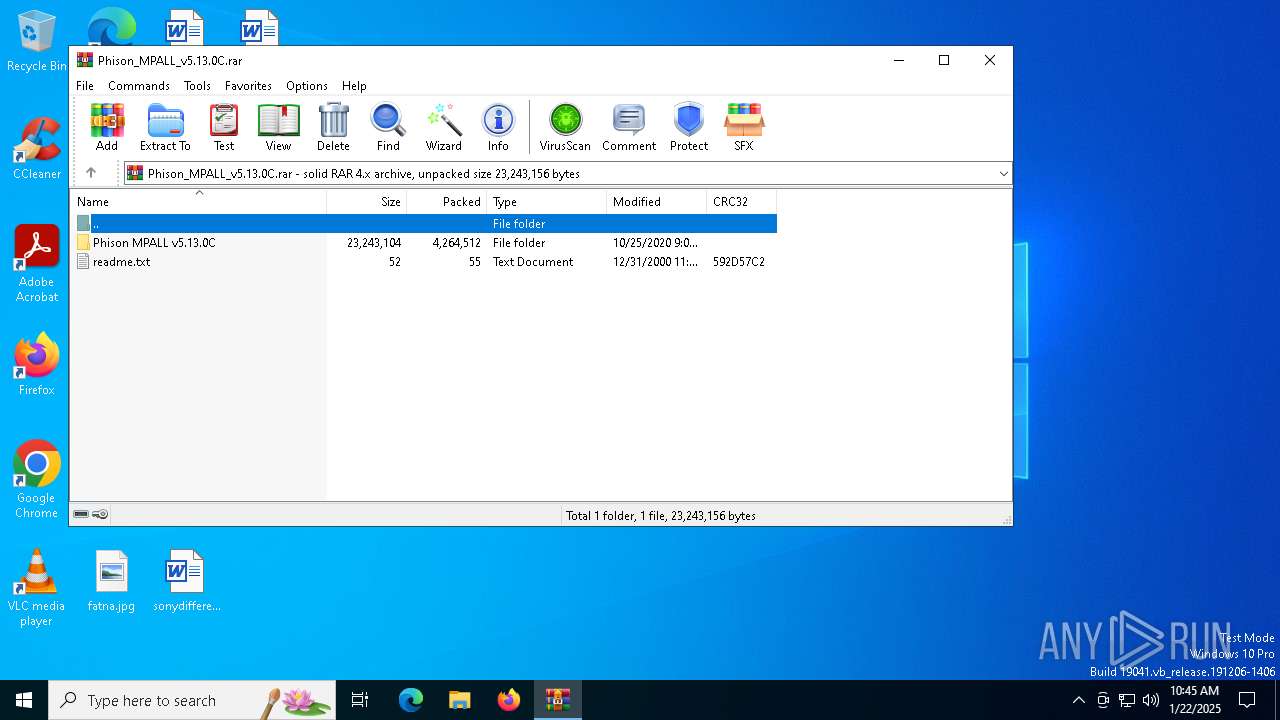
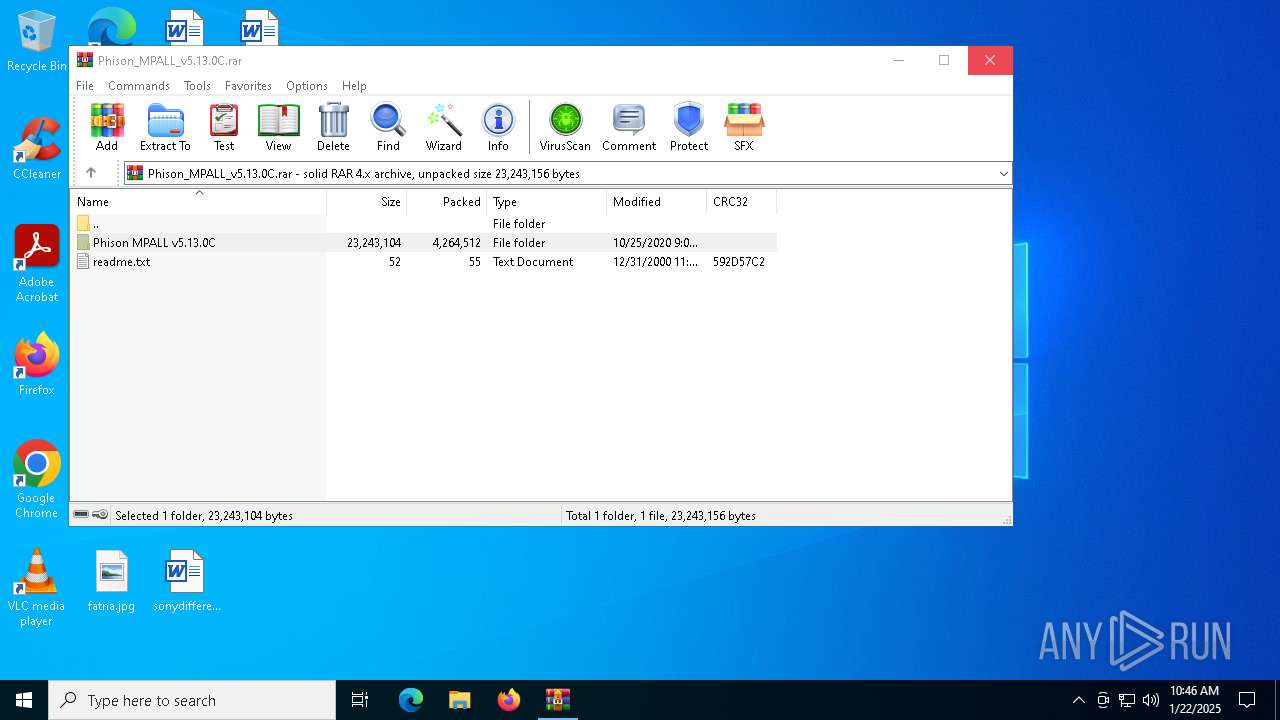
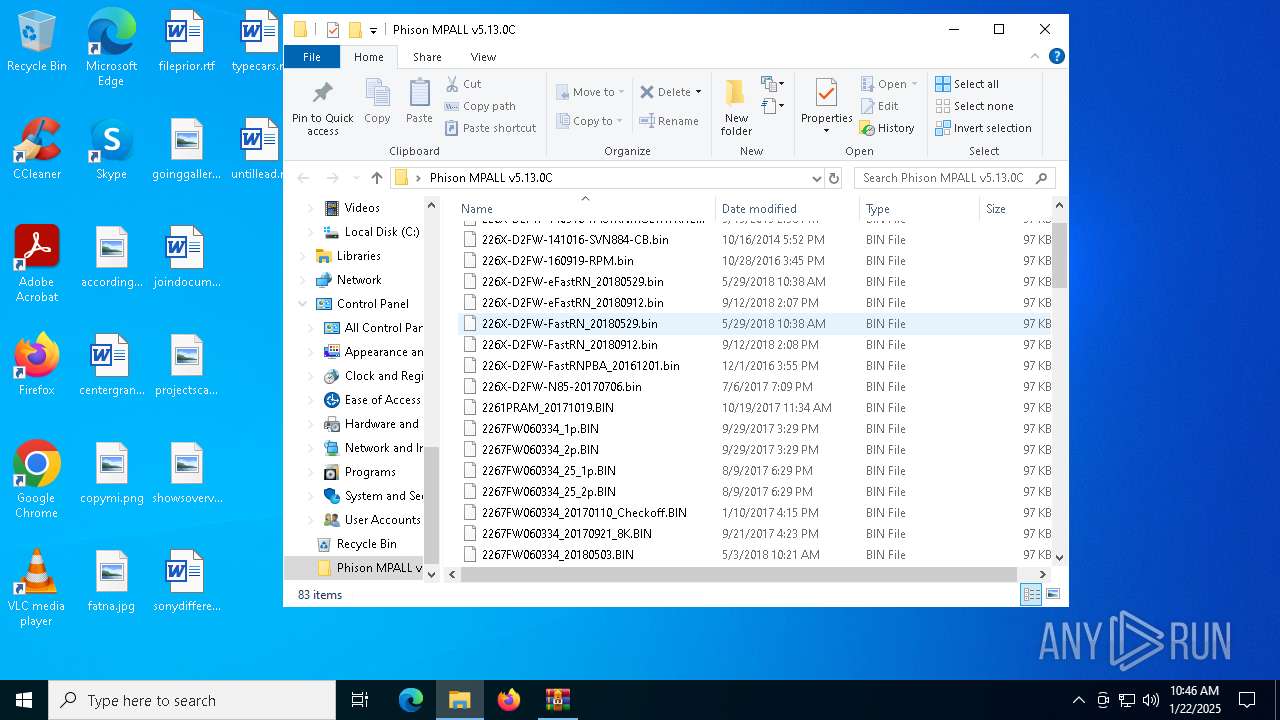
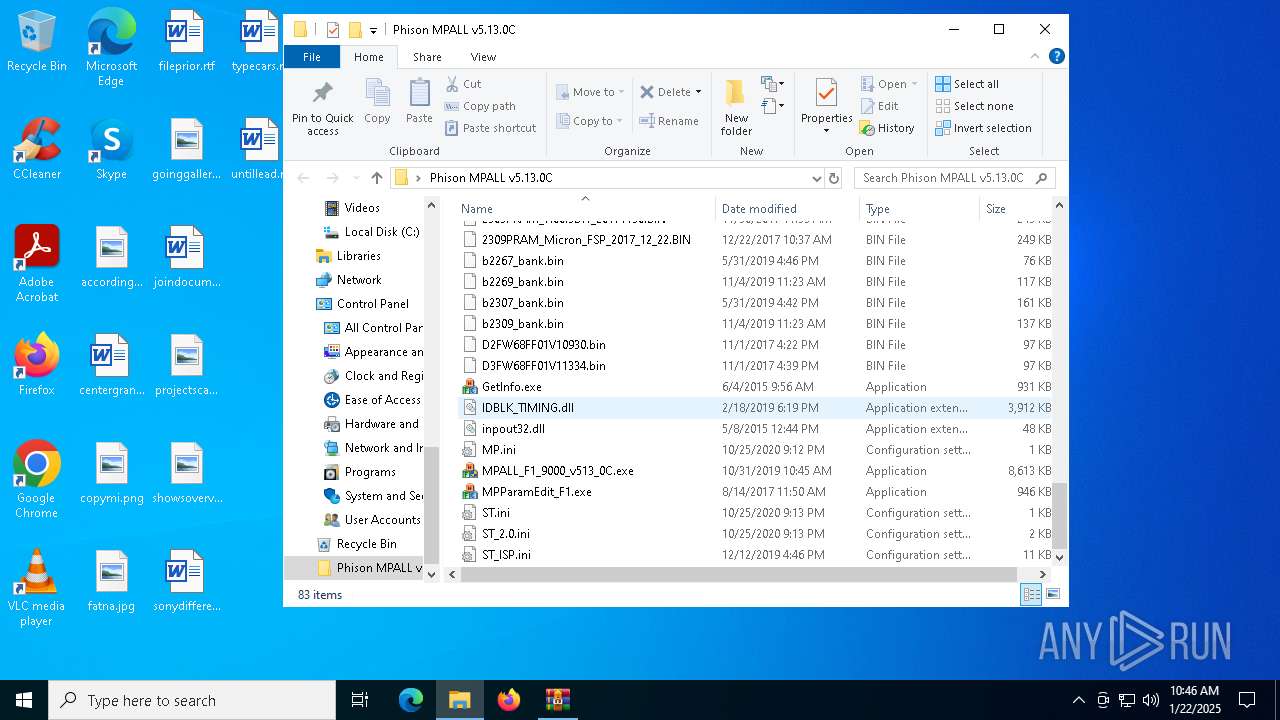
| File name: | Phison_MPALL_v5.13.0C.rar |
| Full analysis: | https://app.any.run/tasks/3fee59f4-c6ab-4cd1-88cc-bf433869f4b5 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2025, 10:45:25 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32, flags: Solid |
| MD5: | 6DEB214436E047E6F736111F97C394B9 |
| SHA1: | AB9FBDCAC8DC55FD646CBAD4996B98F53A2C2066 |
| SHA256: | 9670E21A30A78AF57E5C4B4A702DA1E8E8BF587CBC66A837B9E172F3B1A1182B |
| SSDEEP: | 98304:JmKmjvLKc2HvGGJ0PfMzd12let30/zSMu0IeJkdwM9p3poTqpXqFJYAXOSrY0SWw:Y4PYM1ziN3lP9B9M+e |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the driver directory
- MPALL_F1_9000_v513_0C.exe (PID: 5748)
Creates or modifies Windows services
- MPALL_F1_9000_v513_0C.exe (PID: 5748)
Process drops legitimate windows executable
- MPALL_F1_9000_v513_0C.exe (PID: 5748)
Executable content was dropped or overwritten
- MPALL_F1_9000_v513_0C.exe (PID: 5748)
Drops a system driver (possible attempt to evade defenses)
- MPALL_F1_9000_v513_0C.exe (PID: 5748)
INFO
The sample compiled with chinese language support
- WinRAR.exe (PID: 6352)
The process uses the downloaded file
- WinRAR.exe (PID: 6352)
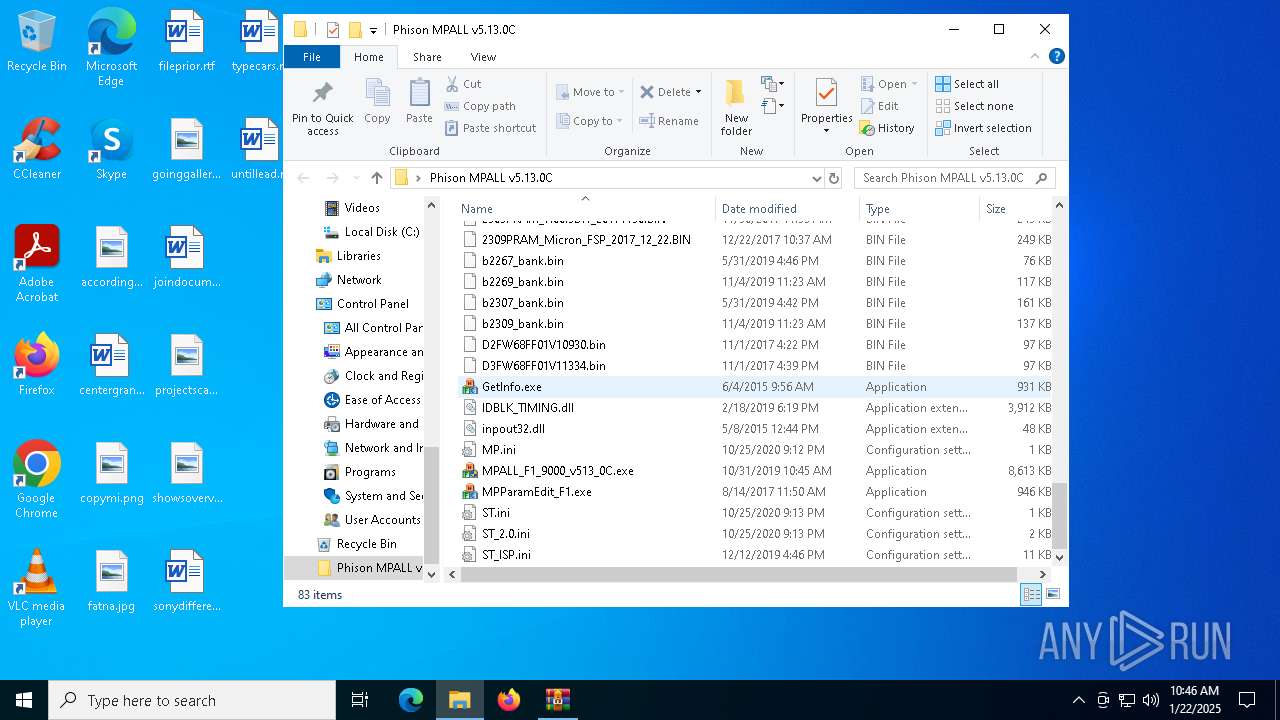
Checks supported languages
- GetInfo.exe (PID: 1448)
- MPALL_F1_9000_v513_0C.exe (PID: 5748)
The sample compiled with english language support
- WinRAR.exe (PID: 6352)
- MPALL_F1_9000_v513_0C.exe (PID: 5748)
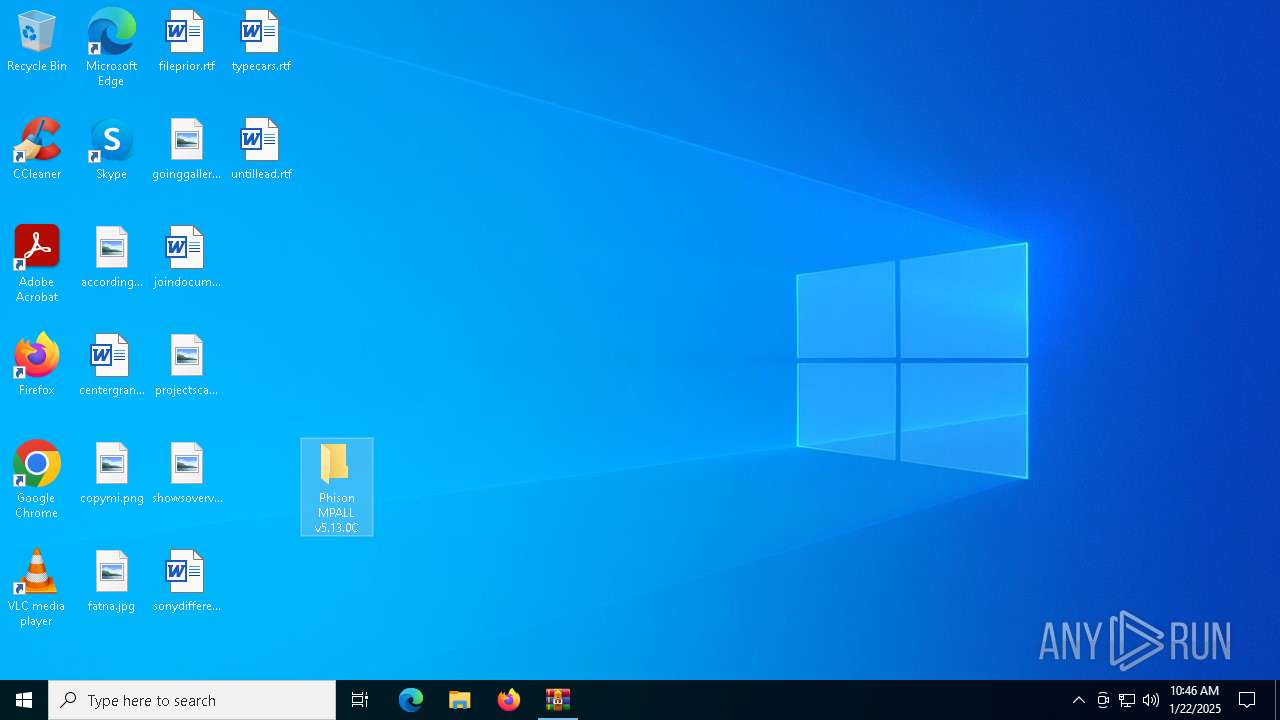
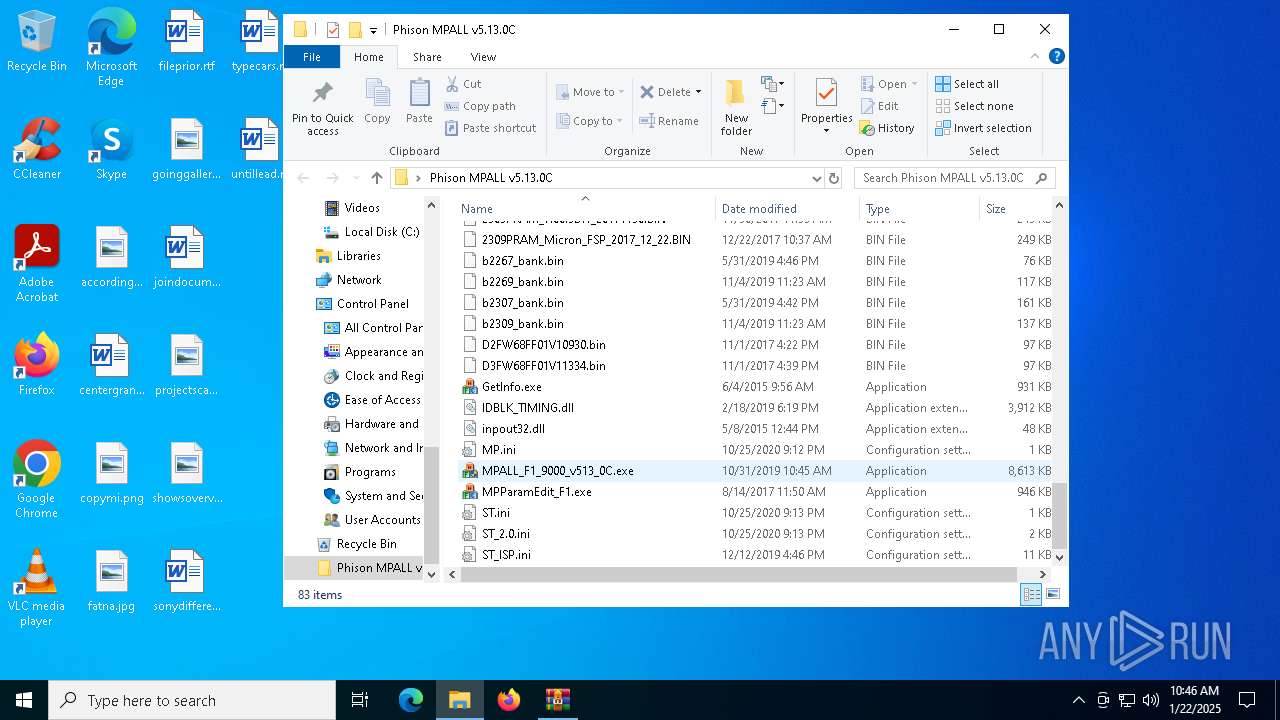
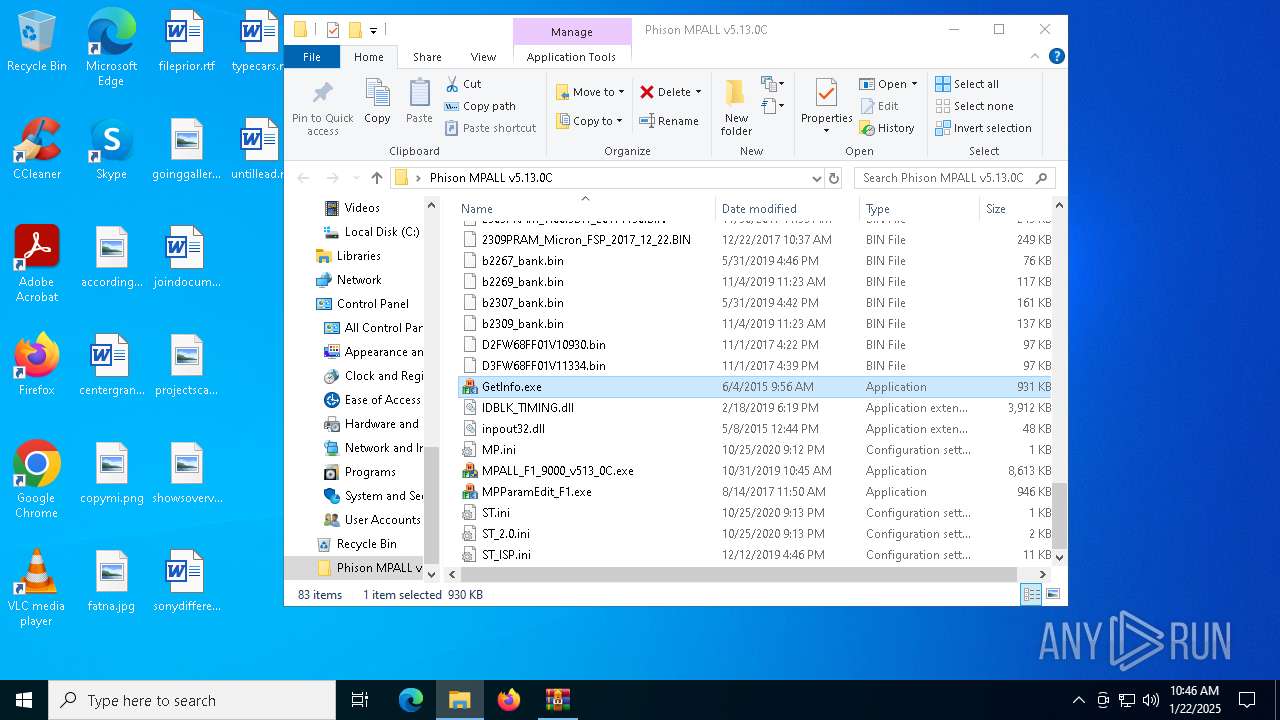
Manual execution by a user
- MPALL_F1_9000_v513_0C.exe (PID: 5748)
- GetInfo.exe (PID: 1448)
- MPALL_F1_9000_v513_0C.exe (PID: 4952)
Reads the computer name
- GetInfo.exe (PID: 1448)
- MPALL_F1_9000_v513_0C.exe (PID: 5748)
Executable content was dropped or overwritten
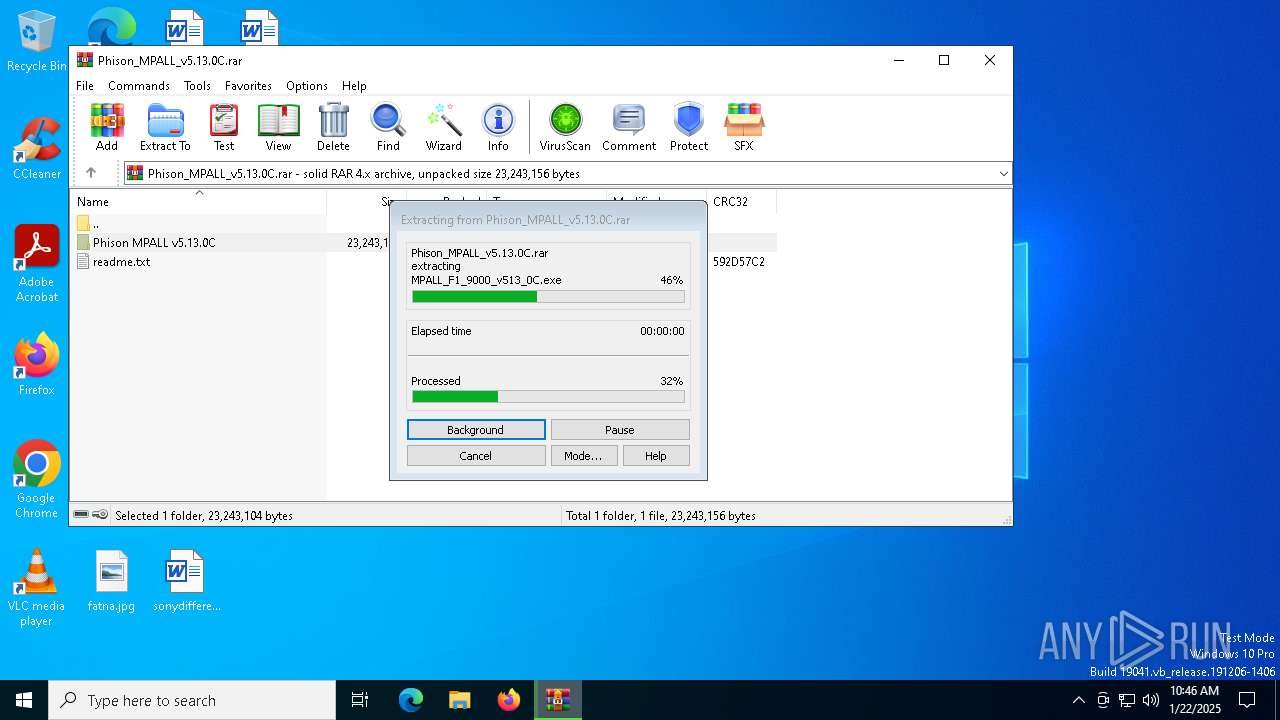
- WinRAR.exe (PID: 6352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| FileVersion: | RAR v4 |
|---|---|
| CompressedSize: | 595 |
| UncompressedSize: | 707 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2020:10:25 21:12:46 |
| PackingMethod: | Best Compression |
| ArchivedFileName: | Phison MPALL v5.13.0C\MP.ini |
Total processes
129
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
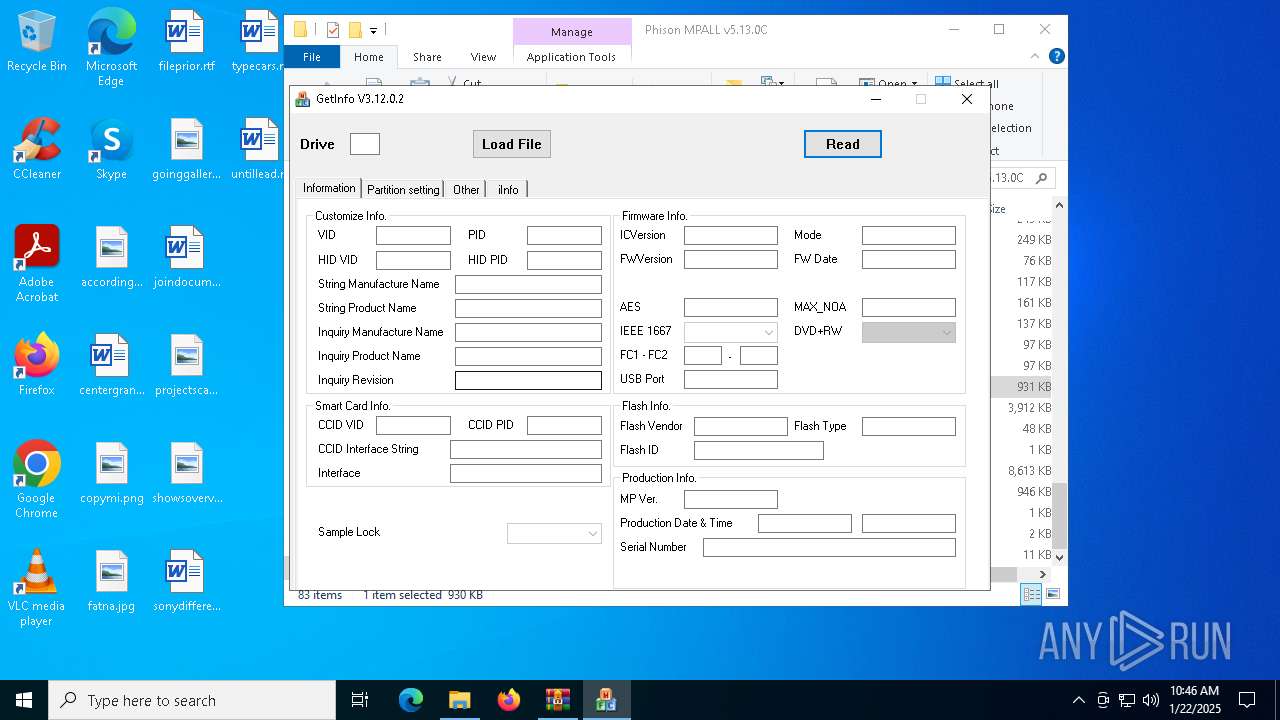
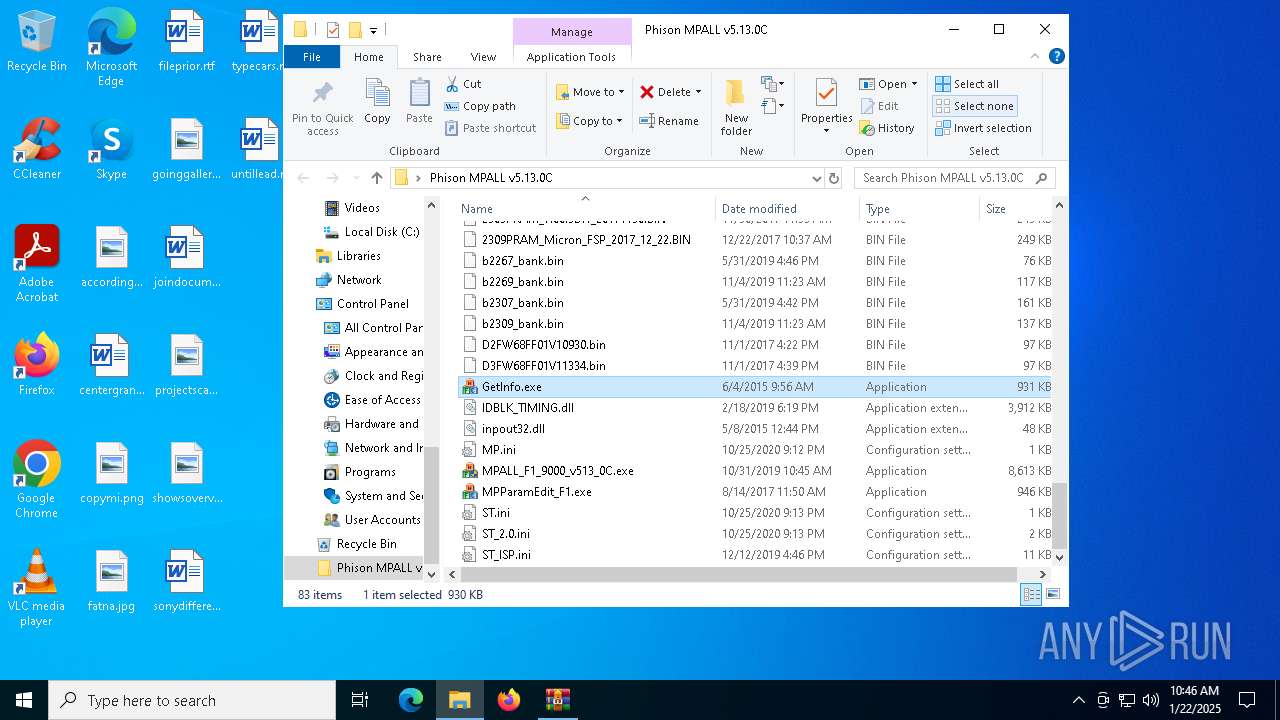
| 1448 | "C:\Users\admin\Desktop\Phison MPALL v5.13.0C\GetInfo.exe" | C:\Users\admin\Desktop\Phison MPALL v5.13.0C\GetInfo.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Version: 3, 12, 0, 2 Modules
| |||||||||||||||
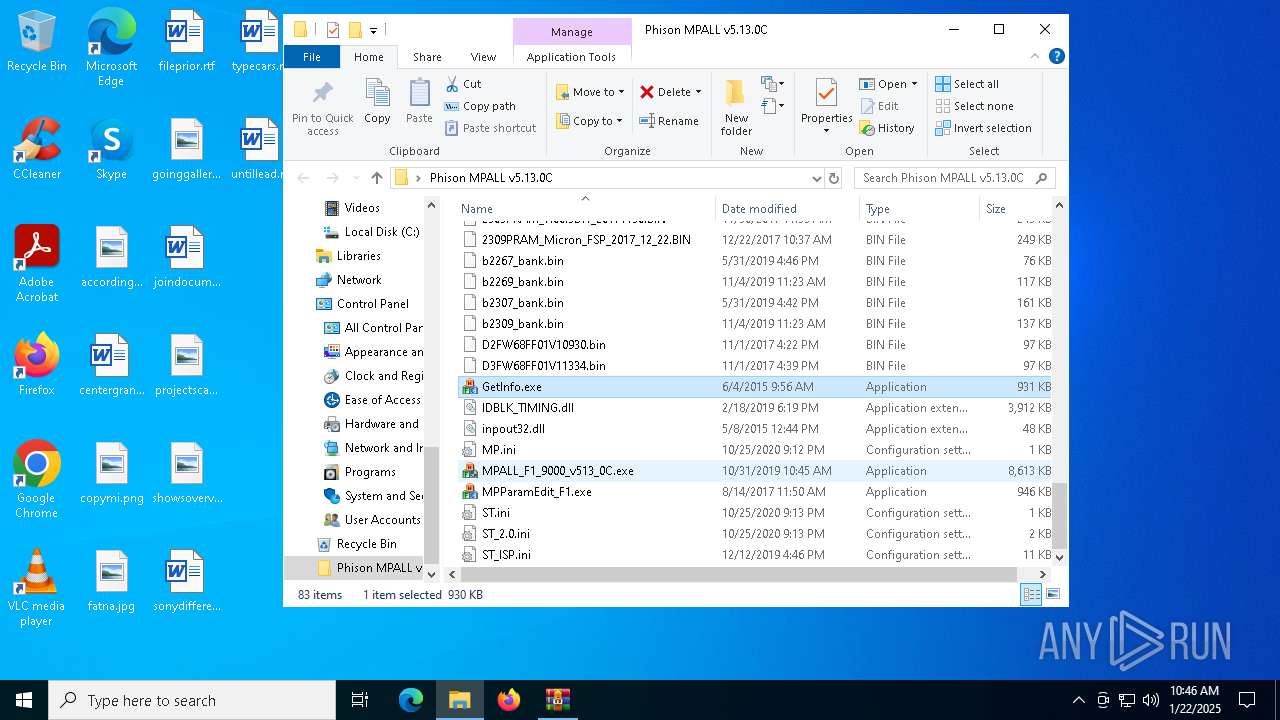
| 4952 | "C:\Users\admin\Desktop\Phison MPALL v5.13.0C\MPALL_F1_9000_v513_0C.exe" | C:\Users\admin\Desktop\Phison MPALL v5.13.0C\MPALL_F1_9000_v513_0C.exe | — | explorer.exe | |||||||||||
User: admin Company: Best Company Integrity Level: MEDIUM Description: Build by VC Exit code: 3221226540 Version: 2.0.1.6 Modules
| |||||||||||||||
| 5748 | "C:\Users\admin\Desktop\Phison MPALL v5.13.0C\MPALL_F1_9000_v513_0C.exe" | C:\Users\admin\Desktop\Phison MPALL v5.13.0C\MPALL_F1_9000_v513_0C.exe | explorer.exe | ||||||||||||
User: admin Company: Best Company Integrity Level: HIGH Description: Build by VC Version: 2.0.1.6 Modules
| |||||||||||||||
| 5916 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
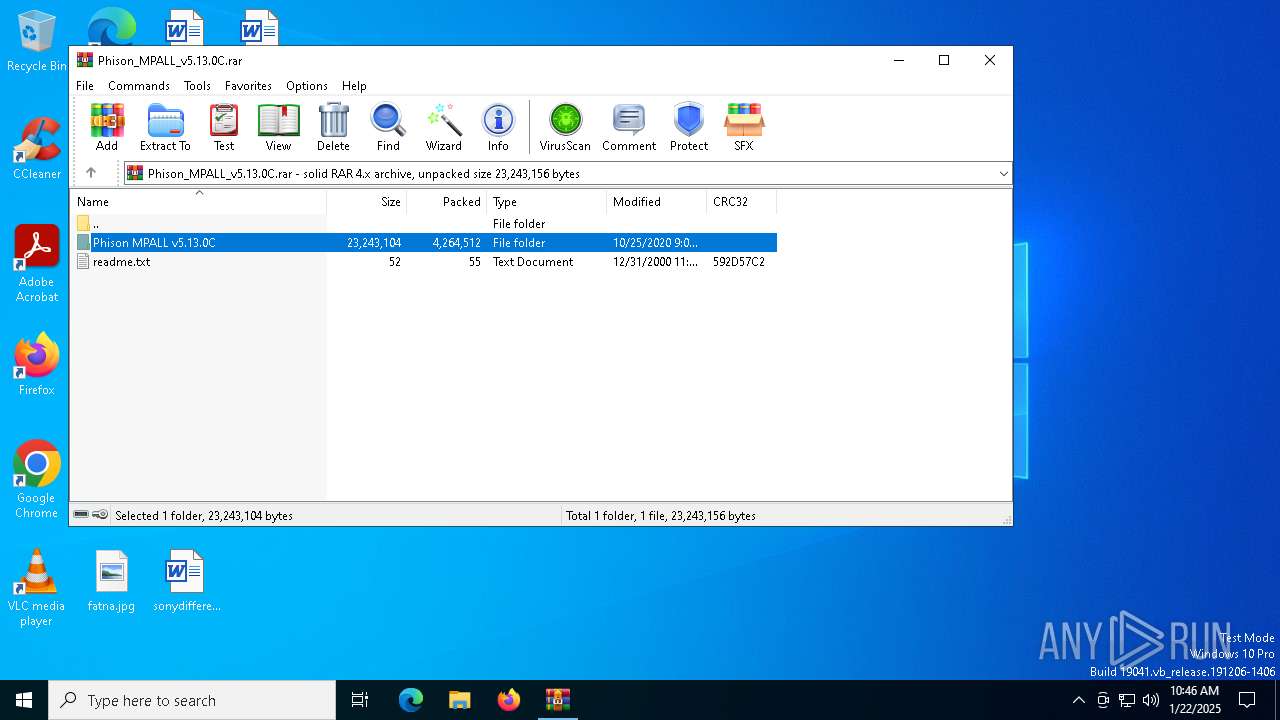
| 6352 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Phison_MPALL_v5.13.0C.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
1 781
Read events
1 763
Write events
18
Delete events
0
Modification events
| (PID) Process: | (6352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Phison_MPALL_v5.13.0C.rar | |||
| (PID) Process: | (6352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5748) MPALL_F1_9000_v513_0C.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\cdrom |
| Operation: | write | Name: | AutoRun |
Value: 0 | |||
| (PID) Process: | (5748) MPALL_F1_9000_v513_0C.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\usbflags |
| Operation: | write | Name: | IgnoreHWSerNum13fe3100 |
Value: 01 | |||
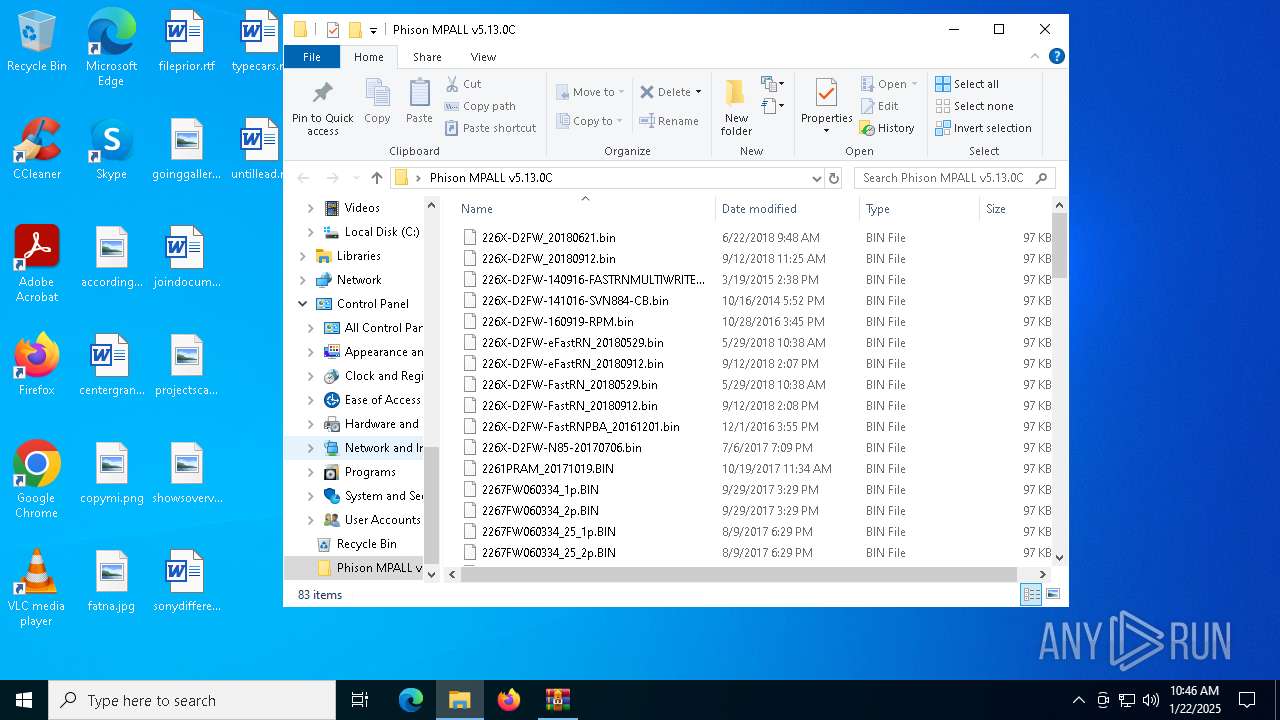
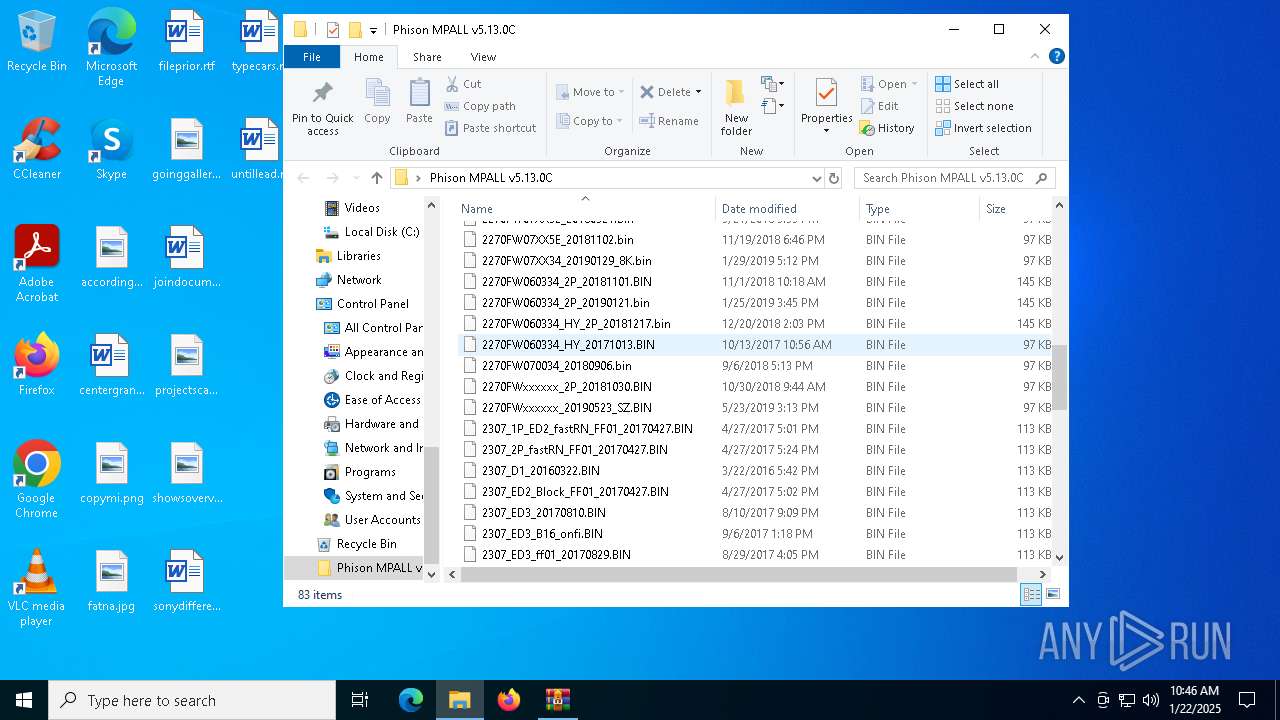
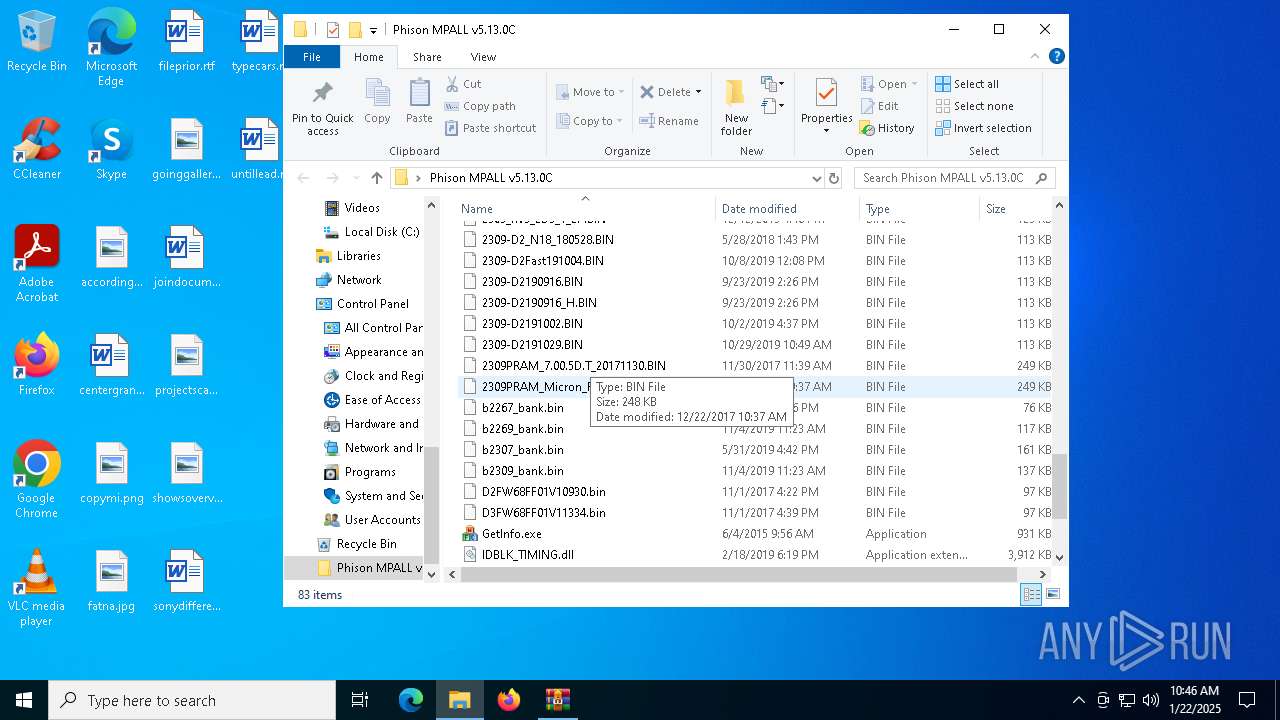
Executable files
14
Suspicious files
73
Text files
1
Unknown types
0
Dropped files
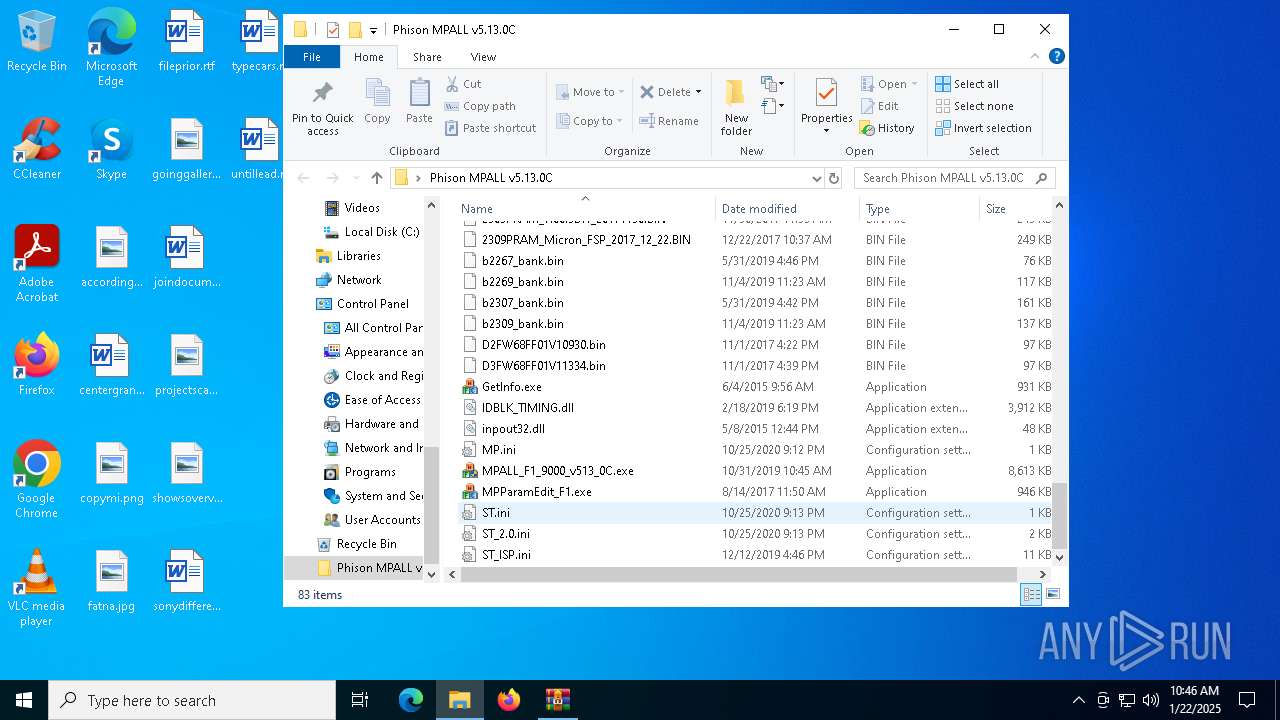
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6352.7872\Phison MPALL v5.13.0C\inpout32.dll | executable | |
MD5:99ECECB007D9D62941AC0EDCDB4C265E | SHA256:2A08780ECD3A2C42BEBDA55D3EEC3A69A417312E7A884F89B53AECAD729B9AF3 | |||
| 6352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6352.7872\Phison MPALL v5.13.0C\2261PRAM_20171019.BIN | binary | |
MD5:ED0A2A5F61184384652EDD95023D6095 | SHA256:6046750A5EF7E65253D18328E61F02C90DBA47F896951175255BC467812CE02F | |||
| 6352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6352.7872\Phison MPALL v5.13.0C\ST.ini | text | |
MD5:C0A56324488E8CA18224D107029C3660 | SHA256:D4010463F7CABC47389DE5FBB6D15AE1DCDFD97BC44BF3A1BA3B04118B822A6D | |||
| 6352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6352.7872\Phison MPALL v5.13.0C\MP.ini | text | |
MD5:C0A56324488E8CA18224D107029C3660 | SHA256:D4010463F7CABC47389DE5FBB6D15AE1DCDFD97BC44BF3A1BA3B04118B822A6D | |||
| 6352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6352.7872\Phison MPALL v5.13.0C\MPALL_F1_9000_v513_0C.exe | executable | |
MD5:0B7385B9B717FD12FE45D984FBF91D0E | SHA256:F61E264404E768E80F1FE09C09205882B42EB2C2C773B18926E86070B28F0704 | |||
| 6352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6352.7872\Phison MPALL v5.13.0C\ST_ISP.ini | text | |
MD5:8F9F39CFFA8A79D8A59F294C07DB64DD | SHA256:4CF5478AC30F801277B5D68269532E04DD3845B6E0979CE125D610CFC5722B9E | |||
| 6352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6352.7872\Phison MPALL v5.13.0C\ST_2.0.ini | text | |
MD5:A66825D350905E62E47B3AC2BD2083AC | SHA256:E20C7579201B89B9B89BCBD9EB7CCBEEC10907500A4F6987C4F0D7EF3E957C33 | |||
| 6352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6352.7872\Phison MPALL v5.13.0C\2267FW060334_2p.BIN | binary | |
MD5:55C95DE47198F8473C5DD64F5D573964 | SHA256:0C9427FD08D4285622FA53BCC37A8AFB0DAC1535957CCB9D81849910A6E2BFF3 | |||
| 6352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6352.7872\Phison MPALL v5.13.0C\IDBLK_TIMING.dll | executable | |
MD5:1DAFD56538A94B6DA2B4C76C63981573 | SHA256:7FA222EF7132D64218C9DE375F7B5B392AF3141AACB4A4BBB6ECE6203A8936F5 | |||
| 6352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6352.7872\Phison MPALL v5.13.0C\2267FW060334_20180503.BIN | binary | |
MD5:A3774EB8EE8AD58782422AF55E57DCE7 | SHA256:77464307D375CF731696F557F3A0455C2CDCBE4008EEE961491D22165D597FDD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 973 b | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
6520 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
7044 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 419 b | whitelisted |
7044 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | QA | binary | 408 b | whitelisted |
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 1.01 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 104.126.37.162:443 | — | Akamai International B.V. | DE | unknown |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.161:443 | — | Akamai International B.V. | DE | unknown |
1076 | svchost.exe | 2.23.242.9:443 | go.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1176 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
GetInfo.exe | 2 |
GetInfo.exe | 3 |
MPALL_F1_9000_v513_0C.exe | LockPort |
MPALL_F1_9000_v513_0C.exe | ****CMPProgramDlg::GetVarFromIni
|
MPALL_F1_9000_v513_0C.exe | blEraseKeepEarly = 1 |
MPALL_F1_9000_v513_0C.exe | W7 GetMACaddress start |
MPALL_F1_9000_v513_0C.exe | W7 GetMacAddress [96EE] |
MPALL_F1_9000_v513_0C.exe | IgnoreHWSerNum13fe3100 |
MPALL_F1_9000_v513_0C.exe | IgnoreHWSerNum13fe3400 |
MPALL_F1_9000_v513_0C.exe | Get ini File 3 |