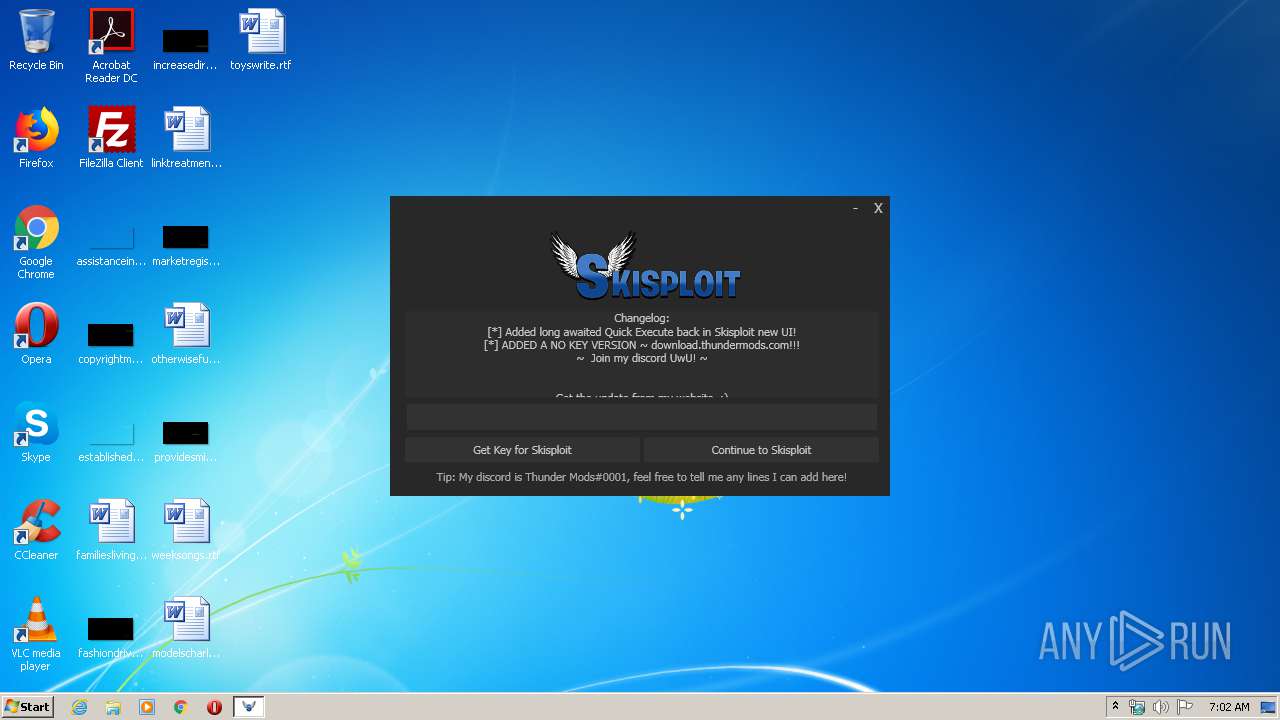
| File name: | Skisploit.exe |
| Full analysis: | https://app.any.run/tasks/23dff9f9-a1c1-4b20-b66c-6b3ca9cb817d |
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2020, 07:01:30 |
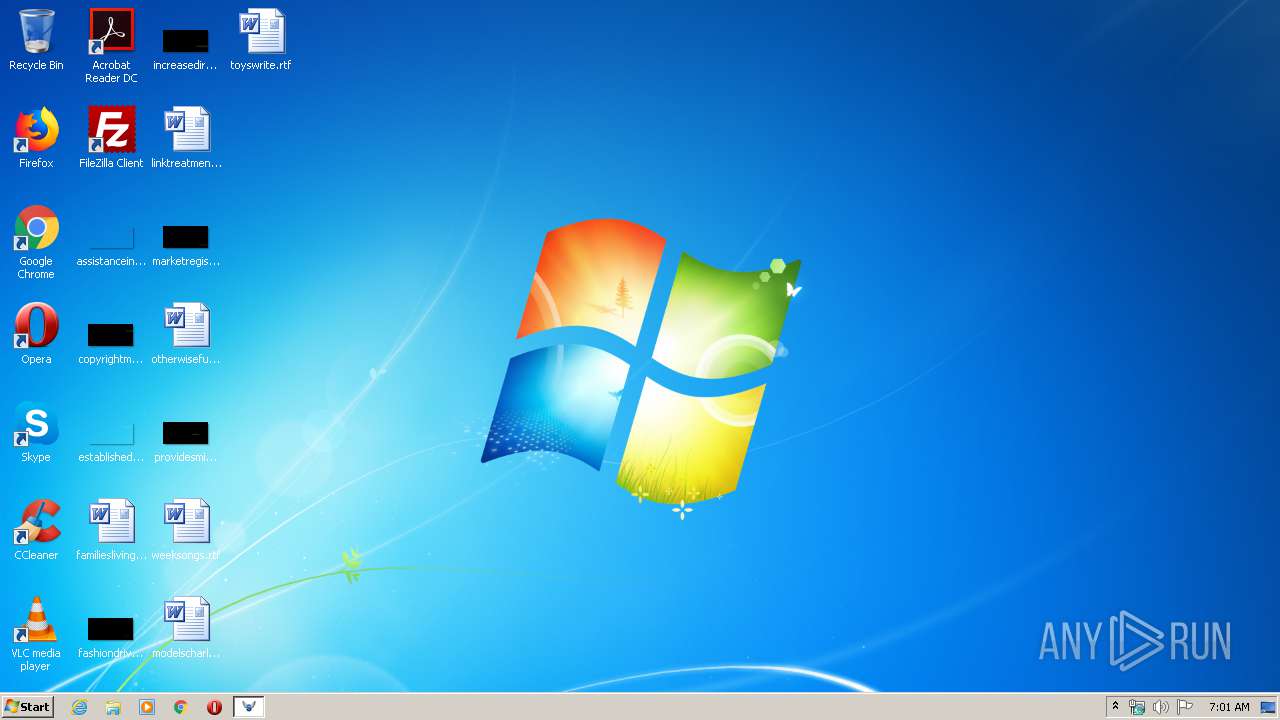
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 31FD10C212FDC962B136688814D6362D |
| SHA1: | 78BDA37C546257E23D575322C1A1B0D58D4AAAE0 |
| SHA256: | 967B4AA18CDFE1E6005A5BBAF5508651986CE238C961939D9CE0305BE187CDEA |
| SSDEEP: | 6144:2QIwUtiKBnuPTCSQaftmdYpjKYZMkSawenf7DwUtiKBNa:JIFiKBnuPjFlSawqf7DFiKBNa |
MALICIOUS
No malicious indicators.SUSPICIOUS
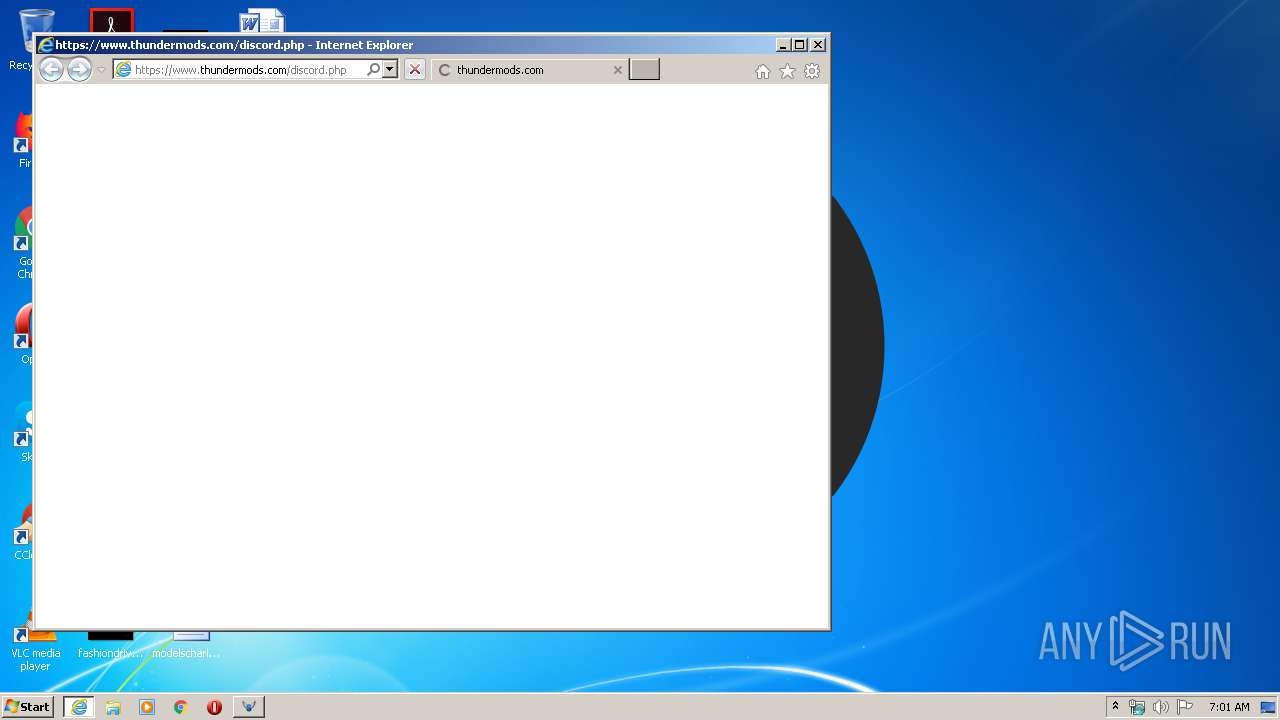
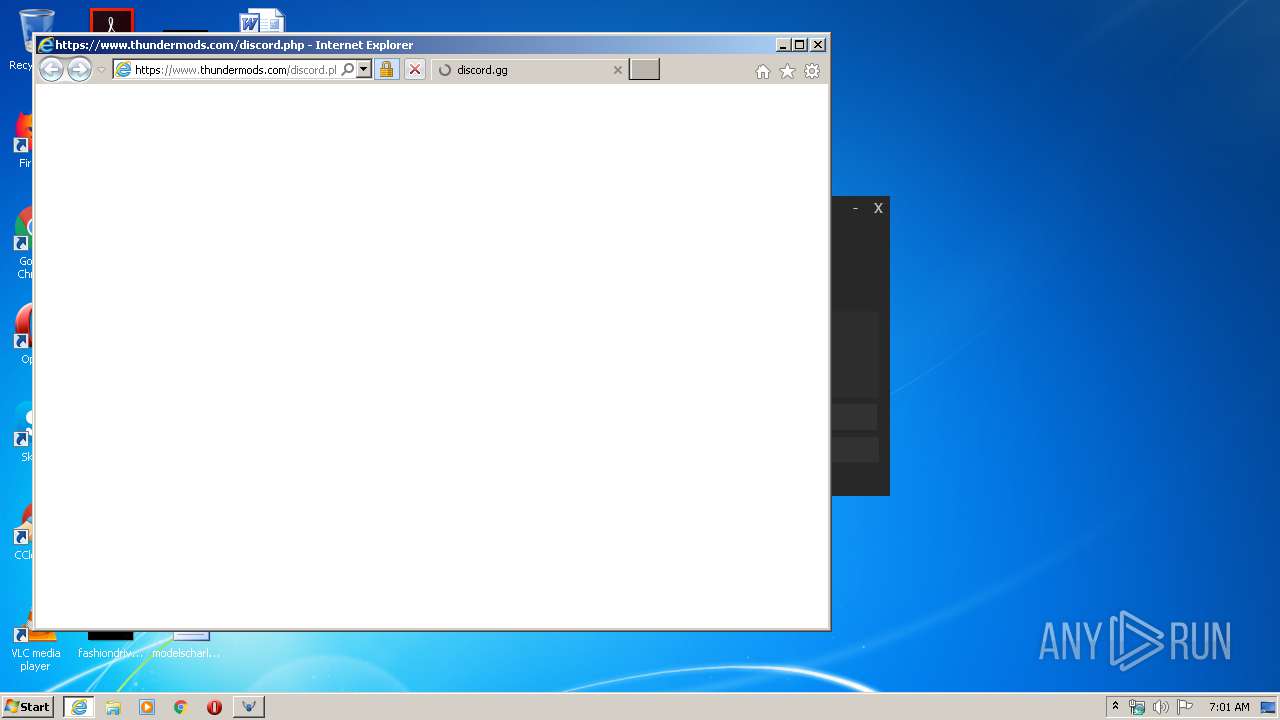
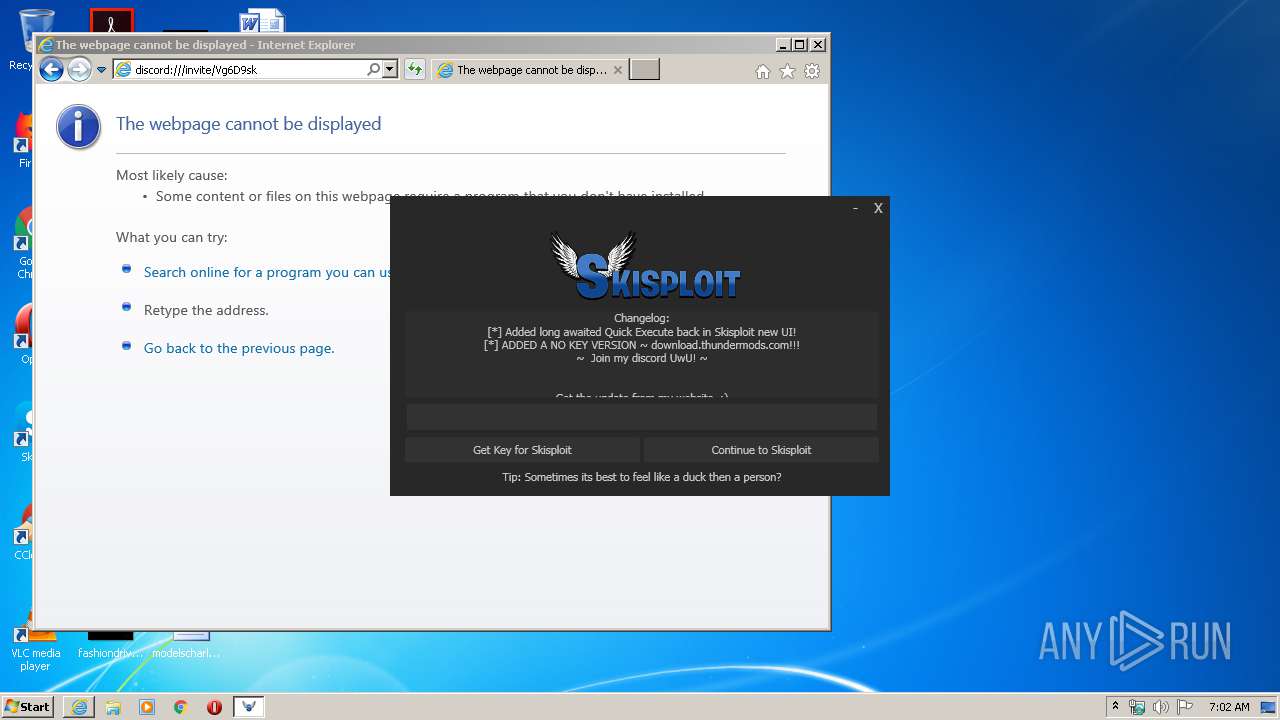
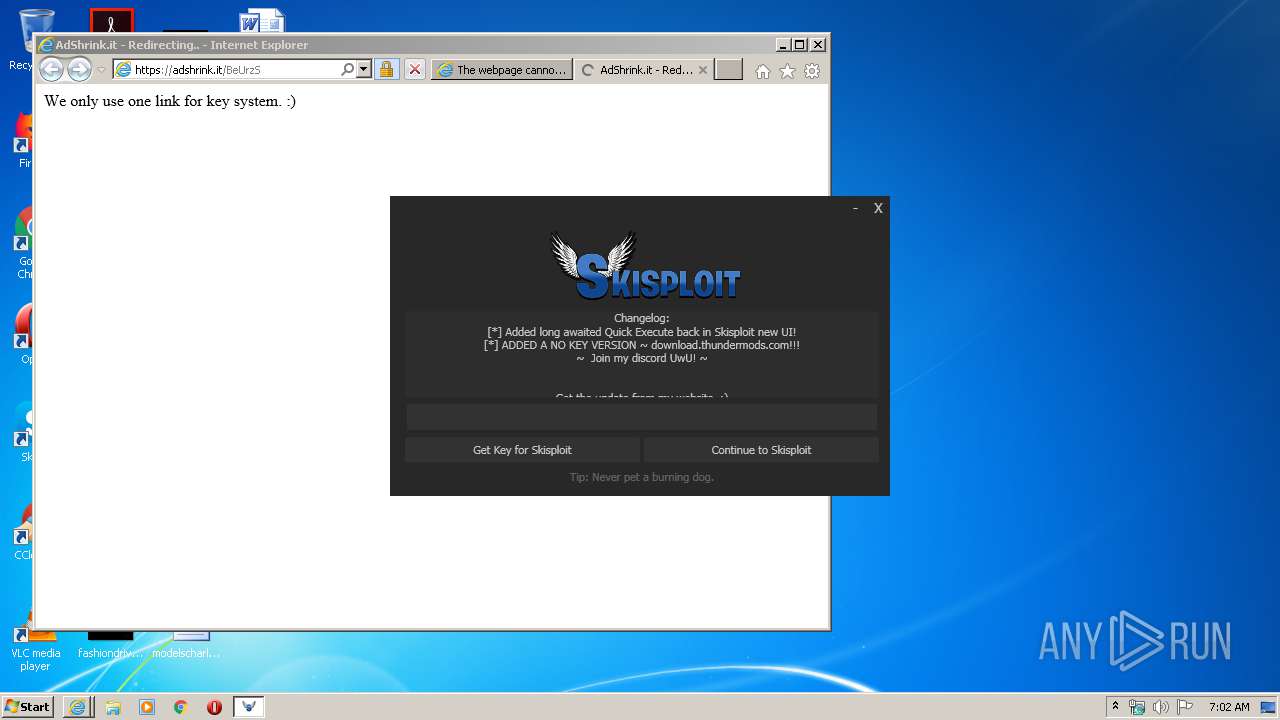
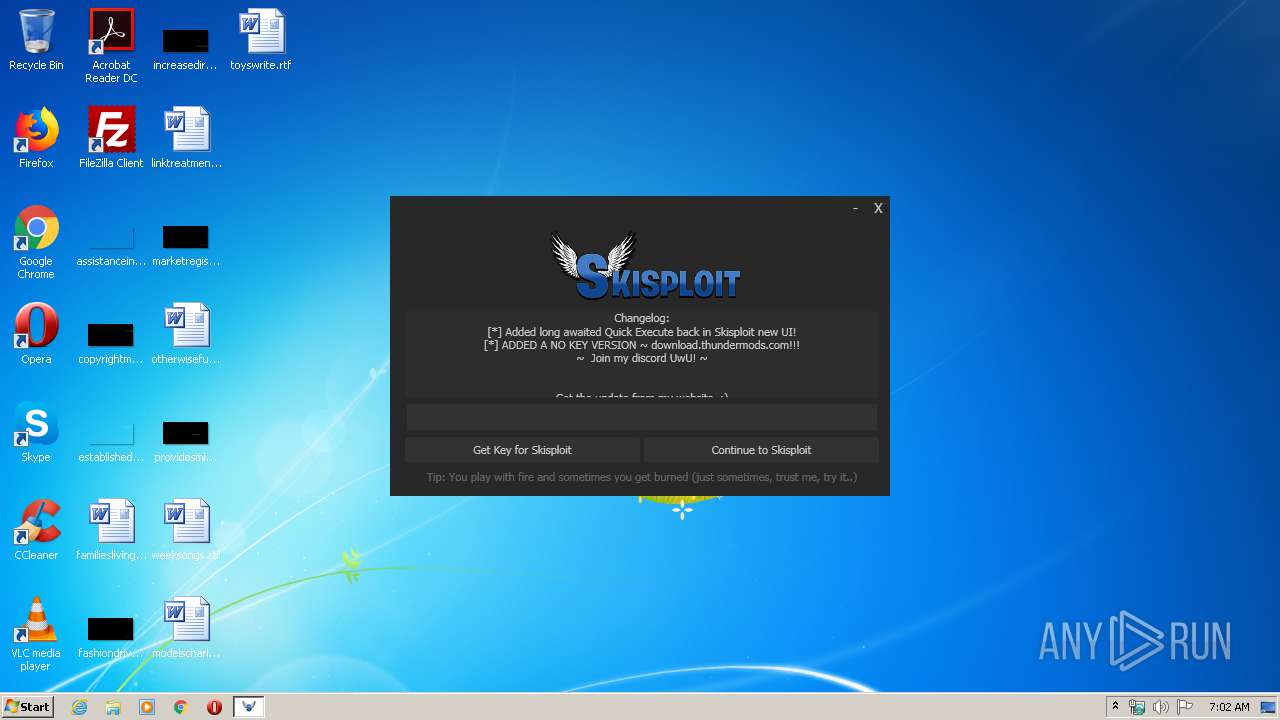
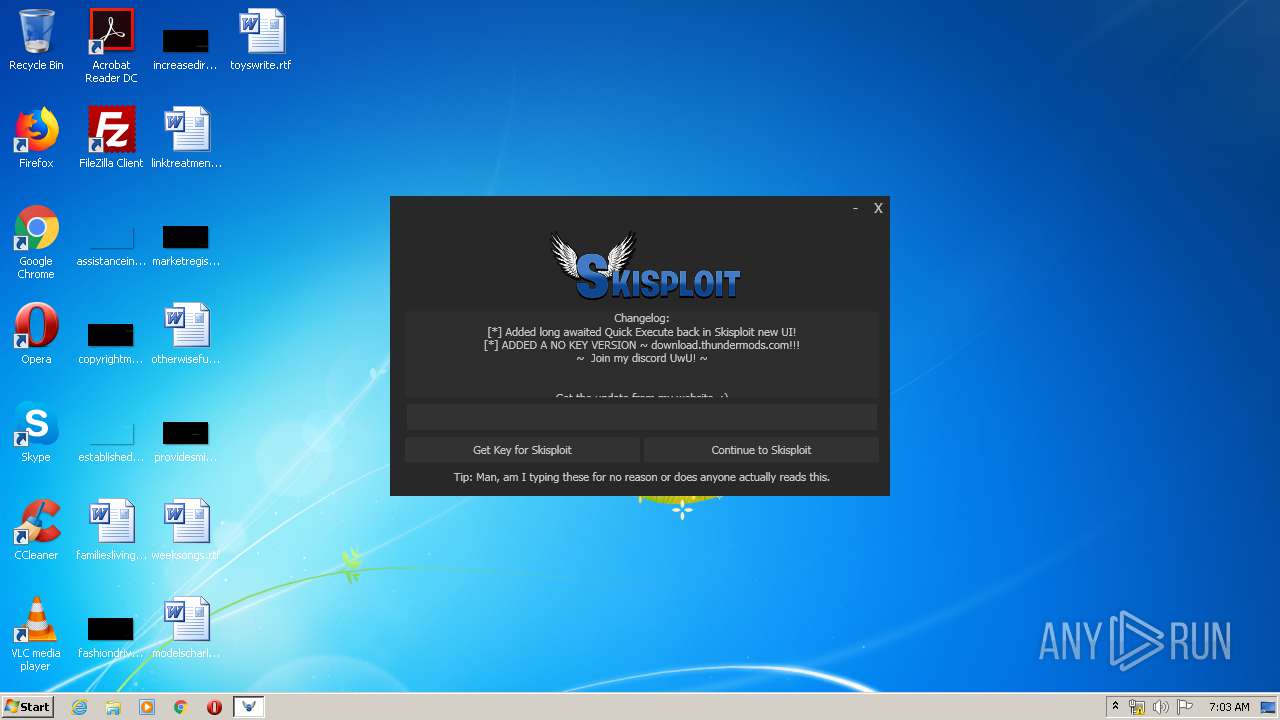
Starts Internet Explorer
- Skisploit.exe (PID: 3540)
Executable content was dropped or overwritten
- Skisploit.exe (PID: 3540)
Reads Environment values
- Skisploit.exe (PID: 3540)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 4008)
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 1504)
Changes internet zones settings
- iexplore.exe (PID: 4008)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1504)
- iexplore.exe (PID: 1232)
Reads internet explorer settings
- iexplore.exe (PID: 1504)
- iexplore.exe (PID: 1232)
Creates files in the user directory
- iexplore.exe (PID: 4008)
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 1504)
Application launched itself
- iexplore.exe (PID: 4008)
Reads settings of System Certificates
- iexplore.exe (PID: 1504)
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 4008)
Changes settings of System certificates
- iexplore.exe (PID: 4008)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2038:11:01 18:07:23+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 408064 |
| InitializedDataSize: | 140800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6581e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.1 |
| ProductVersionNumber: | 2.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Skisploit |
| FileVersion: | 2.0.0.1 |
| InternalName: | Skisploit.exe |
| LegalCopyright: | ThunderMods© 2020 |
| LegalTrademarks: | ZestyUIDev™ 2020 |
| OriginalFileName: | Skisploit.exe |
| ProductName: | Skisploit |
| ProductVersion: | 2.0.0.1 |
| AssemblyVersion: | 2.0.0.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Sep-1902 10:39:07 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Skisploit |
| FileVersion: | 2.0.0.1 |
| InternalName: | Skisploit.exe |
| LegalCopyright: | ThunderMods© 2020 |
| LegalTrademarks: | ZestyUIDev™ 2020 |
| OriginalFilename: | Skisploit.exe |
| ProductName: | Skisploit |
| ProductVersion: | 2.0.0.1 |
| Assembly Version: | 2.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 26-Sep-1902 10:39:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00063824 | 0x00063A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.92309 |
.rsrc | 0x00066000 | 0x00022288 | 0x00022400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.67125 |
.reloc | 0x0008A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.58185 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.87277 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.04019 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.24382 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.61552 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.79908 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1232 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4008 CREDAT:3675422 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4008 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3540 | "C:\Users\admin\AppData\Local\Temp\Skisploit.exe" | C:\Users\admin\AppData\Local\Temp\Skisploit.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Skisploit Exit code: 0 Version: 2.0.0.1 Modules
| |||||||||||||||
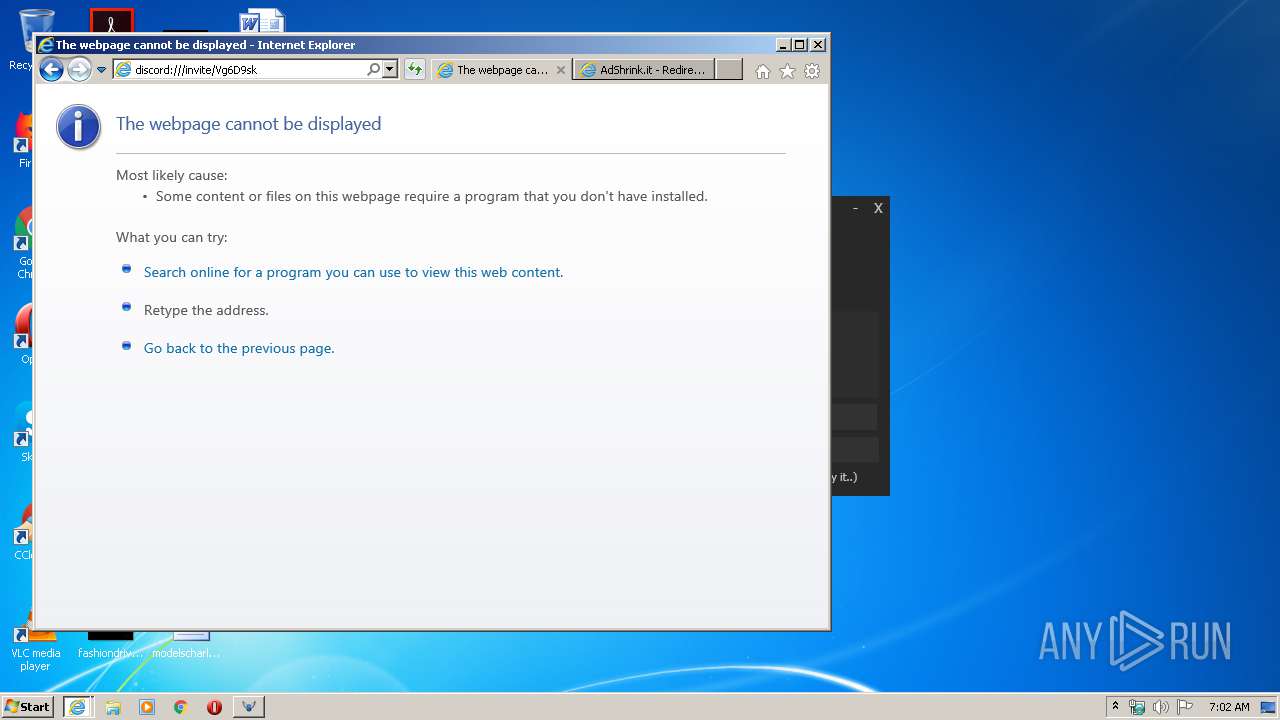
| 4008 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.thundermods.com/discord.php | C:\Program Files\Internet Explorer\iexplore.exe | Skisploit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
9 424
Read events
1 360
Write events
5 413
Delete events
2 651
Modification events
| (PID) Process: | (3540) Skisploit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Skisploit.exe | |||
| (PID) Process: | (3540) Skisploit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Skisploit_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3540) Skisploit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Skisploit_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3540) Skisploit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Skisploit_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3540) Skisploit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Skisploit_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3540) Skisploit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Skisploit_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3540) Skisploit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Skisploit_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3540) Skisploit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Skisploit_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3540) Skisploit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Skisploit_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3540) Skisploit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Skisploit_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
2
Suspicious files
63
Text files
97
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab86FB.tmp | — | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar86FC.tmp | — | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9EC3B71635F8BA3FC68DE181A104A0EF_F6C39EF89D8A3A72327D8412589658B2 | der | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\SKG85NY2.txt | text | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\1c02e551b13d04fe4126[1].js | text | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | der | |
MD5:— | SHA256:— | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | binary | |
MD5:— | SHA256:— | |||
| 3540 | Skisploit.exe | C:\Users\admin\AppData\Local\Temp\EasyExploits.dll | executable | |
MD5:5897E5BD1E922BF6009EF2C8ACC742BB | SHA256:B1FBF20BBDAEEAB2CDD9627B6EACAED781ED68253D4305E6E401CCAEF84966C9 | |||
| 1504 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\YNFN3F8O.txt | text | |
MD5:— | SHA256:— | |||
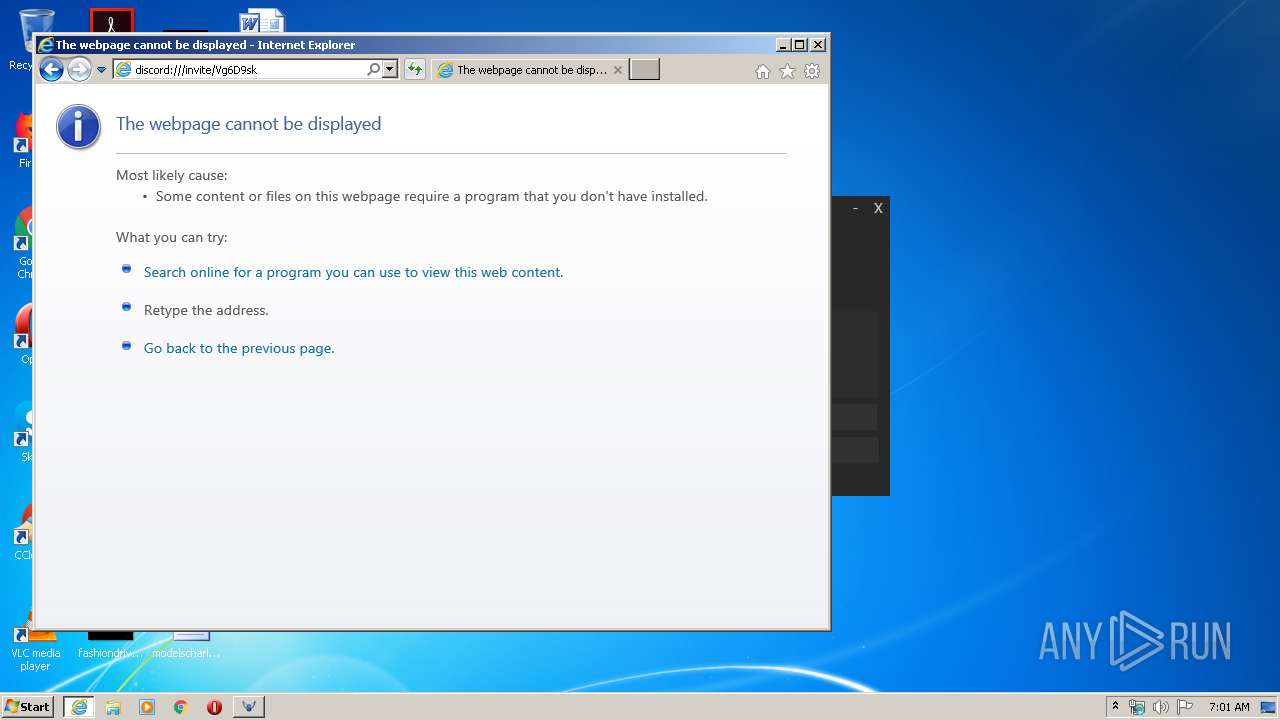
| 1504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Vg6D9sk[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
74
DNS requests
33
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1504 | iexplore.exe | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
1232 | iexplore.exe | GET | 200 | 2.21.242.245:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgNTPj8bgIxevWCKNR6jokXTcw%3D%3D | NL | der | 527 b | whitelisted |
3540 | Skisploit.exe | GET | 200 | 69.90.160.210:80 | http://api.thundermods.com/dlldownloadeasy.txt | CA | text | 93 b | malicious |
3540 | Skisploit.exe | GET | 200 | 69.90.160.210:80 | http://api.thundermods.com/loadingtips.txt | CA | text | 523 b | malicious |
1504 | iexplore.exe | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
3540 | Skisploit.exe | GET | 200 | 69.90.160.210:80 | http://api.thundermods.com/dlldownload.txt | CA | text | 90 b | malicious |
1232 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1232 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1232 | iexplore.exe | GET | 200 | 2.21.242.245:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgNTPj8bgIxevWCKNR6jokXTcw%3D%3D | NL | der | 527 b | whitelisted |
1232 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1504 | iexplore.exe | 69.90.160.210:443 | api.thundermods.com | Peer 1 Network (USA) Inc. | CA | suspicious |
3540 | Skisploit.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
1504 | iexplore.exe | 162.159.136.234:443 | discord.gg | Cloudflare Inc | — | shared |
4008 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4008 | iexplore.exe | 69.90.160.210:443 | api.thundermods.com | Peer 1 Network (USA) Inc. | CA | suspicious |
1504 | iexplore.exe | 2.21.242.187:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
1232 | iexplore.exe | 46.30.213.206:443 | www.shrink-service.it | One.com A/S | DK | suspicious |
1504 | iexplore.exe | 151.139.128.14:80 | ocsp.trust-provider.com | Highwinds Network Group, Inc. | US | suspicious |
1232 | iexplore.exe | 2.21.242.245:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | NL | whitelisted |
1504 | iexplore.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.thundermods.com |
| malicious |
cdn.discordapp.com |
| shared |
www.thundermods.com |
| malicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
discord.gg |
| whitelisted |
ocsp.trust-provider.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
discordapp.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report