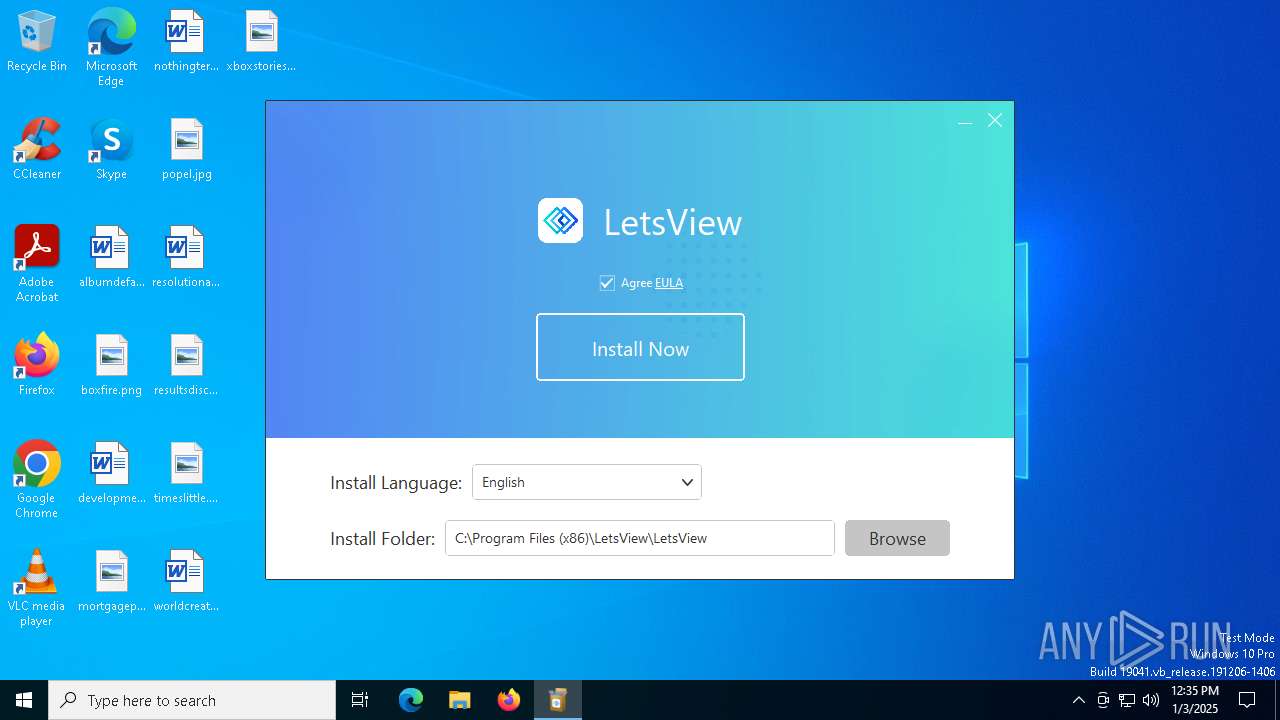
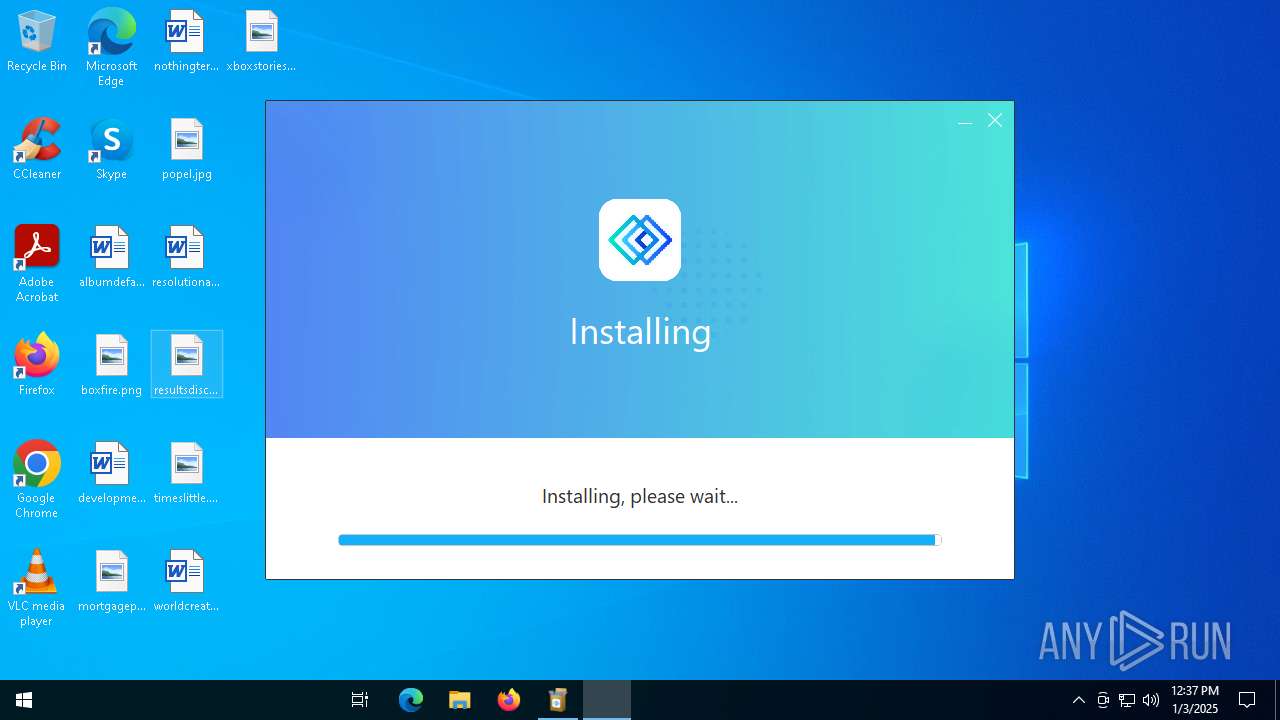
| download: | /letsview-setup.exe |
| Full analysis: | https://app.any.run/tasks/6de219e2-83bf-4eff-a0f7-cbcdeb88157a |
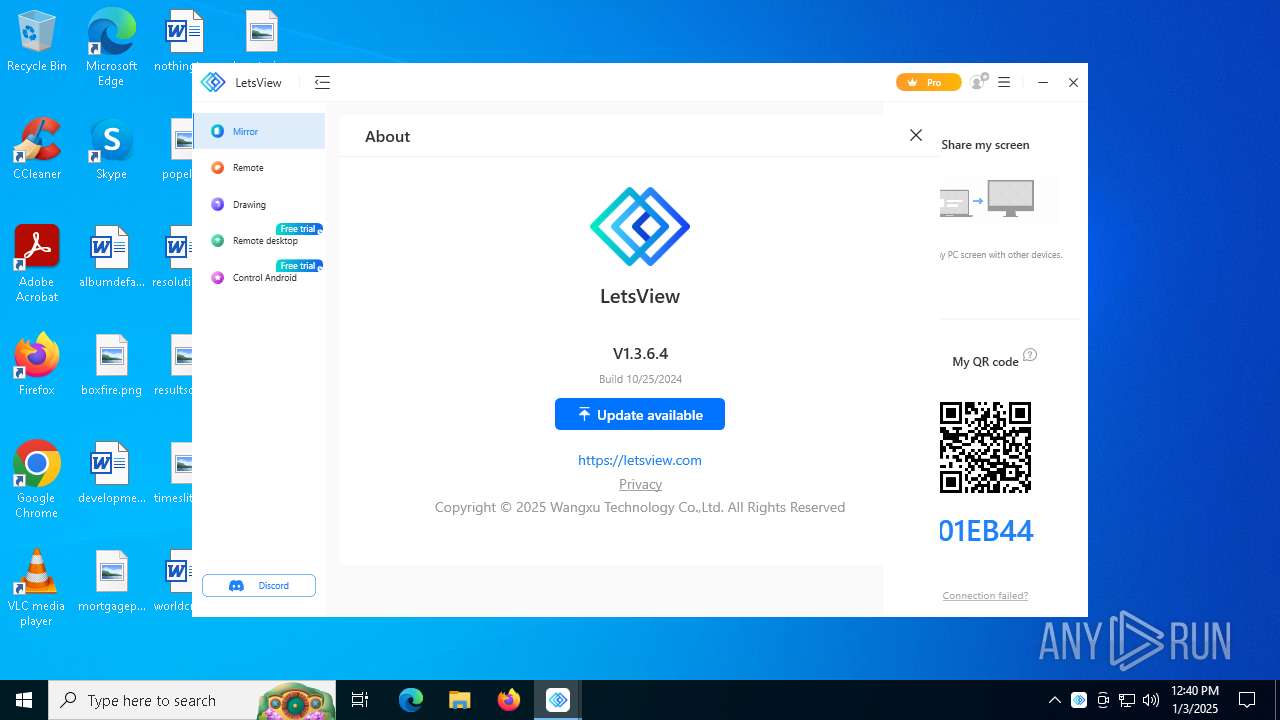
| Verdict: | Malicious activity |
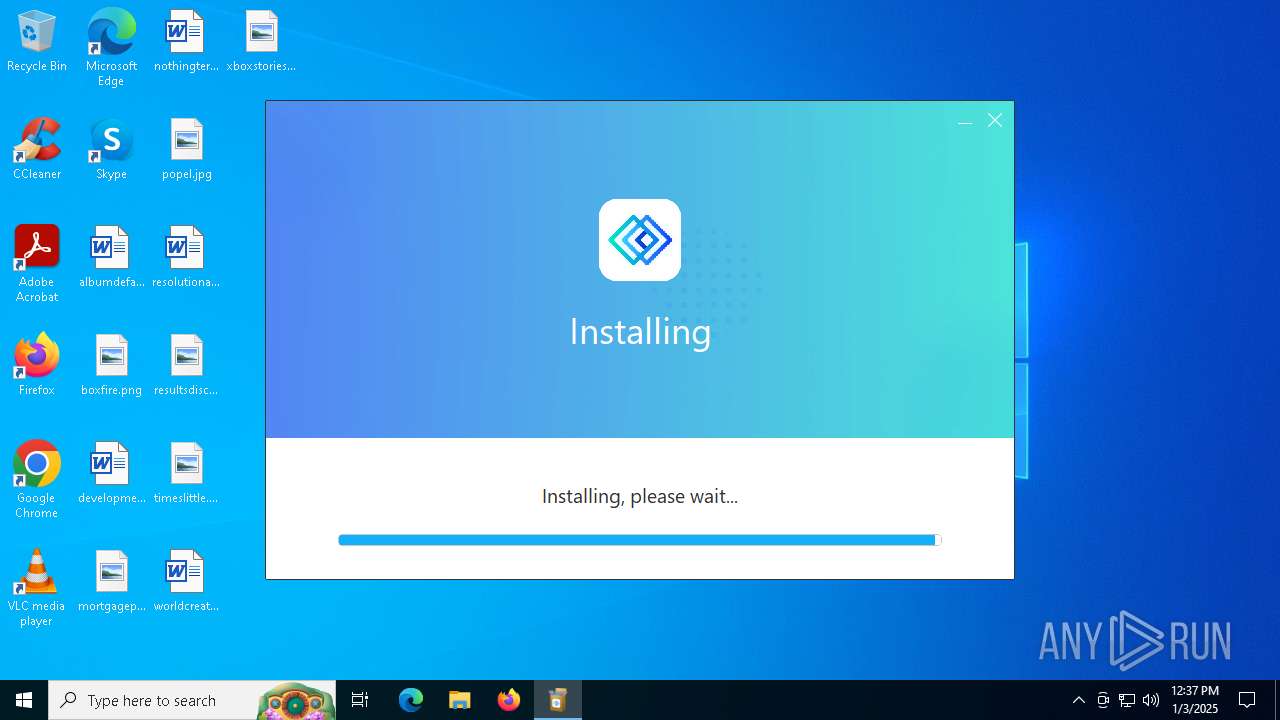
| Analysis date: | January 03, 2025, 12:34:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 7578D269FEF4AC377832C4122C78E0BB |
| SHA1: | 8901F9B7DF38BCB2E1BFAE7BAAB64A0D1F6B37A8 |
| SHA256: | 9668AD0DEF75C0BFCCFA01A0A8B4FE3AA24A4F386F0807871EDB14B979AC51BF |
| SSDEEP: | 98304:jNwW9ScCoSFaO/MB3HvlEf6AB34CfQLtQ2WKxX7Z+bhQLtQ2WKxX7CKYj:ldldW |
MALICIOUS
Executing a file with an untrusted certificate
- mDNSResponder.exe (PID: 6300)
SUSPICIOUS
Reads security settings of Internet Explorer
- letsview-setup.exe (PID: 6644)
- Letsview.exe (PID: 6104)
- PinTaskbarTool.exe (PID: 6224)
Executable content was dropped or overwritten
- installer.exe (PID: 6612)
- installer.tmp (PID: 1864)
- drvinst.exe (PID: 4468)
Stops a currently running service
- sc.exe (PID: 1576)
Windows service management via SC.EXE
- sc.exe (PID: 2744)
- sc.exe (PID: 6916)
Reads the Windows owner or organization settings
- installer.tmp (PID: 1864)
Changes Internet Explorer settings (feature browser emulation)
- installer.tmp (PID: 1864)
Process drops legitimate windows executable
- installer.tmp (PID: 1864)
- msiexec.exe (PID: 2280)
The process drops C-runtime libraries
- installer.tmp (PID: 1864)
Checks for Java to be installed
- msiexec.exe (PID: 5488)
Executes as Windows Service
- mDNSResponder.exe (PID: 6300)
- WXCastService.exe (PID: 6980)
- WUDFHost.exe (PID: 7044)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 2280)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- installer.tmp (PID: 1864)
Executing commands from a ".bat" file
- installer.tmp (PID: 1864)
- WXCastService.exe (PID: 6980)
Starts CMD.EXE for commands execution
- installer.tmp (PID: 1864)
- WXCastService.exe (PID: 6980)
Creates a new Windows service
- sc.exe (PID: 5200)
Uses ICACLS.EXE to modify access control lists
- installer.tmp (PID: 1864)
Uses NETSH.EXE to add a firewall rule or allowed programs
- installer.tmp (PID: 1864)
Creates files in the driver directory
- deviceinstaller64.exe (PID: 1828)
- drvinst.exe (PID: 4468)
Checks Windows Trust Settings
- drvinst.exe (PID: 4468)
INFO
Checks supported languages
- letsview-setup.exe (PID: 6644)
- installer.exe (PID: 6612)
- installer.tmp (PID: 1864)
- msiexec.exe (PID: 2280)
- msiexec.exe (PID: 6860)
- msiexec.exe (PID: 5732)
- WXCastService.exe (PID: 6980)
- mDNSResponder.exe (PID: 6300)
- Letsview.exe (PID: 6104)
- deviceinstaller64.exe (PID: 1828)
- PinTaskbarTool.exe (PID: 6224)
- drvinst.exe (PID: 4468)
- drvinst.exe (PID: 1796)
Creates files in the program directory
- letsview-setup.exe (PID: 6644)
- installer.tmp (PID: 1864)
- WXCastService.exe (PID: 6980)
Reads the computer name
- letsview-setup.exe (PID: 6644)
- installer.tmp (PID: 1864)
- msiexec.exe (PID: 5732)
- msiexec.exe (PID: 6860)
- msiexec.exe (PID: 2280)
- PinTaskbarTool.exe (PID: 6224)
- mDNSResponder.exe (PID: 6300)
- deviceinstaller64.exe (PID: 1828)
- drvinst.exe (PID: 4468)
Process checks computer location settings
- letsview-setup.exe (PID: 6644)
- Letsview.exe (PID: 6104)
- PinTaskbarTool.exe (PID: 6224)
The process uses the downloaded file
- letsview-setup.exe (PID: 6644)
Create files in a temporary directory
- installer.exe (PID: 6612)
- letsview-setup.exe (PID: 6644)
- installer.tmp (PID: 1864)
The sample compiled with english language support
- installer.tmp (PID: 1864)
- msiexec.exe (PID: 2280)
Application launched itself
- msiexec.exe (PID: 2280)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2280)
Checks proxy server information
- msiexec.exe (PID: 5488)
- Letsview.exe (PID: 6104)
The sample compiled with chinese language support
- installer.tmp (PID: 1864)
Creates files or folders in the user directory
- installer.tmp (PID: 1864)
- Letsview.exe (PID: 6104)
Creates a software uninstall entry
- msiexec.exe (PID: 2280)
Sends debugging messages
- WXCastService.exe (PID: 6980)
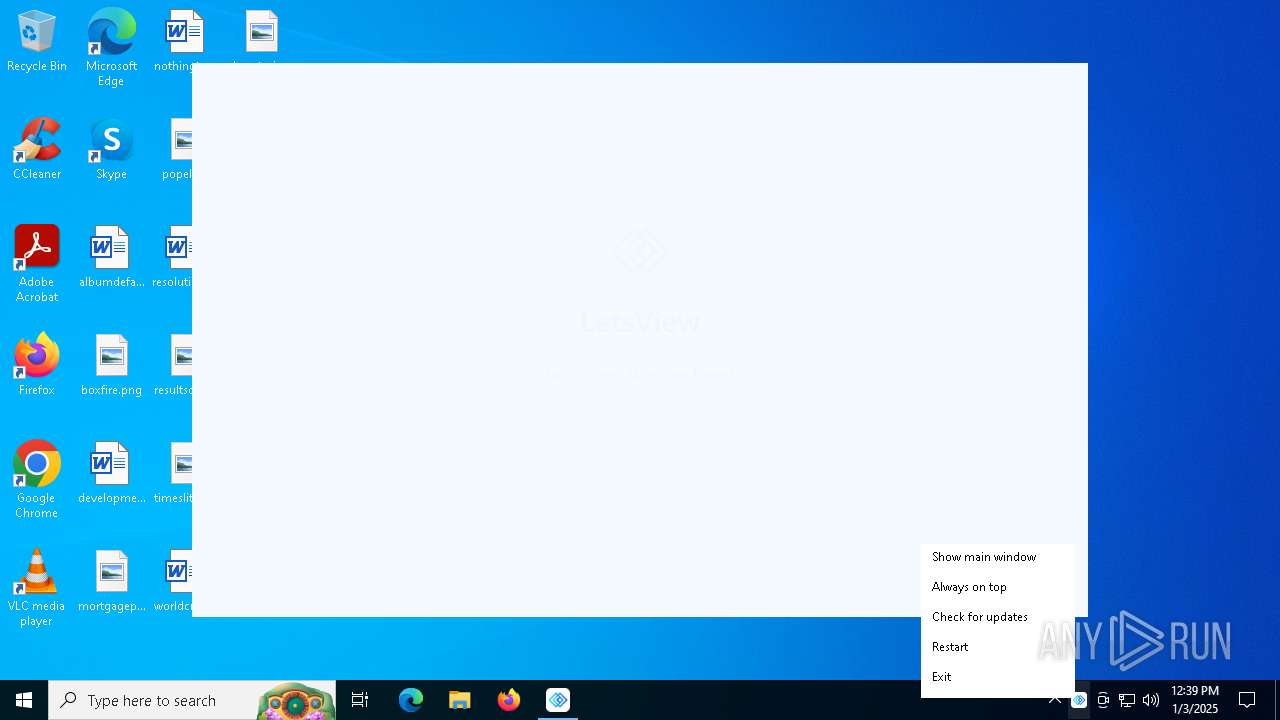
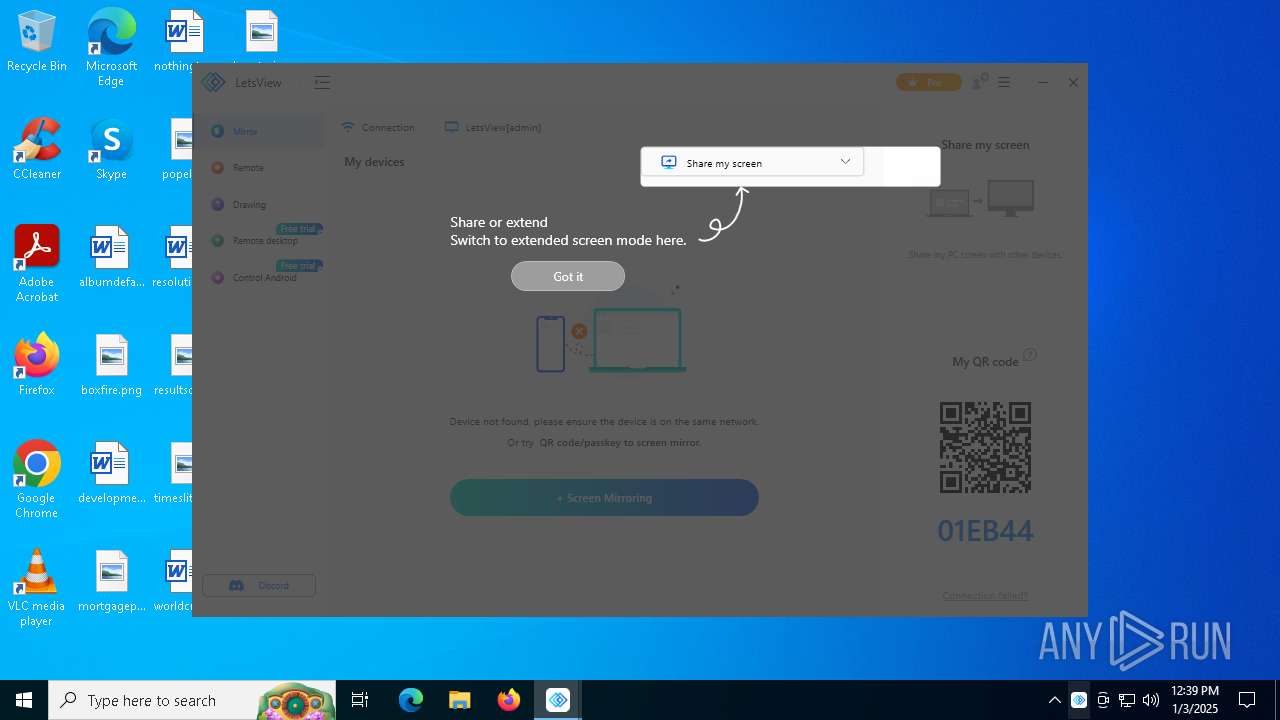
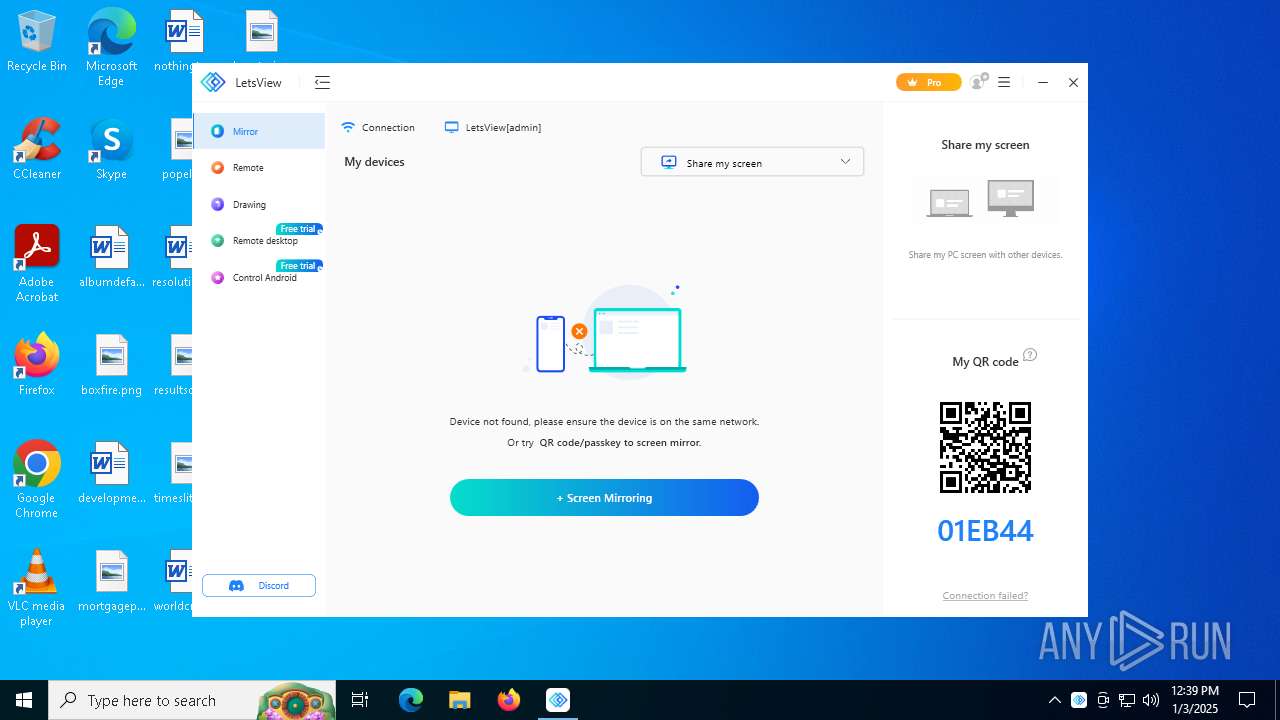
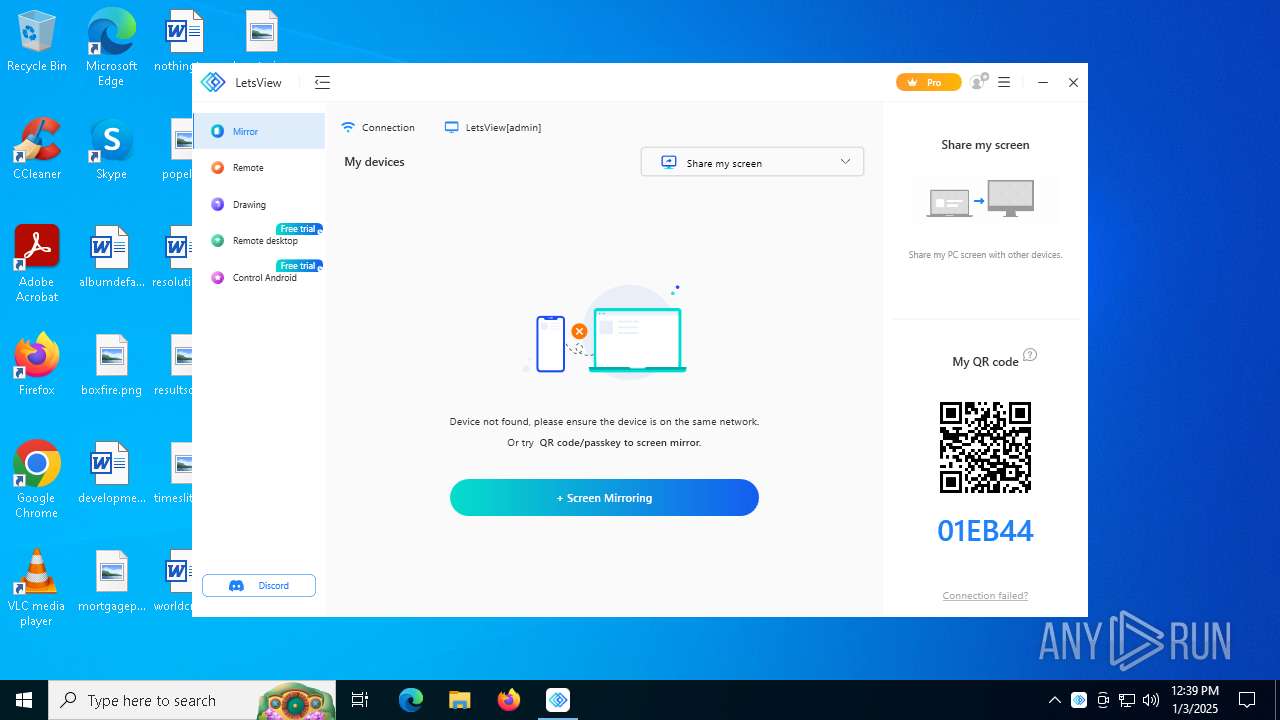
Manual execution by a user
- Letsview.exe (PID: 6104)
Reads CPU info
- Letsview.exe (PID: 6104)
Reads the machine GUID from the registry
- Letsview.exe (PID: 6104)
- PinTaskbarTool.exe (PID: 6224)
- drvinst.exe (PID: 4468)
Reads the software policy settings
- deviceinstaller64.exe (PID: 1828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (18) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.9) |
| .exe | | | Generic Win/DOS Executable (1.3) |
| .exe | | | DOS Executable Generic (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:05:30 03:26:04+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 1210368 |
| InitializedDataSize: | 1291264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xe6115 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.1.5 |
| ProductVersionNumber: | 1.1.1.5 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | LetsView |
| FileDescription: | LetsView Installer |
| FileVersion: | 1.1.1.5 |
| InternalName: | LetsView Installer.exe |
| LegalCopyright: | Copyright (C) 2023 WANGXU TECHNOLOGY CO. Ltd. |
| OriginalFileName: | LetsView Installer.exe |
| ProductName: | LetsView Installer |
| ProductVersion: | 1.1.1.5 |
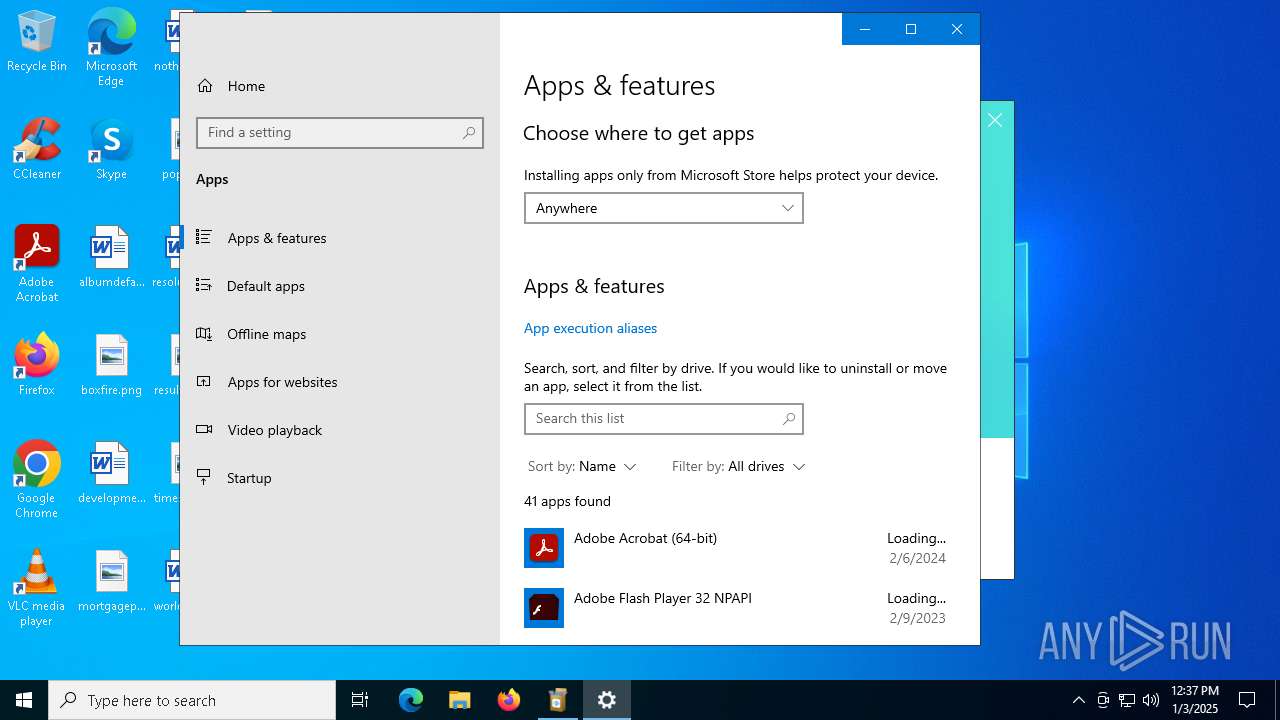
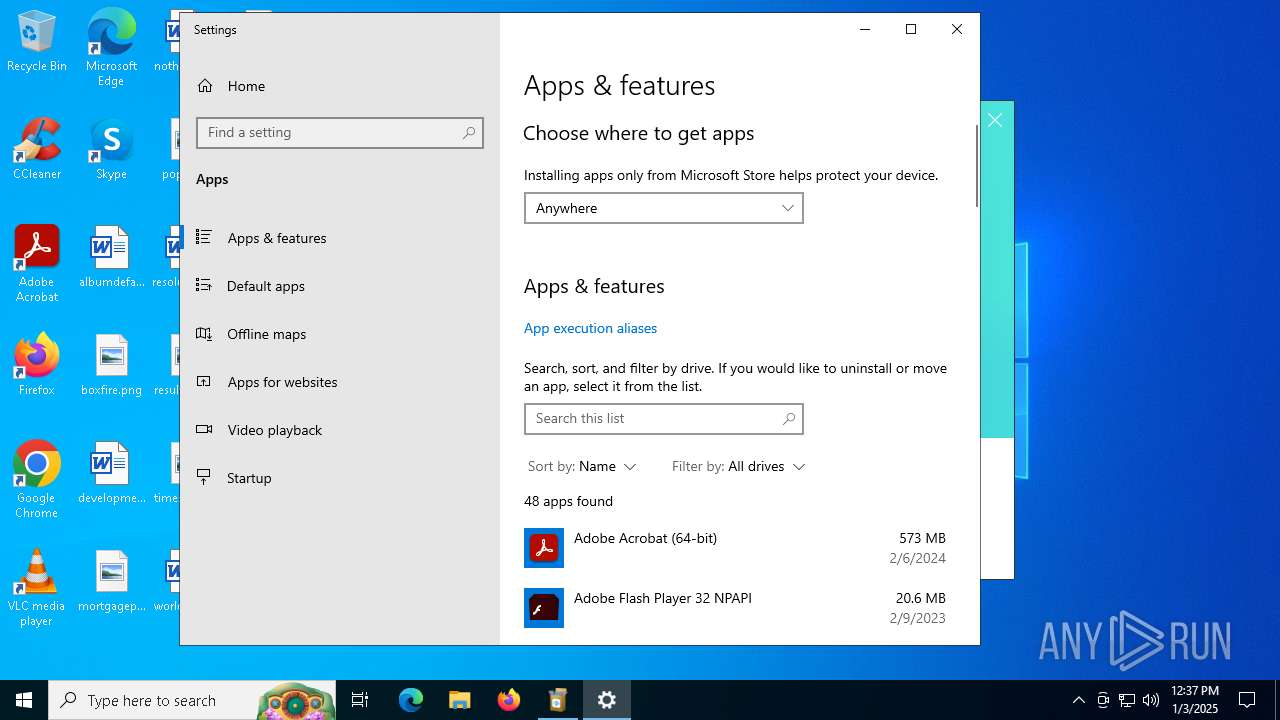
Total processes
185
Monitored processes
42
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\Program Files (x86)\Bonjour\mdnsNSP.dll" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1576 | "sc" stop LetsViewService | C:\Windows\SysWOW64\sc.exe | — | installer.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1668 | "C:\WINDOWS\system32\cmd.exe" /C ""C:\Program Files (x86)\LetsView\LetsView\usbmmidd_v2\wxcastservice_start.bat"" | C:\Windows\SysWOW64\cmd.exe | — | installer.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1796 | DrvInst.exe "2" "211" "ROOT\DISPLAY\0000" "C:\WINDOWS\INF\oem1.inf" "oem1.inf:d470a17d4e87d07b:MyDevice_Install:2.0.0.1:usbmmidd," "4f9666e1f" "0000000000000204" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 1828 | deviceinstaller64.exe install usbmmidd.inf usbmmidd | C:\Program Files (x86)\LetsView\LetsView\usbmmidd_v2\deviceinstaller64.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Amyuni Technologies Integrity Level: SYSTEM Description: USB Mobile Monitor Device Installer Exit code: 0 Version: 1, 0, 2, 9 | |||||||||||||||
| 1864 | "C:\Users\admin\AppData\Local\Temp\is-544A2.tmp\installer.tmp" /SL5="$502D2,46659782,920064,C:\Users\admin\AppData\Local\Temp\installer.exe" /VERYSILENT /SUPPRESSMSGBOXES /FORCECLOSEAPPLICATIONS /DIR="C:\Program Files (x86)\LetsView\LetsView" /LANG=English | C:\Users\admin\AppData\Local\Temp\is-544A2.tmp\installer.tmp | installer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2280 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2744 | "sc" delete LetsViewService | C:\Windows\SysWOW64\sc.exe | — | installer.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3640 | "icacls" "C:\Users\admin\Documents\LetsView\LetsView" /grant Users:(OI)(CI)(F) /t | C:\Windows\SysWOW64\icacls.exe | — | installer.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 3 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
32 761
Read events
32 305
Write events
428
Delete events
28
Modification events
| (PID) Process: | (1864) installer.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | LetsView.exe |
Value: 11001 | |||
| (PID) Process: | (1864) installer.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | CertificateRevocation |
Value: 0 | |||
| (PID) Process: | (1864) installer.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WinTrust\Trust Providers\Software Publishing |
| Operation: | write | Name: | State |
Value: 146944 | |||
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\E2973290AA2EED1189EFB358558D5939 |
| Operation: | write | Name: | 8BFDDD6597F70844985D521E5FA22BF8 |
Value: C:\?WINDOWS\system32\jdns_sd.dll | |||
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\4FFEE71173BD0E113858BB12944210B9 |
| Operation: | write | Name: | 8BFDDD6597F70844985D521E5FA22BF8 |
Value: C:\Program Files\Bonjour\dns_sd.jar | |||
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\9606584ACD9166045B551767F3CC6A8F |
| Operation: | write | Name: | 8BFDDD6597F70844985D521E5FA22BF8 |
Value: C:\Program Files\Bonjour\ | |||
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedDlls |
| Operation: | write | Name: | C:\WINDOWS\system32\jdns_sd.dll |
Value: 1 | |||
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\AB0314D776C27C545BAAEAB8DBF8474A |
| Operation: | write | Name: | 8BFDDD6597F70844985D521E5FA22BF8 |
Value: C:\?WINDOWS\SysWOW64\jdns_sd.dll | |||
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\57F0E281463ADB44392A152014012252 |
| Operation: | write | Name: | 8BFDDD6597F70844985D521E5FA22BF8 |
Value: C:\Program Files (x86)\Bonjour\dns_sd.jar | |||
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\52C3F7D42A4EF244CA22A8C79C130119 |
| Operation: | write | Name: | 8BFDDD6597F70844985D521E5FA22BF8 |
Value: C:\Program Files (x86)\Bonjour\ | |||
Executable files
367
Suspicious files
46
Text files
2 193
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6644 | letsview-setup.exe | C:\Users\admin\AppData\Local\Temp\installer.exe | — | |
MD5:— | SHA256:— | |||
| 6644 | letsview-setup.exe | C:\Users\admin\AppData\Local\Temp\installer.exe.err.log | text | |
MD5:BC22565517F6D611D54FA8E4F82BF277 | SHA256:0E66DEE5C690F07B7094AC8D83B4A1457FEF5E0F31A361940EF576D2DEF3B88B | |||
| 6644 | letsview-setup.exe | C:\Users\admin\AppData\Local\Temp\_gaid.txt | text | |
MD5:D4E7BE7017E2627A9B3B9422F8A12E65 | SHA256:5858091F6A3EE3AF9F202C49B63E6D67F8641ABA5C0C4097928A3EBE759EFBBB | |||
| 1864 | installer.tmp | C:\Users\admin\AppData\Local\Temp\is-ANR0V.tmp\isxdl.dll | executable | |
MD5:F7B445A6CB2064D7B459451E86CA6B0E | SHA256:BD03543C37FEB48432E166FE3898ABC2A7FE854B1113EE4D5D284633B4605377 | |||
| 1864 | installer.tmp | C:\Program Files (x86)\LetsView\LetsView\is-63SM7.tmp | executable | |
MD5:FE523CF564489A7CDD4BAAA99845E74F | SHA256:74A6FA40CC3351AB22A387A94D62C4012913F6303FD4F997304C01DC691BA0FC | |||
| 6612 | installer.exe | C:\Users\admin\AppData\Local\Temp\is-544A2.tmp\installer.tmp | executable | |
MD5:88EBA8CDA15027AAB1700DB1F80570F8 | SHA256:F6B079D36AADF4DCEA30AC84752A528CD70185BC85D52B9E94813B8717FB713D | |||
| 1864 | installer.tmp | C:\Program Files (x86)\LetsView\LetsView\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:7FEC155413DACDCDF317125D0028864C | SHA256:E67E489A49D060E62D84E9DA69A6D75AAE16BCDCF4F3A1A93C5736D38B442FBF | |||
| 1864 | installer.tmp | C:\Program Files (x86)\LetsView\LetsView\is-0M54N.tmp | executable | |
MD5:14B60DED99DF8E266A906164C02D19E0 | SHA256:5AEB3573394FC01B3001F65A20DA936DC7C5275DD44AAE95C03EE34FED2BC067 | |||
| 1864 | installer.tmp | C:\Users\admin\AppData\Local\Temp\is-ANR0V.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 1864 | installer.tmp | C:\Program Files (x86)\LetsView\LetsView\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:35E0A11F1BDBFF0C994F769FC5BEFA14 | SHA256:740FE94F94043B42710641ABF81693F4794D57D4DE9AB552498F796046550B13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
78
DNS requests
48
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6644 | letsview-setup.exe | GET | 200 | 47.90.119.19:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=39e30d720e18376278a9be61a436df98&session_id=1735907706&app=LetsView&appid=349&apptype=saas&installer_version=1.1.1.5&is_old_user=-1&last_step_duration=0&os_available_memory=2663964000&os_culture=0409&os_dpi=100&os_fullname=Microsoft%20Windows%2010%20Pro&os_lang=en-US&os_resolution=1280x720&os_total_memory=4188620000&os_version=10.0.19045&step=1 | unknown | — | — | unknown |
6644 | letsview-setup.exe | GET | 200 | 47.90.119.19:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=39e30d720e18376278a9be61a436df98&session_id=1735907706&app=LetsView&appid=349&ga_request=https%3A%2F%2Fdownload.aoscdn.com%2Fapi%2Fclient%2Finfo%3Fot%3D1%26mt%3D1735907704%26ct%3D1735907704%26cc%3D4%26tz%3DGMT%252B0000%26ov%3D10.0%26g%3DMicrosoft%2520Basic%2520Display%2520Adapter%26h%3D7578d269fef4ac377832c4122c78e0bb&step=1 | unknown | — | — | unknown |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6644 | letsview-setup.exe | GET | 200 | 47.90.119.19:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=39e30d720e18376278a9be61a436df98&session_id=1735907706&app=LetsView&appid=349&ga_error=&ga_ok=0&ga_response=%7B%22status%22%3A404%2C%22message%22%3A%22Not%20found%22%7D&gaid=&step=1 | unknown | — | — | unknown |
6644 | letsview-setup.exe | GET | 200 | 47.90.119.19:80 | http://wx-user-behavior.cn-hongkong.log.aliyuncs.com/logstores/webtrack/track?APIVersion=0.6.0&__topic__=win-launcher&unique_id=39e30d720e18376278a9be61a436df98&session_id=1735907706&app=LetsView&app_install_path=C%3A%5CProgram%20Files%20%28x86%29%5CLetsView%5CLetsView&app_lang=English&appid=349&apptype=saas&last_step_duration=8&step=2 | unknown | — | — | unknown |
6644 | letsview-setup.exe | GET | 404 | 163.181.131.215:80 | http://cdn.aoscdn.com/img/contact-group/installer-349-qq.png?20091 | unknown | — | — | whitelisted |
6644 | letsview-setup.exe | GET | 302 | 47.243.121.132:80 | http://download.aoscdn.com/down.php?softid=letsviewinstall | unknown | — | — | unknown |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.21.245.134:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3996 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3220 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.21.245.14:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6644 | letsview-setup.exe | 47.90.119.19:80 | wx-user-behavior.cn-hongkong.log.aliyuncs.com | Alibaba US Technology Co., Ltd. | HK | suspicious |
6644 | letsview-setup.exe | 47.243.121.132:443 | download.aoscdn.com | Alibaba US Technology Co., Ltd. | HK | suspicious |
— | — | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| unknown |
google.com |
| whitelisted |
wx-user-behavior.cn-hongkong.log.aliyuncs.com |
| unknown |
download.aoscdn.com |
| unknown |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
cdn.aoscdn.com |
| whitelisted |
download.apowersoft.info |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
2192 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
2192 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
6104 | Letsview.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6104 | Letsview.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6104 | Letsview.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6104 | Letsview.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6104 | Letsview.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6104 | Letsview.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
6104 | Letsview.exe | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
Process | Message |
|---|---|
WXCastService.exe | My Sample Service: ServiceWorkerThread: Entry |