analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
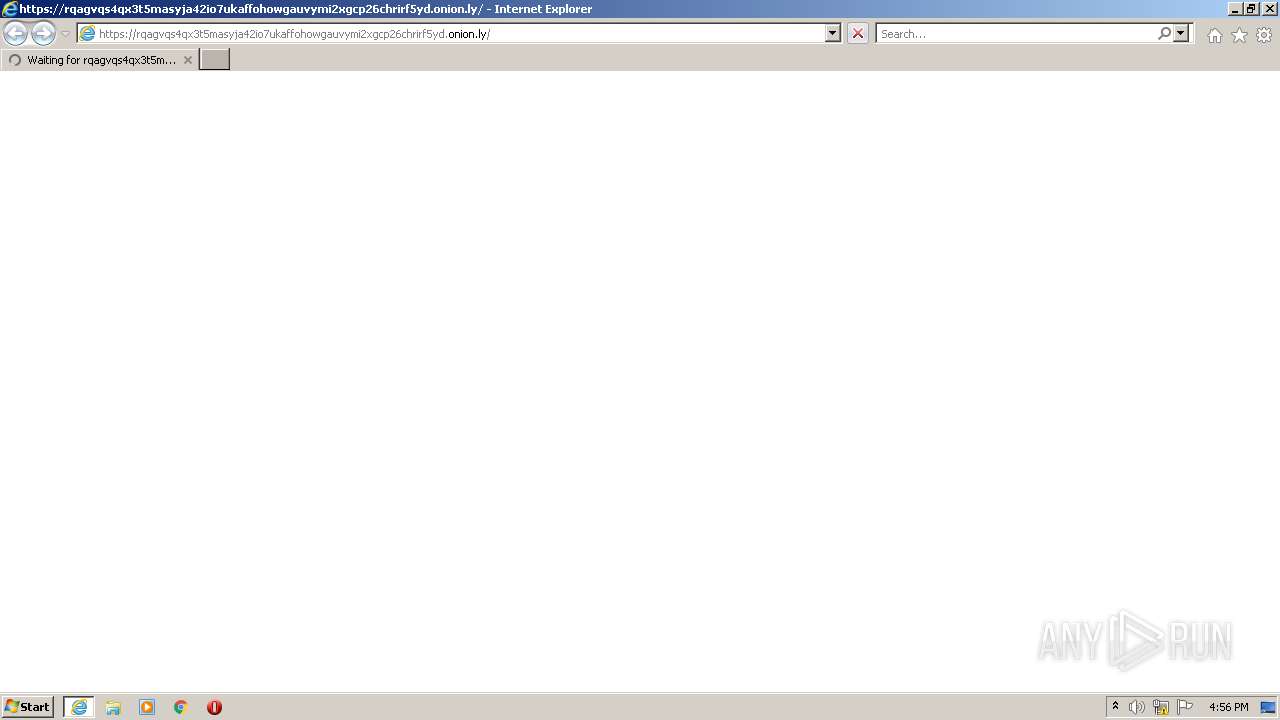
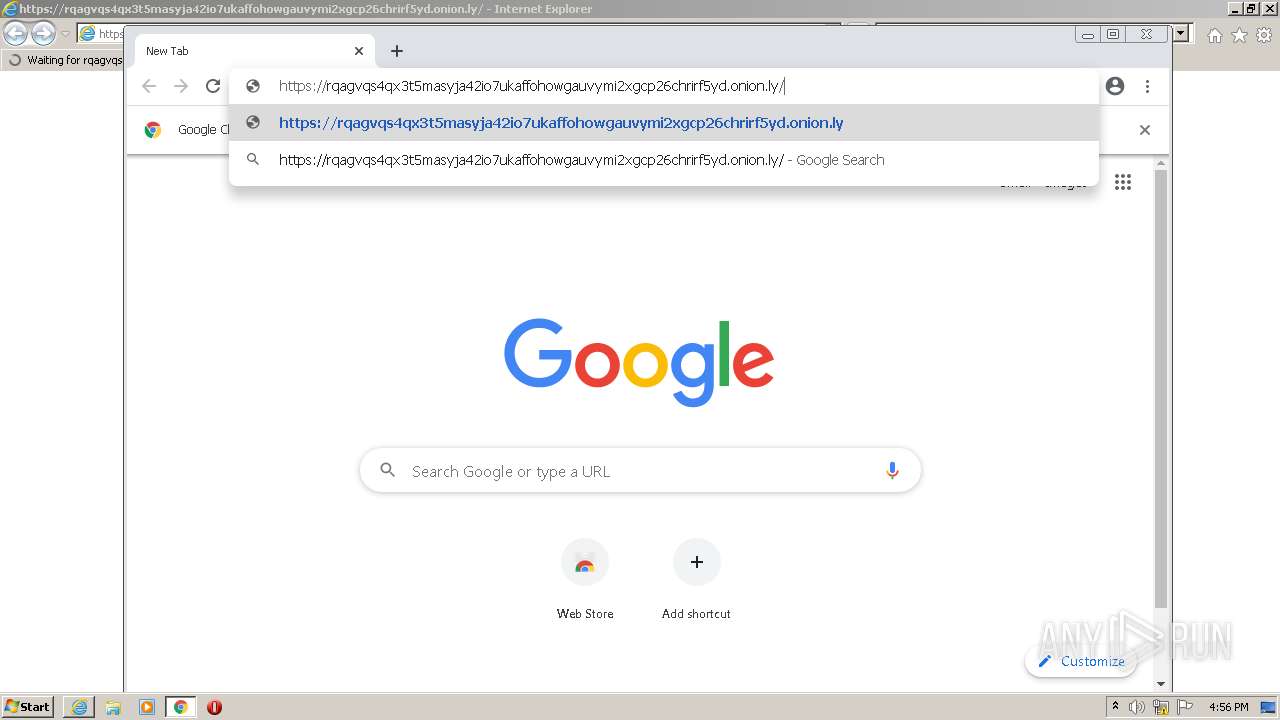
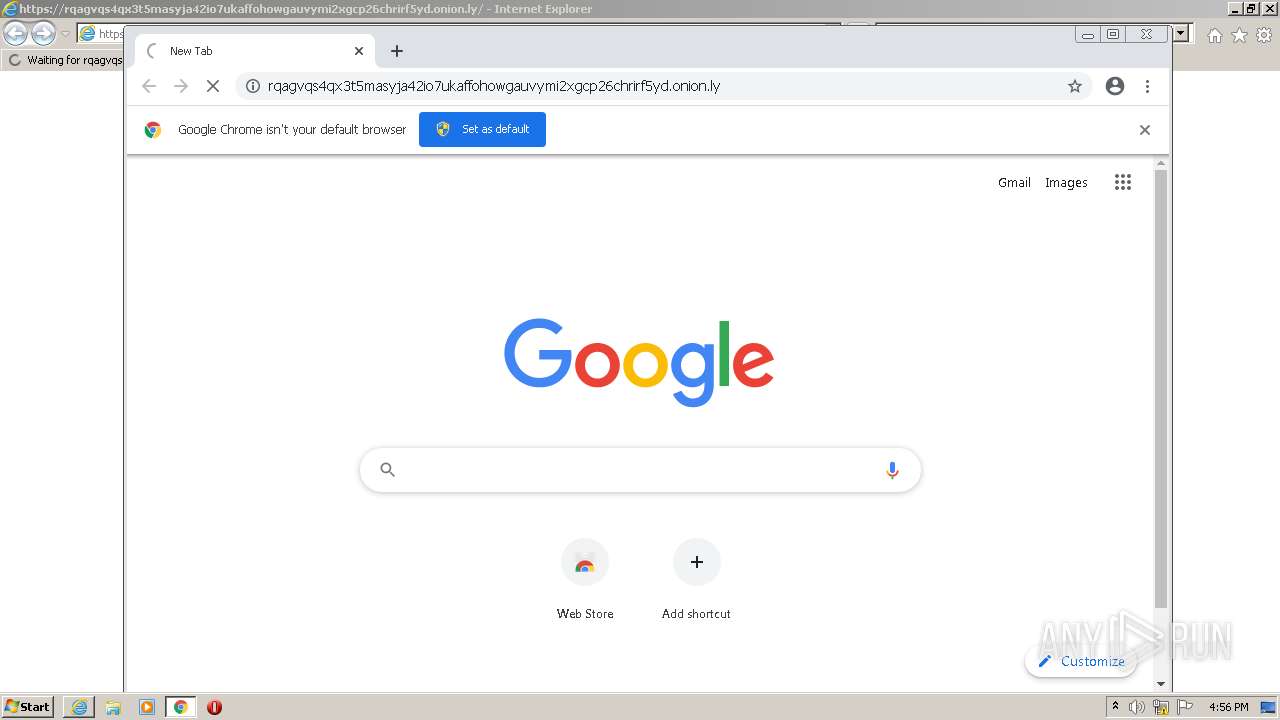
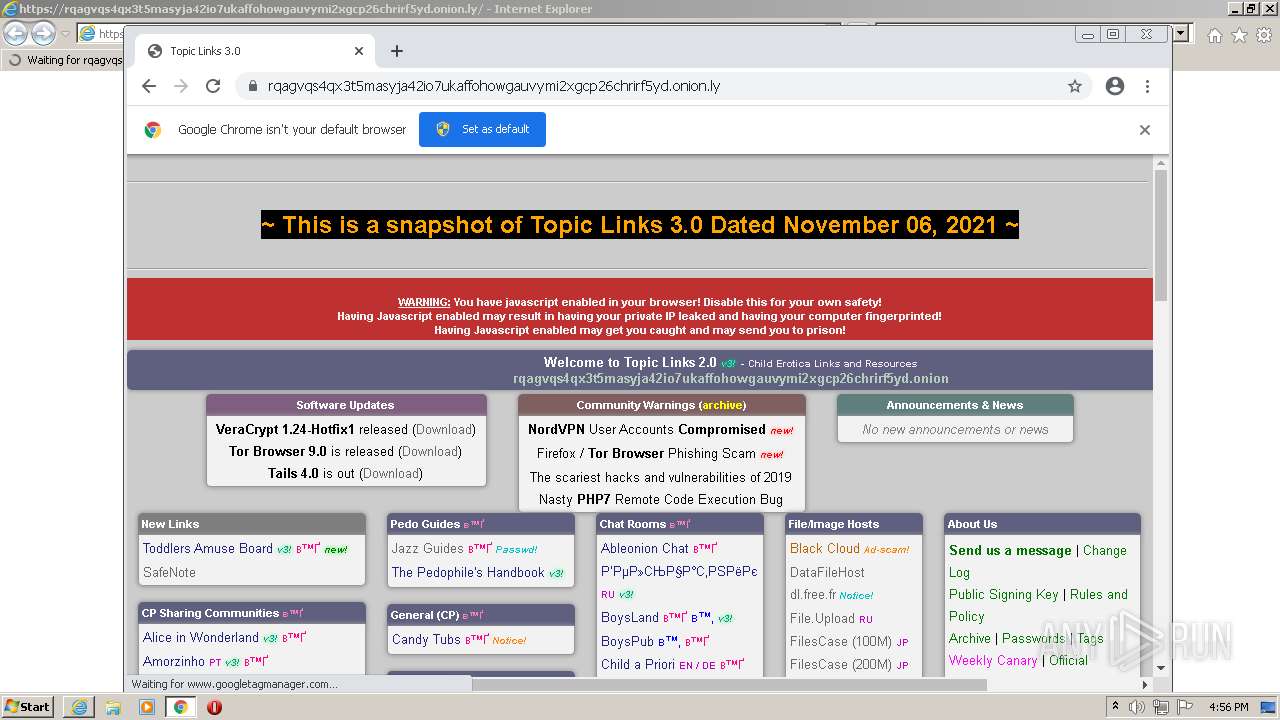
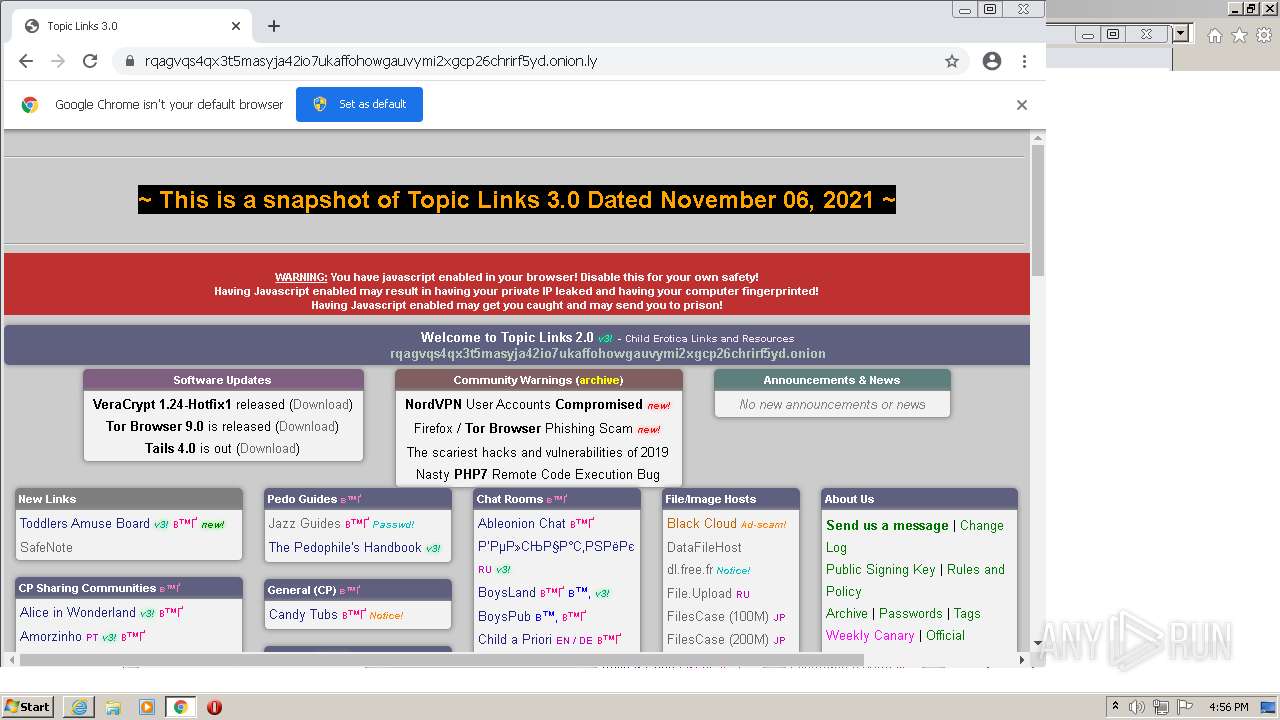
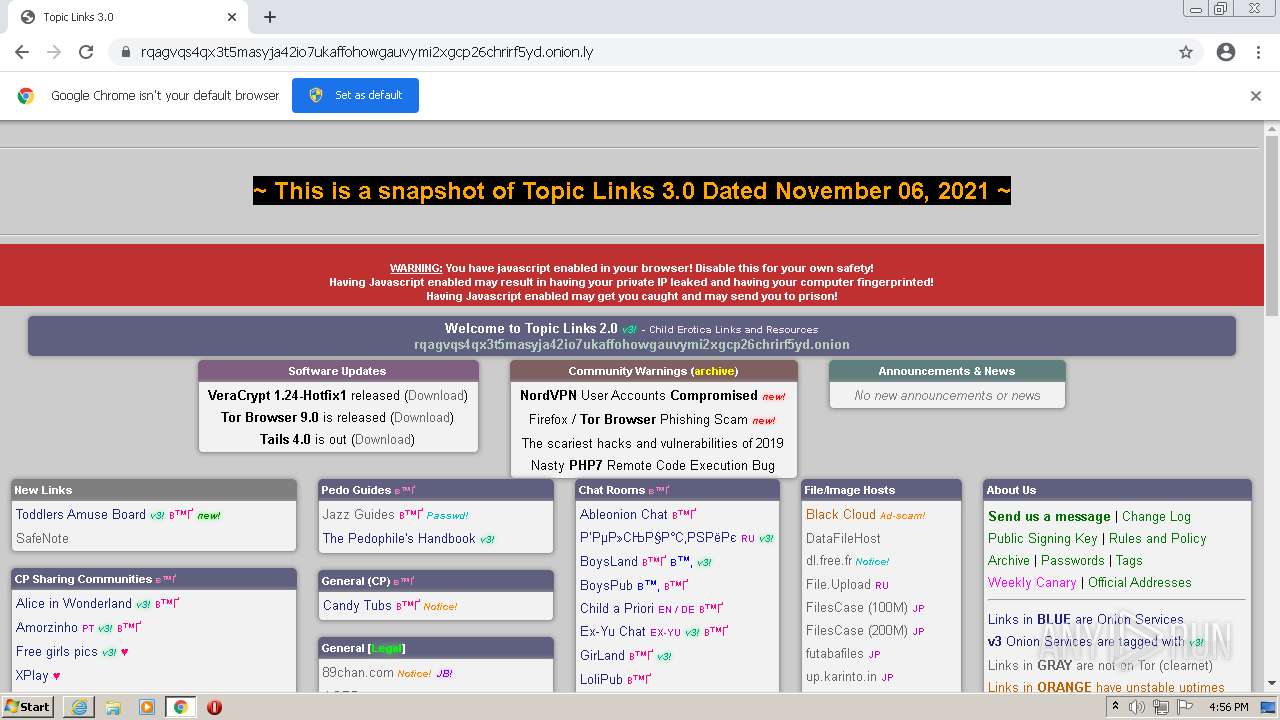
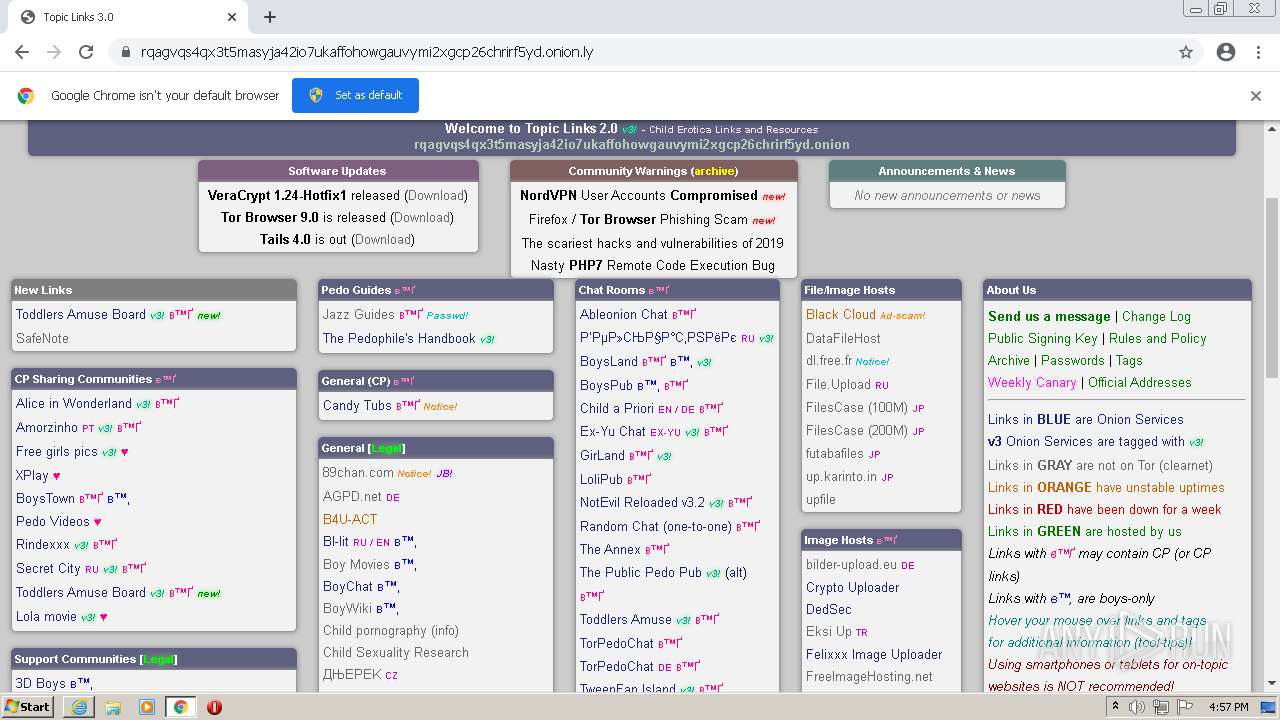
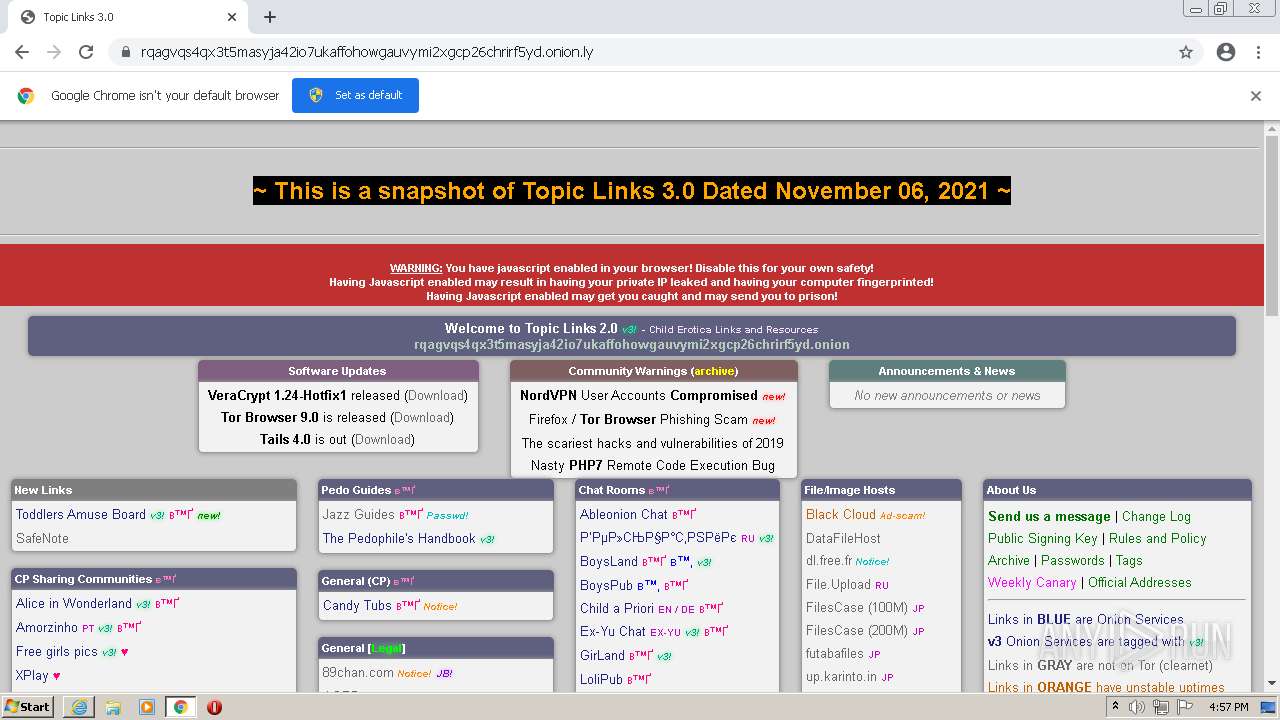
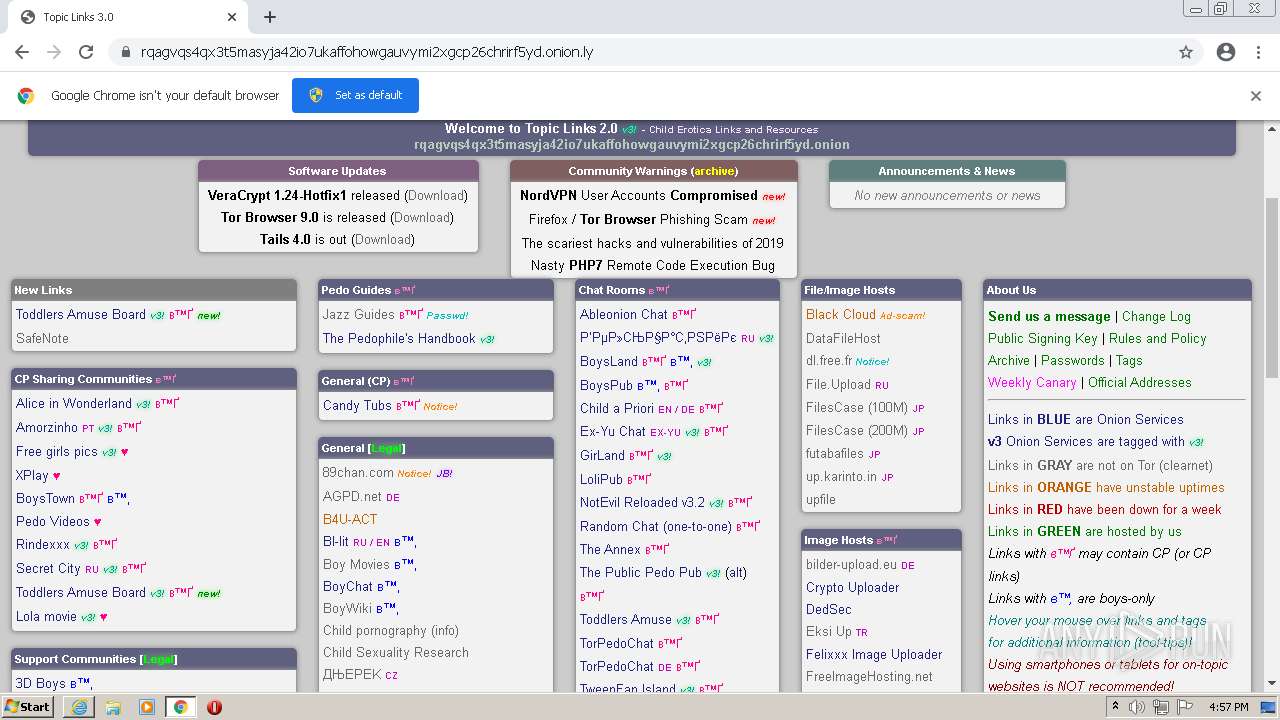
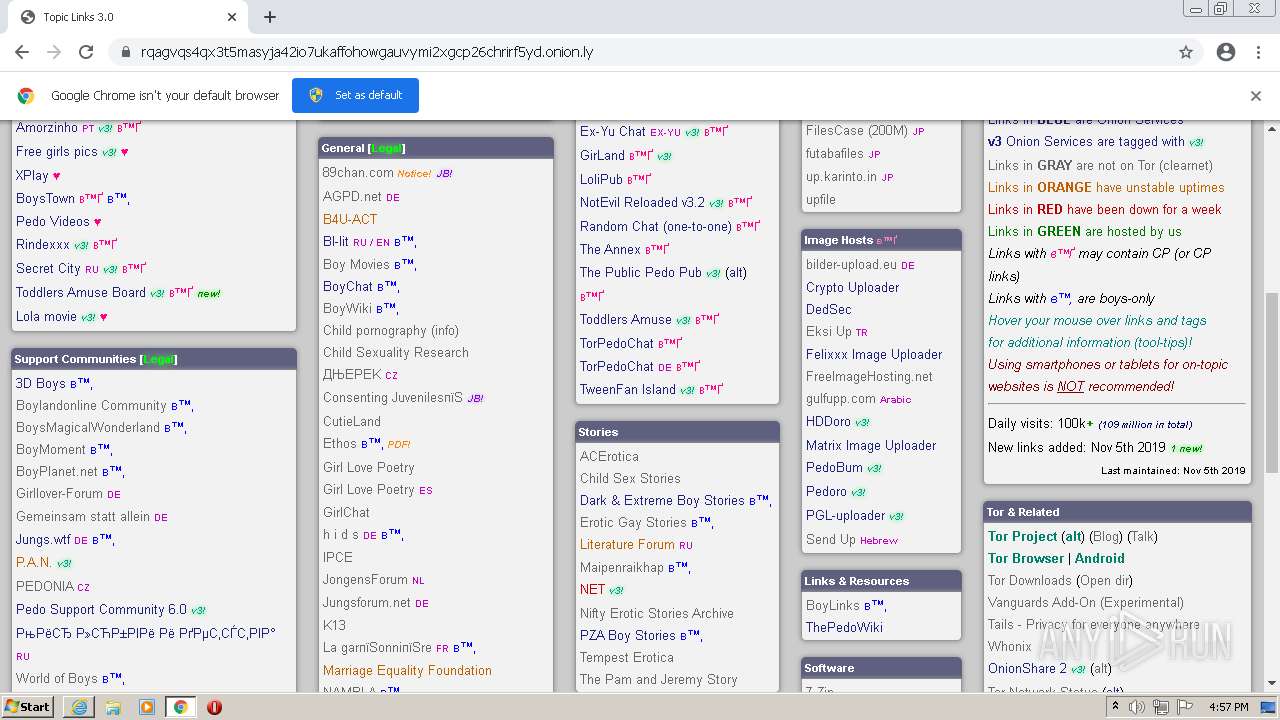
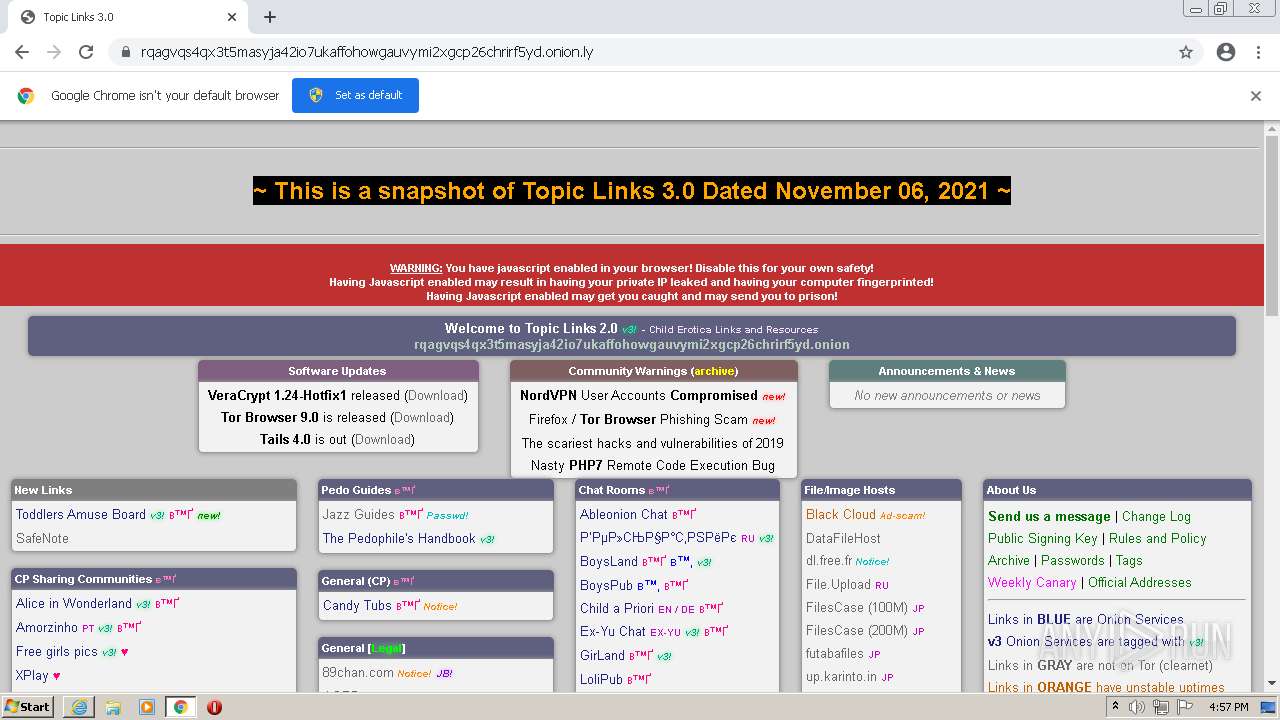
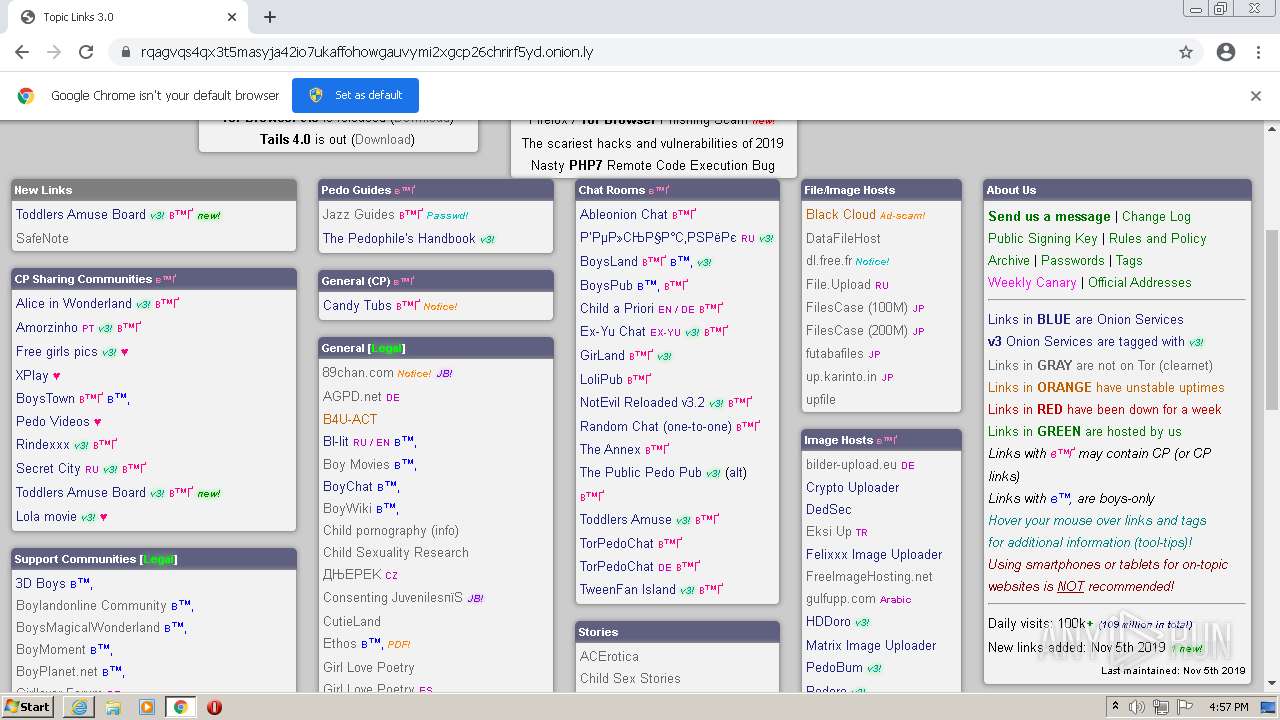
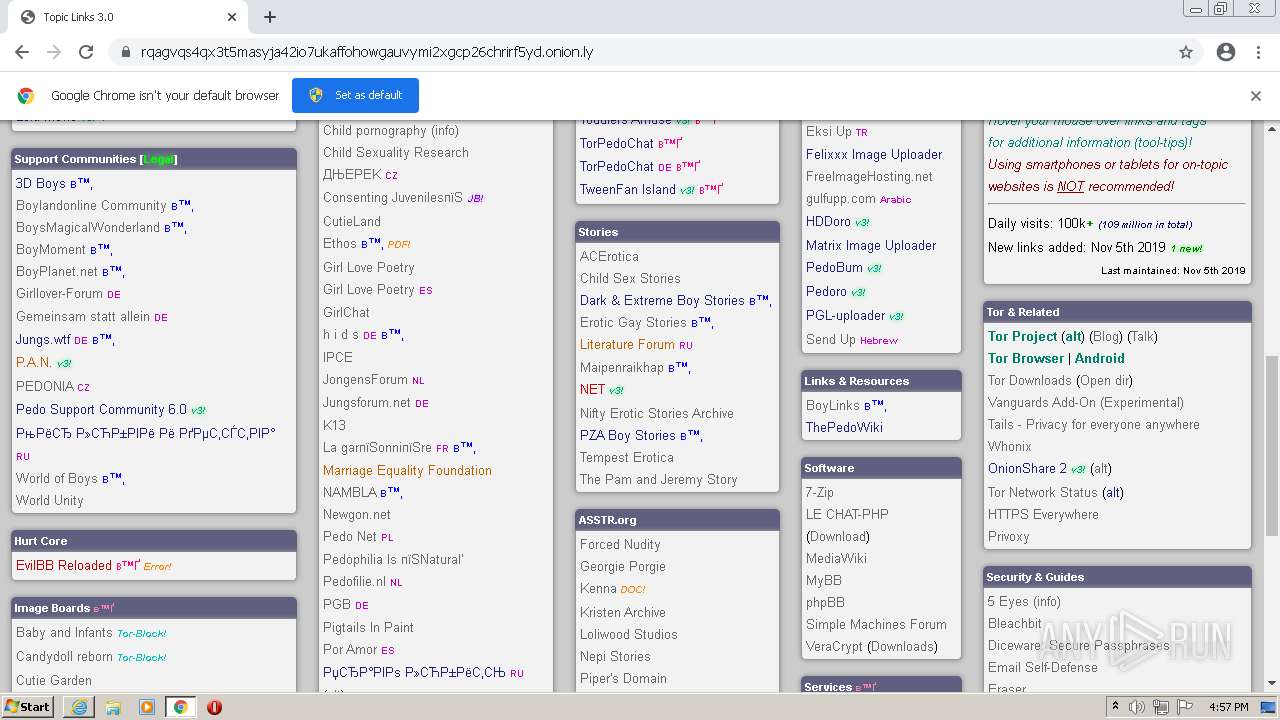
| URL: | https://rqagvqs4qx3t5masyja42io7ukaffohowgauvymi2xgcp26chrirf5yd.onion.ly |
| Full analysis: | https://app.any.run/tasks/d14da12e-9632-41f8-afa1-be6e91a59677 |
| Verdict: | Malicious activity |
| Analysis date: | April 27, 2022, 15:56:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5D89AAA20C6636C3E1E1CCF82632ACA7 |
| SHA1: | B1A42F61E0EDB8CD1338325A2D30C9410BFBBC1B |
| SHA256: | 967C2E9050985529F4AA9BE99C32B8181AAACF119DA378710DB19E829E3A5165 |
| SSDEEP: | 3:N8qTa8RyY0R5TacTmfS:2qTa8EDR5TJB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3540)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3948)
INFO
Reads the computer name
- iexplore.exe (PID: 3096)
- iexplore.exe (PID: 3540)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 2460)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 2624)
Checks supported languages
- iexplore.exe (PID: 3096)
- iexplore.exe (PID: 3540)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 3736)
- chrome.exe (PID: 1068)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 852)
- chrome.exe (PID: 1228)
- chrome.exe (PID: 1868)
- chrome.exe (PID: 2460)
- chrome.exe (PID: 2972)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 1924)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 2892)
Changes internet zones settings
- iexplore.exe (PID: 3096)
Manual execution by user
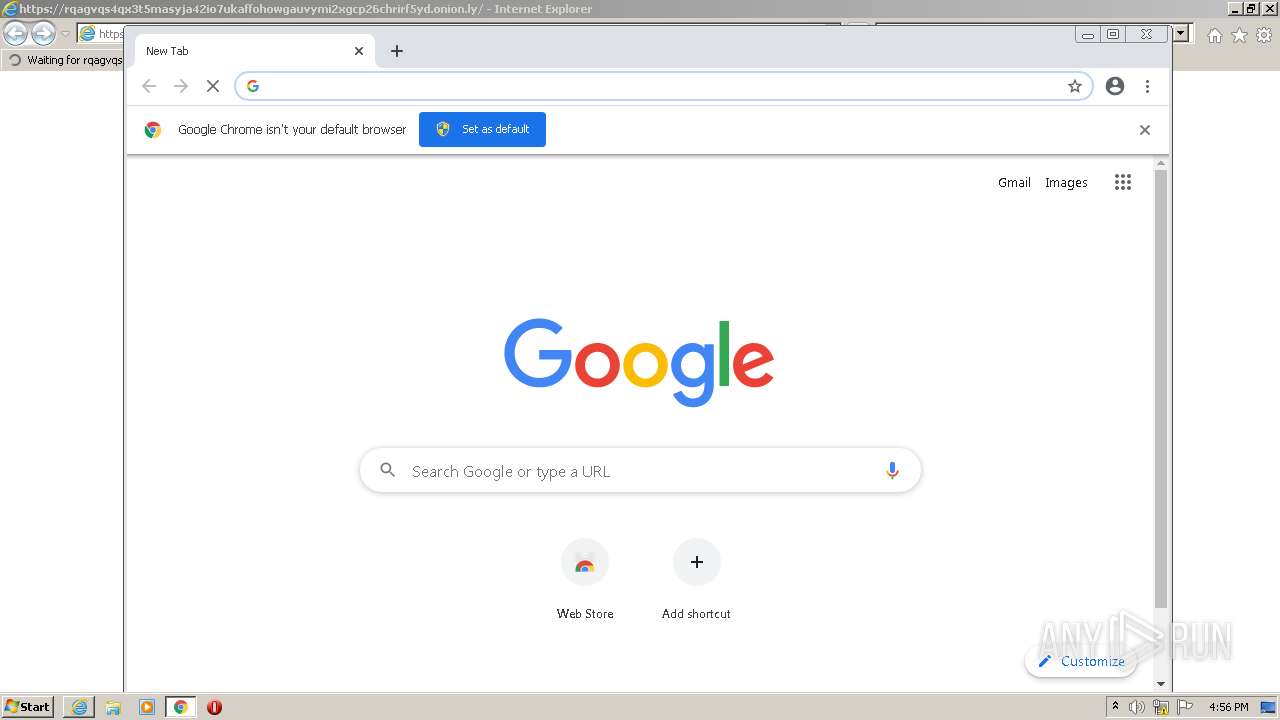
- chrome.exe (PID: 3948)
Checks Windows Trust Settings
- iexplore.exe (PID: 3540)
- iexplore.exe (PID: 3096)
Reads settings of System Certificates
- iexplore.exe (PID: 3540)
- iexplore.exe (PID: 3096)
- chrome.exe (PID: 3452)
Application launched itself
- iexplore.exe (PID: 3096)
- chrome.exe (PID: 3948)
Reads the hosts file
- chrome.exe (PID: 3452)
- chrome.exe (PID: 3948)
Dropped object may contain URL to Tor Browser
- iexplore.exe (PID: 3540)
- iexplore.exe (PID: 3096)
Reads internet explorer settings
- iexplore.exe (PID: 3540)
Changes settings of System certificates
- iexplore.exe (PID: 3096)
Reads the date of Windows installation
- chrome.exe (PID: 2216)
Creates files in the user directory
- iexplore.exe (PID: 3540)
- iexplore.exe (PID: 3096)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3096 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://rqagvqs4qx3t5masyja42io7ukaffohowgauvymi2xgcp26chrirf5yd.onion.ly" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3540 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3096 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f40d988,0x6f40d998,0x6f40d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,15772227013380894585,4844263669804566894,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1032 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1028,15772227013380894585,4844263669804566894,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1320 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,15772227013380894585,4844263669804566894,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,15772227013380894585,4844263669804566894,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,15772227013380894585,4844263669804566894,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,15772227013380894585,4844263669804566894,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2844 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
23 410
Read events
23 154
Write events
242
Delete events
14
Modification events
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30956111 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30956111 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
136
Text files
128
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-626967C0-F6C.pma | — | |
MD5:— | SHA256:— | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:3FDB18D87070B2AE92906AE57E13F89C | SHA256:06F9965BDAC3A1466AC6482EC2A745316B69F0038F132906847C392BAE020B78 | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:FD4D90869174EDF5BA2FE916C342D5C3 | SHA256:F46CE53688932DCD9A46DF6A6CB3C5930170A68C449CE41122899B07566261D3 | |||
| 3540 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:AD8E032271F02AF2A955CE10661CC3A8 | SHA256:D5081BF75D530E9336A6DA0F9142BC10F4D06368C365CF0E33F7C99B0F643CE8 | |||
| 3540 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:5E7962CF05681284C77222A7479C4631 | SHA256:A016A4E2ECB272361213661E5EEC58F375F5BE733962F316EF61D8D07B74C7A6 | |||
| 3540 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:9E260CE74A19BE571B84F239DC1A31A8 | SHA256:0B4DFCB39FCF4BBBDE5DF0A0B008BE31C9233D1E5A75C10A2F27A05D350D3EA6 | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:972E0A8AAFA1DC78FE6DFA40A8D46AAB | SHA256:27D399B01A129E5C8515A259E3CC7BD8BE5D260612D82D46AA33EAFB8093BC47 | |||
| 2744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1363fd.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a5b46d37-fc64-4782-9415-c2f3b740ea83.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:CDB4EE2AEA69CC6A83331BBE96DC2CAA9A299D21329EFB0336FC02A82E1839A8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
81
DNS requests
41
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3540 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEGxVq9vQB5LHnQcM2BGe1r8%3D | US | der | 727 b | whitelisted |
— | — | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
— | — | HEAD | 200 | 173.194.137.72:80 | http://r3---sn-aigzrn76.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=185.192.69.85&mm=28&mn=sn-aigzrn76&ms=nvh&mt=1651074740&mv=m&mvi=3&pl=24&rmhost=r2---sn-aigzrn76.gvt1.com&shardbypass=sd&smhost=r5---sn-aigzrn7s.gvt1.com | US | — | — | whitelisted |
— | — | HEAD | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
3540 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3540 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3096 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3096 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3540 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://zerossl.ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQILj%2F5BYz%2BinwYvRPv3x0WYHB6awQUyNl4aKLZGWjVPXLeXwo%2B3LWGhqYCEQDtWI1yIt5sllv2NfGtWSqP | US | der | 728 b | whitelisted |
3540 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 978 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3540 | iexplore.exe | 23.216.77.80:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
3096 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3540 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
3096 | iexplore.exe | 13.107.22.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3452 | chrome.exe | 142.250.186.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3540 | iexplore.exe | 209.141.38.247:443 | rqagvqs4qx3t5masyja42io7ukaffohowgauvymi2xgcp26chrirf5yd.onion.ly | FranTech Solutions | US | malicious |
3452 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 142.250.185.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 142.250.184.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3540 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rqagvqs4qx3t5masyja42io7ukaffohowgauvymi2xgcp26chrirf5yd.onion.ly |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
— | — | Potential Corporate Privacy Violation | ET POLICY .onion.ly Proxy domain in SNI |
— | — | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
— | — | Potential Corporate Privacy Violation | ET POLICY .onion.ly Proxy domain in SNI |
— | — | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
— | — | Potential Corporate Privacy Violation | ET POLICY .onion.ly Proxy domain in SNI |
— | — | Potential Corporate Privacy Violation | ET POLICY .onion.ly Proxy domain in SNI |
— | — | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
— | — | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |