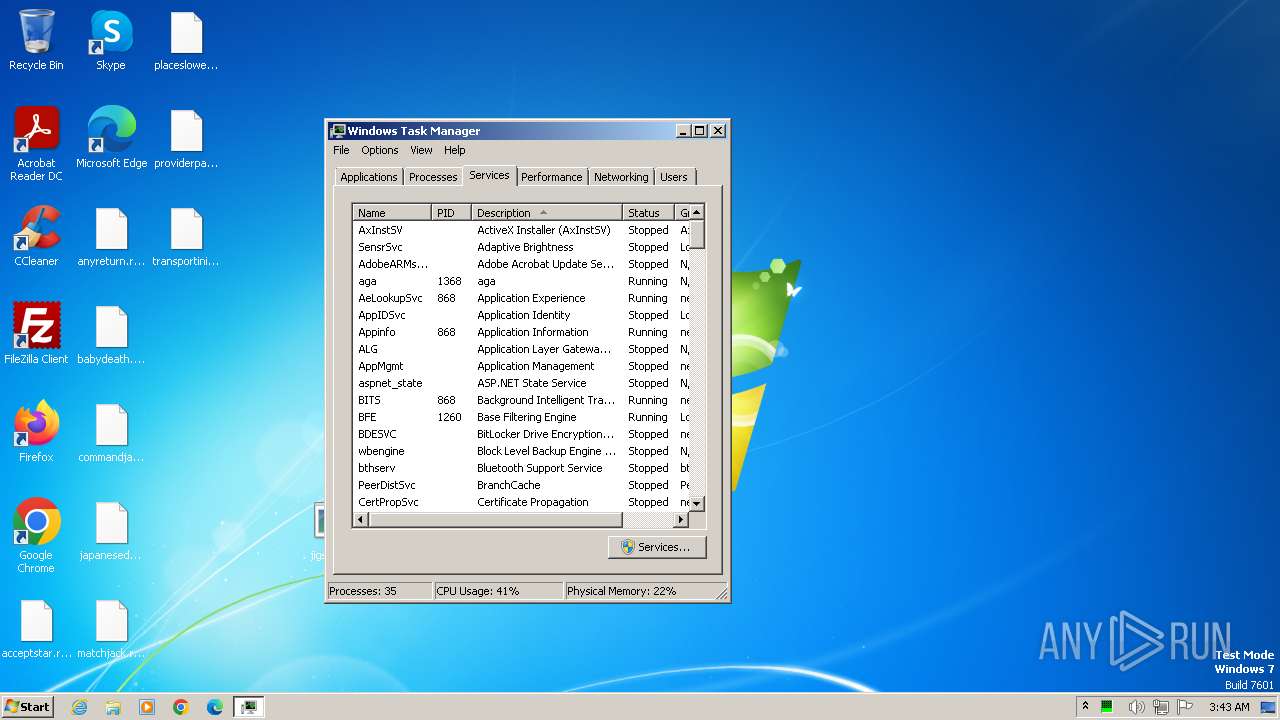
Manual execution by a user
- wmpnscfg.exe (PID: 3756)
- jigsaw.exe (PID: 3956)
- taskmgr.exe (PID: 3696)
Reads the computer name
- wmpnscfg.exe (PID: 3756)
- jigsaw.exe (PID: 3956)
Checks supported languages
- wmpnscfg.exe (PID: 3756)
- drpbx.exe (PID: 4036)
- jigsaw.exe (PID: 3956)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3756)
- jigsaw.exe (PID: 3956)
- drpbx.exe (PID: 4036)
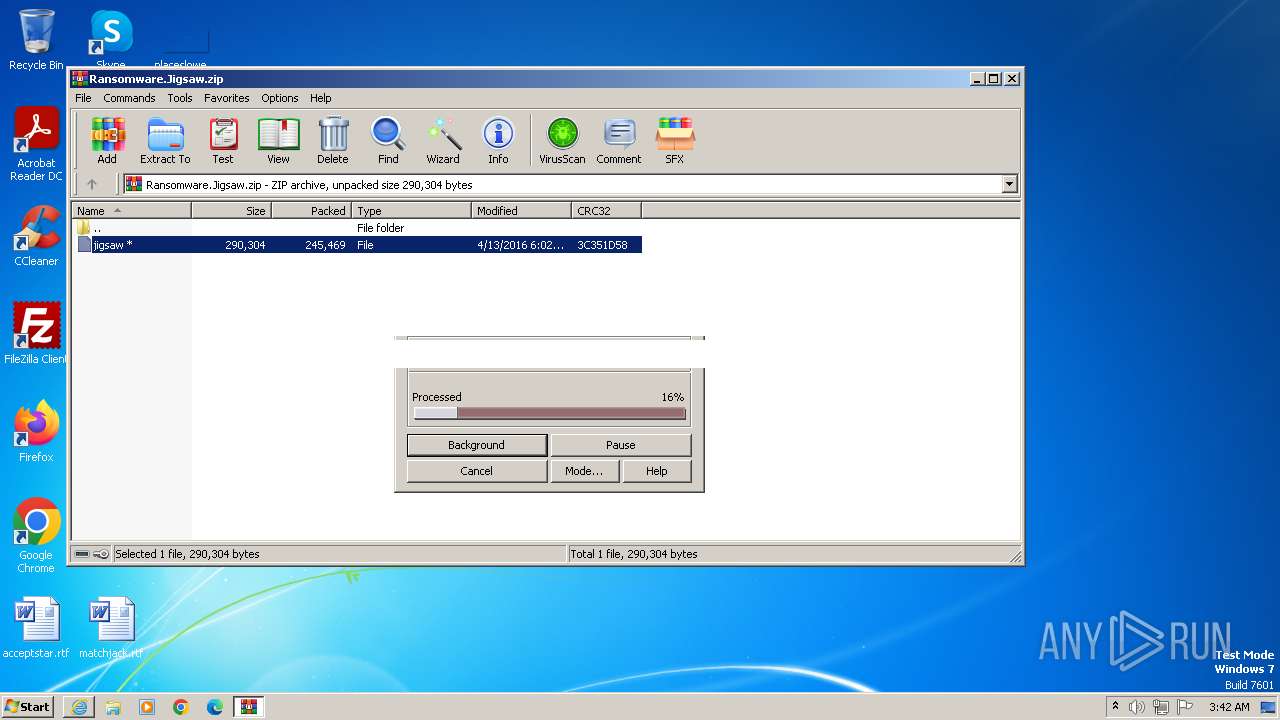
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3940)
Creates files or folders in the user directory
- jigsaw.exe (PID: 3956)
- drpbx.exe (PID: 4036)
The process uses the downloaded file
- WinRAR.exe (PID: 3940)
- iexplore.exe (PID: 3196)
Creates files in the program directory
- drpbx.exe (PID: 4036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
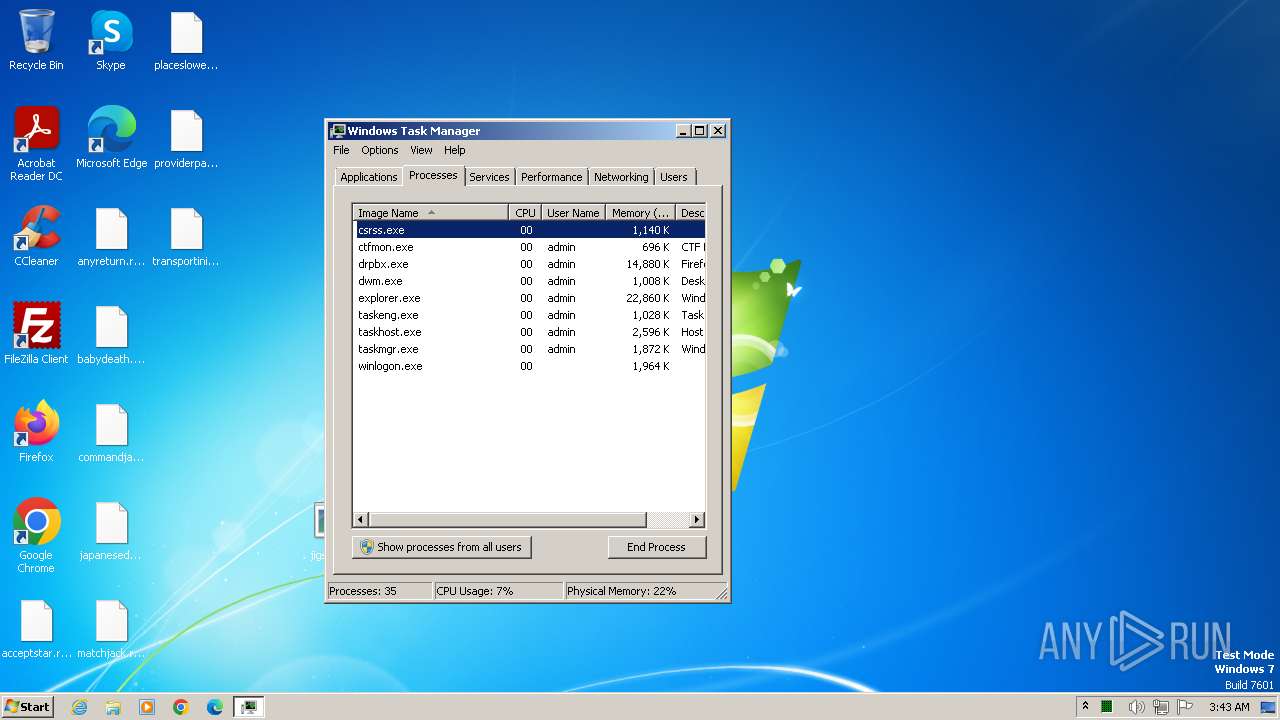
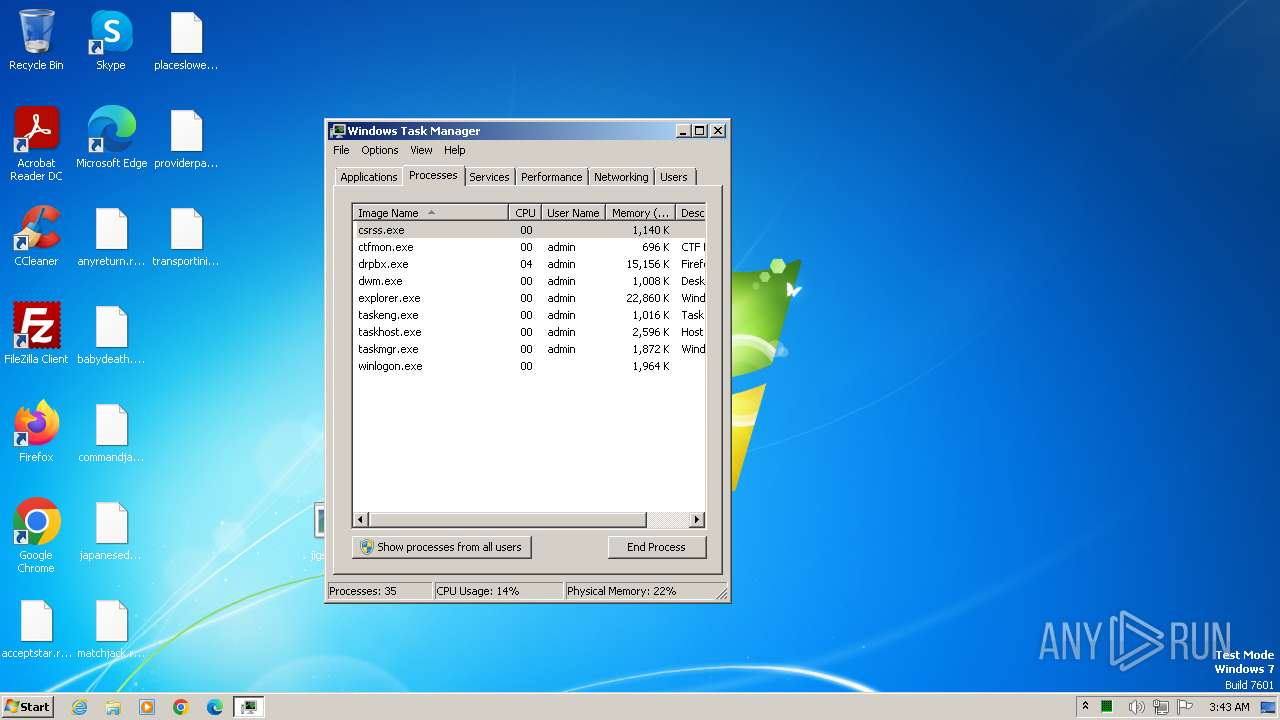
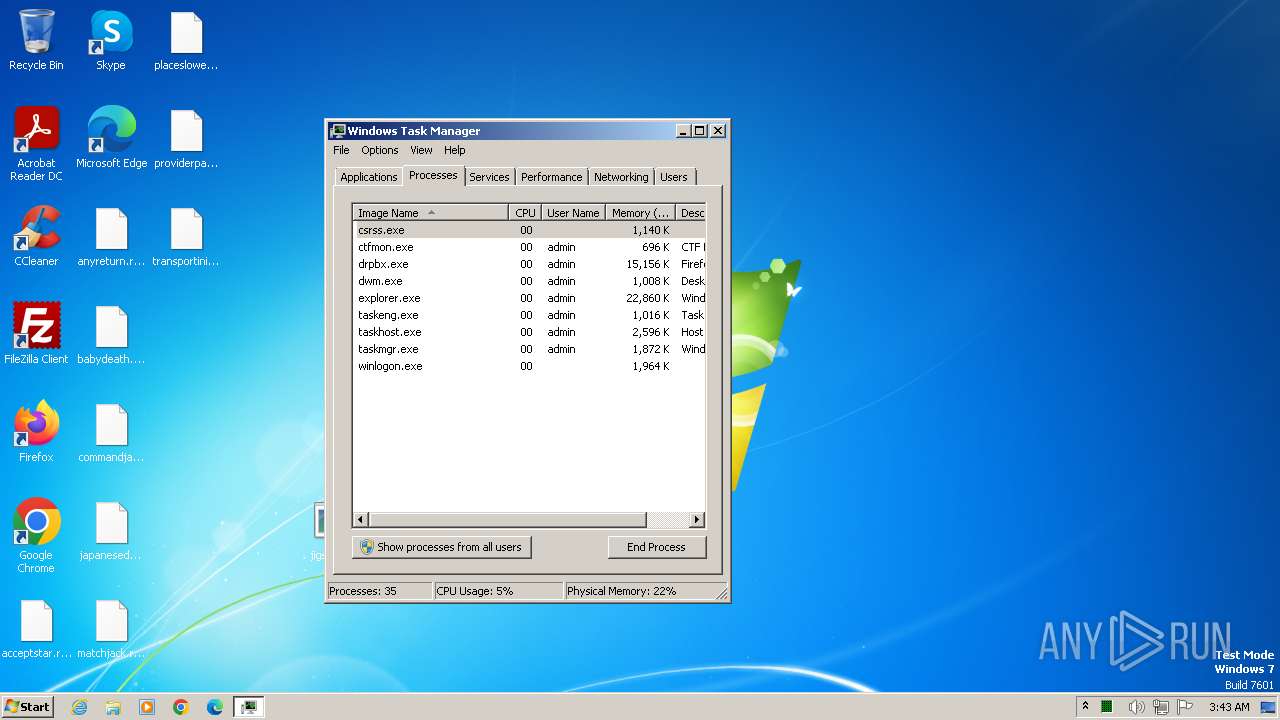
Total processes
44
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2900 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3196 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
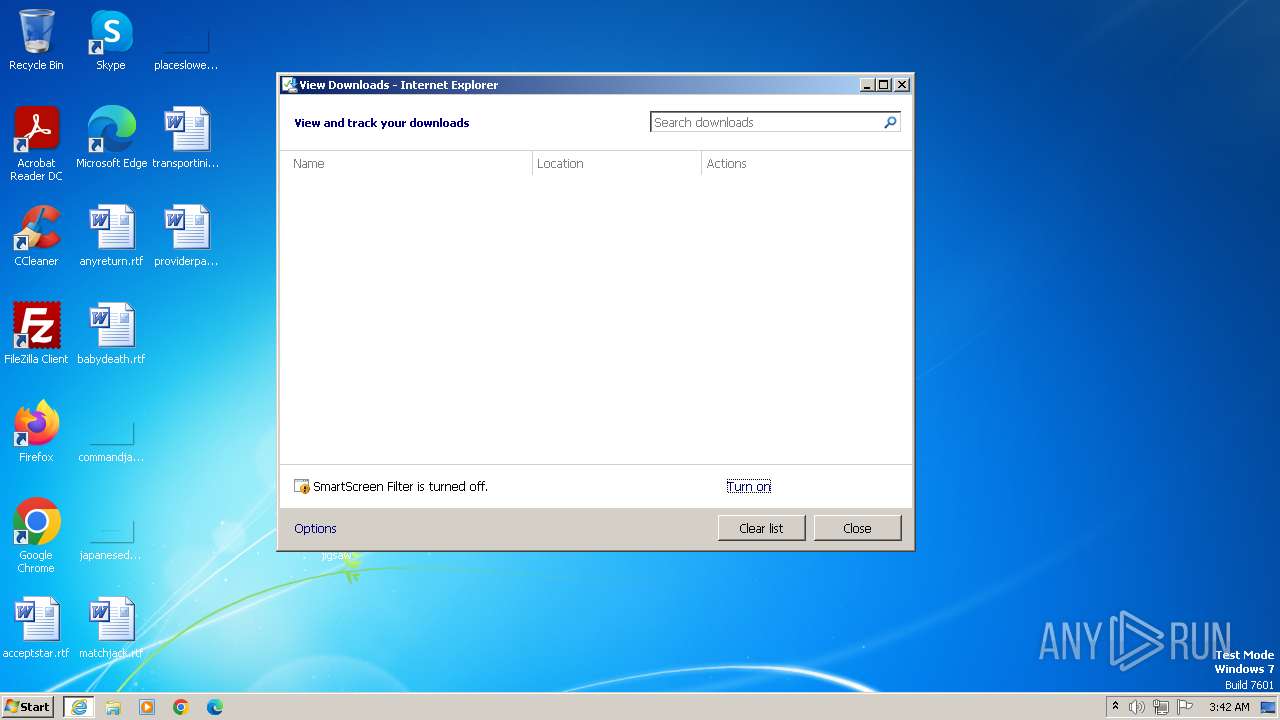
| 3196 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/kh4sh3i/Ransomware-Samples/raw/main/Jigsaw/Ransomware.Jigsaw.zip" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3696 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 3756 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
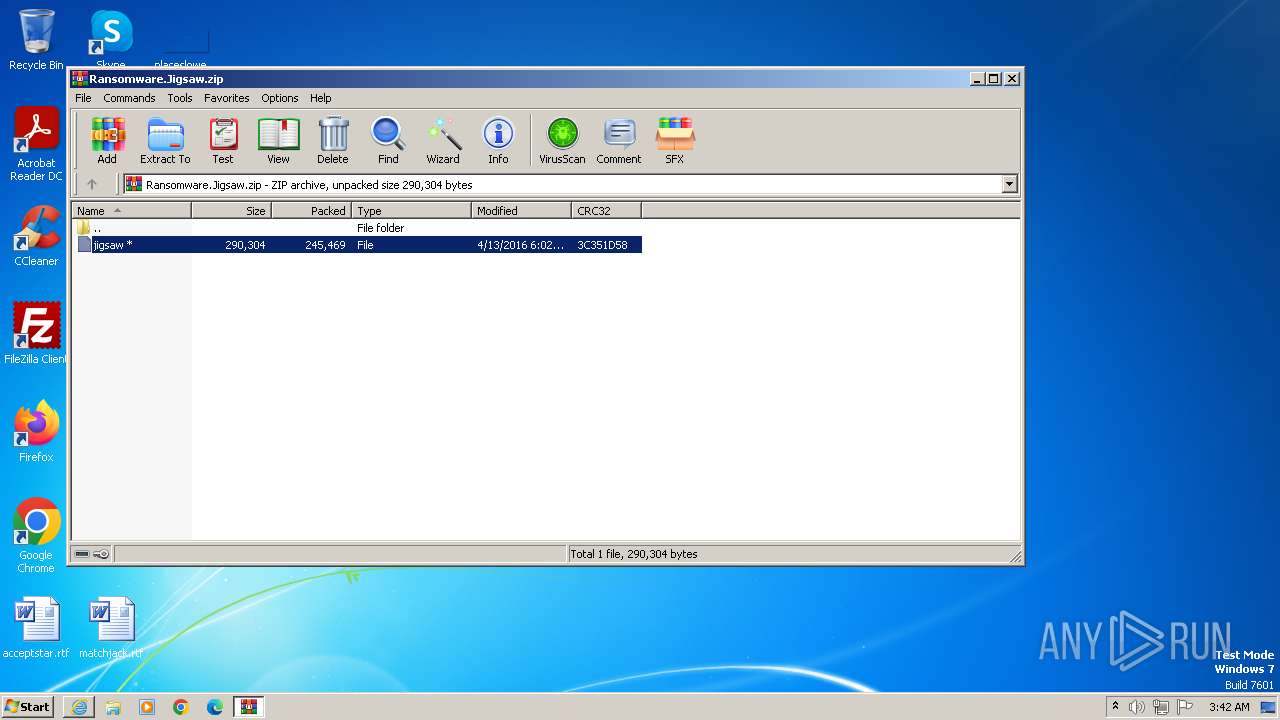
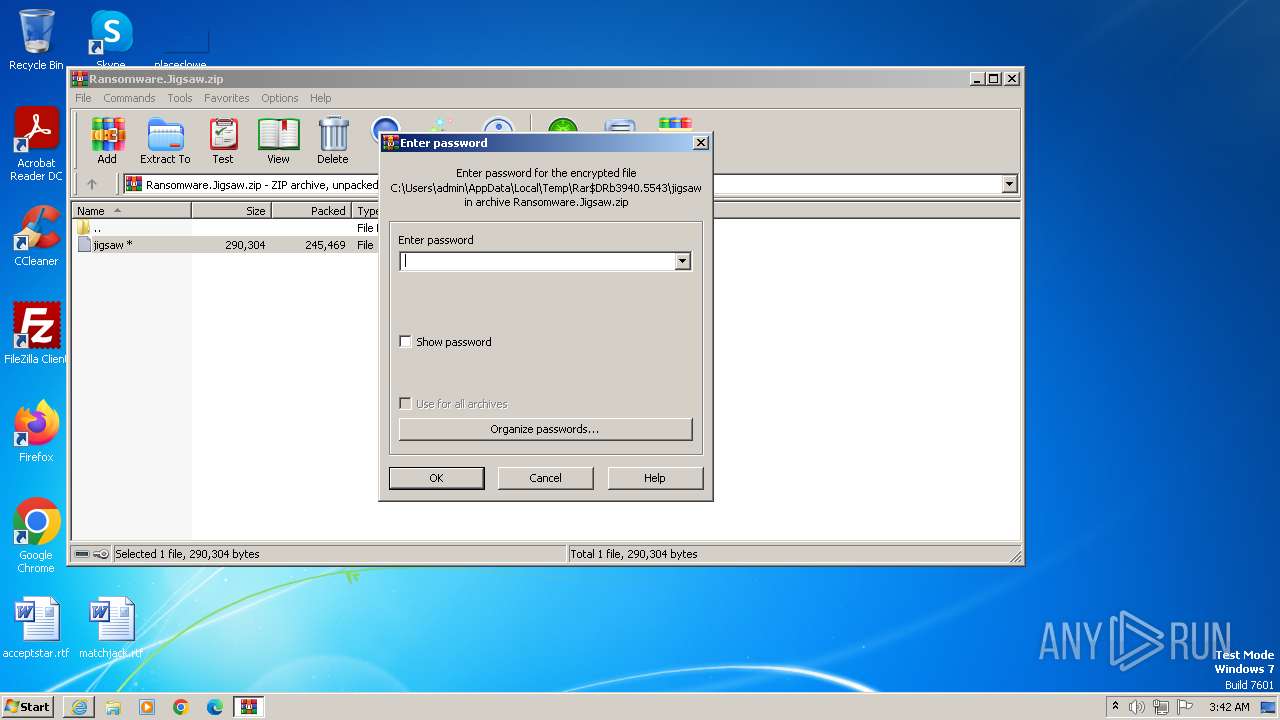
| 3940 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Ransomware.Jigsaw.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
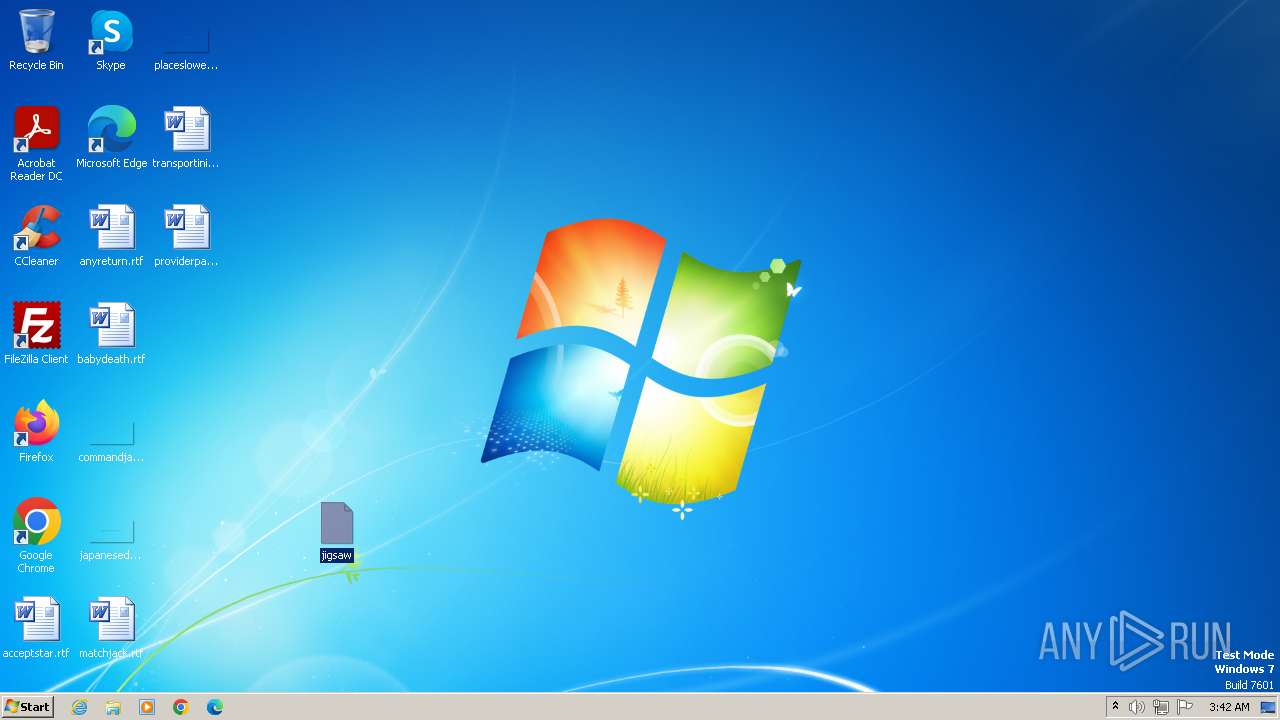
| 3956 | "C:\Users\admin\Desktop\jigsaw.exe" | C:\Users\admin\Desktop\jigsaw.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 4036 | "C:\Users\admin\AppData\Local\Drpbx\drpbx.exe" C:\Users\admin\Desktop\jigsaw.exe | C:\Users\admin\AppData\Local\Drpbx\drpbx.exe | jigsaw.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
Total events
21 988
Read events
21 920
Write events
64
Delete events
4
Modification events
| (PID) Process: | (3196) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3196) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3196) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3196) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3196) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3196) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3196) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3196) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3196) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3196) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
5
Suspicious files
660
Text files
24
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Ransomware.Jigsaw[1].zip | compressed | |
MD5:F2145E44504831F48E9A6C7D12D6FBB8 | SHA256:6B649E28B857FCBA7512DD673E0CA3C541C07F52DFB433B928200D8578E0A442 | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_D222662A57BAA60D2F5EA0D2CC7B2F1C | binary | |
MD5:F68F71B3727F05699EE0E5D642241302 | SHA256:37C194983437F8AB9DDC41E621E8CBD10230DA566CC9A0B6A8DB7888B9F7F13D | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:3FC77DD9583E2513CC517810CCA6615A | SHA256:1D77EAC0C3B887B1045F6719BD20F105478A7348AD180F5AAA83C9D6E57B9CD1 | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:B2322A457F5564D8FCCEDB128A5187CA | SHA256:671DB162FFB6148F93ECCC66B070CE0F470F4F328AC0A76BD3C89CFC341B2996 | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:1BF0C3E1DF5BEF0270C26BD3A6F90996 | SHA256:0D19F8EA41DDCA75D5174BCDE73F16839A9A98723EFD31CCD6E5C07D5F2257CB | |||
| 3940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3940.5543\jigsaw | executable | |
MD5:2773E3DC59472296CB0024BA7715A64E | SHA256:3AE96F73D805E1D3995253DB4D910300D8442EA603737A1428B613061E7F61E7 | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3465DA4B5A56FC67.TMP | binary | |
MD5:B714771C820D21D4278B086BFD63AB54 | SHA256:F5B24CDF737C974FB1D8DFE153819115AA3934CAB48A874B6BEB88F187942B97 | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Ransomware.Jigsaw.zip.ohty9y1.partial:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 3196 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFCBCBB751A1D345FA.TMP | binary | |
MD5:2F994B90DEF069E1737730AD782B1E1B | SHA256:60BB6E7CA2289EEFF75B23B57EA74FC6FDBA51795F596FE13E366E890C0A1D04 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
11
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2900 | iexplore.exe | GET | 200 | 8.253.207.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d1270903ad75d1e2 | unknown | compressed | 4.66 Kb | unknown |
2900 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAzQqL7GMs%2FmReygqbCE%2Bxw%3D | unknown | binary | 314 b | unknown |
2900 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | unknown | binary | 471 b | unknown |
2900 | iexplore.exe | GET | 200 | 8.253.207.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4531cc57055924f8 | unknown | compressed | 4.66 Kb | unknown |
2900 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2900 | iexplore.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
2900 | iexplore.exe | 8.253.207.120:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
2900 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2900 | iexplore.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
raw.githubusercontent.com |
| shared |