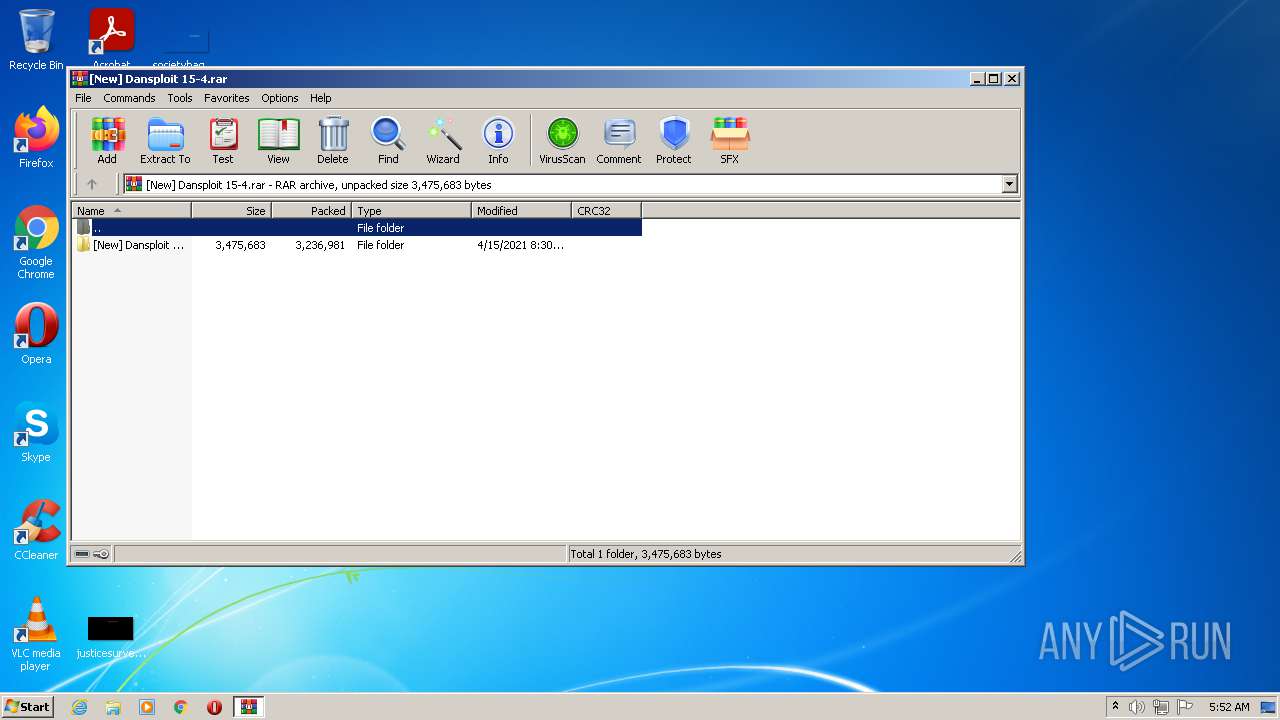
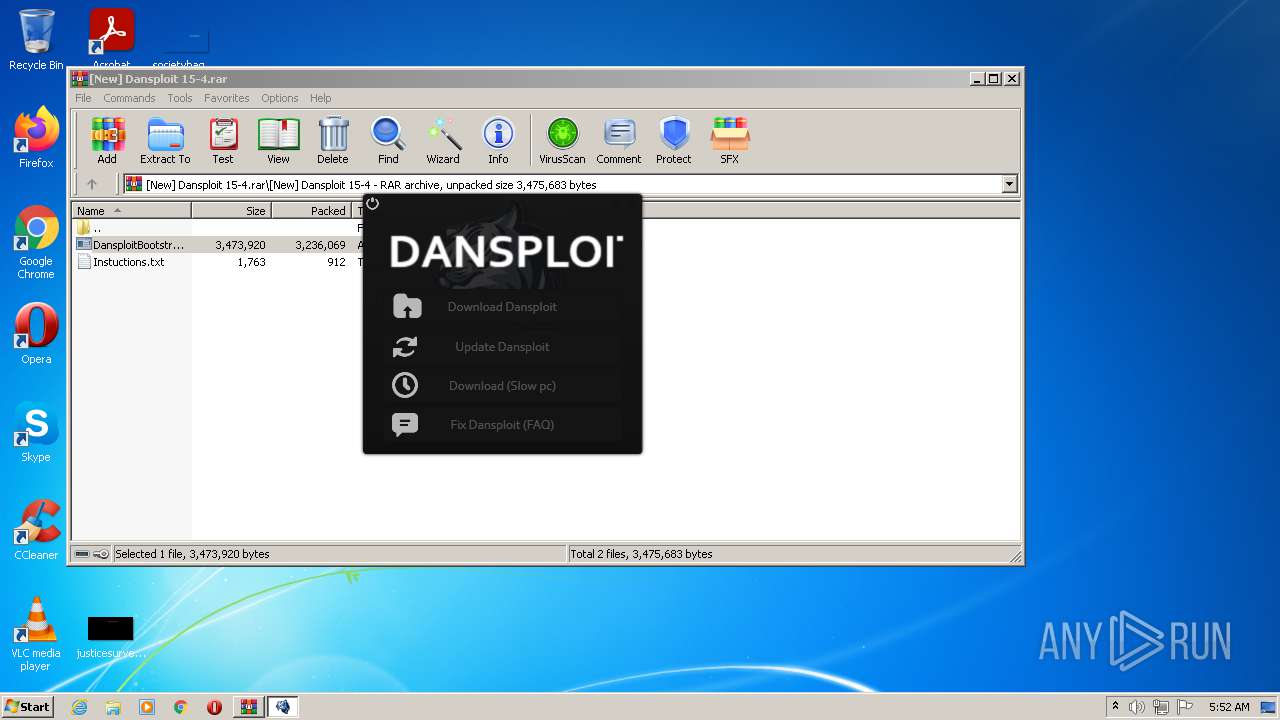
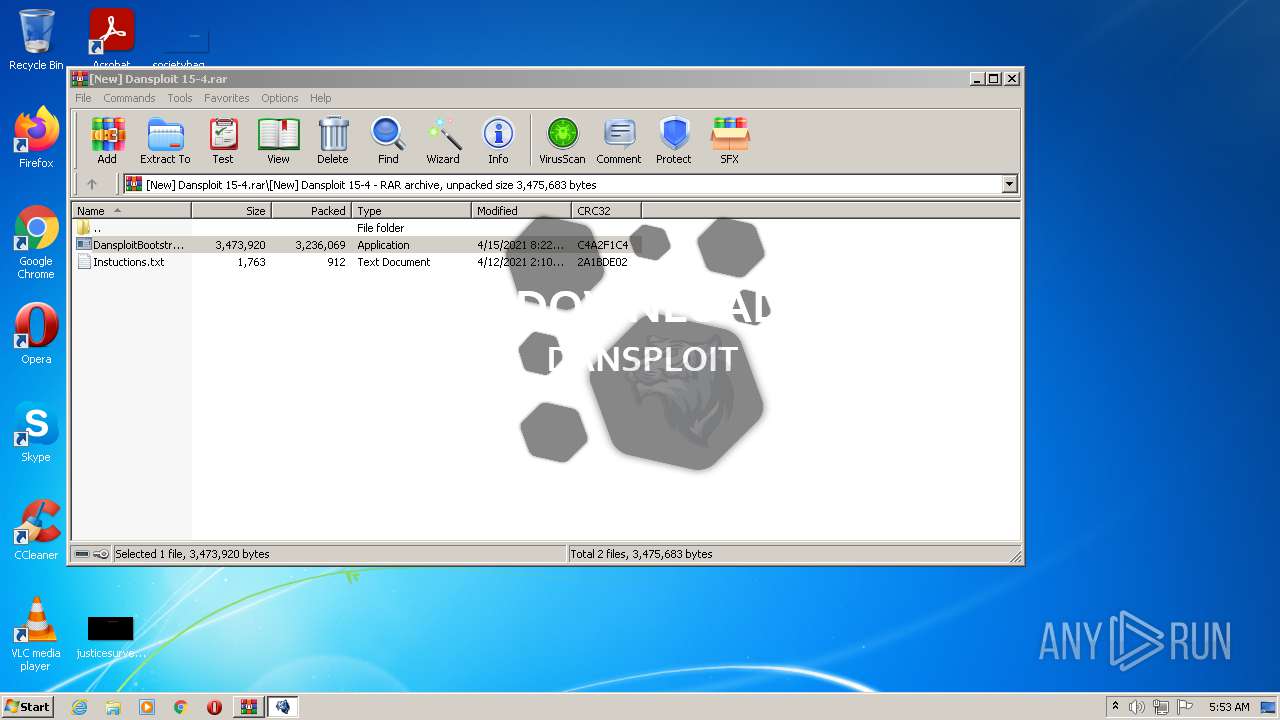
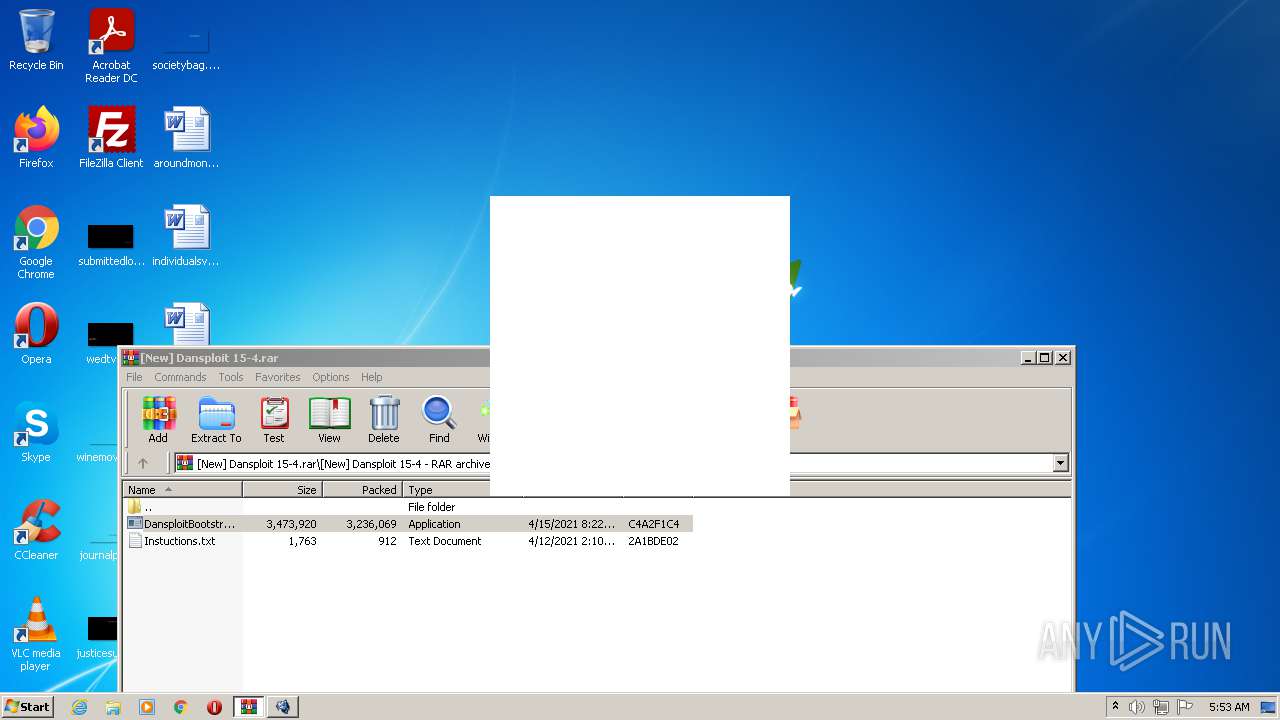
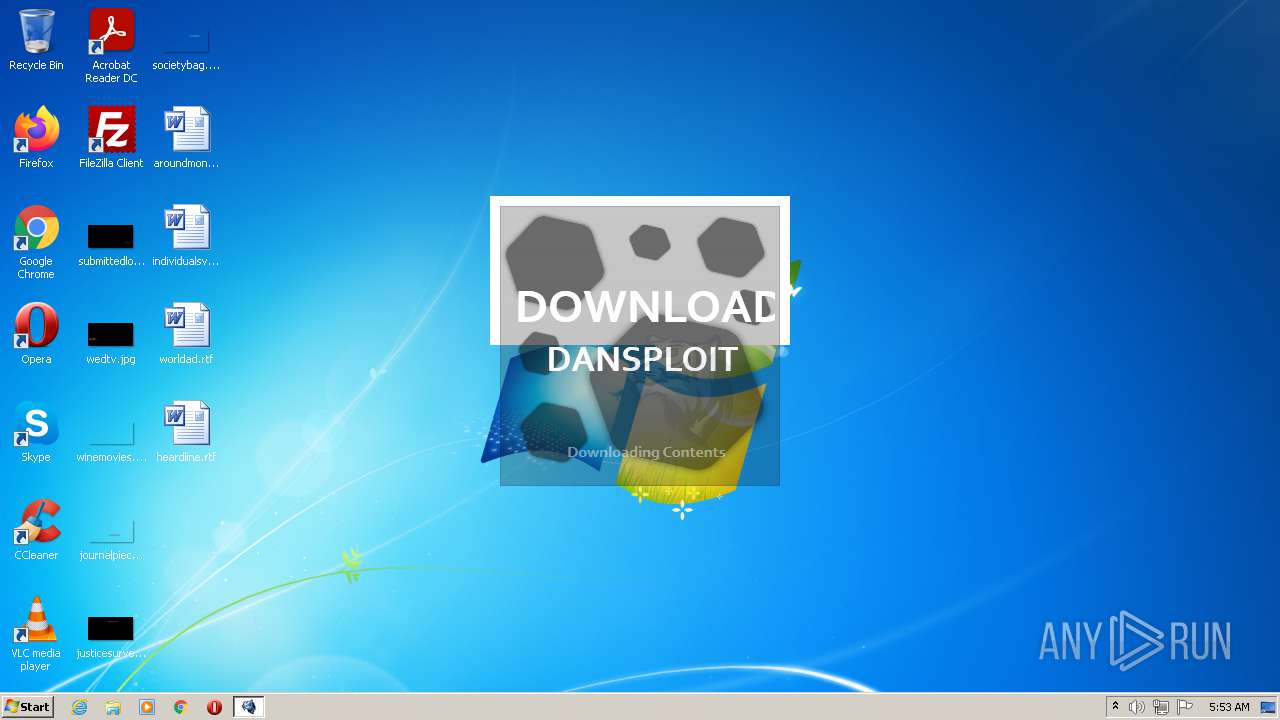
| File name: | [New] Dansploit 15-4.rar |
| Full analysis: | https://app.any.run/tasks/1a29b505-4294-4620-8377-a92d40974141 |
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2021, 04:52:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 530385709CF6536B095501ADA12CB9D4 |
| SHA1: | 2C56AC473501A163262FCE3E73BC0B8CA30809D2 |
| SHA256: | 967B018D194ABE8211CD3F440744D7F93DA6EC8B369BEB1A8444ADC667473DB1 |
| SSDEEP: | 98304:HcxOUuP9+PSydZp5aJrJvyzh/1lRWZee2Tg:7F1mjneJrJvyldCag |
MALICIOUS
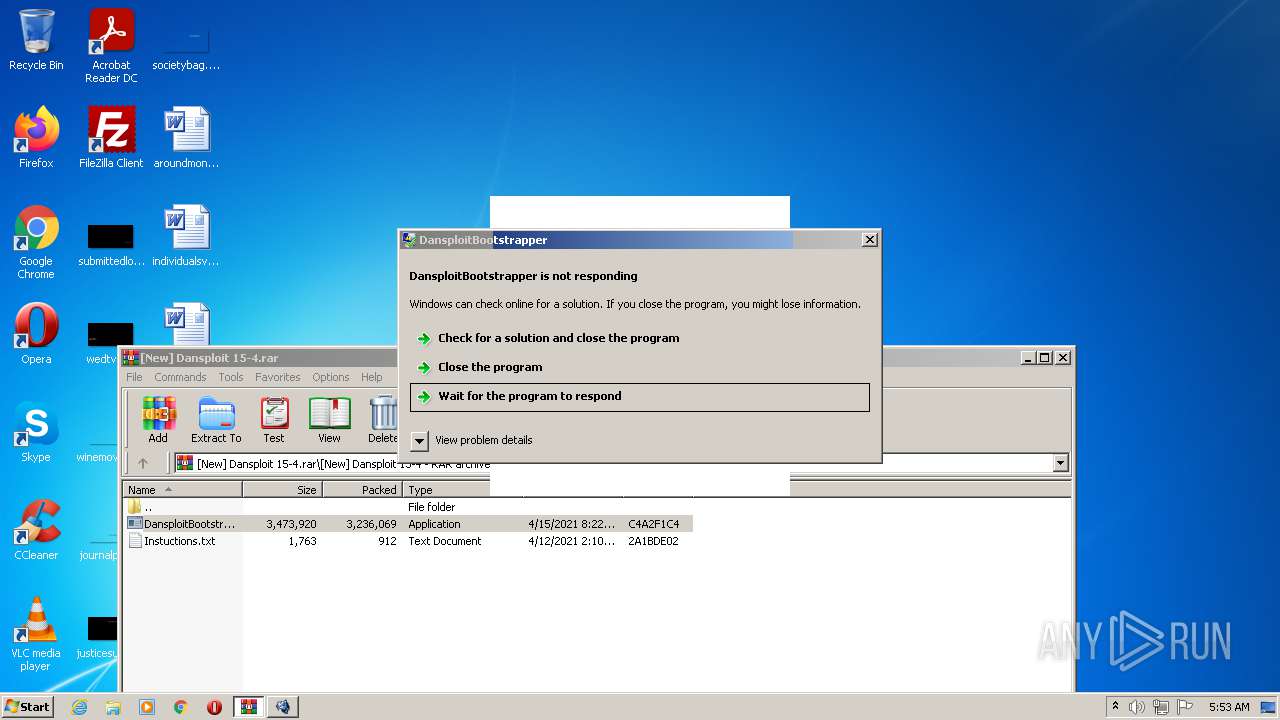
Application was dropped or rewritten from another process
- DansploitBootstrapper.exe (PID: 3364)
SUSPICIOUS
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2604)
- DansploitBootstrapper.exe (PID: 3364)
Checks supported languages
- DansploitBootstrapper.exe (PID: 3364)
- WinRAR.exe (PID: 2604)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2604)
- DansploitBootstrapper.exe (PID: 3364)
Reads the computer name
- WinRAR.exe (PID: 2604)
- DansploitBootstrapper.exe (PID: 3364)
Drops a file that was compiled in debug mode
- DansploitBootstrapper.exe (PID: 3364)
Reads Environment values
- DansploitBootstrapper.exe (PID: 3364)
Drops a file with too old compile date
- DansploitBootstrapper.exe (PID: 3364)
INFO
Checks supported languages
- WISPTIS.EXE (PID: 116)
Reads the computer name
- WISPTIS.EXE (PID: 116)
Reads settings of System Certificates
- DansploitBootstrapper.exe (PID: 3364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | DansploitBootstrapper.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 24 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
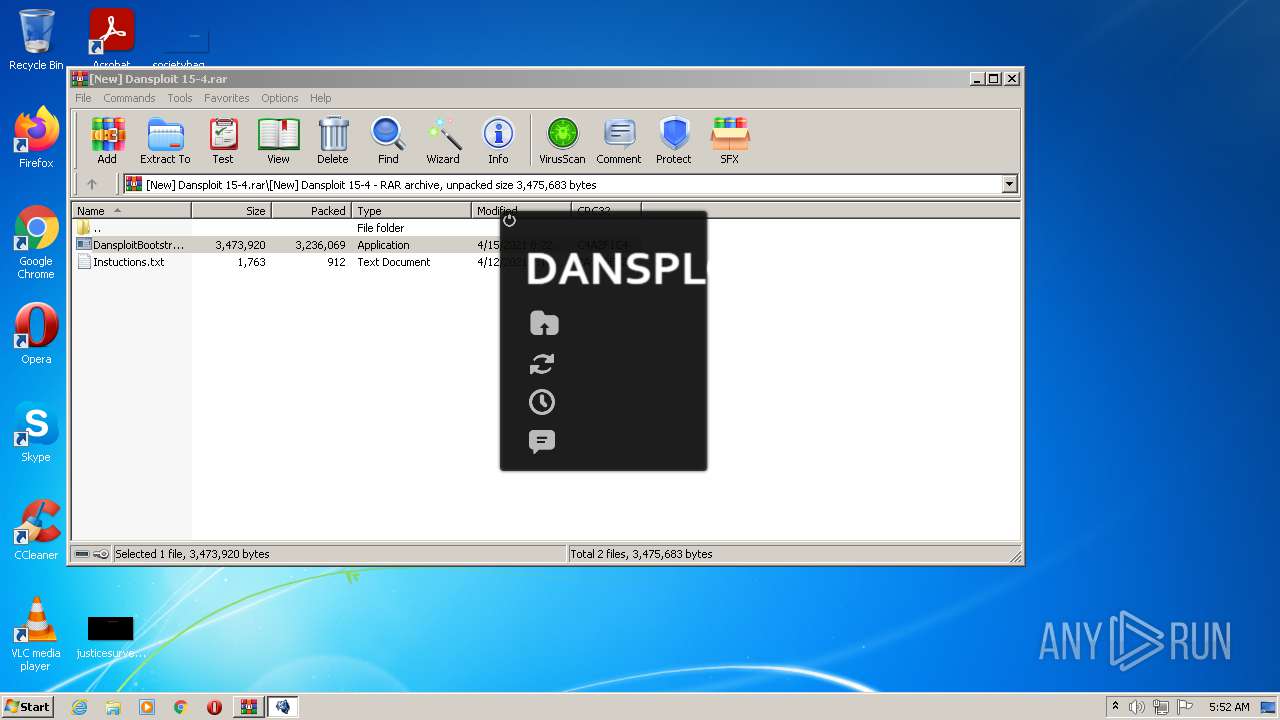
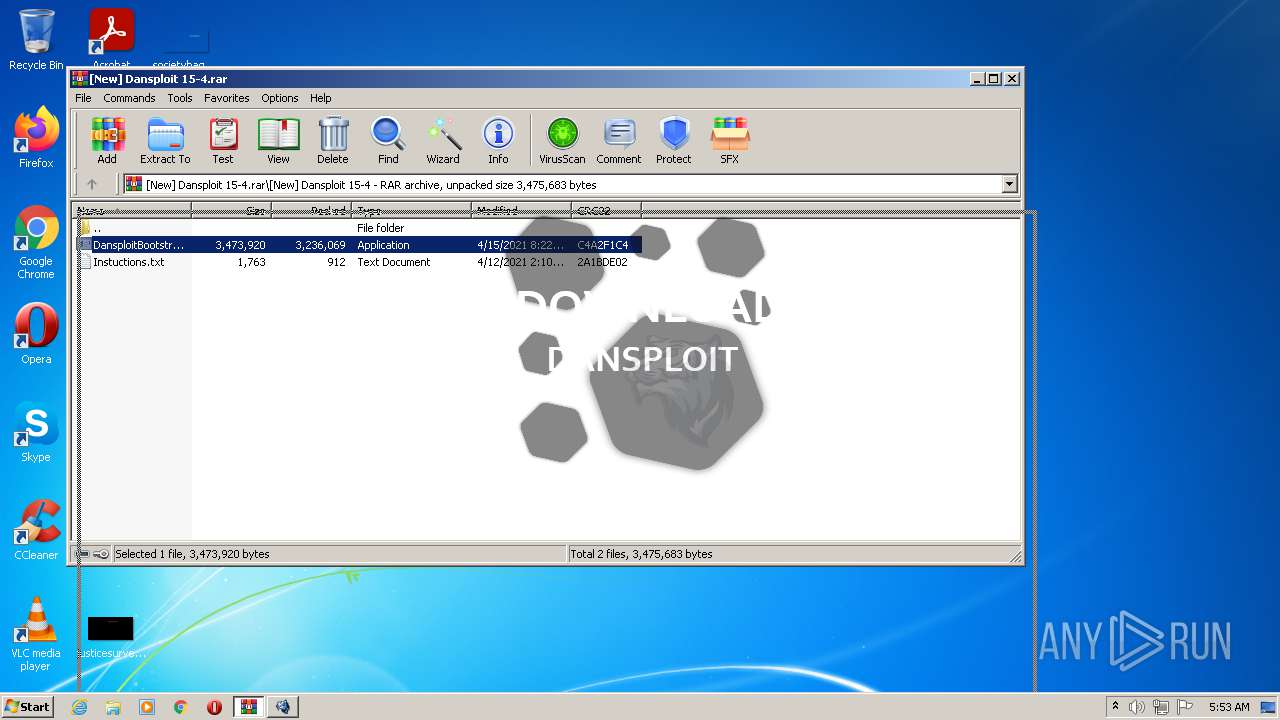
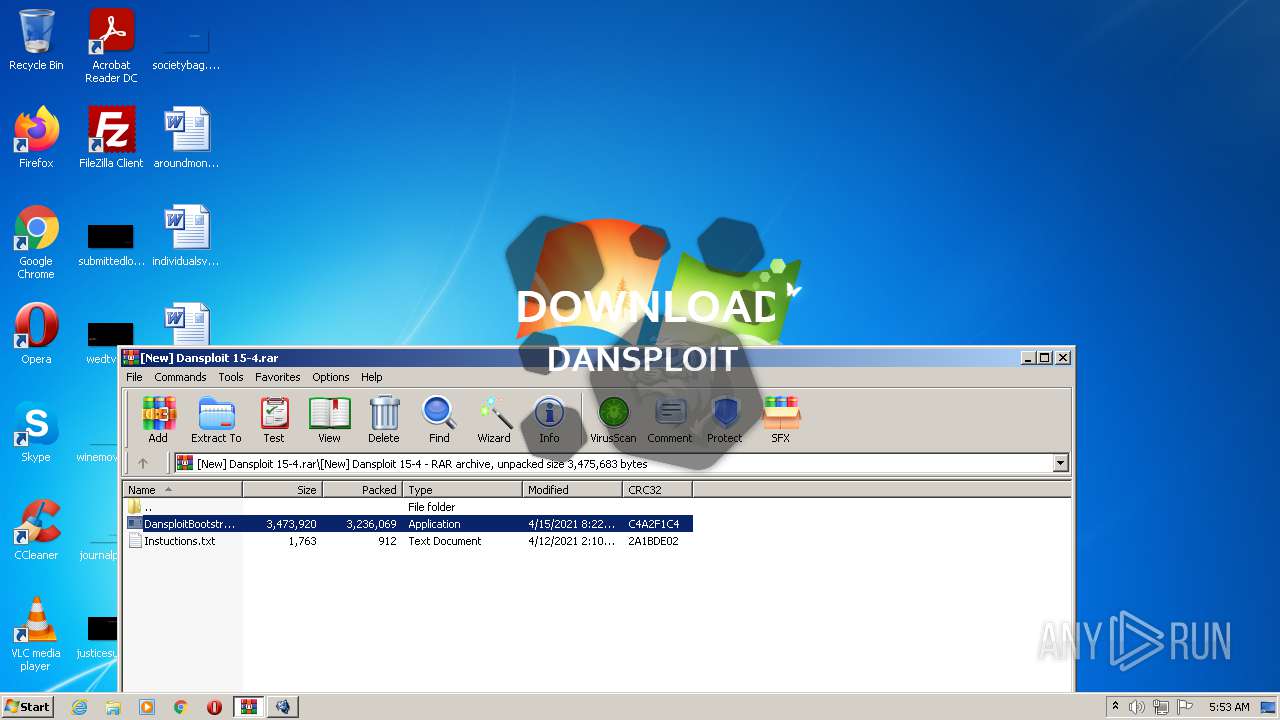
| 2604 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\[New] Dansploit 15-4.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
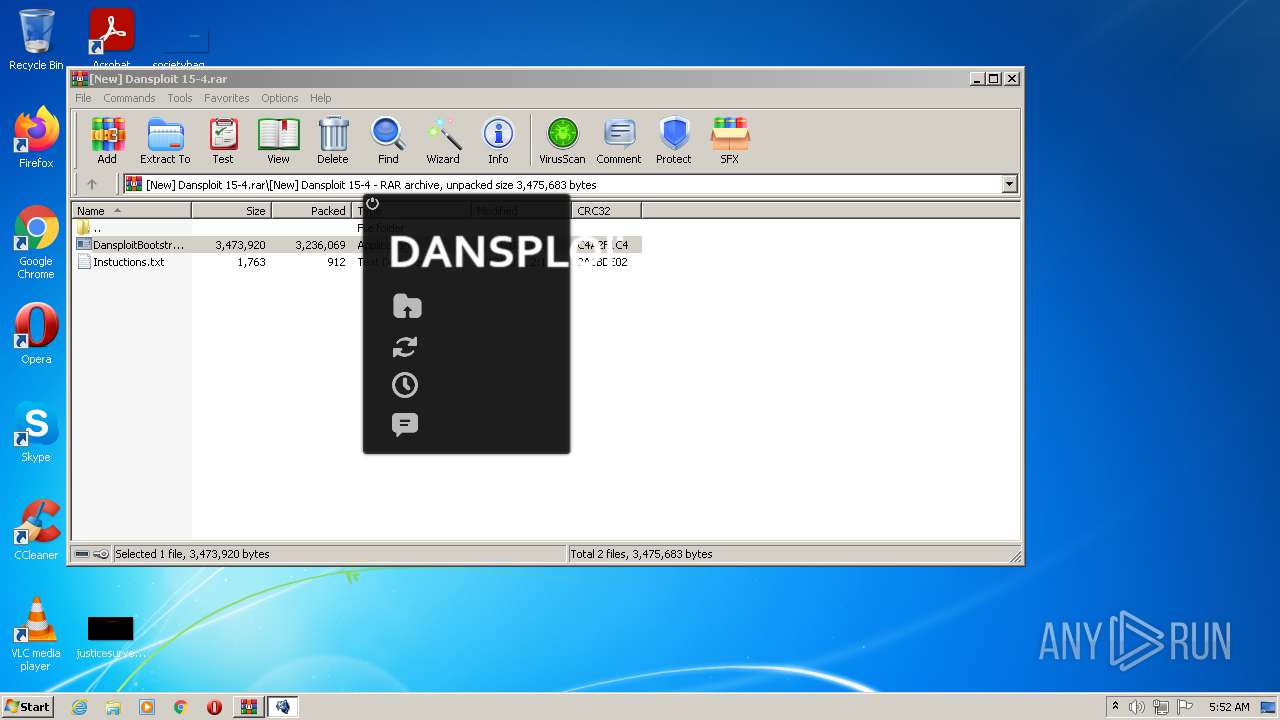
| 3364 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\DansploitBootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\DansploitBootstrapper.exe | WinRAR.exe | ||||||||||||
User: admin Company: DanielNiewold Integrity Level: MEDIUM Description: DansploitBootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3516 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | DansploitBootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 436
Read events
4 332
Write events
104
Delete events
0
Modification events
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\[New] Dansploit 15-4.rar | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
9
Suspicious files
0
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2604 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\Instuctions.txt | text | |
MD5:— | SHA256:— | |||
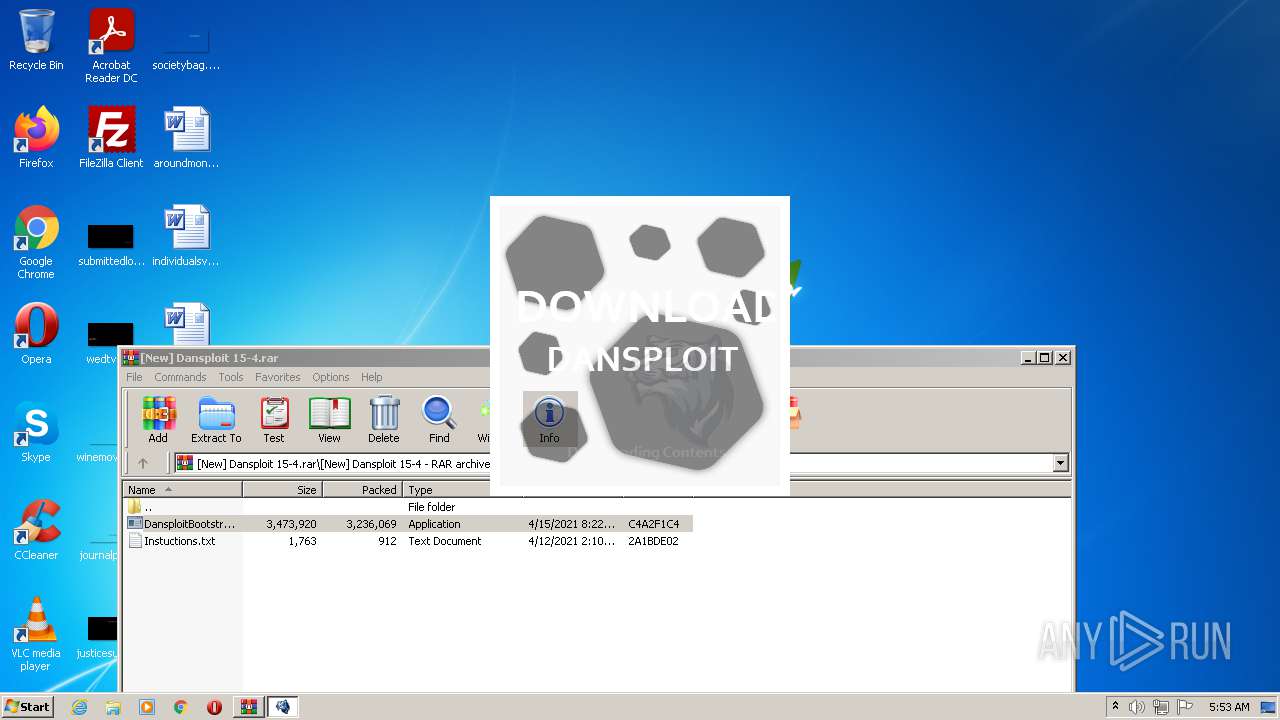
| 3364 | DansploitBootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\Dansploit\bin\Minecraft\Dansploit\Dansploit.jar | java | |
MD5:— | SHA256:— | |||
| 3364 | DansploitBootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\Dansploit\easyexploits.dll | executable | |
MD5:— | SHA256:— | |||
| 3364 | DansploitBootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\Dansploit\bin\Minecraft\Dansploit\Dansploit.json | text | |
MD5:— | SHA256:— | |||
| 3364 | DansploitBootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\Dansploit\Scripts\Fly Press E.txt | text | |
MD5:— | SHA256:— | |||
| 3364 | DansploitBootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\Dansploit\Scripts\Phantom_Forces_GUI_OP.txt | text | |
MD5:— | SHA256:— | |||
| 3364 | DansploitBootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\Dansploit\Dll's\DansploitCSGO.dll | executable | |
MD5:— | SHA256:— | |||
| 3364 | DansploitBootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\Dansploit\bin\CSGhost_v2.4.exe | executable | |
MD5:— | SHA256:— | |||
| 3364 | DansploitBootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\Dansploit\Scripts\CMD-X.txt | text | |
MD5:— | SHA256:— | |||
| 2604 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2604.38717\[New] Dansploit 15-4\DansploitBootstrapper.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3364 | DansploitBootstrapper.exe | 162.159.129.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
3364 | DansploitBootstrapper.exe | 104.23.98.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
cdn.discordapp.com |
| shared |